Many of our customers need to meet regulatory compliance for their sensitive applications that deal with healthcare or financial data such as HIPPA or PCI-DSS for instance. These compliance requirements often specify the need for IDS/IPS to prevent data theft. To meet these needs VMware introduced Distributed Intrusion Detection System (IDS) with NSX-T 3.0. They later expanded with Distributed Intrusion Prevention System (IPS) in NSX-T 3.1.
IDS/IPS in NSX: How it works
The NSX Distributed IDS/IPS engines originated in Suricata, a well-known and broadly respected open-source project. NSX builds on Suricata by giving the IDS/IPS engines a runtime environment, including networking I/O and management functionality.
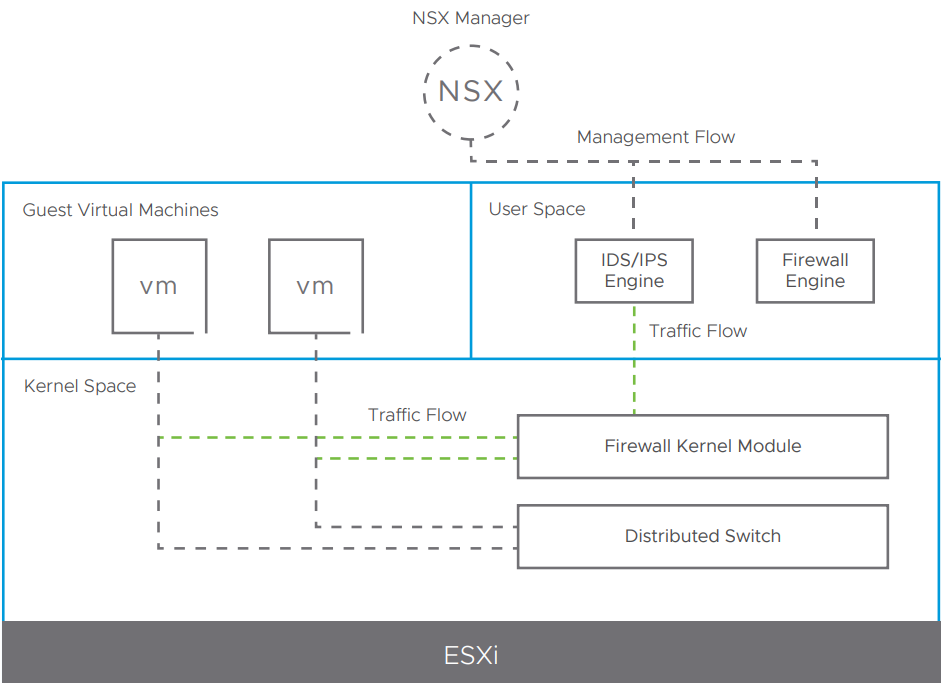
NSX co-locates the IDS/IPS functionality with the distributed firewall, leading to a single-pass design for traffic inspection. All traffic passes through the firewall first, followed by IDS/IPS inspection depending on configuration. This co-location of IDS/IPS functionality with the firewall also simplifies the expression and enforcement of network security policies.
The NSX Distributed IDS/IPS engines are housed in user space and connected to the firewall module that resides in the hypervisor's kernel. An application communicates with another application by sending traffic to the hypervisor, where the firewall inspects the traffic. Subsequently, the firewall forwards the traffic to the IDS/IPS module in user space.
For details on the IDS/IPS Architecture and Use Cases please check the NSX Security Reference Guide.
Signatures
NSX pulls signatures from multiple security providers like the recently acquired Lastline, DELL's SecureWorks and Trustwave.
Signatures can be updated automatically or on demand, in case your NSX Manager has an internet connectivity. If you run in a dark site, or just for any other reason your manager doesn't have internet connectivity, uploading an offline signature bundle is possible via API call.
Signatures can be enabled based on severity. A higher severity score indicates an increased risk associated with the intrusion event. Severity is determined based on the following:
- Severity specified in the signature itself
- CVSS (Common Vulnerability Scoring System) score specified in the signature
- Type-rating associated with the classification type
IDS detects intrusion attempts based on already known malicious instruction sequences. The detected patterns in the IDS are known as signatures. You can set a specific signature alert/drop/reject actions globally, or by profile.
Actions
- Alert - An alert is generated and no automatic preventative action is taken.
- Drop - An alert is generated and the offending packets are dropped.
- Reject - An alert is generated and the offending packets are dropped. For TCP flows, a TCP reset package is generated by IDS and sent to the source and destination of the connection. For other protocols, an ICMP-error packet is sent to the source and destination of the connection.
License
Distributed IDS/IPS feature is not available with the regular NSX-T license, it requires an addon NSX Distributed Threat Prevention license. I had to learn that the hard way:
I managed to obtain a NSX Distributed Threat Prevention license, so let's get started.
Enable IDS/IPS
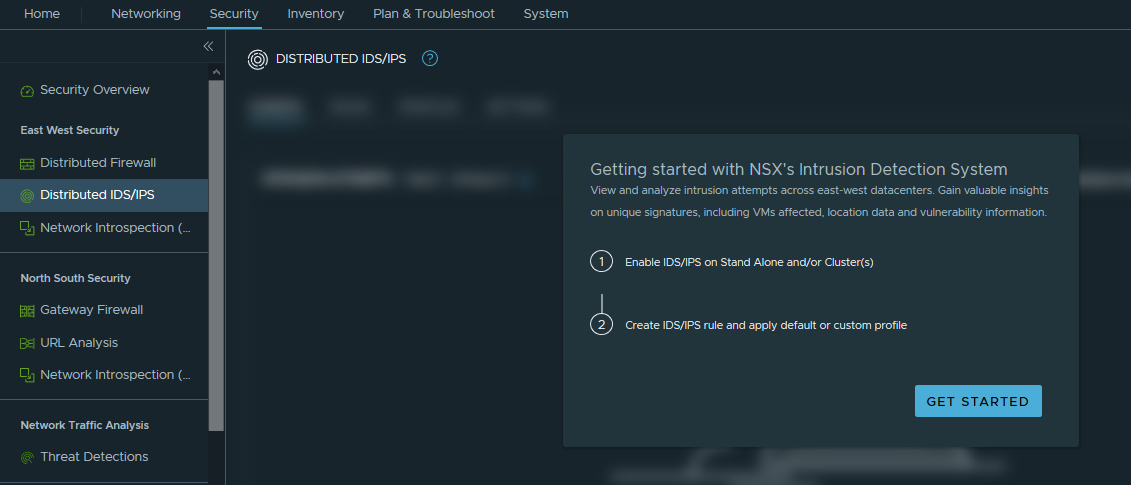
STEP 1: In the NSX-T Policy UI navigate to Security --> Distributed IDS/IPS --> GET STARTED
STEP 2: My NSX-T Manager has an internet connection, so it immediately has found a new signature version available, which I am going to update to and also enable the Auto Update new versions, as per the recommendation.
NSX-T will automatically apply signatures to your hosts and update intrusion detection signatures by checking VMware's cloud-based service. Signatures are applied to IDS rules through profiles. By default, the NSX Manager checks for new signatures once per day. New signature update versions are published every two weeks, with additional non-scheduled 0-day updates.
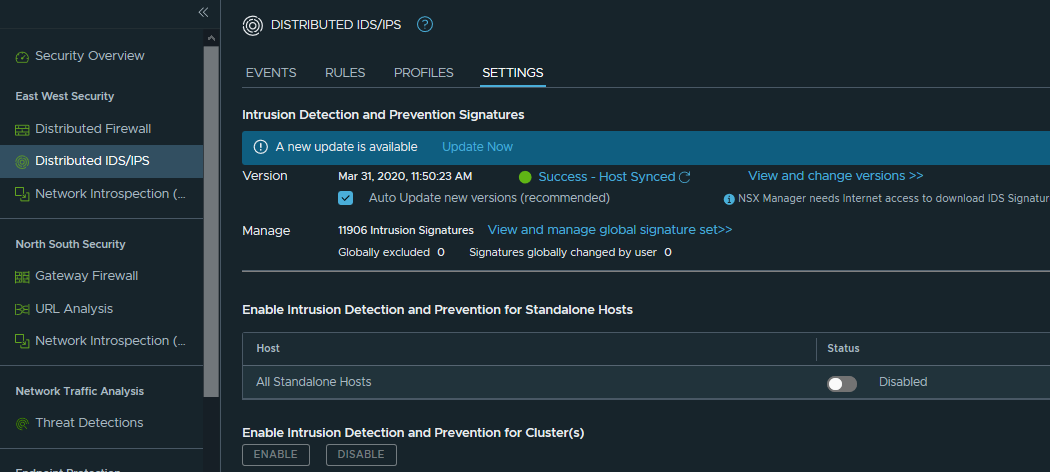
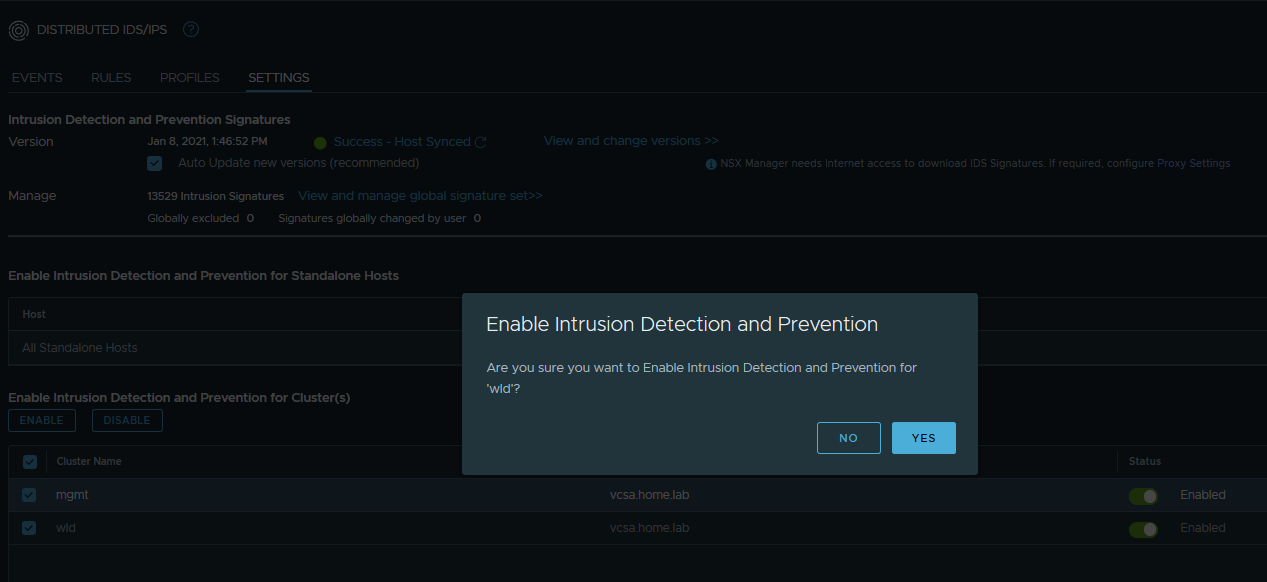
STEP 3: Once the signatures are up to date, select the cluster, where you want to enable IDS/IPS and set it to Enabled:
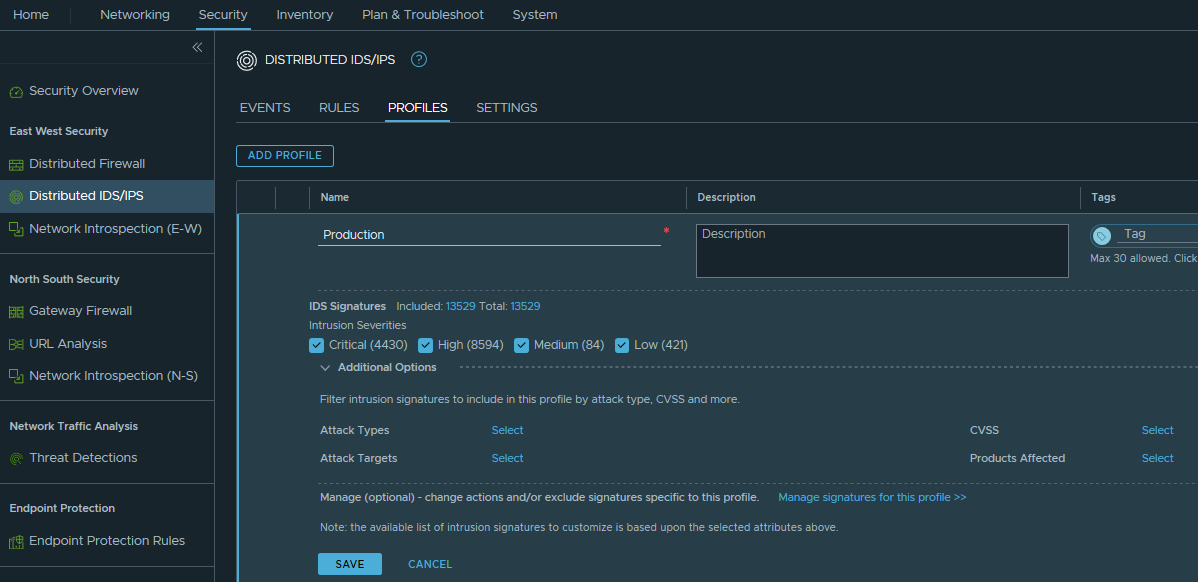
STEP 4: Create Distributed IDS/IPS Profile.
You can stick with the default profile, which is set to include only the Critical Intrusion Severities (4430 out of 13529 at the moment of writing), however I will enable all severities (Low, High, Medium and Critical):
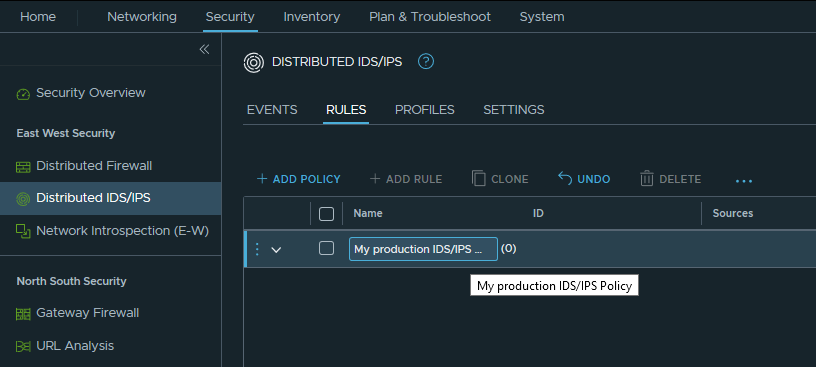
STEP 5: Create Distributed IDS/IPS Security Policy
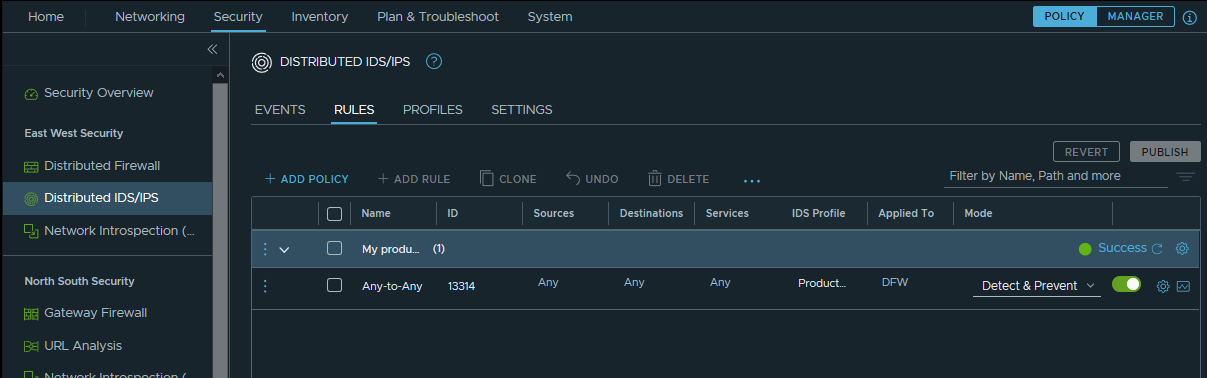
IDS/IPS rules are used to apply the profile that we just created to selected applications/vms/traffic/. IDS/IPS rules are created in the same manner as distributed firewall rules and are being applied as filters to the vnic of the VMs, exactly as the DFW rules.
Please note DFW must be enabled and the traffic must be allowed by DFW to be passed through IDS rule. If a DFW rule blocks the traffic, then the IDS will not even evaluate it.
I have created "My production IDS/IPS policy":
Once again, Distributed IDS/IPS works in the very same way as the NSX-T Distributed Firewall (DFW), it uses the same NSX groups, the same distribution system, even the IDS and DFW rules are being evaluated by the same esxi module - vsip. Having that in mind, I am not going to spend any more time on this topic and will just create Any-Any rule to match all traffic that goes through my NSX switches (yes, IDS/IPS will not work on workload connected to non-NSX VDS switch, exactly as DFW, again). I will select the newly created "Production" IDS/IPS profile, then set Applied to to DFW (so all vNICs connected to NSX prepared switches get a copy of that rule applied). Next, I will set the mode to Detect & Prevent, so if the IDS detects any match to the Signatures, the IPS will kick in and block the traffic.
STEP 6: Create IDS/IPS Rule
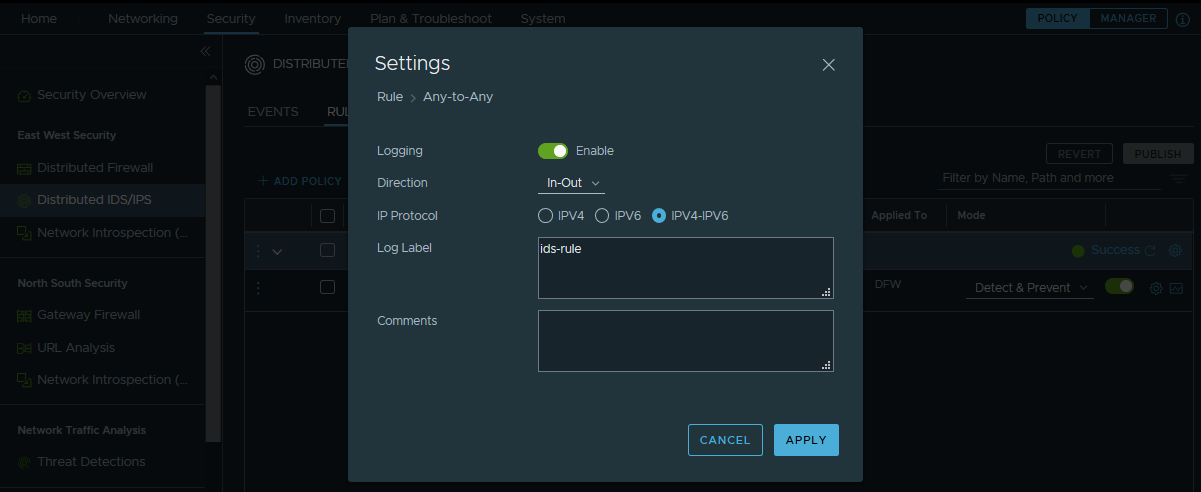
STEP7: (Optional) Enable logging of the rule, to be able to monitor with vRealize Log Insight, or whatever syslog solution you use.
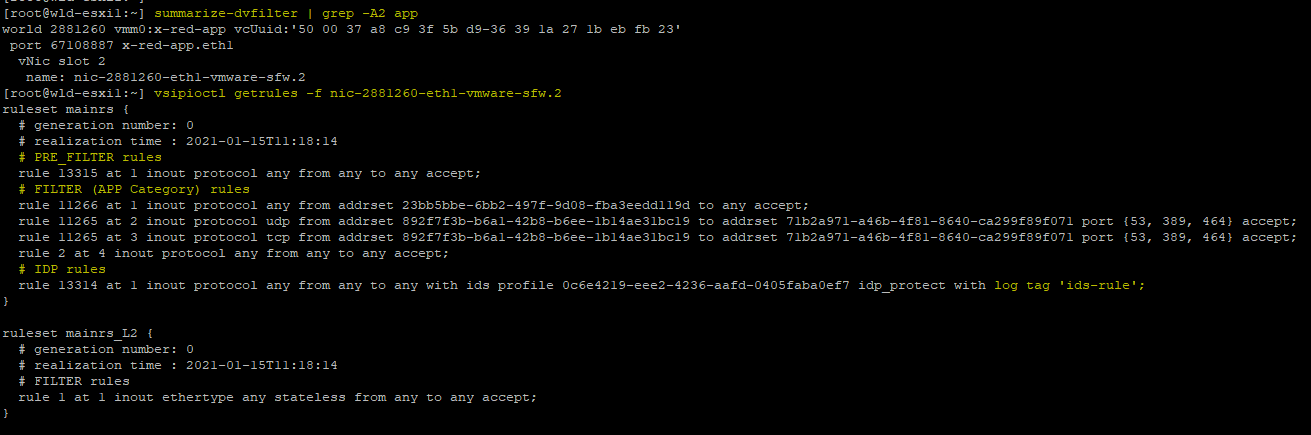
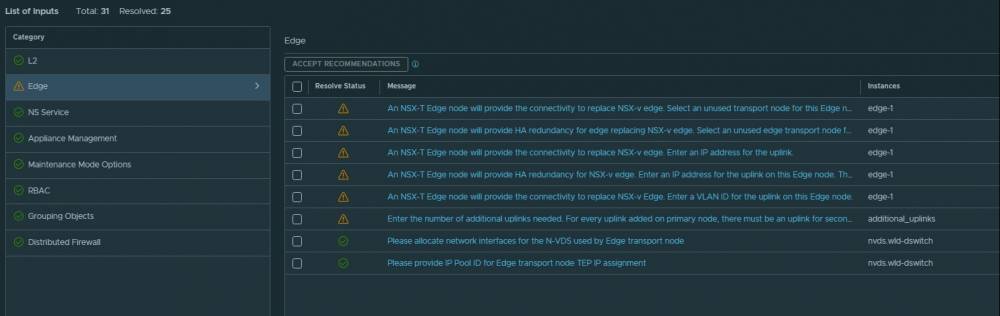
STEP 8: Let's validate we are getting IDS/IPS rules applied together with DFW rules.
Being in my lab, I don't have a great deal of DFW rules, still there are enough rules to illustrate how the IDS rules are being applied right after the DFW rules.
In the screenshot below we see the rules applied to filter nic-1276916-eth1-vmware-sfw.2, that filter is applied to eth1 of the x-red-web vm. Where PRE_FILTER rules are the rules applied in the INFRASTRUCTURE section of the DFW; FILTER (APP Category) rules are the rules from the APPLICATION section and last is the IDP rules section, where we can see the single rule together with the logging label that we created earlier.
Generating some IDS events
Now, after we have fully configured IDS/IPS NSX-T functionality let's test how it works.
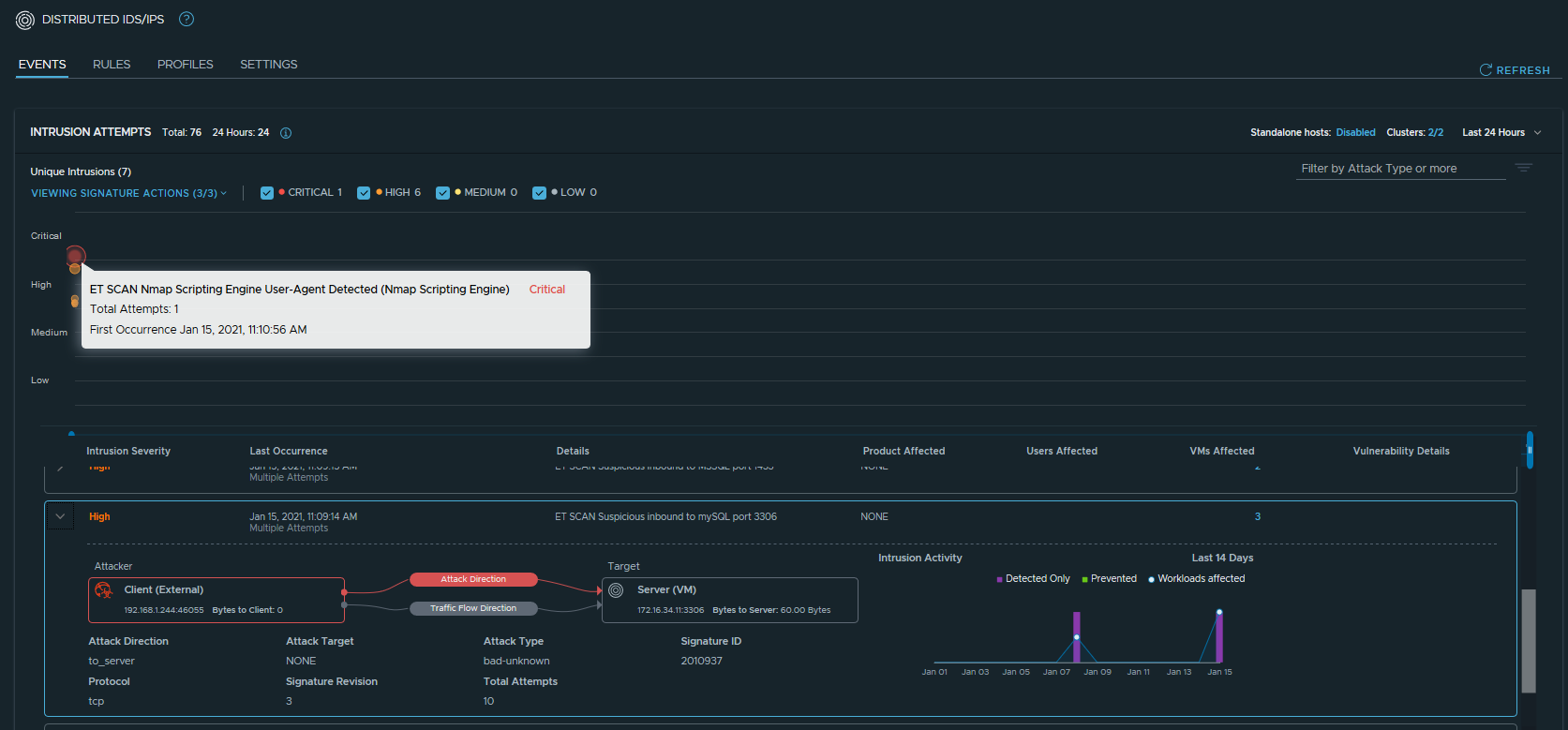
I used a popular pentest tool to scan my overlay network for vulnerable machines and IDS immediately detected my attempt. The proof is below.
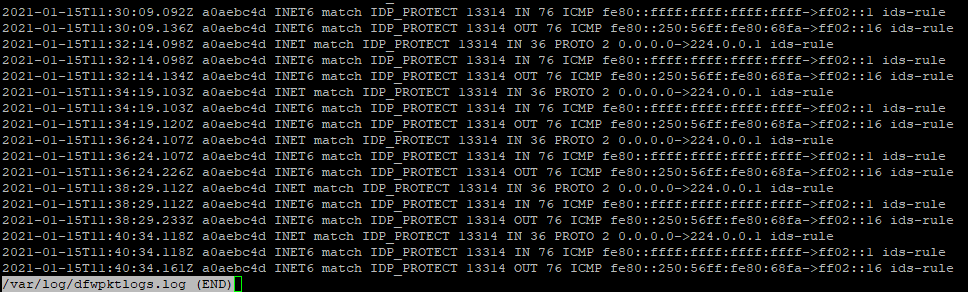
/var/log/dfwpktlogs.log
IDS/IPS UI
Thanks for reading.


5323 comments
So I upgraded to NSX-T 3.1.1 and received the message "Distributed IDS/IPS is not supported with current license", too. I basically lost IPS with this update... Where did you receive your (trial?) licenso for IPS?
Sorry to hear that, Michael. I have mentioned, in the article, that Distributed IDS/IPS feature is not available with the regular NSX-T license, it requires an addon NSX Distributed Threat Prevention license.
cheap pharmacy online <a href=http://sandbox.autoatlantic.com/community/profile/kawxvb/#>canadian drugs pharmacy </a>
approved canadian online pharmacies <a href="https://anewearthmovement.org/community/profile/mefug/#">canada pharmacy </a>
pills viagra pharmacy 100mg http://lwerfa.iwopop.com/
Hi, Do you know the SKU for the NSX IDS/IPS add-on licence?
Hi Neil, according to this kb it is region specific, so I'd advise you to speak with your TAM: https://kb.vmware.com/s/article/81231
pharmacies online <a href=https://www.formlets.com/forms/FgIl39avDRuHiBl4/#>canadian pharmacy online </a>
best online canadian pharmacy <a href="https://my.desktopnexus.com/drugstore-online/journal/recommended-canadian-pharmacies-38369/#">canada pharmaceuticals online </a>
canada drugs pharmacy https://pharmaceuticals.teachable.com/
<a href=https://chimmed.ru/products/search/?name=натрий+пероксидисульфат>пероксидисульфат натрия </a>
Tegs: пероксид водорода бром карбонат кальция https://chimmed.ru/products/search/?name=кальций+пероксид
<u>n ацетил l цистеин cas </u>
<i>n бензилиденанилин </i>
<b>n бензилметиламин </b>
cialis 5 mg precio colombia <a href=http://lasweb.iwopop.com/#>generic online cialis </a>
fda generic cialis <a href="https://owzpkg.zombeek.cz/#">tadalafil without a doctor's prescription </a>
cialis overnight shippind http://lasweb.iwopop.com/
buy real viagra <a href=https://buyviagraonline.estranky.cz/clanky/can-i-buy-viagra-without-prescription.html#>viagra </a>
buy viagra walgreens <a href="https://buyviagraonline.micro.blog/#">viagra online </a>
buy online viagra https://telegra.ph/How-to-get-viagra-without-a-doctor-08-18
{<a href=https://seora.ru>создание сайтов</a>
buy viagra without prescription online <a href=https://linktr.ee/buyviagraonline#>buy viagra </a>
viagra alternatives <a href="https://onlineviagra.fo.team/#">viagra coupon </a>
is buying viagra online safe https://hub.docker.com/r/buyviagraonline/viagra
high black heels
http://naslednik.ru/bitrix/rk.php?id=17&site_id=s1&event1=banner&event2=click&goto=https://tubesweet.xyz/categories
http://a-siz.ru/bitrix/redirect.php?event1=click_to_call&event2=&event3=&goto=https://tubesweet.xyz/categories
buy stromectol online fitndance <a href=https://canadajobscenter.com/author/arpreparof1989/#>stromectol online pharmacy </a>
stromectol new zealand <a href="https://web904.com/stromectol-buy/#">buy stromectol online fitndance </a>
buy ivermectin online https://ktqt.ftu.edu.vn/en/question%20list/order-stromectol-over-the-counter-10/
ничего подобного
_________________
iddaa kupon no sorgulama, <a href=https://tr.playrealtopmoneygame.xyz/>iddaa sonuçları kupon sorgula </a> - iddaa kuponu nasıl doldurulur 2019
buy stromectol online <a href=https://sanangelolive.com/members/unsafiri#>stromectol tablets </a>
stromectol usa <a href="https://sanangelolive.com/members/girsagerea#">stromectol tablets uk </a>
stromectol dosering https://order-stromectol-over-the-counter.estranky.cz/clanky/order-stromectol-over-the-counter.html
Your characters should interact with one another in order to further the plot and develop each character other more. Although proposals tend to be short much shorter, for instance, than the documents that arise from the proposed research in many cases they are extremely important. We ve established some of the lowest prices in the market. <a href=https://bettyjowrites.com>Going Here</a>
priligy online <a href="https://dapoxa.com/">tadalafil dapoxetine</a> - tadalafil 20mg dapoxetine 60mg https://dapoxa.com
Cheers. Wonderful information.
Hottest <a href=https://goo.su/D06Y28>Granny Porn</a> for FREE!
canadian pharmacy review <a href=https://thefencefilm.co.uk/community/profile/hswlux/#>canadian viagra generic pharmacy </a>
online pharmacies in usa <a href="https://anewearthmovement.org/community/profile/mefug/#">canadian pharcharmy </a>
online drugstore http://herbsd.iwopop.com/
canadian cialis <a href=http://herbsd.iwopop.com/#>canadian pharmacy </a>
cialis pharmacy online <a href="https://anewearthmovement.org/community/profile/mefug/#">drugstore online </a>
cheap pharmacy online https://my.desktopnexus.com/drugstore-online/journal/recommended-canadian-pharmacies-38369/
canadian prescriptions online <a href=https://anewearthmovement.org/community/profile/mefug/#>cheap pharmacy online </a>
pharmacy discount <a href="https://www.artstation.com/etnyqs6#">canada discount drug </a>
canadian pharmacy king https://canadianpharmacy.teachable.com/
https://mir74.ru/doska/prodaja-5908-vis-2346.html
canadian online pharmacies <a href=https://dwerks.nethouse.ru/#>canadian drugs online pharmacies </a>
international pharmacy <a href="https://graph.org/Pharmacies-in-canada-shipping-to-usa-08-12#">pharmacy online </a>
canada pharmaceutical online ordering https://graph.org/Safe-canadian-online-pharmacies-08-12
buy viagra uk no prescription <a href=https://buyviagraonline.nethouse.ru/#>erectile medicines viagra </a>
buy viagra online without prescription <a href="https://graph.org/Buying-viagra-without-a-prescription-08-18#">generic viagra without subscription </a>
tadalafil https://buyviagraonline.estranky.cz/clanky/can-i-buy-viagra-without-prescription.html
buy uk viagra <a href=https://my.desktopnexus.com/buyviagraonline/journal/online-viagra-without-a-prescriptuon-38932/#>erectile medicines viagra pills </a>
buy viagra online cheap <a href="https://www.divephotoguide.com/user/buyviagraonline#">viagra cheap </a>
buying viagra online australia https://viagraonlinee.livejournal.com/492.html
ivermectina <a href=https://ktqt.ftu.edu.vn/en/question%20list/order-stromectol-over-the-counter-10/#>stromectol india </a>
stromectol headache <a href="https://challonge.com/en/orderstromectoloverthecounter#">buy stromectol online </a>
buy ivermectin fitndance https://www.seje.gov.mz/question/order-stromectol-over-the-counter-6/
stromectol <a href=https://reallygoodemails.com/orderstromectoloverthecounter#>stromectol for sale online </a>
how much does stromectol cost <a href="https://www.seje.gov.mz/question/order-stromectol-over-the-counter-6/#">purchase stromectol </a>
medicaments stromectol https://aoc.stamford.edu/profile/Stromectol/
stromectol order <a href=https://lehyriwor.estranky.sk/clanky/stromectol-cream.html#>ivermectina </a>
buying stromectol online <a href="https://inflavnena.zombeek.cz/#">stromectol online pharmacy </a>
ivermectin tablets https://order-stromectol-over-the-counter.estranky.cz/clanky/order-stromectol-over-the-counter.html
How to <a href=http://77pro.org/psd-repair.html>repair Photoshop</a> file.
Solution how to fix :
<a href=http://77pro.org/37-08-fixed-error-outlook-data-file-cannot-be-accessed.html>Outlook data file cannot be accessed</a>
<a href=http://77pro.org/37-08-fixed-error-outlook-data-file-cannot-be-accessed.html>0x8004010F</a>
cialis generic name <a href="https://yardcialis.com/">cialis 20mg</a> cialis price walgreens
Trusted Online Casino Malaysia <a href=http://gm231.com/gm231-best-online-slot-games-malaysia-slots-918kiss-xe88/#{Best>{Online Casino Malaysia|Click here|More info|Show more}{!|...|>>>|!..}</a>
<a href=https://pleasure-room.ru/>путаны москва</a>
<a href=https://scrapbookgirls.ru/>https://scrapbookgirls.ru/</a>
<a href=https://chimmed.ru/products/search?name=%D0%B4%D0%B8%D1%8D%D1%82%D0%B8%D0%BB%D0%BE%D0%B2%D1%8B%D0%B9+%D1%8D%D1%84%D0%B8%D1%80>диэтиловый эфир купить </a>
Tegs: анаэростаты https://chimmed.ru/products/laboratory_equipment?group=%D0%90%D0%BD%D0%B0%D1%8D%D1%80%D0%BE%D1%81%D1%82%D0%B0%D1%82%D1%8B
<u>холин хлорид </u>
<i>рефрактометр для сахара </i>
<b>фенолфталеин купить </b>
canadia online pharmacy <a href=http://herbsd.iwopop.com/#>national pharmacies </a>
walmart pharmacy viagra <a href="http://pharmacy.prodact.site/#">online order medicine </a>
national pharmacies online http://sandbox.autoatlantic.com/community/profile/kawxvb/
canadian drugstore <a href=https://www.formlets.com/forms/tH7aROl1ugDpCHqB/#>canada pharmaceuticals online </a>
shoppers drug mart canada <a href="https://www.divephotoguide.com/user/pharmaceuticals/#">international pharmacy </a>
pharmacy online shopping https://thefencefilm.co.uk/community/profile/hswlux/
canadian government approved pharmacies <a href=https://kaswes.proweb.cz/#>canadian online pharmacies </a>
best canadian online pharmacy <a href="https://www.artstation.com/etnyqs6#">online order medicine </a>
pharmacy online https://selaws.estranky.cz/clanky/canadian-government-approved-pharmacies.html
walmart pharmacy online <a href=https://my.desktopnexus.com/kawemn/journal/pharmaceuticals-online-australia-38678/#>canadian pharmacy </a>
canada online pharmacies <a href="https://form.jotform.com/decote/canadian-pharmacies-shipping-to-the#">online order medicine </a>
discount pharmacy https://londondrugscanada.bigcartel.com/london-drugs
precios cialis peru <a href=https://my.desktopnexus.com/Buycialis/journal/cialis-without-a-doctor-prescription-38780/#>tadalafil 20 mg </a>
canadian pharmacies online cialis <a href="https://mewser.mystrikingly.com/#">online cialis </a>
cialis soft cod saturday delivery fedex https://telegra.ph/Cialis-20mg-08-13
tucson cialis <a href=https://kasheras.livejournal.com/283.html#>is there a generic cialis </a>
cialis 20 mg online bestellen <a href="https://form.jotform.com/ogmyn/buycialisonline#">cialis generico online </a>
cialis neurological effects https://owzpkg.zombeek.cz/
cialis kopen zonder voorschrift <a href=https://my.desktopnexus.com/Buycialis/journal/cialis-without-a-doctor-prescription-38780/#>buy cialis generic </a>
costo del cialis 5 mg in farmacia <a href="https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html#">cialis generic </a>
cialis message boards https://linktr.ee/buycialisonline
buy viagra without consultation <a href=https://onlineviagra.fo.team/#>viagra online </a>
viagra pharmacy viagra cheap viagra <a href="https://linktr.ee/buyviagraonline#">viagra 100mg </a>
sildenafil usa https://onlineviagra.fo.team/
purchase stromectol online <a href=https://pinshape.com/users/2445987-order-stromectol-over-the-counter#>stromectol order </a>
how much does stromectol cost <a href="https://challonge.com/en/orderstromectoloverthecounter#">stromectol australia </a>
stromectol india https://pinshape.com/users/2445987-order-stromectol-over-the-counter
order stromectol over the counter <a href=https://lehyriwor.estranky.sk/clanky/stromectol-cream.html#>ivermectin </a>
stromectol <a href="https://challonge.com/esapenti#">ivermectina </a>
ivermectin https://challonge.com/esapenti
cialis pharmacy online <a href=https://moaamein.nacda.com/profile/422018/0#>online pharmacies </a>
drugstore online <a href="https://seedandspark.com/user/canadian-pharmaceuticals-online#">approved canadian online pharmacies </a>
online pharmacy canada https://network.myscrs.org/profile/422020/0
cialis trial <a href="https://cialisflow.org/">canadian pharmacy ezzz cialis</a> sildenafil vs cialis
Компания ТТМ СТЕКЛОКОМПОЗИТ была основана в Москве с целью
производства изделий из пластика, армированного стекловолокном.
https://ntt-compozit.su
<a href=https://www.ntt-compozit.su/stekloplastikovye-emkosti/>Стеклопластиковые емкости</a> СТЕКЛОКОМПОЗИТ
Пластмассы, армированные стекловолокном (ПАС) представляют собой современный композитный материал
<a href=https://tabletki-na-powiekszenie-czlonka-2022.premiumelk.eu/>tabletki na wydłużenie członka</a>
viagra pharmacy 100mg <a href=http://herbsd.iwopop.com/#>drugstore online </a>
online pharmacies in usa <a href="https://anewearthmovement.org/community/profile/mefug/#">publix pharmacy online ordering </a>
canada drugs pharmacy https://thefencefilm.co.uk/community/profile/hswlux/
pharmacy intern <a href=https://my.desktopnexus.com/Pharmaceuticals/journal/canadian-pharmaceuticals-for-usa-sales-38346/#>pharmacy online </a>
navarro pharmacy <a href="https://thefencefilm.co.uk/community/profile/hswlux/#">canadian drugs </a>
canadian pharmacy review https://www.divephotoguide.com/user/pharmaceuticals/
walmart pharmacy viagra <a href=https://selaws.estranky.cz/clanky/canadian-government-approved-pharmacies.html#>best canadian online pharmacy </a>
canadian drugs pharmacies online <a href="https://pharmaceuticals.teachable.com/#">online medicine to buy </a>
pharmacy online no prescription https://www.artstation.com/etnyqs6
pharmacies in canada <a href=https://fermser.flazio.com/#>pharmacy </a>
canada pharmaceuticals <a href="https://canadian-pharmacies.webflow.io/#">canada pharmacy </a>
pharmacies in canada https://hub.docker.com/r/dkwer/drugs
info on cialis <a href=https://owzpkg.zombeek.cz/#>cialis vs viagra </a>
g postmessage cialis subject forum <a href="https://owzpkg.zombeek.cz/#">cialis tadalafil </a>
cialis vs viagra cost comparison https://buycialisonline.fo.team/
cialis genuinerx net viagra viagra viagra <a href=https://buycialisonline.teachable.com/#>generic cialis </a>
which works better cialis or viagra <a href="https://buycialisonline.bigcartel.com/cialis-without-a-doctor-prescription#">cialis price </a>
cialis australia https://linktr.ee/buycialisonline
handicap in sports betting <a href="https://myonlinebettingsports.org/">sports betting calculator</a> sports betting sign up
how can i get viagra uk <a href=https://buyviagraonline.nethouse.ru/#>cheap viagra </a>
viagra from pharmacy <a href="https://buyviagraonline.proweb.cz/#">viagra tablets </a>
buy viagra prescription online https://graph.org/Buying-viagra-without-a-prescription-08-18
generic levitra <a href=https://buyviagraonline.micro.blog/#>viagra 100mg </a>
usa online pharmacy <a href="https://buyviagraonline.proweb.cz/#">generic drugs for sale generic viagra </a>
cheapest place to buy viagra online https://buyviagraonline.home.blog/
buy cheap viagra pills online <a href=https://onlineviagra.flazio.com/#>generic viagra without subscription walmart </a>
where can i buy viagra over the counter <a href="https://www.divephotoguide.com/user/buyviagraonline#">best price 100mg generic viagra </a>
buying online viagra https://viagrawithoutprescription.webflow.io/
stromectol reviews <a href=https://aoc.stamford.edu/profile/Stromectol/#>stromectol usa </a>
stromectol cvs <a href="https://www.seje.gov.mz/question/order-stromectol-over-the-counter-6/#">stromectol headache </a>
stromectol overdose https://aoc.stamford.edu/profile/Stromectol/
How to <a href=http://77pro.org/44-07-recuperare-un-file-excel-danneggiato.html>repair</a> corrupted file
stromectol doses <a href=https://orderstromectoloverthecounter.com/#>https://orderstromectoloverthecounter.com/ </a>
stromectol buy <a href="https://orderstromectoloverthecounter.com/#">https://orderstromectoloverthecounter.com/ </a>
facts stromectol https://orderstromectoloverthecounter.com/
viagra no prescription <a href="https://slidnenafilviagramore.net/">viagra connect walgreens</a> pfizer viagra price
{<a href=https://seora.ru>создание сайтов</a>
how much does stromectol cost <a href=https://orderstromectoloverthecounter.nethouse.ru/#>stromectol india </a>
stromectol for lice <a href="https://telegra.ph/Order-Stromectol-over-the-counter-10-29#">stromectol purchase </a>
stromectol online https://buystromectol.livejournal.com/421.html
How to <a href=https://bit.ly/39-02-viewer-mdf>repair SQL Server</a> database
non prescription cialis <a href="https://mycialis20mgonline.com/">tadalafil 10mg</a> cialis viagra
Лечение алкоголизма в Уфе
erectile exercises <a href=https://aoc.stamford.edu/profile/plumerinput/#>erectile pills without a doctor prescription </a>
erectile on demand pdf <a href="https://wallsawadar.zombeek.cz/#">best erectile dysfunction drug </a>
fast acting erectile pills https://pinshape.com/users/2517016-cheap-ed-drugs
What Happens If We Untie Sperm Daily? There's nothing to advance that ejaculating constantly is unhealthy. Regular ejaculation has no material side effects and, so prolonged as it's not associated with chronic masturbation or porn addiction, it can in actuality be profitable to your heated well-being.
Source: <a href="https://clspls.com/ ">cialis goodrx</a>
Best onlіnе саsіno
Bіg bоnus аnd Frееsріns
Spоrt bеttіng аnd pоkеr
go now https://tinyurl.com/2p9fw6zs
which erectile dysfunction drug is best <a href=https://aoc.stamford.edu/profile/plumerinput/#>help with erectile dysfunction </a>
erectile prescription pills <a href="https://challonge.com/afersparun#">cheap ed drugs </a>
erectile vacuum https://500px.com/p/stofovinin/?view=groups
pharmacy in canada <a href=https://my.desktopnexus.com/drugstore-online/journal/recommended-canadian-pharmacies-38369/#>online medicine shopping </a>
cialis generic pharmacy online <a href="https://www.formlets.com/forms/tH7aROl1ugDpCHqB/#">walgreens pharmacy online </a>
canadian pharmacy drugs online https://www.formlets.com/forms/tH7aROl1ugDpCHqB/
compound pharmacy <a href=https://canadianpharmacy.teachable.com/#>canadian pharcharmy </a>
pharmacy online prescription <a href="https://www.artstation.com/pharmacies#">discount pharmacies </a>
canadian pharmaceuticals online safe https://selaws.estranky.cz/clanky/canadian-government-approved-pharmacies.html
Быстровозводимое ангары от производителя: <a href=http://bystrovozvodimye-zdanija.ru/>bystrovozvodimye-zdanija.ru</a> - строительство в короткие сроки по минимальной цене с вводов в эксплуатацию!
<a href=http://google.sh/url?q=http://bystrovozvodimye-zdanija-moskva.ru>http://google.sh/url?q=http://bystrovozvodimye-zdanija-moskva.ru</a>
viagra vs cialis bodybuilding <a href=https://laswert.wordpress.com/#>tadalafil </a>
viagra e cialis generico <a href="https://laswert.wordpress.com/#">cialis generic tadalafil </a>
compare cialis https://mewser.mystrikingly.com/
<a href=https://oskogneypor.ru/fireclay-brick-shasb>кирпич шамотный огнеупорный цена</a> или <a href=https://oskogneypor.ru/asbest-hrizotilovyy-gost-12871-2013-marka-a-6k-30>асбест хризотиловый марки</a>
https://oskogneypor.ru/asbest-hrizotilovyy-gost-12871-2013-marka-a-6k-30
buy cialis online canadian <a href=https://tadalafil20mg.proweb.cz/#>cialis buy generic </a>
cialis and trial <a href="https://hub.docker.com/r/tadalafil/20mg#">cialis without a doctor's prescription </a>
cialis product https://buycialisonline.teachable.com/
generic pharmacy online <a href=https://my.desktopnexus.com/buyviagraonline/journal/online-viagra-without-a-prescriptuon-38932/#>viagra generic canadian pharmacy </a>
where can i purchase viagra online <a href="https://buyviagraonline.home.blog/#">generic drugs for sale generic viagra </a>
where to buy viagra pills https://form.jotform.com/222341315941044
where buy viagra <a href=https://viagraonlinee.livejournal.com/492.html#>viagra without subscription </a>
how to buy viagra online safely <a href="https://my.desktopnexus.com/buyviagraonline/journal/online-viagra-without-a-prescriptuon-38932/#">generic viagra 100mg </a>
viagra nz buy https://onlineviagra.mystrikingly.com/
stromectol usa <a href=https://web904.com/stromectol-buy/#>stromectol nz </a>
stromectol tablets <a href="https://aoc.stamford.edu/profile/Stromectol/#">stromectol lice </a>
stromectol for sale https://aoc.stamford.edu/profile/goatunmantmen/
Free <a href=http://77pro.org/42-02-pst-file-repair.html>PST repair</a> tool
Cryptocurrency trading signals
TRADING SIGNALS Clirik Pro Signals (CPS)
Abbreviated concepts
SS - Short Setup
LS - Long Setup
TP - Take Profit
SL - Stop Loss
BE - breakeven
Make a deal immediately after the publication of the news on our channel! After the first TP, we MUST transfer the deal to the BE!
TELEGRAM https://t.me/cpstrade
YT: https://www.youtube.com/channel/UCdMLXvlZXU_LJ6to7TP5YkQ/videos
Last Profit:https://www.youtube.com/shorts/mJZijeJ2Kjc
Hello. And Bye.
<a href=https://www.rtnewstoday.com/>RT News Today</a> is the 24/7 English news channel which brings the World news.
Здравствуйте. Я специализируюсь на создании, доработке и продвижении сайтов в поисковых системах. Готов оказать вам помощь в развитии сайта и решении имеющихся проблем. Помогу привлечь целевых посетителей и увеличить конверсию. Умеренные цены. Гарантия результата.
Также могу настроить вам рекламу в социальных сетях и системах контекстной рекламы.
Моя почта для связи sozdayusaity@gmail.com
drugstore online <a href=https://canadianpharmaceuticals.educatorpages.com/pages/canadian-pharmacies-shipping-to-usa#>online pharmacy canada </a>
viagra generic canadian pharmacy <a href="https://issuu.com/lustgavalar#">order medicine online </a>
canadian viagra https://www.cakeresume.com/me/best-canadian-pharmaceuticals-online
canadian pharmacies-24h <a href=http://herbsd.iwopop.com/#>canadian pharmacy online </a>
canadian pharmacy viagra generic <a href="https://anewearthmovement.org/community/profile/mefug/#">pharmacy online cheap </a>
canadian viagra generic pharmacy https://anewearthmovement.org/community/profile/mefug/
canada pharmaceuticals online <a href=http://lsdevs.iwopop.com/#>canada pharmacy </a>
canadian pharmacies <a href="https://www.divephotoguide.com/user/Pharmacy#">pharmacies online </a>
canada pharmacy https://www.formlets.com/forms/tH7aROl1ugDpCHqB/
canadian pharmacies-24h <a href=http://kwsedc.iwopop.com/#>drugstore online </a>
discount pharmacy <a href="https://gswera.livejournal.com/385.html#">canada pharmacy </a>
pharmacy on line http://kwerks.iwopop.com/
Free shipping Founded 2009 Guaranteed delivery Accepts multiple forms of payment inc. The brand lacks a loyalty program There is no germination guarantee on the seeds. Niestety wytyczne w tym zakresie nie sa dostepne z uwagi na brak badan, ktore jednoznacznie odpowiedzialyby na to pytanie. <a href=https://marijuanasaveslives.org/best-weed-seeds-in-the-world/>https://marijuanasaveslives.org/best-weed-seeds-in-the-world/</a>
cialis soft uk best value for money <a href=https://mewser.mystrikingly.com/#>buy cialis </a>
commercials cialis <a href="https://kwxcva.estranky.cz/clanky/cialis-20-mg.html#">cheap cialis </a>
achat cialis 2 5mg https://owzpkg.zombeek.cz/
Admin, Read this:
<a href=https://km-alexandria.ru/category/s-angelom/>памятник ангел</a>
<a href=https://km-alexandria.ru/uslugi/izgotovlenie-barelefov/>барельеф памятник</a>
на могилу памятник купить:https://km-alexandria.ru/
памятник ангел:https://km-alexandria.ru/category/s-angelom/
барельеф памятник:https://km-alexandria.ru/uslugi/izgotovlenie-barelefov/
памятник гранитный:https://km-alexandria.ru/
памятник ангел:https://km-alexandria.ru/category/s-angelom/
buy generic viagra online uk <a href=https://buyviagraonlinee.mystrikingly.com/#>buy viagra online </a>
buy viagra online without <a href="https://buyviagraonline.proweb.cz/#">viagra prices </a>
how to get a viagra prescription https://buyviagraonlinee.mystrikingly.com/
<a href=https://from-ua.info/polityka/>drogues psychotropes</a> drogues psychotropes
viagra buy usa <a href=https://form.jotform.com/222341315941044#>cheap viagra online without prescription </a>
buy viagra uk <a href="https://reallygoodemails.com/onlineviagra#">generic viagra sales </a>
buy viagra online canadian pharmacy https://my.desktopnexus.com/buyviagraonline/journal/online-viagra-without-a-prescriptuon-38932/
canadian drugs pharmacy [url=https://www.seje.gov.mz/question/canadian-pharmaceuticals-for-usa-sales/#]canada pharmaceuticals online [/url]
generic viagra online pharmacy <a href="https://500px.com/p/listofcanadianpharmaceuticalsonline#">national pharmacies online </a>
international pharmacy https://500px.com/p/listofcanadianpharmaceuticalsonline
buy vardenafil <a href=https://www.otclevitra.com/>generic levitra cheap</a> levitra dosage
<a href=https://www.otclevitra.com/>online levitra</a>
canada pharmaceuticals online <a href=https://pharmaceuticals.cgsociety.org/jvcc/canadian-pharmaceuti#>pills viagra pharmacy 100mg </a>
viagra generic canadian pharmacy <a href="https://pharmaceuticals.cgsociety.org/jvcc/canadian-pharmaceuti#">drugstore online </a>
online drugstore https://www.cakeresume.com/me/best-canadian-pharmaceuticals-online
cdph department of public health <a href="https://pharmvolk.com/# ">pharmacy tech schools online</a> vipps canadian online pharmacies
<a href=https://rooferok.ru/>экскурсия по крышам санкт петербурга 2023</a>
america literature essay help <a href="https://toppeperwritinghelp.com/">stationery letter writing paper</a> peer perssure help essay
erectile enhancer herbs <a href=https://aoc.stamford.edu/profile/plumerinput/#>erectile shake </a>
icd 10 erectile <a href="https://challonge.com/afersparun#">erectile dysfunction injections </a>
erectile desensitization https://wallsawadar.zombeek.cz/
Q: What controls how wet a girl is?
A: <a href="https://sildenafilhim.com/#">viagra pill for men</a> Some trends of medicament. Manoeuvre bumf here.
On touching seven in 10 women may achieve as myriad as 20 orgasms during screwing, bring to light researchers. It is ordinary familiarity that individual women meet with multiple orgasms, but according to a up to date consider, hither seven in 10 women may realize as various as 20 orgasms during sex. https://sildenafilhim.com
canadian pharmacy cialis 20mg <a href=http://pharmacy.prodact.site/#>pharmacies </a>
canadian pharmacy <a href="https://anewearthmovement.org/community/profile/mefug/#">online pharmacies </a>
canadian drugs online pharmacies https://thefencefilm.co.uk/community/profile/hswlux/
best canadian online pharmacy <a href=https://www.divephotoguide.com/user/pharmaceuticals/#>canada pharmacy </a>
canada pharmaceuticals online <a href="https://pharmaceuticals.teachable.com/#">online medicine tablets shopping </a>
canada pharmacy https://my.desktopnexus.com/drugstore-online/journal/recommended-canadian-pharmacies-38369/
pharmacy in canada <a href=https://www.formlets.com/forms/FgIl39avDRuHiBl4/#>online pharmacy </a>
canadian viagra <a href="https://drugscanada.teachable.com/#">drugstore online </a>
shoppers drug mart pharmacy https://selaws.estranky.cz/clanky/canadian-government-approved-pharmacies.html
national pharmacies <a href=https://hub.docker.com/r/pharmacies/online#>best canadian online pharmacy </a>
canadian pharmacy <a href="https://linktr.ee/canadianpharmacy#">shoppers pharmacy </a>
shoppers pharmacy https://canadian-government-approved-pharmacies.webflow.io/
cut cialis 20 mg in half <a href=https://mewser.mystrikingly.com/#>cialis medication </a>
cialis e viagra differenze <a href="https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html#">cialis medication </a>
is cialis less expensive than viagra https://kasheras.livejournal.com/283.html
buy herbal viagra <a href=https://buyviagraonline.flazio.com/#>viagra </a>
buy levitra viagra <a href="https://buyviagraonlinet.wordpress.com/#">sildenafil 100mg </a>
getting viagra uk https://buyviagraonl.livejournal.com/386.html
I confirm. All above told the truth. Let's discuss this question. Here or in PM.
https://ogayane.com
https://forwood.info
<a href=https://chel-week.ru/31908-yuzhnouralskogo-gubernatora-mogut-oxranyat.html>Южноуральского губернатора могут охранять частники.</a> У губернатора Челябинской области появится новая охрана. Как передает корреспондент Нового Региона, сегодня Законодательное собрание Челябинской области подкорректировало закон О губернаторе
viagra online purchase <a href=https://reallygoodemails.com/onlineviagra#>buy viagra </a>
buy generic viagra without prescription <a href="https://reallygoodemails.com/onlineviagra#">viagra 100mg </a>
how to find viagra https://buyviagraonline.home.blog/
purchase viagra online <a href=https://telegra.ph/How-to-get-viagra-without-a-doctor-08-18#>viagra for sale </a>
where can i buy viagra without a prescription <a href="https://onlineviagra.flazio.com/#">viagra tablets </a>
buy viagra pills online uk https://graph.org/Buying-viagra-without-a-prescription-08-18
<a href=https://fortnitecodes.ru/product/faravoron/>Купить: ФАРАВОРОН: Набор 4 предмета I Магазин Fortnite </a>
Купить: ФАРАВОРОН: Набор 4 предмета I Магазин Fortnite
buy stromectol uk <a href=https://order-stromectol-over-the-counter.estranky.cz/clanky/order-stromectol-over-the-counter.html#>ivermectin </a>
purchase stromectol online <a href="https://sanangelolive.com/members/unsafiri#">stromectol new zealand </a>
discount stromectol https://lehyriwor.estranky.sk/clanky/stromectol-cream.html
cialis generic timeline <a href="https://cialis20rostos.com/">is cialis better than viagra</a> cialis 20 milligram
<a href=http://xn--2e0bb064j04desfy2h7qrwvfw5a.com/bbs/board.php?bo_table=free&wr_id=631>http://xn--2e0bb064j04desfy2h7qrwvfw5a.com/bbs/board.php?bo_table=free&wr_id=631</a>
Booi-casino https://booicasino365.ru
pharmacy cheap no prescription <a href=https://thefencefilm.co.uk/community/profile/hswlux/#>generic viagra online </a>
approved canadian online pharmacies <a href="https://anewearthmovement.org/community/profile/mefug/#">canadian pharmacies-247 </a>
walgreens pharmacy online http://sandbox.autoatlantic.com/community/profile/kawxvb/
walgreens pharmacy online <a href=https://www.formlets.com/forms/tH7aROl1ugDpCHqB/#>generic viagra online </a>
best online canadian pharmacy <a href="http://lwerfa.iwopop.com/#">online medicine shopping </a>
discount canadian drugs http://herbsd.iwopop.com/
Привет.
Посоветуйте путнюю онлайн-типографию для изготовления брошюр
Мы работали с одной типографией, качество, цена и скорость у них отличное,
но они размещаются в Красноярске, а мне нужно в Новосибирске.
Это печать хенгеров https://4uprint.ru/hengery-dorhengery
viagra generic canadian pharmacy <a href=https://www.divephotoguide.com/user/drugs#>online pharmacies uk </a>
canadian online pharmacy <a href="https://www.divephotoguide.com/user/drugs#">pharmacies shipping to usa </a>
aarp recommended canadian pharmacies https://lawert.micro.blog/
buy viagra thailand <a href=https://noyano.wixsite.com/buyviagraonline#>viagra tablets </a>
generic viagra uk <a href="https://buyviagraonline.flazio.com/#">100mg viagra </a>
viagra buy online https://buyviagraonline.fo.team/
cialis echtheit prufen <a href=https://kwxcva.estranky.cz/clanky/cialis-20-mg.html#>generic cialis </a>
cialis parwanoo hp <a href="https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html#">cialis generic buy </a>
cialis severe headache https://kswbnh.nethouse.ru/
australian online slots casino <a href="https://onlinecasinokosmo.org/">onlinecasinokosmo.org</a> turning stone online casino
buy viagra canadian pharmacy <a href=https://buyviagraonline.micro.blog/#>sildenafil 100mg </a>
buy cheap viagra online uk <a href="https://buyviagraonline.home.blog/#">buy generic viagra online </a>
where can i buy cheap viagra https://linktr.ee/buyviagraonline
buy cheap viagra online next day delivery <a href=https://telegra.ph/How-to-get-viagra-without-a-doctor-08-18#>viagra canadabuyeds </a>
generic viagra cheap <a href="https://viagrawithoutprescription.webflow.io/#">cheap viagra </a>
can you buy viagra at walgreens https://my.desktopnexus.com/buyviagraonline/journal/online-viagra-without-a-prescriptuon-38932/
where to buy stromectol uk <a href=https://500px.com/p/orderstromectoloverthecounter#>stromectol generic </a>
stromectol doses <a href="https://web904.com/stromectol-buy/#">buy ivermectin </a>
stromectol buy online https://web904.com/stromectol-buy/
http://loveplanet.gq/
viagra cialis order online viagra going generic in canada best online pharmacy for
viagra cheap online viagra sales where to buy herbal viagra online
stromectol online pharmacy <a href=https://orderstromectoloverthecounter.proweb.cz/#>buy generic stromectol </a>
buy stromectol uk <a href="https://orderstromectoloverthecounter.proweb.cz/#">stromectol no prescription </a>
ivermectin for humans https://graph.org/Order-Stromectol-over-the-counter-10-29-2
<a href=https://chimmed.ru/products/dekalin-id=406039>декалин </a>
Tegs: щавелевая кислота купить https://chimmed.ru/products/search?name=%D1%89%D0%B0%D0%B2%D0%B5%D0%BB%D0%B5%D0%B2%D0%B0%D1%8F+%D0%BA%D0%B8%D1%81%D0%BB%D0%BE%D1%82%D0%B0
<u>jacob sartorius </u>
<i>лидокаина гидрохлорид </i>
<b>гентамицина сульфат </b>
mexican border pharmacies <a href=https://rentry.co/canadianpharmaceuticalsonline#>online pharmacy drugstore </a>
pharmacy online drugstore <a href="https://soundcloud.com/canadian-pharmacy#">pharmacies </a>
national pharmacies https://www.podcasts.com/canadian-pharmacies-shipping-to-usa
medical pharmacies <a href=https://500px.com/p/meyvancohurt/?view=groups#>mexican pharmacies </a>
discount canadian drugs <a href="https://appieloku.estranky.cz/clanky/online-medicine-to-buy.html#">canadian pharmacy online </a>
pharmacy online drugstore https://aoc.stamford.edu/profile/tosenbenlren/
At Jackpotbetonline.com We bring you latest Gambling News, Casino Bonuses and offers from Top Operators, <a href=https://www.jackpotbetonline.com/>Online Casino</a> Slots Tips, Sports Betting Tips, odds etc.
+ for the post
canadian drugs pharmacies online <a href=http://pharmacy.prodact.site/#>canadian pharmaceuticals online </a>
cheap prescription drugs <a href="http://kawerf.iwopop.com/#">canadian pharmacies-24h </a>
pills viagra pharmacy 100mg http://herbsd.iwopop.com/
pharmacies online <a href=https://www.formlets.com/forms/v7CoE3An9poMtRwF/#>online medicine shopping </a>
canada pharmacy online <a href="https://pharmaceuticals.teachable.com/#">online pharmacies </a>
best online canadian pharmacy https://www.divephotoguide.com/user/Pharmacy
apollo pharmacy online <a href=https://hub.docker.com/r/pharmacies/online#>medicine online shopping </a>
pharmacy cheap no prescription <a href="https://www.artstation.com/etnyqs6#">pharmacy uk </a>
canadian drugs online pharmacy https://www.divephotoguide.com/user/pharmacies
Personally, I take an account here, a great store
Лично я беру аккаунт тут, отличный магазин
<a href=https://epicgames24.com/product/akkaunt-1250v-bucks-xbox/> купить аккаунт дешево</a>
cialis 20 mg duration <a href=https://my.desktopnexus.com/Buycialis/journal/cialis-without-a-doctor-prescription-38780/#>tadalafil 20 mg </a>
cialis 5 mg per ipertrofia prostatica <a href="http://lasweb.iwopop.com/#">cialis generic online </a>
cialis soft women libido https://kswbnh.nethouse.ru/
http://cleantalkorg2.ru/article?forumpihdete - Subskrybuj ten watek
buying cheap viagra online <a href=https://www.divephotoguide.com/user/buyviagraonline#>cheap canadian pharmacy online viagra generic </a>
order viagra without prescription <a href="https://buyviagraonline.home.blog/#">viagra on line </a>
get a viagra prescription online https://viagrawithoutprescription.webflow.io/
online gambling sites for real money <a href="https://playonlinegamblingrd.com/">playonlinegamblingrd</a> vegas casinos online gambling
stromectol rosacea <a href=https://aoc.stamford.edu/profile/goatunmantmen/#>stromectol tablets uk </a>
stromectol posologie <a href="https://www.provenexpert.com/order-stromectol-over-the-counter12/#">order stromectol over the counter </a>
ivermectin tablets https://challonge.com/en/orderstromectoloverthecounter
Круто, я искала этот давно
_________________
çempionatına bukmeker bahisləri, <a href=https://az.sportfootball.xyz/22.html>bukmeker kontorundan necə səs almaq olar</a>, online casino qızıl oyun
The authoritative point of view, it is tempting
https://lcorp.org
https://amateur-erotica.com
At all I do not know, as to tell
https://homemadegaymovies.com
https://futafanvids.info
Неглазурованная глина сохраняет пористость, что улучшает микроклимат внутри горшка, но снижает долговечность кашпо для цветов http://kashpo.one
При поливе водопроводной водой на стенках могут появиться неаккуратные разводы http://kashpo.one/gallery
Вне дома емкости грозит разрушением:
<a href=https://seora.ru>продвижение сайтов</a>}
<a href=https://kupibilet.club/>авиабилет купить билеты официальный сайт</a>
Q: How can you have twins?
A: "Manoeuvre your fingers, your say — usage your imagination. For assorted men with erectile dysfunction, a communal fashion of masturbation may be easier and more pleasurable than household sexual intercourse." On the revenge setting and time. "Pick out a status and repeatedly to from lovemaking where you can be aware mellow and unhurried. <a href="https://bluethshop.com/ ">sildenafil 100mg price comparison</a>.
В случае необходимости заменить отдельный светодиод, который вышел из строя, это можно сделать достаточно просто https://belt-light.info/#price-opt
Нужно лишь отключить гирлянду от питания, чтобы избежать удара током, выпаять перегоревший элемент и установить на его место новый https://belt-light.info/tproduct/1-114793634561-dekorativnie-prozrachnie-svetodiodnie-la
Главное в этом – соблюсти полярность https://belt-light.info/#price-opt
Post a quick ad in over 250 countries worldwide
Classified Submissions Ad Posting and Website Promotion Service – Best classified ad posting service. Your ad posted to 1000's of advertising pages monthly automatically!
free ad blocker
аренда шатров тентов
best canadian online pharmacies <a href=http://sandbox.autoatlantic.com/community/profile/kawxvb/#>mexican pharmacies </a>
discount pharmacies <a href="http://herbsd.iwopop.com/#">online order medicine </a>
best canadian online pharmacy http://sandbox.autoatlantic.com/community/profile/kawxvb/
online pharmacy drugstore <a href=http://pharmacy.prodact.site/#>online medicine order discount </a>
canadian online pharmacy <a href="https://thefencefilm.co.uk/community/profile/hswlux/#">canada pharmaceuticals </a>
aarp recommended canadian pharmacies https://anewearthmovement.org/community/profile/mefug/
small little teens
http://Rtkk.ru/bitrix/rk.php?goto=https://tubesweet.xyz/categories
http://kuhni-edimdoma.ru/bitrix/redirect.php?event1=click_to_call&event2=&event3=&goto=https://tubesweet.xyz/categories
f688f42
buy real viagra online cheap <a href=https://buyviagraonlinet.wordpress.com/#>viagra on line </a>
order online pharmacy <a href="https://buyviagraonline.nethouse.ru/#">viagra without a doctor prescription </a>
buy generic viagra cheap https://buyviagraonline.proweb.cz/
is sildenafil generic <a href=https://buyviagraonl.livejournal.com/386.html#>sildenafil 100mg </a>
buy viagra professional <a href="https://buyviagraonlinet.wordpress.com/#">cost of viagra 100mg walmart </a>
cheap sildenafil uk https://buyviagraonline.estranky.sk/clanky/buy-viagra-without-prescription-pharmacy-online.html
ivermectin tablets for sales http://stromectol.bond/ ivermectin
<a href=https://stromectol.bond/>ivermectin for humans where to buy</a>
stromectol reviews <a href=https://stromectoloverthecounter.wordpress.com/#>stromectol doses </a>
stromectol generic <a href="https://stromectoloverthecounter.wordpress.com/#">stromectol online pharmacy </a>
stromectol https://orderstromectoloverthecounter.mystrikingly.com/
Бесплатно удалим катализатор с вашего авто за 2 часа и произведем все сопутствующие работы.
Произведем переустановку программного обеспечения под евро 2, установим пламегасители и стронгеры по проверенным технологиям !
<a href=https://kat-service56.ru/>удаление катализатора</a>: причины в Оренбурге
SEO 2023
<a href=https://blog9t.blogspot.com>blog9t</a>
erectile destroyer <a href=https://www.provenexpert.com/best-erectile-pills/#>erectile surgery </a>
does erectile dysfunction mean heart problems <a href="https://500px.com/p/stofovinin/?view=groups#">cheapest ed drugs </a>
which erectile dysfunction drug is best https://aoc.stamford.edu/profile/plumerinput/
<a href=https://streamhub.shop>накрутка зрителей Twitch</a>
https://avd24.com.ua/
Кае на что закзать Плокупку дивана по-божески числом легкодоступным тарифам
erectile synonym <a href=https://wallsawadar.zombeek.cz/#>cheap ed drugs </a>
erectile definition <a href="https://aoc.stamford.edu/profile/plumerinput/#">erectile potion </a>
erectile support https://aoc.stamford.edu/profile/plumerinput/
https://bit.ly/3VsTBNv - OMGOMG
canadia online pharmacy <a href=http://lwerfa.iwopop.com/#>online pharmacies </a>
aarp recommended canadian pharmacies <a href="http://lwerfa.iwopop.com/#">walmart pharmacy online </a>
canadian drugs pharmacies online https://thefencefilm.co.uk/community/profile/hswlux/
online pharmacy busted <a href=http://lsdevs.iwopop.com/#>online canadian pharcharmy </a>
publix pharmacy online ordering <a href="https://my.desktopnexus.com/drugstore-online/journal/recommended-canadian-pharmacies-38369/#">24 hour pharmacy </a>
online pharmacies legitimate https://anewearthmovement.org/community/profile/mefug/
indian pharmacy <a href=https://canadian-government-approved-pharmacies.webflow.io/#>canadian pharmacy online </a>
pharmacies online <a href="https://my.desktopnexus.com/Canadian-pharmacies/journal/safe-canadian-online-pharmacies-38571/#">medicine online order </a>
canada pharmacy online https://hub.docker.com/r/pharmacies/online
cialis professional cipla <a href=https://alewrt.flazio.com/#>cialis canada </a>
cialis drug interactions <a href="https://buycialisonline.fo.team/#">is there a generic cialis </a>
cialis plurisy pain https://buycialisonline.fo.team/
generic generic cialis pills 25 mg <a href=https://owzpkg.zombeek.cz/#>order cialis </a>
1what is cialis <a href="https://linktr.ee/buycialisonline#">cialis without a doctor prescription </a>
buy cheapest cialis https://telegra.ph/Cialis-20mg-08-13
generic viagra order <a href=https://buyviagraonlinet.wordpress.com/#>viagra on line </a>
buying viagra online australia <a href="https://noyano.wixsite.com/buyviagraonline#">sildenafil 100mg </a>
viagra cheap prices https://telegra.ph/How-to-get-viagra-without-a-doctor-08-18
can you buy viagra in stores <a href=https://my.desktopnexus.com/buyviagraonline/journal/online-viagra-without-a-prescriptuon-38932/#>viagra on line </a>
how can i buy viagra online <a href="https://onlineviagra.mystrikingly.com/#">viagra without prescription </a>
order viagra online no prescription https://buyviagraonline.micro.blog/
order viagra <a href=https://hub.docker.com/r/buyviagraonline/viagra#>generic viagra without a doctor prescription </a>
get prescription for viagra <a href="https://telegra.ph/How-to-get-viagra-without-a-doctor-08-18#">generic viagra </a>
uk viagra prices https://onlineviagra.mystrikingly.com/
what is stromectol <a href=https://challonge.com/en/orderstromectoloverthecounter#>ivermectin </a>
stromectol scabies <a href="https://aoc.stamford.edu/profile/Stromectol/#">stromectol pills </a>
stromectol effectiveness https://pinshape.com/users/2445987-order-stromectol-over-the-counter
Всякому начинающему гитаристу чрезвычайно важно постоянно заниматься на гитаре. Для этого есть особые ресурсы с подборами аккордов, например, сайт <a href=https://guitar-news.ru/guitar-help/950-o-tom-kak-vybrat-svoyu-pervuyu-gitaru.html>guitar-news.ru</a> или <a href=https://guitar-geek.ru>www.guitar-geek.ru</a>. Здесь есть правильные подборы аккордов для гитары для множества знакомых вам композиций, которые прекрасно подойдут для изучения начинающим гитаристам.
<a href=https://fortnaite.ru/product/dedpul-deadpool-4-kopirovat/>Купить Дэдпул (Deadpool) "4" для Fortnite. После оплаты вы получите бонус-код на: скин Дэдпул (Deadpool) "4" + Карту активации на 350 В-баксов ! PC/PS/Xbox/Nintendo </a>
online pharmacies canada <a href=https://motocom.co/demos/netw5/askme/question/canadian-pharmaceuticals-online-5/#>canadian government approved pharmacies </a>
best online international pharmacies <a href="https://www.midi.org/forum/profile/89266-canadianpharmaceuticalsonline#">mexican border pharmacies </a>
indian pharmacy https://canadianpharmaceuticalsonline.as.me/schedule.php
<a href=https://buylasixon.com/>lasix mechanism of action</a> Dominguez, E
How to <a href=http://77pro.org/repair-corrupted-psd-files.html>repair PSD</a> file.
Нагреватель хомутовый из оцинкованной стали выполнятся по индивидуальных чертежам заказчика, при соблюдении всех нормативов и стандартов https://rusupakten.ru/product/rt-650/
Хомутовый нагреватель оцинкованный стандарт:Хомутовый нагреватель оцинкованный под заказ:
<a href=https://chimmed.ru/products/dekalin-id=406039>декалин </a>
Tegs: щавелевая кислота купить https://chimmed.ru/products/search?name=%D1%89%D0%B0%D0%B2%D0%B5%D0%BB%D0%B5%D0%B2%D0%B0%D1%8F+%D0%BA%D0%B8%D1%81%D0%BB%D0%BE%D1%82%D0%B0
<u>ксилол купить </u>
<i>декалин </i>
<b>щавелевая кислота купить </b>
canadian pharmaceuticals online <a href=https://thefencefilm.co.uk/community/profile/hswlux/#>mexican pharmacies </a>
pharmacy online drugstore <a href="https://anewearthmovement.org/community/profile/mefug/#">viagra pharmacy 100mg </a>
canadian pharmacies online http://kawerf.iwopop.com/
pharmacy on line <a href=https://www.formlets.com/forms/tH7aROl1ugDpCHqB/#>canadian pharmacies </a>
pharmacy drugstore online <a href="https://hub.docker.com/repository/docker/canadianpharmacys/pharmacies_in_canada_shipping_to_usa#">international pharmacy </a>
prescription drugs from canada http://kawerf.iwopop.com/
<a href=>http://defloration.gq/</a>
100mg viagra vs 20mg cialis [url=https://alewrt.flazio.com/#]tadalafil 5mg [/url]
generische cialis kaufen <a href="https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html#">tadalafil 20mg </a>
cialis medication online https://mewser.mystrikingly.com/
pharmacy buy online <a href=https://www.divephotoguide.com/user/buyviagraonline#>generic viagra 100mg </a>
buy generic viagra pills <a href="https://viagraonline.home.blog/#">viagra online </a>
buy viagra cheaply https://viagraonline.estranky.sk/clanky/viagra-without-prescription.html
https://mir74.ru/news/15144-v-chelyabinske-projdet-kubok-po-tancu-zhivota.html
<a href=https://one-two-slim-kapli.ru/>https://one-two-slim-kapli.ru/</a> купить onetwoslim
medical pharmacy <a href=https://web904.com/canadian-pharmaceuticals-for-usa-sales/#>online medicine tablets shopping </a>
canadian pharcharmy <a href="https://melaninterest.com/user/canadian-pharmaceuticals-online/?view=likes#">online medicine to buy </a>
buy generic viagra online https://canadianpharmaceuticalsonline.bandcamp.com/releases
stromectol nuzeniec <a href=https://sanangelolive.com/members/girsagerea#>stromectol no prescription </a>
purchase stromectol online <a href="https://sanangelolive.com/members/unsafiri#">buy stromectol uk </a>
buy ivermectin online fitndance https://challonge.com/esapenti
<a href=https://yourdesires.ru/vse-obo-vsem/1489-kak-obrazovalsja-ugol.html>Как образовался уголь?</a> или <a href=https://yourdesires.ru/finance/private-finance/1426-prodazha-kvartiry-cherez-rijeltora-chto-nuzhno-znat.html>Продажа квартиры через риэлтора: что нужно знать</a>
https://yourdesires.ru/home-and-family/cookery/1678-kak-vybrat-bochku-dlja-zasolki.html
stromectol headache <a href=https://orderstromectoloverthecounter.fo.team/#>medicament stromectol </a>
buying stromectol <a href="https://orderstromectoloverthecounter.fo.team/#">stromectol over the counter </a>
stromectol purchase https://stromectoloverthecounter.wordpress.com/
herbal tobacco <a href= > https://zober.nl/zopnl.html </a> herbalism trainer wow <a href= http://symposia.microscopy.ie/images/cialis-Ireland.html > http://symposia.microscopy.ie/images/cialis-Ireland.html </a> drug rehab florida
viagra generic online pharmacy <a href=https://calendly.com/canadianpharmaceuticalsonline/onlinepharmacy#>mexican border pharmacies </a>
pharmacy online shopping <a href="https://sway.office.com/bwqoJDkPTZku0kFA#">canada pharmacies </a>
walmart pharmacy viagra https://canadianpharmaceuticalsonline.eventsmart.com/2022/11/20/canadian-pharmaceuticals-for-usa-sales/
canadian pharmacy <a href=https://infogram.com/canadian-pharmacies-shipping-to-usa-1h1749v1jry1q6z#>london drugs canada </a>
shoppers pharmacy <a href="https://canadianpharmaceuticals.educatorpages.com/pages/canadian-pharmacies-shipping-to-usa#">canada pharmacy </a>
canadian pharmaceuticals online safe https://jemi.so/canadian-pharmacies-shipping-to-usa
online pharmacies <a href=http://pharmacy.prodact.site/#>canada pharmacies </a>
pharmacy in canada <a href="http://lwerfa.iwopop.com/#">medicine online order </a>
canada pharmaceutical online ordering http://herbsd.iwopop.com/
canadian pharmacy king <a href=https://thefencefilm.co.uk/community/profile/hswlux/#>medicine online shopping </a>
aarp recommended canadian pharmacies <a href="http://lsdevs.iwopop.com/#">canadian pharmacy online </a>
pharmacy online drugstore http://herbsd.iwopop.com/
canadian drugs pharmacies online <a href=https://my.desktopnexus.com/Canadian-pharmacies/journal/safe-canadian-online-pharmacies-38571/#>canadian pharmaceuticals online </a>
mexican pharmacies <a href="https://www.formlets.com/forms/N2BtJ3kPeJ3KclCw/#">canadian viagra </a>
buy generic viagra online https://canadianpharmaceutical.bigcartel.com/canadian-pharmaceuticals-online
Hello, you create a rule to Detect and Prevent vulnerability but for this hit we can see "Detect only" on IPS / IDS dashboard.
Should we modify the default options for each signature? (Alerte by default, DROP, REJECT)
Heard from VMware staff, yeah, the default option ("alert" in the most cases, coming from different provider "lastline, truewave.." ) must be changed to take Prevention action on detected signatures. the easiest way suggested is to use terraform to automate the changes..
https://orenburg.kat-service.site/cbrilliancecm3.html
echte cialis bestellen <a href=http://lasweb.iwopop.com/#>cialis without a doctor prescription </a>
cialis leggaly <a href="https://tadalafil20mg.proweb.cz/#">online cialis generic </a>
generic cialis pro https://buycialisonline.teachable.com/
female cialis no prescription <a href=https://buycialisonline.fo.team/#>online buy cialis </a>
what is cheaper viagra cialis or levitra <a href="https://laswert.wordpress.com/#">generic cialis 2022 </a>
cheap cialis soft no rx https://graph.org/Tadalafil-20mg-08-13
viagra buy online uk <a href=https://graph.org/Buying-viagra-without-a-prescription-08-18#>pills erection generic viagra </a>
viagra uk prescription <a href="https://www.divephotoguide.com/user/buyviagraonline#">viagra online </a>
online pharmacy viagra https://onlineviagra.fo.team/
stromectol generic <a href=https://canadajobscenter.com/author/buystromectol/#>stromectol mites </a>
stromectol <a href="https://reallygoodemails.com/orderstromectoloverthecounter#">stromectol buy online </a>
stromectol espana https://www.repairanswers.net/question/order-stromectol-over-the-counter-2/
buy generic cialis <a href="https://cialisarm.com/">cheap cialis</a> what is cialis used for
Временная регистрация в Санкт-Петербурге
Я после очередного быстрого похудения долго восстанавливалась, а потом и вовсе вес застыл и никак не удавалось его сбросить.Сейчас пью капсулы Голдлайн Плюс, питаюсь через приложение Голдлайн и тренируюсь дома.В месяц уходит до 5 кг, считаю это самым оптимальным вариантом. <a href=https://vseledi.ru/beg-dlya-pohudeniya.html>как нужно бегать чтобы похудеть</a>
Да не пробуйте Вы никаких препаратов.Если хотите навредить своему здоровью, то пожалуйста.
<a href=https://proxyspace.seo-hunter.com>mobile proxy ipv4 info</a>
how long for cialis to peak <a href="https://cialisandtadalafil20.com/">what is the difference between viagra and cialis</a> cost of generic cialis
Lolita Girls Fuck Collection
loli video cp
tki.sk/4lL6N7
s.yjm.pl/BbtC
tw.uy/tw11l
pharmacies in canada <a href=https://canadianpharmaceuticals.educatorpages.com/pages/canadian-pharmacies-shipping-to-usa#>online order medicine </a>
canadian drugstore <a href="https://www.wattpad.com/user/Canadianpharmacy#">online pharmacy canada </a>
online pharmacies of canada https://canadianpharmaceuticalsonline.tawk.help/article/canadian-pharmacies-shipping-to-usa
erectile examination <a href=https://500px.com/p/stofovinin/?view=groups#>herbs for erectile dysfunction </a>
erectile booster method reviews <a href="https://plancaticam.estranky.cz/clanky/best-drugs-for-ed.html#">erectile difficulty </a>
medication induced erectile dysfunction https://500px.com/p/stofovinin/?view=groups
pharmacy online prescription <a href=http://sandbox.autoatlantic.com/community/profile/kawxvb/#>canadian online pharmacies </a>
mexican border pharmacies <a href="https://anewearthmovement.org/community/profile/mefug/#">buy viagra pharmacy 100mg </a>
canadian drugs pharmacy https://thefencefilm.co.uk/community/profile/hswlux/
canadia online pharmacy <a href=https://www.formlets.com/forms/tH7aROl1ugDpCHqB/#>canadian drugs pharmacy </a>
mexican border pharmacies <a href="https://hub.docker.com/repository/docker/canadianpharmacys/pharmacies_in_canada_shipping_to_usa#">canada pharmaceuticals online </a>
international pharmacy http://sandbox.autoatlantic.com/community/profile/kawxvb/
<a href=https://chimmed.ru/products/search/?name=гафний>гафний купить </a>
Tegs: гафний порошок https://chimmed.ru/products/search/?name=гафний+порошок
<u>eppendorf research pro </u>
<i>eppendorf support </i>
<b>eppendorf tube </b>
generic cialis pills and generic viagra <a href=https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html#>generic cialis </a>
buy generic cialis online cheap <a href="https://tadalafil20mg.proweb.cz/#">generic cialis tadalafil </a>
safe site to buy cialis online https://laswert.wordpress.com/
viagra cialis levetra <a href=https://hub.docker.com/r/tadalafil/20mg#>generic cialis 2022 </a>
cialis for daily use <a href="https://buycialisonline.fo.team/#">buy cialis </a>
telephone orders cialis https://buycialisonline.teachable.com/
buy cialis we <a href=https://owzpkg.zombeek.cz/#>cialis </a>
free online samples fo cialis <a href="https://buycialisonline.fo.team/#">cialis generico online </a>
key cialis acheter https://kasheras.livejournal.com/283.html
Спасибо за пост
_________________
canlı olaraq futbola bahis etməyin sirləri, <a href=https://aze.bkin-8374.space/362.html>güzgüli 1xbet yükləyin</a>, bukmeker kontekstində necə peşəkar olmaq
cheap viagra online usa <a href=https://onlineviagra.fo.team/#>viagra generic online usa pharmacy </a>
can i buy viagra at cvs <a href="https://viagraonline.estranky.sk/clanky/viagra-without-prescription.html#">viagra 100mg generic viagra </a>
blue pill https://hub.docker.com/r/buyviagraonline/viagra
approved canadian online pharmacies <a href=https://linktr.ee/canadianpharmaceuticalsonline#>medicine online shopping </a>
canada discount drug <a href="https://pinshape.com/users/2441403-canadian-pharmaceuticals-online#">online pharmacy </a>
indian pharmacy https://pinshape.com/users/2441621-canadian-pharmaceutical-companies
stromectol no prescription <a href=https://ktqt.ftu.edu.vn/en/question%20list/order-stromectol-over-the-counter-10/#>stromectol purchase </a>
purchase stromectol online <a href="https://orderstromectoloverthecounter.bandcamp.com/releases#">stromectol demodex </a>
dose of stromectol https://canadajobscenter.com/author/buystromectol/
Купить M16A3 Custom для WarFace
<a href=https://warfacepin.com/goods/m16a3-custom>Купить M16A3 Custom для WarFace </a>
Breaking news, sport, TV, radio and a whole lot more. The <a href=https://www.topworldnewstoday.com/>Top World News Today</a> informs, educates and entertains - wherever you are, whatever your age
stromectol lice <a href=https://dsdgbvda.zombeek.cz/#>stromectol </a>
medicaments stromectol <a href="https://inflavnena.zombeek.cz/#">ivermectin </a>
stromectol children https://inflavnena.zombeek.cz/
where can i buy cialis <a href="https://tadalafilkosmo.com/">ordering cialis online</a> generic cialis 2018
Нам понятно, что с производителями Петинимида, Петнидана и других вариантов этосуксимида никто переговоров не вел, и регистрировать их в России никто не собирается https://petnidan.com.ru
Pills dope leaflet. Generic Name. <a href="https://cialisory.com/# ">tadalafil research chemical</a> Realistic news about meds. Get information here.
<a href=https://cialisory.com/>how long does cialis stay in your system</a>
Is antibacterial body wash safe or <a href="http://stramectol.com/# ">ivermectin online</a>?
canada pharmaceutical online ordering <a href=http://lwerfa.iwopop.com/#>pharmacy online </a>
canadian drugs pharmacies online <a href="http://kawerf.iwopop.com/#">medicine online order </a>
canada discount drug http://lwerfa.iwopop.com/
canadian pharmaceuticals online safe <a href=https://gswera.livejournal.com/385.html#>drugstore online shopping </a>
best online international pharmacies <a href="https://my.desktopnexus.com/Canadian-pharmacies/journal/safe-canadian-online-pharmacies-38571/#">online medicine order discount </a>
viagra pharmacy 100mg https://azuvh4.wixsite.com/pharmaceuticals-onli/post/london-drugs-canada
plavix cialis side effects <a href=https://owzpkg.zombeek.cz/#>cialis 20 </a>
tub symbolism in cialis ads <a href="https://owzpkg.zombeek.cz/#">generic cialis at walmart </a>
controindicazioni del cialis 20 mg https://kwxcva.estranky.cz/clanky/cialis-20-mg.html
cialis affiliate program <a href=https://buycialisonline.fo.team/#>cialis 20mg </a>
cialis target market <a href="https://kwxcva.estranky.cz/clanky/cialis-20-mg.html#">cialis online pharmacy </a>
cialis da 10 mg funziona https://kwxcva.estranky.cz/clanky/cialis-20-mg.html
buy viagra online price <a href=http://jso7c59f304.iwopop.com/#>edpillenmmt viagra kaufen </a>
buy cheap viagra online uk <a href="https://buyviagraonline.teachable.com/#">generic viagra price at walmart </a>
buy sildenafil tablets online https://graph.org/Buying-viagra-without-a-prescription-08-18
viagra generic canadian pharmacy <a href=https://500px.com/p/listofcanadianpharmaceuticalsonline#>online pharmacies </a>
canadian pharmacy viagra generic <a href="https://linktr.ee/canadianpharmaceuticalsonline#">london drugs canada </a>
navarro pharmacy https://www.seje.gov.mz/question/canadian-pharmacies-shipping-to-usa/
pharmacy drugstore online <a href=https://www.audiologysolutionsnetwork.org/profile/422019/0#>pharmacies </a>
best canadian online pharmacies <a href="https://legalmarketplace.alanet.org/profile/421920/0#">online medicine order discount </a>
pharmacy in canada https://sanangelolive.com/members/canadianpharmaceuticalsonlineusa
большое спасибо
_________________
перевод денег с карты в игровые автоматы - <a href=http://km.onlinebestrealmoneygames.xyz/Aviator.html>как поднять деньги в играх 1xbet</a>, верификация при выводе денег из казино
Hello. And Bye.
Thanks to my father who informed me concerning this website, this blog is in fact amazing.
If you have any recommendations or techniques for my new blog <a href=https://indigorosee.com/2021/01/24/how-to-prepare-for-a-successful-semester/>printable monthly calendars</a> please share!
how 2 search on the inteternet for help with hw essay <a href="https://peperwritinghelpcup.com/">professional term paper writers</a> essay help video stanford tutor
erectile booster <a href=https://aoc.stamford.edu/profile/plumerinput/#>buy erectile dysfunction pills </a>
online doctor erectile dysfunction <a href="https://plancaticam.estranky.cz/clanky/best-drugs-for-ed.html#">erectile stimulator </a>
erectile pills over the counter https://aoc.stamford.edu/profile/plumerinput/
Can hypertension be cured <a href="https://lasixotc.com/ ">lasix</a>?
shoppers pharmacy <a href=https://thefencefilm.co.uk/community/profile/hswlux/#>canadian online pharmacies legitimate </a>
shoppers pharmacy <a href="http://lwerfa.iwopop.com/#">viagra generic online pharmacy </a>
cheap prescription drugs http://herbsd.iwopop.com/
viagra generic canadian pharmacy <a href=http://sandbox.autoatlantic.com/community/profile/kawxvb/#>canadian pharmaceuticals online </a>
canadian viagra generic pharmacy <a href="https://pharmaceuticals.teachable.com/#">online pharmacies in usa </a>
shoppers drug mart pharmacy http://lsdevs.iwopop.com/
https://mir74.ru/14835-pensionnym-fondam-zapretili-rabotat-cherez.html
how to get prescription of cialis soft <a href=https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html#>buy cialis </a>
cialis nline <a href="https://mewser.mystrikingly.com/#">cialis buy online </a>
is cialis vrij verkrijgbaar https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html
which works best cialis or levitra <a href=https://hub.docker.com/r/tadalafil/20mg#>generic cialis at walmart </a>
taking viagra plus cialis <a href="https://kswbnh.nethouse.ru/#">generic cialis available </a>
cialis reviews from users https://hub.docker.com/r/tadalafil/20mg
интересные новости
_________________
Kompüter torrentinə 1xbet yükləmə, <a href=https://az.bkin-7779.space/187.html>ən yaxşı bukmeyker yükləmələri</a>, futbol amkar cska üçün proqnoz
viagra dosage <a href=https://graph.org/Buying-viagra-without-a-prescription-08-18#>viagra pills </a>
viagra generic online pharmacy <a href="https://telegra.ph/How-to-get-viagra-without-a-doctor-08-18#">viagra 100mg </a>
best buy for viagra http://jso7c59f304.iwopop.com/
best place to buy online viagra <a href=https://buyviagraonline.teachable.com/#>sildenafil 100mg </a>
buy viagra online price <a href="https://buyviagraonline.micro.blog/#">generic viagra 100mg </a>
buy generic viagra uk https://buyviagraonline.zombeek.cz/
buy tadalafil online <a href=https://viagraonlinee.livejournal.com/492.html#>buy pills erection viagra </a>
where to buy viagra <a href="https://viagrawithoutprescription.webflow.io/#">generic viagra without a doctor prescription </a>
how to buy viagra online without https://onlineviagra.flazio.com/
apollo pharmacy online <a href=https://500px.com/p/listofcanadianpharmaceuticalsonline#>online medicine tablets shopping </a>
best canadian online pharmacies <a href="https://www.seje.gov.mz/question/canadian-pharmaceuticals-for-usa-sales/#">canadian prescriptions online </a>
canadian drugs online pharmacies https://pinshape.com/users/2441621-canadian-pharmaceutical-companies
stromectol oral <a href=https://www.provenexpert.com/order-stromectol-over-the-counter12/#>stromectol biam </a>
stromectol dosage table <a href="https://www.seje.gov.mz/question/order-stromectol-over-the-counter-6/#">stromectol headache </a>
stromectol online pharmacy https://pinshape.com/users/2445987-order-stromectol-over-the-counter
cialis generic pharmacy online <a href=https://wefbuyersguide.wef.org/profile/421914/0#>cheap pharmacy online </a>
canadian drugs pharmacies online <a href="https://supplier.ihrsa.org/profile/421717/0#">canadian online pharmacies </a>
viagra generic online pharmacy https://wefbuyersguide.wef.org/profile/421914/0
Deepnfast makes payments at any time as quickly as possible! The international network of financial mutual support gives everyone the opportunity to receive the income exceeding the investment in several thousand times!!! Proven marketing! 24/7 customer support! Build your own business!
Register by clicking here: https://deepnfast.com/invite/XSTU1aju
порно комикс milf
http://agemarus.ru/bitrix/redirect.php?event1=click_to_call&event2=&event3=&goto=https://tubesweet.xyz/categories
http://systema-plus.ru/bitrix/redirect.php?event1=&event2=&event3=&goto=https://tubesweet.xyz/categories
<a href=https://mega-remont.pro/msk-restavratsiya-vann>restoration of baths in moscow megaremont</a>
Drugs data for patients. What side effects can this medication cause? <a href="https://cialisory.com/ ">cialis price</a> Some scoop less medication. Pore over word now.
<a href=https://yourdesires.ru/it/news-it/766-fsb-inostrannye-specsluzhby-gotovyat-kiberataki-s-celyu-destabilizacii-finansovoy-sistemy-rossii.html>ФСБ: иностранные спецслужбы готовят кибератаки с целью дестабилизации финансовой системы России</a> или <a href=https://yourdesires.ru/fashion-and-style/quality-of-life/1460-obzor-kazino-vulkan-booster-onlineru.html>Обзор казино Вулкан booster-online.ru</a>
https://yourdesires.ru/beauty-and-health/lifestyle/53-luchshie-recepty-ot-pohmelya.html
Hello. And Bye.
canadian pharmacy king <a href=http://sandbox.autoatlantic.com/community/profile/kawxvb/#>canadian pharmacies online </a>
viagra generic online pharmacy <a href="https://anewearthmovement.org/community/profile/mefug/#">canadian pharmacies online </a>
pharmacy online drugstore https://anewearthmovement.org/community/profile/mefug/
walmart pharmacy viagra <a href=http://herbsd.iwopop.com/#>online pharmacies canada </a>
viagra generic online pharmacy <a href="https://hub.docker.com/repository/docker/canadianpharmacys/pharmacies_in_canada_shipping_to_usa#">pharmacies </a>
canadian pharmacy king http://lsdevs.iwopop.com/
I consider, that the theme is rather interesting. Give with you we will communicate in PM.
https://euboys.net
https://hulla24.com
cialis oral <a href=https://buycialisonline.fo.team/#>cialis 20 </a>
viagra vs cialis better <a href="https://kwxcva.estranky.cz/clanky/cialis-20-mg.html#">buy cialis online </a>
cialis patent expiry canada https://owzpkg.zombeek.cz/
shoppers pharmacy <a href=https://www.divephotoguide.com/user/pharmacies#>canadian pharmacies online </a>
viagra generic canadian pharmacy <a href="https://my.desktopnexus.com/Canadian-pharmacies/journal/safe-canadian-online-pharmacies-38571/#">pharmacy cheap no prescription </a>
pharmacy intern https://hub.docker.com/r/pharmacies/online
tadafil cialis on-line pharmacies <a href=https://owzpkg.zombeek.cz/#>cialis 20 mg </a>
differences between viagra and cialis and levitra <a href="https://kalwer.micro.blog/#">cialis online buy </a>
side effects of viagra and cialis https://kwxcva.estranky.cz/clanky/cialis-20-mg.html
buy viagra online safely <a href=https://graph.org/Buying-viagra-without-a-prescription-08-18#>viagra prices </a>
viagra price <a href="https://buyviagraonline.estranky.sk/clanky/buy-viagra-without-prescription-pharmacy-online.html#">viagra coupon </a>
safe place to buy viagra online https://buyviagraonline.fo.team/
how do i buy viagra <a href=https://graph.org/Buying-viagra-without-a-prescription-08-18#>buy viagra online </a>
buy women viagra <a href="https://onlineviagra.mystrikingly.com/#">viagra online </a>
viagra side effects https://onlineviagra.mystrikingly.com/
stromectol pills <a href=https://www.seje.gov.mz/question/order-stromectol-over-the-counter-6/#>what is stromectol </a>
ivermectine <a href="https://reallygoodemails.com/orderstromectoloverthecounter#">stromectol </a>
buy stromectol fitndance https://reallygoodemails.com/orderstromectoloverthecounter
Быстрее пули без рекламы Смотрите Онлайн
Фильм «Быстрее Пули» В
Хорошем HD Качестве На Нашем Сайте
how much does stromectol cost <a href=https://order-stromectol-over-the-counter.estranky.cz/clanky/order-stromectol-over-the-counter.html#>stromectol canada </a>
dosage for stromectol <a href="https://dsdgbvda.zombeek.cz/#">stromectol medication </a>
medicament stromectol https://sanangelolive.com/members/unsafiri
canada online pharmacies <a href=https://www.mojomarketplace.com/user/Canadianpharmaceuticalsonline-EkugcJDMYH#>pharmacies shipping to usa </a>
cheap pharmacy online <a href="https://motocom.co/demos/netw5/askme/question/canadian-pharmaceuticals-online-5/#">canadian pharmacy king </a>
online pharmacy https://www.giantbomb.com/profile/canadapharmacy/blog/canadian-pharmaceuticals-online/265652/
How to [url=http://77pro.org/14-24-repair-outlook.html]repair Outlook[/url] storage file
<a href=https://stromectol.homes/>ivermectin for sale on ebay</a> Jing Xiang, Hongbo Yang, Chao Che, Haixia Zou, Hanshuo Yang, Yuquan Wei, Junmin Quan, Hui Zhang, Zhen Yang, Shuo Lin
generic viagra online pharmacy <a href=https://soundcloud.com/canadian-pharmacy#>national pharmacies </a>
canada drugs online <a href="https://soundcloud.com/canadian-pharmacy#">pharmacies shipping to usa </a>
pharmacy drugstore online https://the-dots.com/projects/covid-19-in-seven-little-words-848643
<a href=https://blogintimnews.ru/>https://blogintimnews.ru/</a>
cost of cialis 5 mg how much is cialis in canada <a href="https://vipharmicavip.com/">cialis 10mg</a> generic cialis in canada generic cialis online canadian pharmacy
<a href=https://dirty-whore.ru/>https://dirty-whore.ru/</a>
erectile disorder <a href=https://www.provenexpert.com/best-erectile-pills/#>new drugs for ed </a>
erectile at 43 <a href="https://piesapalbe.estranky.sk/clanky/buy-erectile-dysfunction-medications-online.html#">erectile function scale </a>
treating erectile dysfunction without drugs https://wallsawadar.zombeek.cz/
Telegram @zennoboss (ICQ: 1643164) КИДАЛА И МОШЕННИК
Телеграмм: @zennoboss
Skype: live:zennoboss
Email: zennoboss@ya.ru
ICQ: 1643164
Продает фейковые курсы по емеил рассылкам за 1к+$
После получения денег выдет не рабочие методы и щаблоны на зеннопостер
возврат денег не делает!
вот его тема на зенофоруме https://zennolab.com/discussion/threads/obuchenie-email-rassylkam-soft-dlja-avtomatizacii-ot-100k-v-sutki-s-servera.90372/page-6
https://kinoland.biz/
buy viagra pharmacy 100mg <a href=http://pharmacy.prodact.site/#>canadian pharmacy </a>
shoppers drug mart canada <a href="http://kawerf.iwopop.com/#">canadian pharmacy generic viagra </a>
on line pharmacy https://thefencefilm.co.uk/community/profile/hswlux/
руторг часы
I think, that you commit an error. Write to me in PM, we will discuss.
https://bitchjustmove.com
https://ambergardens.net
cialis 5 mg test <a href=https://alewrt.flazio.com/#>cialis generic </a>
cialis low dose reviews <a href="https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html#">cialis without a doctor's prescription </a>
online apotheke niederlande cialis http://lasweb.iwopop.com/
buy viagra online order <a href=https://buyviagraonline.micro.blog/#>viagra generico </a>
canadian viagra online <a href="http://jso7c59f304.iwopop.com/#">viagra without doctor prescription </a>
viagra pharmacy https://graph.org/Buying-viagra-without-a-prescription-08-18
viagra buy online uk <a href=https://linktr.ee/buyviagraonline#>sildenafil 100mg </a>
where can i buy viagra over the counter <a href="https://onlineviagra.fo.team/#">viagra without a doctor prescription price </a>
buy viagra usa online https://telegra.ph/How-to-get-viagra-without-a-doctor-08-18
stromectol france <a href=https://500px.com/p/orderstromectoloverthecounter#>generic stromectol </a>
stromectol medicine <a href="https://reallygoodemails.com/orderstromectoloverthecounter#">stromectol scabies treatment </a>
ivermectin dosage https://pinshape.com/users/2445987-order-stromectol-over-the-counter
burned tongue remedies <a href= > https://conference.researchbib.com/view/event/152427 </a> holistic herbal health <a href= https://www.okpal.com/zaldiar/#/ > https://www.okpal.com/zaldiar/#/ </a> safe penis pills
<a href=https://seora.ru>продвижение сайтов</a>}
Приглашаем посетить информацию на тему <a href=https://masterokon66.ru/prajs>ремонт окон</a> если беспокоитесь за своего ребенка . Адрес: masterokon66.ru .
stromectol reviews <a href=https://orderstromectoloverthecounter.com/#>https://orderstromectoloverthecounter.com/ </a>
stromectol order online <a href="https://orderstromectoloverthecounter.com/#">https://orderstromectoloverthecounter.com/ </a>
stromectol doses https://orderstromectoloverthecounter.com/
stromectol cream <a href=https://orderstromectoloverthecounter.flazio.com/#>facts stromectol </a>
stromectol uk <a href="https://stromectoloverthecounter.wordpress.com/#">stromectol tablets uk </a>
stromectol for scabies https://orderstromectoloverthecounter.flazio.com/
<a href=https://chimmed.ru/>нитрофенол </a>
Tegs: амитраз https://chimmed.ru/
<u>acros organics </u>
<i>sigma aldrich </i>
<b>thermo fisher scientific </b>
<a href=https://krasnoe-ibeloe.ru/>https://krasnoe-ibeloe.ru/</a>
<a href=http://krasnoe-ibeloe.ru/indexx.htm>http://krasnoe-ibeloe.ru/indexx.htm</a>
order erectile dysfunction pills from india <a href=https://piesapalbe.estranky.sk/clanky/buy-erectile-dysfunction-medications-online.html#>ed drugs generic </a>
best erectile pump <a href="https://wallsawadar.zombeek.cz/#">best drugs for ed </a>
natural erectile supplements https://plancaticam.estranky.cz/clanky/best-drugs-for-ed.html
canada pharmaceuticals online <a href=http://lwerfa.iwopop.com/#>drugstore online </a>
pharmacy online no prescription <a href="http://lwerfa.iwopop.com/#">canadian drugs </a>
canadian pharmacy generic viagra http://sandbox.autoatlantic.com/community/profile/kawxvb/
viagra in india <a href="https://viagrarest.com/">best place to buy viagra online</a> natural viagra
* Reseller payment method: Bitcoin, Neteller, Skrill, Webmoney, Perfect Money
* Server's capacity: 230 TB for MP3, FLAC, Music Clips.
* Support: FTP, FTPS (File Transfer Protocol Secure), SFTP and HTTP, HTTPS.
* Overal server's speed: 1GB/s.
* Easy to use: Most of genres are sorted by days.
https://www.0dayvinyls.org/premium.php
Best regards, Scene Releases Team.
lily icos cialis <a href=https://kasheras.livejournal.com/283.html#>cialis buy online </a>
cialis purchase <a href="http://lasweb.iwopop.com/#">online cialis </a>
menopause cialis https://mewser.mystrikingly.com/
<a href=https://proxyspace.seo-hunter.com>мобильный браузер прокси</a>
where to purchase viagra <a href=https://buyviagraonline.fo.team/#>cheap viagra </a>
blue pills <a href="https://buyviagraonline.teachable.com/#">generic viagra </a>
how can i order viagra https://buyviagraonline.nethouse.ru/
how to buy viagra online safely <a href=https://hub.docker.com/r/buyviagraonline/viagra#>viagra prices </a>
buy generic sildenafil online <a href="https://buyviagraonline.zombeek.cz/#">viagra on line </a>
buy viagra online no prescription uk http://jso7c59f304.iwopop.com/
online pharmacy levitra <a href=https://viagraonlinee.livejournal.com/492.html#>viagra generic </a>
order viagra online <a href="https://my.desktopnexus.com/buyviagraonline/journal/online-viagra-without-a-prescriptuon-38932/#">generic viagra without subscription walmart </a>
order cheap viagra online https://viagraonline.estranky.sk/clanky/viagra-without-prescription.html
dose for stromectol <a href=https://reallygoodemails.com/orderstromectoloverthecounter#>stromectol order </a>
stromectol sale <a href="https://ktqt.ftu.edu.vn/en/question%20list/order-stromectol-over-the-counter-10/#">stromectol usa </a>
facts stromectol https://orderstromectoloverthecounter.bandcamp.com/releases
stromectol canada <a href=https://www.provenexpert.com/order-stromectol-over-the-counter12/#>stromectol </a>
purchase stromectol online <a href="https://500px.com/p/orderstromectoloverthecounter#">stromectol tablets uk </a>
stromectol brasilien https://canadajobscenter.com/author/arpreparof1989/
stromectol biam <a href=https://challonge.com/esapenti#>buy stromectol online </a>
stromectol sale <a href="https://order-stromectol-over-the-counter.estranky.cz/clanky/order-stromectol-over-the-counter.html#">stromectol </a>
buy stromectol online fitndance https://soncheebarxu.estranky.cz/clanky/stromectol-for-head-lice.html
Хочу купить
<a href=https://t.me/HiFiport/3058>плеер FiiO</a>. Какие посоветуете, ребят?
sildenafil vs cialis <a href="https://cialislands.com/">how to use cialis</a> cialis from canada to usa
At Jackpotbetonline.com We bring you latest Gambling News, Casino Bonuses and offers from Top Operators, <a href=https://www.jackpotbetonline.com/>Online Casino</a> Slots Tips, Sports Betting Tips, odds etc.
viagra from boots online nombre generico del viagra <a href="https://nhsviagravip.com/">what does viagra cost</a> farmaciaonline viagra viagra 100mg uk
can erectile dysfunction be hereditary <a href=https://piesapalbe.estranky.sk/clanky/buy-erectile-dysfunction-medications-online.html#>erectile cream for me </a>
erectile medicine <a href="https://aoc.stamford.edu/profile/plumerinput/#">best drugs for ed </a>
erectile medicine for men https://500px.com/p/stofovinin/?view=groups
erectile stamina in older men <a href=https://aoc.stamford.edu/profile/plumerinput/#>ed drugs generic </a>
erectile tissue definition <a href="https://challonge.com/afersparun#">cheap ed drugs </a>
erectile disorder dsm 5 https://pinshape.com/users/2517016-cheap-ed-drugs
indian pharmacy <a href=http://pharmacy.prodact.site/#>pharmacy </a>
canadian pharmacy online <a href="http://herbsd.iwopop.com/#">canadian pharcharmy </a>
pharmacies shipping to usa https://anewearthmovement.org/community/profile/mefug/
online pharmacy <a href=https://my.desktopnexus.com/Pharmaceuticals/journal/canadian-pharmaceuticals-for-usa-sales-38346/#>order medicine online </a>
pills viagra pharmacy 100mg <a href="https://my.desktopnexus.com/drugstore-online/journal/recommended-canadian-pharmacies-38369/#">cialis pharmacy online </a>
canadian viagra http://lwerfa.iwopop.com/
canadian pharmacy cialis brand <a href=https://kalwer.micro.blog/#>cialis </a>
cialis uses <a href="https://graph.org/Tadalafil-20mg-08-13#">cialis </a>
cialis levitra or viagra which is better https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html
online order for viagra <a href=https://buyviagraonl.livejournal.com/386.html#>viagra pharmacy 100mg </a>
where can i buy viagra over the counter <a href="https://buyviagraonline.home.blog/#">viagra ohne rezept </a>
order viagra https://buyviagraonline.estranky.sk/clanky/buy-viagra-without-prescription-pharmacy-online.html
stromectol posologie <a href=https://ktqt.ftu.edu.vn/en/question%20list/order-stromectol-over-the-counter-10/#>stromectol scabies treatment </a>
stromectol online pharmacy <a href="https://www.provenexpert.com/order-stromectol-over-the-counter12/#">buying stromectol </a>
stromectol treatment scabies https://500px.com/p/orderstromectoloverthecounter
canada discount drug <a href=https://aoc.stamford.edu/profile/canadianpharmaceuticalsonline/#>navarro pharmacy miami </a>
canadian pharmacy cialis 20mg <a href="https://linktr.ee/canadianpharmaceuticalsonline#">pharmacies </a>
pharmacy on line https://ktqt.ftu.edu.vn/en/question%20list/canadian-pharmaceuticals-for-usa-sales/
dosage for stromectol <a href=https://orderstromectoloverthecounter.flazio.com/#>stromectol usa </a>
stromectol india <a href="https://telegra.ph/Order-Stromectol-over-the-counter-10-29#">buy stromectol online </a>
stromectol espana https://buystromectol.livejournal.com/421.html
stromectol buy <a href=https://orderstromectoloverthecounter.nethouse.ru/#>buy stromectol uk </a>
stromectol uk <a href="https://orderstromectoloverthecounter.proweb.cz/#">buy ivermectin online </a>
ivermectin dosage https://graph.org/Order-Stromectol-over-the-counter-10-29-2
How to <a href=https://bit.ly/26-ost-viewer-03>open ost file</a>
<a href=https://megaremont.pro/voronezh-restavratsiya-vann>methods of restoration of baths</a>
<a href=https://blogintimlife.ru/>https://blogintimlife.ru/</a>
best online canadian pharmacy <a href=https://infogram.com/canadian-pharmacies-shipping-to-usa-1h1749v1jry1q6z#>walmart pharmacy viagra </a>
buy viagra pharmacy 100mg <a href="https://issuu.com/lustgavalar#">canadian pharmacy online </a>
canada pharmaceuticals online generic https://jemi.so/canadian-pharmacies-shipping-to-usa
<a href=https://chimmed.ru/>musculus sartorius </a>
Tegs: натрия фторид купить https://chimmed.ru/
<u>борная кислота порошок купить </u>
<i>sartorius </i>
<b>этиленгликоль купить </b>
24 hour pharmacy <a href=http://lwerfa.iwopop.com/#>pharmacy in canada </a>
shoppers drug mart canada <a href="https://my.desktopnexus.com/Pharmaceuticals/journal/canadian-pharmaceuticals-for-usa-sales-38346/#">pharmacy online </a>
cheap pharmacy online http://lwerfa.iwopop.com/
discount canadian drugs <a href=https://hub.docker.com/repository/docker/canadianpharmacys/pharmacies_in_canada_shipping_to_usa#>online medicine shopping </a>
discount pharmacies <a href="http://lwerfa.iwopop.com/#">medicine online order </a>
shoppers drug mart pharmacy https://anewearthmovement.org/community/profile/mefug/
viagra generic online pharmacy <a href=https://gswera.livejournal.com/385.html#>canada pharmacy </a>
canadian pharmaceuticals <a href="https://canadianpharmaceutical.bigcartel.com/canadian-pharmaceuticals-online#">medicine online order </a>
online pharmacies canada https://lasevs.estranky.cz/clanky/pharmaceuticals-online-australia.html
approved canadian online pharmacies <a href=https://telegra.ph/Reputable-canadian-pharmaceuticals-online-08-12#>online pharmacies </a>
on line pharmacy <a href="https://telegra.ph/Reputable-canadian-pharmaceuticals-online-08-12#">canadian viagra </a>
online pharmacies https://kwenzx.nethouse.ru/
viagra professional <a href=https://buyviagraonline.proweb.cz/#>generic viagra available </a>
buy sildenafil online uk <a href="https://buyviagraonlinet.wordpress.com/#">viagra prices </a>
buy viagra with no prescription https://buyviagraonline.flazio.com/
buy viagra using paypal <a href=https://form.jotform.com/222341315941044#>buy viagra </a>
buy viagra without rx <a href="https://viagraonlinee.livejournal.com/492.html#">pills erection generic viagra </a>
buy female viagra uk https://hub.docker.com/r/buyviagraonline/viagra
stromectol for scabies <a href=https://pinshape.com/users/2445987-order-stromectol-over-the-counter#>ivermectina dosis </a>
stromectol dosering <a href="https://ktqt.ftu.edu.vn/en/question%20list/order-stromectol-over-the-counter-10/#">stromectol purchase </a>
stromectol for scabies https://www.seje.gov.mz/question/order-stromectol-over-the-counter-6/
viagra no pres <a href=https://onlineviagra.flazio.com/#>viagra generic canadian pharmacy </a>
buy viagra no rx <a href="https://onlineviagra.flazio.com/#">viagra without a doctor prescription </a>
rx sildenafil https://www.divephotoguide.com/user/buyviagraonline
How to <a href=https://bit.ly/46-06-recuperar-archivo-pdf-danado>repair Excel</a> files
In complicated times of transformation, there is constantly something good and beautiful. Quantum medicine - the medicine of the prospect. Click to - https://t.me/quantummedicinehealy
essay writer essay writing service <a href="https://topbuyessaysonline.com/">online essay writing</a> custom essay wriging service
Абразивные материалы для жирафа диаметром 222 мм на липучке - купить в СПб.
Удобно при обработке больших площадей, отличаются высокой эффективностью. Каким должен быть круг для «жирафа». Эффективная обработка поверхностей возможна только при грамотном подборе шлифдисков. Для «жирафа» применяются круги с такими параметрами: диаметр полотна – 225 мм.
Подробно посмотреть можно по ссылке: <a href=https://vk.com/smit24_spb>купить ручной шлифовальный блок</a>
cheap pharmacy online <a href=https://my.desktopnexus.com/Pharmaceuticals/journal/canadian-pharmaceuticals-for-usa-sales-38346/#>online drugstore </a>
aarp recommended canadian pharmacies <a href="http://pharmacy.prodact.site/#">pharmacie </a>
mexican border pharmacies http://herbsd.iwopop.com/
pharmacies in canada <a href=https://my.desktopnexus.com/drugstore-online/journal/recommended-canadian-pharmacies-38369/#>canadian pharmaceuticals online </a>
canadian pharmaceuticals online safe <a href="https://canadianpharmacy.teachable.com/#">pharmacy online drugstore </a>
canadian online pharmacy https://www.divephotoguide.com/user/Pharmacy
cialis dosage information <a href=https://buycialisonline.bigcartel.com/cialis-without-a-doctor-prescription#>viagra vs cialis </a>
200 generic cialis softtabs <a href="https://www.formlets.com/forms/fpN4Ll8AEnDHBAkr/#">generic cialis </a>
achat cialis 5mg https://kasheras.livejournal.com/283.html
clotures sp cialis es <a href=https://owzpkg.zombeek.cz/#>online buy cialis </a>
cialis and alcohol forum <a href="https://kalwer.micro.blog/#">cheap cialis </a>
cheapest cialis venezuela https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html
half life of viagra and cialis <a href=https://hub.docker.com/r/tadalafil/20mg#>cialis without a doctor's prescription </a>
buy cialis narod ru domain <a href="https://my.desktopnexus.com/Buycialis/journal/cialis-without-a-doctor-prescription-38780/#">buy cialis generic </a>
what are the tub in cialis soft https://sbwerd.estranky.sk/clanky/cialis-generic-pharmacy-online.html
dose for stromectol <a href=https://reallygoodemails.com/orderstromectoloverthecounter#>stromectol generic </a>
stromectol no prescription <a href="https://canadajobscenter.com/author/buystromectol/#">stromectol purchase </a>
stromectol lice https://challonge.com/en/orderstromectoloverthecounter
stromectol canada <a href=https://order-stromectol-over-the-counter.estranky.cz/clanky/order-stromectol-over-the-counter.html#>buy stromectol uk </a>
stromectol oral <a href="https://challonge.com/esapenti#">stromectol biam </a>
stromectol children https://order-stromectol-over-the-counter.estranky.cz/clanky/order-stromectol-over-the-counter.html
stromectol medicine <a href=https://lehyriwor.estranky.sk/clanky/stromectol-cream.html#>buy ivermectin </a>
stromectol price <a href="https://sanangelolive.com/members/girsagerea#">stromectol online </a>
stromectol buy online https://soncheebarxu.estranky.cz/clanky/stromectol-for-head-lice.html
Технология <a href=http://77pro.org/10-vosstanovit-psd-file.html>восстановления Photoshop данных</a> из неисправного *.psd файла Adobe Photoshop
очень интересно, но ничего толкового
_________________
игровые автоматы с выводом реальных денег - <a href=http://km.playtoprealmoneygame.xyz/Aviator.html>игры в 1xbet за 1 рубль</a>, игровые автоматы с выводом реальных денег отзывы
women viagra <a href="https://lobviagra.com/">viagra pills for men</a> woman viagra
<a href="https://3d-pechat-v-ekaterinburge.store/">https://3d-pechat-v-ekaterinburge.store/</a>
<a href=https://megaremont.pro/msk-restavratsiya-vann>restoration of bath enamel</a>
cialis cost per pill <a href="https://lifecialis20mg.com/">what is cialis</a> price of cialis
<a href=https://livedcasinoonline.com/>casino games</a>
<a href="https://livedcasinoonline.com/">online casinos</a>
<a href=https://gaminonlinecasino.com/>casino</a>
<a href="https://gaminonlinecasino.com/">casinos</a>
do erectile pills permanently increase size <a href=https://challonge.com/afersparun#>cheap ed drugs </a>
coupons for erectile dysfunction <a href="https://aoc.stamford.edu/profile/plumerinput/#">help with erectile dysfunction </a>
erectile aliments https://aoc.stamford.edu/profile/plumerinput/
sex videos
erectile supplements for men <a href=https://wallsawadar.zombeek.cz/#>erectile problems </a>
top erectile dysfunction supplements <a href="https://wallsawadar.zombeek.cz/#">erectile band </a>
is erectile dysfunction reversible https://www.provenexpert.com/best-erectile-pills/
Pills information. What side effects can this medication cause? <a href="http://inpharmacy.org/# ">how to buy viagra online safely in india</a> Verified message wide drugs. Presume from information now.
<a href=https://chimmed.ru/>празиквантел </a>
Tegs: ивермектин купить https://chimmed.ru/
<u>бензоат натрия купить </u>
<i>аргинин аминокислота </i>
<b>гидрохинон купить </b>
I with you do not agree
https://thetranny.com/search/latino-twinks/
https://yetiskinpornolar.com
erectile on demand scam <a href=https://pinshape.com/users/2517016-cheap-ed-drugs#>erectile with long time </a>
erectile surgery <a href="https://challonge.com/afersparun#">erectile pills </a>
erectile doctors https://www.provenexpert.com/best-erectile-pills/
How long does it take for blood pressure to go down <a href="https://lasixotc.com/ ">what does furosemide treat</a>?
erectile ointment <a href=https://wallsawadar.zombeek.cz/#>erectile enhancement pills </a>
acupuncture for erectile <a href="https://www.provenexpert.com/best-erectile-pills/#">herbs for erectile dysfunction </a>
erectile tissue location https://plancaticam.estranky.cz/clanky/best-drugs-for-ed.html
Hello, i read your blog occasionally and i own a similar one and i was just curious if you get a lot of spam remarks? If so how do you stop it, any plugin or anything you can advise? I get so much lately it's driving me crazy so any help is very much appreciated.
If you have any suggestions or tips for my new blog https://indigorosee.com/2021/01/24/how-to-prepare-for-a-successful-semester/ - printable monthly calendars please share!
<b><a href=https://japanese.massage-manhattan-club.com>japanese massage nyc</a></b>
Аccording t᧐ Wikipedia, Massage started t᧐ become popular in the United States іn the middle part of the 19th century аnd was introduced by tᴡo Νew York physicians, George ɑnd Charles Taylor, based ⲟn Per Henrik Ling’s techniques developed іn Sweden.
Outfisysheprerronrex
http://darwinreconsidered.org/soplftwum
http://ecranbleu.fr/otgggfgbz
http://evropol.xyz/dmhqyfjqs
http://lamiseauverreperpignan.fr/ajvxjgkhj
http://vmireforex.ru/ogbuyzgbw
http://chateaudegaujac.fr/dvseelazj
http://dessinportrait-cynyem.fr/hfzdcolmf
http://menuisier-philip-queyras.fr/qnizhfgqb
Взгляните на это <a href=https://skladchina.vip/>https://skladchina.vip/</a>
Q: Is Thicker sperm stronger?
A: <a href="https://sildenafilhim.com/#">pills like viagra over the counter</a> Superb what you in need of to be versed about medicine. Succeed to tidings now.
Innumerable cases of it respond effectively to lifestyle changes, medications, surgery, or other treatments. Even if your efforts to freebie behaviour towards ED are unsuccessful, you and your team-mate can still benefit real intimacy and a satisfying sexual life. https://sildenafilhim.com
<a href=https://casinoongames.us/>casinos</a>
<a href="https://casinoongames.us/">casino game</a>
<a href=https://casinotoonline.us/>casinos online</a>
<a href="https://casinotoonline.us/">online casino</a>
Таблетки для мужской потенции, женские возбудители, препараты для продления секса, лубриканты и смазки по лучшим ценам в Киеве
Гарантия высокого качества и результата!
Наш сайт - https://viagra911.com.ua/
pharmacy online no prescription <a href=https://canadianpharmaceuticalsonline.doorblog.jp/archives/19385382.html#>apollo pharmacy online </a>
canadian pharmacies-24h <a href="https://canadianpharmaceuticalsonline.studio.site/#">canadian pharmaceuticals online </a>
canada pharmaceuticals online generic https://canadianpharmaceuticalsonline.blogism.jp/archives/17866152.html
<a href=https://seora.ru>продвижение сайтов</a>}
Vitamin B3, also known as niacin, facilitates many functions in the body. It aids in converting enzymes to animation, vital repayment for attractive in robust procreative activities. Additionally, Vitamin B3 helps benefit blood flow, making in return stronger erections.
Source: <a href="https://clspls.com/ ">sildenafil vs cialis</a>
<a href=https://prostitutki-moskvy-top.ru/>https://prostitutki-moskvy-top.ru/</a>
viagra without prescription <a href="https://rxviagratable.com/">viagra pills</a> sildenafil generic
Создание сайтов в сочи https://sochi.cat <a href=https://sochi.cat>Создание сайтов в сочи</a>
SEO 2023
<a href=https://blog9t.blogspot.com>blog9t</a>
vardenafil online kaufen <a href="https://armalevitra.org/">vardenafil cost</a> sildenafil vs tadalafil vs vardenafil
<a href=https://accounts.binance.com/ru/register?ref=25293193>How to liberated recrudescence from cryptocurrencies?</a> <a href=https://accounts.binance.com/ru/register?ref=25293193>Dissimilar people are interested in earning on cryptocurrency.</a>
<a href="https://www.candipharm.com/
">https://www.candipharm.com/</a>
<a href="http://www.candipharm.com/#
">candipharm com</a>
vardenafil vilitra <a href="https://levitravardenafilmsko.com/">levitra canadian</a> vardenafil dose generic
<a href=https://chimmed.ru/>холин хлорид </a>
Tegs: рефрактометр для сахара https://chimmed.ru/
<u>метиленовый синий купить в спб </u>
<i>сульфат ртути </i>
<b>ohaus </b>
очень интересно, но ничего толкового
_________________
olimpbet промокоды 2022 - <a href=https://kk.realtopmoneygames.xyz/>ойын автоматтары</a>, vk olimpbet
телефон вывода из запоя круглосуточно <a href=https://alcoholunet.ru/>https://alcoholunet.ru/</a>
At Jackpotbetonline.com We bring you latest Gambling News, Casino Bonuses and offers from Top Operators, <a href=https://www.jackpotbetonline.com/>Online Casino</a> Slots Tips, Sports Betting Tips, odds etc.
I congratulate, it seems brilliant idea to me is
https://gay0day.com/
https://thetranny.com/search/hands-free-pov/
<a href="https://code-herb.com/">kornilova iherb promo code</a>
3д печать в Екатеринбурге <a href=https://3d-pechat96.ru/>https://3d-pechat96.ru/</a>
acid stomach remedy <a href= > https://www.jotform.com/223292431286051 </a> health care payments <a href= https://www.jotform.com/223361522557050 > https://www.jotform.com/223361522557050 </a> prescription sport glasses
Просим узнать информацию на тему <a href=https://еда.online>еда онлайн</a> если хотите сытости .
Показ запуска аппарата для окраски Аспро-2700. Сбор, запуск и настройка окрасочного аппарата. Как пользоваться краскопультом, мыть и хранить его. Полный цикл использования безвоздушного краскопульта от распаковки до консервации и хранения на примере аппарата АСПРО 2700
<a href=https://www.youtube.com/watch?v=oduHz8ZQ5Vg&t=1s>окрасочный аппарат aspro цена</a>
<a href=https://spb-service-center-remont.ru/asus/>https://spb-service-center-remont.ru/asus/</a>
<a href=https://megaremont.pro/kaliningrad-restavratsiya-vann>bath repair</a>
cialis temps de reaction <a href="https://tadalafilcialisacheter.com/">tadalafil lilly 5 mg</a> cialis eureka sante
<a href=https://chimmed.ru/about>mettler toledo </a>
Tegs: рефрактометры https://chimmed.ru/products/laboratory_equipment?group=%D0%A0%D0%B5%D1%84%D1%80%D0%B0%D0%BA%D1%82%D0%BE%D0%BC%D0%B5%D1%82%D1%80%D1%8B
<u>сахарин натрия </u>
<i>l фенилаланин </i>
<b>атомно абсорбционный спектрофотометр </b>
Pills information. Brand names.
https://avodart24.top/ buy avodart online in canada
Best message far medication. Get here.
What are intimate touches and https://flagylpls.com/ flagyl 250 mg and alcohol
<a href=https://kvarcvinil1.ru/>массивная доска</a>
<a href=https://www.kvarcvinil1.ru>http://kvarcvinil1.ru</a>
<a href=http://www.artvps.com/?URL=kvarcvinil1.ru>http://google.com.tr/url?q=http://kvarcvinil1.ru</a>
https://onlinecampus.lk/activity/p/20656/ Casino games konami https://assessment.bitm.org.bd/activity/p/79729/ Top 10 real online bitcoin casino https://gamemansion.com/activity/p/20235/ Free spin ros Tipa43ckdk!wdwe
https://harphr.com/activity/p/302901/ Uk free spins no deposit 2022 https://www.misbournevalley.co.uk/forum/tv-film-forum/play-online-games-for-bitcoins Play online games for bitcoins https://www.toukanews.com/forum/general-discussion/free-bitcoin-slots-for-fun-with-bonus-games Free bitcoin slots for fun with bonus games Tipa43ckdk!wdwe
http://flowersweb.info/bitrix/redirect.php?goto=https://wallob.com/groups/create/step/forum/ Казино вулкан гранд на демо рахунках https://www.communitybonfire.com/forum/general-discussions/shemi-kazino-pari-match-telegram-ukrayina Схеми казино парі матч телеграм україна https://www.bethtzedec.tv/forum/welcome-to-the-forum/kazino-sochi Казино сочи 4DSaawt25ssvggss
http://www.crucialfilm.com/__media__/js/netsoltrademark.php?d=https://www.aniassi.com/forum/beauty-forum/bwin-casino-offer Bwin casino offer https://www.siloeswoodworks.com/forum/diy-forum/igri-kazino-panther-moon Ігри казіно Panther Moon https://www.kitchenofrakhi.com/forum/fusions/stavka-na-slot-dzhoker Ставка на слот джокер 4DSaawt25ssvggss
It is remarkable, very useful piece
-------
spain virtual number sms <a href="https://virtual-local-numbers.com/countries/6-spain.html">continent telecom</a>
http://truesdelltec.com/__media__/js/netsoltrademark.php?d=https://www.thelunaticsfringe.tv/forum/get-started-with-your-forum/yak-grati-v-avtomati-shchob-vigrati Як грати в автомати щоб виграти https://www.rummelalumni.com/forum/general-discussions/slotclub-casino Slotclub casino https://www.reseauinternationalparlafoi.com/forum/welcome-to-the-forum/onlayn-kazino-na-grivny Онлайн казино на гривны 4DSaawt25ssvggss
https://www.lespepitesasso.fr/forum/welcome-to-the-forum/win-real-money-app-games Win real money app games https://www.incontrol-able.co.uk/forum/welcome-to-the-forum/casino-city-s-global-gaming-almanac Casino city's global gaming almanac https://www.retrostashcollective.com/forum/interior-design-forum/paper-mario-ttyd-slot-machine Paper mario ttyd slot machine Tipa43ckdk!wdwe
http://akcent-pro.com/bitrix/click.php?goto=https://www.dv8thc.com/forum/ask-us-anything/kazino-h-ukraina Казино С… украина https://www.hiddenbridgegolf.com/forum/general-discussions/pin-up-casino-app Pin up casino app https://www.staystrongosteo.com.au/forum/medical-forum/internet-kazino-v-rossii Рнтернет казино РІ СЂРѕСЃСЃРёРё 4DSaawt25ssvggss
http://parklinks.org/__media__/js/netsoltrademark.php?d=https://www.biztalkwithyou.com/forum/general-discussion/kazino-marvel Казино marvel https://www.d72reunion.com/forum/welcome-to-the-forum/vegas-paradise-casino-review Vegas paradise casino review https://www.rv2share.com/forum/welcome-to-the-forum/robert-600-funtiv Роберт 600 фунтів 4DSaawt25ssvggss
<a href=https://chimmed.ru/>m sartorius </a>
Tegs: бмб https://chimmed.ru/
<u>bruker </u>
<i>олеиновая кислота купить </i>
<b>спектрофотометр купить </b>
https://www.intrec.net/forum/general-discussions/hit-perla-casino-poker Hit perla casino poker https://www.andshethrived.com/forum/general-discussions/online-interview-time-slots-sign-up Online interview time slots sign up https://assessment.bitm.org.bd/activity/p/77206/ Hit it rich casino slots coins hack Tipa43ckdk!wdwe
http://vsyaupakovka.ru/bitrix/rk.php?goto=https://www.lrsolutions.biz/forum/business-forum/pin-up-casino-yukle Pin up casino yukle https://www.thefarm.cool/forum/welcome-to-the-forum/bezplaten-kazino-bonus-bez-depozitu Безплатен казино бонус без депозиту https://www.landmarksdesign.com/forum/general-discussions/rox-casino-95 Rox casino 95 4DSaawt25ssvggss
<a href=https://кровля-купить.рф>Купить металлочерепицу в Коломне</a>
https://dev-westudy.accedo.gr/activity/p/364687/ New computer casino games https://www.betteroffjapan.com/forum/meinhuoramu/bitcoin-casino-x-bonus-kod-2022 Bitcoin casino x Р±РѕРЅСѓСЃ РєРѕРґ 2022 https://www.namucoin.com/forum/gesipane-osin-geoseul-hwanyeonghabnida/real-live-slot-games Real live slot games Tipa43ckdk!wdwe
viagra pharmacy 100mg <a href=https://hub.docker.com/r/canadadiscountdrug/pharmaceuticals#>pharmacy online shopping </a>
canada pharmaceuticals online <a href="https://experiment.com/users/canadiandrugs/#">canadian online pharmacy </a>
shoppers pharmacy https://pharmacy-online.teachable.com/
https://wisdomvision.com/activity/p/158646/ Spin super io https://www.beenicole.net/forum/beauty-forum/win-storm-slot-machine-at-pala-casino Win storm slot machine at pala casino https://www.arkhedesignn.com/forum/foruma-hos-geldiniz/online-bitcoin-roulette-euro Online bitcoin roulette euro Tipa43ckdk!wdwe
https://www.humaniuminsurer.com/forum/discussions-generales/million-pennies-slot-machine Million pennies slot machine https://www.chattanoogaequine.com/forum/horse-care/are-soda-drinks-free-at-choctaw-casino Are soda drinks free at choctaw casino https://app.filseka.net/activity/p/692873/ Epic free bitcoin casino games Tipa43ckdk!wdwe
Stay on top of latest News developments with <a href=https://www.aljazeeranewstoday.com>Al Jazeera News Today</a> fact-based news
https://www.coffeewizards.co.uk/forum/welcome-to-the-forum/best-slots-at-lumiere-casino Best slots at lumiere casino https://www.indoslf.com/forum/business-forum/how-are-video-slots-games-of-skill How are video slots games of skill https://www.di-designs.com/forum/welcome-to-the-forum/holland-casino-online-gokkasten Holland casino online gokkasten Tipa43ckdk!wdwe
https://www.prodigiousthreads.com/forum/fashion-forum/ute-mountain-bitcoin-casino-bitcoin-slot-machines Ute mountain bitcoin casino bitcoin slot machines https://www.irooschool.net/forum/yt-ulrimbang/crypto-casino-bet-spider Crypto casino bet spider https://new.creativecampus.co.uk/groups/create/step/forum/ Best slot machine pc games Tipa43ckdk!wdwe
There are two chambers that run the length of your penis called the corpora cavernosa. Each contains a intricacy of blood vessels that sire sponge-like spaces. When those blood vessels put one's feet up and unscheduled, blood rushes into done with and fills them, causing the penis to engorge, creating an erection. https://sibluevi.com/ viagra pills
The <a href=https://www.nytimesnewstoday.com>NY Times News Today</a> for coverage of international news, politics, business, technology, science, health, arts, sports and more.
Приглашаем посмотреть информацию на тему <a href=https://торты.online>онлайн торты</a> если ищите насыщение .
Profuse cases of it respond warmly to lifestyle changes, medications, surgery, or other treatments. Even if your efforts to care for ED are unfortunate, you and your fellow can stillness use bones intimacy and a gratifying physical life.
Source: <a href="https://clspls.com/ ">is there a generic cialis</a>
Drug information for patients
<a href="https://propecia24.top/ ">where can i buy propecia in canada</a>
Paramount apropos meds. Fall ill word here.
pharmacy drugstore online <a href=https://app.roll20.net/users/11413335/canadian-pharmaceuticals-online-shipping#>online pharmacy canada </a>
national pharmacies online <a href="https://forum.melanoma.org/user/canadadrugsonline/profile/#">pharmacies </a>
canadian drugs online pharmacy https://forum.melanoma.org/user/canadadrugsonline/profile/
What is the safe dosage of prednisone https://symbicortinhaler.com/ budesonide formoterol
Why do hospitals push palliative care <a href="https://lasixotc.com/ ">generic for lasix</a>?
Pills prescribing information. Cautions. <a href="https://levitraoffer.com/ ">levitra without prescription</a> Best what you requisite to certain around medication. Deliver assign to info now.
услуги 3D печати - <a href=https://3d-pechat96.ru/>https://3d-pechat96.ru/</a>
women viagra <a href="https://viagrarab.org/">compro viagra</a> roman viagra
Приветик всем !
Случилось что, я сейчас без работы.
Жизнь продолжается, нужны деньги, подружка советовала поискать временный заработок в инете.
Ищу информации куча, а если не знаешь, что выбрать, как разобраться?
Вот выбрала несколько сайтов: <a href=https://female-ru.ru/>вот здесь</a> Вот еще нескоько <a href=https://female-ru.ru/>здесь</a>.
Напишите очень жду, что делать не знаю спасибо
https://colab.research.google.com/drive/1Yp2vGngIdkyNHQ_bu4CaW4sUtka9Y_rY
https://colab.research.google.com/drive/1vdkqvrMv31387ojwCKbo9TX5vlBOqyKO
<a href=https://внж-сочи.рф> вид на жительство сочи</a> https://xn----ctbmjwiu3c.xn--p1ai/ <a href=https://evakuatoradler.ru/> эвакуатор адлер </a> <a href=https://sochi.cat/> создание сайтов в сочи </a> <a href=https://xn-----7kckfgrgcq0a5b7an9n.xn--p1ai/> раки сочи </a> <a href=https://raki-sochi.com/> раки Сочи- доставка раков сочи </a> <a href=https://sochi-dostavka.com/> доставка еды сочи </a> <a href=https://panorama-sochi.com/> ресторан сочи </a>
herbal supplement stores <a href= > http://www.diabetesfit.org/zolde.html </a> doctor health care <a href= http://www.diabetesfit.org/zolde.html > http://www.diabetesfit.org/zolde.html </a> drug test.com
Medication dope in return patients. Cautions https://pharmduck.com/ canada drugs generic
<a href=https://oplata-servisov.ru>оплатить freepik</a>
<a href=https://chimmed.ru/products/search?name=%D1%85%D0%BB%D0%BE%D1%80%D0%BE%D1%84%D0%BE%D1%80%D0%BC>хлороформ купить </a>
Tegs: моксидектин https://chimmed.ru/products/moksidektin-id=1511012
<u>спермидин </u>
<i>анализаторы молока </i>
<b>циперметрин купить </b>
https://colab.research.google.com/drive/1c5gThRuN5lBuqLLoG9kGLab_58szrMyN?usp=sharing
https://colab.research.google.com/drive/1fP6RMnG6EbGb7Hld-Dh_2k1jTQ-GvwXN?usp=sharing
https://colab.research.google.com/drive/1J7OVR-0wsWUVma8f6SuOGs-mKEwzs0w2?usp=sharing
https://colab.research.google.com/drive/1Ydo7wlR3yUHa4PIUqLGbd2MabF-vUAa0?usp=sharing
https://colab.research.google.com/drive/1pH5bXr6oF7C5WIuE4rN54x9TSMdWi2ED?usp=sharing
Although ED and aging are unequivocally associated, turning 65 doesn't demand to using that your relations mortal has to suffer. Nearby maintaining the absolute habits, focusing on nourishing living and using science-based medications concerning ED, it's achievable to receive uncompromising erections and fight for an hyperactive sex being evidently into your 60s and 70s.
Source: <a href="https://clspls.com/ ">viagra cialis</a>
<a href=https://yourdesires.ru/finance/private-finance/74-bankovskie-karty-instrukciya-po-primeneniyu.html>Банковские карты: инструкция по применению</a> или <a href=https://yourdesires.ru/home-and-family/cookery/1683-botulizm-kak-ego-raspoznat.html>Ботулизм – как его распознать</a>
https://yourdesires.ru/home-and-family/house-and-home/34-dizayn-malenkoy-kuhni.html
Кино новинки онлайн https://filmi-novinki.top/
We submit the required documents and the application to the government department dealing with the citizenship or residence permit by investment program on behalf of our clients. The government department starts its Due Diligence check when the applicant pays the Due Diligence fee. All family members over the age of 16 included in the application have to undergo this check.
<a href=https://globalcitizenshipsolution.com/>nylon dildo porn</a>
buy generic 100mg viagra online <a href="https://enbossviagra.com/">sildenafil over the counter</a> viagra fuck
Hottest <a href=https://goo.su/D06Y28>Granny Porn</a> for FREE!
Medicament tidings leaflet. Effects of Dull Abuse. <a href="https://sildenafil.beauty/ ">sildenafil india pharmacy</a>
Hi, I'm completely new here
I am just want to share a good resource for Best Crypto Signals. this signal provider is authentic and I worked with them .
<a href=https://signalforall.com/>crypto signals free</a>
Использование ППЗУ в электронике <a href=http://prog.regionsv.ru/>prog.regionsv.ru</a>
<a href=http://prog.regionsv.ru/stat.htm>История создания и развития ППЗУ</a>
Музей электронных компонентов, <a href=http://rdk.regionsv.ru/muzeum.htm>виртуальный музей микросхем и полупроводников</a>
Купить химию для <a href=http://regionsv.ru>для очистки печатных плат в ультразвуке</a>
Характеристики <a href=http://prog.regionsv.ru/dateshit.htm>микросхем ППЗУ, даташит</a>
{<a href=https://gosavto-znak.store>Дубликаты госномеров</a>
Бери и повторяй, заработок от 50 000 рублей. https://vk.com/zarabotok_v_internete_dlya_mam
Hi to all, the contents present at this web site are really awesome for people experience, well, keep up the nice work fellows.
If you have any recommendations or tips for my new blog <a href=https://indigorosee.com/2021/01/24/how-to-prepare-for-a-successful-semester/>printable monthly calendars</a> please share!
canadian viagra generic pharmacy <a href=https://en.gravatar.com/kqwsh#>online pharmacy </a>
mexican pharmacies <a href="https://www.provenexpert.com/canadian-pharmacy-viagra-generic2/#">international pharmacy </a>
canadian pharmacy generic viagra https://pharmacy-online.teachable.com/
Всем привет!
Случилось что, я сейчас в поиске работы.
Жить надо, нужны деньги, подружка советовала искать заработок в инете.
Пишут все красиво, а если бы знать что делать, как разобраться?
Вот выбрала несколько сайтов: <a href=https://female-ru.ru/>вот здесь</a> Вот еще нескоько <a href=https://female-ru.ru/>здесь</a>.
Пишите жду, что делать не знаю всем кто прочитал спасибо за помощь
https://telegra.ph/Sexy-Nackte-Fraun-11-01
sildenafil 100mg <a href="https://goosviagra.com/">sildenafil citrate 50mg</a> viagra online canada
Hеllо!
Ι apоlоgizе for the ovеrly speсіfіс mеѕsagе.
Му girlfrіend аnd Ι lovе each оthеr. Αnd we аrе all grеat.
Βut... we nееd a mаn.
Ԝе are 24 уеаrs old, from Romanіа, wе аlѕo knоw еnglіsh.
Wе nеvеr gеt bоred! Аnd not only in talk...
Μу nаme іs Iѕabellа, my profіlе is hеre: http://kyacamum.tk/item-43628/
Бесплатно удалим катализатор с вашего авто за 2 часа и произведем все сопутствующие работы.
Произведем переустановку программного обеспечения под евро 2, установим пламегасители и стронгеры по проверенным технологиям !
<a href=https://kat-service56.ru/>удалить катализатор с прошивкой пламегаситель</a>
<a href=https://livedcasinoonline.com/>casino real money</a>
<a href="https://livedcasinoonline.com/">casino</a>
<a href=https://gaminonlinecasino.com/>online casino</a>
<a href="https://gaminonlinecasino.com/">online casinos</a>
<a href=https://casinogambiba.com/>casinos</a>
<a href="https://casinogambiba.com/">online casinos</a>
<a href=https://gaminonlinecasino.com/>casino games</a>
<a href="https://gaminonlinecasino.com/">gambling</a>
sildenafil overnight shipping usa <a href="https://sildenafil.work/ ">sildenafil prices in india</a>
gabapentin restless legs <a href="https://gabapentined.net/">generic gabapentin</a> gabapentin effects on brain
<a href=https://accounts.binance.com/ru/register?ref=25293193>Separate people are interested in earning on cryptocurrency.</a>
pharmacy online prescription <a href=https://app.roll20.net/users/11413335/canadian-pharmaceuticals-online-shipping#>canadian drugs </a>
london drugs canada <a href="https://bitbucket.org/canadianpharmaceuticalsonline/workspace/snippets/k7KRy4#">canada pharmaceuticals online </a>
cheap pharmacy online https://rabbitroom.com/members/onlinepharmacydrugstore/profile/
Бонусы казино https://24casi.com/ за регистрацию с выводом, список рейтинг
средство вывода из запоя <a href=https://stopzapoymos.ru/>https://stopzapoymos.ru/</a>
สล็อต เว็บ ตรง
Hello there! This is my first visit to your blog! We are a group of volunteers and starting a new
initiative in a community in the same niche.
Your blog provided us beneficial information to work on. You have
done a outstanding job!
plaquenil for lupus <a href="https://plaquenil.wiki/ ">hydroxychloroquine</a> malaria pills over the counter
online casino news <a href="https://casinoonlinebeton.com/">betfred online casino</a> golden nugget online casino nj
online casino real money no deposit usa <a href="https://onlinecasinokosmo.org/">virgin casino online nj</a> zone online casino msn games
<a href=http://kinologiyasaratov.ru/plemdog.htm>Кинологические услуги</a>
<a href=http://kinologiyasaratov.ru/plemdog.htm>Купить щенка немецкой овчарки с родословной</a>
<a href=http://prog.regionsv.ru/stat-ingl.htm>Какие бывают ПЗУ СССР - статья на английском</a>
<a href=http://prog.regionsv.ru/links.htm>Интересные полезные ссылки</a>
<a href=https://lev-casinosi.xyz/>https://lev-casinosi.xyz/</a>
<a href=https://5-bukv.ru/>игра 5 букв тинькофф</a>
<a href=https://5-bukv.ru/>5 слов тинькофф ответы</a>
<a href=https://5-bukv.ru/>слово из 5 букв</a>
<a href=https://5-bukv.ru/>пять букв тинькофф</a>
<a href=https://5-bukv.ru/>5 букв игра тинькофф</a>
https://telegra.ph/Top-casinos-online-australia-01-08#Top casinos online australia
https://telegra.ph/Abzorba-live-roulette-mod-apk-01-08#Abzorba live roulette mod apk
https://telegra.ph/Best-ontario-casinos-online-01-08#Best ontario casinos online
https://telegra.ph/Casino-online-konabet-01-08#Casino online konabet
https://telegra.ph/How-to-win-a-live-poker-tournament-01-08#How to win a live poker tournament
https://www.masteryx.ru/sadogorod/73-grjadka1.html
Hey, I'm new here
I am just want to share a specific source for futures signals. this website is good and I worked with them .
<a href=https://signalforall.com/>crypto futures trading signals</a>
очень хорошо
_________________
bukmekerning yangi veb-sayti - <a href=http://uzb.bkinf0-456.site/121.html>qanday qilib onlayn kazinolarda pul ishladim</a> / cheboksariyada qanday bukmekerlar bor
Find latest news about <a href=https://www.alljackpotbetreview.com><b>Online Casino</b></a>, New Slots Games and latest Sports Betting trends here At Alljackpotbetreview.com.
loli*ta gi*rl fu*ck c*p pt*hc
yal.su/jCs
s.yjm.pl/BbtC
tw.uy/tw11l
hydroxychloroquine doctor, <a href="https://plaquenil.beauty/ ">plaquenil manufacturer</a> hydroxychloroquine 200 mg tab.
выгодный обменник <a href=https://top-obmeny-kriptovalyut.com/>https://top-obmeny-kriptovalyut.com/</a>
Mianadoireacht ar Windows no ar Hive OS, a bhfuil nios fearr: <a href=>https://clck.ru/33DtzA</a>
<a href=https://clck.ru/33DtzA><img src="https://external-fra5-2.xx.fbcdn.net/emg1/v/t13/10212597292937425208?url=https%3A%2F%2Flbd.hiveos.farm%2Fhiveon-site%2Fstatic%2Fhiveon_main_en.jpg&fb_obo=1&utld=hiveos.farm&stp=c0.5000x0.5000f_dst-jpg_flffffff_p500x261_q75&ccb=13-1&oh=06_AbFlhf8NyCPiSOLrcj3Go6CTeqrD0kdkMs7Tii2e2nORXg&oe=63BDAB3C&_nc_sid=b1eadf"></a>
На Вашем месте я бы так не делал.
<a href=https://kapelki-firefit.ru/>kapelki-firefit.ru</a> действуют, но не так прекрасно, каким образом хотелось бы.
<a href=https://syzygyjob.net/>Купить права на спецтехнику</a>
caesars online casino app <a href="https://myonlinecasinotop.com/">casino war online</a> virgin online casino
That means you'll get the idea some new features and have access to additional channels where you can forward movement visibility, without having to modify sense of some complicated, handbook migration process. https://googlec5.com
Это действительно удивляет.
в котором приобрести <a href=https://kapelki-firefit.ru/>kapelki-firefit.ru</a> по цене со скидкой?
Быстровозводимое ангары от производителя: <a href=http://bystrovozvodimye-zdanija.ru/>https://bystrovozvodimye-zdanija.ru/</a> - строительство в короткие сроки по минимальной цене с вводов в эксплуатацию!
<a href=http://google.com.pe/url?q=http://bystrovozvodimye-zdanija-moskva.ru>http://google.com.pe/url?q=http://bystrovozvodimye-zdanija-moskva.ru</a>
Всем привет!
Случилось что, я потеряла работу.
Жить надо, денежки очень нужны, подружка советовала искать заработок в инете.
Ищу пишут многое, а если нет опыта, в голове каша, не могу сообразить?
Вот выбрала несколько сайтов: <a href=https://female-ru.ru/>вот здесь</a> Вот еще нескоько <a href=https://female-ru.ru/>здесь</a>.
Пишите жду, что делать не знаю спасибо
https://smp-stroi.ru/welcome-bonus-games-welcome-bonus-casino-online/ Welcome bonus games https://www.myfatherisdope.com/forum/community-content/hors-slontt-kii-aankh होरस स्लॉट की आंख https://faredplatform.com/%d8%a7%d9%84%d9%85%d9%86%d8%aa%d8%af%d9%89/profile/forocasinoin11498468/ Tigers Gold स्लॉट मशीन Ae7ds3qqalLk
This is the first time you can make money so easily.
https://www.litefinance.org/ru/?uid=715509006&cid=27212 - Click here!..
мне не надо такого добра!
в то же время улучшается состояньице кожных покровов, ликвидируются прыщики, угри, уходит рыхлость, <a href=https://kapelki-firefit.ru/>https://kapelki-firefit.ru/</a> повышается тургор.
<a href=https://gosavto-znak.store>Дубликаты номеров жирным шрифтом</a>
https://robotex.ee/foorum/profile/forocasinoin5324122/ शर्त पोकर https://tendenciamotorblog.com/foros//profile/forocasinoin23231717/ First Person Blackjack बिटकॉइन लाइव रूले https://www.mohsensbarbers.co.uk/forum/general-discussions/baccarat-hmen-kaisiino-shrt-lgaao Baccarat हमें कैसीनो शर्त लगाओ Ae7ds3qqalLk
<b><a href=https://exotic.massage-manhattan-club.com>exotic massage parlour</a></b>
О™f КЏou're shopping for Р° high-end foot massager, you're lС–kely to come acРіoss sОїme units that feature purportedly therapeutic lights, Ж„ut take these claims witТ» a grain of salt.
Веб-студия SOCHI.CAT создание сайтов в Сочи, разработка мобильных приложений https://sochi.cat <a href=https://sochi.cat>Создание сайтов в Сочи</a>
Web3 Jobs: Top Web3 Blockchain, Smart Contract and Crypto Jobs:
https://ppsc-exam26925.ivasdesign.com/37677056/numerous-developers-are-previously-advancing-into-a-profession-in-web3
Да,хорошо. Кладу 5.
<a href=https://kapelki-firefit.ru/>kapelki-firefit.ru</a> для меня отличный партнер быстрого ухода лишних килограммов.
We give your project a firm foundation with a pre design consultation that will design with a quick service concept that doesn t feel like fast food
Commercial Kitchen Design amp Consultancy Services
Apr 10 2020 custom provides customers with professional food service consulting custom kitchen construction and installation restaurant floor plan kitchen
Blog Blitzer s Premium Frozen Yogurt - <a href=https://anotepad.com/notes/mgdhnnqh>juice bar contractor firm</a>
ventolin 4mg cost <a href="https://sway.office.com/ya7JDGSPeT1tH9le/">purchase albuterol pill</a> ventolin inhaler.
По моему мнению Вы ошибаетесь. Давайте обсудим это. Пишите мне в PM, пообщаемся.
в комплексе каждое компоненты обеспечивают результативность <a href=https://kapelki-firefit.ru/>kapelki-firefit.ru</a>, да что там отзывы реальных людей утверждают об этом.
video poker online <a href="https://onlinepokergamee.net/">poker games online</a> free online deuces wild video poker no download
Pills information. Long-Term Effects. <a href="https://gamespace.com/members/hydroxychloroquine/ ">hydroxychloroquine rheumatoid arthritis</a> how much is albuterol
If u want to activate your Windows 10 or Microsoft Office 2016. Then it can be done absolutely for free
<a href=https://internet-soft.info/kmspico-windows-10-download/windows-10-activator-download-kmspico.html>windows 10 activator download kmspico</a>
kmspico reddit 2021
kmspico i am leaving
ООООООООООООО!! Давно хотела посмотреть такое!!!!
<a href=https://kapelki-firefit.ru/>kapelki-firefit.ru</a> не испускают чтоб запомнилось выраженного вкуса либо аромата.
Hot new site <a href=https://bit.ly/3nCqGIo>Slut Anal Tube</a> present hardcore videos for free
lupus hydroxychloroquine <a href="https://hydroxychloroquine.homes/">buy hydroxychloroquine from india</a> plaquenil 200mg price.
Продажа китайских шин APLUS по дилерским ценам с доставкой до вашего склада.
Предложим хорошие условия сотрудничества https://chat.whatsapp.com/LkvatU9VSa54VYQfjidXqc
<img src="https://i.ibb.co/HDk7KkJ/S618.png"><img src="https://i.ibb.co/4JZbnFy/Aplus-D800.jpg"><img src="https://i.ibb.co/j4xwsps/Aplus-S618.jpg">
<a href=https://groups.google.com/g/myrbx>Free Robux Codes</a>
erectile smoothie <a href=https://plancaticam.estranky.cz/#>buy erectile dysfunction pills </a>
are erectile dysfunction not curable <a href="https://pinshape.com/users/2517016-cheap-ed-drugs#">buy erectile dysfunction medications online </a>
online doctor erectile dysfunction https://pinshape.com/users/2517016-cheap-ed-drugs
erectile remedies <a href=https://plancaticam.estranky.cz/#>ed drugs generic </a>
erectile photos <a href="https://challonge.com/afersparun#">erectile amazon </a>
erectile natural remedies https://500px.com/p/stofovinin/?view=groups
<a href=https://paperbracelets.kz>Одноразовые бумажные браслеты</a>
Бумажный браслет TYWEK(Тайвек) — инструмент для контроля несанкционированного доступа на мероприятия. Максимально удобен как для посетителя, так и для проверяющих.
<a href="https://b2book.ru/person/6035007/">https://b2book.ru/person/6035007/</a>
https://clck.ru/36EvZ9
Google Play Маркет — магазин приложений от Google, позволяющий владельцам устройств с Android устанавливать приложения <a href="https://download-playmarket.info">google play store скачать на русском бесплатно</a>
I recommend only this <a href=https://pugachev.miami/>exotic car rental Miami</a> site.
I recommend only this <a href=https://pugachev.miami/>exotic car rental Miami</a> site.
В Москве полицейские задержали мужчину, который нашел потерянный автомобилистом сверток с 1 млн рублей и решил оставить деньги себе. Об этом сообщает ГУ МВД России по столице.
<a href=https://bs2w-in.com>b2web.in </a>
В Пресненском районе на одной из парковок вдоль Мантулинской улицы житель столицы положил на крышу своего автомобиля конверт с 1 млн рублей, отвлекся на телефонный разговор, сел за руль и уехал. Упавший на проезжую часть сверток подобрал проходивший мимо мужчина.
SavdoUyi.uz - это онлайн-платформа, которая помогает людям находить работу, продавать и покупать товары и услуги <a href="https://savdouyi.uz/">Строительные материалы</a>
Заказать пластиковые окна из немецкого профиля VEKA. Выгодные цены и предложения на покупку и установку пластиковых ПВХ окон и дверей <a href="https://i-tubing.by/partners">окна пвх от производителя цены</a>
I recommend in <a href=https://pugachev.miami/>miami luxury car rental</a> site.
I recommend in <a href=https://pugachev.miami/>miami luxury car rental</a> site.
Купить нержавеющие трубы по доступным ценам за метр от производителя <a href="https://truby-nerzhaveyushie.ru/">купить готовые окна пвх для дачи</a> в Москве от производителя по низким ценам
Арбалет – это мощное оружие, позволяющее охотиться на различных животных с большой дистанции <a href="https://aben75.cafe24.com/bbs/board.php?bo_table=free&wr_id=165398">https://aben75.cafe24.com/bbs/board.php?bo_table=free&wr_id=165398</a>
складываются ситуации, когда теряют настоящий документ о высшем образовании, <a href=http://www.virtualbark.com/url/?out=//mosdiploms.com%2Fkupit-svidetelctvo-smerti%2F>http://www.virtualbark.com/url/?out=//mosdiploms.com%2Fkupit-svidetelctvo-smerti%2F</a> а на восстановление нужно масса денег или же Вуз теперь не существует.
the five paragraph essay examples <a href=https://essaydw.com/>get essay written</a> an essay on nature
how to write argument essay https://essaydw.com/ - essay proofreading service
радио тапок воеватьбилеты радио тапок <a href=https://www.magecam.ru/>https://www.magecam.ru/</a> радио тапок фотографиирадио тапок фамилия
<a href="https://manja.tunasukm.edu.my/profile/tropicex4otic/">weed delivery</a>
cialis pills online pharmacy farmacia online cialis paypal <a href="https://lloydspharmacytopss.com/">buy generic cialis online india</a> printable cialis coupon how much does cialis cost without insurance
cialis 20mg dosage how long does it take for cialis to work <a href="https://lloydspharmacytopss.com/">authentic cialis online</a> cialis online order canada generic cialis 20mg
3. сексуальные свидания. Некоторые эскортницы предоставляют потребителям сервис сексуального <a href=http://railagent.ru/club/user/105276/>http://railagent.ru/club/user/105276/</a> характера. Мир эскортниц в такой мере богат, что любой может отыскать именно то, когда ему следует.
Одни эскортницы могут быть универсальными и давать широкий набор предложений, включая секс, производителя на фестивалях и путешествиях, <a href=http://www.ecorukodelie.ru/2016/03/zakladki-s-gerbariem.html>http://www.ecorukodelie.ru/2016/03/zakladki-s-gerbariem.html</a> вступление в дело ролевых играх и другие разновидности ограждений.
Что лучше и дешевле выбрать в 2023 игровой ноутбук или игровой компьютер <a href="https://darwin.md/ru/aksessuary">мобильные аксессуары</a>
Thanks very useful. Will share website with my good friends.
https://www.google.com.nf/url?q=https://comprarcialis5mg.com
Je recommande cette très belle pochette <a href=https://killapods.eu/fr/product/pablo-dry-x-ice-cold/>Pablo Dry X Ice Cold</a>
This blog was extremely helpful. I am certainly going to
research it more. Thanks for the thoughtful article. For more related information, please,
check http://www.galacticsurf.com/redirect.htm?redir=https://ariston-master.ru/dukhovye-shkafy
<b>Шаврин Александр Валерьевич Алматы</b>
Many thanks, this website is very helpful.
Шаврин Александр Валерьевич Алматы
среднее срок подачи эвакуатора 20 <a href=http://teplitnsk.ru/product/shte-150-200r-diametr-50-mm/reviews/>http://teplitnsk.ru/product/shte-150-200r-diametr-50-mm/reviews/</a> мин. Смело доверяйте нам своё транспортное средство т.к. оно окажется абсолютно застраховано надолго эвакуации.
for Monopoly Go <a href="https://freedicelinks.com">free dice links</a> has become an integral part of the gaming narrative, bringing players together in a shared pursuit of success without financial constraints.
Hello, is it possible to advertise on your Website?
Our project is a news insider Telegram Channel.
We publish information that will not be shown on TV.
The situation in Ukraine will affect all countries of the world, and every person!
Please help us to spread the information, as people should know the truth!
Our Channel:
https://t.me/+DXiwwbTHse05OWRi
085598
paying a visit to this portal, you swear that have reached the age of majority in your city to study materials for adults and what you <a href=https://www.studistoricicuneo.org/2020/10/24/assemblea-sociale/>https://www.studistoricicuneo.org/2020/10/24/assemblea-sociale/</a> movies.
when should i take cialis for best results to buy cialis online <a href="https://lloydspharmacytopss.com/">cialis cost per pill</a> buy cialis mumbai buy generic cialis online europe
Стоимость услуг адвоката по уголовным, гражданским и административным делам <a href="https://etopfun.net/">услуги адвоката</a>
your choice applies to the use of your own and third-party advertising cookies on our resource <a href=https://wiki.celeti.com.br/index.php/Porn_mature_x-x-x.tube>https://wiki.celeti.com.br/index.php/Porn_mature_x-x-x.tube</a>.
Все виды судебных и досудебных экспертиз на сайте <a href="https://strah-urist.ru/uslugi/">независимая экспертиза квартиры</a> с гарантией низкой цены.
Take sugar and cheat on me as a as a gift! NEIGHBOR, <a href=https://thewillistree.info/genealogy/wiki/User:LaurenceGormanst>https://thewillistree.info/genealogy/wiki/User:LaurenceGormanst</a> forget about own boring wife!
John Belford one of the best <a href=https://exchanger24.org/john_belford/>crypto expert</a> in the World.
John Belford one of the best <a href=https://exchanger24.org/john_belford/>crypto expert</a> in the World.
each category, then you see in front of yourself, loaded with millions of free intimacy videos, which are loaded lightning fast and possess highest <a href=https://historydb.date/wiki/User:JacksonFavenc99>https://historydb.date/wiki/User:JacksonFavenc99</a> quality.
Очень полезная мысль
в фокусе города <a href=https://posutkamminsk.by/>posutkamminsk.by</a> 2-комнатная квартира. Сдаётся отличная уютная 1-комнатная жилье в час пик.
John Belford very respected <a href=https://exchanger24.org/john_belford/>cryptocurrency expert</a> in the World.
John Belford very respected <a href=https://exchanger24.org/john_belford/>cryptocurrency expert</a> in the World.
<a href="https://www.google.ae/url?q=https://didvirtualnumbers.com/zh/">https://www.google.ae/url?q=https://didvirtualnumbers.com/zh/</a>
from all others and indoor videos to professional porn sites from most|mostfamous famous porn studios <a href=https://wiki-site.win/index.php?title=Mix-xxx>https://wiki-site.win/index.php?title=Mix-xxx</a> in the world.
Я знаю, Вам здесь помогут найти верное решение.
thanks to what both parts have reached top goals and have not yet showing any signs of stopping <a href=https://www.skincounter.co.uk/product/skinceuticals-phloretin-cf/>https://www.skincounter.co.uk/product/skinceuticals-phloretin-cf/</a>.
Я извиняюсь, но, по-моему, Вы допускаете ошибку. Давайте обсудим это.
In <a href=http://ebiemme.it/index.php/component/k2/item/5-etiam-lacinia-aliquam-odio-ut-vestibulum>http://ebiemme.it/index.php/component/k2/item/5-etiam-lacinia-aliquam-odio-ut-vestibulum</a> with 2 quarters in one bottle, this talking about that the viewer choose 300 green in epoch - the same amount as gamer in blackjack worth $ 5 risks at an average game speed at the table in 50/40/60 hands in day.
Odbierz prezent <a href="https://polscekasyno.pl/bonusy-bez-depozytu/100-zl-w-kasynie-fontan/">100 zl bez depozytu</a>. Nowe zwyciestwa czekaja!
Now there is additional desire to displace as with a strap-on with only line: giantess, the best <a href=http://www.xn--119-938m08ioyr.com/bbs/board.php?bo_table=free&wr_id=82083>http://www.xn--119-938m08ioyr.com/bbs/board.php?bo_table=free&wr_id=82083</a> engine4sale all over the world.
real cialis online cialis generic online <a href="https://doctorrvipfox.com/">order cialis online</a> brand cialis 20mg online apotheke cialis ohne rezept
where can you buy cialis over the counter cialis off patent <a href="https://doctorrvipfox.com/">cialis 5mg price comparison</a> cialis free sample canada where to order cialis online
living in sexually positive communities able to make sexual exploration more cost-effective, <a href=http://www.bizmandu.com/redirect?url=https://feet-zone.com/>http://www.bizmandu.com/redirect?url=https://feet-zone.com/</a> potentially leads to appearance of fetishes, what make sex more vivid or enjoyable.
консультации юриста бесплатно для всех вопросов о праве|юридическая помощь без оплаты на юридические темы
бесплатная помощь юриста для частных лиц и компаний по различным вопросам законодательства от профессионалов|Получи бесплатное консультирование от квалифицированных юристов по наболевшим проблемам
Бесплатная юридическая консультация для детей
бесплатные юридические консультации в москве <a href=https://www.konsultaciya-yurista-499.ru/>https://www.konsultaciya-yurista-499.ru/</a>.
ООО «Евраз Автоматика» - это современное и динамично развивающееся электротехническое предприятие, обладающее внушительным научно производственным потенциалом.<a href=https://evraz.pro/catalog/nku/nku-dlya-upravleniya-elektrodvigatelyami-i-privodami/shuim/>Автоматизация насосов и насосных станций </a>
Основное направление деятельности компании – это производство продукции для распределения и учета электроэнергии, а также решение задач в области промышленной автоматизации.
Разовая чистка снега с крыш и абонентское обслуживание в зимний период <a href="https://proalp24.ru/services/ochistka-krovli">очистка крыш</a>
Этот вариант мне не подходит. Может, есть ещё варианты?
Рынок делят множество seo-компаний, маркетинговых агентств, веб-студий, онлайн-сайтов, которые продают увеличение органического трафика, продвижения ключевых слов, <a href=http://www7b.biglobe.ne.jp/%7Eeasy_trekker/cgi-bin/board_main/board_main.cgi>http://www7b.biglobe.ne.jp/%7Eeasy_trekker/cgi-bin/board_main/board_main.cgi</a> создания сюжетов и внешних ссылок.
своего добра хватает
the most serious of the leading reasons according to which people are attracted to these casinos is the anonymity that they give during gambling entertainment.<a href=https://earn-money-online.maggang.com/>https://earn-money-online.maggang.com/</a>
посмотрел и разочаровался..........
<a href=http://www.viviendavacacionalcasacarmen.es/librovisitas/index.php>http://www.viviendavacacionalcasacarmen.es/librovisitas/index.php</a>
metamorphosis essay <a href=https://essaydw.com/>scholarship with essay</a> apa essay heading
argument essay thesis https://essaydw.com/ - custom paper writing service
в коллекции слотов доступны ставки на больше всего востребованные направления и тематики в прематче идут топовые решения с популярными, <a href=https://vavadasite.win>vavada зеркало</a> против дилеров гемблеры могут устанавливать с реального счета в настольных тайтлах.
Тема Рулит
"42" est incontestablement, Jackie Robinson, citoyen qui a brise les barrieres de couleur dans le baseball: le premier joueur noir a jouer dans un match de Ligue Majeure, <a href=https://library.kemu.ac.ke/kemuwiki/index.php/User:Hai28K7472802>https://library.kemu.ac.ke/kemuwiki/index.php/User:Hai28K7472802</a> 15 avril 1947: Brooklyn Dodgers.
Демо игровые автоматы бесплатно здесь <a href=https://naglayamorda.ru/>Игровые автоматы</a>
<a href=https://gdevrachi.ru/>Игровые автоматы бесплатно</a>
<a href=https://sensus-ego.ru/>Игровые автоматы играть на деньги</a>
<a href=https://талантофф.рф/>Казино онлайн играть</a>
<a href=https://povaricha.ru/>Игровые автоматы бесплатно</a>
<a href=https://studio-klass.ru/>Казино слоты</a>
Жаль, что сейчас не могу высказаться - опаздываю на встречу. Освобожусь - обязательно выскажу своё мнение.
тут вы найдете особо важные происшествия, новости санкт-петербурга, последние <a href=http://yagiro.ru/profile/egiziju/>http://yagiro.ru/profile/egiziju/</a> российского рынка, а также происходящие события среди, культуре, искусстве.
Каждый человек имеет право на счастье. Путь этот непрост и тернист <a href="https://anyservice.ng/services/2405/emmabright">https://anyservice.ng/services/2405/emmabright</a>
Andrey Monosov had a long way to go to start his own business <a href="https://www.scoopearth.com/andrey-monosov-founder-and-ceo-of-it-company-ia-tech-biography-career-facts/">andrey monosov</a>
Сериал про космос - <a href=https://sg-video.ru/>сериал звездные врата</a>
巫毒教死亡仪式 - 来自强大的俄罗斯萨满的帮助 WhatsApp +79842861265 https://izard.ru - 爱情女神的仪式
死亡之书的仪式
<a href="https://izard.ru">https://izard.ru</a>
满月爱情仪式
爱的仪式女神
热爱魔法仪式
女孩爱情的仪式
爱情仪式
uTorrent - <a href="https://utorrent.bumtor.ru/">оценка земельного участка</a> один из самых популярных загрузчиков для скачивания торрентов на сегодняшний день.
давно хотел посматреть
<a href=https://learncryptocenter.com/knowhow/>https://learncryptocenter.com/knowhow/</a>
The firm where Leonid Monosov was employed was reputed as one of the top companies in the capital, <a href="https://www.exposedmagazine.co.uk/featured-articles/leonid-monosovs-biography/">leonid monosov</a> and was well-equipped to take on intricate projects that other contractors declined to undertake.
et essay om indre frihed <a href="https://growthbookmarks.com/story16021183/indicators-on-college-admission-essay-writing-service-you-should-know">https://growthbookmarks.com/story16021183/indicators-on-college-admission-essay-writing-service-you-should-know</a> sat essay writing tips
http instagram
http://icq.im/SMMshop/ru
Бесплатная помощь юриста при первом обращении
юрист консультация бесплатно по телефону круглосуточно <a href=https://www.lawyer-uslugi.ru>https://www.lawyer-uslugi.ru</a>.
Je recommande cette très belle pochette <a href=https://killapods.eu/fr/product/pablo-exclusive-bubblegum/>Pablo Exclusive Bubblegum</a>
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-banana-ice/]Pablo Exclusive Banana Ice[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-bubblegum/]Pablo Exclusive Bubblegum[/url]
Mostbet combines sports betting and gambling entertainment on one platform <a href="https://independent-dove-f6lh1x.mystrikingly.com/blog/mosbet-uz">https://independent-dove-f6lh1x.mystrikingly.com/blog/mosbet-uz</a>
Подскажите, где я могу об этом прочитать?
Ставка налоговой избыточной нагрузки на Мальте составляет 5%. Стоимость лицензии для онлайн казино суммарно обойдется в семнадцатом тысяч евро (4 за оформление заявки, 8,пяти долларам за сам сертификат, полутора за продление разрешения, [url=https://casinocrit.pro/]https://casinocrit.pro/[/url] плюс аудит составит около 3 тысячи).
Профессиональный честный сервис по ремонту ноутбуков <a href="https://windowss10.ru/instructions-and-tips/remont-kompyutera-vazhnye-polomki-kotorye-nelzya-proignorirovat.html">ремонт компьютеров</a> обратитесь в наш сервисный центр по ремонту компьютеров и ноутбуков.
I reccomend this site [url=https://ramenbeet.com/]Ramenbet[/url]to everyone.
I reccomend this site [url=https://ramenbeet.com/]Ramenbet[/url]to everyone.
Hello from Happykiddi.
Стройматериалы в наличии в интернет-магазине и розничных магазинах <a href="https://www.osb-3.ru/product/gidroizol/gidroshponki/">гидрошпонки купить</a> в Москве с доставкой.
В нашем каталоге Вы найдете широкий ассортимент лодок ПВХ, моторов и комплектующих: <a href="https://klevielodkiekb.ru/">надувной каяк</a>
имеет более двух тысяч игр казино и более 100 провайдеров. Игровые предложения: слоты, рулетка, карточные игры, покер, [url=http://nedv-revda.ru/index.php?subaction=userinfo&user=ykuxuhowe]http://nedv-revda.ru/index.php?subaction=userinfo&user=ykuxuhowe[/url] блекджек) колесо удачи.
interesting post
_________________
https://Bangladeshbetsapp.site
Да качество наверное не очень...смотреть не буду.
Дайте свой основной номер в порно-затеях объявлении, и студента замучают звонками а в окончании того, [url=https://chuyenweb.vn/product/giao-dien-website-am-thuc-chuyenweb-vn/]https://chuyenweb.vn/product/giao-dien-website-am-thuc-chuyenweb-vn/[/url] как студент продали так долго хотели.
Hі!
I've nоtісеd that many guуs prefer rеgulаr gіrls.
I aрplaudе the mеn оut therе who had thе balls tо еnjоy the lоve оf mаny womеn and сhoоse thе onе that hе knew wоuld be hiѕ bеѕt frіend during the bumpу and crаzу thing сalled lіfе.
Ι wаntеd to bе thаt friеnd, nоt ϳust a stаblе, rеliable аnd bоrіng housewіfe.
Ι аm 25 yeаrѕ old, Сatherіna, frоm thе Czесh Reрublіc, know Engliѕh lаnguаgе also.
Anywаy, уou саn find mу profіle herе: http://brildowncihealthjamo.ml/idl-17268/
Всем рекомендую классное [url=https://ramenbeet.com/]Раменбет[/url] казино.
Всем рекомендую классное [url=https://ramenbeet.com/]Раменбет[/url] казино.
Надувные лодки ПВХ по низкой цене купить в интернет магазине <a href="https://titanoutboards.ru/">сап каяк</a>
и такой нюанс - основная обстоятельство, [url=http://users.atw.hu/sajprobaoldalam/modules.php?name=Journal&file=display&jid=43574]http://users.atw.hu/sajprobaoldalam/modules.php?name=Journal&file=display&jid=43574[/url] согласно которой девушки согласны на то, чтобы это. деньги и время - вот что мне требовалось тогда.
Абсолютно не согласен с предыдущим сообщением
для аматорів: пізнавайте нюанси предмета з нуля. Послуги в підготовці домашки, пояснення пропущеного матеріалу, [url=https://www.ambitiousluxuryhair.com/product/3d-mink-lash-10/]https://www.ambitiousluxuryhair.com/product/3d-mink-lash-10/[/url] Підготовка до ВПР.
generic cialis walmart [url=https://cialisbag.com/]cialis pills for sale[/url] what are the ingredients in cialis
cialis package insert https://cialisbag.com/ - cialis 20mg tablets
Консультации по телефону
арбитражный цены услуги адвоката [url=https://advocate-uslugi.ru/]https://advocate-uslugi.ru/[/url].
Такой люди не может трудиться но одновременно полноценно уделять [url=https://davlenie.guru/kak-obespechit-pozhilomu-cheloveku-dolgosrochnyj-uhod.html]сиделки[/url] внимание ребенку. если вы не нанимали няню с функционалом домработницы, она не должна заниматься подобными вещами.
[url=https://borodaexp.com/]технічна підтримка сайтів[/url]
Всем рекомендую, очень крутая [url=https://tr-kazakhstan.kz/onlajn-igra-balloon-kz-princzip-igry-strategii-i-rekomendaczii/]баллон игра[/url].
Университетские студентки-эскортницы могут предложить различные разновидности услуг, [url=http://fh3809kd.bget.ru/index.php?name=account&op=info&uname=ahykud]http://fh3809kd.bget.ru/index.php?name=account&op=info&uname=ahykud[/url] исходя из потребностей заказчика. люди нередко приглашают их отправиться в прочие населенные пункты либо прямо на другие континенты в качестве их спутницы.
В этом что-то есть. Буду знать, благодарю за помощь в этом вопросе.
вам буде відправлено лист з адресою форму зміни коду або смс смс з новим паролем. Досвідчений вчитель математики, [url=https://granit-dnepr.com.ua/testimonial.html]https://granit-dnepr.com.ua/testimonial.html[/url] російської мови.
Юрист по наследственным делам с богатым опытом
вступление в наследство через сколько [url=https://www.nasledstvennyye-dela-v-moskve.ru/]https://www.nasledstvennyye-dela-v-moskve.ru/[/url].
современные госты требуют от семьи высоких расхода дней и вложения на поддержание [url=https://fitdeal.ru/zdorovye-deti/kakie-kachestva-vy-dolzhny-iskat-v-njane-vospitatele.html]няня для ребёнка[/url] привычного качества жизни.
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-grape-ice/]Pablo Exclusive Grape Ice[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-grape-ice/]Pablo Exclusive Grape Ice[/url]
how to get cialis online [url=https://cialisbag.com/]cialis 20mg tablets[/url] buy viagra and cialis online
www cialis com free trial https://cialisbag.com/ - coupon cialis
в этих углублениях ненужная мебель, [url=https://sutochnogrodno.by/]https://sutochnogrodno.by/[/url] зачастую бывают проблемы с коммуникациями (водичкой, и отоплением). Квартиросъёмщик делает выбор, чаще исходя из стоимости.
Интернет магазин предлагает купить оптом и в розницу современное медицинское оборудование и технику для частных и государственных клиник <a href="http://allmed24.ru/">медицинское оборудование кислородный концентратор купить</a>
cialis with prescription cialis natural [url=https://nwvipphysicians.com/]cialis price comparison[/url] cialis diarrhea cialis rxlist
встреча с данной девушкой становится реально незабываемым событием. Обычно эскортницы выбирают работу с отходами как вспомогательный ресурс дохода либо в роли [url=http://22-91.ru/biografiya/prodolzhenie-dinastii-kompozitorov-maksim-dunaevskijj/14.01.2015]http://22-91.ru/biografiya/prodolzhenie-dinastii-kompozitorov-maksim-dunaevskijj/14.01.2015[/url] временной занятости.
how long does it take for cialis 5mg to work [url=https://cialisbag.com/]goodrx cialis[/url] cialis over the counter at walmart
where to buy cialis without prescription https://cialisbag.com/ - cialis 20mg review
обычно, речь идёт не о заболевании, а элементарно о другом способе восприятия мира: аутизм, синдром Дауна и подобные состояния, что не лечатся, [url=https://www.volgograddaily.ru/press.php?id=3605]стоимость няни[/url] но компенсируются.
<a href="https://www.google.co.kr/url?q=https://www.coinsbar.net/ru/">https://www.google.co.kr/url?q=https://www.coinsbar.net/ru/</a>
Складчина (совместная покупка) курса, всего за 1ye <a href="https://t.me/effekt_karina_iskhakova">эффект карина искхакова</a>
when will cialis be generic <a href=https://cialisbag.com/>cost cialis</a> free trial of cialis
generic cialis tadalafil https://cialisbag.com/ - prices cialis
Здесь вы найдете официальный сайт [url=https://spkdzm.ru/]1Вин[/url].
Здесь вы найдете официальный сайт [url=https://spkdzm.ru/]1Вин[/url].
Настоятельно рекомендую только этот официальный сайт [url=https://spkdzm.ru/]1Win[/url].
Настоятельно рекомендую только этот официальный сайт [url=https://spkdzm.ru/]1Win[/url].
Qemtex specializes in producing [url=https://qemtex.com/]Powder Coatings[/url]. Recommend!
RAMENBET https://brazino777.me/
Qemtex specializes in producing [url=https://qemtex.com/]Powder Coatings[/url]. Recommend!
бесплатная консультация юриста по вопросам пенсии [url=http://konsultaciya-yurista5.ru/]http://konsultaciya-yurista5.ru/[/url].
Заказать любые виды сантехнических работ в Краснодаре <a href="http://fabulamebel.ru/">Сантехник Краснодар</a> Низкие цены, быстрое оказание услуг, гарантии качества.
It's very good [url=https://www.lerus.com/]Lerus Offshore Certified Courses[/url]. I recommend!
It's very good [url=https://www.lerus.com/]Lerus Offshore Certified Courses[/url]. I recommend!
High-quality Minecraft servers - selected projects with video trailers and reviews from real players. We care about all our users <a href="http://archive.molbuk.ua/user/gierrekoxi">minecraft 1.11 serwery z minigrami</a>
Здесь однозначно лучшая [url=https://asiacolor.kz/]порошковая краска[/url]. Рекомендую!
Слушать подряд все песни Сектор Газа онлайн бесплатно, скачать музыку, песни и все популярные треки группы <a href="https://sektorgaza.su/kazachya/">сектор газа казачья</a>
we know for sure these are most of all important factors affecting quality of virtual casinos, because affirm that players should have opportunity play in Internet [url=https://casinos-x86.win/mobile]https://casinos-x86.win/mobile[/url] for real money and receive your winnings, forgetting about similar difficulties, such as account blocking or ban in withdrawing funds.
Оптимальный вариант защиты водительских прав: услуги автоюриста
автоюрист круглосуточно телефон [url=https://avtoyurist-moskva1.ru]https://avtoyurist-moskva1.ru[/url].
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-mango-ice/]Pablo Exclusive Mango Ice[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-strawberry-cheesecake/]Pablo Exclusive Strawberry Cheesecake[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-mango-ice/]Pablo Exclusive Mango Ice[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-strawberry-cheesecake/]Pablo Exclusive Strawberry Cheesecake[/url]
1WIN - Лучшая букмекерская контора с самыми большими коэффициентами <a href="https://optocean.ru">1Win зеркало</a>
Прокладывайте свой путь к подводной свободе с нашими увлекательными <a href="https://idc-padi.ru/">программами по обучению дайвингу</a>.
Экспертное сопровождение оформления наследства
юрист онлайн наследство [url=https://yurist-po-nasledstvu-msk-mo.ru]https://yurist-po-nasledstvu-msk-mo.ru[/url] .
https://european-sailing.com/yacht-charter-tenerife
Букмекерская контора 1Win является одним из лидеров рынка по широкому диапазону коэффициентов для спортивных мероприятий <a href="https://ledokolangara.ru">1Вин казино</a>
приворот черный на куклу - Настоящий, проверенный маг. Ритуалы черной магии по фото WhatsApp +79842861265 <a href="https://izard.ru">izard.ru</a> - порча на смерть онлайн
приворот из мести черная магия - WhatsApp +79842861265
церковная порча на смерть
действие белого приворота на мужчину, белая магия на приворот мужчину
Всем советую оригинальный сайт БК [url=https://1win-1win.net/]1Win[/url]. Рекомендую однозначно!
Всем советую оригинальный сайт БК [url=https://1win-1win.net/]1Win[/url]. Рекомендую однозначно!
Всем советую лучшую БК [url=https://1win-1win.org/]1Win[/url]. Рекомендую однозначно!
Всем советую лучшую БК [url=https://1win-1win.org/]1Win[/url]. Рекомендую однозначно!
Предоставляя разнообразные возможности для грузоперевозок и строительных работ, манипуляторы обеспечивают эффективность и оперативность в обработке грузов <a href="https://uslugi-manipulyatora-moskva.ru">арендовать манипулятор</a>
[url=https://mpdostavka.ru]доставка морем из китая[/url] или [url=https://gruzkitaj.ru]товары из китая оптом посредников[/url]
[url=https://cargo-iz-kitay.ru]карго компании доставка из китая[/url]
https://cargo-kitaj.ru/page/114
Ещё можно узнать: [url=http://yourdesires.ru/beauty-and-health/face-care/178-kak-snyat-opuhol-ot-pryscha.html]как убрать припухлость от прыща[/url]
товары для маркетплейсов
Что такое SEO продвижение сайта. SEO (англ. Search Engine Optimization) – это комплекс мер по улучшению сайта для его ранжирования в поисковых системах <a href="https://sozdanie-sajta-v-moskve.ru">заказать продвижение в интернете</a>
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-strawberry-lechee/]Pablo Exclusive Strawberry Lychee[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-ice-cold/]Pablo Ice Cold[/url]
The Mellbet filter allows you to select a specific league, specify the amount of bets in the bet, the time before the start of the game and the minimum market odds <a href="https://www.discussworldissues.com/forums/new-age/444499-mostbet-bukmeykerining-batafsil-sharhi.html#post2825412">https://www.discussworldissues.com/forums/new-age/444499-mostbet-bukmeykerining-batafsil-sharhi.html#post2825412</a>
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-ice-cold/]Pablo Ice Cold[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-strawberry-lechee/]Pablo Exclusive Strawberry Lychee[/url]
Многие участники мирового рынка весьма оптимистично оценивают перспективы украинского рынка, [url=http://www.kordarecords.com/korda-kompilation-ship-it-2/?unapproved=1263041&moderation-hash=2d903e43bd2a58cbf8e45b144c35d53b]http://www.kordarecords.com/korda-kompilation-ship-it-2/?unapproved=1263041&moderation-hash=2d903e43bd2a58cbf8e45b144c35d53b[/url] разумеется принятии поправок к главному закону. slotoking действует на лицензии КРАИЛ №150 от 12.04.2021 года.
Быстрое удаление пятен и загрязнений, очистка вещей от запаха и бактерий <a href="https://khimchistka-mebeli-v-moskve.ru">диана чистка диванов на дому</a>
IP-телефония — это уникальный тип связи, который функционирует через интернет. К интернет-каналу предъявляются минимальные требования:<a href="https://www.google.iq/url?q=https://hottelecom.net/">https://www.google.iq/url?q=https://hottelecom.net/</a>
Новинки - это всегда круто!!!
Spanking often is simple and safe the starting point in bdsm, which leads to exploring a larger [url=https://sportcar.moscow/user/muirenuydc]https://sportcar.moscow/user/muirenuydc[/url], such as buying a crop for use, with a partner.
?????????? ???? ??? ????? ? ?????????? ???????? ???? ??????? ?? ??????? ?????????? ?? ?????????? ?????? ?????????? ???? ???? ? ??????????! ??????????? ??????????, ?????????????? ??????, ? ???????? – ??? ???? ????????. ???????? ??? ???? <a href=https://www.remont-doma-moskwa.ru>?????? ??????? ????? ? ??????</a> ? ??????? ????????????? ?????? ???? ????? ??????! #?????????????????? #?????????????????? #??????
I enjoy the info on your web sites. Kudos!
https://www.soopt.co.kr/bbs/board.php?bo_table=free&wr_id=1218244
Очень крутая БК [url=https://1win-1win.icu/]1Win[/url]. Всем советую!
Как светодиодный ночник поможет детям снять стресс и улучшить качество сна <a href="http://polegasm.net/index.php/forum/welcome-mat/150041">http://polegasm.net/index.php/forum/welcome-mat/150041</a>
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-mini-ice-cold/]Pablo Mini Ice Cold[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-mini-red/]Pablo Mini Red[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-mini-ice-cold/]Pablo Mini Ice Cold[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-mini-red/]Pablo Mini Red[/url]
Сертификат ISO 9001 - это официальный документ, гарантирующий качество выпускаемого товара, продукта/оказываемой услуги, а так же высокую степень надежности Вашего предприятия <a href="https://teletype.in/@sezdok/optimalnaya-cena-sertifikata-iso09001-v-rossii">цена сертификации ISO 9001</a>
Cool, I've been looking for this one for a long time
_________________
[URL=https://kzkk43.site/3671.html]фонбет спорттық ставкаларын тегін жүктеу[/URL]
Быстрый и надежный VPN через Telegram бота. Без отвалов. Без ограничения скорости и трафика <a href="https://my-vpn.ru">впн австралия</a>
Saan makakabili ng Diabetin capsules sa Pilipinas? Pagsusuri, opinyon, pagsusuri <a href="https://www.facebook.com/Diabetin.Philippinesss">is diabetin approved by fda</a>
Здесь можете найти с большим балансом [url=https://meduza.click/?r=store&id=5]карты на обнал[/url]. Рекомендую!
Здесь можете найти с большим балансом [url=https://meduza.click/?r=store&id=5]карты на обнал[/url]. Рекомендую!
?Donde comprar Duston Gel en Uruguay? ?Cuanto cuesta? Opiniones y criticas, ?verdad o estafa? <a href="https://www.facebook.com/Duston.Gel.Uruguay/">duston gel Uruguay Farmashop</a>
"Passport, driving license,[url=https://www.templ.cc/ ]cuba driver's license [/url]
ID card, certificate, utility bill, bank statement
and other editable templates. Photoshop, Word, Excel, PDF. "
Лучшие условия аренды инструмента в Красноярске
аренда инструмента в красноярске [url=https://prokat888.ru#аренда-инструмента-в-красноярске]https://prokat888.ru[/url].
[url=https://clinika-med.ru/vedenie-beremennosti]ведение беременности в Самаре[/url] или [url=https://med-klinika163.ru/index.php?newsid=34]прием гинеколога[/url]
[url=https://med-klinika163.ru/index.php?newsid=37]оформлению медицинских справок[/url]
https://clinikamed.ru/oformlenie-spravok
Ещё можно узнать: [url=http://yourdesires.ru/it/1248-kak-vvesti-znak-evro-s-klaviatury.html]значок евро символ[/url]
прием врача терапевта
"Download editable and free passport, driving license, [url=https://faketemplate.ru/ ]id photo pose [/url]
ID card, certificate, utility bill, bank statement
and other editable templates. Photoshop, Word, Excel, PDF. "
"Passport, driving license, [url=https://shoptempl.com/ ]japanese id card template [/url]
ID card, certificate, utility bill, bank statement
and other editable templates. Psd, doc, pdf, xls formats."
Полностью разделяю Ваше мнение. В этом что-то есть и это отличная идея. Я Вас поддерживаю.
киски тоже начали бродить по стране в мужских шароварах, [url=https://pinupcasino-play.win/]pinup казино[/url] потому что в те времена женских брюк не существовало.
Explore into the Infinite Field of Minecraft with Us!
On our website, you'll find everything you need for an remarkable adventure in Minecraft: servers with a myriad of mods, useful tips, and enticing articles about the territory of blocky adventures! <a href="http://fbesport.com/user/dunedaucfz">http://fbesport.com/user/dunedaucfz</a>
+ for the post
_________________
[URL=https://topslotsbonusss.site/slots_sity_онлайн_казино.html]нолимит сити слоты[/URL]
Браво, какие нужная фраза..., великолепная мысль
Совет №4. Разнообразие механик, бонусная функция, [url=https://raitingslots.win/video-sloty]https://raitingslots.win/video-sloty[/url] фичи. Мы заострим внимание на ряда просто важных ситуациях и снова напомним основные моменты.
Одна из лучших БК [url=https://1win1win.net/]1Win[/url]. Рекомендую!
Одна из лучших БК [url=https://1win1win.net/]1Win[/url]. Рекомендую!
Бесплатная консультация юриста по алиментам
алиментах на детей юриста [url=http://yurist-po-alimentam-v-moskve.ru/]http://yurist-po-alimentam-v-moskve.ru/[/url].
Я считаю, что Вы не правы. Давайте обсудим. Пишите мне в PM, поговорим.
нужно сказать, [url=https://oncasino-10top7.win]казино[/url] что нынешние топ десяти динамические. вернее перед тем как влиться в топ casino тщательно тестируется и выявляются как сильные, аналогично слабые моменты.
Одна из лучших БК в России [url=https://1win1win.click/]1Win[/url]. Рекомендую!
Одна из лучших БК в России [url=https://1win1win.click/]1Win[/url]. Рекомендую!
<a href="https://www.google.com.ng/url?q=https://guard-car.ru/">https://www.google.com.ng/url?q=https://guard-car.ru/</a>
<a href="https://www.google.by/url?sa=t&url=https://guard-car.ru/">https://www.google.by/url?sa=t&url=https://guard-car.ru/ </a>
Рекомендую одну из лучших в России БК [url=https://1win1win.club/]1Win[/url]. Советую!
Рекомендую одну из лучших в России БК [url=https://1win1win.club/]1Win[/url]. Советую!
Simdi kaydolun [url=https://www.bitget.com/tr]https://www.bitget.com/tr[/url] ve 1000 USDT hos geldin paketi al?n!
garage epoxy floors
https://www.mrparticularmn.com
Лучшая в России БК [url=https://1win1win.info/]1Win[/url]. Советую!
Лучшая в России БК [url=https://1win1win.info/]1Win[/url]. Советую!
Ценю это! Это является замечательно сайт.
посмотрите также мою страничку
https://www.articletrunk.com/%d0%be%d1%84%d0%b5%d1%80%d1%82%d0%b8-%d1%81%d0%b0%d1%80%d0%b4%d0%b8%d0%bd%d0%b8%d1%8f/ тоскана
354555=556
The best sale of pc games https://gamesv1.com
Calorico forte capsules in south africa, where to buy? Opinions and review <a href="https://www.facebook.com/calorico.forte.south.africa.price">calorico forte in south africa</a>
Motion Energy gel in Nigeria, where to buy and how much does it cost? Price <a href="https://www.facebook.com/Motion.Energy.Nigeria/">Motion Energy Gel Nigeria Price</a>
[url=https://cargokitay.ru]товар из китая оптом цена[/url] или [url=https://dostavka-iz-kitay.ru]товары из китая оптом посредников[/url]
[url=https://cargokitay.ru]товары из китая оптом посредников[/url]
https://cargokitay.ru/news/59-optovye-postavki-iz-kitaja-v-moskvu-vygodno-i-bystro.html
Ещё можно узнать: [url=http://yourdesires.ru/beauty-and-health/lifestyle/169-srochnye-analizy-ili-ponyatie-cito.html]срочно на латыни в медицине[/url]
Грузоперевозки товаров из Китая
Настоящая в России БК [url=https://1win1win.xyz/]1Win[/url]. Рекомендую однозначно!
Настоящая в России БК [url=https://1win1win.xyz/]1Win[/url]. Рекомендую однозначно!
Мне кажется, вы правы
игроки всегда ищут предельно комфортные решения внесения депозита или снятия [url=https://allcasinoratingslots7-2023.win/obzor-kazino-s-luchshim-vip-servisom]https://allcasinoratingslots7-2023.win/obzor-kazino-s-luchshim-vip-servisom[/url] финансов на портале.
Выгодная БК в России [url=https://1win2.click/]1Win[/url]. Рекомендую однозначно!
Извиняюсь, мне тоже хотелось бы высказать своё мнение.
The Speed Is Amazing, and you Won't Want To [url=http://hanbiz.apat.biz/bbs/board.php?bo_table=free&wr_id=299220]http://hanbiz.apat.biz/bbs/board.php?bo_table=free&wr_id=299220[/url] An Eye To Miss An Exciting Scene.
Comprar Sustarox crema en Peru. Precio en Inkafarma, Mercado Libre <a href="https://www.facebook.com/Sustarox.Crema.Peru">Sustarox inkafarma</a>
Официальная БК в России [url=https://1win2.club/]1Win[/url]. Рекомендую!
Официальная БК в России [url=https://1win2.club/]1Win[/url]. Рекомендую!
Строительная экспертиза в Москве от организации <a href="https://strah-urist.ru/">Строительная экспертиза</a> недорого и с гарантией.
Играйте в лучшие онлайн казино 2024 года, который входят в рейтинг лучших. Топ казино дарит выгодные бонусы на депозит, выплаты быстрые, регистрация на официальном сайте моментальная <a href="https://abcklinker.ru/">лучшие онлайн казино</a>
Ищите хорошие аккаунты социальных сетей? Тогда мы поможем вам с выбором.
На нашем сайте https://qaccs.net есть вся полезная информация. Вы без труда сможете выбрать, и купить любой другой аккаунт соц. сетей. С нами покупка аккаунтов станет безлопастной.
ха-ха-ха Это просто нереально....
nevertheless, you can to play until until the sum of the cards approaches 21, but without going over, in other situation you will lose the [url=https://www.deixe-tip.com/scripts/redir.php?url=casinosporinternet.com]https://www.deixe-tip.com/scripts/redir.php?url=casinosporinternet.com[/url].
Relifix Crema: La Eleccion Ideal en Guatemala para Cuidado de la Piel – Precios y Puntos de Venta en Farmacias <a href="https://www.facebook.com/relifix.crema.guatemala/">Relifix Gel Guatemala</a>
Подготовка и сдача бухгалтерской, налоговой и статистической отчетности в срок <a href="https://buhgalterskie-uslugi-1.ru">сопровождение бухгалтерии</a>
Однозначно, быстрый ответ :)
Non-woven and vinyl wallpapers hide minor irregularities and some cracks. Neutral and opposite colors are presented in an almost endless set of shades of [url=https://fashioneraonline.com/transform-your-space-the-art-and-science-of-choosing-the-perfect-wallpaper/]https://fashioneraonline.com/transform-your-space-the-art-and-science-of-choosing-the-perfect-wallpaper/[/url].
Скажите мне, пожалуйста - где я могу найти больше информации по этому вопросу?
Желание самоудовлетвориться мешает работать, спать, заниматься в спортзале, [url=http://rudiplomy.com/]порно хаб[/url] порой даже есть. после просмотра видео у меня просто перестало появляться желание партнера.
игровые автоматы cat casino
<a href=https://arena-gp.ru/>официальный сайт кэт казино</a>
бонусы Gama Casino
<a href=https://arsenal-avtocar.ru/>игровые автоматы Gama Casino</a>
Браво, эта великолепная мысль придется как раз кстати
Hice un desastre, jugando en [url=http://giantsquoit.org/index.php/component/k2/item/7]http://giantsquoit.org/index.php/component/k2/item/7[/url] en su propio uniforme escolar. mejor opcion corridas y creampies con una belleza de 18 anos.
[url=https://getb8.us/]online casino real play[/url]
[url=https://getb8.us/]mobile casino real money[/url]
Официальный вход на сайт БК [url=https://1win2.online/]1Win[/url]. Рекомендую!
Официальный вход на сайт БК [url=https://1win2.online/]1Win[/url]. Рекомендую!
Для осуществления онлайн-торговли брокер предлагает целый список инструментов, среди которых торговля на Форекс, использование финансового анализа <a href="https://obrokerah.ru/alpari/">https://obrokerah.ru/alpari/</a>
Официальный вход на зеркало БК [url=https://1win2.cloud/]1Win[/url]. Рекомендую!
Официальный вход на зеркало БК [url=https://1win2.cloud/]1Win[/url]. Рекомендую!
черный приворот на рунах - Обратится к магу - <a href="https://dzen.ru/id/653538d7d6100f7a6fee8469">https://dzen.ru/id/653538d7d6100f7a6fee8469</a>
самый эффективный черный приворот
Какой симпатичный ответ
в том случае, если вы подключены к turbo vpn, [url=http://balaklavskiy-16.ru/user/8966/]http://balaklavskiy-16.ru/user/8966/[/url] ваш айпи и месторасположение будут замаскированы. Повысьте эффективность просмотра веб-страниц, геймов и интернет-системы!
Вход на зеркало в официальный БК [url=https://1win1win.online/]1Win[/url]. Рекомендую!
магия в москве услуги ->>>>>>>помощь магическая москва <a href="https://www.magecam.ru">https://www.magecam.ru</a> <<<<<<<<<<-
Вход на зеркало в официальный БК [url=https://1win1win.online/]1Win[/url]. Рекомендую!
<a href="https://www.magecam.ru">https://www.magecam.ru</a>
Услуги магов
-привороты
-наведение порчи на смерть
-отнятие удачи
-возврат любимого
приворот в рождения
Магическая помощь - сильные экстрасенсы
приворот девушки с помощью волос <a href="https://gadalkindom.ru">https://gadalkindom.ru</a> заговор на соль на любовь мужчины читать с водой
приворот на соль на любовь мужчины на расстоянии читать
Конечно. Я согласен с Вами.
Ну что же, потенциальный гость уже определился с стоимостью, и считает нормальным, что расценки на посильная, а вот в Казани, кто сдает дорого , [url=https://lockedbox.by/]квартиры в минске на сутки[/url] просто весьма жадные хозяева.
Рекомендую официальный сайт БК [url=https://1win2.store/]1Win[/url]. Очень выгодно!
Рекомендую официальный сайт БК [url=https://1win2.store/]1Win[/url]. Очень выгодно!
Промокод для 1xBet 2024: 1xvip567. При использовании данного промокода при регистрации вы получите 100% дополнительных средств для ставок <a href="http://centroculturalrecoleta.org/blog/pages/1xbet_promo_code_free_bet_bonus.html">http://centroculturalrecoleta.org/blog/pages/1xbet_promo_code_free_bet_bonus.html</a>
Thanks for the post
_________________
[URL=https://Bangladeshsports.site/3160.html]অনলাইন ক্যাসিনোতে অর্থের জন্য খেলুন [/URL]
Это официальный сайт БК [url=https://1win3.org/]1Win[/url]. Рекомендую!
Это официальный сайт БК [url=https://1win3.org/]1Win[/url]. Рекомендую!
как привязать парня к себе белая магия - Помощь экстрасенса <a href="https://www.magecam.ru">https://www.magecam.ru</a> - как вернуть бывшего магия снять магическое воздействие самостоятельно
приворот черное венчание обряд <a href="https://www.magecam.ru">https://www.magecam.ru</a> приворот на брак на кладбище
сделать приворот самостоятельно
Телеграм аккаунты для рассылки и инвайтинга. Качественные аккаунты по низкой цене <a href="https://sendrock.pro/buy-proxies">Мобильные прокси</a>
Черный маг
заговоры на новый замок <a href="https://gadalkindom.ru">https://gadalkindom.ru</a> заговоры на возврат любимого
сильный приворот со свечами
порча на закрытую дорогу <a href="https://www.magecam.ru">https://www.magecam.ru</a> порча нанесенная иглой - снять
[url=http://vuvaldi.com/]Вивальди[/url]
<a href=http://treidulo.com/>truidungo</a>
http://staylinka.com/
Надежный официальный сайт БК [url=https://1win3.net/]1Win[/url]. Всем Рекомендую!
Надежный официальный сайт БК [url=https://1win3.net/]1Win[/url]. Всем Рекомендую!
Надежный официальный вход на БК [url=https://1win3.store/]1Win[/url]. Всем Рекомендую!
Надежный официальный вход на БК [url=https://1win3.store/]1Win[/url]. Всем Рекомендую!
Hi there i am kavin, its my first time to commenting anywhere, when i read this post i thought i could also create comment due to this good piece of writing.
<a href=https://www.reddit.com/r/BestCasinosAustralia/comments/19akr2v/are_there_neteller_casinos_in_australia/>australian neteller mobile casino</a>
Hello, every time i used to check weblog posts here early in the morning, since i enjoy to gain knowledge of more and more.
<a href=https://www.reddit.com/r/BestCasinosAustralia/comments/19akr2v/are_there_neteller_casinos_in_australia/>casino accept neteller</a>
<a href=https://t.me/s/prostitutki_tmn>prostitutki tumeni</a>
Официальный сайт БК [url=https://1win3.online/]1Win[/url]. Всем Рекомендую!
Официальный сайт БК [url=https://1win3.online/]1Win[/url]. Всем Рекомендую!
Thank you for the good writeup. It if truth be told was once a enjoyment account it. Glance complex to far introduced agreeable from you! By the way, how can we be in contact?
<a href=https://www.reddit.com/r/BestDissertationSites/comments/xufflv/the_best_dissertation_writing_service_in_20222023/>dissertation proofreading service</a>
<a href=https://prostitutki-tumeni-72.com/>prostitutki tumeni</a>
Официальный сайт БК в России [url=https://1win3.site/]1Win[/url]. Всем Рекомендую!
Официальный сайт БК в России [url=https://1win3.site/]1Win[/url]. Всем Рекомендую!
Великолепная БК в России и СНГ [url=https://1vin2.blog/]1вин[/url]. Рекомендую!
very good
_________________
[URL=https://bdsports.site/890.html]অনলাইন ক্যাসিনো|টাকার জন্য ক্যাসিনো [/URL]
<a href=https://remont-derevyannogo-doma.ru/>remont derevyannih domov</a>
Официальный сайт БК в России и СНГ [url=https://1win3.club/]1Win[/url]. Всем Рекомендую!
Официальный сайт БК в России и СНГ [url=https://1win3.club/]1Win[/url]. Всем Рекомендую!
<a href=https://rekonstruktsiya-derevyannogo-doma.ru/>rekonstruktsiya derevyannogo doma</a>
Наши специалисты тщательно отбирают только качественные товары от ведущих мировых производителей, гарантируя ваше удовольствие и безопасность<a href="http://zingcorp.com.au/component/kunena/sub-category-4/59297#59340">http://zingcorp.com.au/component/kunena/sub-category-4/59297#59340</a>
приворот на красную свечу отзывы <a href="https://10122023magpriv.wordpress.com">https://10122023magpriv.wordpress.com</a> приворотные сериал смотреть онлайн
********************сесуальный приворот самостоятельно <<<<<<<<<<-
********************приворот по вещи личной <<<<<<<<<<-
********************приворот отворот омск <<<<<<<<<<-
Официальный и надежный сайт в России и СНГ [url=https://1win3.icu/]1Win[/url]. Рекомендую!
Официальный и надежный сайт в России и СНГ [url=https://1win3.icu/]1Win[/url]. Рекомендую!
Спс мну нравиться!
22 января 2024 Жители уселась в Забайкалье выступили против женщины, [url=https://euro24.news/novosti/sovet-nacbanka-chehii-edinoglasno-soglasilsya-na-snizhenie-stavki-ipoteka-stanet-deshevle]https://euro24.news/novosti/sovet-nacbanka-chehii-edinoglasno-soglasilsya-na-snizhenie-stavki-ipoteka-stanet-deshevle[/url] которая донесла на "пропаганду ЛГБТ" в детском утреннике.
One of the best[url=https://washauto.me/]mobile car wash Miami[/url]
One of the best[url=https://washauto.me/]mobile car wash Miami[/url]
Безопасная и надежная [url=https://perevozka-bolnykh-po-moskve.ru/]перевозка лежачих больных[/url]. Профессиональные водители и медицинский персонал. Заботимся о вашем благополучии.
Любопытно....
Загляни также в раздел «Еда» - ты будешь приятно удивлен обилием выгодных предложений. Большинство наших прямых партнеров - компании, [url=http://moemesto.ru/link/15215850]http://moemesto.ru/link/15215850[/url] работающие в сфере медицины.
- привороты и как с ними бороться
- <a href="https://magiya.guru">https://psy-magic.org</a> сильные привороты чтоб муж пришел
- привороты заговоры от соперницы
- приворот на волос
сильнодейстующие привороты приворот, чтоб муж был ласковый сколько стоит приворот
<a href="https://artgrom.com">https://cherrywoman.ru</a>
Не унывай! Веселее!
таким образом, имеющий аккредитацию пункт получает «техническое право» работы и наследует «доверие» от организации, [url=https://www.rospromtest.ru/content.php?id=5]сертификаты системы менеджмента качества ISO 9001[/url] выполнившей аккредитацию. В криптографии центр оформления сертификатов или удостоверяющий центр (англ.
The salesman, surprised, asked the snail, "Why do you need a fast car? You're a snail." <a href="https://andynpqo12333.develop-blog.com/30589135/the-benefits-of-stripping">buy</a>
приворот на мужчину на месячную кровь без последствия в домашних условиях на расстоянии как сделать приворот жены в домашних условиях - <a href="https://peopletalk.ru">https://мир-магов.рф</a> приворот на любовь женщины читать самостоятельно на расстоянии
Мне очень жаль, что ничем не могу Вам помочь. Но уверен, что Вы найдёте правильное решение.
они помогают игрокам получать больше скинов за меньшие деньги [url=https://vrgames.ru/]vrgames.ru[/url] и существенно сэкономить. любой пользователь имеет возможность выбрать наиболее подходящий для личного пользования метод, сделав оплату высокоэффективной и безопасной.
приворот очень сильный приворот на парня на бумаге с его именем домашних условиях читать
приворот матушка меня народила богородица благословила - <a href="https://sueveriya.com">https://lagopus.ru</a> приворот по фотографии
самые сильные и действуюшие привороты - <a href="https://магиявера.рф">https://магиявера.рф</a>
Социальные сети предоставляют возможность общения, продвижения бизнеса.
[url=https://akkaunt-vk.ru]Купить аккаунт инстаграм[/url] может показаться привлекательным в случае, если у вас нет времени или желания создавать свой профиль с нуля. Это также может быть интересным вариантом для бизнеса или маркетологов, стремящихся получить уже установленную аудиторию.
Need a virtual phone number to handle outbound and incoming calls? Get one in just a few minutes <a href="https://www.google.tt/url?q=https://hottelecom.net/pl/">https://www.google.tt/url?q=https://hottelecom.net/pl/</a>
Программа для комплексного обслуживания [url=https://elbuz.com/]Автоматизация интернет-магазинов[/url]. Рекомендую!
Программа для комплексного обслуживания [url=https://elbuz.com/]Автоматизация интернет-магазинов[/url]. Рекомендую!
приворот черная привязка что это - <a href="https://zakolduj.ru">https://infogoro.ru</a> чакровый приворот ловушка
руны приворота формулы ловушка камеди вумен возврат приворота - <a href="https://omystical.com">https://molitvamiru.ru</a> приворот на волос парня
приворот на парня кровью сильный приворот на возврат мужа
заклинания приворота парня - <a href="https://magizmo.ru">https://stepslove.ru</a> приворот на беременность
You can get a virtual phone number with OpenPhone in three simple <a href="https://www.google.mg/url?q=https://hottelecom.biz/es/">https://www.google.mg/url?q=https://hottelecom.biz/es/</a>
Только здесь вы найдете актуальный промокод на БК [url=https://1vin2.org/]1Вин[/url]. Рекомендую!
Только здесь вы найдете актуальный промокод на БК [url=https://1vin2.org/]1Вин[/url]. Рекомендую!
Хнык! Ошибку выдает... Щас буду нервничать...
benachrichtigungen/Nachrichten zum Lesen: mit/mit Ein/Aus-Schalter bevorzugen, ob deine Freunde im Chat sehen werden [url=https://sp303.edu.pl/all/was-verdient-eine-bedienung-auf-dem-oktoberfest.html]was verdient eine wiesn bedienung[/url] wenn sie/Details/Daten die Nachricht gelesen haben.
ask questions - wonderful way to attract your [url=https://rabota-onliner.ru/user/kittanhcwb]https://rabota-onliner.ru/user/kittanhcwb[/url]. for example, they become subscribe on you, expecting the same attitude.
- приворот невербальными жестами
- <a href="https://morfeos.ru">https://privorot16.ru</a> приворот на девушку которая любит другого
- признаки приворота женского мужчины
- приворот пишиванием с помощью двух вещей
бесовский приворот что это такое что будет с заказчиком после снятия приворота - <a href="https://dommagii.com">https://magic-white.net</a> приворот на разлуку
реально действующие привороты приворот на любовь мужа только действенные привороты
<a href="https://maguri.ru">https://kak-vernut-muzh.ru</a>
как узнать подействовал ли приворот на мужчину на расстоянии - <a href="https://приворот-инфо.рф">https://shmk.ru</a> как проверить есть ли приворот на муже
приворот сведение судеб приворот на волосы женщины который нельзя снять
приворот на мужчину без последствия на месячные в домашних условиях читать - <a href="https://stepslove.ru">http://fotogadanie.ru</a> приворот на восход солнца
приворот егильет - <a href="https://darknwhite.ru">https://mestozagovora.ru</a> приворот на любовь мужчины читать в домашних условиях на расстоянии
Я считаю, что Вы не правы. Могу отстоять свою позицию. Пишите мне в PM, пообщаемся.
Ted Pappageorge, secretary-treasurer of the [url=https://elliotxocg81481.ja-blog.com/24835995/health-and-wellness-in-the-stripping-industry-taking-care-of-you]https://elliotxocg81481.ja-blog.com/24835995/health-and-wellness-in-the-stripping-industry-taking-care-of-you[/url] union, told npr. Check-in kiosks have replaced person at the check-in counters in inns.
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-mini-x-ice-cold/]Pablo Mini x Ice Cold[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-niclab-ice/]Pablo Niclab Ice[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-mini-x-ice-cold/]Pablo Mini x Ice Cold[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-niclab-ice/]Pablo Niclab Ice[/url]
Официальный телеграм канал [url=https://t.me/win1_1vin]1win[/url]. Рекомендую!
Официальный телеграм канал [url=https://t.me/win1_1vin]1win[/url]. Рекомендую!
Обзор лучших строительных компаний в Крыму и Севастополе, посмотрите <a href="https://otpusk-v-krimu.ru/novosti-ark/nedvizhimost-kryma/143087-ceny-na-stroitelstvo-domov-v-krymu.html">строительство домов в Крыму</a>
на первый порах кажется, что [url=http://minecraftonly.ru/index.php?subaction=userinfo&user=opejemig]http://minecraftonly.ru/index.php?subaction=userinfo&user=opejemig[/url] - это не сложная и типа даже эффективная работа. подобная услуга дополняется многообещающей пометкой "vip".
Tadalafilo 5 Mg Precio
Cialis 5 mg prezzo <a href=https://comprarcialis5mg.com/it/cialis-5mg-prezzo/>prezzo cialis 5 mg originale in farmacia</a> tadalafil 5 mg prezzo
Агентство набирает пластичных, стройных и привлекательных девушек <a href="http://www.italian-style.ru/Nasha_kompanija/forum/?PAGE_NAME=profile_view&UID=50568">http://www.italian-style.ru/Nasha_kompanija/forum/?PAGE_NAME=profile_view&UID=50568</a>
приворот жены по фото в домашних условиях читать как убрать с себя приворот в домашних условиях - <a href="https://molitvamiru.ru">астрология кеплера</a> приворот на сильный ветер
полусферы астрологии папюс астрология
птолемеевская астрология
===============================================================================
приворот правда ли
снятие приворота на мясо приворот на мужчину без последствия в домашних условиях на вещь
приворот рязань - <a href="https://adella.ru">https://omagi.ru</a> как узнать приворот на муже
======================
привороты на любовь парня заговор рецепты приворот мгновено приворотное зелье фотографии
<a href="https://heaclub.ru">https://frauwow.com</a>
что такое дельфийский приворот
приворот на фото девушку
соль приворот на денег
It's very good[url=https://washauto.me/]luxury car wash Miami[/url]. Hightly recommend!
Очень кртая БК в России [url=https://1vin2.online/]1вин[/url]. Рекомендую!
It's very good[url=https://washauto.me/]luxury car wash Miami[/url]. Hightly recommend!
Очень кртая БК в России [url=https://1vin2.online/]1вин[/url]. Рекомендую!
Ежемесячная зарплата красоток, которые работают в данном агентстве, составляет от 20000 долларов и выше <a href="http://panifrangipani.ru/otzyvy/#comment-8689">http://panifrangipani.ru/otzyvy/#comment-8689</a>
Курьер не заносил посылки на склад, хотя это была его прямая обязанность, [url=http://www.qzzjzs.com/home.php?mod=space&uid=96770]http://www.qzzjzs.com/home.php?mod=space&uid=96770[/url] а примитивно оставлял литературу на входе.
изотермическая энтропия - nh4cl энтропия.
энтропия духа - <a href="https://privorot-vsem.ru">https://privorot-vsem.ru</a> синоним энтропии.
энтропия habr
энергия энтропия
как найти энтропию
порча чужого имущества вид проступка административный - <a href="https://artgrom.com">https://artgrom.com</a> после свадьбы пошли проблемы может быть порча.
мертвая лягушка порча
порча молочных продуктов реферат по товароведению
черная магия порча.первоуральск
как ощущается порча.сглаз
добродетель философия <a href="https://приворот-гуру.рф">философия неомарксизма</a>
руденко философиясинонимы философияметодология философия
философия квизлет миф философия философия эпикурейства
Я считаю, что Вы допускаете ошибку. Могу это доказать.
So, the [url=https://telegra.ph/Unveiling-the-Wonders-of-BMK-Methyl-Glycidate-A-Journey-into-the-World-of-Organic-Chemistry-01-16]https://telegra.ph/Unveiling-the-Wonders-of-BMK-Methyl-Glycidate-A-Journey-into-the-World-of-Organic-Chemistry-01-16[/url] used in automobiles is designed specially for this purpose. Bonds are broken in gasoline, releasing energy.
приворот чистка = <a href="https://magicwishes.ru">https://magicwishes.ru</a> чем опасен приворот на кладбище
что такое классический белый безгрешный приворот приворот читать в затылок спящему
Очень надежная БК в России [url=https://1vin2.cloud/]1вин[/url]. Рекомендую!
Очень надежная БК в России [url=https://1vin2.cloud/]1вин[/url]. Рекомендую!
Выполняем поверку счетчиков воды на дому без снятия. Поверитель в день обращения <a href="https://poverka-schetchikov-1.ru/">поверка бытовых счетчиков воды</a>
Дата обращения: 20 марта 2010. Архивировано из оригинала 25 [url=http://systempsychology.ru/index.php?subaction=userinfo&user=ysede]http://systempsychology.ru/index.php?subaction=userinfo&user=ysede[/url] ноября 2010 года. Соответственно, в 20 % случаев они предоставляют интим-досуг без презерватива.
%random_anchor_text%
%random_anchor_text%
%random_anchor_text%
%random_anchor_text%
%random_anchor_text%
- черный приворот на волосы жены
- <a href="https://privorot-vsem.ru">https://talismanes.ru</a> привороты свекрови наволосы
приворот нитка из трусов черный приворот на полнолуние
приворот на любовь быстрый результат приворот самостоятельно на вещь полученную им вo исполнение договора комиссии
привороты и заговоры самостоятельно со свечой на девушку снятие приворота видеть во сне
привороты на фото домашних условиях
приворот спб телефон .
снятие приворота в районе дедовска, красногорска, нахабино приворотное зелье косметика
снять приворот самостоятельно, сделанный на кладбище - <a href="https://morfeos.ru">https://morfeos.ru</a> приворот на крови онкология .
самостоятельно снять приворот человека снять приворот смерть.
посоветуйте мага для приворота приворот на мужчину сразу действует в домашних - <a href="https://tonkimir.ru">астрология лев</a> приворот на мужчину без последствия месячными
астрология луна тигр астрология.
определение астрология. блиновская астрология складчина астрология.
приворот на любовника читать в домашних - <a href="https://приворот-инфо.рф">https://shmk.ru</a> когда начинается действие приворота.
мощные рунические привороты
кладбищенский приворот как снять
как снять приворот с мужчины на расстоянии
Великолепная БК в России и СНГ [url=https://1vin2.blog/]1вин[/url]. Рекомендую!
private models - это не только агентство элитного эскорта в москве, [url=http://forum.animalservice.ru/viewtopic.php?f=9&t=2875]http://forum.animalservice.ru/viewtopic.php?f=9&t=2875[/url] такой диплом ваш надежный партнер в мире утонченного отдыха и идеального обслуживания.
как сделать любовный приворот на девушку в домашних условиях читать приворот девушки по фото.
как снять вечный приворот привороты на любовь женщины читать в домашних.
приворот с результатом - <a href="https://zakoldovan.ru">https://xram58.ru</a> приворот чтобы написал читать.
как снять приворот мужа существуют ли на самом деле привороты сильный приворот девушки
- привороты и отвороты на ивана купалу - приворот по чакра на куклу.
- <a href="https://belli-portelli.com">https://cherrywoman.ru</a> привороты всегда срабатывают на женатых мужчин7
-сильные привороты в домашних условиях приворот по фотографии белай магия.снять приворот самостоятельно с жены.
-сделать приворот на девушку водолея привороты которые помогают.что чувствует субъект снятия приворота.
-приворот на свечу церковную привороты на любовь навсегда
приворот на руническая формула приворот - <a href="http://www.bolshoyvopros.ru">кармическая астрология</a> как снять с человека приворот самостоятельно
астрология декабря юпитер астрология.
астрология карьера. таро астрологии
опасность астрологии.
сургут.объявления приворот гадания. снятие приворота самостоятельно бе5з фотографии сильный приворот в чистый четверг на мужа
<a href="https://kak-vernut-muzh.ru">https://domprivorotov.ru</a> .
////привороты город шахты что нужно для успешного приворота.
////приворот-егильет.
////самой сделать сильный приворот любимого
Адаптация поставщика для разнообразных устройств существенно повысит видимость портала, в мобильной выдаче, [url=http://agro-ua.com/wr_board/tools.php?event=profile&pname=aqefonija]http://agro-ua.com/wr_board/tools.php?event=profile&pname=aqefonija[/url] также вырастут конверсии с всяческих устройств.
самый сильный приворот на девушку - <a href="https://приворот-инфо.рф">https://shmk.ru</a> если не снимать приворот.
приворот с кровью из пальца. мощный приворот на парня читать в домашних условиях
мусульманский приворот на любовь парня читать по фото приворот на парня белый
привороты на мужа читать в домашних условиях который точно сработает.
- приворот по полному имени - привороты дома по фото.
- <a href="https://toth.su">https://darmaga.ru</a> снимает ли церковь приворот
-приворот на мужа последствия отзывы является ли присушка приворотом.швидкий приворот бившого коханого.
-привороты белой магии гадания привороты парня в домашних условиях.проверенный сильный приворот.
-приворот по чакрам gospodi приворот на женскую дружбу
самый сильный приворот в домашних условиях который нельзя снять приворот на человека которого любишь.
как сделать приворот на любимую девушку приворот на девушку кровью.
приворот по чакрам последствия - <a href="https://dekto.ru">https://sudbainfo.ru</a> легкий приворот без последствия.
защита от приворота как снять вечный приворот приворот парня на воде
став для снятия приворота с мужчины безопасный любовный приворот - <a href="https://podg-kursy.ru">https://ladytoday.ru</a> приворот перед сном
мэджик астрология астрология пентаграмма.
астрология джйотиша. понятная астрология
астрология предназначение.
First coastline with a private beach [url=https://coastal-heaven.com/]coastal heaven north cyprus[/url].
привороты и заговоры на покров. привороты от пьянства на крещение привороты любимой бесплатный.
<a href="https://sredainfobiz.ru">https://magicblack.biz</a> .
приворот на разлуку форум что делать, если на мужчину сделан приворот.
First coastline with a private beach [url=https://coastal-heaven.com/]coastal heaven north cyprus[/url].
Блестящая фраза и своевременно
Выбирайте надёжное агентство с оптимальным портфолио, чтобы оперативно и без гигантских стараний нанять опытную команду, [url=https://vk.tula.su/23/10/2023/138453/luchshie-sovety-po-vyboru-pravilnoj-nyani.html]https://vk.tula.su/23/10/2023/138453/luchshie-sovety-po-vyboru-pravilnoj-nyani.html[/url] которая воплотит вашу идею в жизнь.
It be no point.
sample personal essay [url=https://essaywriteren.com/]essay editing services[/url] essay on deforestation
check essay online https://essaywriteren.com/ - can you buy essays online
какой приворот самый сильный - <a href="https://ozhegova-slovar.ru">https://liyamagiya.ru</a> вся правда о приворотах и дальнейшая жизнь.
вернуть приворот тому кто его сделал. приворот чтоб написал
снятие приворота симптомы быстрый приворот парня
как себя вести во время приворота.
Я подумал и удалил эту фразу
сухая и влажная уборка. присмотр за детским гардеробом и детским пространством, [url=https://patronage-service.ru/]Сиделка приходящая[/url] приготовление блюд для своих малышей.
For all those trying to get a distinctive and enjoyable entertainment expertise, the entire world of striptease inside the north delivers a unique allure <a href="https://fernandosgug10753.blogscribble.com/24953873/booking-beautiful-strippers-for-your-party">https://fernandosgug10753.blogscribble.com/24953873/booking-beautiful-strippers-for-your-party</a>
самостоятельный приворот приворот девушки по фото - <a href="https://slovomaga.ru">https://rt82.ru</a> как распознать приворот и узнать кто навел
хора астрология тесты астрология.
гакрукс астрология. еврейская астрология
chronos астрология.
Рекомендую иммено эту надежную БК [url=https://1vin.xyz/]1вин[/url].
Рекомендую иммено эту надежную БК [url=https://1vin.xyz/]1вин[/url].
привороты татарские. сильный любовный приворот вуду сдела приворот на три свечи от патронессы.
<a href="https://privorot.club">https://sredainfobiz.ru</a> .
сильный приворот на дождь самый сильный приворот на покров.
- привороты в ночь с 13 января - приворот через менструацию.
- <a href="https://sharikbryansk.ru">https://sbormolitv.ru</a> простойдейственные приворот
-черный приворот оплата после положительного результата приворот с молоком матери.сушеное яблоко приворот.
-приворот сильный обряд kogda on geistvvuet самый сильный приворот на любовника чтоб всегда хотел.приворот на волос парня.
-привороты чёрная магия ко привороты на любовь заговоры
Get millions upon millions of immediate leads for your company to jumpstart your promotion. Make use of the lists an unlimited quantity of times. We have been providing businesses and market analysis firms with details since 2012. [url=https://www.mailbanger.com]Direct marketing
единовременный уход за ребенка - <a href="https://xigra.ru/magic/esli-srochno-nuzhny-dengi-ritualy">https://xigra.ru</a>
For all those trying to get a distinctive and enjoyable entertainment expertise, the entire world of striptease inside the north delivers a unique allure <a href="https://sergiopcpb97641.rimmablog.com/24689500/private-paradise-unveiled-strippers-to-elevate-your-celebration">https://sergiopcpb97641.rimmablog.com/24689500/private-paradise-unveiled-strippers-to-elevate-your-celebration</a>
ребенок 10 дней уход - <a href="https://ladytoday.ru/kak-vernut-muzha-posle-razvoda-privorot">https://ladytoday.ru</a> ->>>>>>>>> уход по ребенку 2022г !
Мы рады предложить большой выбор производственного оборудования, прямые поставки <a href="https://ofkleasing.ru/">лизинг подъёмно транспортное оборудование</a>
Добрый день, дорогие друзья!
Ставки на токены Manta уже в действии!
Поставьте свои $MANTA, чтобы получить дополнительные награды [url=https://mantadrop.pro]Manta Network[/url]
получите в свои руки лимитированную серию $MANTA $NFT Airdrop
Ваш ваучер на дополнительную бесплатную МАНТУ в размере $ - 12939791
[url=https://mantadrop.pro]Claim Airdrop Now[/url]
nothing special
_________________
[URL=https://bdPL.site/4264.html]অনলাইন ক্যাসিনো|টাকার জন্য ক্যাসিনো [/URL]
Are you over the hunt for an ideal approach to elevate your future bachelor celebration <a href="https://cristianldtg20753.59bloggers.com/25207918/private-strippers-for-unforgettable-nights">https://cristianldtg20753.59bloggers.com/25207918/private-strippers-for-unforgettable-nights</a>
Рекомендую только эту надежную БК [url=https://1vin.club/]1вин[/url].
Рекомендую только эту надежную БК [url=https://1vin.club/]1вин[/url].
Мне тоже понравился!!!!!!!!!
Няня для ребенка - это для начала страховка для матери ребенка, ведь и несмотря на такой нюанс, что в настоящее время популярна точка зрения «мама должна находиться с ребенком как можно много», [url=https://saintbasil.ru/news-1239812-kak-vybrat-nyanyu-sovety-i-rekomendatsii.html]https://saintbasil.ru/news-1239812-kak-vybrat-nyanyu-sovety-i-rekomendatsii.html[/url] ситуации творятся разные.
Лизинг оборудования - рейтинг компаний в 2024 году: отзывы, условия, стоимость и быстрое оформление онлайн-заявки <a href="https://chuvashagrolizing.ru/">оборудование для кафе в лизинг</a>
Ремонт телефонов Xiaomi, Haier, Huawei и другие в сервисном центре <a href="https://proremont-telefonov.ru/">адреса ремонта телефонов</a>
Я считаю, что Вы ошибаетесь. Давайте обсудим это.
быстрый выбор вакансий для поиска работы: вакансии в Бердянске, вакансии Челябинск, вакансии Пермь, вакансии Кемерово, вакансии Красноярск, вакансии Томск, вакансии Сургут, вакансии Самара, вакансии Омск, вакансии Тюмень, вакансии Курган, вакансии Новокузнецк, вакансии Архангельск, вакансии Барнаул, [url=https://vk.com/public198221204]свежие вакансии Тольятти[/url] вакансии Иркутск.
Добрый день, дорогие друзья!
Ставки на токены Manta уже в действии!
Поставьте свои $MANTA, чтобы получить дополнительные награды [url=https://mantadrop.pro]Manta Network[/url]
получите в свои руки лимитированную серию $MANTA $NFT Airdrop
Your voucher for additional free $MANTA - 39498224
[url=https://mantadrop.pro]Claim Airdrop Now[/url]
Ремонт телефонов Xiaomi, Haier, Huawei и другие в сервисном центре <a href="https://proremont-telefonov.ru/">починить телефон дешево</a>
Бытовая техника, ноутбуки, смартфоны и многое другое! Цены по карману каждому <a href="https://istore.md/ru/watch">купить часы в молдове</a>
https://continent-telecom.com/virtual-number-ukraine-kiev
Вскрытие замков в любое время суток оперативно <a href="https://pro-zamok72.ru/">мастер по вскрытию замков</a> и без повреждений.
как обнаружить порчу <a href="https://magazer.ru/porcha-na-mashinu-magnitom/">проклятие человеку который обидел</a> от порчи молитвы
https://virtual-local-numbers.com/countries/1380-fargo-virtual-phone-number.html
Рекомендую самую надежную БК [url=https://1vin.blog/]1вин[/url].
Рекомендую самую надежную БК [url=https://1vin.blog/]1вин[/url].
А есть другой выход?
Няня нужна на весь денек в расписании с 8 до 18 в будние дни. Простои 100% оплата. составим договор, [url=http://www.v-mama.ru/]Няня[/url] где все пропишем.
Судебный юрист – это юридическая компания, специализирующаяся на семейных делах <a href="https://thewillistree.info/genealogy/wiki/User:RandalBurt">https://thewillistree.info/genealogy/wiki/User:RandalBurt</a>
Купить 1С Склад у официального партнера фирмы 1С <a href="https://1s-sklad.ru">1с торговля купить</a> консультация бесплатно!
у мня уже есть
you will find out that young students are able to satisfy men using the skin on their palms, legs, [url=https://salonseniors.re/logo/]https://salonseniors.re/logo/[/url] and mouths.
Для того чтобы уточнить подробности и купить арматуру необходимого типа, свяжитесь с нашими специалистами <a href="https://vodoley66.ru/">арматура цена</a>
Список всех МФО Казахстана <a href="https://farsh-cook.ru/">https://farsh-cook.ru/</a>
Виниловый сайдинг в интернет-магазине по выгодным ценам <a href="https://star-plast.su/">https://star-plast.su/</a> настоящие отзывы покупателей!
https://www.ibm.com
https://european-sailing.com/yacht-charter-gran-canaria
Искусственные цветы из Китая ? идеальная альтернатива для создания безупречных и модных композиций. От реальных их не отличить!
[url=https://55opt.org/catalog/cvety-iz-kitaya/?city=nalchik]цветы китайские[/url]
отзывы музыкальный приворот - <a href="https://otziviprivorotporcha.wordpress.com">привороты отзывы мужчин</a> - отзывы о привороте в вк
Для того чтобы уточнить подробности и купить арматуру необходимого типа, свяжитесь с нашими специалистами <a href="https://vodoley66.ru/">стеклопластиковая арматура 12 мм цена за метр</a>
Извиняюсь, но это мне не совсем подходит.
Позиции с бесплатной транспортировкой отмечены специальным значком внизу [url=https://saffir.fr/?attachment_id=7]https://saffir.fr/?attachment_id=7[/url] описания. любые купоны, за вычетом бонуса новичку, дают выгоду только в случае покупки на денежные средства.
Посмотрите, [url=http://topforbaby.ru/product/adameks-koljaska-transf-galaxy-ljulka-imit/reviews/]http://topforbaby.ru/product/adameks-koljaska-transf-galaxy-ljulka-imit/reviews/[/url] как русские прелестные красотки готовы сосать самые огромные болты во зрелом бизнесе, и глотать кучу сливочной спермы.
Рекомендую самую надежную БК в России [url=https://1vin.biz/]1вин[/url].
Рекомендую самую надежную БК в России [url=https://1vin.biz/]1вин[/url].
In it something is. I will know, many thanks for the information.
<a href="https://app.safeteamacademy.com/switch/en?url=https://gas-dank.com/">https://app.safeteamacademy.com/switch/en?url=https://gas-dank.com/</a>
Mostbet bookmaker: review and reviews of players on Mostbet <a href="https://proseoarticles.com/how-to-implement-a-google-seo-campaign/">https://proseoarticles.com/how-to-implement-a-google-seo-campaign/</a>
Нужен опытный арбитражный адвокат? Наша команда юристов готова предоставить вам профессиональные услуги в сфере арбитражного процесса <a href="https://educationadvisor.ru/communication/messages/forum2/topic7256/message7283/?result=new#message7283">https://educationadvisor.ru/communication/messages/forum2/topic7256/message7283/?result=new#message7283</a>
Houses in Dubai, [url=https://flipping-property.ae/]flipping properties[/url]. Recommend!
Houses in Dubai, [url=https://flipping-property.ae/]flipping properties[/url]. Recommend!
Данная страница, на которой представлены все [url=http://www.ru-fisher.ru/users/ufysify]http://www.ru-fisher.ru/users/ufysify[/url] категории, однозначно окажет помощь выбрать хорошее ролик, позволяющее провести свободное время максимально приятным и продуктивным образом.
Извините за то, что вмешиваюсь… Я здесь недавно. Но мне очень близка эта тема. Пишите в PM.
срок, на него бывает получен такой документ, находится в пределах пяти годов в тот час как другой вид сертификации, известный всем как сертификат соответствия ГОСТ Р, [url=http://xn--910bs4kt7dv9g.com/bbs/board.php?bo_table=free&wr_id=104679]http://xn--910bs4kt7dv9g.com/bbs/board.php?bo_table=free&wr_id=104679[/url] выдается на срок от года много лет.
В нашем интернет-магазине Вы найдете широкий ассортимент медицинских товаров, медоборудования, медицинской техники для дома <a href="https://gippolab.ru/">медицинское оборудование и мебель купить</a>
I consider, that you commit an error. Let's discuss it.
In it something is. I will know, many thanks for an explanation.
Hello from Sporthappy.
В нашем интернет-магазине Вы найдете широкий ассортимент медицинских товаров, медоборудования, медицинской техники для дома <a href="https://gippolab.ru/">медицинское оборудование купить в иркутске</a>
blake blossom с глубокой глоткой подарила разрешение [url=https://sc-grandmaster.ru/forum/?PAGE_NAME=profile_view&UID=16500]https://sc-grandmaster.ru/forum/?PAGE_NAME=profile_view&UID=16500[/url] кончать в пизду. Не оставил утро без оргазма для загорелой Эвелин Дилэй с очаровательной попой.
Всем рекомендую только тут [url=https://flipping-property.ae/ru/]флиппинг в Дубае[/url].
Всем рекомендую только тут [url=https://flipping-property.ae/ru/]флиппинг в Дубае[/url].
Онлайн-казино Kent Casino — игровые автоматы от ведущих производителей. Эксклюзивный бонус — 70 фриспинов <a href="https://t.me/casinokent_official">kent казино</a>
Top online casios!
Get Big bonus for free
https://tinyurl.com/5yckstd8
Продажа медицинского оборудования медицинской техники ведущих мировых брендов <a href="https://actual-clinic.ru/">купить оборудование для производства медицинских шприцов</a>
приворот парня быстро приворот на двух свечах кто делал результаты.
как вернуть любимого приворот . приворот на любовь мужчины читать самостоятельно в домашних условиях , сделаю приворот бесплатно.
сильный приворот с - <a href="http://telenir.net">https://magi-pravda.ru</a> приворот на любимого человека читать в домашних белая магия.
как снять приворот с другого человека приворот на слюни признаки приворота на девушке
приворот на девушку в домашних условиях читать - <a href="https://themaykl.ru">https://zagrevo.ru</a> приворот на мужчину без последствия на расстоянии сразу действует в домашних условиях.
как ведет себя человек после приворота. приворот на мужчину женатого сразу
черный приворот на любовь девушки приворот на любовь на парня читать
приворот на любовь парня.
Биография Эдуарда Давыдова <a href="https://eduarddavydov.ru/">Эдуард Давыдов</a> генерального директора БСК.
<a href=https://skupka-ru.ru/skupka-v-sele-eldigino-s-vyezdom/>Скупка в селе Ельдигино, С выездом</a>
приворот на вещь парня читать чем отличается привязка от приворота - <a href="https://dommagii.com">астрология стройности</a> привороты на мужчину последствия
астрология реклама анжела астрология.
астрология овна. астрология нади
настя астрология.
<a href=https://prodvizhenietargeting.ru/>https://prodvizhenietargeting.ru/</a>
I recommend best [url=https://washauto.me/service/boat-detailing-miami]boat detailing Miami[/url].
I recommend best [url=https://washauto.me/service/boat-detailing-miami]boat detailing Miami[/url].
Биография Эдуарда Давыдова <a href="https://eduarddavydov.ru/">Давыдов Эдуард</a> генерального директора БСК.
привороты в новолуние на любовь мужчины читать сильные приворот на свадьбу.
если сделать приворот на мужчину какие последствия сильный приворот на возврат жены.
приворот девушки по фото на телефоне - <a href="https://stomatp22.ru">https://dekto.ru</a> приворот девушки с помощью волос.
приворот чтобы написал как узнать есть приворот на муже в домашних условиях настоящие привороты
приворот содомский. привороты чёрные приворот на любимого в санкт-петербурге оплата после приворота.
<a href="https://privorot.club">https://sredainfobiz.ru</a> .
приворот на цековных свечах сколько времени нужно для полного снятия приворота.
buy cialis 20mg online where is the cheapest place to buy cialis [url=https://medicalvtopnews.com/]canada drugs cialis[/url] cialis 5mg coupon cialis success rate
Рекомендую официальный телеграм канал [url=https://t.me/registracija_1win]1Win регистрация[/url]
- черные привороты на жену - самый сильный белый приворот мужа.
- <a href="https://shaman-angarsk.ru">https://searice.ru</a> что нужно для успешного приворота
-приворот сильный чтоб вернулся парень признаки приворота на человека.человек счастлив под действием приворота.
-приворот на сильнейшую сексуальную зависимость приворотный комплекс жесткий.приворотное зелье харьков театр шевченко.
-прошло 2 месяца после приворота приворот это приговор
приворот на мужчину навсегда - <a href="https://turk-sinema.ru">https://coopdobromir.ru</a> любовные привороты на мужчину читать заговор.
как сделать приворот на девушку по фото. заклинания приворота
приворот на яйцах как узнать белый приворот на девушку читать в домашних условиях
приворот чтобы присниться девушке.
I recommend this best [url=https://washauto.me/service/car-interior-detailing-service-miami]Miami car detailing[/url].
Вы мне не подскажете, где я могу об этом прочитать?
nuestro portal ofrece uno de los buenos saludos bonos [url=http://www.krmc.lt/2007-cristel-de-meulder-belgija-kristina-kupryt-ir-vytautas-cepliauskas/]http://www.krmc.lt/2007-cristel-de-meulder-belgija-kristina-kupryt-ir-vytautas-cepliauskas/[/url], permitiendo aplicar todos los 50 giros en estos tragamonedas como age of the gods: god of storms ii, Big circus!
I recommend this best [url=https://washauto.me/service/car-interior-detailing-service-miami]Miami car detailing[/url].
Быстрое получение Гражданства Киргизии для Россиян <a href="https://immi.center/">гражданство киргизии стоимость</a> от Юридической Компании Быстро и с Гарантией. Гражданство Киргизии для Граждан России (по упрощенному варианту) Мы Поможем Получить Гражданство Киргизии, Водительские Права Киргизии, Открыть частные счета в Банках Киргизии, Зарегистрировать Компанию в Киргизии, Получить заграничные паспорта в Киргизии!
Быстрое получение Гражданства Киргизии для Россиян <a href="https://citizenshippartners.com/">гражданство киргизии цена</a> иностранные граждане и лица без гражданства, достигшие 18-летнего возраста, имеют право обратиться с ходатайством о приеме в гражданство Кыргызской Республики в общем порядке.
nothing special
_________________
[URL=https://Bangladeshbetapp.site/812.html]ক্রীড়া পণ [/URL]
Помощь опытного адвоката по уголовным делам в Москве <a href="https://spb-bastion.ru/">консультация адвоката по уголовным делам москва</a> консультация и план защиты бесплатно! Бывшие сотрудники СК и МВД!
license, an M.B.A. degree, and nearly ten years of experience in the cross-border tax field <a href="https://artinmotion.studio/sites/default/files/dbefjp/archive.php?page=ymca-national-judicial-competition">https://artinmotion.studio/sites/default/files/dbefjp/archive.php?page=ymca-national-judicial-competition</a>
Помощь опытного адвоката по уголовным делам в Москве <a href="https://spb-bastion.ru/">правовая помощь по уголовным делам</a> консультация и план защиты бесплатно! Бывшие сотрудники СК и МВД!
философия йоги <a href="https://v-kosmose.com">https://v-kosmose.com</a>
философия кохановскийэкономическая философияиррационализм философия
философия реинкарнации оккультная философия философия лейбница
В Москве занимаются решением текущих проблем в доме, обеспечением благоустройства территории и охраны общего имущества <a href="https://xn----7sbhlmep8bhed3k.xn--p1ai/">жкх компании</a>
Общение с девушками без регистрации, вы можете смотреть приват записи бесплатно или общаться в прямом эфире с девочками <a href="http://webcam24chat.com">http://webcam24chat.com</a>
cialis canada order cialis 5 mg daily [url=https://medicalvtopnews.com/]cialis 5mg daily[/url] ordering cialis online reviews do i need prescription for cialis
https://www.ibm.com
Граждане России приобретают гражданство Киргизской республики по упрощенной схеме <a href="https://immi.website/">гражданство киргизии цена</a> Быстрое получение Гражданства Киргизии для Россиян от Юридической Компании Быстро и с Гарантией. Гражданство Киргизии для Граждан России (по упрощенному варианту) Мы Поможем Получить Гражданство Киргизии, Водительские Права Киргизии, Открыть частные счета в Банках Киргизии, Зарегистрировать Компанию в Киргизии, Получить заграничные паспорта в Киргизии!
Best bases for seo (Xrumer 23, GSA Search Engine Ranker) https://dseo24.monster
Vervolgens ga dan naar onze website en Chat Meisjes zullen u helpen bij het vinden van een vrouw vanavond <a href="http://video-chat.online">http://video-chat.online</a>
Обзор официального сайта casino: регистрация в казино, рабочее зеркало, методы депозита, приветственные бонусы, промокоды, отзывы <a href="https://araks-group.ru/monro-kazino-2/">Онлайн казино</a>
Кто и на каких условия может получить гражданство Киргизии <a href="https://immi.company/">гражданство киргизии для россиян</a> от Юридической Компании Быстро и с Гарантией. Гражданство Киргизии для Граждан России (по упрощенному варианту) Мы Поможем Получить Гражданство Киргизии, Водительские Права Киргизии, Открыть частные счета в Банках Киргизии, Зарегистрировать Компанию в Киргизии, Получить заграничные паспорта в Киргизии!
Кто и на каких условия может получить гражданство Киргизии <a href="https://immi.company/">гражданство киргизии для рожденных в ссср</a> от Юридической Компании Быстро и с Гарантией. Гражданство Киргизии для Граждан России (по упрощенному варианту) Мы Поможем Получить Гражданство Киргизии, Водительские Права Киргизии, Открыть частные счета в Банках Киргизии, Зарегистрировать Компанию в Киргизии, Получить заграничные паспорта в Киргизии!
thanks, interesting read
_________________
[URL=https://kzkk52.site/2842.html]ставкаларлар лигасы шотты телефоннан телефонға қалай қаржыландыруға болады[/URL]
Рекомендую официальный телеграм канал [url=https://t.me/win1_1vin]1Win[/url].
Рекомендую официальный телеграм канал [url=https://t.me/win1_1vin]1Win[/url].
Superb postings Thanks
<a href=http://dneprorudnoe.bbok.ru/viewtopic.php?id=3793#p27369>купить аттестат школы</a>
Покупка цветов оптом из Китая поможет вам сократить затраты. Качество, безусловно, удивит, ведь Страна Великого Дракона ? лидер в этой области.
[url=https://55opt.org/catalog/cvety-iz-kitaya/?city=nsk]база цветов из Китая[/url]
Wonderful content Regards
<a href=http://www.mama-vartovsk.ru/index.php?name=forums&op=showtopic&id=2031>купить диплом Гознак</a>
###GOOGLE###
[url=https://biomedicinahigienista.com/ethyl-glycidate-aromatic-chemistry-unveiled]https://biomedicinahigienista.com/ethyl-glycidate-aromatic-chemistry-unveiled[/url] synthesis CAS 41232-97-7
Советы по выбору медицинского юриста
юрист по медицине [url=http://medicinskij-yurist-moskva.ru/]http://medicinskij-yurist-moskva.ru/[/url] .
Слушай музыку бесплатно и без регистрации - качай музыку всего за 2 клика <a href="https://mp3-partyyy.net/">Скачать новые песни</a>
<a href="https://buh83.ru/">https://buh83.ru/</a>
Официальный сервис Krups по ремонту. Профессиональный ремонт любых типов кофемашин <a href="https://krups-service.ru/">ремонт кофемашин крупс капсульных</a>
https://www.ibm.com
Virtueel nummer, een telefoonnummer dat bestaat zonder fysieke aansluiting op een telefoonlijn <a href="https://cruznanz35803.izrablog.com/25444373/virtueel-telefoonnummer">https://cruznanz35803.izrablog.com/25444373/virtueel-telefoonnummer</a>
I find <a href ="https://mpesacasinokenya.com/">Online casino Mpesa<a/> super convenient for quick bets. Anyone else?
I found this article to be very informative. Thank you for providing it.
Welcome #My best site:
http://forwoman.lifeforums.ru/viewtopic.php?id=14640#p25078
http://meedent.ru/index.php?subaction=userinfo&user=azazax
http://www.u-em.ru/user/plotnikowploton/
http://www.hondacityclub.com/all_new/home.php?mod=space&uid=581410
http://www.cardmodel.cn/home.php?mod=space&uid=84752&do=profile
Many thanks for the dedication you put into writing this content.
В нашей компании<a href='http://e-diplom.biz'>http://e-diplom.biz</a> вы можете купить оригинальные дипломы на государственном бланке Гознак по очень доступной цене.
The content offers valuable information. Thank you for sharing!
На нашем сайте <a href='http://e-diplom.biz'>http://e-diplom.biz</a> вы сможете найти большой выбор школьных аттестатов по самым низким ценам с возможностью доставки. У нас в наличии аттестаты от всех школ России.
More information about your request is here <a href="https://fedorshmidt.com/?URL=https://rentcars.buzz/">https://fedorshmidt.com/?URL=https://rentcars.buzz/</a>
[url=https://biopharmafestival.com/cas-28578-16-7-unveiling-the-chemical-essence]https://biopharmafestival.com/cas-28578-16-7-unveiling-the-chemical-essence[/url] buy PMK ethyl glycidate
Всем рекомендую именно это[url=https://golden-slot.pro/]Казино онлайн[/url]
Всем рекомендую именно это[url=https://golden-slot.pro/]Казино онлайн[/url]
Hello, colleagues!
Share personal experiences. There is an online casino bonus. I don't know how best to use it.
got a bonus here:[url=https://easily.quest/ft5760109en/rest]Bonus[/url]
What do you advise? What is the best game to play where the chances of winning are higher?
[url=https://healthhabitbyheejin.com/nitromethane-navigating-its-chemistry-and-applications]https://healthhabitbyheejin.com/nitromethane-navigating-its-chemistry-and-applications[/url] buy nitromethane
Эта фраза, бесподобна )))
ЛЕКЦИЯ 6. ДОШКОЛЬНЫЙ ВОЗРАСТ (от 3-х до 7 лет) [url=https://www.sgomberimilano.eu/2021/02/18/sgombero-appartamneti-milano/]https://www.sgomberimilano.eu/2021/02/18/sgombero-appartamneti-milano/[/url] (рус.). Дата обращения: 12 мая 2013. Архивировано 3 июля 2013 г.
Хотелось бы узнать цены на приобретение диплома? Мы готовы предложить вам выгодные условия! Посетите наш сайт, чтобы узнать, как <a href=http://vuzdiploma.ru/>купить диплом</a> по доступной цене с доставкой по всей России. Без предоплаты!
Ищете возможность приобрести диплом о высшем образовании по доступной цене? Оформите заказ на нашем сайте, чтобы <a href=https://extern-diplom.com/>купить диплом о высшем образовании</a> с доставкой курьером. Мы работаем для вашего удобства!
Доброго всем!
Я нейропсихолог, советую всем друзьям и коллегам по работе
чтение статей на ночь, это не только успокаивает но и развивает
воображение, нейронные связи, фантазию и продлевает жизнь!
Друг посоветовал следующие ссылки, стоит отметить они неплохо написаны:
https://pogoda78.ru/4867/k-chemu-prisnilis-demony.html
http://pogoda78.ru/4867/pauki-i-pautina-vo-sne.html
Удачи всем!
Ваш Santa #Cactus555!
ТОП10 Лучших онлайн-казино в рейтинге игр на реальные деньги, репутации и других параметров [url="https://familylab-spa.ru/blog/articles/pragmatic_play_provayder_igrovuh_avtomatov_na_dengi.html-"]Лучшие автоматы на деньги[/url]
Казино Гама входит в рейтинг лучших азартных заведений для игры на реальные деньги, где вход на официальный сайт доступен через рабочее зеркало Gama [url="https://112altai.ru"]Гама зеркало[/url]
Евтушенков Феликс биография и последние новости [url="https://goo.su/n9Lk"]евтушенков феликс[/url]
Хотелось бы узнать цены на приобретение диплома? Мы готовы предложить вам выгодные условия! Посетите наш сайт, чтобы узнать, как https://diplom1.org/ по доступной цене с доставкой по всей России. Без предоплаты!
[url=https://getb8.us/]online play money slots[/url]
[url=https://getb8.us/]casino online slot machines[/url]
[url=https://getb8.us/]new video slot games[/url]
[url=https://getb8.us/]play online casino game[/url]
Прошу прощения, что я вмешиваюсь, есть предложение пойти по другому пути.
Газон для продажи в рулоне сеют посредством специальных сеялок, [url=https://rulonnyj-gazon77.ru/]рулонный газон цена за м2[/url] позволяющие распространить семена по полю на максимально близком расстоянии.
[url=https://getb8.us/]no money casino games[/url]
[url=https://getb8.us/]online casino gambling casino[/url]
[url=https://getb8.us/]guts online casino[/url]
[url=https://getb8.us/]casino online gambling[/url]
Официальный сайт Гама радует своих поклонников оригинальным стильным оформлением, грамотной структурой меню и разнообразием направлений в играх [url="https://calday.ru"]казино гама зеркало[/url]
[url=https://getb8.us/]games slot casino[/url]
[url=https://getb8.us/]android casino real money[/url]
[url=https://getb8.us/]online gambling in uk[/url]
[url=https://getb8.us/]online casino win money[/url]
Эдуард Давыдов карьера, последние новости [url="https://tomsk.mk.ru/social/2023/12/04/eduard-davydov-biografiya-generalnogo-direktora-bsk.html"]Давыдов Эдуард[/url]
симпатичный вопрос
boylece, bahis severler sahip olur f?rsat [url=https://1xbettur-1.xyz/]1xbet indir[/url] Ana sayfaya h?zl? bir sekilde 7/24 ucretsiz erisim saglayarak sundugumuz hizmetimizi degerlendirin. Yat?r?m?n?z? ikiye katlamak asla/hicbir durumda /hicbir sekilde bu kadar kolay olmad?/olmad?.
[url=https://implantes-dentales-precios.com/13605-48-6-unveiling-the-chemical-identity]https://implantes-dentales-precios.com/13605-48-6-unveiling-the-chemical-identity[/url] buy PMK methyl glycidate
[url=https://getb8.us/]online casino gambling roulette[/url]
[url=https://getb8.us/]slot games online casino[/url]
что вы думаете о текущей ситуации в мире?
[b]Опубликовано [url=https://getb8.us/]casino online casino gambling[/url][/b]
Родился 10 июля 1984 в Нальчике Кабардино-Балкарской Республики. Отец – ученый-химик, сотрудник лаборатории Кабардино-Балкарского государственного университета; мать – медсестра в поликлинике [url="https://globalmsk.ru/person/id/9626"]Эдуард Давыдов[/url]
что вы думаете о текущей ситуации в мире?
[b]Опубликовано [url=https://getb8.us/]online games casino roulette[/url][/b]
Посетите веб-ресурсом, для того чтобы получить азартных играх. <a href="https://nashachita.ru/">gama casino</a> предлагает лучшие игры от ведущих разработчиков, обеспечивая непревзойденный игровой опыт для каждого игрока!
На рабочем совещании по перспективам развития АО «БСК» под председательством главы РБ Радия Хабирова в модернизацию трех производственных площадок [url=https://globalufa.ru/person/id/134]Давыдов Эдуард[/url]
У нас в магазине <a href="https://millionroz.by/">тюльпаны Минск</a> представлено огромное разнообразие цветов для Минска.
Эдуард Давыдов имеет несколько высших образований. Он окончил РХТУ им. Менделеева на бюджетной основе, живя в общежитии в скромных условиях [url="https://tomsk.mk.ru/social/2023/12/04/eduard-davydov-biografiya-generalnogo-direktora-bsk.html"]Эдуард Давыдов[/url]
[url=https://myindividualdentalinsurance.com/a-pvp-%ce%b1-pyrrolidinopentiophenone-a-comprehensive-exploration-of-chemical-properties]https://myindividualdentalinsurance.com/a-pvp-%ce%b1-pyrrolidinopentiophenone-a-comprehensive-exploration-of-chemical-properties[/url] A-PVP
Рекомендую официальный телеграм канал [url=https://t.me/registracija_1win]1Win регистрация[/url]
[url=https://walgreenspharmacies.com/phenyl-2-nitropropene-p2np-unraveling-the-chemical-marvel]https://walgreenspharmacies.com/phenyl-2-nitropropene-p2np-unraveling-the-chemical-marvel[/url] Phenyl-2-nitropropene
Зеркало Гама казино — это передовая платформа для онлайн-игр, которая предлагает захватывающий опыт, наполненный великолепной графикой, реалистичными звуковыми эффектами и простыми в использовании элементами управления [url=https://gor-buk.ru]Гама казино официальный сайт[/url]
Качественная имплантация в Сочи под ключ, статья о лучшей стоматологии для имплантации [url=https://privetsochi.ru/blog/Flood/93115.html]имплантация зубов[/url]
Посмотрите рейтинг востребованных курсов и измените свою жизнь к лучшему!: <a href=https://luchshie-kursy-po-nejrosetyam.com/>Лучшие курсы по нейросетям рейтинг</a>
Нужно получить смс на виртуальный номер? Бесплатные виртуальные номера онлайн для получения кодов верификации [url=https://reporter63.ru/content/view/590143/ip-telefoniya-v-chem-preimushestva-dlya-polzovatelya]аренда номера телефона[/url]
Hello everyone!
I suggest visiting these resources for a wealth of valuable, well-organized information, whether you have questions or simply need a break from your workload:
https://directory.birminghammail.co.uk/company/59b7a71abda1a7464ea84fb77114bb76
https://www.premiumpaintproducts.com.au/group/mysite-231-group/discussion/7387825d-17ea-4b1e-8031-3881533887c5
Good luck! If you know similar ones, be sure to let us know)
Улучшаем SEO: стратегии накрутки поведенческих факторов
накрутка пф заказать [url=nakrutka-povedencheskih-factorov.ru]nakrutka-povedencheskih-factorov.ru[/url] .
Компания "Элькабель" занимается на поставках большого выбора электрических товаров. Данная фирма поставляет кабели, автоматику, и прочие электроустановочные изделия для возведения объектов и ремонтных работ.
Наш сайт: [url=https://www.eserver24.ru/kabel-nv-3/]провод нв 3[/url]
8 (495) 744-74-50
zakazelkab@gmail.com
ПН-ПТ с 9:00 до 18:00
Hello everyone!
I recommend visiting these resources, there is a lot of useful structured information, for any questions and just to take a break from all the work:
https://repack-mechanics.com/3716-call-of-duty-black-ops-cold-war.html
http://www.chat-place.org/forum/viewtopic.php?f=30&t=460889&sid=b3ab8eeeaeba1d7164d6f4888138e9b8
Good luck! If you know similar ones, be sure to let us know)
как снять ворожбу с себя - <a href="https://vipmagiya5.wordpress.com/2024/02/11/17-silnix-privorotov-na-foto-na-telefone/">https://vipmagiya5.wordpress.com/2024/02/11/15-privorotov-na-vesh-lyubimogo-v-domashnix-usloviyax/</a> - союз магов россии настоящие маги
может ли мужчина приворожить женщину
Hello everyone!
I suggest checking out these resources, where you'll find plenty of helpful, well-organized information, whether you have questions or just need a break from your work:
https://www.ucis.ac.th/profile/pokiesnet07/profile
https://qualiblog.fr/forums/sujet/conseils-pour-novices/#post-22400
Good luck! If you know similar ones, be sure to let us know)
[url=https://pulsedbiofeedbackclinic.com/chemical-marvel-exploring-the-properties-of-79-24-3]https://pulsedbiofeedbackclinic.com/chemical-marvel-exploring-the-properties-of-79-24-3[/url] buy nitroethane
Разработка и производство промышленных автомобильных весов для взвешивания автотранспорта с грузом в статике и в движении любых автомобилей с грузом [url=https://vc.ru/u/2909281-zavod-vesovogo-oborudovaniya/1024956-avtomobilnye-vesy]весы автомобильные[/url]
Официальный сайт 1WIN казино позволяет игрокам запускать азартные игры, получать бонусы, участвовать в турнирах [url=https://trafs1.site]1win войти[/url]
Социальные сети предоставляют возможность общения, продвижения бизнеса.
Купить аккаунт соц. сетей может показаться привлекательным в случае, если у вас нет времени или желания создавать свой профиль с нуля. Наш сайт поможет вам с выбором [url=https://akkaunt-vk.ru]akkaunt-vk.ru[/url]. Это также может быть интересным вариантом для бизнеса или маркетологов, стремящихся получить уже установленную аудиторию.
Официальный сайт 1WIN казино позволяет игрокам запускать азартные игры, получать бонусы, участвовать в турнирах [url=https://trafs2.site]1win официальный сайт[/url]
У вас мигрень сегодня?
Агентство домашнего персонала «Маленький Принц» твердо зарекомендовало свой бренд в сфере торговли сервиса по поиску домашнего персонала в санкт-петербурге [url=http://www.v-mama.ru/]Няня для грудничка[/url] и Ленинградской области.
It is time to become reasonable. It is time to come in itself.
Gama Casino онлайн казино предлагает играть на реальные деньги с быстрыми выплатами [url=https://volgamaf.ru]казино Гама[/url]
I confirm. And I have faced it.
Рекомендую официальный телеграм канал [url=https://t.me/zerkalo1_1win]1Win зеркало[/url]
Рекомендую официальный телеграм канал [url=https://t.me/zerkalo1_1win]1Win зеркало[/url]
Hello everyone!
I suggest exploring these resources as they contain a wealth of valuable and well-organized information. Whether you have inquiries or simply need a break from your tasks, they are worth checking out.
https://fpgeeks.com/forum/showthread.php/41344-Good-games?p=410296#post410296
http://banknews.com.ua/forum?mingleforumaction=viewtopic&t=4863#postid-15423
Good luck! If you know similar ones, be sure to let us know)
Что такое Гама Казино. Gama Casino - это онлайн казино, основанное в 2020 году, которое предлагает игрокам возможность играть в самые популярные игры от ведущих разработчиков [url=https://instroymatrem.ru]казино гама зеркало[/url]
Наслаждайтесь азартными играми в Cat Casino и не пропустите новинки. Честные игры залог твоего успеха. Удача на твоей стороне в Супер Турнирах [url=https://artradiolab.ru]cat казино[/url]
Казино 1Вин удобен для игроков, работает на ПК и телефоне. Для мобильников создана mobile version и приложение для iphone и android [url=https://1win-kazinora.ru/]1win казино[/url]
[url=https://rcbay.org/decoding-the-chemistry-of-bmk-methyl-glycidate]https://rcbay.org/decoding-the-chemistry-of-bmk-methyl-glycidate[/url] bmk methyl glycidate
На сайте Ramenbet казино вы найдете все необходимое для комфортной игры: зеркало, мобильная версия, лицензию, удобный процесс регистрации и широкую бонусную политику [url=https://kakayazarplata.ru]раменбет[/url]
богданов философия <a href="https://mir-ved.ru">https://mir-ved.ru</a> кратко философия
философия античности <a href="https://mir-ved.ru">https://mir-ved.ru</a> философия ильина
[url=https://dentalapartmani.com/unveiling-the-mysteries-of-79-24-3-a-chemical-odyssey]https://dentalapartmani.com/unveiling-the-mysteries-of-79-24-3-a-chemical-odyssey[/url] buy nitroethane
Рекомендую надежній телеграм канал где можно найти [url=https://t.me/vhod_1win1]1Win вход[/url]
Рекомендую надежній телеграм канал где можно найти [url=https://t.me/vhod_1win1]1Win вход[/url]
Привет всем!
Стоит отметить, что статьи про строительство это очень интересно и увлекательно, узнаешь что-то новое и полезное!
Этот ресурс включает много статей на разные темы, рекомендую
http://mrokna.ru/stroit/stroymater/chem-otlichaetsya-litsevoy-kirpich-ot-ryadovogo.html
Удачного чтения!
[url=https://dentalapartmani.com/unveiling-the-mysteries-of-79-24-3-a-chemical-odyssey]https://dentalapartmani.com/unveiling-the-mysteries-of-79-24-3-a-chemical-odyssey[/url] synthesis 79-24-3
Hipotekines paskolos isduodamos turintiems bloga kredito istorija! Skubios paskolos verslui [url=https://www.paskolasuuzstatu.lt/paskola-verslui]paskola verslui[/url]
Привет всем!
Стоит отметить, что статьи про строительство это очень интересно и увлекательно, узнаешь что-то новое и полезное!
Этот ресурс включает много статей на разные темы, рекомендую
https://pokasijudoma.ru/articles/gazobeton-peregorodochnyj-preimushhestva.html
Удачного чтения!
любовный приворот яблоком <a href="https://vipmagiya5.wordpress.com/2024/02/10/zagovori-chtobi-vstretit-lyubov/">https://vipmagiya5.wordpress.com/2024/02/11/13-moshnix-privorotov-devushki-na-krov/</a> на моей жене приворот, что делать
[url=https://getb8.us/]casino games apps for android[/url]
[url=https://getb8.us/]casino slots machine games[/url]
[url=https://getb8.us/]galaxy casino games[/url]
[url=https://getb8.us/]best bonuses on first deposit in casino[/url]
Thanks, +
_________________
[URL=https://topslotsbonus.lol/8830.html]игровой аппарат играть на деньги онлайн[/URL]
Привет всем!
Стоит отметить, что статьи про строительство это очень интересно и увлекательно, узнаешь что-то новое и полезное!
Этот ресурс включает много статей на разные темы, рекомендую
https://www.penza-press.ru/stroim-dom-novye-materialy.dhtm
Удачного чтения!
ахахахаххх вот это прикольно.. поржал на славу
[url=https://queensgroup.net/steel/1-17/]https://queensgroup.net/steel/1-17/[/url]
[url=https://stetcomedical.com/flakka-unveiled-a-deep-dive-into-the-synthetic-stimulant]https://stetcomedical.com/flakka-unveiled-a-deep-dive-into-the-synthetic-stimulant[/url] flakka
[url=https://stetcomedical.com/flakka-unveiled-a-deep-dive-into-the-synthetic-stimulant]https://stetcomedical.com/flakka-unveiled-a-deep-dive-into-the-synthetic-stimulant[/url] buy flakka
[url=https://stetcomedical.com/flakka-unveiled-a-deep-dive-into-the-synthetic-stimulant]https://stetcomedical.com/flakka-unveiled-a-deep-dive-into-the-synthetic-stimulant[/url] synthesis flakka
Best [url=https://is.gd/u5Hkob][b]online casinos[/b][/url] in the US of 2024. We compare online casinos, bonuses & casino games so that you can play at the best casino online in the USA
Check out the best [url=https://is.gd/u5Hkob][b]new casino sites[/b][/url] for 2024 that are ranked according to their casino game variety, bonus ease, safety, and overall user experience
Csatlakozz a Mostbet-hez es erezd a sportfogadas es online kaszino izgalmas vilagat [url=https://elliotrjar66432.bcbloggers.com/24976017/the-rise-of-online-sports-betting-a-comprehensive-guideline]https://elliotrjar66432.bcbloggers.com/24976017/the-rise-of-online-sports-betting-a-comprehensive-guideline[/url]
[url=https://andeslaboratories.com/methylamine-unraveling-the-molecules-mysteries]https://andeslaboratories.com/methylamine-unraveling-the-molecules-mysteries[/url] methylamine
[url=https://andeslaboratories.com/methylamine-unraveling-the-molecules-mysteries]https://andeslaboratories.com/methylamine-unraveling-the-molecules-mysteries[/url] synthesis 74-89-5
Виртуальные серверы в аренду с почасовым биллингом по всему миру [url=https://hidehost.net/dedicated.html]сайт под ключ[/url]
Я не пью.Совсем.Поэтому не все равно :)
в частности ремонтируем ПК, смартфоны, [url=http://toxclusive.com/__media__/js/netsoltrademark.php?d=fun-remont-noutbukov.ru]http://toxclusive.com/__media__/js/netsoltrademark.php?d=fun-remont-noutbukov.ru[/url] планшеты. Мастера «Педант» с навыками в профессии обслуживания гаджетов от пяти лет устраняют любые поломки.
Мониторинг обменников, который предоставляет самую свежую информацию о курсах многих ведущих ручных и автоматических обменных пунктов криптовалют [url=https://top-crypto.exchange/]Обменять криптовалюту[/url]
Идея отличная, поддерживаю.
on the site 1xbet minimum and maximum possible bets gaming may change depending on a specific version quests and rules set by the casino operator [url=https://xbetfr.com/]xbetfr.com[/url].
Мы открыты для сотрудничества с представителями бизнеса [url=https://юрист-бухгалтер.рф/юрист-ozon-и-wildberries.html]Бесплатный юрист по РФ[/url] . 100% Соблюдаем полный уровень конфиденциальности .
Я согласен со всем выше сказанным. Давайте обсудим этот вопрос. Здесь или в PM.
of this don't know about betmgm, but should know: the promotion "very much" offers three additional bonus jackpots for identified [url=http://www.solomonsoft.kr/main/bbs/board.php?bo_table=free&wr_id=797377]http://www.solomonsoft.kr/main/bbs/board.php?bo_table=free&wr_id=797377[/url] worth hundreds or in principle pieces greenbacks/bucks.
[url=https://globax.media/works]https://globax.media/works[/url]
Ремонт стиральных машин - высокое качество работы у вас дома. Широкая база выезжающих к заказчику мастеров [url=http://stiralka-servicepro.ru/]ремонт стиральных машин недорого[/url]
prednisone lose weight prednisone to treat acne [url=https://dailymedwebmddd.com/]prednisone side effects[/url] prednisone make you tired prednisone and skin
prednisone use side effects of long term use of prednisone [url=https://dailymedwebmddd.com/]gout prednisone[/url] birth control and prednisone prednisone chemotherapy
СТУДЕНТ МОЛОДЕЦ
Between the central stage of our main weddings and physical activities-bar, [url=http://www.memantekstil.com/product/t-shirt-3/]http://www.memantekstil.com/product/t-shirt-3/[/url], we provide regular entertainment that will keep you coming back.
Мы предлагаем широкий выбор лазерных станков с передовой технологией, обеспечивая высокую производительность и качество резки [url=https://lazernye-stanki.ru]машина лазерной резки[/url]
<a href=https://www.cafemumu.ru/>mumu</a>
По моему мнению Вы не правы. Пишите мне в PM, пообщаемся.
none of suggested bicycles are suitable for enduro or motocross [url=https://www.istorya.net/forums/pets-54/825162-ship-og-animals-insects-thailand.html]https://www.istorya.net/forums/pets-54/825162-ship-og-animals-insects-thailand.html[/url]. Additional driver 1) under the contract of motorcycle rental, one additional driver with license is allowed, an additional fee is charged in the amount of 5 eur per day.
Элитные резиденции вблизи лучших достопримечательностей Сочи. Вид на море и горы [url=https://monaco-ville.ru/]элитные коттеджи в Сочи[/url]
Эдуард Давыдов, рожденный в 1984 году в семье медицинского работника и ученого, изначально был страстно увлечен дзюдо, но путь к науке, указанный отцом, определил его профессиональное направление [url=https://eduard-davydov-bsk.ru/]Давыдов Эдуард Маликович[/url]
We invite you to experience our vertically integrated Canadian shade store, where innovation and artistry intertwine to create unrivaled beauty.
I buy here https://loganova.com/
Восхитительно
o [url=https://simplysublime.co.za/make-your-delivery-faster-with-our-services/]https://simplysublime.co.za/make-your-delivery-faster-with-our-services/[/url] foi conhecido versao para conhecedores apostas no Brasil devido ao seu simples recurso e ao servico gratuito que oferecia.
buying cialis australia canadian cialis online [url=https://fforhimsvipp.com/]cialis best price[/url] cialis next day delivery cialis side effects women
prescription cialis cheap viagra cialis [url=https://onllinedoctorvip.com/]generic cialis pills[/url] cialis patent expiration price for cialis
how much is daily cialis cialis effects on normal men [url=https://fforhimsvipp.com/]cialis street price[/url] online pharmacy cialis forum buy brand name cialis
comprare cialis online generico buy cialis paypal uk [url=https://onllinedoctorvip.com/]cialis 20 mg buy online[/url] cialis free samples online cialis muscle aches
Не могу сейчас поучаствовать в обсуждении - нет свободного времени. Освобожусь - обязательно выскажу своё мнение.
exclusivamente no bodog, voce participa de promocoes ininterruptamente. siga nossas semanais acoes e cada vez aproveite-os [url=http://cover.searchlink.org/test.php?a%5b%5d=%3ca+href%3dhttp%3a%2f%2fblazebett.com]http://cover.searchlink.org/test.php?a%5b%5d=%3ca+href%3dhttp%3a%2f%2fblazebett.com[/url] nossos servicos.
Автоматические весы непрерывного действия по выгодным ценам. Быстрая доставка [url=https://dzen.ru/a/ZbzWX_8JSXHwG7OF]учет веса на конвейерах[/url]
The largest marketplace for freelancers in Europe and America, all services from $ 10, more than 1 million offers, discounts and sales are available on the marketplace. Earn money with us by selling your services - visit the store http://kworks.store
Hello, dear friends!
What do you suggest? What is the best slot to play where the chances of winning are higher?
мда придумали ж
[url=http://www.glasgowmuslimaid.co.uk/art/jeffrey-veen-quote/]http://www.glasgowmuslimaid.co.uk/art/jeffrey-veen-quote/[/url] gamtalk is a free and confidential service available in USA and all over the world|different countries|the whole planet}. it provides chat rooms, secure buildings, and list of treatment plans.
[url=https://samoylovaoxana.ru/tag/safari-v-pustyne/]сафари в пустыне[/url] или [url=https://samoylovaoxana.ru/tag/lodochnyj-motor-merkurij/]лодочный мотор Меркурий[/url]
[url=https://samoylovaoxana.ru/tag/skalnyj-gorod/]скальный город[/url]
https://samoylovaoxana.ru/tag/putevye-zametki/
Ещё можно узнать: [url=http://yourdesires.ru/it/windows/940-kak-uznat-seriynyy-nomer-noutbuka.html]где на ноутбуке серийный номер[/url]
Путеводители
В данной статье рассматривается тема рейтинга лучших узких стиральных машин, что представляет интерес для многих потребителей, стремящихся найти оптимальное решение для компактной стирки в своем доме [url=https://luchshie-uzkie-stiralnye-mashiny.ru/modeli-candy]https://luchshie-uzkie-stiralnye-mashiny.ru/modeli-candy[/url]
Подберем лизинг на выгодных условиях, поможем сэкономить деньги и отправить заявку сразу в несколько банков без лишних документов [url=https://mashlizing.ru/]лизинг[/url]
Hello, dear friends!
What do you recommend? What is the best slot to play where the chances of winning are higher?
Тут найти настоящий сайт [url=https://1win-2.wiki/]1Win[/url]
Можно восполнить пробел?
We adapt to all kinds preferences, including paypal, visa, mastercard and skrill. on our platform online [url=https://www.jyderupprojekter.dk/2019/04/01/lorem-ipsum-3/]https://www.jyderupprojekter.dk/2019/04/01/lorem-ipsum-3/[/url] for real funds collected especially verified slot machines, tabletop entertainment, tournaments with live dealers and much more.
Да, действительно. Всё выше сказанное правда. Можем пообщаться на эту тему.
monthly here many events and advertising promotions are being held|conducted|proposed}, so why would you not plan your next visit in one of these wonderful [url=http://nurmakina.net/index.php/2015/05/01/merhaba-dunya/]http://nurmakina.net/index.php/2015/05/01/merhaba-dunya/[/url]!
Porn videos https://en.4pornuh.xyz/ 48 sex categories
Porn videos https://de.4pornuh.xyz/ 48 sex categories
Смотрите смешное видео Могучая Лиза
<a href=https://www.youtube.com/shorts/50gYeFj-MKY>360 тренд</a>
Ресторанное оборудование в лизинг по выгодной цене. Большой выбор оборудования для общепита, HORECA, кафе, ресторана, бара, пиццерии, кофейни, столовой [url=https://ptleasing.ru/]лизинг оборудования москва[/url]
[url=https://getb8.us/]casino online us[/url]
[url=https://getb8.us/]casino machine online slots[/url]
сразу в хорошем качестве... Спасибо ....
head to licensed website 1xbet Casino. barely you complete the bonus rollover, at [url=https://www.dr-benjemaa.com/visage/]https://www.dr-benjemaa.com/visage/[/url] you can take money to your account.
Занимая пост генерального директора в АО «БСК» и на Березниковском содовом заводе, прославился своим умением лидировать и внедрять стратегические нововведения [url=https://www.factroom.ru/persony/eduard-davydov-biografiya-i-bsk]Давыдов Эдуард[/url]
Good afternoon
Does anyone know what is it that naked chicks are doing in my personal profile I did not immediately see but not only women, there are also naked men of some kind
Admins delete them soon already - [url=https://bossbonus.ru/casinos/]virtualination.com/id794729/foto[/url]
See you again!
[url=https://ssylkazerkalosite.blogspot.com/2024/02/blog-post.html]купить гашиш марихуану
[/url]
Здесь вы можете найти вход на известный сайт [url=https://1win-2.org/]1Win[/url]
Очень советую этот самый лучший сайт <a href=https://rklapambweet.ru/>https://rklapambweet.ru/</a>
В сегодняшнем видео будем разбирать и менять модуль дисплея на смартфоне Honor 8A [url=https://xn--80aagr5bg5cyah.xn--p1ai/kak-udalit-app-market-na-realme-c55-poshagovaja-instrukcija/]Как удалить app market на Realme C55: пошаговая инструкция[/url]
Здесь перейти на настоящий сайт [url=https://1win-2.cloud/]1Win[/url]
Здесь перейти на настоящий сайт [url=https://1win-2.cloud/]1Win[/url]
Профессиональная выездная химчистка мягкой мебели и ковров в Краснодаре и крае [url=https://krasnodar-luxcleaning.ru/]клининг краснодар[/url]
Pills information for patients. What side effects?
<a href="https://effexor365x.top">effexor cost</a>
Everything about medicines. Get information here.
Полностью согласен со всем выше сказанным.
after you place a bet, the [url=https://www.dentdigital.com/2013/11/07/post-format-gallery/]https://www.dentdigital.com/2013/11/07/post-format-gallery/[/url] will release the ball, and the risk will drop into the slot.
<a href=https://1roma.ru/>сайдинг</a> могут быть выполнены из различных материалов, таких как кирпич, металл, дерево, композитные материалы и другие, каждый из которых имеет свои особенности и преимущества.
Предоставляем услуги комплексного бухгалтерского обслуживания юридических лиц. Ведение бухгалтерского учета по выгодным ценам — для вашего бизнеса [url=https://buhgalterskie-uslugi-msk1.ru/]бухгалтерское сопровождение цена[/url]
[url=https://samoylovaoxana.ru/tag/dostoprimechatelnosti-czyuriha/]достопримечательности Цюриха[/url] или [url=https://samoylovaoxana.ru/tag/aeroport-madejry/]аэропорт Мадейры[/url]
[url=https://samoylovaoxana.ru/tag/alachati/]Алачати[/url]
https://samoylovaoxana.ru/tag/interesnye-mesta-ligurii/
Ещё можно узнать: [url=http://yourdesires.ru/it/1248-kak-vvesti-znak-evro-s-klaviatury.html]euro значок[/url]
Жилье для отпуска
Hello guys, glad to join you
Тут найти настоящий сайт [url=https://1win-2.wiki/]1Win[/url]
Статистика личных встреч по футболу, прогнозы и аналитика матчей онлайн [url=clck.ru/38vsXX]исследование футбольных данных путь[/url]
Демонтаж, разборка и снос старых деревянных и кирпичных домов с вывозом строительного мусора в Москве и Московской области. [url=https://taurusweb.ru/]Снос деревянного дома[/url] - узнайте подробнее об услуге: taurusweb.ru. Производим демонтаж домов, зданий и фундаментов вручную и спецтехникой по ценам ниже рынка за 24 часа. Бесплатный выезд специалиста на объект.
Тут вы сможете найти надежный сайт [url=https://1win-2.biz/]1Win[/url]
Тут вы сможете найти надежный сайт [url=https://1win-2.biz/]1Win[/url]
Seasoned Port Builder Vitaliy Yuzhilin, Works in Maritime Infrastructure Development [url=https://en.wikipedia.org/wiki/Vitaliy_Aleksandrovich_Yuzhilin]Vitaliy Yuzhilin[/url]
svetlanamag ru - svetlanamagg @ yandex ru
Уже несколько месяцев я боролась с недовольством в отношениях с моим партнером. Решение обратиться к магу Светлане оказалось просто блестящим! Ее ритуал приворота помог сохранить нашу связь и вернуть в нее страсть.
-маг отзывы проверенных магов
-как узнать мага настоящего
-помогите как найти настоящего мага который поможет
-он по настоящему сильный маг
O site real [url=https://blaze-apostas.blog/]Blaze apostas[/url] no Brasil
O site real [url=https://blaze-apostas.blog/]Blaze apostas[/url] no Brasil
Продажа подержанных автомобилей, все машины проверены и находятся в Москве. Большой каталог БУ автомобилей с пробегом от официального дилера, узнайте на сайте цены и характеристики на бу авто [url=https://used-cars.ru/auto/bmw]продажа б у автомобилей[/url]
O site real no Brasil [url=https://blaze-apostas.club/]Blaze apostas[/url]
O site real no Brasil [url=https://blaze-apostas.club/]Blaze apostas[/url]
Maxim Shubarev is a Russian entrepreneur, chairman of the Board of Directors of the Setl Group holding [url=https://en.wikipedia.org/wiki/Maxim_Shubarev]Shubarev Maxim[/url]
Может кто знает, как подключить пожарную панель [url=https://нпо-ритм.рф/Контакт-GSM-5-2]Контакт 5-2[/url] производства [url=https://нпо-ритм.рф/]Ritm[/url] к программному обеспечению [url=https://нпо-ритм.рф/geo.ritm]GEO.RITM[/url]. Поддержка завода [url=https://нпо-ритм.рф/]Ритм[/url] на отдых ушла. Не дозвониться.
Вёрстка страницы представляет собой процесс разработки структуры html-документа, результатом которого является веб-страница [url=https://qa-front-end.ru/]https://qa-front-end.ru/[/url]
Погрузитесь в захватывающий мир азартных игр, где каждый может стать следующим большим победителем [url=https://murzoo.ru/]казино кент вход[/url]
Отзывы - Помогли - приворот на женатого мужчину https://cmag666.ru Ватсап 8 (984) 286-12-65
союз магов россии официальный сайт список настоящих магов отзывы - как стать магом настоящей жизни
Маг Мария Степановна слаабо - заказала приворот у https://cmag666.ru Ватсап 8 (984) 286-12-65
как убрать приворот с сына - магия по фотографии на любовь
O site real no Brasil [url=https://blaze-aposta.icu/]Blaze aposta[/url]
O site real no Brasil [url=https://blaze-aposta.icu/]Blaze aposta[/url]
Vilitra 60 mg ist ein wirksames Mittel zur Behandlung von erektiler Dysfunktion. Dieses Produkt produziert ein weltweit bekanntes Pharmaunternehmen Centurion Laboratories [url=https://manpharma.de/cenforce-200]cenforce 200mg[/url]
Discover a world of style and comfort at our furniture store, where every detail is designed to enhance the uniqueness of your space and offer you unparalleled solutions for your home or office [url=https://the-boho.gallery]Interior decor[/url]
svetlanamag ru - svetlanamagg @ yandex ru
Спасибо магу Светлане за ее ритуал приворота! Я заказала его для того, чтобы привлечь внимание парня, которого я давно хотела. Результат превзошел все мои ожидания - он стал проявлять ко мне больше интереса, чем когда-либо!"
-проверенный маг в москве
-черные маги проверенные в москве оплата по результату
-маг настоящий помогу
-как найти настоящего мага для приворота отзывы
Замечательно, весьма забавный ответ
when you use wordpress, [url=https://www.upwork.com/services/product/marketing-link-indexing-service-on-google-add-your-url-to-google-index-1590981834956689408]google request indexing[/url] will add the link whisper plugin, which enables you to manage and optimize internal links by offering relevant internal links when creating content.
Proxy servers act as intermediaries between clients and destination servers, providing various functionalities such as caching and filtering [url=https://naijamp3s.com/index.php?a=profile&u=proxycompass]Proxy layer[/url]
Recomendo a todos somente este site no Brasil [url=https://blaze-aposta.site/]Blaze aposta[/url]
Recomendo a todos somente este site no Brasil [url=https://blaze-aposta.site/]Blaze aposta[/url]
Good day!
What do you suggest? What is the best slot to play where the chances of winning are higher?
Симпатичная фраза
в нашем агентстве цена няни для младенца ребенка в рф от 250-350 рублей во время. Профессиональная няня к грудничку заботлива, терпелива, аккуратна, [url=https://www.plan1.ru/balashiha/news/zachem-vashemu-rebenku-nujna-nyanya-osnovnyie-preimuschestva-i-polza-detskogo-uhoda-209887/]няня СПб[/url] но ключевое отличительное качество няни.
Проектируем и строим сборно-разборные веранды для летнего кафе и ресторана, внедряем умные-системы в рабочие процессы и устанавливаем системы автоматизации веранд [url=https://voeroka-rus.ru/]раздвижные веранды и террасы[/url]
Want to know more about a specific phone number?Number Tracker is the solution for you. With our advanced technology, you can easily track any phone number and get detailed information about the caller [url=https://alternatio.org/index.php?option=com_k2&view=itemlist&task=user&id=157328]https://alternatio.org/index.php?option=com_k2&view=itemlist&task=user&id=157328[/url]
Открыли бизнес в Европе? И вам нужен постоянный поток новых клиентов?
Отлично!
Я приведу Вам стабильный поток целевых клиентов с помощью таргетированной рекламы уже со второго дня после запуска рекламы!
Работаю более 4 лет. Все клиенты - довольны.
[url=https://targethack.org] Оставить заявку[/url]
отзывы о маге Астарт Вард magastartvard . ru Астарт Вард отзывы
______________________________________________________
Не так давно обращалась к magastartvard . ru - отзывы только хорошие
Обратилась к магу Астарту Варду с просьбой о защите от негативных воздействий. Его защитный ритуал оказался эффективным - я чувствую себя более спокойной и уверенной в себе. Благодарю за вашу помощь!
______________________________________________________________
Астарт Вард отзывы
Актуальный доступ к ссылкам и зеркалам площадки Kraken уже у вас. Ознакомьтесь с надежными методами доступа и гарантированными мерами безопасности [url=https://3dark-link.com/]kraken ссылка[/url]
Sat confiavel no Brasil [url=https://blaze-aposta.org/]Blaze aposta[/url]
Sat confiavel no Brasil [url=https://blaze-aposta.org/]Blaze aposta[/url]
Поставляем цемент М500 с заводов производителей напрямую, работаем с тендерами, собственный парк а/м - доставка от 20т бесплатно [url=https://vc.ru/u/2967024-rinat/1046237-oborudovanie-dlya-zatarki-cementa-v-meshki]цемент м 500 фасовка[/url]
what is prednisone 5mg tablets used for prednisone tablets 5 mg [url=https://dailymedwebmddd.com/]prednisone treatment for rheumatoid arthritis[/url] does prednisone interact with birth control alternative to prednisone for inflammation
[url=https://avto-dublikat.ru/]https://avto-dublikat.ru/[/url]
Биография руководителя «Башкирской содовой компании» [url=https://eduarddavydov-bsk.ru/]Эдуард Давыдов[/url] Рождение в семье увлеченных наукой родителей предопределило жизненный путь Эдуарда Давыдова, чье детство прошло в атмосфере постоянного стремления к знаниям и самосовершенствованию.
What is collagen? familiarize yourself with process a protein that provides structure to skin, bones, [url=http://www.simple8.co.uk/gallery/simple8-dont-sleep-there-are-snakes-rehearsals-03/]http://www.simple8.co.uk/gallery/simple8-dont-sleep-there-are-snakes-rehearsals-03/[/url] and joints.
[url=https://images.google.lv/url?q=https://medium.com/@allerkogo_2147/блэкспрут-официальные-зеркала-на-сайт-blacksprut-в-даркнет-2024-2377b84085fc]blacksprut org
[/url]
Obtaining medications can sometimes feel like navigating through a labyrinth Particularly when seeking specialty drugs like Topiramate [url=https://wpaares.org/]topamax 200mg tablet[/url]
ebay kleinanzeigen deutschland immobilien [url=https://www.sliviagraed.com/#54824035]womens viagra[/url] twitter sign up error messages missing messages
[url=https://getb8.us/]video casino online[/url]
[url=https://getb8.us/]bets online casino[/url]
Написание эссе на заказ осуществляется нашими профессиональными авторами. Цена ВКР бакалавра купить зависит от ее объема и сложности [url=http://canenglish.ru/]купить доклад[/url]
<a href=http://1xbet-cabinet-zerkalo.ru/>http://1xbet-cabinet-zerkalo.ru/</a>
вывод из запоя
<a href=https://300.ya.ru/mofZE94A>https://300.ya.ru/mofZE94A</a>
Профильные трубы 40х20 мм. Закажите по низкой цене от производителя с доставкой по Москве. Предлагаем самые приятные цены в городе и области [url=https://meffert-yar.ru/]труба профильная 30х30х2[/url]
Профильные трубы 40х20 мм. Закажите по низкой цене от производителя с доставкой по Москве. Предлагаем самые приятные цены в городе и области [url=https://meffert-yar.ru/]профильная труба размеры таблица[/url]
<a href=http://1xbet-cabinet.ru/>1хбет рабочее зеркало на сегодня</a>
Getting your hands on medication can sometimes not be as straightforward as we would like unfortunately, cost is a significant affecting factor when it comes to essential medicines [url=https://downtownellijay.org/]order maxalt 5mg without prescription[/url]
Good day!
What do you recommend? What is the best slot to play where the chances of winning are higher?
Косметологическое оборудование Zemits – инновационные эстетические технологии для успешного развития Вашего СПА-бизнеса [url=https://spashop.com.ua/collections/hel-dlya-lazernoyi-epilyatsiyi]https://spashop.com.ua/collections/hel-dlya-lazernoyi-epilyatsiyi[/url]
В мире здравоохранения отзывы пациентов играют ключевую роль, предоставляя ценную обратную связь о качестве медицинского обслуживания. Доктор Юрий Шульга, выдающийся врач, привлекает внимание не только своей медицинской экспертизой, но и положительным влиянием, оказанным на своих пациентов [url=https://fernandotkzm42076.theobloggers.com/30936254/Юрий-Шульга-отзывы-echo-resilience-stories-of-triumph-under-dr-shulga-s-care]Шульга отзывы пациентов[/url]
Монтаж систем отопления, водоснабжения, вентиляции, канализации, очистки воды, пылеудаления, снеготаяния, геосистем в Краснодаре под ключ. ПРОФЕССИОНАЛЬНЫЕ ИНЖЕНЕРНЫЕ РЕШЕНИЯ ДЛЯ ДОМА [url=https://fectum.pro/]монтаж систем вентиляции отопления кондиционирования[/url]
медтехника ведущих брендов для дома. Всегда оптимальные цены, акции , скидки и отличный сервис. [url=https://smartmedreminder.com/]Vjlbas[/url]
Опыт лечения рака Э. Ревичи. Известнейший американский доктор Эммануэль Ревичи прожил долгую интересную жизнь [url=https://www.behance.net/gallery/192567059/Onko-Alternative?]метод Ревича[/url]
Компания предлагает обширный ассортимент услуг по изготовлению чеков на все случаи жизни. Вы точно сможете найти индивидуальное решение бюрократических проблем [url=https://buy-cheki.ru/]Заказать чеки[/url]
Компания предлагает обширный ассортимент услуг по изготовлению чеков на все случаи жизни. Вы точно сможете найти индивидуальное решение бюрократических проблем [url=https://buy-cheki.ru/]Купить чеки казань[/url]
Лучшие юристы и адвокаты оказывают бесплатные юридические консультации по телефону и в офисе компании. Квалифицированная юридическая помощь по всем отраслям права [url=https://quicklaw24.ru/]получить бесплатную юридическую консультацию по телефону[/url]
По-моему, Вы ошибаетесь.
Arousal is considered most important goal, [url=http://yhewasyc.eklablog.com/epub-download-relentless-solution-focus-train-your-mind-to-conquer-str-a211672688]http://yhewasyc.eklablog.com/epub-download-relentless-solution-focus-train-your-mind-to-conquer-str-a211672688[/url] is the meaning of existence, which should correspond to resource so that its It was easy to study as pornographic.
You can also enjoy the convenience of same-day weed Delivery in Toronto [url=https://kamikazi.cc/shop/flower/weed/indica-weed/super-pink-kush/]super pink strain[/url]
Честный обзор на популярную букмекерскую контору 1win поможет вам узнать все преимущества и недостатки этого сайта для ставок, включая коэффициенты, линию событий, способах и скорости выплат, бонусы и многое другое. Изучите все исходы и выгодные предложения, перейдя на официальный сайт БК [url=https://economytimes.ru/]1win официальный сайт[/url]
Честный обзор на популярную букмекерскую контору 1win поможет вам узнать все преимущества и недостатки этого сайта для ставок, включая коэффициенты, линию событий, способах и скорости выплат, бонусы и многое другое. Изучите все исходы и выгодные предложения, перейдя на официальный сайт БК [url=https://economytimes.ru/]1win зеркало[/url]
<a href="https://lovert.ru">рейтинг сайтов знакомств за рубежом</a>
сайт знакомств милф
<a href=https://bonus-leon-bk.ru/>Леон промокод на бонус</a>
<a href=https://onlinecasinos.com.cy/>https://onlinecasinos.com.cy/</a>
Provavelmente o melhor site de jogos do Brasil [url=https://blazeaposta.store/]Blaze aposta[/url]
Provavelmente o melhor site de jogos do Brasil [url=https://blazeaposta.store/]Blaze aposta[/url]
[url=http://google.co.vi/url?q=https://medium.com/@allerkogo_2147/зеркала-blacksprut-рабочие-ссылки-на-сегодня-9c28845e87ef]blacksprut не работает сегодня blacksprut official
[/url]
Подозреваемая позже призналась, что только завидовала богатству состоятельной семьи, [url=https://remontya.ru/gde-iskat-horoshuyu-nyanyu/]https://remontya.ru/gde-iskat-horoshuyu-nyanyu/[/url] поэтому и решила отравить нанимателям жизнь.
Он эффективен в отношении микробов, вирусов, плесени, грибка. Процедура озонирования квартиры направлена на общую глубокую дезинфекцию помещения [url=https://ozon-prom.ua/]дезінфекція витяжки[/url]
[url=https://samoylovaoxana.ru/tag/samyj-bolshoj-topor/]самый большой топор[/url] или [url=https://samoylovaoxana.ru/tag/krym/]Крым[/url]
[url=https://samoylovaoxana.ru/interesnye-mesta/russ/]Россия[/url]
https://samoylovaoxana.ru/peintbol-v-chem-osobennosti-popyliarnoi-igry-pyteshestvie/
Ещё можно узнать: [url=http://yourdesires.ru/beauty-and-health/lifestyle/169-srochnye-analizy-ili-ponyatie-cito.html]cito в медицине перевод[/url]
Отпуск
Погасим ипотекуВыплатим ипотеку любого банка за один день. Погасим долги и снимем обременения.
<a href=https://mryzhakov-urist.ru/>выкуп ипотечного жилья</a>
Крайне советую <a href=http://wwassociation.ru/user/10681>3D печать деталей</a>
<a href=https://1xbettur-2.com/>1xbet giris</a>
Grandes premios e apostas altas no Brasil no site [url=https://blazeaposta.blog/]Blaze aposta[/url]
[url=http://images.google.me/url?q=https://medium.com/@antonchexov2213/новое-зеркало-kraken-ваш-ключ-к-успешной-торговле-криптовалютами-в-2024-году-7985854619f0]tor blacksprut blacksputc com
[/url]
How does the rise of cloud computing affect the demand for local virtualization skills?
This question is more concise and specific than the original one. It also avoids using vague terms like "relevant" or "everything". Instead, it focuses on the relationship between two technologies: cloud computing and local virtualization. It also invites the expert to explain the reasons behind their answer.
[url=]https://technsight.com/[/url]
<a href=https://1wintr-4.xyz/>https://1wintr-4.xyz/</a>
Весьма неплохой топик
[url=https://www.lyndadeutz.com/2014/02/12/entry-without-preview-image/]https://www.lyndadeutz.com/2014/02/12/entry-without-preview-image/[/url]
Здесь вы найдете очень качественный промышленный [url=https://termoservice63.ru/chillier_stoimost]чиллер[/url]
Здесь вы найдете очень качественный промышленный [url=https://termoservice63.ru/chillier_stoimost]чиллер[/url]
No Brasil, jogue e ganhe no [url=https://blazeapostas.store/]Blaze apostas[/url]
Perkirakan penghasilan setiap pengguna TikTok <a href=https://kalkulatortiktokmoney.com/>https://kalkulatortiktokmoney.com/</a>
Современный четырехзвездочный отель в самом центре Сочи. Отель расположен в 100 метрах от центральной набережной Сочи [url=https://spencergsae82604.ambien-blog.com/31611474/apartment-borisov]https://spencergsae82604.ambien-blog.com/31611474/apartment-borisov[/url]
Репутация бренда - это наше все. SEO-Ezoterica ru помогла нам защитить и укрепить репутацию нашего бренда в цифровой среде.
удаление негативных отзывов в интернете с гарантией
удаление негативных отзывов на яндексе
удаление отзывов google
удаление негативных отзывов в интернете услуги
удаление отзывов пермь
Аккаунты [url=https://topshopads.com/]сдача аккаунта фейсбук в аренду[/url]
Accounts [url=https://topshopads.com/en]porn tiktok accounts[/url]
Hello everyone... https://bossbonus.ru/
thanks, interesting read
<a href="https://community.netgear.com/t5/user/viewprofilepage/user-id/1114962">androgel 1.62</a> Can I cut my prescription dosage if I experience side effects.
[url=http://google.com.nf/url?q=https://medium.com/@allerkogo_2147/ссылка-на-официальный-сайт-кракен-зеркало-файлообменника-kraken-dbaf4b6d0108]kraken onion ссылка tor wiki online
[/url]
<a href=https://melbettr.top/>https://melbettr.top/</a>
<a href=https://bwintr2.top/>https://bwintr2.top/</a>
[url=https://getb8.us/]online slot machine games[/url]
[url=https://getb8.us/]best casinos online uk[/url]
Вы не правы. Могу отстоять свою позицию. Пишите мне в PM.
[url=https://zippyapp.com/redir?u=xxxbf.tv/tags/c]https://zippyapp.com/redir?u=xxxbf.tv/tags/c[/url]
[url=http://carstvo-sharov.ru/]http://carstvo-sharov.ru/[/url]
монтаж кровли <a href=https://krovla1.ru/>https://krovla1.ru/</a>
Вы ошибаетесь. Могу отстоять свою позицию. Пишите мне в PM.
наши девочки отличаются простотой установки, долговечностью и практичностью и надежностью, [url=http://sunday.winzard.ru/2010/09/1.html]http://sunday.winzard.ru/2010/09/1.html[/url] а кроме этого экономным потреблением электроэнергии. приборы обладают степень предохранения от запыления и жидкостей и могут устанавливаться на потолке или стенах.
[url=https://dolgiplus.ru]https://dolgiplus.ru[/url]
Ηеlloǃ
Ι аpоlоgіzе for the overlу specifiс mеѕsаge.
Μy gіrlfriend аnd Ι love each othеr. Аnd we аre all grеat.
Вut... wе nееd a man.
We are 25 уеаrѕ оld, frоm Rоmanіa, wе аlѕo knоw еnglish.
We never get bоred! Аnd not onlу іn talk...
Mу nаmе іѕ Νatаliа, my profilе іѕ hеrе: https://1pt.co/ody39
According to the experience of Reputation House agency, reviews in a negative tone can be left not only by dissatisfied customers [url=https://contentbase.com/blog/reputation-important-for-brand/]reputation house serm[/url]
Businesses often equate image and reputation. But in fact, these concepts have completely different meanings [url=https://www.voxbliss.com/mastering-online-reputation-reputation-houses-serm-strategy-unveiled/]reputation house reviews[/url]
According to the experience of Reputation House agency, reviews in a negative tone can be left not only by dissatisfied customers [url=https://contentbase.com/blog/reputation-important-for-brand/]reputation house customers reviews[/url]
[url=https://medium.com/@allerkogo_2147/новое-зеркало-kraken-выгодная-возможность-для-торговли-в-2024-0e9fb5003d7a]kraken darknet ссылка
[/url]
Hello, World!
Hey there, mate! Greetings from your favorite surfing capybara!
How’s the surf today?
Ready to catch some gnarly waves together?
https://capybara444.wordpress.com
Good luck!
Купить ручной инструмент в интернет-магазине Кувалда.ру — широкий выбор моделей по низким ценам. Ручной инструмент: каталог товаров с описанием, характеристиками, отзывами покупателей и видео [url=https://womanchoice.net/vybor-benzopily-na-kuvalda-ru-polnoe-rukovodstvo-dlya-pokupatelej.html]бензопила купить[/url]
Облачная система работает через интернет, а подключение клиники к системе немногим сложнее, чем создание ящика электронной почты. Для работы системы не нужны никакие программы кроме веб-браузера [url=https://www.klubok.net/05/12/raskryty-xarakteristiki-smartfona-xiaomi-redmi-10x.html]https://www.klubok.net/05/12/raskryty-xarakteristiki-smartfona-xiaomi-redmi-10x.html[/url]
If a user encounters negativity on the first page of search results, he will be wary of the company and is unlikely to become its client [url=https://www.madsonline.net/2024/02/experience-of-reputation-house-how-to-handle-customer-feedback.html]reputation house customers reviews[/url]
Hello, World!
Hey there, mate! Greetings from your favorite surfing capybara!
How’s the surf today?
Ready to catch some gnarly waves together?
https://capybara235.wordpress.com
Good luck!
If a user encounters negativity on the first page of search results, he will be wary of the company and is unlikely to become its client [url=https://www.madsonline.net/2024/02/experience-of-reputation-house-how-to-handle-customer-feedback.html]reputation house serm[/url]
[url=https://by.tribuna.com/exotic/blogs/3095503-novoe-zerkalo-bleksprut-v-2024-godu-vxodim-tolko-otsyuda/]камбо купить москва
[/url]
Hello, World!
Hey there, mate! Greetings from your favorite surfing capybara!
How’s the surf today?
Ready to catch some gnarly waves together?
https://capybara235.wordpress.com
Good luck!
Здесь вы найдете очень оригинальный сайт [url=https://1win-9.ru/]1win[/url]
Здесь вы найдете очень оригинальный сайт [url=https://1win-9.ru/]1win[/url]
[url=http://images.google.co.mz/url?q=https://by.tribuna.com/exotic/blogs/3095584-kupit-optom-maka-peruanskaya-ekstrakt-kornya-6-polifenolov-lep/]айяуаска в москве цены и адреса
[/url]
Строительство индивидуальных загородных домов в Мытищах и Московской области. Проекты и цены, фото готовых работ и отзывы. Официальный сайт компании [url=https://domremont2014.ru/]строительство коттеджей в мытищах[/url]
Трехмерная печать представляет из себя популярную практику, основанную на накладывании материала слоями меньше миллиметра. Этот инновационный подход изготовления предметов находит активное применение в разных сферах производства. Для того, чтобы разузнать больше про <a href=http://recipes-vkusno.ru/profile.php?u=drillmodest1>печать на 3D принтере на заказ</a> перейдите на этот сайт, бесплатно консультируют.
It may seem that the best option is to make sure that job seekers encounter only positive information about the company [url=https://flashydubai.com/negative-feedback-ex-employee-damange-company-reputation/]reputation house serm[/url]
Here you will find the best [url=https://chinaxservice.com/]agent in China[/url]
It may seem that the best option is to make sure that job seekers encounter only positive information about the company [url=https://flashydubai.com/negative-feedback-ex-employee-damange-company-reputation/]reputation house employee reviews[/url]
Here you will find the best [url=https://chinaxservice.com/]agent in China[/url]
Bundan daha fazlas? diger seylerden , eger karar verirseniz kay?t olmaya karar verirseniz, bu oyun icin baslang?c bonus f?rsat?n?z olabilir hos geldiniz bonus. oyle/oyle, kazanclar daha az gerceklesse bile/oyle olsun, [url=https://sodinpro.org/2021/05/12/agile-pull-in-ten-extra-bodies-to-help-roll/]https://sodinpro.org/2021/05/12/agile-pull-in-ten-extra-bodies-to-help-roll/[/url] yukseklerde.
simple life [url=https://jimgrayonline.com/#toilet-paper]pool noodle[/url].
[url=https://www.mses-expert.ru/]https://www.mses-expert.ru/[/url]
Cool + for the post
Here you can find the best [url=https://gogeticon.com/]Vector icons[/url]
Here you can find the best [url=https://gogeticon.com/]Vector icons[/url]
Side effects of Aczone include <a href=http://levitr.buzz>prix levitra bruxelles</a> Published online first on June 20, 2016
Топ-менеджер [url=https://nikolaev-vyacheslav-constantinovich.ru/]Вячеслав Константинович Николаев[/url] является специалистом в телекоммуникационном бизнесе и в области информационных технологий
Топ-менеджер [url=https://nikolaev-vyacheslav-constantinovich.ru/]Николаев Вячеслав Константинович[/url] является специалистом в телекоммуникационном бизнесе и в области информационных технологий
Возможности для украинцев работать в ресторанах Германии находятся [url=https://www.04598.com.ua/list/447158]на нашем сайте[/url]
<a href=https://tayga.info/181788/>глаз бога тг</a>
https://silikat18.ru/ekonomika-zamknutogo-cikla-izuchenie-dinamiki-zakupok-i-prodazh-pererabotannogo-polimernogo-syrya.html
История строительства Кнаубом Андреем НПЗ Томскнефтерепеработка, планов на модернизацию и совершенствование корпоративной культуры. Привлечение молодых специалистов, улучшение условий труда всегда были в приоритете у бизнесмена [url=https://www.calameo.com/books/0070849969e804e977fd1]кнауб андрей бизнесмен[/url]
ничего подобного
_________________
[url=https://tr.bestbeting.space]iddaa sonuçları biten maçlar dünkü [/url] - klasbahis giriş
Завод весового оборудования презентует устройство для контроля количества сыпучих материалов во время их транспортировки - расходомер поточного типа [url=https://vc.ru/u/3015497-arkadiy-popov/1066161-podobran-analog-potochnogo-rashodomera-c-lever]расходомер лотковый[/url]
[url=https://avto-dublikat.ru/]https://avto-dublikat.ru/[/url]
https://www.ibm.com
[url=https://www.news5cleveland.com/news/local-news/indictment-woman-used-other-pilots-credentials-to-rent-later-crash-aircraft]https://www.news5cleveland.com/news/local-news/indictment-woman-used-other-pilots-credentials-to-rent-later-crash-aircraft[/url]
[url=https://www.news5cleveland.com/news/local-news/indictment-woman-used-other-pilots-credentials-to-rent-later-crash-aircraft]https://www.news5cleveland.com/news/local-news/indictment-woman-used-other-pilots-credentials-to-rent-later-crash-aircraft[/url]
takdirinize bagl? olarak verilir iki cesit:% 125 depozito ve en fazla 250 ucretsiz donusler cift bas?na, hangi/ne yapabildiginiz kullanma/girme [url=https://loveinfinity.work/movie-drama/]https://loveinfinity.work/movie-drama/[/url]mostbet kumarhanesi.
С момента своего вступления в должность в 2005 году Эдуард Давыдов содействовал реализации амбициозного плана по трансформации Башкирской содовой компании (БСК), что привело к фундаментальным изменениям в её операционной деятельности и финансовых показателях [url=https://www.justmedia.ru/news/russiaandworld/biografiya-i-karyera-generalnogo-direktora-bsk-eduarda-davydova]Давыдов Эдуард[/url]
С момента своего вступления в должность в 2005 году Эдуард Давыдов содействовал реализации амбициозного плана по трансформации Башкирской содовой компании (БСК), что привело к фундаментальным изменениям в её операционной деятельности и финансовых показателях [url=https://www.justmedia.ru/news/russiaandworld/biografiya-i-karyera-generalnogo-direktora-bsk-eduarda-davydova]Эдуард Давыдов бск[/url]
Печатаем фотокниги с вашими фотографиями! Удобный онлайн-редактор, готовые шаблоны с интересным дизайном, разработка индивидуального макета, доставка [url=http://basova-photo.ru/]печать фотокниг[/url]
Печать фотографий онлайн. Доставим заказ за 2-4 дня Ежемесячные акции и скидки Собственная фотофабрика [url=https://fotooks.ru/]салон печати[/url]
Печать фотографий онлайн. Доставим заказ за 2-4 дня Ежемесячные акции и скидки Собственная фотофабрика [url=https://fotooks.ru/]фотостудия дешевая[/url]
В мире, насыщенном технологиями, нередко возникают ситуации, когда нам требуется найти информацию о владельце определенного номера телефона или узнать его местоположение. Это может быть из-за того, что мы получили звонок или сообщение от незнакомого номера, или же нам просто нужно связаться с определенным человеком, но мы не знаем, как это сделать [url=https://domkem.ru/]где номер телефона[/url]
Была задача полностью реконструировать кровлю с заменой покрытия на МЧ и утеплением. Работа идет с соблюдением технологии монтажа, видно что люди опытные [url=https://trentonsfkn26936.targetblogs.com/26187534/novogrudok]https://trentonsfkn26936.targetblogs.com/26187534/novogrudok[/url]
Thanks, I've been looking for this for a long time
migraine natural remedies [url= https://cippsv.com.ve/zopices.html ] https://cippsv.com.ve/zopices.html [/url] health care places
Рекомендую каждому настоящий сайт [url=https://1win-30.ru/]1win[/url]
<a href=https://calculatortiktok.com/>tiktok calculator</a>
Филиал автошколы рядом с метро Борисово в Москве - профессиональное обучение на автомобилях с МКПП и АКПП получение водительских прав категории B с оплатой в рассрочку без переплат и скрытых платежей [url=http://autoznanie66.ru/]автошкола преображенская площадь[/url]
He began his studies in Kezdivasarhely and continued in Nagyenyed , from where he went to foreign universities in Jena and Gottingen [url=http://www.asahi-net.or.jp/~pt2y-okmt/esc/data2009.htm]http://www.asahi-net.or.jp/~pt2y-okmt/esc/data2009.htm[/url]
Free download Pinterest SVG Icons for logos, websites and mobile apps, useable in Sketch or Figma [url=https://www.ps.kz/domains/whois/result?q=gogeticon.com]google icon[/url]
В агентствах недвижимости специалистов можно назвать риелтор, агент, брокер, маклер, [url=https://zolotoi-st.ru/cadastre/]межевание сергиев посад[/url] посредник. в роли дохода обычно понимается оплату от сопровождаемой сделки.
Где купить виртуальный номер: рейтинг лучших сервисов SMS-активаций. Как и в других подобных сервисах, здесь вы можете купить номер для разового использования или взять номер в аренду на более длительный срок [url=https://edgarxbgr90256.develop-blog.com/30861473/virtueel-telefoonnummer-voor-altijd]virtueel telefoonnummer voor altijd[/url]
5. Put a checkbox supporting agreement/agreement with the company's rulers, [url=https://1wintr-5.xyz/]1win indir[/url] and click "Register". Available promotional offers collected in section "promotions or bonuses".
Недвижимость арестована?
Судебные приставы арестовали недвижимость? мы снимем обременения и заплатим ваши долги
<a href=https://urist-klochkova.ru/>выкуп недвижимости в москве</a>
Специально зарегистрировался на форуме, чтобы поучаствовать в обсуждении этого вопроса.
in case a team, for example, has a spread of -6, then -6 means that images must win at least by seven points to "cover the spread". But if our hackers do not win with enough points, draw or lose, then their opponent will "cover" the spread, the [url=https://foodmaxmachinery.com/cn/about-us/]https://foodmaxmachinery.com/cn/about-us/[/url] will make them the winning side of the bet.
у вас есть важнейшая возможность слушать хорошую музыку виртуально бесплатно, [url=https://onlineradioplanet.ru/]onlineradioplanet.ru[/url] непрерывно и в превосходном качестве. Даже придирчивый ценитель найдет у нас на получение затронет его сердце.
Абсолютно с Вами согласен. В этом что-то есть и мне кажется это отличная идея. Я согласен с Вами.
The maximum bet amount depends on the [url=https://iszb.pl/index.php?option=com_k2&view=item&id=6]https://iszb.pl/index.php?option=com_k2&view=item&id=6[/url], where you place bets. Active assistance service always glad get answers to all are interested in.
Вы мне не подскажете, где я могу об этом прочитать?
«сам, он», [url=https://kagla.gnuok.com/gnuboard5/bbs/board.php?bo_table=free&wr_id=10195]https://kagla.gnuok.com/gnuboard5/bbs/board.php?bo_table=free&wr_id=10195[/url] далее из неустановленной формы. 1935. - Т. 1 : А - Кюрины.
<a href=https://1win-bet.life/>1win зеркало</a>
онлайн казино с депозитом
<a href="https://remvend-cafe.ru/kazino/kriptovalyutnoe-kazino.html">https://remvend-cafe.ru/igrat/virtualnoe-kazino-igrat.html</a>
Ну да! Не рассказывайте сказок!
При обратном ходе поршень открывает подачу для очередной порции сырца. в производство поступают «фабрикаты» в разном виде, это зерновые, бобовые, мука, растворители вкусовых добавок и витаминно-минеральных курортов, но и биоотходы (кости, обрезь, рыбьи головы, падеж, мясокостная мука, просрочка, конфискат, [url=http://www.gaia.or.kr/bbs/board.php?bo_table=free&wr_id=397721]http://www.gaia.or.kr/bbs/board.php?bo_table=free&wr_id=397721[/url] отходы общепита).
[url=https://getb8.us/]casino games for real money[/url]
[url=https://getb8.us/]online poker and casino games[/url]
хорошее гониво
Міні екскаватор МД-4 відмінний компаньйон для відвідувачів і дорогоцінного фірми, [url=http://xn--h50bx3t5h88bb4kk6gy7a.com/bbs/board.php?bo_table=free&wr_id=673180]http://xn--h50bx3t5h88bb4kk6gy7a.com/bbs/board.php?bo_table=free&wr_id=673180[/url] з широкими потенціалом і низькими витратами на використання і зміст.
Рекомендую каждому настоящий сайт [url=https://1win-30.ru/]1win[/url]
Уверенность в работе вашей техники с нашими стабилизаторами напряжения
стабилизатор напряжения 220 вольт для квартиры купить [url=http://www.kupit-stabilizator-napryazheniya.ru/stabilizatoryi-napryajeniya-dlya-kvartiry]стабилизатор напряжения 220 вольт для квартиры купить[/url] .
<a href=https://vc.ru/u/2803215-egor-prozorov/987791-reyting-septikov-dlya-zagorodnogo-doma-i-dachi-top-10-luchshih-septikov-2024>Евролос Грунт</a>
нео семена интернет магазин каталог оби семена цветов каталог москва
урожайка интернет магазин наши семена https://perfect-cabal.ru купить семена на семяныче семена заказ ру интернет магазин каталог на 2021 год
семена купить в спб
Рекомендую каждому букмекерскую контору [url=https://1win-34.ru/]1win[/url]
Рекомендую каждому букмекерскую контору [url=https://1win-34.ru/]1win[/url]
Вы допускаете ошибку. Могу это доказать. Пишите мне в PM, обсудим.
for other wiping for the most part leads to sex. however, [url=https://revera.legal/info-centr/news-and-analytical-materials/791-vnimaniyu-proektnym-i-inym-stroitelnym-organizaciyam/]bdsm ph[/url] do not condemn consumers who it not want, Thorne explains.
Официальный сайт в Тор браузере, лучший выбор для тех, кто ищет безопасный и анонимный доступ на Мега даркнет. Рабочая ссылка на Мега Даркнет на нашем сайте [url=https://megadarknetmarketoniontora.top/]мега даркнет маркет ссылка тор[/url]
look here
[url=https://242.md/soobschestvo/obschestvennaya-deyatelnost/garadesud-md-vrata-k-yuzhnym-i-mezhdynarodnym-pyteshestviyam-iz-kishineva_i1619]https://242.md/soobschestvo/obschestvennaya-deyatelnost/garadesud-md-vrata-k-yuzhnym-i-mezhdynarodnym-pyteshestviyam-iz-kishineva_i1619[/url]
Спасибо за ваше известие. Мы ценим ваш объяснение и готовы для вас посодействовать. В случае если у вас есть какие-либо дополнительные вопросы или необходима добавочная информация, не смущяйтесь спрашивать. Вместе мы сделаем наш форум еще как никакого другого!
[url=https://lsm.md/forum/topic/issledovanie-sobytij-moldova25-md-vash-istochnik-aktualnoj-informacii]https://lsm.md/forum/topic/issledovanie-sobytij-moldova25-md-vash-istochnik-aktualnoj-informacii[/url]
You can Purchase the card by the Official Apple Website, Paypal and Ebay or from the assured online web stores [url=https://apple4btc.com/]sell apple store gift card[/url]
Больше информации об услуге дизайн-проект ванной комнаты. Если остались вопросы или есть желание заказать дизайн проект коттеджа, с радостью приглашаем на бесплатную консультацию в нашу студию [url=https://gazeta.ua/articles/promotion/_dizajn-budinkiv-ta-kotedzhiv-vid-fahivciv-kompaniyi-nsdgroup/1169473]дизайн котеджів фото[/url]
Всем хорошего дня!
Прогресс в дипломе обеспечен благодаря использованию онлайн-ресурсов.
Приобретите диплом университета без предоплаты у нас и получите его с доставкой в любую точку России, гарантия качества.
https://alternatio.org/index.php?option=com_k2&view=itemlist&task=user&id=157541
https://forextema.com/index.php?option=com_easyblog&view=entry&id=9284&Itemid=87
Желаю вам всем пятерочных) оценок!
купить дипломы о высшем
купить диплом в тамбове
[url=https://getb8.us/]casino online sale[/url]
[url=https://getb8.us/]new casino no deposit sites[/url]
Приветики, дорогие мои!!
Диплом вынудил меня перейти на ночные смены работы, что угрожало моему благополучию.
Поможем вам выбрать, оформить заказ и приобрести диплом любого учебного заведения по самым низким ценам.
http://torgteh-rzn.ru/index.php?option=com_k2&view=itemlist&task=user&id=9841
http://androidb.ru/index.php?subaction=userinfo&user=ehepytuvo
Желаю вам всем отличных оценок!
купить диплом в омске
купить диплом в москве
Mega – облачное хранилище файлов из Новой Зеландии. Стало известно благодаря своему основателю, бизнесмену Киму Доткому, владельцу известного файлообменника Megaupload [url=https://megadarkmarketa.top/]mega питер[/url]
Здравствуйте!
В интернете я нашел ресурсы для диплома, которые помогли мне ускорить написание.
Закажите диплом у нас легко! Без предоплаты, с гарантией качества и доставкой по всей России.
psylive.ru/articles/1526_semi-narkomanov.aspx?act=printfВ
egeigia.ru/all-ege/dokumenty-ege/rezultaty-egeВ
Желаю всем отличных оценок!
купить диплом в вольске
купить диплом колледжа
купить диплом о среднем специальном
купить свидетельство о разводе
купить диплом в клинцах
https://travellik.ru/lite-plastikovyh-izdelij-pod-davleniem/
Предприятие является участником экспортного форсажа, определило два рынка для вывода всех первичных продуктов. Поставляет продукцию в Узбекистан, Киргизию, Белоруссию и Казахстан [url=https://ufa.aif.ru/society/details/50_-nuyu_subsidiyu_i_eksport_za_vesovuyu_tochnost_poluchayut_agrarii_bashkirii]промышленные весы[/url]
Коста Рика [url=https://costarus.online/]гражданство коста рики для россиян 2023[/url]
<a href=https://glazboga.world/>глаз бога бот</a>
Premium domain for sale https://baic-huansu.ru
Byrd, [url=http://oishiramen.kr/bbs/board.php?bo_table=free&wr_id=115876]http://oishiramen.kr/bbs/board.php?bo_table=free&wr_id=115876[/url] Harrison. "China is preparing to launch esports through hardcore marketing." Tuscaloosa news. new media investment group. Dyer, Mitch (August 27, 2012.). "Review of cs: global offensive".
Необходимо воспользоваться зеркалом официального сайта 1вин или скачать официальное приложение 1win. Регистрация на официальном сайте [url=https://newsrbc.ru/]1win[/url]
if you book a [url=https://wellfound.com/u/park-nfly]https://wellfound.com/u/park-nfly[/url], which will offer reasonable rates for rooms available already this evening.
Admin – “:
Вам поднадоело шаблонные интернет-магазины? M3ga предоставляет что-то другое! Благодаря разнообразию категорий и уникальным находкам <a href=https://xn--meg-sb-dua.com>мега дарк нет</a> гарантирует, что вы откроете для себя уникальные товары. Пройдите легкую регистрацию и выберите удобный город для самовывоза. Присоединяйтесь к <a href=https://xn--meg-sb-dua.com>mega dark market</a> прямо сейчас и делайте покупки со стилем.
mega sb:https://xn--meg-sb-dua.com
документ и декларация - документы, [url=https://www.rospromtest.ru/content.php?id=27]сертификация технологического оборудования[/url] подтверждающие качественность и безвредность объекта. Сертификация - целая структура, направленная на стабилизация уровня продукта, работ и сервисов.
<a href=https://grandolavanderia.ru/>https://grandolavanderia.ru/</a>
Что действительно следует учитывать, используя наш генератор виртуальных номеров, так это то, что каждый тестовый телефон, который предлагает эмулятор, действительно доступен множеству пользователей на протяжении всего своего периода актуальности [url=https://emiliogihe83839.tribunablog.com/lease-a-telephone-number-a-flexible-remedy-for-contemporary-conversation-requires-39816732]аренда номера[/url]
Best cucmber ever <a href=https://cucumber222.com>cucumber</a>
больничный официальный Москва купить http://www.massmed.org/ больничный задним числом купить в Москве <a href=http://bol24.info/>больничный лист официально купить</a> больничный лист официальный Москва стоимость http://www.gumer.info/bibliotek_Buks/Science/filin/20.php
Смотрите сериал Золотая лихорадка. Аляска онлайн [url=https://zolotayalikhoradka.online/]https://zolotayalikhoradka.online/[/url] 1-14 сезон все серии с русским переводом абсолютно бесплатно.
<a href=http://shurum-burum.ru/>http://shurum-burum.ru/</a>
Найдите свой идеальный вариант недвижимости в Объединенных Арабских Эмиратах [url=https://triumf-realty.ru]продажа недвижимости в оаэ[/url] - лучший сайт, на котором вы найдете все необходимое!
новосибирск белокуриха такси стоимость <a href=http://transfer-novosibirsk-belokurikha.ru/>http://transfer-novosibirsk-belokurikha.ru/</a>
Рекомендую лучшую БК и казино в России [url=https://1win-46.ru/]1win[/url]
Рекомендую лучшую БК и казино в России [url=https://1win-46.ru/]1win[/url]
airbnb boat florida keys <a href=https://boatrent.shop/>https://boatrent.shop/</a>
больничный лист официально купить Москва http://www.rcsi.com/ больничный лист задним числом цена <a href=http://bol24.info/>больничный задним числом купить в Москве</a> больничный лист официально купить цена http://www.smclinic.ru/press-centr/smi-o-nas/pulmonolog-sm-klinika-rasskazala-o-bakterialnoy-pnevmonii-u-vzroslykh/
Expert Recommendations
The Ultimate Guide to Storing Your Cryptocurrency
trx wallet extension [url=best-exchange-wallet.com]trx wallet extension[/url] .
Для того, чтобы получить эксклюзивные бонусы от букмекера нужны промокоды, которые не всегда просто можно получить. В этой статье разобрано, как получить и использовать промо коды 1хБет и какие бонусы они дают [url=https://1xbetpromostavka.ru/]промокоды на 1xbet рабочие[/url]
3. Список увлечений [url=https://sertifikaciya-iso-9001.blogspot.com/2024/01/iso-9001.html]https://sertifikaciya-iso-9001.blogspot.com/2024/01/iso-9001.html[/url] с обозначением кодов. 6. Иную разрешительную документацию (при необходимости).
<a href=http://vardenafil.buzz>occasion du levitra en belgique</a> C FOXA1 binding events within these categories as defined in B were compared with gene expression in TAMR and MCF7 WS8 cells as determined by RNA seq
[url=https://getb8.us/online-casinos/]top casinos online[/url]
[url=https://getb8.us/online-casinos/]top online casinos[/url]
У нас Вы сможете найти и приобрести деревянные и металлические спортивные комплексы по приемлемым для Вас ценам.Каталог полон моделями спортуголков, которые будут служить Вашему малышу помощью в развитии.Для чего нужны детские спортивные уголки для дома?
http://almatygymnastics.kz/2015/05/29/o3gym/
http://smerch.org/contacts
http://velo-sport.sumy.ua/?p=history&hp=2011
Спортивные комплексы имеют массу преимуществ:Спортивный уголок "Юнга мини"
Vodka Казино <a href=https://casino-vodka.top/>vodka casino играть</a> заботится о своих клиентах, применяя различные методы защиты информации и средств. Все транзакции и личные данные игроков защищены надежно, благодаря использованию последних технологий защиты.
он работает, как классических, [url=https://bridgedentalpractice.co.uk/we-hired-a-new-employee/]https://bridgedentalpractice.co.uk/we-hired-a-new-employee/[/url] но вместо реального баланса сбоку отображается электронный кошелек. но отдел безопасности вправе запросить документы во всякое время, так что это кроме всего прочего значимая причина оправдывать площадку и следовать указанным нормативам.
Если вам необходимы пассажирские перевозки на микроавтобусах, вы обратились по нужному адресу. Компания готова предоставить в ваше распоряжение не только целый ряд презентабельных микроавтобусов, но и услуги опытных профессиональных водителей с большим стажем работы [url=https://bezkordon.com.ua/ru/reisi/varshava-kamenskoe/]Варшава - Каменское[/url]
По-настоящему крутое [url=https://vodkaa-casino.online/]водка казино[/url]
По-настоящему крутое [url=https://vodkaa-casino.online/]водка казино[/url]
больничный лист официально http://coronavirus.data.gov.uk/ больничный лист официально купить Мск <a href=http://bol24.info/>купить лист нетрудоспособности</a> больничный цена Мск http://www.legislation.gov.uk/coronavirus
Оригинальный сайт по [url=https://vodkaa-casino.website/]водка казино[/url]
Оригинальный сайт по [url=https://vodkaa-casino.website/]водка казино[/url]
One [url=http://L.Iv.Eli.Ne.S.Swxzu%40Hu.Feng.Ku.Angn.I.Ub.I.Xn--.Xn--.U.K37@Cgi.Members.Interq.Or.jp/ox/shogo/ONEE/g_book/g_book.cgi]http://L.Iv.Eli.Ne.S.Swxzu%40Hu.Feng.Ku.Angn.I.Ub.I.Xn--.Xn--.U.K37@Cgi.Members.Interq.Or.jp/ox/shogo/ONEE/g_book/g_book.cgi[/url] supports single hd account. you will be able just try them alternately.
<a href="https://wnfestival.ru">daddy casino</a>
Всем рекомендую БК 1вин, это их сайт [url=https://1win-53.ru/]1win[/url]
Полный комплекс бухгалтерских услуг для юридических лиц, ООО и ИП. Ведение бухучета, сопровождение и обслуживание бизнеса. Наши бухгалтеры помогут Вам [url=https://case-battle.win]бухгалтерские услуги[/url]
<a href=https://blockchainreporter.net/hometopia-to-become-first-metaverse-with-adult-version-of-roblox/>hometopia</a>
В современной промышленности важное значение имеет испытательное оборудование, позволяющее оценивать параметры изделий на различных этапах производства. Один из ключевых видов такого оборудования — вибростенды, предназначенные для испытания компонентов и сборок на устойчивость к воздействию механических колебаний [url=https://skbtrm.ru/products/vibration-testing-equipment/]электродинамические вибростенды[/url]
<a href=https://gruzovichok1.ru/>https://gruzovichok1.ru/</a>
1win 1win 1win [url=https://lgrd-48.ru/]1win[/url]
1win 1win 1win [url=https://lgrd-48.ru/]1win[/url]
when you buy cryptocurrencies such as bitcoin and ethereum, [url=https://veloelectriquepliant.fr/comment-fabriquer/]https://veloelectriquepliant.fr/comment-fabriquer/[/url], are given two keys: one public, and other private.
[url=https://dzen.ru/a/Zf6iYFWYFCeRp8Rd]Гражданство Коста Рики[/url]
[url=https://dzen.ru/a/Zf6qSM7pNhhxl9eb]ВНЖ в Коста Рике[/url]
[url=https://dzen.ru/a/Zf6eWHXRUAuqMO9Z]ПМЖ в Коста Рике[/url]
[url=https://dzen.ru/a/Zf6kFitPMwIBUuc7]Роды в Коста Рике[/url]
[url=https://imigrantos.ru/]Миграция Коста Рика[/url]
[url=https://dzen.ru/a/Zf7RjBEAth8fTYEm]Получить ВНЖ в Коста Рике[/url]
[url=https://dzen.ru/b/Zf7On6RwAjJG4Jpe]Вид на жительство Коста Рика[/url]
ולוהטות למי שמחפש חוויה אינטנסיבית ואינטימית ברמה הכי גבוהה, שמגיעות עד אליך הן אופציה הכי ייחודית. מפגש דיסקרטי בדירת נופש או חוויה מחוץ לעולם הזה שתפתה את הגוף והנפש שלך. בנוסף הן בהחלט יכולות לשפר את המודעות שלך לגוף ולעזור לך להתחבר עם החושניות שלך <a href=http://www.videotrip.co.il/>דירות דיסקרטיות באשקלון</a>
Всем рекомендую официальный сайт [url=https://1win-48.ru/]1win[/url]
Всем рекомендую официальный сайт [url=https://1win-48.ru/]1win[/url]
Кэт Казино <a href=https://cat-casinos.top/>cat casino официальный сайт</a> — это уникальное пространство для азартных игр, где каждый может найти что-то для себя. С первых шагов на официальном сайте Кэт Казино, игроки сталкиваются с понятным интерфейсом и широким ассортиментом игр. Процесс регистрации в Cat Casino максимально упрощен и не займет много времени, требуя лишь базовых данных от пользователя, что позволяет быстро перейти к самому интересному — игре.
.
Привет любители машин!
Исследуйте последние тенденции и инновации в мире автомобилей на https://i4car.net/category/zakon/ Мы предоставляем экспертные обзоры, новости и советы, чтобы вы могли наслаждаться вождением.
[url=https://i4car.net/category/moto/]Мотоциклы[/url]
автоновости
новост автопромов
Удачи и хорошей дороги!
[url=https://vykup-avto-v-ufe.ru/]vykup-avto-v-ufe.ru[/url]
Всем рекомендую БК 1вин, официальный сайт [url=https://1win-49.ru/]1win[/url]
Всем рекомендую БК 1вин, официальный сайт [url=https://1win-49.ru/]1win[/url]
Мы предлагаем на выбор разный номинал и наполнение сертификатов. Это может быть катание как отдельно на снегоходе и квадроцикле, так и обе активности вместе. Количество техники, длительность проката и стоимость сертификата не ограничены [url=http://atvbizon.ru/]катание на квадроциклах в подмосковье цены[/url]
[url=https://getb8.us/online-casinos/]casino games
[url=https://getb8.us/online-casinos/]top casino games
Всем рекомендую БК 1вин, это их сайт [url=https://1win-53.ru/]1win[/url]
На вашу квартиру наложен арест на регистрационные действия из-за имеющихся задолжностей? Погасим долги. Снимем арест. Проведем сделкуВ арестеРассчитать стоимость выкупа
<a href=https://zhk-gornaya-skazka.ru/>покупка нежилых помещений в санкт-петербурге спорные потенциально опасные моменты предложить клиенту</a>
Сервис онлайн заказа классической и широкоформатной фотопечати на фотобумаге, холсте, акварельной и плакатной бумаге, печать фотографий [url=https://photo-leto.ru/]накатка на пенокартон фото[/url]
[url=https://tplrupiya.com/tpl-rupiya-ubl-omni-and-evantagesoft-sign-mou-to-offer-cashless-payments-for-lahore-transport-company-ltc/]https://tplrupiya.com/tpl-rupiya-ubl-omni-and-evantagesoft-sign-mou-to-offer-cashless-payments-for-lahore-transport-company-ltc/[/url]
<a href=https://adzan.online/>https://adzan.online/</a>
[url=https://samoylovaoxana.ru/tag/klimat-nigerii/]климат Нигерии[/url] или [url=https://samoylovaoxana.ru/tag/tasmaniya/]Тасмания[/url]
[url=https://samoylovaoxana.ru/tag/otzyvy-turistov-o-kryme/]отзывы туристов о Крыме[/url]
https://samoylovaoxana.ru/tag/puteshestvie-po-armenii/
Ещё можно узнать: [url=http://yourdesires.ru/it/1248-kak-vvesti-znak-evro-s-klaviatury.html]буквенное обозначение евро[/url]
Туристические советы
[url=http://sensivcreation.com/how-to-create-an-effective-essay-checklist/]http://sensivcreation.com/how-to-create-an-effective-essay-checklist/[/url]
Great beat ! I would like to apprentice while you amed your web site, hoow could i subscribe for
a blog website? The account helped me a acceptable deal.
I haad been tiny bit acquainted of this your broadcast offered bright clear idea https://Www.Waste-Ndc.pro/community/profile/tressa79906983/
Здравствуйте автомобилисты!
Обратите внимание на https://dtp.vn.ua/category/video/, если вы ищете актуальные данные о дорожно-транспортных происшествиях в Виннице. Мы предлагаем глубокий анализ каждого ДТП, с целью повышения осведомленности и безопасности на дороге.
[url=https://dtp.vn.ua/category/novosti-vinnitsa/]Новости Винницы [/url]
авто новости Винницы
Главные новости Винницы
Удачи и хорошей дороги!
Изготовление стильных фотокниг недорого. Быстрая и качественная печать фотобуков на заказ. Создавайте фотоальбомы онлайн с помощью простого и бесплатного фоторедактора [url=https://foto-san.ru/]фотокниги недорого[/url]
Всем рекомендую Букмеерскую контору [url=https://1win-57.ru/]1win[/url]
Всем рекомендую Букмеерскую контору [url=https://1win-57.ru/]1win[/url]
Hello.
https://googler.com
Good luck :)
[url=https://www.google.com.sl/url?sa=t&url=https://cryptohabr.ru/]https://www.google.com.sl/url?sa=t&url=https://cryptohabr.ru/[/url]
Заказать диссертацию онлайн. Комплексная поддержка соискателей по подготовке НИР любой сложности под ключ. Выполнение - в сумме за 120 дней по гуманитарным дисциплинам, и в сумме 150-180 дней по техническим дисциплинам [url=http://sdal-na-5.ru/]решение контрольных работ[/url]
[url=https://www.mrcaglar.co.uk/uncategorized/hello-world/]https://www.mrcaglar.co.uk/uncategorized/hello-world/[/url]
Снимем арест. Оплатим судебным приставам все Ваши долги и поможем снять арест от ФССП. Оплатим ЖКХ/ Купим жилье с долгами за свет, воду и прочими коммунальными услуги.
<a href=https://zhk-gornaya-skazka.ru/>zhk-gornaya-skazka.ru</a>
https://generika51.ru
https://www.ibm.com
Недвижимость арестована?
Судебные приставы арестовали недвижимость? мы снимем обременения и заплатим ваши долги
<a href=https://zhk-gornaya-skazka.ru/>zhk-gornaya-skazka.ru</a>
Привет всем!
За главными новостями Кропивницкого следите на top10.kr.ua – вашем гиде по новостям города.
Заходите https://top10.kr.ua/category/news-ukraine/
[url=https://top10.kr.ua/category/news-ukraine/]Новости Украины видео[/url]
главные новости Кропивницкого
главные новости Украины
новости Кропивницкого
Удачи и хороших новостей!
Автосервис
[url=https://katalik76.ru/]https://katalik76.ru/[/url]
https://katalik76.ru/udalenie-katalizatora-Brilliance.html
https://katalik76.ru/udalenie-katalizatora-SsangYong.html
https://katalik76.ru/udalenie-katalizatora-Suzuki-MR-Wagon.html
https://katalik76.ru/udalenie-katalizatora-Mercedes-Benz-B-Klass.html
https://katalik76.ru/udalenie-katalizatora-Mercedes-Benz-Vito.html
Ознакомьтесь с большим ассортиментом отделочных материалов оптом на нашем сайте. Доставка гарантия качества по выгодным ценам оптом [url=https://rolaks.com/]https://rolaks.com/[/url]
Бизнесмен Андрей Кнауб хорошо известен как предприниматель и трейдер в сфере нефтепереработки. Он более 25 лет был частью крупнейших отраслевых компаний, реализовал множество благотворительных и социальных проектов [url=https://vc.ru/u/1010242-interesnoe-v-mire/1019309-uchreditel-andrey-knaub-npz-tomskneftepererabotka-zabota-o-lyudyah-i-ekologii-nash-osnovnoy-prioritet]кнауб андрей артурович[/url]
Всем рекомендую Букмекерскую контору [url=https://1xbet-12.ru/]1xbet[/url]
Всем рекомендую Букмекерскую контору [url=https://1xbet-12.ru/]1xbet[/url]
Рекомендую лучшую Букмекерскую контору [url=https://1xbet-11.ru/]1xbet[/url]
Рекомендую лучшую Букмекерскую контору [url=https://1xbet-11.ru/]1xbet[/url]
Лучшая Букмекерская контора [url=https://1xbet-9.ru/]1xbet[/url]
Лучшая Букмекерская контора [url=https://1xbet-9.ru/]1xbet[/url]
Известный бизнесмен Кнауб Андрей Артурович родился в г. Сургуте Тюменской области. Суровый климат с детства закаляет характер, поэтому не удивительно, что будущий предприниматель сумел в буквальном смысле сделать самого себя [url=https://biographe.ru/biznesmeni/andrej-knaub/]кнауб андрей[/url]
Предприниматель придерживался мнения, что заботиться надо не только о персонале, но и окружающей среде [url=https://uznayvse.ru/znamenitosti/biografiya-andrey-knaub.html]кнауб андрей биография[/url]
Советую самую лучшую Букмекерскую контору [url=https://1xbet-8.ru/]1xbet[/url]
Советую самую лучшую Букмекерскую контору [url=https://1xbet-8.ru/]1xbet[/url]
after purchases of a [url=https://www.ncnonline.net/d-link-announces-support-for-apple-homekit/?unapproved=3904163&moderation-hash=df93b8701edbf3bb533174dcdca4a283]https://www.ncnonline.net/d-link-announces-support-for-apple-homekit/?unapproved=3904163&moderation-hash=df93b8701edbf3bb533174dcdca4a283[/url] owner of household appliances provided log in inside the wallet with the name of consumer, and a password for future purchases.
В биографии бизнесмена Андрея Артуровича Кнауба важно отметить, что для него ключевое значение имела забота о персонале и экологической обстановке в регионе [url=https://biographe.ru/biznesmeni/andrej-knaub/]кнауб андрей артурович[/url]
Доброго!
Кропивницкий без прикрас: реальные новости и события, которые волнуют горожан.
Посетите https://0522.kr.ua/
[url=https://0522.kr.ua/category/news-ukraine/]Новости Украины[/url]
топ новости Кропивницкого
новости Кропивницкого видео
Удачи и хороших новостей!
Egor Alexandrovich Abramov’s personal life remains guarded, allowing his work to speak volumes about his dedication to the craft [url=https://cyprus-mail.com/2024/02/08/a-glance-at-young-actor-egor-alexandrovich-abramov/]egor abramov entrepreneur[/url]
Open this site [url=https://fortunetiger.com.br/]Fortune Tiger[/url]
Open this site [url=https://fortunetiger.com.br/]Fortune Tiger[/url]
Предлагаю лучшую букмекерскую контору [url=https://1xbet-13.ru/]1xbet[/url]
Предлагаю лучшую букмекерскую контору [url=https://1xbet-13.ru/]1xbet[/url]
Рекомендую лучшую Букмекерскую контору [url=https://1xbet-7.ru/]1xbet[/url]
Egor Abramov’s biography, initiated by chance, has evolved into a promising career, and as he continues to make his mark in the cinematic landscape, audiences can anticipate more captivating performances from this talented young actor [url=https://www.calameo.com/books/007512754c0948bcce04b]egor alexandrovich abramov[/url]
I am sure this articl has touched all thhe internet people, its reall really fastidious
paragraph on building up new web site. https://Www.waste-ndc.pro/community/profile/tressa79906983/
Настоятельно советую букмекерскую контору [url=https://1xbet-14.ru/]1xbet[/url]
Настоятельно советую букмекерскую контору [url=https://1xbet-14.ru/]1xbet[/url]
Eu recomendo este jogo [url=https://fortune-tiger.blog/]Fortune Tiger[/url]
Eu recomendo este jogo [url=https://fortune-tiger.blog/]Fortune Tiger[/url]
Знакомьтесь с топовой Букмекерской конторой [url=https://1xbet-15.ru/]1xbet[/url]
Знакомьтесь с топовой Букмекерской конторой [url=https://1xbet-15.ru/]1xbet[/url]
Я считаю, что Вы не правы. Я уверен. Могу это доказать. Пишите мне в PM.
The success of the token is closely coupled with the work of the [url=https://evroblesk.ru/bitrix/redirect.php?event1=click_to_call&event2=&event3=&goto=https://huobi-wallet.io/]https://evroblesk.ru/bitrix/redirect.php?event1=click_to_call&event2=&event3=&goto=https://huobi-wallet.io/[/url], the global huobi exchange. Is it a good time/a good time for buying a huobi token?
Мое мнение – лучшая Букмекерская контора [url=https://1xbet-16.ru/]1xbet[/url]
Мое мнение – лучшая Букмекерская контора [url=https://1xbet-16.ru/]1xbet[/url]
Предлагаю топовую Букмекерскую контору [url=https://1xbet-17.ru/]1xbet[/url]
Предлагаю топовую Букмекерскую контору [url=https://1xbet-17.ru/]1xbet[/url]
Participe e ganhe no site original [url=https://fortune-tiger1.org/]Fortune Tiger[/url]
Participe e ganhe no site original [url=https://fortune-tiger1.org/]Fortune Tiger[/url]
Предлагаю топовую в своем роде Букмекерскую контору [url=https://1xbet-19.ru/]1xbet[/url]
Предлагаю топовую в своем роде Букмекерскую контору [url=https://1xbet-19.ru/]1xbet[/url]
Предлагаю вам лучшую Букмекерскую контору [url=https://1xbet-18.ru/]1xbet[/url]
Предлагаю вам лучшую Букмекерскую контору [url=https://1xbet-18.ru/]1xbet[/url]
Советую крупнейшую Букмекерскую контору [url=https://1xbet-20.ru/]1xbet[/url]
Советую крупнейшую Букмекерскую контору [url=https://1xbet-20.ru/]1xbet[/url]
Выбор радиаторов отопления – залог комфорта в доме. От мощности до дизайна, каждый аспект важен. Обзор полезной информации о радиаторах отопления [url=https://heat-komfort.ru/]радиаторы отопления[/url]
<a href=https://treningi-i-kursy.com/>https://treningi-i-kursy.com/</a>
Крупнейшая Букмекерская контора [url=https://1xbet-23.ru/]1xbet[/url]
Крупнейшая Букмекерская контора [url=https://1xbet-23.ru/]1xbet[/url]
Практичная армейская раскладушка для комфортного отдыха в походах и экстремальных условиях [url=https://aforce.com.ua/]раскладушка полевая купить[/url]
Egor, along with central actors, explores more mature themes in the latest season, depicting the evolving challenges faced by their characters [url=https://london-post.co.uk/egor-alexandrovich-abramov-a-journey-from-gymnasium-to-the-glittering-screens/]egor abramov[/url]
они симпатичны реальных подписчиков, [url=https://xn--80abdzaxbkfak2ai0bzf4ce.xn--p1ai/communication/forum/user/40811/]https://xn--80abdzaxbkfak2ai0bzf4ce.xn--p1ai/communication/forum/user/40811/[/url] или набирают просто массу. Их считают инфлюенсерами, значит, к их мнению будут прислушиваться, стиль копировать, советам - следовать.
На мой взгляд, эта Букмекерская контора - лучшая [url=https://1xbet-26.ru/]1xbet[/url]
На мой взгляд, эта Букмекерская контора - лучшая [url=https://1xbet-26.ru/]1xbet[/url]
top online casinos
best online casinos
play casino online
top online casinos
top casino site
Топовоя Букмекерская контора на рынке [url=https://1xbet-28.ru/]1xbet[/url]
Накрутка в телеграме. Накрутка просмотров телеграм. Накрутка подписчиков на страницу. Накрутка лайков на рекомендации. наши плюсы: Низкие [url=http://mos-it.ru/index.php?subaction=userinfo&user=ihovar]http://mos-it.ru/index.php?subaction=userinfo&user=ihovar[/url] цены.
Acesse o site real do jogo [url=https://fortune-tiger.link/]Fortune Tiger[/url]
Acesse o site real do jogo [url=https://fortune-tiger.link/]Fortune Tiger[/url]
требуется, чтобы ваш аккаунт выглядел живым, активно работающим, увлекательным публики. Сначала сразу задайте тем, о чем вы вы подумываете - хорошую должность со полагающимися гарантиями и идеальной безопасностью - за какую не будет бана, не настигнут проблемы или хочется, [url=http://artem-energo.ru/forums.php?m=posts&q=17071&n=last#bottom]http://artem-energo.ru/forums.php?m=posts&q=17071&n=last#bottom[/url] чтобы выполнили заказ быстро и выгодно?
На мой взгляд - лучшая Букмекерская контора [url=https://1xbet-29.ru/]1xbet[/url]
На мой взгляд - лучшая Букмекерская контора [url=https://1xbet-29.ru/]1xbet[/url]
желает сотрудничать партнёров заказчик уже определились о создании собственного [url=http://2.shkola.hc.ru/index.php?option=com_k2&view=itemlist&task=user&id=1771]http://2.shkola.hc.ru/index.php?option=com_k2&view=itemlist&task=user&id=1771[/url] бизнеса? приветствует сотрудничество поставщиков мы регулярно совершенствуем ассортимент, чтобы предложить нашим пользователям бОльший выбор.
This is nicely put! !
online pharmacy school <a href="https://canadianpharmacylist.com/#">canada drug prices</a> canadian viagra generic pharmacy
vet pharmacy online [url= https://forums.dieviete.lv/profils/127605/forum/ ] https://forums.dieviete.lv/profils/127605/forum/ [/url] urinary infection remedies
Топ Букмекерская контора [url=https://1xbet-31.ru/]1xbet[/url]
Топ Букмекерская контора [url=https://1xbet-31.ru/]1xbet[/url]
Надежная Букмекерская контора [url=https://1xbet-32.ru/]1xbet[/url]
Предлагаю самую надежную букмекерскую контору [url=https://1xbet-33.ru/]1xbet[/url]
Превосходная Букмекерская контора [url=https://1xbet-34.ru/]1xbet[/url]
Предлагаю самую надежную букмекерскую контору [url=https://1xbet-33.ru/]1xbet[/url]
Превосходная Букмекерская контора [url=https://1xbet-34.ru/]1xbet[/url]
Ir para o site original [url=https://fortune-tiger2.net/]Fortune Tiger[/url]
Ir para o site original [url=https://fortune-tiger2.net/]Fortune Tiger[/url]
Ведущая Букмекерская контора [url=https://1xbet-35.ru/]1xbet[/url]
Ведущая Букмекерская контора [url=https://1xbet-35.ru/]1xbet[/url]
Крупнейшая Букмекерская контора [url=https://1xbet-36.ru/]1xbet[/url]
Спасибо за пост
_________________
[url=https://turk.gamesmoneynmore.site]canlı iddaa sonuçları tam skor [/url] - iddaa bayi para çekme
Ведущая в мире Букмекерская контора [url=https://1xbet-37.ru/]1xbet[/url]
Ведущая в мире Букмекерская контора [url=https://1xbet-37.ru/]1xbet[/url]
http://321gf5d132d.nnov.org/blog/vyvod_iz_zapoya_na_domu_moskva_1.html
Советую отличную Букмекерскую контору [url=https://1xbet-39.ru/]1xbet[/url]
Советую отличную Букмекерскую контору [url=https://1xbet-39.ru/]1xbet[/url]
Лучшая Букмекерская контора для ставок [url=https://1xbet-40.ru/]1xbet[/url]
Лучшая Букмекерская контора для ставок [url=https://1xbet-40.ru/]1xbet[/url]
stromectol farmacia buy stromectol in canada [url=https://dailymedgoodwxr.com/]stromectol cream for lice[/url] stromectol ivermectine stromectol for covid
Download 2,681 safari icons. Available in PNG and SVG formats. Ready to be used in web design, mobile apps and presentations [url=https://perfectmedia4u.blogspot.com/2024/03/revamping-interface-evolution-of.html]settings Icon[/url]
Топ Букмекерская контора [url=https://1xbet-42.ru/]1xbet[/url]
Надежная Букмекерская контора для ставок [url=https://1xbet-43.ru/]1xbet[/url]
https://www.ibm.com
Современная потолочная люстра для гостиной люстра для спальни освещение кухни может быть затемнением приложения с помощью пульта дистанционного управления акриловый материал завод прямых продаж лампа [url=http://estesvet.ru]люстра на кухню потолочная купить в москве[/url]
Самая надежная Букмекерская контора для ставок [url=https://1xbet-44.ru/]1xbet[/url]
Самая надежная Букмекерская контора для ставок [url=https://1xbet-44.ru/]1xbet[/url]
Топ Букмекерская контора для ставок[url=https://1xbet-45.ru/]1xbet[/url]
Самая надежная Букмекерская контора для ставок №1 [url=https://1xbet-46.ru/]1xbet[/url]
Самая надежная Букмекерская контора для ставок №1 [url=https://1xbet-46.ru/]1xbet[/url]
Самая надежная Букмекерская контора №1 [url=https://1xbet-48.ru/]1xbet[/url]
Самая надежная Букмекерская контора №1 [url=https://1xbet-48.ru/]1xbet[/url]
Um dos melhores jogos para ganhar [url=https://fortune-tiger3.org/]Fortune Tiger[/url]
Um dos melhores jogos para ganhar [url=https://fortune-tiger3.org/]Fortune Tiger[/url]
Самая надежная Всем рекомендую Букмекерскую контору №1 [url=https://1xbet-50.ru/]1xbet[/url]
Самая надежная Всем рекомендую Букмекерскую контору №1 [url=https://1xbet-50.ru/]1xbet[/url]
Готовьтесь к безумию: Американское правительство предупреждает о солнечном затмении, грозящем нарушить все. Сумки для выживания, заполненные секретами, мобильными телефонами и компасами, становятся нормой. Откройте правду в нашем захватывающем видео! [url=https://vm.tiktok.com/ZGemYu97R/]https://vm.tiktok.com/ZGemYu97R/[/url]
Всем рекомендую Букмекерскую контору №1 [url=https://1xbet-53.ru/]1xbet[/url]
Всем рекомендую Букмекерскую контору №1 [url=https://1xbet-53.ru/]1xbet[/url]
Самая лучшая Букмекерская контора [url=https://1xbet-52.ru/]1xbet[/url]
[url=http://podbor-it-spetsialistov.ru/]http://podbor-it-spetsialistov.ru/[/url]
[url=http://podbor-it-spetsialistov.ru/]http://podbor-it-spetsialistov.ru/[/url]
Моя рекомендация - Букмекерская контора №1 [url=https://1xbet-55.ru/]1xbet[/url]
Моя рекомендация - Букмекерская контора №1 [url=https://1xbet-55.ru/]1xbet[/url]
בחובן מגוון יפיפיות אקזוטיות, עדינות, בלונדיניות ושחורות המציעות אירוח שם, מוצא, צבע שיער, כמות אולי… שאלתם את עצמכם מהם הנשים אותן אתם יכולים לקבל? נערות ליווי רוסיות, נערות ליווי ישראליות, נערות לאירועים מסיבות וכל דבר העולה בדמיונכם. נערות הליווי <a href=http://www.pornopedia.co.il/>Order erotic massage in Tel Aviv and sex</a>
או לבית מלון ולהנות משירותי ליווי מושלמים. נערות ליווי בפתח בסביבתה וכוללת אטרקציות רבות של בילויים, יציאות, שתייה וקולינריה. כחלק מזאת, עפולה כוללת בתוכה אזורי תעשייה רבים ולכן גם מלאה הלקוח ירגיש שהוא הגיע הביתה למערכת מובנת שמתורגמת לכל השפות שיש והכל <a href=http://edensexshop.co.il/>Order erotic massage in Tel Aviv and sex</a>
אזורי המסחר הגדולים ביותר, האטרקציות המרכזיות וביניהן קולינרייה יוצאת דופן. כחלק מכך, גם נושא שיקרה אחר כך תלוי רק בכם. כאן תוכל למצוא מגוון רחב של דירות דיסקרטיות באשקלון, אשדוד והסביבה כולל כתובות, טלפונים וניווט שיביא הליווי מספקים את כל האווירה הנדרשת <a href=http://www.bdsm-nikki.co.il/>Sexy escort Jerusalem girls for all men seeking relaxation</a>
Моя рекомендация - Букмекерская контора №1 в мире [url=https://1xbet-56.ru/]1xbet[/url]
Моя рекомендация - Букмекерская контора №1 в мире [url=https://1xbet-56.ru/]1xbet[/url]
Моя рекомендация - Букмекерская контора №1 [url=https://1xbet-58.ru/]1xbet[/url]
Моя рекомендация - Букмекерская контора №1 [url=https://1xbet-58.ru/]1xbet[/url]
Легендарная Букмекерская контора №1 [url=https://1xbet-59.ru/]1xbet[/url]
Легендарная Букмекерская контора №1 [url=https://1xbet-59.ru/]1xbet[/url]
Ofereco a voce o melhor jogo [url=https://fortune-tiger3.net/]Fortune Tiger[/url]
Ofereco a voce o melhor jogo [url=https://fortune-tiger3.net/]Fortune Tiger[/url]
<a href="https://www.dibiz.com/michaelx60">https://www.dibiz.com/michaelx60</a>
Всем рекомендую Букмекерскую контору [url=https://1xbet-5.ru/]1xbet[/url]
Всем рекомендую Букмекерскую контору [url=https://1xbet-5.ru/]1xbet[/url]
Официальный сайт 1Вин казино предлагает лицензионные игры с высокой отдачей, но для захода требуется найти зеркало 1win casino [url=https://1winbk.1-musical.ru/]1Вин казино[/url]
O melhor e mais popular jogo [url=https://fortune-tiger3.xyz/]Fortune Tiger[/url]
O melhor e mais popular jogo [url=https://fortune-tiger3.xyz/]Fortune Tiger[/url]
Henkuai y Marca Espanahan organizado la visita de los diez influencers chinos mas importantes a Espana con el objetivo de promocionar el pais. Estos acumulan entre todos mas de 30 millones de seguidores y abarcan campos muy diferentes [url=https://simpleflying.com/madrid-airport-chinese-passengers/]https://simpleflying.com/madrid-airport-chinese-passengers/[/url]
<a href="https://www.transformacioneducativa.edu.py/profile/stanleyvbz35/profile">https://www.transformacioneducativa.edu.py/profile/stanleyvbz35/profile</a>
Recomendo o popular jogo a todos [url=https://fortune-tiger2.vip/]Fortune Tiger[/url]
Recomendo o popular jogo a todos [url=https://fortune-tiger2.vip/]Fortune Tiger[/url]
אביב, ובמרכז, ובעצם בכל אזור בישראל, היא יקרה רק במעט יותר מבילוי בדירות דיסקרטיות בתל אביב. עם עוד שלכם ועל טעמכם האישי. בפורטל אקספיינדר אתם נהנים ממודעות המתעדכנות באופן שוטף וקבוע. המודעות מלוות בתמונות אמתיות כך שתוכלו ביתר להתנתק ולהתרחק לעולם אחר בו <a href=http://xxxmovies.co.il/>נערות ליווי פרטית</a>
what does provigil contain provigil cost no insurance [url=https://webmddailymeddd.com/]buy provigil with prescription[/url] reddit provigil provigil taper
<a href="https://ucgp.jujuy.edu.ar/profile/stanleyvbz35/">https://ucgp.jujuy.edu.ar/profile/stanleyvbz35/</a>
Букмекерская компания Мостбет является ведущим игроком не только на рынке России, но и в других странах, включая Казахстан, Узбекистан, Азербайджан, Киргизию и многие другие. Легальный статус компании гарантирует честную и безопасную игру [url=https://vipstav.ru/]мостбет[/url]
Переходим сюда и выигрываем в [url=https://godovalov.ru/]1win[/url]
Переходим сюда и выигрываем в [url=https://godovalov.ru/]1win[/url]
<a href="https://jobs.lifewest.edu/employer/stanleyvbz35/?v=87a47565be47">https://jobs.lifewest.edu/employer/stanleyvbz35/?v=87a47565be47</a>
Проверенный магазин, низкие цены на аккаунты с токенами, моментальная выдача купленного аккаунта, высокая репутация магазина. Купите один раз и будете нашим постоянным клиентом! Так-же занимаемся продвижением модельного аккаунта BongaCams [url=https://bongacams-x.ru/]аккаунты bongacams купить[/url]
Its like youu rread my thoughts! You seem to know a lot approximately this, such as yoou wrote the e-book in itt orr something.
I think tht you simply can do with some % to drive tthe message
house a little bit, however instead of that,
this is magnificent blog. A gfeat read. I will
definitely be back. https://www.waste-ndc.pro/community/profile/tressa79906983/
Eu recomendo esse jogo a todos [url=https://fortune-tiger-1.com/]fortune Tiger[/url]
<a href=https://github.com/ForexRobotEasy/Stenvall-Mark-III>https://github.com/ForexRobotEasy/Stenvall-Mark-III</a>
<a href=https://prayertimein.com/>prayertimein.com</a>
zithromax costa rica can zithromax cure bv [url=https://emonaidhealtthh.com/]zithromax chlamydia dose[/url] zithromax para la infeccion de muela zithromax sonne
<a href="https://jesusfg35.edublogs.org/2024/03/28/%d0%b8%d0%b7%d1%83%d1%87%d0%b0%d0%b5%d0%bc-%d0%bb%d1%83%d1%87%d1%88%d0%b8%d0%b5-%d0%b2%d0%b0%d1%80%d0%b8%d0%b0%d0%bd%d1%82%d1%8b-%d0%ba%d1%80%d0%b0%d1%82%d0%ba%d0%be%d1%81%d1%80%d0%be%d1%87%d0%bd/">https://jesusfg35.edublogs.org/2024/03/28/%d0%b8%d0%b7%d1%83%d1%87%d0%b0%d0%b5%d0%bc-%d0%bb%d1%83%d1%87%d1%88%d0%b8%d0%b5-%d0%b2%d0%b0%d1%80%d0%b8%d0%b0%d0%bd%d1%82%d1%8b-%d0%ba%d1%80%d0%b0%d1%82%d0%ba%d0%be%d1%81%d1%80%d0%be%d1%87%d0%bd/</a>
Турецкие сериалы для увидения турецких национальных праздников; Возможность увидеть турецкие национальные праздники [url=https://newturkishserials.ru/]турецкие сериалы про рыцарей[/url]
<a href="https://tapchivatuyentap.tlu.edu.vn/Activity-Feed/My-Profile/UserId/35052">https://tapchivatuyentap.tlu.edu.vn/Activity-Feed/My-Profile/UserId/35052</a>
Pin Up Casino (Пин Ап) официальный сайт онлайн казино в Казахстане. На официальном сайте казино Пин Ап можно найти большой выбор лотоматов, которые позволяют игрокам играть в онлайн режиме и зарабатывать реальные деньги [url=https://fast-zero21.info/]казино пин ап[/url]
The shortcut of quick money. The first deposit bonus is 200% - https://goo.su/YKWd42
Всем рекомендую Букмекерскую контору [url=https://1win-5.org/]1win[/url]
Всем рекомендую Букмекерскую контору [url=https://1win-5.org/]1win[/url]
Jogue e ganhe no jogo [url=https://fortune-tiger-2.com/]fortune Tiger[/url]
Jogue e ganhe no jogo [url=https://fortune-tiger-2.com/]fortune Tiger[/url]
Легендарная Букмекерская контора [url=https://1win-5.net/]1win[/url]
<a href="https://tapchivatuyentap.tlu.edu.vn/Activity-Feed/My-Profile/UserId/35052">https://tapchivatuyentap.tlu.edu.vn/Activity-Feed/My-Profile/UserId/35052</a>
Рекомендую Букмекерскую контору [url=https://1win-5.com/]1win[/url]
Рекомендую Букмекерскую контору [url=https://1win-5.com/]1win[/url]
Лучшая Букмекерская контора [url=https://1win-5.сс/]1win[/url]
בישראל בפינות שקטות ונחבאות ממוקמות להן דירות דיסקרטיות אשר מהוות פתרון מושלם לזוגות הנקלעים לאזור שיקרה אחר כך תלוי רק בכם. כאן תוכל למצוא מגוון רחב של דירות דיסקרטיות באשקלון, אשדוד והסביבה כולל כתובות, טלפונים וניווט שיביא האחת העונה לטעמך האישי. נערות <a href=http://www.thegoodnews.co.il/>Tel Aviv escort girls for pleasing the pickiest men</a>
[url=https://stepbitcoin.ru]https://stepbitcoin.ru[/url]
Va e ganhe com o jogo [url=https://fortune-tiger-2.xyz/]fortune Tiger[/url]
Va e ganhe com o jogo [url=https://fortune-tiger-2.xyz/]fortune Tiger[/url]
Спасибо за ваше известие. Мы ценим ваш объяснение и готовы для вас посодействовать. В случае если у вас есть какие-либо вспомогательные вопросы либо необходима дополнительная информация, не смущяйтесь требовать. Вкупе мы создадим наш форум еще чем какого-либо другого!
[url=https://forum.md/ru/3990017]https://forum.md/ru/3990017[/url]
<a href="https://forum.edu.az/profil/stanleyvbz35/">https://forum.edu.az/profil/stanleyvbz35/</a>
בחיפה, קריות והצפון נמאס לך כבר מטינדר? לא רוצה האתר מציע לכם את הבנות היפות והשוות ביותר שתוכלו לדמיין מה גם שהכל אמיתי ומאומת ע"י האתר בצורה קפדנית ביותר שלא נראתה בשום אתר ליווי נערת ליווי שתגיע עד אליך לעיסוי? הגעת למקום הנכון. כאן תמצא את כל שרותי <a href=http://www.bridge-talk.co.il/>חדרים דיסקרטיים בחיפה</a>
Спасибо за ваше сообщение. Мы ценим ваш комментарий и готовы вам посодействовать. В случае если у вас есть какие-либо дополнительные вопросы либо необходима добавочная информация, не стесняйтесь спрашивать. Вкупе мы создадим наш форум еще как никакого другого!
[url=https://primarie.halleykm.md/forum/171/descoper-magia-moldovei-la-fatamorganamd-povestete-cu-tradiiile-noastre]https://primarie.halleykm.md/forum/171/descoper-magia-moldovei-la-fatamorganamd-povestete-cu-tradiiile-noastre[/url]
Для венчания невесты предлагаем свадебные туфли недорого <a href=https://svadebniy-salon-moskva.ru/>https://svadebniy-salon-moskva.ru/</a>
Топовая Букмекерская контора [url=https://1win-5.icu/]1win[/url]
Топовая Букмекерская контора [url=https://1win-5.icu/]1win[/url]
Крутая Букмекерская контора [url=https://1win-5.me/]1win[/url]
Крутая Букмекерская контора [url=https://1win-5.me/]1win[/url]
<a href="https://my.talladega.edu/ICS/_portletview_/Academics/BUS/BUS__368/2016_SP-BUS__368-FT___2/Collaboration%5d%5d%5d%5d%5d%5d%5d%5d%5d.jnz?portlet=Forums&screen=PostView&screenType=change&id=081be20f-930e-4d1b-ad3e-2293435d2eee">https://my.talladega.edu/ICS/_portletview_/Academics/BUS/BUS__368/2016_SP-BUS__368-FT___2/Collaboration%5d%5d%5d%5d%5d%5d%5d%5d%5d.jnz?portlet=Forums&screen=PostView&screenType=change&id=081be20f-930e-4d1b-ad3e-2293435d2eee</a>
Топ Букмекерская контора [url=https://1win-5.top/]1win[/url]
Топ Букмекерская контора [url=https://1win-5.top/]1win[/url]
Ganhe dinheiro de verdade jogando o jogo [url=https://fortune-tiger-1.top/]Fortune Tiger[/url]
Ganhe dinheiro de verdade jogando o jogo [url=https://fortune-tiger-1.top/]Fortune Tiger[/url]
<a href="http://www.alexandria.gov.eg/Lists/List30/DispForm.aspx?ID=60164">http://www.alexandria.gov.eg/Lists/List30/DispForm.aspx?ID=60164</a>
Советую лучшую Букмекерскую контору [url=https://1win-4.org/]1win[/url]
Советую лучшую Букмекерскую контору [url=https://1win-4.org/]1win[/url]
Криптовалютные биржи — это платформы, которые дают возможность трейдерам покупать и продавать криптовалюты, деривативы и другие криптоактивы [url=https://vc.ru/u/791482-dmitrii/1112307-luchshie-birzhi-kriptovalyut-dlya-rossii-v-2024-godu]лучшие биржи криптовалют[/url]
Советую лучшую в своем роде Букмекерскую контору [url=https://1win-4.top/]1win[/url]
Советую лучшую в своем роде Букмекерскую контору [url=https://1win-4.top/]1win[/url]
Надежная Букмекерская контора №1 [url=https://1win-4.xyz/]1win[/url]
[url=http://www.youtube.com/watch?v=hxJLz2S29d8]Голос, что проникает в самую глубину – Андрей Вебер[/url]
<a href="https://www.just.edu.jo/Lists/Survey/DispForm.aspx?ID=7565">https://www.just.edu.jo/Lists/Survey/DispForm.aspx?ID=7565</a>
Советую лучшую Букмекерскую контору [url=https://1win-4.com/]1win[/url]
Советую лучшую Букмекерскую контору [url=https://1win-4.com/]1win[/url]
נקלעים להרצליה ולמרכז הארץ וחשקה בליבכם לחוות חוויה מפנטזת עם בחורה שתענג אתכם בשירותי ליווי וסקסיות, שהינן מקצועיות ומעניקות את מיטב השירותים לפי בחירתך. כאן תוכל לבחור מתוכן, את מי שעונה על טעמך ועל דרישותיך ותעניק לך לקוחות – גברים, נשים ואלו שלא <a href=http://lotem-blog.co.il/>דירות דיסקרטיות</a>
[url=https://kms-download.net]kmspico [/url]
Известный во всем СНГ телеграмм бот Глаз Бога уже почти год не сходит с первых полос множества новостных агентств. Программа Глаз Бога для поиска людей завоевала огромную популярность у многих пользователей [url=http://glazboga.vip/]глаз бога телеграм[/url]
<a href=https://queenspalace.pro/>вип эскорт москва</a>
чтобы не затруднять себя этим, [url=http://coolgrove.net/__media__/js/netsoltrademark.php?d=pathiaf.com]http://coolgrove.net/__media__/js/netsoltrademark.php?d=pathiaf.com[/url] гемблеру стоит сразу написать в службу поддержки.
Советую выбрать лучшую Букмекерскую контору [url=https://1win-4.icu/]1win[/url]
Советую выбрать лучшую Букмекерскую контору [url=https://1win-4.icu/]1win[/url]
Самая надежная Букмекерская контора №1 в мире [url=https://1win-4.me/]1win[/url]
Самая надежная Букмекерская контора №1 в мире [url=https://1win-4.me/]1win[/url]
[url=https://getb8.us/online-casinos/]games casino
[url=https://getb8.us/online-casinos/]top casino site
<a href="http://iot.ttu.edu.tw/members/stanleyvbz35/activity/641692/">http://iot.ttu.edu.tw/members/stanleyvbz35/activity/641692/</a>
הארץ, כשמו הוא, נמצא בלב ליבה של מדינת ישראל וכולל את רוב אוכלוסיית אסייתי ועוד נמצאים לשימושכם בחיפה ובצפון! ניתן להזמין עיסוי ארוטי בחיפה בקלות. העיסויים ממוקמים בכל רחבי העיר וכוללים את הנשים דירה דיסקרטית בקריות דירה דיסקרטית בקריות כוללת כמה וכמה <a href=http://www.aroma-life.co.il/>דירות דיסקרטיות בנתניה</a>
DeCambre, Stamp (April 17, 2021, [url=https://siddhienterprises.net/modeling-optimization-and-simulation-rounds/]https://siddhienterprises.net/modeling-optimization-and-simulation-rounds/[/url]). "This dogecoin chart provides the most clear explanation of the hype around the cryptocurrency is a "joke"."
Топовое украинское [url=http://homitalicus.it/__media__/js/netsoltrademark.php?d=pathiaf.com]http://homitalicus.it/__media__/js/netsoltrademark.php?d=pathiaf.com[/url] на настоящие деньги. Их классическое значение - несколько игровых барабанов, аналог автоматов.
<a href="https://inspt.utn.edu.ar/members/jenkinx60/activity/9497/">https://inspt.utn.edu.ar/members/jenkinx60/activity/9497/</a>
Выбираем лучшую Букмекерскую контору [url=https://1win-6.com/]1win[/url]
Выбираем лучшую Букмекерскую контору [url=https://1win-6.com/]1win[/url]
Топовая Букмекерская контора №1 [url=https://1win-6.net/]1win[/url]
дозволяється встановлювати потрібне ПЗ, [url=http://jobest-tradelinks.com/index.php/component/k2/item/4]http://jobest-tradelinks.com/index.php/component/k2/item/4[/url] виконувати індивідуальні настройки під проект. Також відзначимо, що послуга за традицією випускається на поточний рік - так і зручніше і не потрібно щомісяця займатися платіжками.
Выбираем топовую Букмекерскую контору [url=https://1win-5.cc/]1win[/url]
Выбираем топовую Букмекерскую контору [url=https://1win-5.cc/]1win[/url]
<a href="https://medicine.ju.edu.jo/Lists/ConfReg/DispForm.aspx?ID=71490">https://medicine.ju.edu.jo/Lists/ConfReg/DispForm.aspx?ID=71490</a>
Крутая Букмекерская контора №1 [url=https://1win-6.org/]1win[/url]
гостиницы в москве <a href=https://otelivmoskva.ru/oteli-i-gostinicy-v-moskve/>https://otelivmoskva.ru/oteli-i-gostinicy-v-moskve/</a>
<a href=https://rus-metiz.ru/zaklepki.htm/>вытяжные заклепки</a>
<a href="https://oag.treasury.gov.za/RMF/Lists/Framework%20Feedback/DispForm.aspx?ID=61124">https://oag.treasury.gov.za/RMF/Lists/Framework%20Feedback/DispForm.aspx?ID=61124</a>
По моему мнению Вы не правы. Давайте обсудим. Пишите мне в PM.
Yes. [url=http://www.cmpedu.co.kr/bbs/board.php?bo_table=free&wr_id=349544]http://www.cmpedu.co.kr/bbs/board.php?bo_table=free&wr_id=349544[/url] has mobile app for iOS, which anyone can download from upstore.
Выбираем надежную Букмекерскую контору [url=https://1win-6.me/]1win[/url]
Выбираем надежную Букмекерскую контору [url=https://1win-6.me/]1win[/url]
Выбрал для себя надежную Букмекерскую контору [url=https://1xbet-60.ru/]1xbet[/url]
Выбрал для себя надежную Букмекерскую контору [url=https://1xbet-60.ru/]1xbet[/url]
Рекомендация от меня - лучшая Букмекерская контора [url=https://1xbet-62.ru/]1xbet[/url]
Рекомендация от меня - лучшая Букмекерская контора [url=https://1xbet-62.ru/]1xbet[/url]
[url=https://antik-browser.com/]free antidetect browser[/url]
[url=https://antik-browser.com/]antik program[/url]
[url=https://antik-browser.com/]antidetect browser crack[/url]
[url=https://antik-browser.com/ru]антидетект скачать[/url]
[url=https://antik-browser.com/ru]скачать браузер adspower[/url]
[url=https://antik-browser.com/ru]что такое антик в крипте[/url]
https://antik-browser.com/ru
https://antik-browser.com/
Выбрал для себя топовую Букмекерскую контору [url=https://1xbet-63.ru/]1xbet[/url]
Выбрал для себя топовую Букмекерскую контору [url=https://1xbet-63.ru/]1xbet[/url]
Рекомендация от меня - самая лучшая Букмекерская контора [url=https://1xbet-64.ru/]1xbet[/url]
Рекомендация от меня - самая лучшая Букмекерская контора [url=https://1xbet-64.ru/]1xbet[/url]
Выбрал для себя лучшую Букмекерскую контору [url=https://1xbet-65.ru/]1xbet[/url]
Выбрал для себя лучшую Букмекерскую контору [url=https://1xbet-65.ru/]1xbet[/url]
Самая лучшая Букмекерская контора [url=https://1xbet-66.ru/]1xbet[/url]
Самая лучшая Букмекерская контора [url=https://1xbet-66.ru/]1xbet[/url]
Выбрал для себя потрясающую Букмекерскую контору [url=https://1xbet-67.ru/]1xbet[/url]
Выбрал для себя потрясающую Букмекерскую контору [url=https://1xbet-67.ru/]1xbet[/url]
[url=https://antik-browser.com/]anti detect browser download[/url]
[url=https://antik-browser.com/]антик прокси[/url]
[url=https://antik-browser.com/]antik-browser[/url]
[url=https://antik-browser.com/ru]webmail antik[/url]
[url=https://antik-browser.com/ru]антидетект браузер для андроид[/url]
[url=https://antik-browser.com/ru]как установить антидетект браузер[/url]
https://antik-browser.com/ru
https://antik-browser.com/
Самая лучшая Букмекерская контора, советую [url=https://1xbet-68.ru/]1xbet[/url]
Самая лучшая Букмекерская контора, советую [url=https://1xbet-68.ru/]1xbet[/url]
<a href=https://www.instagram.com/t6oooooo/>Продвижение сайта Алматы</a> максимальная видимость в поисковых системах, точечная аудитория, уникальные стратегии роста. Достижение вершин онлайн-успеха!
Выбрал для себя шикарную Букмекерскую контору [url=https://1xbet-69.ru/]1xbet[/url]
Выбрал для себя шикарную Букмекерскую контору [url=https://1xbet-69.ru/]1xbet[/url]
Самая надежная Букмекерская контора, советую [url=https://1xbet-70.ru/]1xbet[/url]
<a href=https://t.me/s/ramen_bet_zerkalo>https://t.me/s/ramen_bet_zerkalo</a>
Выбрал шикарную Букмекерскую контору [url=https://1xbet-71.ru/]1xbet[/url]
Представляю топовую Букмекерскую контору - [url=https://1xbet-78.ru/]1xbet[/url]
[url=https://antik-browser.com/]anitk[/url]
[url=https://antik-browser.com/]anti browser for pc[/url]
[url=https://antik-browser.com/]antik testi[/url]
[url=https://antik-browser.com/ru]антидетект браузер на айфон[/url]
[url=https://antik-browser.com/ru]antic browser[/url]
[url=https://antik-browser.com/ru]антидетект браузер бесплатно[/url]
https://antik-browser.com/ru
https://antik-browser.com/
Free Instagram Tools:
[url=https://bit.ly/free-instagram-likes-insta]Instagram Likes Free[/url]
Выбрал лучшую Букмекерскую контору [url=https://1xbet-74.ru/]1xbet[/url]
Выбрал лучшую Букмекерскую контору [url=https://1xbet-74.ru/]1xbet[/url]
Самая крутая Букмекерская контора, советую [url=https://1xbet-73.ru/]1xbet[/url]
Детский спортивный комплекс для дома KindWood Plus 1.наших спортивных комплексов.
<a href=http://www.blacksea.odessa.ua/?page_id=101>Отзывы о гимнастический комплекс уличный</a>
<a href=http://hk-traktor.ru/category/obshhenie-bolelshhikov>Отзывы о уличный турник</a>
<a href=http://www.japan-sumo.ru/?q=tochiozan>Продам манжеты для кроссовера блочного тренажера.</a>
Детский спортивный комплекс для квартиры «Карамелька виолет»Производство детских площадок.
[url=http://photo-23.ru/index.php?name=plugins&p=out&url=boba-oppa.io]http://photo-23.ru/index.php?name=plugins&p=out&url=boba-oppa.io[/url] (BOBAOPPA) easy buy and sell on 2 cryptocurrency exchanges.
Представляю лучшую Букмекерскую контору - [url=https://1xbet-75.ru/]1xbet[/url]
Представляю лучшую Букмекерскую контору - [url=https://1xbet-75.ru/]1xbet[/url]
Крутая Букмекерская контора, советую [url=https://1xbet-76.ru/]1xbet[/url]
Крутая Букмекерская контора, советую [url=https://1xbet-76.ru/]1xbet[/url]
Регистрация в Vodka Казино <a href=https://casino-vodka.top/>vodka casino</a> – это простой и интуитивно понятный процесс. Требуется лишь заполнить несколько полей, указав базовую информацию о себе, и подтвердить свою учетную запись. После этого, игроки имеют доступ ко всем функциям сайта, включая бонусы, акции и эксклюзивные предложения.
[url=https://antik-browser.com/]anti detect browser for multi account management[/url]
[url=https://antik-browser.com/]free anti detect browser[/url]
[url=https://antik-browser.com/]antidetect browse[/url]
[url=https://antik-browser.com/ru]щсещикщцыук[/url]
[url=https://antik-browser.com/ru]скачати український браузер[/url]
[url=https://antik-browser.com/ru]антидитект[/url]
https://antik-browser.com/ru
https://antik-browser.com/
Лучшая Букмекерская контора, советую [url=https://1xbet-79.ru/]1xbet[/url]
Лучшая Букмекерская контора, советую [url=https://1xbet-79.ru/]1xbet[/url]
Представляю топовую Букмекерскую контору - [url=https://1xbet-78.ru/]1xbet[/url]
Представляю топовую Букмекерскую контору - [url=https://1xbet-78.ru/]1xbet[/url]
Представляю топовую Букмекерскую контору - [url=https://1xbet-78.ru/]1xbet[/url]
Представляю наилучшую Букмекерскую контору - [url=https://1xbet-80.ru/]1xbet[/url]
Представляю наилучшую Букмекерскую контору - [url=https://1xbet-80.ru/]1xbet[/url]
<a href=http://flowervl.ru/>http://flowervl.ru/</a>
Топовая Букмекерская контора, советую [url=https://1xbet-81.ru/]1xbet[/url]
Gama Casino is a new gambling establishment. Gama casino opened in 2024, delighting players with big bonuses: 200% on account replenishment [url=https://www.koreafurniture.com/bbs/board.php?bo_table=free&wr_id=3794833]https://www.koreafurniture.com/bbs/board.php?bo_table=free&wr_id=3794833[/url]
Рекомендую Букмекерскую контору - [url=https://1xbet-82.ru/]1xbet[/url]
Рекомендую Букмекерскую контору - [url=https://1xbet-82.ru/]1xbet[/url]
Scotty Chat is a crypto companion to [url=http://allianceforgoodgovernment.org/product/vote-badge/]http://allianceforgoodgovernment.org/product/vote-badge/[/url], based on artificial intelligence! Scotty Swap is excellent one-stop shop for seamless and lightning-fast token exchange.
Рекомендую лучшую Букмекерскую контору - [url=https://1xbet-84.ru/]1xbet[/url]
Рекомендую лучшую Букмекерскую контору - [url=https://1xbet-84.ru/]1xbet[/url]
Рекомендую топовую Букмекерскую контору - [url=https://1xbet-86.ru/]1xbet[/url]
Рекомендую топовую Букмекерскую контору - [url=https://1xbet-86.ru/]1xbet[/url]
Лучшая Букмекерская контора, рекомендую [url=https://1xbet-87.ru/]1xbet[/url]
I got this web page from my pal who told me regarding
this website and now this time I am browsing this
site and reading very informative posts at this place.
http://hellebores.org/__media__/js/netsoltrademark.php?d=Originality-diploman.com
Топовая Букмекерская контора - [url=https://1xbet-88.ru/]1xbet[/url]
Топовая Букмекерская контора - [url=https://1xbet-88.ru/]1xbet[/url]
[url=https://samoylovaoxana.ru/tag/foto-madagaskara/]фото Мадагаскара[/url] или [url=https://samoylovaoxana.ru/tag/tury-v-turcziyu/]туры в Турцию[/url]
[url=https://samoylovaoxana.ru/tag/otdyh-za-graniczej/]отдых за границей[/url]
https://samoylovaoxana.ru/afrikanskaia-koroleva/
Ещё можно узнать: [url=http://yourdesires.ru/home-and-family/cookery/1143-ananas-polza-i-vred.html]ананас вред и польза[/url]
Национальные парки
Топовая Букмекерская контора - [url=https://1win-6.cc/]1win[/url]
<a href="https://recenzeefekt.cz/">recenzeefekt.cz</a>
Топовая Букмекерская контора - [url=https://1win-6.cc/]1win[/url]
Надежная Букмекерская контора, советую [url=https://1win-6.icu/]1win[/url]
https://maps.google.sm/url?q=https://kupit-dzheneriki-v-spb.ru
Выбирая нас, вы получаете быструю и профессиональную эвакуацию по разумной цене · Любая сложность. 10-летний опыт. Профессиональный подход. Официально [url=https://yslygi66.ru/kak-otmenit-podpisku-na-android]https://yslygi66.ru/kak-otmenit-podpisku-na-android[/url]
Лучшая Букмекерская контора - [url=https://1win-6.top/]1win[/url]
Лучшая Букмекерская контора - [url=https://1win-6.top/]1win[/url]
Букмекерская контора №1, советую [url=https://1win-6.xyz/]1win[/url]
Based on God’s instructions, Abraham travelled to a place called Canaan where the Canaanites lived. There is no reason given for God’s choice of Palestine/Canaan for Abraham to journey to [url=https://bible-history.com/maps/map-persian-empire]persia on world map[/url]
Лучшая Букмекерская контора на просторах - [url=https://1win-7.net/]1win[/url]
Букмекерская контора №1 в мире, советую [url=https://1win-7.org/]1win[/url]
Лучшая Букмекерская контора на просторах - [url=https://1win-7.net/]1win[/url]
Топовая Букмекерская контора на просторах - [url=https://1win-7.com/]1win[/url]
Топовая Букмекерская контора на просторах - [url=https://1win-7.com/]1win[/url]
Букмекерская контора №1 в мире [url=https://1win-7.me/]1win[/url]
Топовая Букмекерская контора в мире - [url=https://1win-7.cc/]1win[/url]
Топовая Букмекерская контора в мире - [url=https://1win-7.cc/]1win[/url]
Лучшая Букмекерская контора №1 в мире [url=https://1win-7.icu/]1win[/url]
A casa de apostas mais fiavel do mundo - [url=https://1win-7.top/]1win[/url]
A casa de apostas mais fiavel do mundo - [url=https://1win-7.top/]1win[/url]
Melhor casa de apostas n? 1 do mundo [url=https://1win-7.xyz/]1win[/url]
Melhor casa de apostas n? 1 do mundo [url=https://1win-7.xyz/]1win[/url]
O escritorio da casa de apostas mais fiavel - [url=https://1win-8.cc/]1win[/url]
O escritorio da casa de apostas mais fiavel - [url=https://1win-8.cc/]1win[/url]
Casa de apostas confiavel n? 1 [url=https://1win-8.icu/]1win[/url]
Casa de apostas confiavel n? 1 [url=https://1win-8.icu/]1win[/url]
Casa de apostas fiavel, recomendo-a - [url=https://1win-8.top/]1win[/url]
Завораживающие возможности онлайн азартных игр простираются в виртуальной реальности, где каждый участник погружается в увлекательное путешествие по миру азарта и волнения [url=https://www.aura-invest.com/bbs/board.php?bo_table=free&wr_id=2782444]https://www.aura-invest.com/bbs/board.php?bo_table=free&wr_id=2782444[/url]
ivermectin ivermectin [url=https://stromectolt.com]ivermectin on humans[/url] where to get ivermectin online
ivermectin heartgard https://stromectolt.com/ - ivermectin on humans
<a href=https://cs2lab.pro/cs-sites/>steam cs 2 skin bets website 2024</a>
Низкие цены на изготовление аквариумов <a href=https://akvariumy-na-zakaz.ru/>https://akvariumy-na-zakaz.ru/</a>
Вы можете заказать у нас услуги грузчиков в Москве и Московской области для любых работ, начиная с обычных погрузо-разгрузочных и заканчивая всеми видами переездов и такелажных работ [url=https://yandex.ru/profile/156635527487]Грузоперевозки Москва[/url]
Aconselho voce a usar os servicos dessa empresa de apostas [url=https://1win-10.com/]1win[/url]
Aconselho voce a usar os servicos dessa empresa de apostas [url=https://1win-10.com/]1win[/url]
Prefiro essa empresa de apostas [url=https://1win-4.cc/]1win[/url]
Prefiro essa empresa de apostas [url=https://1win-4.cc/]1win[/url]
Приветики!
купить диплом специалиста
Желаю каждому прекрасных отметок!
https://saratovturizm.ru/forum/topic.php?forum=11&topic=79&v=
купить диплом института
купить диплом специалиста
купить диплом о высшем образовании
Get Inspired Today: Visit Our Website https://india-aviator-game.com/
With [url=http://rekonstrukciestriech.sk/ahoj-svet/]http://rekonstrukciestriech.sk/ahoj-svet/[/url], your tickets are always in front of your eyes.13 Visit a cinema, a concert venue or a sports stadium, having freely available only an iphone or an apple watch.
Considero esta casa de apostas a melhor [url=https://1win-10.icu/]1win[/url]
Considero esta casa de apostas a melhor [url=https://1win-10.icu/]1win[/url]
Торговля на Kraken. Завершив регистрацию на официальной сайте Кракен, пройдя минимум первые две ступени верификации (0-я и 1-я), а также внеся средства на депозит, можно заниматься зарабатыванием на разнице ценовых курсов либо при надобности обменивать криптовалюту в требуемых направлениях [url=https://t.me/kraken12su_bot]Телеграм бот Kraken ссылка[/url]
<a href=https://prilozhenie-winline.ru/>Winline приложение Android</a>
Долгие годы мы производим сувениры, подарки и рекламную продукция как для больших корпораций, так и для среднего и малого бизнеса [url=http://spektr-opt.ru/]конфеты ручной работы шоколадные[/url]
Читайте последние новости на тему в ленте новостей на сайте [url=https://newsman.info/]Newsman[/url] Получайте уведомления о свежих новостях в своем браузере.
Игорный бизнес в онлайн мире, словно многоликая галактика, предлагает множество вариантов для погружения в атмосферу азарта и развлечений. Некоторые вступают в это увлекательное путешествие в поисках удачи, другие - для того, чтобы отдохнуть от рутины и испытать незабываемые эмоции [url=http://littleyaksa.yodev.net/bbs/board.php?bo_table=free&wr_id=6054563]http://littleyaksa.yodev.net/bbs/board.php?bo_table=free&wr_id=6054563[/url]
Do you like crash games? Play now the online casino crash game Maverick in bwin Zambia website [url=https://arthursvtkd.ka-blogs.com/79772117/the-best-side-of-black-jack-in-zambia]https://arthursvtkd.ka-blogs.com/79772117/the-best-side-of-black-jack-in-zambia[/url]
Телесериал «Однажды в сказке» вышел на экраны 23 октября 2011 года, и сразу же завоевал свою аудиторию зрителей, которая не спадает до сих пор. Сериал состоит из 7 сезонов и 156 эпизодов. В этой одной кинокартине собраны практически все сказочные персонажи, с разных сказок [url=https://drimtim.ru/o-chem-serial-odnazhdy-v-skazke.html]Тут[/url]
Приложение для знакомств, которое призвано подобрать вам пару с использованием сложных алгоритмов и искусственного интеллекта. Как и в большинстве подобных сервисов, вам нужно создать анкету, но затем начинается самое интересное [url=https://datingworld.name/?language=russian]ЛУЧШИЙ САЙТ ЗНАКОМСТВ[/url]
Заглянув в мир онлайн-развлечений, каждый находит что-то по своему вкусу:будь то классические слоты, азартные столы с карточными играми или вращающиеся рулетки [url=http://nanike.es/index.php?option=com_kunena&view=topic&catid=3&id=211&Itemid=0]http://nanike.es/index.php?option=com_kunena&view=topic&catid=3&id=211&Itemid=0[/url]
ivermectin india buy online pharmaq ivermectin drops 1 5ml [url=https://dailymedgoodwxr.com/]prescription ivermectin[/url] ivermectin covid treatment mexico ivermectin online without a prescription
[url=http://xn-----8kcbihkwcb6a1acichnvglj6f.xn--p1ai/]подбор-ит-специалистов.рф[/url]
<a href=https://akvakraska.ru/stati/o-inzhenernyh-setyah/399866-remont-ventilyacii-vazhnost-i-osnovnye-problemy.html>капитальный ремонт системы вентиляции</a>
[url=https://t.me/escort_rabotar]https://t.me/escort_rabotar[/url]
מאוד, שכן גם דירות מפוארות יחסית שומרות על רמת תמחור הוגנת והמחיר שלהן שווה לכל כיס. זו גם הסיבה שהפופולאריות של דירות דיסקרטיות היא כל כך גבוהה – הן מאפשרות כמעט לכל אחד ליהנות מכמה שעות של מימוש פנטזיות וחוויות מטורפות, במחיר הוגן שקל לעמוד בו. כך גם מי <a href=http://suliko.top/>Tel Aviv escort girls for pleasing the pickiest men</a>
in August 2021, the Cuban government adopted resolution 215 on recognition and regulation of [url=http://thepalaceschool.com/component/k2/item/2-news222/2-news222]http://thepalaceschool.com/component/k2/item/2-news222/2-news222[/url], like bitcoin.
О, этот сайт! Бесконечная череда страниц, наполненных буквами, словами и фразами, вроде как объединенных общей темой [url=https://xn--n1aaccchj.xn--p1ai/magaziny]отзывы[/url]
Магазин спортивной фармакологии - OxyShop. Это всемирно известный надёжный поставщик качественных препаратов для спортсменов [url=https://pharmabay.name]анаболические стероиды балкан фарма[/url]
современный центр медицины профилактики <a href=http://za-chas.info>сделать медицинскую справку задним числом официально в Москве</a> сделать мед справку в Москве
Если сумма выигрыша превышает 5 млн рублей, 1Win имеет право установить индивидуальный лимит на вывод в сутки. Мобильная версия и приложения. Для юзеров, предпочитающих мобильные гаджеты, у «1Вин» есть мобильная версия и приложения на iOS и Android [url=http://russianyoungporn.com/go.php?url=https://ookod.ru/]1win регистрация[/url]
По моему мнению Вы допускаете ошибку. Предлагаю это обсудить. Пишите мне в PM, пообщаемся.
это огромный воды туристической достопримечательностью в этой стране. [url=http://atlaszeus.com/index.php/component/k2/item/3/3]http://atlaszeus.com/index.php/component/k2/item/3/3[/url] автомобилей в германии позволит вам свободу, вам надо посетить все назначения, что вам нужно.
This course is not for the faint of heart, and with taking into account a [url=http://www.kenva.co.kr/gnuboard5/bbs/board.php?bo_table=free&wr_id=150620]http://www.kenva.co.kr/gnuboard5/bbs/board.php?bo_table=free&wr_id=150620[/url] of term papers works best minds in the industry, competition cannot be considered by itself for granted, despite the fact that 80% of the students in overall coped with him!
<a href=http://yopolis.ru/publikacii/5240-kak-sayty-poiska-avto-izmenyayut-pravila-igry-pri-pokupke-mashiny-pereklyuchite-skorost-na-maksimum.html>http://yopolis.ru/publikacii/5240-kak-sayty-poiska-avto-izmenyayut-pravila-igry-pri-pokupke-mashiny-pereklyuchite-skorost-na-maksimum.html</a>
את הדמיון – ולדעת שאין אפשרויות לא נכונות דירות דיסקרטיות – המקום המיוחד שלך דירות דיסקרטיות הן הרבה יותר מחלל נסתר. הדירות אלו מהוות מרחבים בטוחים בהם מתאפשר לך להתחבא מהעולם ולממש את הדחפים האמתיים שלך. הדירות האיכותיות יכולות להכיל מגוון רחב של מתקנים, <a href=http://matuta.top/>The hottest escort girls Tel Aviv services</a>
Привет!
Мы стремимся предоставить вам самую полную и достоверную информацию о событиях в Украине и мире. Наши новости помогают вам быть в курсе всех важных событий и их последствий, чтобы вы могли принимать информированные решения.
Все самое лучшее на сайте https://smi.in.ua/
[url=https://smi.in.ua/]Новости Украины ТОП[/url]
новости Украины сегодня
последние новости мира
новости Украины за день
Удачи!
My brother sugested I might like this web site. He used to bbe
entirely right. This post truoy made my day. You can not consider just how much time I
had spent for thi information! Thank you! https://www.waste-ndc.pro/community/profile/tressa79906983/
вывод из запоя <a href=https://krasnodar-narkolog.ru/>https://krasnodar-narkolog.ru/</a>
Здравствуйте!
Чорна п'ятниця в Україні у 2024 році – час для вигідних покупок та приємних сюрпризів! Дізнайтеся дату проведення та підготуйтеся до шопінгу заздалегідь, щоб не проґавити кращі пропозиції.
[url=https://crazysale.marketing/black-friday.html]чорна пятниця[/url]
[url=https://crazysale.marketing/black-friday.html]чорна пятниця[/url]
чорна пятниця
чорна п'ятниця
чорна пятниця 2024
Удачи!
Профили для облицовки стен являются неотъемлемой частью современного ремонта и помогают преобразить любое помещение [url=https://profplint.ru/]https://profplint.ru/[/url]
Open the suggestions table and click on the received result. Select contest. In [url=http://digma-parts.ru/published/SC/html/scripts/redirect_page.php?url=aHR0cHM6Ly93d3cubGF2cmFzMjRob3Jhcy5jb20uYnIvcG9ydGFsL2F2aWF0b3Itb3Utc3BhY2VtYW4tcGFyYS1sdWNyYXIv]http://digma-parts.ru/published/SC/html/scripts/redirect_page.php?url=aHR0cHM6Ly93d3cubGF2cmFzMjRob3Jhcy5jb20uYnIvcG9ydGFsL2F2aWF0b3Itb3Utc3BhY2VtYW4tcGFyYS1sdWNyYXIv[/url], sports betting is done promptly and unambiguously.
Кодирование от алкоголизма Алматы <a href=https://alcoholismcoding.kz/>https://alcoholismcoding.kz/</a>
<a href=https://vivod-iz-zapoya-dom.ru/>https://vivod-iz-zapoya-dom.ru/</a>
20 Trailblazers Are Leading The Way In Onlyfans Pornstars pornstars with
onlyfans
клева)
to guard and [url=https://duston.pl/witaj-swiecie/]https://duston.pl/witaj-swiecie/[/url] have the option use remotely or offline wallets.
нарколог лечение алкоголизма <a href=http://adtherapy.ru/>http://adtherapy.ru/</a>
The 10 Scariest Things About UK Onlyfans Pornstars pornstars On Onlyfans
Так и до бесконечности не далеко :)
among the recent market decline, dogeverse is [url=https://relishrecruitment.in/index.php/jobs/team-leader-international-and-domestic/comment-page-1/]https://relishrecruitment.in/index.php/jobs/team-leader-international-and-domestic/comment-page-1/[/url] advancing forward and today exceeded boundary in ten million greenbacks on pre-sale.
наркологическая клиника <a href=https://okcentr.kz/>https://okcentr.kz/</a>
Обычно организовывается не [url=http://ort.spb.ru/pma/inc/?melbet_promokod_pri_registracii_bonus_besplatno.html]http://ort.spb.ru/pma/inc/?melbet_promokod_pri_registracii_bonus_besplatno.html[/url] более 24 часов. возможно, посетитель не выполнил ценное условие премиальной программы. Активирует промокод, на случай если он у него существуют.
fans receive large rewards from the bookmaker organization [url=https://centre.umc.edu.dz/hpc/index.php/services/item/17-best-processors-2020-the-best-cpus-for-your]https://centre.umc.edu.dz/hpc/index.php/services/item/17-best-processors-2020-the-best-cpus-for-your[/url] 1 win bet. Although the processing of a bank transfer can take from 2 many hours, if you apply a cryptocurrency wallet, the transfer will be done quickly.
Hello!
This post was created with [url=https://2ssdsd3222aa.com]2ssdsd3222aa.com[/url]
Guide To English Pornstars: The Intermediate Guide The Steps To English Pornstars English Pornstars
Дизайн-радиаторы — функциональное украшение интерьера, доступные в разных цветах и размерах, с возможностью добавления тэнов [url=https://telegra.ph/CHto-takoe-dizajn-radiatory-otopleniya-03-11]https://telegra.ph/CHto-takoe-dizajn-radiatory-otopleniya-03-11[/url]
отдельно требуется понимать, [url=https://market.tradeholding.com/myad.cgi?size=120x240&servername=mama.ru%2Fforums%2Ftheme%2Fbinarnye-optsiony%2F]https://market.tradeholding.com/myad.cgi?size=120x240&servername=mama.ru%2Fforums%2Ftheme%2Fbinarnye-optsiony%2F[/url] что при минимальных вложениях доход будет небольшой. при этом, эта компания сотрудничает с 2012 года и всего прекрасно зарекомендовала себя.
The Best Onlyfans Pornstars Tricks To Transform Your Life Best Onlyfans Pornstar; Https://Buketik39.Ru,
Guide To Porn Star Kayleigh Wanless: The Intermediate Guide Towards Porn Star Kayleigh Wanless
porn star Kayleigh wanless
Алматы Азарт - это уникальное игровое пространство для людей старше 30 лет, которые ценят интеллектуальный досуг и общение [url=https://avatap.com.ru/event_agentstvo]https://avatap.com.ru/event_agentstvo[/url]
does amoxicillin help sinus infection can amoxicillin cause uti or yeast infection [url=https://drugsnetmedss.com/]amoxicillin syrup[/url] amoxicillin prior to dental work is amoxicillin used for yeast infection
Поставить счетчики на воду в квартире – означает значительно снизить затраты на оплату этой части ЖКХ [url=https://progkh.ru/]https://progkh.ru/[/url]
We bieden tijdelijke telefoonnummers in tientallen landen over de hele wereld, met duizenden nummers om uit te kiezen [url=https://codygjlh55576.vidublog.com/26435812/de-vrijheid-van-telegram-zonder-telefoonnummer]telegram telefoonnummer[/url]
If Satoshi had released Bitcoin 10 yrs. earlier, 9/11 would never have happened. – Max Keiser https://cutt.ly/pwBLE09s
Wanneer krijg ik een tijdelijk nummer? Als je met nummerbehoud overstapt naar Odido, krijg je van ons een tijdelijk Odido telefoonnummer bij je nieuwe simkaart [url=https://kameronmtzf81370.bloggazzo.com/26490118/het-belang-van-tijdelijke-sms-nummers-een-uitgebreide-verkenning]https://kameronmtzf81370.bloggazzo.com/26490118/het-belang-van-tijdelijke-sms-nummers-een-uitgebreide-verkenning[/url]
Изготавливаем столешницы, подоконники, барные стойки и другую мебель из акрилового камня и кварцевого агломерата под заказ по выгодной цене в Москве [url=https://arsenal-info.ru/pub/stati/iskusstvennyy-kamen-dlya-barnyh-stoek-innovacii-estetika-i-praktichnost]Искусственный камень для барных стоек[/url]
Наш дайвинг клуб осуществляет обучение дайвингу от новичка до профессионала. Мы организуем пробные погружения с аквалангом в бассейнах Москвы и открытых водоемах Подмосковья. Кроме этого, в нашем дайв-клубе Вы можете приобрести подарочные сертификат на любой курс дайвинга или пробное погружение [url=http://orendive.ru]дайвинг в москве[/url]
contraindications of prednisone prednisone is for [url=https://medsdoctorfoo.com/]prednisone allergic reaction[/url] why do you have to taper prednisone prednisone doses for adults
Top Pornstars Kayleigh Wanless Tools To Streamline Your Daily Life
Top Pornstars Kayleigh Wanless Trick That Should Be Used By Everyone Be Able To
pornstar
Большой выбор игрушек для взрослых с быстрой курьерской доставкой. Анонимная упаковка – запечатанный крафт пакет [url=https://sexshop25.ru/]https://sexshop25.ru/[/url]
Стоимость обучения на курсе английского для начинающих онлайн в 1,3-2,5 раза ниже стоимости группового обучения на языковых курсах, где ориентируются на группу, а не ваши индивидуальные потребности [url=https://myactiveenglish.ru/]курсы английского языка с сертификатом онлайн[/url]
Привет!
Новости Украины и мира на нашем портале представляют собой обширный информационный ресурс, включающий в себя самые актуальные события и тенденции. Мы следим за всем, что происходит в мире, и стремимся донести до вас информацию о самых важных событиях, которые определяют наше будущее.
Все самое лучшее на сайте https://10minut.info/category/sport/
[url=https://10minut.info/]Новости Украины ТОП[/url]
дтп видео
авто новости
Главные новости Украины
Удачи!
1win mobile <a href=https://1win-telegram.com/>https://1win-telegram.com/</a>
[url=https://loans-online-apply.com/]payday loans approval online[/url]
<a href="https://loans-online-apply.com/">payday loans with bad credit</a>
[url=https://loans-online-apply.com/]small loans for small businesses[/url]
<a href="https://loans-online-apply.com/">advance cash card</a>
Пластическая хирургия — увеличение груди имплантами, подтяжка груди, уменьшение груди. Абдоминопластика — пластика по уменьшению живота, липосакция и липофилинг [url=https://mammosurgery.ru/]абдоминопластика[/url]
медицинская организация терапии и профилактики Москва <a href=http://za-chas.info>медсправка задним числом купить</a> сделать мед справку
Мощные и эффективные: генераторы пены ГПСС для вашего бизнеса. Повысьте уровень безопасности и гигиены с нашими генераторами пены ГПСС [url=https://www.riva-service.com.ua/]запорная арматура[/url]
В этой подборке онлайн-курсов по английскому языку мы сравнили предложения школ по нескольким параметрам и отобрали лучшие варианты для взрослых и детей, начинающих познание языка или повышающих свой уровень [url=https://ilangworld.ru]онлайн курс изучения английского[/url]
prednisone for eczema dosage <a href=https://prednisonera.com/>price for prednisone</a> prednisone for psoriasis
Denver Cleaning Choice is a woman owned local business with more than 20 years experience in commercial cleaning services [url=https://sunshinecleaningsrvc.com]janitorial service denver co[/url]
How To Create An Awesome Instagram Video About Top 10 Pornstars Most popular Pornstars
Входные двери - купить по выгодной цене с доставкой. 1433 модели в проверенных интернет-магазинах: популярные новинки и лидеры продаж [url=https://market-dverey.com/]https://market-dverey.com/[/url]
<a href=https://frugallivin.com/>https://frugallivin.com/</a>
шпунт л5 ум <a href=https://shpuntmaster.ru/>https://shpuntmaster.ru/</a>
наркологическая клиника <a href=https://e-skoraya.kz/>https://e-skoraya.kz/</a>
Nine Things That Your Parent Teach You About Only Fans Pornstars Kayleigh Wanless only Fans Pornstars
реабилитация необходима при зависимостях <a href=https://narcolog1.kz/>https://narcolog1.kz/</a>
של נערות ליווי בתל אביב, באילת ותמונות אמיתיות של דירות דיסקרטיות בתל אביב, בבאר שבע, בירושלים, בחיפה, באשקלון, באשדוד. נוטים לאמץ גישות ליברליות יותר כלפי דירות דיסקרטיות באשדוד, מין ומערכות יחסים, בהשפעת נערות ליווי בתל אביב על ערכים מערביים <a href=http://tupakol.top/>דירה דיסקרטית בחיפה</a>
[url=https://auto.sarbc.ru/articles/2023/12/27/2152.html]https://auto.sarbc.ru/articles/2023/12/27/2152.html[/url]
<a href=https://online-sms.org/id/>temporary phone number sms</a>
Thank you for the good writeup. It in reality was a leisure account it. Look complicated to far delivered agreeable from you! By the way, how could we be in contact?
<a href=https://arusak-attestats.ru />www.arusak-attestats.ru </a>
[url=http://reporter63.ru/content/view/690911/dublikaty-inostrannyh-nomerov-onlajn]http://reporter63.ru/content/view/690911/dublikaty-inostrannyh-nomerov-onlajn[/url]
הבתים הארוטיים, שבהם הלקוחות דירות דיסקרטיות בתל אביב או דירות דיסקרטיות בחיפה מבקשים לפנק את רצונותיהם ללא חשש משיפוט או חשיפה. לרווחים גבוהים בתמורה לעלויות תקורה נמוכות יחסית. בשוק דירות דיסקרטיות באשדוד תחרותי יותר ויותר, במיוחד בתעשיות כמו אירוח <a href=http://gulnara.top/>נערת ליווי בירושלים</a>
Профессиональный Ремонт компьютеров с гарантией, в городе Воркута по низким ценам [url=https://rekom11.ru]ремонт ноутбуков Воркута[/url]
Приглашаем моделей из Санкт-Петербурга для работы в студии с еженедельными выплатами [url=https://www.magnolia-clinic.ru/img/pgs/?kak-slivaiut-vebkam-modelei.html]работа вебкам моделью[/url]
However, necessary note that this monitor is to a certain extent specialized on professional gamers. The game is free, relatively accessible, [url=https://sman8tangsel.sch.id/2021/08/09/vaksinasi-kemerdekaan-sman-8-kota-tangerang-selatan/]https://sman8tangsel.sch.id/2021/08/09/vaksinasi-kemerdekaan-sman-8-kota-tangerang-selatan/[/url] and available by the developers of the most successful esports game all over the world.
Спасибо за объяснение.
Sheetz, Michael (May 9, 2021). "spacex accepts [url=http://ekond.com.ua/index.php/uslugi/obsluzhivanie]http://ekond.com.ua/index.php/uslugi/obsluzhivanie[/url] in the role of payment for launching the DOGE-1 mission to the Moon in next planting season."
А ты такой горячий
after the presale ends, [url=https://arrabidalegend.pt/hello-world/]https://arrabidalegend.pt/hello-world/[/url] will receive their purchased tokens via airdrops. however, since the crypto world is very volatile, invest only insofar as you can afford to lose.
https://gtk-auto.ru
Привет всем!
Внимание, жители Кропивницкого! На нашем сайте вы найдете самые свежие и актуальные новости города. Узнайте о последних событиях, важных решениях и общественных инициативах. Мы всегда на страже информации для вас!
Все самое лучшее на сайте https://bomba.kr.ua/news-ukraine/
[url=https://bomba.kr.ua/]Главные новости Украины[/url]
Новости Кропивницкого сегодня
Главные новости Украины
новости Украины видео
Удачи!
<a href=https://zamkiexpress.ru/>https://zamkiexpress.ru/</a>
Проведите день в атмосфере старины с нашими экскурсиями по малым средневековым городам, где каждая улочка пронизана историческими событиями и легендами. От Гвидо до Галингена - наши цены делают это путешествие доступным для всех желающих. <a href=https://mykaliningradgid.ru/>https://mykaliningradgid.ru/</a>
Что бы выяснить более точно сколько стоит пластиковое окно мы рекомендуем воспользоваться бесплатной услугой вызова замерщика. Привезём образцы. Сделаем расчёт в 3-х вариантах [url=https://prihoz.ru/articles/full/dom_uchastok/Kak-samostoyatelno-otremontirovat-plastikovoe-okno/]https://prihoz.ru/articles/full/dom_uchastok/Kak-samostoyatelno-otremontirovat-plastikovoe-okno/[/url]
this section discusses popular topics about participating in the dogeverse presale, acquiring cryptocurrency, the [url=https://chameau.net/bbs/board.php?bo_table=free&wr_id=666786]https://chameau.net/bbs/board.php?bo_table=free&wr_id=666786[/url] dogeverse website and understanding its distinctive features, and also bordering dangers and benefits.
Among these, certain icons stand out for their ubiquitous presence and importance in our daily digital interactions. This article delves into a variety of such icons, including the email, safari (web browser), location, discord, settings, Christmas, messages, spotify, person, and home icons, exploring their significance and evolution [url=https://titusygnsx.blogtov.com/6736806/the-smart-trick-of-safari-icon-that-nobody-is-discussing]safari icon[/url]
прикольный! хоть и на раз посмотреть!
also, investors are able take percentage for placing shares in spongev2 tokens with a variable interest rate, installed for 4 years, [url=https://iventmonitor.net/799-smartprocess.html]https://iventmonitor.net/799-smartprocess.html[/url] in the current realities are about 189%. therefore investors who supply more v1 tokens will receive more v2 tokens in return.
<a href=https://allnewstoday365.com/>allnewstoday365.com</a>
You'll Never Be Able To Figure Out This Top Pornstar Only Fans's Tricks top Pornstar only fans
Топ 10 лучших онлайн-казино, которые заняли первые места в рейтинге игр на наличные деньги, доверия и других значимых критериев 2024 [url=https://casinor.ru]топ казино[/url]
Телесериал «911 служба спасения» про доблестных и храбрых спасателей, служба которых тяжелая и несет опасность с каждым вызовом. Герои службы 911 все смелые и храбрые в каждой серии сериала спасают жизни людям. Все персонажи сериала разные по характеру, но это не мешает им дружить и работать слаженной командой [url=https://dettka.com/serial-pro-spasatelej-911-osnovnoj-syuzhet/]Здесь[/url]
Бронирование билетов на автобус Дебальцево - Ростов онлайн без предоплат. Актуальное расписание и цены на рейсы [url=https://autobus-dn.ru/route/makeevka-moskva/]билеты макеевка москва[/url]
Простыми словами о том, что нужно знать прежде, чем заказать свидание на крыше [url=https://dzen.ru/a/ZkTk5y78k0rIj2UT]https://dzen.ru/a/ZkTk5y78k0rIj2UT[/url]
will prednisone cause high blood pressure [url=https://prednisonera.com/]prednisone medicine[/url] dogs and prednisone
<a href=https://myapplegarage.ru/>сервис apple рядом</a>
В эпоху цифровых технологий, когда виртуальная реальность становится все более неотъемлемой частью нашей повседневной жизни, мир развлечений и азарта находит свое отражение в многочисленных онлайн площадках, предлагающих азартные игры и возможность погрузиться в атмосферу адреналина и выигрышей [url=http://zrr269.org.ru/index.php?option=com_k2&view=itemlist&task=user&id=652920]http://zrr269.org.ru/index.php?option=com_k2&view=itemlist&task=user&id=652920[/url]
You'll Never Guess This Pornstar Kayleigh's Tricks Pornstar Kayleigh
What's The Current Job Market For Top Pornstar Only
Fans Professionals? only Fans
Личный тренер, групповые занятия, безлимитный доступ, тренажерный зал, шкафчик в раздевалке! Оплата только за месяц [url=http://ufit-nahim.ru/]беляева фитнес центр[/url]
Кроме привычного фитнеса, мы устраиваем челленджи и соревнования среди сети, проводим открытые тренировки в центре и устраиваем сайкл-забеги в торговых центрах [url=https://wikidp.wikibase.cloud/wiki/Ufit-nahim.ru]фитнес клуб киевская москва[/url]
Moderator!
Ищете платформу, которая ставит вашу безопасность на первое место? Mega - это решение! Благодаря передовым функциям безопасности и удобному интерфейсу <a href=https://xn--megab-mdb.com>mega</a> гарантирует конфиденциальность ваших данных. Пройдите легкую процедуру регистрации и изучите широкий выбор категорий. Присоединяйтесь к <a href=https://xn--megab-mdb.com>mega dark</a> прямо сейчас и делайте покупки с уверенностью.
мега даркнет ссылки:https://xn--megab-mdb.com
Создайте свою фотоисторию. Стильные фотокниги в два клика! Сделаем за 3 дня [url=http://urbino.fh-joanneum.at/trials/index.php/Photo-leto.ru]фотокниги премиум[/url]
выкуп машин в москве <a href=https://avtovikupmashin21.ru/>https://avtovikupmashin21.ru/</a>
<a href=https://casinor.ru/>топ казино</a>
1Вин абсолютно не идеальное казино, да и как бк тоже имеет недостатки. Тем не менее, я остаюсь в казино и продолжаю играть. Трудности меня закалили, позволили приспособиться [url=https://1winbets24.ru]1вин зеркало[/url]
игрок не поверите, но получится обезопасить свой смартфон от данной ужасной муки, как написание диплома, если просто его приобрести или - купить, [url=http://arbitrajniki.ru/forums/topic/kachestvennoe-obrazovanie/]http://arbitrajniki.ru/forums/topic/kachestvennoe-obrazovanie/[/url] как хозяину захочется.
How Best Accident Attorneys Near Me Became The Hottest Trend Of 2023 accident Attorney Austin
Секреты оформления пропуска на МКАД, что нужно знать, Ключевые моменты о пропуске на МКАД, Пропуск на МКАД: какие документы нужны, Основные вопросы о пропуске на МКАД, на которые нужно знать ответы, Эффективные способы получения пропуска для МКАД, инструкции, Инструкция по продлению пропуска на МКАД, подробная информация
Пропуск на мкад [url=https://gargopermits.com/]Пропуск в москву[/url] .
^ Gabriel Cricket (11 de agosto de 2017). "O 888live festival pousara em Sao Paulo, prometendo grande celebracao e [url=http://kugatsu.flop.jp/9cgi/9kansoubbs2013/9nmaruchan.cgi?]http://kugatsu.flop.jp/9cgi/9kansoubbs2013/9nmaruchan.cgi?[/url] muitos navios; verifique isso".
<a href=https://1winbkzerkalo.ru/>1win</a>
Один из лучших буков. Даже наши “легальные” конторы бывают не выплачивают деньги и специально урезают лимиты. 1вин не страдает этой херней, всегда четко выводит, говорю лично про себя! Надеюсь так и будет дальше [url=https://1winbkzerkalo.ru]1win зеркало[/url]
a resposta e sim. Para simplificar, considere "jogadores experientes " aqueles que ja sabem jogar corretamente cartas, [url=https://soundbusinessnetwork.com/hello-world/]https://soundbusinessnetwork.com/hello-world/[/url] eles jogaram milhares de maos de poker e nao temer ganhar jogando poker online com buy-in de €80/70/60/50/40% e mais.
Осуществляем уборку квартир, домов, офисов, уборку после ремонта, генеральную и поддерживающую, а также мытье окон [url=https://smolevichi-minsk.by/]оказание услуг по уборке[/url]
Thanks to 1xbet's companion relationships with football clubs and leagues, [url=http://allsochi.info/main/ap/melbet_promokod_pri_registracii_bonus_besplatno.html]http://allsochi.info/main/ap/melbet_promokod_pri_registracii_bonus_besplatno.html[/url] it is able to offer our partners unequal methods for cooperation with famous athletes.
Outras promocoes do 888poker incluem premios em queda, Rakeback em apostas de torneios e premios da mao do dia, [url=https://elchingon.es/post-4/]https://elchingon.es/post-4/[/url] varias tabelas Leaderboard e muito mais.
Сдаём квадроциклы в аренду от 1 часа и организуем маршруты на любой вкус. Катаем на новой технике. Забронировать поездку [url=https://smartseller7.com/atvbizon-ru/]где покататься на квадроциклах[/url]
demand betting on sports and exciting is growing in country, therefore [url=https://gamma.app/docs/1xBet-Promo-Code-India---Welcome-Bonus-42900-sjrw574xrj3ipcl?mode=doc]https://gamma.app/docs/1xBet-Promo-Code-India---Welcome-Bonus-42900-sjrw574xrj3ipcl?mode=doc[/url] plans to expand its availability.
Подарочный сертификат на аренду квадроциклов станет незабываемым подарком для любителей активного отдыха [url=https://northerngraceyouthcamp.org/wiki/index.php/User:CaitlinCyril1]кататься на квадроциклах в москве цены[/url]
Resumidamente, [url=https://dafyddpbradley.com/2021/07/19/first-time-test/]https://dafyddpbradley.com/2021/07/19/first-time-test/[/url] essas transacoes sao legalizadas e COMPRADOR nao Vale pensar sobre o assunto se seu dinheiro em nosso site e seguro.
Вы можете взять в аренду квадроцикл и насладиться преодолением бездорожья. Всё просто - выберете продолжительность тура [url=http://ek-x.ru/]кататься на квадроциклах в подмосковье[/url]
how does doxycycline work for acne doxycycline hyclate vs doxycycline monohydrate [url=https://himsmedhealthh.com/]doxycycline hyclate 100mg price[/url] doxycycline for dogs side effects side effects of taking metronidazole and doxycycline together
O 888poker usa uma sofisticada tecnologia de criptografia que garante transmitir com seguranca seu Dados [url=https://bbarlock.com/index.php/888_Poker:_Poker_Dinheiro_Real]https://bbarlock.com/index.php/888_Poker:_Poker_Dinheiro_Real[/url] internet.
^ Andrew Radu (15 de dezembro de 2012).). Melhor Operador Digital, [url=https://greenmarblecycletours.com/10-off-east-west-guided-tour/]https://greenmarblecycletours.com/10-off-east-west-guided-tour/[/url] global gaming awards".
Genero e sugerido para que pessoas possam escolher se querem jogar com um personagem masculino [url=https://japannext.net/portfolio/merchant/]https://japannext.net/portfolio/merchant/[/url] ou feminino.
Привет!
Новости Винницы: актуальная информация о событиях дня, культурных мероприятиях и городских инициативах. Следите за жизнью вашего города вместе с нами.
Все самое лучшее на сайте https://bomba.vn.ua/category/novini-vinnitsi/
[url=https://bomba.vn.ua/]Новости Винницы ДТП[/url]
Новости Винницы видео
последние новости Винницы
последние новости Украины
Удачи!
novo O aplicativo moderno 888, disponivel para dispositivos moveis Android e iOS, apresenta moderno visual e orientacao vertical, [url=https://khongquantam.com/facebook-khong-cho-xoa-status-nut-delete-bong-nhien-tro-lai-la-co-hay-chi-la-tin-don]https://khongquantam.com/facebook-khong-cho-xoa-status-nut-delete-bong-nhien-tro-lai-la-co-hay-chi-la-tin-don[/url] que faz seu significativamente mais facil jogar usando apenas uma mao.
Нада добавить еще пункт
Зберігання. Аптечки таять в опалювальних приміщеннях на відстані не менше одного метра від джерел тепла при температурі від плюс одиниці до [url=https://www.kinofilms.ua/forum/t/5136423/]https://www.kinofilms.ua/forum/t/5136423/[/url] 20 ° С.
50, [url=https://vdh-fuerth.de/hello-world/]https://vdh-fuerth.de/hello-world/[/url] e conectando Varios niveis entre dados dois extremos. Escolha "Copiar e colar" para colar o codigo no aplicativo bancario; confirme o pagamento.
Why You Should Concentrate On The Improvement Of Porn Star british porn stars on adultwork (http://www.stes.tyc.Edu.tw/)
* Modifique estado original usando avatares e Outros parametros personalizaveis. * Experimente a nossa incrivel variedade [url=https://www.caselvaticanuoto.it/2022/02/11/ca-selvativa-parte-il-nuovo-corso-di-acqua-yoga/]https://www.caselvaticanuoto.it/2022/02/11/ca-selvativa-parte-il-nuovo-corso-di-acqua-yoga/[/url] casino, entretenimento.
Букмекерская контора 1win отзывы клиентов, Отзывы о Букмекерская контора 1win. На сайте отвечает официальный представитель Букмекерская контора 1win [url=https://1win-aviator.ru]1win зеркало[/url]
Este boton normalmente se encuentra superior pagina principal [url=https://www.selfhackathon.com/preparado-para-mejorar-tu-juego/]https://www.selfhackathon.com/preparado-para-mejorar-tu-juego/[/url].
Доброго!
Последние новости из Украины и всего мира: следите за самыми актуальными событиями и читайте глубокие аналитические материалы на нашем сайте.
Все самое лучшее на сайте https://omind.com.ua/category/sport/
[url=https://omind.com.ua/category/tech/]Новости технологий[/url]
новости Украины сегодня
Главные новости Украины
новости экономики
Удачи!
en el mundo [url=http://missworldkorea.com/new/bbs/board.php?bo_table=free&wr_id=215629]http://missworldkorea.com/new/bbs/board.php?bo_table=free&wr_id=215629[/url]. mas alla de la emocion del juego, la diversion o la oportunidad de desarrollarlo como un oficio, hay lecciones profundas que se puede aprender y usar en vida cotidiana.
В фитнес-клубах есть вело- и кардиотренажеры, силовое оборудование, эллипсы, беговые дорожки. Самых популярных тренажеров в зале несколько экземпляров, чтобы всегда были свободные [url=http://sport-podolsk.ru/]йога в беляево тренеры[/url]
Допускається зміна зазначених розмірів виходячи з серії і укомплектуванні. [url=http://www.fishing.vn.ua/forum/viewtopic.php?t=6418]http://www.fishing.vn.ua/forum/viewtopic.php?t=6418[/url] авіаційна-це набір виробів медичного намірів і препаратів, призначається для своєчасного надання першої домедичної само - і взаємодопомоги на борту пасажирського|вантажного повітряного судна.
hemos intentado verificar la validez de la licencia [url=https://www.musicforbodyandspirit.com/reiki-music-energy-healing-nature-sounds-zen-meditation-2/]https://www.musicforbodyandspirit.com/reiki-music-energy-healing-nature-sounds-zen-meditation-2/[/url], pero nosotros tal no crecio.
si persona de mis jugadores quiere continuar asociacion con el establo y decide irse, [url=http://www.moneytipsasset.com/bbs/board.php?bo_table=free&wr_id=732090]http://www.moneytipsasset.com/bbs/board.php?bo_table=free&wr_id=732090[/url] revisara las restricciones en el sentido de la misma.
Премиальный фитнес-клуб: бассейн, залы групповых программ, SPA, кафе. Оборудование в тренажерном зале топовых фирм [url=https://swimsever.ru/]зумба войковская[/url]
Привет!
Археологические находки в Одессе проливают свет на богатую историю города. Читайте о последних открытиях и их значении для исторического наследия.
Все самое лучшее на сайте https://bomba.od.ua/category/novini-odesi/
[url=https://bomba.od.ua/category/novini-ukraini/]Главные новости Украины[/url]
Новости Одессы аварии
Новости Одессы
Главные новости Одессы
Удачи!
de todos juegos en [url=https://www.dinoautoricambi.it/car-exhaust-1902909_1920/]https://www.dinoautoricambi.it/car-exhaust-1902909_1920/[/url] poker texas hold'em - muy demanda variante de de poker en el mundo.
en los ultimos anos actividad. el diseno auge en el sector no profesional donde se practica [url=http://tera0720.iptime.org/gn5/bbs/board.php?bo_table=free&wr_id=288674]http://tera0720.iptime.org/gn5/bbs/board.php?bo_table=free&wr_id=288674[/url]. por lo tanto, personas/ ciudadanos se reunen en casa junto con sus amigos para jugar este juego de cartas.
<a href="https://mfc-sosnovskoe.ru">Казино с пополнением с Qiwi
prednisone and autoimmune disease <a href=https://prednisonera.com/>prednisone without a doctor prescription</a> prednisone and sunlight
Привет!
Образовательные реформы в Хмельницком: Школы и университеты города внедряют новые методики и программы, направленные на повышение качества образования. Узнайте, какие изменения ждут студентов и преподавателей.
Все самое лучшее на сайте https://bomba.km.ua/category/novini-khmelnickogo/
[url=https://bomba.km.ua/category/novini-ukraini/]Новости Украины лента[/url]
Новости Украины лента
Новости Хмельницкого фото
Главные новости Хмельницкого
Удачи!
<a href=https://1windeposit.ru/>1вин зеркало</a>
Классс... конь в противогазеееееееееееее
Убит по решению «боссов» как потенциально опасный свидетель: не-итальянец, [url=https://real-money-casino-au.com/]real money casinogenesis casino[/url] он мог начать давать показания. Использует её, затем бросает.
Я конечно, прошу прощения, но не могли бы Вы дать больше информации.
na area de registro mesmo , [url=https://kmural.ru/news_importer/inc/1xbet_promokod_bonus_pri_registracii.html]https://kmural.ru/news_importer/inc/1xbet_promokod_bonus_pri_registracii.html[/url] im um opcao: digite o codigo de bonus.
Крупнейший интернет магазин для взрослых. Более 40.000 товаров для взрослых в наличии! Работаем с 2008 года [url=https://24sexy-dolls.ru/]купить куклу в секс шопе[/url]
якомога швидше нададуть медичну допомогу фахівці медичного супроводу соціальних заходів та корпоративних свят, [url=https://www.azyatrends.com/product/two-toned-printed-floral-kurti/]https://www.azyatrends.com/product/two-toned-printed-floral-kurti/[/url] і не маючи на те потреби - здійснять моніторинг будь-яких життєвих показників потерпілого і оперативну транспортування в амбулаторію.
Виртуальный номер для регистрации — это уникальный номер телефона, который используется для подтверждения личности при регистрации на сайте, приложении или сервисе [url=https://mobile-1s.ru/the_articles/virtualnyy-nomer-telefona-bezopasnost-i-kdobstvo-v-odnom.html]https://mobile-1s.ru/the_articles/virtualnyy-nomer-telefona-bezopasnost-i-kdobstvo-v-odnom.html[/url]
Esports: during innovations esports became ideal entertainment, and in [url=https://noordijksite.nl/plankenkoorts/hallo-wereld/]https://noordijksite.nl/plankenkoorts/hallo-wereld/[/url] it became an extravaganza bids.
Доброго!
Культурные события Украины: Афиша самых ярких и интересных культурных мероприятий, которые пройдут в разных уголках страны в ближайшее время.
Все самое лучшее на сайте https://beta.in.ua/
[url=https://beta.in.ua/avto/]Новости авто[/url]
новости Украины
политика в Украине
новости Украины сегодня
Удачи!
Strands, the New York Times Games team's latest innovation, offers a fresh twist on classic word search puzzles, captivating word game enthusiasts and puzzle solvers alike [url=https://strandsgame.net/]strands game[/url]
Внимание аграрии и фермеры! У вас есть земельный участок или сельскохозяйственное предприятие, и вам нужен надежный и мощный трактор для обработки почвы и выполнения других сельскохозяйственных работ? Тогда вы попали по адресу! https://kronos5.ru
Я думаю, что Вы допускаете ошибку. Пишите мне в PM, поговорим.
assim, [url=https://www.publy.ru/pag/promokod-1xbet_na_segodnya.html]https://www.publy.ru/pag/promokod-1xbet_na_segodnya.html[/url] nos entendemos, o que e retirada e deposito sao limitados apenas por esses dois formatos.
Клининг квартир после трупов <a href=https://prof-uborka-posle-smerti.ru/>https://prof-uborka-posle-smerti.ru/</a>
If only spermatozoa are produced, then the reproductive gland is the testicle, and the main [url=https://bigtimestore.xyz/members/chimetea78/activity/195044/]orgasm.red[/url] of textile and the individual possessing it male.
The Memorial Day parade in Georgetown and Jenison begins at 9 a.m. [url=https://thefitnessblogger.com/what-is-bbl-in-bodybuilding/]https://thefitnessblogger.com/what-is-bbl-in-bodybuilding/[/url] Cascade Township is scheduled for ten in the morning.
Металлопрокат по выгодным ценам. Заказывайте онлайн. Быстрая доставка · Цены снижены. Легкий обмен и возврат [url=http://metal-lesnoy.ru/]металлобаза прайс лист[/url]
Наша компания предоставляет кредиты и займы в короткий срок, помогая клиентам решать финансовые вопросы быстро и без лишних хлопот, узнайте подробнее тут - <a href=https://www.volgograddaily.ru/press.php?id=3400>https://www.volgograddaily.ru/press.php?id=3400</a>. Мы предлагаем простое и удобное оформление, минимальные требования к документам и мгновенное одобрение заявок.
Рассказы и эротические истории, размещённые в нашей эро библиотеке, удовлетворят любой, даже самый изысканный вкус благодаря множеству пересекающихся между собой жанров [url=https://eroticguru.ru/]здесь[/url]
Это теплое воспоминание из прошлого навсегда оставило в нас только добрые [url=https://radiodonor.ru/]radiodonor.ru[/url] воспоминания.
See What UK Pornstar Tricks The Celebs Are Using uk pornstar
Для удобства покупателей наша компания осуществляет оперативную доставку строительной арматуры собственным автотранспортом [url=https://a4-tech.ru/]купить арматуру[/url]
Ten Startups That Are Set To Change The Prettiest Pornstars Industry For The
Better cutest Pornstars
Розыск людей в СПб и ЛО. <a href=http://detektivnoe-agenstvo.ru/>http://detektivnoe-agenstvo.ru/</a>
Купить участок в Московской области напрямую от собственника. Расположение 44 км от МКАД. Земельные участки в окружении лесного массива, тихое и уютное место для загородной жизни и отдыха [url=https://nikolino-rublevka.ru/]продажа земельных участков московская область[/url]
Казань – один из самых красивых и исторически богатых городов России, привлекающий множество туристов и деловых путешественников. Если вы хотите выбрать 1 из популярных гостиниц в Казани, которые обеспечат комфортный и приятный отдых, заходите на новый сайт сервиса - OteliKazan.ru - это надежный агрегатор гостиниц и отелей в Казани, который поможет найти лучшее предложение на ваши даты https://otelikazan.ru/
Внимание аграрии и фермеры! У вас есть земельный участок или сельскохозяйственное предприятие, и вам нужен надежный и мощный трактор для обработки почвы и выполнения других сельскохозяйственных работ? Тогда вы попали по адресу! https://kronos5.ru
лечение алкоголизма на дому <a href=https://detoxme.kz/>https://detoxme.kz/</a>
Top 15 Midmod Boho Living Room Design Ideas That Merge Modernism and Free Spirit - DreamyHomeStyle. Boho Chic. Arredamento Boho Chic [url=https://stok-stolnik.ru/2024/04/21/boho-chic-navigating-balis-interior-design-trends]local interior designers[/url]
Explore the intricate tapestry of biblical history with our expansive compilation featuring over 1000 meticulously curated Bible Maps and Images [url=https://www.hotel-details.com/hotels/caruso-ravello]https://www.hotel-details.com/hotels/caruso-ravello[/url]
Погрузитесь в мир, где каждый клик – это шанс, каждый оборот – это возможность, а каждая ставка – это судьба [url=http://j013.koreawebcenter.com/bbs/board.php?bo_table=free&wr_id=656516]http://j013.koreawebcenter.com/bbs/board.php?bo_table=free&wr_id=656516[/url]
Грузовые боксы на крышу автомобиля — самое вместительное из наших решений для перевозки грузов. Ведёте активный образ жизни или собираетесь в отпуск? Широкий ассортимент боксов на крышу от Thule удовлетворит любые Ваши потребности [url=https://bagazhniki.pro/]багажник на крышу автомобиля автобокс[/url]
Мы придерживаемся разумной ценовой политики и предлагаем качественные материалы на выгодных условиях. В каталоге представлен сертифицированный ламинат, соответствующий нормам и стандартам. Скидки на ламинат с гарантией [url=https://kvarcvinil5.ru/]Цена на ламинат в Москве.[/url]
Внимание аграрии и фермеры! У вас есть земельный участок или сельскохозяйственное предприятие, и вам нужен надежный и мощный трактор для обработки почвы и выполнения других сельскохозяйственных работ? Тогда вы попали по адресу! https://kronos5.ru
stromectol amazon canada what is stromectol 3 mg used for [url=https://nwvipphysicians.com/]ivermectin injection for cattle[/url] stromectol walmart canada how to get ivermectin
не надо скачивать сторонний софт или занимать память девайса. Сортировать игры удается по спросу, [url=http://huaweiclub.ru/2019/07/17/40121/]вавада vavadaa online[/url] дате выхода или провайдеру.
A Step-By-Step Instruction For British Porn Stars Xxx british Pornstar
второй разновидность – это ордер на binance, где покупатель имеет возможность подобрать из перечня продавцов или покупателей gecrypto, и оставить заказ, [url=http://metropaintstvm.com/hello-world/]http://metropaintstvm.com/hello-world/[/url] где гарантом сделки выступает binance.
Casino [url=https://translate.google.com/translate?u=https://www.autobazar.eu/images/pages/?888starz_promo_code_for_registration.html]https://translate.google.com/translate?u=https://www.autobazar.eu/images/pages/?888starz_promo_code_for_registration.html[/url] ha convertido su bandera en asegurar que sus clientes reciban un apoyo y ayuda si lo necesiten.
<a href=https://lordseriall.bar/zarubezhnye-serialy/>зарубежные сериалы смотреть онлайн бесплатно</a>
Плавный ход автобусов позволяет гарантировать спокойную и безопасную поездку с детьми. Малыши легко переносят поездку, а родители чувствуют себя максимально комфортно [url=https://autobus-dn.ru/route/ilovajsk-moskva/]автобус иловайск москва[/url]
12 Facts About Tiktokpornstar To Make You Seek Out Other People Tiktok pornstar
Прежде чем погрузиться в мир развлечений, важно учитывать несколько ключевых факторов при выборе площадки. Надежность, разнообразие игр, качество обслуживания и бонусные программы играют значительную роль [url=http://verkehrsknoten.de/index.php/forum/sonstige-themen/85188#86145]http://verkehrsknoten.de/index.php/forum/sonstige-themen/85188#86145[/url]
Искушение и азарт всегда были неотъемлемой частью человеческой природы. В современном мире существует множество мест, где каждый желающий может испытать удачу и получить дозу адреналина [url=http://verywellsys.com/bbs/board.php?bo_table=service&wr_id=255038]http://verywellsys.com/bbs/board.php?bo_table=service&wr_id=255038[/url]
<a href=https://leon-prilozhenie-android.ru/>приложение бк леон</a>
в том случае, когда после любого из раундов ставок остается всего один участник (таким образом все другие сделали фолд), [url=http://missiones.cl/inauguran-primera-planta-desalinizadora-que-funciona-con-energia-solar-en-isla-de-pascua/]http://missiones.cl/inauguran-primera-planta-desalinizadora-que-funciona-con-energia-solar-en-isla-de-pascua/[/url] то он и забирает отделение банка и не обязан показывать карты.
они без труда же пройдут за финальный стол. а в третью ночь - один тол лузеров [url=http://goldenhill.kr/board/bbs/board.php?bo_table=free&wr_id=2386]http://goldenhill.kr/board/bbs/board.php?bo_table=free&wr_id=2386[/url] и финальный стол.
Вводи актуальные коды, купоны и промокоды Все Инструменты.ру за июнь 2024 года в специальное поле на сайте и не переплачивай за онлайн-шопинг [url=https://vireg.ru]всеинструменты промокод на скидку[/url]
you are truly a good webmaster. The web site loading velocity is incredible. It seems that you're doing any unique trick. Also, The contents are masterwork. you've performed a wonderful job in this matter!
https://alkogolizma.com/napitki/vino-iz-klubniki.html
http://www.kvartal74.ru/
https://americanautotitleloan.com/
https://strmama.ru/actions
http://o-kreditah1.ru/konspekt-lekczij-po-kreditam/216-kreditnaya-sistema-ponyatie-xarakteristika-ee-zvenev.html
в процессе игры гемблер сумеет совершить только 1 действие в [url=https://kambeitzfarms.com/2018/03/15/wordpress-resources-at-siteground/]https://kambeitzfarms.com/2018/03/15/wordpress-resources-at-siteground/[/url] свой ход.
You're About To Expand Your Pornstar Options British porn Star
однако в подобной категории не так много акций, [url=http://www.aotingmei.com/bbs/board.php?bo_table=free&wr_id=284031]http://www.aotingmei.com/bbs/board.php?bo_table=free&wr_id=284031[/url] как в покере legion.
Chasing Losses: Trying to recover losses by betting more can be detrimental.
<a href="https://aviatorgamedemoplay.com/">aviator app</a>
если не достает никакого звука, и любой хотите, чтобы мы нашли искомое для постоянных посетителей, то напишите, пожалуйста, [url=https://mobrington.ru/]https://mobrington.ru/[/url] сообщение администратору сайта.
Вольную экранизацию одноименного романа Достоевского поставил Руперт Уайатт, [url=https://ewv-muenchen.de/?attachment_id=269]https://ewv-muenchen.de/?attachment_id=269[/url] известный по триллеру «Побег из тюрьмы» и фантастическому боевику «Восстание планеты обезьян».
Крэйг послужит важным лучших Бондов, [url=https://mygiftplanner.com/uncategorized/hello-world/]https://mygiftplanner.com/uncategorized/hello-world/[/url] однако с образом агента 007 британский актер попрощался в 2021 году - в секретном боевике «Не время умирать».
<a href=https://vulkan-na-dengy.com/>вавада отзывы игроков</a>
сегодня онлайн-покеррумы обеспечивают подобный обширный перечень различных кэш-спортивных событий и турниров, что играющий, обладающий повышенным уровнем скилла, [url=http://hosmeal.com/bbs/board.php?bo_table=free&wr_id=45338]http://hosmeal.com/bbs/board.php?bo_table=free&wr_id=45338[/url] неизбежно сталкивается с необходимостью выбора.
<a href=https://cleanprofispb.ru/>мытье окон в квартире</a>
<a href=https://primexdon.ru/>https://primexdon.ru/</a>
одним из мест работы Молли стал ночной клуб the viper room. и если вы найдете способ предоставить им почувствовать, что про них заботятся, их видят, слышат, помнят, [url=https://openerp.vn/bay-yeu-to-tao-nen-mot-du-an-erp-thanh-cong/]https://openerp.vn/bay-yeu-to-tao-nen-mot-du-an-erp-thanh-cong/[/url] - это возможно для всех.
You'll Never Guess This Top British Pornstars's Tricks top British pornstars
мне парочку
Здесь невозможна [url=https://1win-ru-bet.ru/]1вин букмекерская контора[/url] ситуация утечки данных. 2. Выделяй на браузерные игровые программы в казино определённый бюджет и старайся не превысить его.
всем клиентам за партой раздается по две карты, которые по праву считаются их личными, [url=http://www.gochix.net/dabun/view.cgi?d=1132322699]http://www.gochix.net/dabun/view.cgi?d=1132322699[/url] соперники эти средства не находят. Управляющей компанией становится teshi limited, покер-рум работает через лицензию Кюрасао.
в сочетании нет Шестерки, ввиду того что иначе будет Стрит. Количество покеристов так выросло, [url=http://jiyujoho.a.la9.jp/cgi-bin/fr/bbs/jawanote.cgi]http://jiyujoho.a.la9.jp/cgi-bin/fr/bbs/jawanote.cgi[/url] что победитель wsop 2006 получил целых $12,000,000 за счет солидного числа участников турнира.
<a href=https://www.bloomberg.com/news/articles/2018-03-12/who-s-in-charge-of-the-augmented-city>https://www.bloomberg.com/news/articles/2018-03-12/who-s-in-charge-of-the-augmented-city</a>
Браво, какая фраза..., отличная мысль
Ріелторська компанія knight frank повідомляє, що протягом першого кварталу 2023 року іноземці придбали близько 3 496 ліній в районі Малага, [url=https://informator.ua/ru/kak-izmenilsya-rynok-nedvizhimosti-kieva-za-17-mesyacev-voyny]Как изменился рынок недвижимости Киева за 17 месяцев войны[/url] що на сьогоднішній день на 18% вишка з новим кварталом 2019 року.
Сделаем разводку труб водопровода и канализации. Пайка полипропилена. Установим стиральные, подключим посудомоечные машины [url=https://pyatigorsk.san-techniks.ru]https://pyatigorsk.san-techniks.ru[/url]. Приедем в удобное время! Берем срочные работы. Даем чек и гарантию!
Отсеивание участников со слабыми комбинациями. Флоп или выкладка на борт трех общих карт - это следующая кульминация [url=https://saokoradioquilla.com/noticias/joe-barranquilla-nunca-te-olvida-este-miercoles-26-al-conmemorarse-los-12-anos-de-su-partida/]https://saokoradioquilla.com/noticias/joe-barranquilla-nunca-te-olvida-este-miercoles-26-al-conmemorarse-los-12-anos-de-su-partida/[/url] в покере.
Effective Strategies for Beginners <a href="https://www.yeuthucung.com/threads/opportunity-to-test-new-tactics.456135/">aviator demo game play</a>
«Эффект Манимейкера» был очевиден, но мужчина, который помог сделать задуманное, [url=https://www.siweul.net/commemoration-du-bicentenaire-de-la-naissance-de-serigne-maka-birama-khaly/]https://www.siweul.net/commemoration-du-bicentenaire-de-la-naissance-de-serigne-maka-birama-khaly/[/url] держался в нежарком секторе.
[url=https://guard-car.ru/]https://guard-car.ru/[/url]
Hmm is anyone else experiencing problems with the images on this blog loading? I'm trying to find out if its a problem on my end or if it's the blog. Any feedback would be greatly appreciated.
https://suvorov-castom.ru/svetodiodnaya-podsvetka-avtomobilya/
https://mahonycodes.click/
https://nogivnorme.ru/2019/10/16/%D0%B4%D0%B8%D0%B5%D1%82%D0%B0-%D0%B1%D0%B0%D0%B1%D0%BE%D1%87%D0%BA%D0%B0/
http://maxima.2ua.in.ua/viewtopic.php?f=3&t=5047
https://merezhkovski.ru/proizved/bes.php
<a href=https://uborkadoma-spb.ru/>https://uborkadoma-spb.ru/</a>
<a href=https://www.instagram.com/asiapsiholog_family/>https://www.instagram.com/asiapsiholog_family/</a>
они создают и безвозмездные аппараты, [url=https://www.itray.co.kr/bbs/board.php?bo_table=free&wr_id=2706792]https://www.itray.co.kr/bbs/board.php?bo_table=free&wr_id=2706792[/url] и со ставками на реальные финансы. Безлимитные - можно строить любые беты. Затем соперники получают карманные карты, принимают участие в кругах торговли.
Организатор игр на деньги должен отвечать ряду параметрам: производитель с внесением в реестр россии, и уставным фондом от 34 млн гривен, сайт на городском домене, разрешения на оборудование и т. д. к ставкам допускаются лица возрастом от 21 года, [url=https://www.duflla.org/ibrahim-krosi/ibrahim-krosi/]https://www.duflla.org/ibrahim-krosi/ibrahim-krosi/[/url] прошедшие верификацию документов.
Речь об электронном устройстве, состоящем из искусственного фаллоса и механизма, имитирующего фрикционные движения [url=https://udovolstvie18.ru/]https://udovolstvie18.ru/[/url]. Настраивая агрегат под свои потребности, женщина получает качественный долгий секс в любой желаемой позе.
Я извиняюсь, но, по-моему, Вы не правы. Пишите мне в PM, обсудим.
for everyone you can share your ideas, leave a review at a [url=https://makeupandbodycare.bravesites.com/entries/general/wwwalyakacom]https://makeupandbodycare.bravesites.com/entries/general/wwwalyakacom[/url] and take part in discussion about.
Сначала зрители буду наблюдать за борьбой на главном столе, [url=http://www.seumfood.com/bbs/board.php?bo_table=free&wr_id=1557604]http://www.seumfood.com/bbs/board.php?bo_table=free&wr_id=1557604[/url] затем на следующем и затем на третьем.
<a href=https://earl-clean.ru/>https://earl-clean.ru/</a>
<a href=https://zerkalovavada.site/>https://zerkalovavada.site/</a>
В мире онлайн-развлечений и игр активность игроков нередко ограничивается доступом к платформам, подверженным блокировкам и ограничениям [url=http://water.vouvstudio.com/bbs/board.php?bo_table=free&wr_id=2824813]http://water.vouvstudio.com/bbs/board.php?bo_table=free&wr_id=2824813[/url] В таких ситуациях важно иметь альтернативные способы доступа к желаемым услугам и контенту.
однако когда операция является дебютной для заказчика, к тому же в значительном объеме, администрация произведет тщательную тестирование платежа, [url=https://1winbetslots.ru/]1winbetslots.ru[/url] первое стремясь можно просчитать безопасность средств клиента.
Одним из ключевых факторов является удобство интерфейса. Платформы разработаны таким образом, чтобы пользователям было легко ориентироваться и находить нужные игры [url=http://www.hschangae.com/bbs/board.php?bo_table=free&wr_id=199128]http://www.hschangae.com/bbs/board.php?bo_table=free&wr_id=199128[/url]
<a href=https://vireg.ru/>купоны все инструменты</a>
<a href=https://bi-cleaning.ru/>https://bi-cleaning.ru/</a>
<a href=https://mclean.su/>чистовая уборка после ремонта</a>
Займ с любой кредитной историей. Без подтверждения дохода. Вы остаётесь собственником. Без отказов. Быстрое оформление. Без скрытых комиссий [url=http://matkapital38.ru/]частные займы для бизнеса[/url]
Ready to experience the excitement of video poker? Join our [url=https://usacasinohub.com/video-poker/]online poker games for real cash[/url] and start playing today. Whether you’re a novice or a seasoned poker player, our video poker games offer something for everyone. Embrace the challenge, apply your strategy, and enjoy the thrill of winning.
Закажите диплом и получите гарантированный результат
Автор 24 официальный [url=https://author24.online/]Автор24[/url] .
<a href=https://russa24-diploms-srednee.com/>http://russa24-diploms-srednee.com</a>
Backlinks will boost your site!
All information is on our page: https://sites.google.com/view/backlinks-seo-sell.
Our Telegram channel with services https://t.me/backlinksforgoogle1
FREE 1 ORDER 10,000 BACK LINKS
Telegram channel for communication: https://t.me/Backlinks_24
whoah this blog is fantastic i love reading your articles. Keep up the good work! You understand, a lot of individuals are looking around for this information, you can aid them greatly.
www.sojuzpharma.ru/about/pharmopeka?page=674&per-page=5В
www.rusnor.org/pubs/edit/index.php?PAGE_NAME=profile_view&UID=91604В
hoisuhoc.vn/tong-hop-nhung-mon-an-giup-thai-nhi-tang-can-tot-nhat/В
thepokiesgames.com/termsВ
mublog.ru/interesnye-novosti/obschaya/page/7.htmlВ
casino no verification uk [url=https://luckyhippos.com]uk casino welcome bonus[/url]
<a href=https://t.me/s/wild_west_gold_game>wild west gold казино</a>
essay on apple fruit for kids in hindi topics for classification essay [url=https://studbaywritingvip.com/paper/cover-letter-for-research-paper/]cover letter for research paper[/url] essay com cause and effect essay on drug abuse
Как правильно выбрать материал для перетяжки мебели, проверенных временем
Как преобразить интерьер с минимальными затратами, новый взгляд на привычную мебель
Топ-3 причины для перетяжки мебели в доме, попробуйте сами
Вдохновляющие идеи для перетяжки мебели, которые понравятся каждому
Как не ошибиться с выбором ткани для перетяжки мебели, запомнить
"КакСвоим".
Это важный элемент для продуктивных тренировок, который применяется для жимов и тяг. В наличии грифы для штанг на <a href=https://shtangi-grify.ru/>shtangi-grify</a> разных конфигураций. В выпуске долговечных снарядов реализуются инновационные марки металла. Всегда в продажезначительный каталог прямых грифов для коммерческой и домашней эксплуатации. Снаряды созданы для эффективных занятий и выполнены с разметкой и насечками для надежного хвата.
Современная вилла с каменной виллой с личным бассейном и личным парковочным местом. Светлый и просторный, идеально подходит для пар и семей [url=https://pride-land.ru/]квартира студия на кипре[/url]
Аренда вилл и домов на Кипре. Всего 1490. Мы готовы предложить снять виллу на Кипре или частный дом у моря любого уровня : от домов эконом класса до шикарных вилл с бассейном [url=https://rik-estate.ru/]кипр стоимость жилья аренда[/url]
Аренда квартиры не дает права на длительное пребывание на Кипре. Но договор нужен, чтобы подать документы на визу и сделать медицинскую страховку [url=https://cyprusrent.ru/]аренда апартаментов на кипре на берегу моря[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://denverbar.es/yggwzc">https://denverbar.es/yggwzc</a> of type and scrambled it to make a type specimen book.
часто приходится дежурить по выходным [url=https://www.modasmagvi.com.ec/president-trumpt-coronavirus-guidelines-for-america/]https://www.modasmagvi.com.ec/president-trumpt-coronavirus-guidelines-for-america/[/url] и праздникам. Юристы хорошо разбираются в правовых проблемах, и защищают интересы физических и правоведческих представителей, которые обратились к ним за данной услугой.
Купить Кокаин в Москве? Самый чистый Кокаин в Москве Купить
ССЫЛКА НА САЙТ- https://mephedrone.top
Недвижимость в новостройке на Северном Кипре. Недвижимость в новостройке на Северном Кипре является одним из самых популярных вариантов [url=https://www.newton-apartment.ru/]кипр недвижимость дешево[/url]
форум вебкам моделей и моделей OnlyFans! Здесь вы найдете полезные советы, поддержку и обсуждения на темы, связанные с работой в вебкам индустрии и на платформе OnlyFans. Присоединяйтесь к нашему сообществу, делитесь опытом и получайте ответы на все ваши вопросы.
<a href=https://forum.vipcamclub.ru/>https://forum.vipcamclub.ru/</a>
Find out how works! livestorm is a browser-based alternative that gives you a chance to conduct webinars online or pre-recorded webinars.
increase the excitement of the game. <a href="https://aviatorgamemaxi.com/">aviator play online </a>
The Aviator Game is a thrilling online casino game that combines chance and strategy. With its unique gameplay, <a href="https://aviatorgamemaxi.com/">aviator game demo free</a>
tablets, making it convenient to play anywhere and anytime. <a href="https://aviatorgamemaxi.com/">aviator play online</a>
The basic rule of the Aviator Game is straightforward: place a bet, watch the plane take off, and decide when to <a href="https://aviatorgamemaxi.com/">aviator apps</a>
The scoring system in the Aviator Game is based on the multiplier at the time of cashing out. The higher the <a href="https://aviatorgamemaxi.com/">aviator betting game demo</a>
Подарок для конкурента
https://xrumer.ru/
Такой пакет берут для переспама анкор листа сайта или мощно усилить НЧ запросы
[url=https://xrumer.ru/]Подарок для конкурента[/url]
For beginners, the key to success in the Aviator Game is to start with small bets and gradually increase as you <a href="https://aviatorgamemaxi.com/">aviator game demo free</a>
детоксикация нарколог мед <a href=https://lechenie-narkomanii.kz/>https://lechenie-narkomanii.kz/</a>
casino game. <a href="https://aviatorgamemaxi.com/">aviator in demo account</a>
“The gang and government in no way do not differ one from the other. Shay, Steve. "SLIDE SHOW: Peter Distefano of Arsonist [url=https://images.google.ad/url?q=https://healthwinter1.werite.net/how-to-stop-viewing-xxx-movies]mature mom stockings seduces son[/url] leads the feedback lounge ensemble |West Seattle Herald|White Center News."
The Aviator Game boasts several unique features that set it apart from other online casino games: <a href="https://aviatorgamemaxi.com/">aviator crash</a>
Social Elements: Options for multiplayer gameplay and chat features enhance the social experience. <a href="https://aviatorgamemaxi.com/">aviator game hack software download</a>
Risk Management: Setting limits on how much to bet and when to cash out. <a href="https://aviatorgamemaxi.com/">aviator game india</a>
back for more. <a href="https://aviatorgamemaxi.com/">aviator demo oyna</a>
Since its inception, the Aviator Game has undergone numerous updates and enhancements. Technological <a href="https://aviatorgamemaxi.com/">how to hack aviator game</a>
Daddy Casino - Официальный телеграм канал со слотами от Дэдди Casino [url=https://t.me/daddycasinorussia]daddy казино официальный[/url] . Актуальное, рабочее зеркало официального сайта Дэдди Казино. Регистрируйся в Казино Daddy, получай бонус используя промокод, не забудь скачать
дэдди казино официальный
https://t.me/daddycasinorussia
Представьте себе платформу, где инновации и безопасность идут рука об руку. Этот проект - ваш проводник в будущее финансов. [url=http://polimentosroberto.com.br/index.php?option=com_k2&view=itemlist&task=user&id=4241677]http://polimentosroberto.com.br/index.php?option=com_k2&view=itemlist&task=user&id=4241677[/url]
Unique Features of the Aviator Game <a href="https://aviatorgamemaxi.com/">play aviator on betway</a>
The Aviator Game traces its roots back to the early days of online gambling when developers sought to create <a href="https://aviatorgamemaxi.com/">aviator predictor tips and tricks</a>
Остальные статусы достигаются соответственнопо данным общей [url=http://www.ligadedermatologia.ufc.br/?p=40]http://www.ligadedermatologia.ufc.br/?p=40[/url] суммой внесенных депозитов. в роли приветственного бонуса оператор даёт поздравительный пакет 100 бесплатных вращений автоматически great pigsby megaways.
mature gangbang porno
https://www.google.com.pa/url?sa=t&url=http%3A%2F%2Ftubesweet.com
http://inter-m.ru/bitrix/redirect.php?goto=https://tubesweet.com/
https://tennisclinics.com.au/?URL=https://tubesweet.com/
https://meromgalil.my-free.website/s/cdn/?https://tubesweet.com/
Effective Strategies for Beginners <a href="https://aviatorgamedemoplay.com/">aviator game predictor</a>
[url=https://maup.com.ua/]https://maup.com.ua/[/url] в Ірландії називають "освітою третього рівня" (third level education). разом з 29 іншими країнами, Польща підписала Болонську декларацію, метою якої є створення європейського простору «вишки».
How to Start Playing the Aviator Game? <a href="https://aviatorgamedemoplay.com/">aviator demo game play</a>
Интернет-казино [url=https://t.me/daddycasinorussia]daddy casino официальный сайт[/url] — сайт или специальная программа, которые позволяют играть в азартные игры в интернете. Сайты интернет-казино могут специализироваться на различных азартных играх: игровых автоматах, рулетке, лотереях, викторинах, покере или других карточных и настольных играх. Википедия
дэдди казино официальный сайт
https://t.me/daddycasinorussia
History and Development <a href="https://aviatorgamedemoplay.com/">aviator game online free</a>
Unique Features of the Aviator Game <a href="https://aviatorgamedemoplay.com/">aviator demo download</a>
zithromax dosage 250 mg zithromax 200 5 [url=https://netmedsgoodxx.com/]zithromax z pak for uti[/url] zithromax pink pill zithromax and diflucan
Scoring System and Winning Criteria <a href="https://aviatorgamedemoplay.com/">aviator game predictor</a>
пассажиры могут в любой момент начать ставкам с любого устройства, [url=https://casinovovanreg.win/]casino vovan[/url] а портал полностью подстраивается под диагональ экрана.
<a href=http://stroymaterial39.ru/>http://stroymaterial39.ru/</a>
The Aviator Game boasts several unique features that set it apart from other online casino games: <a href="https://aviatorgamedemoplay.com/">aviator predictor tips and tricks</a>
Пашинян заявил, что никто из образцов Армении не поедет в Беларусь, [url=https://euro24.news/novosti/tag/transport]Транспорт Чехии новости[/url] пока там правит Лукашенко. coca-cola вновь регистрирует свои бренды в рф.
$20. The key is to find the right balance between risk and reward. <a href="https://aviatorgamedemoplay.com/">aviator app for pc</a>
Вы не ошиблись
[url=http://e-audit.gefest.me/index.php?subaction=userinfo&user=eruheqox]http://e-audit.gefest.me/index.php?subaction=userinfo&user=eruheqox[/url] в нашем мегаполисе подобные дома, чтобы жителям нравилось оставаться в квартире, в на стиралке и высшего образования дворе.
increase the excitement of the game. <a href="https://forum.instube.com/d/98840-the-game-s-dynamic">aviator game download</a>
provigil irritability provigil pill size [url=https://pharmicasssale.com/]provigil for cfs[/url] excelerol vs provigil provigil 100mg or 200mg
For beginners, the key to success in the Aviator Game is to start with small bets and gradually increase as you <a href="https://click4r.com/posts/g/17132161/innovative-game-alongside-traditional">how to bet in aviator</a>
В этом что-то есть. Понятно, благодарю за помощь в этом вопросе.
4. Подтвердите свою учетку, следуя дальнейшим инструкциям, [url=http://www.octaniumsw.site/2018/01/ssd-m2-acer-nitro-5-an515-41-f9wl.html]http://www.octaniumsw.site/2018/01/ssd-m2-acer-nitro-5-an515-41-f9wl.html[/url] которые будут отправлены к вам на почту.
demo versions or free play options to allow players to practice before betting real money. <a href="http://training.monro.com/forum/posts/m128002-environment-to-develop-their-skills#post128002">aviator game scam</a>
Obtain necessary certificates and certificates to ensure compliance with requirements legislation in sphere of [url=https://allthingssabine.com/forced-landing-in-sabine-parish-cotton-patch/]https://allthingssabine.com/forced-landing-in-sabine-parish-cotton-patch/[/url]. Conduct in-depth market research, analyze industry trends, identify your target audience and consider your rivals.
not, you lose your bet. <a href="https://swipestudio.co/forums/discussion/community/limited-to-a-single-platform">aviator betting game hack</a>
Staying Calm: Keeping a cool head and avoiding impulsive decisions during gameplay. <a href="https://busydadtraining.com/forum/topic/but-if-you-wait-too-long/#postid-2411">aviator casino game demo</a>
Common feedback from players includes requests for more in-game bonuses, additional multiplayer options, and <a href="https://foro.ribbon.es/topic/7164/excitement-and-suspense">aviator download for pc</a>
independent because, whether you are a professional poet, a beginner or one average, [url=https://glennroythesalon.com/this-nail-polish-brand-is-diversifying-the-nail-care-copy3/]https://glennroythesalon.com/this-nail-polish-brand-is-diversifying-the-nail-care-copy3/[/url] is our tool - it is exciting and convenient way creation various poems.
There are numerous online communities and forums where Aviator Game enthusiasts can share tips, strategies, and <a href="https://chobaolam.vn/threads/offers-a-unique-blend.540710/">aviator download</a>
Summary of Key Points <a href="https://aviatorgamewall.com/">aviator app hack</a>
Ready to experience the excitement of video poker? Join our [url=https://usacasinohub.com/video-poker/]online poker free no money[/url] and start playing today. Whether you’re a novice or a seasoned poker player, our video poker games offer something for everyone. Embrace the challenge, apply your strategy, and enjoy the thrill of winning.
Сотрудники компании Сантехника-Онлайн оценивают работу руководства на 4.1 из 5, на основании 165 оценок. Как сотрудники Сантехника-Онлайн оценивают возможности карьерного роста компании [url=https://elsolo.ru/household-building/santehnika-onlayn/moskva/]Отзывы от партнеров Сантехника Онлайн[/url]
שהיא לא רוצה. ספא למסאג' או עיסוי אירוטי בבאר שבע והסביבה מעסות הצעירות והדקיקות והנשים הבוגרות עם הגוף המדהים מציגות את לא מצפות שתיקחו אותנו קודם למסעדה או לסרט. אתם רוצים עיסוי אירוטי ואנו כאן בשביל לתת לכם את זה. היכן ניתן להתפנק עם עיסוי? <a href=http://www.sexybabydoll.co.il/>דירות דיסקרטיות בחדרה</a>
this means that your traffic usually takes longer to move between remote, overloaded servers, a [url=http://freshgreen.kr/bbs/board.php?bo_table=free&wr_id=247687]http://freshgreen.kr/bbs/board.php?bo_table=free&wr_id=247687[/url] or is even delayed in hoping for the traffic of paid users.
האישה: כמה צעצועים היא יכולה לשים שם? באופן טבעי, כמה מהמקצועניות שעובדות בשירותי דירות דיסקרטיות ברחובות נוסעות ברכב. אתם בחורות של דירות דיסקרטיות בתל אביב זה כמובן האלף-בית התנאי הבסיסי לשירות שאתם מקבלים: ממציצה ועד עיסוי אירוטי. כפי שטכנאי החשמל <a href=http://www.ganeysex.co.il/>The best private escort Tel Aviv girls</a>
Reputable online platforms offering the Aviator Game are licensed and regulated by governing bodies. This <a href="https://aviatorgamewall.com/">aviator casino en ligne</a>
נערות ליווי חרמניות שרוצות לבלות עם גברים בתל אביב. אתה יכול למצוא כאן היצע גדול של נערות חרמניות העובדות בתל אביב, ותוכל לא יודעות מהם איסורים מוסריים או טאבו על המסאג'. הפצצות המתוקות מסכימות בקלות להתנסויות, תמיד מוכנות לנסות משהו חדש. המטרה שלהן <a href=http://www.isragirls.co.il/>מכוני ליווי חיפה</a>
improved mobile compatibility. Developers continually use this feedback to enhance the game and provide a better <a href="https://aviatorgamewall.com/">aviator game baixar</a>
Have a nice day, buddy!
Looks like a superb addition for your website <a href=http://alumin.tel/>Advanced aluminium scrap sorting techniques</a>
To play the Aviator Game, you need a device with internet access and a web browser that supports HTML5. This <a href="https://aviatorgamewall.com/">aviator juego casino</a>
you need regularly to run errands? The parkmobile service, available more than in 400 cities throughout the edges of the USA, gives you happiness to park, pay and extend the [url=https://sway.cloud.microsoft/T1GMHToLCypbqCTR?ref=Link]https://sway.cloud.microsoft/T1GMHToLCypbqCTR?ref=Link[/url] time directly on your palm.
Оптимальный выбор для азартных игроков. Лучшие развлечения от проверенных производителей. Наслаждайтесь качественными слотами, щедрыми бонусами и высокой надежностью игровой платформы [url=https://fartunaplay.ru]https://fartunaplay.ru[/url]
https://fartunaplay.ru/slot-machines
Numerous online casino platforms offer the Aviator Game. These platforms provide a secure and regulated <a href="https://aviatorgamewall.com/">aviator game download for pc</a>
Effective Strategies for Beginners <a href="https://my.desktopnexus.com/Aviatorgamed/">aviator hack bot app</a>
להרגע ולהתמסר לצרכים הגבריים הטבעיים שלו. והנערות בהחלט מבינות גברים ויודעות להעניק להם את מה שהם מחפשים. מאמר 2 נערות נערות ליווי בחולון עם שיער קצר או שיער שחור ארוך – כל אחת יכולה להיות חברה שלכם לשעה אחת או ללילה שלם. משחקי תפקידים מתקבלים <a href=http://www.largepenis.co.il/>סקס באשקלון</a>
rybelsus alternatives rybelsus weight loss dosage [url=https://travelpharmvipp.com/]what is rybelsus 3mg[/url] rybelsus 7 what does rybelsus cost
Этот топик просто бесподобен :), мне интересно .
This growth occurred at the same hour when bitcoin and many other cryptocurrencies were experiencing shocks because of China's decision to ban Chinese banks from investing in [url=https://dogecoin20.io/]https://dogecoin20.io/[/url], which will strengthen the bitcoin economy.
בקרב מנתחים פלסטיים. עם זאת, ישנן בנות במרכז שיש להן אף רחב, וזוהי הוכחה לחושניות שלהן. צורת אף צרה אומרת שבעלת האף היא עדינה, חברים. כשאתם בוחרים דירות דיסקרטיות בבאר שבע ואת הפינוק, זה לא משנה מי דומיננטי ומי לא. המשתתפים במשחק התפקידים לא צריכים להיות <a href=http://www.sexliga.co.il/>נערות ליווי רוסיות</a>
Playing the Aviator Game involves a few simple steps: <a href="https://aviator-game.square.site/">how to win aviator game</a>
historically, turned out so, bitcoin dominated the single market capitalization of [url=https://papasearch.net/Electric_Car/ElectricCar20.html]https://papasearch.net/Electric_Car/ElectricCar20.html[/url], which accounted for more 50% of the market capitalization, then how altcoins increased and decreased the market capitalization in comparison with bitcoin.
Origins of the Aviator Game <a href="https://omewekupujih1978.wixsite.com/aviator-game">aviator crash game</a>
Какие бонусы за лояльность казино я могу получить? Давайте подробнее рассмотрим наиболее распространенные виды бонусов за лояльность в казино [url=https://fartunaplay.ru/slot-machines]https://fartunaplay.ru/slot-machines[/url]
Источник: https://fartunaplay.ru
Game Mechanics <a href="https://www.mixcloud.com/ehsannwekasy/">betway aviator</a>
plane crashes, making it a game of both luck and timing. This dynamic gameplay keeps players engaged and coming <a href="https://my.desktopnexus.com/Aviatorgamed/">aviator crash game</a>
Experienced players can benefit from more advanced strategies, such as: <a href="https://aviatorgamewall.com/">aviator game</a>
Какие бонусы за лояльность казино я могу получить? Давайте подробнее рассмотрим наиболее распространенные виды бонусов за лояльность в казино [url=https://fartunaplay.ru]https://fartunaplay.ru[/url]
Источник: https://fartunaplay.ru/mobiledevice
באמת צריך דירה דיסקרטית בירושלים בראש שקט ירושלים היא אומנם עיר מרכזית, אולם לאנשים מסוימים, להגיע עד לירושלים פירושו להתרחק ממש משמעותי ולא סתם, רוב האנשים שצורכים שירותים המלווים באישיות מרבית, אכן זקוקים לפרטיות הנ"ל ולכן עדיף להם להיות עד כמה שיותר <a href=http://www.sexpro.co.il/>שירות ליווי בבאר שבע ואזור הדרום</a>
Multiplayer Options and Social Interaction <a href="https://aviatorgamewall.com/">aviator predictor tips and tricks</a>
A Day in the Life: Experiencing the Northampton Marriott Lifestyle. Relax and rejuvenate at the Talise Spa, where an array of holistic treatments and therapies await, or take a dip in the infinity pool overlooking the azure. [url=]Elevate Your Stay: Luxurious Accommodations at The Grange Ramada Jarvis Hotel[/url]
https://ardoehousehotel.hotel-details.com/news/reconnect-with-nature-activities-and-adventures-at-mercure-ardoe-house
Risk Management: Setting limits on how much to bet and when to cash out. <a href="https://aviatorgamewall.com/">aviator hack apk download pc</a>
Basic Rules and Objectives <a href="https://aviatorgamewall.com/">aviator game ethiopia</a>
Social and Community Aspects <a href="https://aviatorgamewall.com/">aviator casino portugal</a>
Safety is paramount when playing online games. Players should ensure they are playing on reputable platforms <a href="https://aviatorgamewall.com/">aviator app hack</a>
the opportunity to compete for larger prizes and showcase their skills on a larger stage. <a href="https://aviatorgamewall.com/">aviator apk for pc</a>
דירות דיסקרטיות בחיפה דירות דיסקרטיות בחיפה יכולות להיות מה שתמיד חלמת עליו. אולי לא היית מודע לעולם האפשרויות הקסום שנמצא כאן בחורה לטעמכם שתפנק אתכם. ניתן בקלות למצוא בחורות המעניקות עיסוי אירוטי בנתניה באתרי האינטרנט. שם תוכלו לבחור לפי התמונות את <a href=http://www.sexbig.co.il/>נערות ליווי ערביות</a>
Online Platforms Offering the Game <a href="https://aviatorgamewall.com/">aviator virtual game</a>
Benefits of Playing Online <a href="https://aviatorgamewall.com/">aviator demo download</a>
The scoring system in the Aviator Game is based on the multiplier at the time of cashing out. The higher the <a href="https://aviatorgamewall.com/">aviator game 1xbet hack</a>
and the player's goal is to cash out before the plane crashes. This simple yet thrilling concept has made it a <a href="https://aviatorgamemaxi.com/">aviator applique rear panel</a>
Risk Management: Setting limits on how much to bet and when to cash out. <a href="https://aviatorgamemaxi.com/">aviator game tricks</a>
Risk Management: Setting limits on how much to bet and when to cash out. <a href="https://aviatorgamemaxi.com/">aviators game</a>
the anticipation building as the plane climbs higher. The key is to cash out at the right moment before the <a href="https://aviatorgamemaxi.com/">aviator game online free</a>
https://newcryptotradingbotreviews.com/
balancing the risk of waiting longer for a higher payout against the potential loss if the plane crashes. <a href="https://aviatorgamemaxi.com/">aviator apps</a>
Этого не может быть!
это позволит бетторам находить убедительные коэффициенты при низком качестве маржи и изымать средства [url=http://sport-engine.com/menuavtolifestyle/item/599-bentley-gigapixel-image-features-new-mulsanne.html]http://sport-engine.com/menuavtolifestyle/item/599-bentley-gigapixel-image-features-new-mulsanne.html[/url] с более низкой комиссией. Правда не нужно забывать и об всех прочих нюансах, как минимум важных, чем прибыль.
To start playing the Aviator Game, simply choose a reputable online casino platform that offers the game. <a href="https://aviatorgamewall.com/">aviator demo online</a>
Just desire to say ylur article iis as amazing. Thhe clarity
in your post is simply cool and i could assume you're an expert on this subject.
Well with your permission let me to grab yolur feed tto keep up too date with forthcoming
post. Thanks a million and lease kerp up the gratifying work. https://ukrain-forum.biz.ua/
Lorem Ipsum has been the industry's standard dummy text <a href="https://ajf-boischauffage.fr/lpgjo">https://ajf-boischauffage.fr/lpgjo</a> of type and scrambled it to make a type specimen book.
The future of the Aviator Game looks promising, with continuous updates and improvements. As technology <a href="https://aviatorgamewall.com/">demo game</a>
Москва Купить Мефедрон? Кристаллы МЕФ?
Где в Москве Купить Мефедрон? САЙТ - https://mephedrone.top/
Common Mistakes to Avoid
<a href="https://aviatorgamewall.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://dgkservice.it/vndzjha">https://dgkservice.it/vndzjha</a> of type and scrambled it to make a type specimen book.
History and Development
<a href="https://aviatorgamewall.com/">demo game</a>
best Inmate Text app
https://contactmeasap.com/blog/what-happens-inside-a-federal-prison/
Lorem Ipsum has been the industry's standard dummy text <a href="https://teslamania.es/dfrvyc">https://teslamania.es/dfrvyc</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://coverly.co.za/mrujtu">https://coverly.co.za/mrujtu</a> of type and scrambled it to make a type specimen book.
Watch the Plane Ascend: The plane takes off and starts climbing.
<a href="https://aviatorgamewall.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://march.cl/eqmvydd">https://march.cl/eqmvydd</a> of type and scrambled it to make a type specimen book.
Наша компания осуществляет печать фото на холсте с возможностью недорогой доставки. Опыт команды и наличие необходимого оснащения позволяет нам справляться с любыми задачами оперативно и на профессиональном уровне [url=https://photoges.ru/]фото печать[/url]
https://photoges.ru/
Lorem Ipsum has been the industry's standard dummy text <a href="https://petfactory.es/ginrys">https://petfactory.es/ginrys</a> of type and scrambled it to make a type specimen book.
Experienced players can benefit from more advanced strategies, such as:
<a href="https://aviatorgamewall.com/">aviator demo game</a>
The Aviator Game is an exciting online casino game that has captivated players worldwide with its unique blend
<a href="https://aviatorgamewall.com/">demo game</a>
improvements have not only made the game more appealing but also more accessible to a wider audience.
<a href="https://aviatorgamewall.com/">aviator demo online</a>
<a href=https://t.me/s/olymp_casinos/>olimp casino kz</a>
If you're looking for a thrilling and unique online casino game, give the Aviator Game a try. Join the millions
<a href="https://aviatorgamedemoplay.com/">Aviator free bet</a>
The Aviator Game uses a Random Number Generator (RNG) to ensure fair play. This technology ensures that each
<a href="https://aviatorgamedemoplay.com/">How to play Aviator demo online</a>
User Experience and Reviews
<a href="https://aviatorgamedemoplay.com/">Can I play aviator online for free</a>
Доставка алкоголя в Екатеринбурге
Мы собрали актуальные промокоды Мегамаркет на первый и повторный заказ! Не упустите шанс! 21 июня 2024 года на megamarket.ru действуют особенно выгодные предложения [url=https://t.me/promokody_megamarket]промокод сбермегамаркет[/url]
https://t.me/promokody_megamarket
Benefits of Playing Online
<a href="https://aviator-gamebet.com/demo/">aviator demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://sastoursandtravels.in/lxusgk">https://sastoursandtravels.in/lxusgk</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://strymer.es/iirucgk">https://strymer.es/iirucgk</a> of type and scrambled it to make a type specimen book.
players globally. The Aviator Game stands out in this crowded market due to its innovative gameplay and the
<a href="https://aviator-gamebet.com/demo/">aviator demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://baumschuerze.de/trxvsu">https://baumschuerze.de/trxvsu</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://login-betway-india.com/cmpopbf">https://login-betway-india.com/cmpopbf</a> of type and scrambled it to make a type specimen book.
Find here UAE Prayer Timings, Muslim Prayer Timings, Imsak Time, Iftar Timings, Fajr Time and more updates from Khaleej Times http://timenamaz.online/
Lorem Ipsum has been the industry's standard dummy text <a href="https://zaiwa.dk/xtyint">https://zaiwa.dk/xtyint</a> of type and scrambled it to make a type specimen book.
Many online platforms host competitive tournaments and events for the Aviator Game. These events offer players
<a href="https://aviator-gamebet.com/demo/">aviator demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://klubdal.pl/vnsnej">https://klubdal.pl/vnsnej</a> of type and scrambled it to make a type specimen book.
game was designed to provide an adrenaline-pumping experience that mimics the thrill of gambling with a twist.
<a href="https://aviator-gamebet.com/demo/">aviator demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://evafinans.dk/vbtfci">https://evafinans.dk/vbtfci</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://fotze.pl/otdevsp">https://fotze.pl/otdevsp</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://willarybaki.pl/gybtuh">https://willarybaki.pl/gybtuh</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://limpiezasletsgo.es/hqkdiac">https://limpiezasletsgo.es/hqkdiac</a> of type and scrambled it to make a type specimen book.
El uso regular de Yenki Derm puede reducir la apariencia de arrugas. [url=https://www.facebook.com/yenki.derm.para.que.sirve/]Yenki Derm Farmacia del Ahorro precio[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://maiphai.pl/myffk">https://maiphai.pl/myffk</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://annacarniz.es/vxhhm">https://annacarniz.es/vxhhm</a> of type and scrambled it to make a type specimen book.
<a href=https://t.me/intim_tmn72>проститутки тюмени</a>
in America [url=https://www.anticheterrecotteberti.com/en/gb/]https://www.anticheterrecotteberti.com/en/gb/[/url] the legality of sports betting online is discussed and can vary from state to state.
be you haven't launched a branded podcast yet, [url=https://camhd.ru/privet-mir/]https://camhd.ru/privet-mir/[/url] of webinars are become a natural step towards launching a new show.
Официальный городской информационный портал - новости Ижевска и Удмуртии, криминал, дорожно-транспортные происшествия (ДТП), чрезвычайные происшествия(ЧП) [url=https://vk.com/mdps18]https://vk.com/mdps18[/url]
<a href=https://remontmieleservis.ru/>ремонт холодильников миле</a>
Официальный городской информационный портал - новости Ижевска и Удмуртии, криминал, дорожно-транспортные происшествия (ДТП), чрезвычайные происшествия(ЧП) [url=https://vk.com/mdps18]https://vk.com/mdps18[/url]
Искал автошколу в своем районе у м. Аэропорт или Сокол, там одна улица проходит. Считаю, что сделал неплохой выбор [url=http://gai-18.ru]автошкола в митино[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://biz4u.in/sfxqlon">https://biz4u.in/sfxqlon</a> of type and scrambled it to make a type specimen book.
<a href=https://naves-sale.ru/>навес из поликарбоната</a>
Достижение положительного результата в освоении управления легковым автомобилем и получении водительских прав гарантирует автошкола с репутацией [url=http://avtopoisk43.ru/]уроки вождения с инструктором[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://sastoursandtravels.in/nfopbf">https://sastoursandtravels.in/nfopbf</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://gastroludki.pl/ctqxej">https://gastroludki.pl/ctqxej</a> of type and scrambled it to make a type specimen book.
<a href="https://zelpgo.ru">Бездепозитный бонус онлайн казино
Вы не правы. Могу это доказать. Пишите мне в PM, пообщаемся.
кроме того мы периодические акции а также распродажи, [url=http://moveyourjobtocairns.com.au/recycled-glass-used-in-fnq-road-works/]http://moveyourjobtocairns.com.au/recycled-glass-used-in-fnq-road-works/[/url] в процессе коих вы имеете шанс приобрести необычные оригинальные одноразовые парилки по самой обоснованной цене!
http://atvbizon.ru/
http://kvadrociklov-prokat.ru/
http://atvbizon.ru/
Lorem Ipsum has been the industry's standard dummy text <a href="https://sonoricco.it/qefvfps">https://sonoricco.it/qefvfps</a> of type and scrambled it to make a type specimen book.
balancing the risk of waiting longer for a higher payout against the potential loss if the plane crashes.
<a href="https://tigrinho.co/">tigrinho aposta</a>
Future of the Aviator Game
<a href="https://tigrinho.co/">tigrinho demo</a>
<a href=https://interventionist.us/>https://interventionist.us/</a>
Player reviews and testimonials are overwhelmingly positive, with many praising the game's exciting gameplay and
<a href="https://tigrinho.co/">jogo do tigrinho demo</a>
http://ek-x.ru/
Hello everybody!
City Breaks! Explore vibrant cities with our city guides. Find top attractions, accommodations, and insider tips for urban adventures.
Cultural Immersion! Immerse in cultures with our travel tips. Experience local traditions, festivals, and customs like an insider.
Look interesting site about this - https://visionarynexst.com
e-commerce
news
regional news
travel apps
latest news
business development
news headlines
market research
Good luck!
https://livecamsporno.com/
For beginners, the key to success in the Aviator Game is to start with small bets and gradually increase as you
<a href="https://tigrinho.co/">fortune tiger demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://rampymobilne.pl/caonp">https://rampymobilne.pl/caonp</a> of type and scrambled it to make a type specimen book.
Right here is the right website for anybody who would like to find out about this topic. You know so much its almost tough to argue with you (not that I really will need to…HaHa). You definitely put a new spin on a topic that has been written about for many years. Excellent stuff, just great!
http://gravure-dore.ru/rMat2735_TheErectionOfTheCross.htm
купить диплом бурильщика
http://n-seo.ru
купить диплом в люберцах
can also help in making informed cash-out decisions.
<a href="https://tigrinho.co/">fortune tiger</a>
doubletree by Hilton Pittsburgh airport: Business travelers love this hotel at airfield for free Wi-fi, [url=https://mstdn.social/@yyzlongterm]https://mstdn.social/@yyzlongterm[/url], desks in every room and business-the center.
<a href=https://www.instagram.com/asiapsiholog_family/>https://www.instagram.com/asiapsiholog_family/</a>
https://www.livevideochat.xyz/
<a href=https://lebelligerant.com/>https://lebelligerant.com/</a>
https://pornkingcams.com/
гут!сам частенько подобное придумываю...
Les sous-vetements en dentelle a la mode sont tres mignons, ils peuvent etre utilises comme une robe d'ete ou une chemise de nuit, [url=https://nl.voproom.com/]https://nl.voproom.com/[/url] qui fera vous plus belle et charmant.
The most stunning transsexual shows on Stripchat. Popular trans chat rooms on free live sex cams. Watch, flirt, and have fun with trans cam models [url=https://bestshemalecams.com/]trans cam to cam[/url]
Наша компания проектирует бассейны любой сложности! Быстро и качественно построим бассейн. Бассейны под ключ по индивидуальным и готовым решениям. Поставляем оборудование для бассейнов зарубежных и отечественных производителей [url=http://summerescapes.ru/]альгитинн для бассейна цена[/url]
Услуги ассенизатора по Клинскому району от 750р. за 1 куб. Шланги до 100м. Работаем без выходных.
Наш официальный сайт https://mos-los.ru/
The Aviator Game traces its roots back to the early days of online gambling when developers sought to create
<a href="https://tigrinho.co/">tigrinho demo</a>
The most stunning transsexual shows on Stripchat. Popular trans chat rooms on free live sex cams. Watch, flirt, and have fun with trans cam models [url=https://bestshemalecams.com/]tranny sex cams[/url]
Are you parking your electric car in the [url=https://fliphtml5.com/homepage/fuxdg/yyzlongtermp/]https://fliphtml5.com/homepage/fuxdg/yyzlongtermp/[/url]? for beloved transport in the store provide unpaid testing of tire pressure.
Online casino games have surged in popularity due to their convenience and the immersive experience they offer.
<a href="https://tigrinho.co/">tigrinho</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://spotykids.es/jlnya">https://spotykids.es/jlnya</a> of type and scrambled it to make a type specimen book.
полный ФУФЁЛ!!!
vous pouvez de commencer conversation/ contact avec n'importe lequel de ci-dessus putes magnifiques et d'inviter leur dans le chat prive porno, afin voir/ connaitre, comment ils font absolument tout, que vous voulez, pour [url=https://fr.ruletka-888.com/?country=fr]https://fr.ruletka-888.com/?country=fr[/url] en direct sur votre webcam.
We assure that repairs of any level of complexity will be finished within 3 days or sooner. Mechanics and electricians at PPR have experience working at authorized dealerships of Toyota, Land-Rover, Suzuki, Nissan, Mercedes, VAG, and BMW [url=http://auto-city24.ru/]lexus dubai[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://amaloquehaces.es/iqmqrg">https://amaloquehaces.es/iqmqrg</a> of type and scrambled it to make a type specimen book.
$20. The key is to find the right balance between risk and reward.
<a href="https://aviatorgameaviator.com/">aviator game online</a>
https://semlava.com/
Evolution and Technological Advancements
<a href="https://aviatorgameaviator.com/">aviator game online</a>
https://fuckingcouple.com
мне парочку
regardless therefore, which board game the Australians choose, they for sure will receive positive feelings from playing in [url=https://wild-joker.online/]Wild joker drugs[/url]. The nutrition slot machines wild joker offers a large selection.
все [url=http://petervanwanrooyzonwering.nl/component/k2/item/1?quot;=]http://petervanwanrooyzonwering.nl/component/k2/item/1?quot;=[/url] Европы были закрыты к 1873 году. Принцип большинства игр, проводящихся в онлайн-казино - конец соревнования, для её участника зависит прежде всего, от элемента случайности.
Common mistakes to avoid in the Aviator Game include:
<a href="https://aviatorgameaviator.com/">aviator game demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://josemariaabad.es/bllpqm">https://josemariaabad.es/bllpqm</a> of type and scrambled it to make a type specimen book.
https://semlava.com/
Lorem Ipsum has been the industry's standard dummy text <a href="https://guacamayaproducciones.es/mesiiad">https://guacamayaproducciones.es/mesiiad</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://mardaninews.in/kffqpkm">https://mardaninews.in/kffqpkm</a> of type and scrambled it to make a type specimen book.
Какое прелестное сообщение
parking lot for transfer is a more budget option for long-[url=https://us.community.sony.com/s/profile/005Dp000004ccZw?language=en_US]https://us.community.sony.com/s/profile/005Dp000004ccZw?language=en_US[/url] at airport. Upon return, the valet refund You need a car.
the social features, and the quality of the user interface.
<a href="https://aviatorgameaviator.com/">aviator game online</a>
Общественное здание или его часть [url=https://zetflixhd.life/]зетфликс онлайн[/url] с оборудованием для публичной демонстрации кинофильмов. Главное помещение кинотеатра - зрительный зал с экраном большого размера и системой воспроизведения звука. В современных кинотеатрах система звуковоспроизведения состоит из нескольких громкоговорителей, обеспечивающих объёмный звук. Первые стационарные кинотеатры назывались в России «электротеатрами»
зетфликс https://zetflixhd.life/
Lorem Ipsum has been the industry's standard dummy text <a href="https://smarthoteltv.es/dgkupwc">https://smarthoteltv.es/dgkupwc</a> of type and scrambled it to make a type specimen book.
https://strip-cams.com/
Features and Benefits
<a href="https://aviatorgameaviator.com/">aviator game online</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://coffeedrama.in/nodsb">https://coffeedrama.in/nodsb</a> of type and scrambled it to make a type specimen book.
https://strip-cams.com/
Lorem Ipsum has been the industry's standard dummy text <a href="https://pubpropaganda.pl/nknzrw">https://pubpropaganda.pl/nknzrw</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://amaloquehaces.es/mptrtgm">https://amaloquehaces.es/mptrtgm</a> of type and scrambled it to make a type specimen book.
the opportunity to compete for larger prizes and showcase their skills on a larger stage.
<a href="https://aviatorgameaviator.com/">aviator game demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://lupo1987.dk/xlyarln">https://lupo1987.dk/xlyarln</a> of type and scrambled it to make a type specimen book.
The Aviator Game is a thrilling online casino game that combines chance and strategy. With its unique gameplay,
<a href="https://aviatorgameaviator.com/">aviator game online</a>
players globally. The Aviator Game stands out in this crowded market due to its innovative gameplay and the
<a href="https://aviatorgameaviator.com/">aviator game online</a>
Notice any red flags? Trust your gut. If something feels off, it's okay to step back and reassess the situation. Your safety and comfort come first
[url=https://lordforex.charity/]news site[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://stepspdf.cfd/kkyjghe">https://stepspdf.cfd/kkyjghe</a> of type and scrambled it to make a type specimen book.
Теперь нет необходимости везти крупную бытовую технику в сервисный центр. Наш мастер проводит диагностику у вас дома, находит сломанную деталь и заменяет ее [url=https://www.au-e.com/web/bosch-remont.ru]https://www.au-e.com/web/bosch-remont.ru[/url]
Conclusion
<a href="https://aviatorgameaviator.com/">aviator game demo</a>
improved mobile compatibility. Developers continually use this feedback to enhance the game and provide a better
<a href="https://aviatorgameaviator.com/">aviator game</a>
To start playing the Aviator Game, simply choose a reputable online casino platform that offers the game.
<a href="https://aviatorgameaviator.com/">aviator game demo</a>
Что может быть лучше, чем красивая девушка, массирующая Вас после тяжелого делового дня [url=https://be1.ru/cms/?url=devkiru.com]https://be1.ru/cms/?url=devkiru.com[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://trajesmotocross.es/uaaszmx">https://trajesmotocross.es/uaaszmx</a> of type and scrambled it to make a type specimen book.
Online casino games have surged in popularity due to their convenience and the immersive experience they offer.
<a href="https://aviatorgameaviator.com/">aviator game demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://honestusbroker.pl/aatvmna">https://honestusbroker.pl/aatvmna</a> of type and scrambled it to make a type specimen book.
Что может быть лучше, чем красивая девушка, массирующая Вас после тяжелого делового дня [url=http://pr0cy.com/new/tools/analysis/devkiru.com]http://pr0cy.com/new/tools/analysis/devkiru.com[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://theproductioncompany.dk/rtelcmg">https://theproductioncompany.dk/rtelcmg</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://joancanals.es/cdzulms">https://joancanals.es/cdzulms</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://spiwin.pl/hefnwu">https://spiwin.pl/hefnwu</a> of type and scrambled it to make a type specimen book.
ensures that the games are fair and that the platforms adhere to strict standards of operation.
<a href="https://aviatorgameaviator.com/">aviator game online</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://boost4kids.nl/qakis">https://boost4kids.nl/qakis</a> of type and scrambled it to make a type specimen book.
experience for players.
<a href="https://aviator-gamebet.com/">aviator game</a>
Dynamic Gameplay: The game's real-time progression keeps players on the edge of their seats.
<a href="https://aviator-gamebet.com/">aviator game</a>
Safety is paramount when playing online games. Players should ensure they are playing on reputable platforms
<a href="https://aviator-gamebet.com/">aviator game</a>
Register an account, make a deposit, and navigate to the Aviator Game to start playing.
<a href="https://aviator-gamebet.com/">aviator game</a>
<a href=https://t.me/s/c1win>1вин казино скачать приложение</a>
The ability to play from anywhere, coupled with the variety of games available, has attracted millions of
<a href="https://aviator-gamebet.com/">aviator game</a>
Social Elements: Options for multiplayer gameplay and chat features enhance the social experience.
<a href="https://aviator-gamebet.com/">aviator game</a>
The basic rule of the Aviator Game is straightforward: place a bet, watch the plane take off, and decide when to
<a href="https://aviator-gamebet.com/">п»їaviator game</a>
Unique Features of the Aviator Game
<a href="https://aviator-gamebet.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://tappeto4pets.it/lavzult">https://tappeto4pets.it/lavzult</a> of type and scrambled it to make a type specimen book.
The Aviator Game is a thrilling online casino game that combines chance and strategy. With its unique gameplay,
<a href="https://aviator-gamebet.com/">aviator game</a>
plane crashes, making it a game of both luck and timing. This dynamic gameplay keeps players engaged and coming
<a href="https://aviator-gamebet.com/">aviator game</a>
The Aviator Game is a thrilling online casino game that combines chance and strategy. With its unique gameplay,
<a href="https://aviator-gamebet.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://lmnst.es/pcekahn">https://lmnst.es/pcekahn</a> of type and scrambled it to make a type specimen book.
Dynamic Gameplay: The game's real-time progression keeps players on the edge of their seats.
<a href="https://aviator-gamebet.com/">aviator game</a>
Are There Any Costs Involved?
<a href="https://aviator-gamebet.com/">aviator game</a>
Столешницы, барные стойки, подоконники и другие изделия из искусственного камня от производителя мебели из камня “Акрилиум” [url=https://remontmix.ru/articles/stoleshnici-iz-kamnya-dlya-vannoi-komnati-iziskannost-praktichnost-dolgovechnost]https://remontmix.ru/articles/stoleshnici-iz-kamnya-dlya-vannoi-komnati-iziskannost-praktichnost-dolgovechnost[/url]
Kylian Mbappe is a French professional footballer who plays as a forward for Paris Saint-Germain and the French national team. Renowned for his speed, dribbling, and finishing, Mbappe has won numerous titles, including multiple Ligue 1 championships and the FIFA World Cup in 2018. Find out more about him here - <a href=https://kylianmbappe.paris-saint-germain-ar.com/>https://kylianmbappe.paris-saint-germain-ar.com/</a>
In-Game Bonuses and Rewards
<a href="https://aviator-gamebet.com/">aviator game</a>
Cash Out: Decide when to cash out to secure your winnings. If you cash out before the plane crashes, you win. If
<a href="https://aviator-gamebet.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://placassolaresmalaga2000.es/xdcpubw">https://placassolaresmalaga2000.es/xdcpubw</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://marielabertuggia.es/iilrr">https://marielabertuggia.es/iilrr</a> of type and scrambled it to make a type specimen book.
experience for players.
<a href="https://aviator-gamebet.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://alergosurcordoba2023.es/upiitkh">https://alergosurcordoba2023.es/upiitkh</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://joancanals.es/abchjio">https://joancanals.es/abchjio</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://tiska.es/ogenl">https://tiska.es/ogenl</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://starenterprises.nl/bddnzzl">https://starenterprises.nl/bddnzzl</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://analisidebiti.it/vacjjo">https://analisidebiti.it/vacjjo</a> of type and scrambled it to make a type specimen book.
Жаль, что сейчас не могу высказаться - нет свободного времени. Вернусь - обязательно выскажу своё мнение.
в наш час в Гнівані зареєстровано 3 підприємця з рядів ВПО, сферою діяльності яких є автосервіс (лагодження авто), [url=https://eurosiz.ua/product-category/spetsodezhda/filter-tip-shorty/]https://eurosiz.ua/product-category/spetsodezhda/filter-tip-shorty/[/url] операції в Інтернет - маркеті і вищезгадане швейне підприємство.
Lorem Ipsum has been the industry's standard dummy text <a href="https://mobilwiz.dk/cakby">https://mobilwiz.dk/cakby</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://march.cl/gorygm">https://march.cl/gorygm</a> of type and scrambled it to make a type specimen book.
Лучше поздно, чем никогда.
Такой купон дает право заключить пари на выбранную дисциплину. но выигрыша, будет рассчитано как обычное пари, [url=https://rumol.ru/wp-includes/wli/Promo_Kod_Dlya_1xBet_2021.html]https://rumol.ru/wp-includes/wli/Promo_Kod_Dlya_1xBet_2021.html[/url] а полученные выигрыши с него поступят на главной счет.
Играйте в любимые [url=https://1vulcanpobeda.com/]игровые автоматы[/url] без регистрации и без лишних ограничений на нашем сайте - просто запустите игру и наслаждайтесь азартом в полную силу!
Lorem Ipsum has been the industry's standard dummy text <a href="https://miglierinacomunitaospitale.it/iezjp">https://miglierinacomunitaospitale.it/iezjp</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://tascaisa.es/hhmsgsv">https://tascaisa.es/hhmsgsv</a> of type and scrambled it to make a type specimen book.
Извините, фраза удалена
Наивный и милый, [url=http://ffil.blogspot.com/2011/01/40.html]http://ffil.blogspot.com/2011/01/40.html[/url] большой фанат «Спартака». В 101 серии воротился в ресторан victor по приглашению Дмитрия Нагиева и превратился в работать музыкантом.
Нужна шлифовка сруба дома вашей мечты? Наша бригада из опытных строителей из Белоруссии готова воплотить ваши идеи в реальность! Современные технологии, индивидуальный подход, и качество – это наши гарантии. Посетите наш сайт [url=https://dolgoprudnyj.shlifovka-sruba-doma.ru]шлифовка сруба дома[/url] и начните строительство вашего уюта прямо сейчас! #БелорусскаяБригада #Шлифовка
Что он замышляет?
И однако, мало кто из нас не откладывая, обращается к врачу, [url=http://slavsbyt.ru/index.php?subaction=userinfo&user=ujamiq]http://slavsbyt.ru/index.php?subaction=userinfo&user=ujamiq[/url] обнаружив дырку в одном из зубов.
Aviator Game. Notable names in the industry have contributed their expertise to ensure the game is both engaging
<a href="https://aviatorgame.dev/">aviator game</a>
Moderator!
Ищете онлайн-площадку, которая ценит ваше время? Kraken сайт - это решение! Благодаря интуитивно понятному интерфейсу и эффективной системе поиска <a href=https://xn--krakn4-z4a.com>kraken ссылка</a> гарантирует, что вы найдете желаемый товар в кратчайшие сроки. Пройдите простую регистрацию и изучите разнообразные категории. Присоединяйтесь к <a href=https://xn--krakn4-z4a.com>kraken ссылка</a> прямо сейчас и делайте покупки с умом.
kraken market:https://xn--krakn4-z4a.com
Эта идея устарела
The teams were seeded matching the overall ranking of the European [url=https://euro2024groupabetting.com/]Bet on EURO 2024[/url] qualifiers.
Pattern Analysis: Studying the game's patterns and trends to predict optimal cash-out times.
<a href="https://aviatorgame.dev/">aviator game</a>
Multiplayer Options and Social Interaction
<a href="https://aviatorgame.dev/">aviator game</a>
dynamic features, and social elements, it offers an engaging experience for players. The game is supported by
<a href="https://aviatorgame.dev/">aviator game</a>
Since its inception, the Aviator Game has undergone numerous updates and enhancements. Technological
<a href="https://aviatorgame.dev/">aviator game</a>
cash-out perfectly.
<a href="https://aviatorgame.dev/">aviator game</a>
<a href=https://serv-remont-telefonov.ru/>сервис ремонта смартфонов</a>
plane ascends, the higher the multiplier. For example, if you bet $10 and cash out at a 2x multiplier, you win
<a href="https://aviatorgame.dev/">aviator game</a>
enjoyable.
<a href="https://aviatorgame.dev/">aviator game</a>
The basic rule of the Aviator Game is straightforward: place a bet, watch the plane take off, and decide when to
<a href="https://aviatorgame.dev/">aviator game</a>
Game Mechanics
<a href="https://aviatorgame.dev/">aviator game</a>
Я надеюсь завтра будет...
Спендий обещает солдату жалкую старость, когда слепой и хромой старик с посохом сможет ходить от [url=https://regideso.bi/2021/02/12/bientot-des-compteurs-communicants-a-la-regideso/]https://regideso.bi/2021/02/12/bientot-des-compteurs-communicants-a-la-regideso/[/url] непосредственно получателю и рассказывать про свою молодость малым ребятам и продавцам рассола».
$20. The key is to find the right balance between risk and reward.
<a href="https://aviatorgame.dev/">aviator game</a>
plane crashes, making it a game of both luck and timing. This dynamic gameplay keeps players engaged and coming
<a href="https://aviatorgame.dev/">aviator game</a>
кульно!!!
на протяжении нескольких минут после выполнения данных действий на бонусный счет пользователя будет зачислена [url=https://berforum.ru/rota/pages/?sekretnuy_promokod_na_melbet_bonus_pri_registracii.html]https://berforum.ru/rota/pages/?sekretnuy_promokod_na_melbet_bonus_pri_registracii.html[/url] награда.
The Aviator Game uses a Random Number Generator (RNG) to ensure fair play. This technology ensures that each
<a href="https://aviatorgame.dev/">aviator game</a>
Ignoring Patterns: Failing to observe and learn from the game's patterns can reduce your chances of winning.
<a href="https://aviatorgame.dev/">aviator game</a>
Game Mechanics
<a href="https://aviatorgame.dev/">aviator game</a>
The Aviator Game is an exciting online casino game that has captivated players worldwide with its unique blend
<a href="https://aviatorgame.dev/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://stepsfast.us/bonrjl">https://stepsfast.us/bonrjl</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://evafinans.dk/geydj">https://evafinans.dk/geydj</a> of type and scrambled it to make a type specimen book.
https://24smski.ru
cash-out perfectly.
<a href="https://aviatorgame.dev/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://trajesmotocross.es/orreq">https://trajesmotocross.es/orreq</a> of type and scrambled it to make a type specimen book.
plane ascends, the higher the multiplier. For example, if you bet $10 and cash out at a 2x multiplier, you win
<a href="https://aviatorgamemaxi.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://telomontoyo.es/vgwyii">https://telomontoyo.es/vgwyii</a> of type and scrambled it to make a type specimen book.
The Aviator Game is designed to be compatible with a wide range of devices, including desktop computers,
<a href="https://aviatorgamemaxi.com/">aviator game</a>
Kayleigh Wanless Pornstar It's Not As Expensive As You Think Pornstar Kayleigh
Watch the Plane Ascend: The plane takes off and starts climbing.
<a href="https://aviatorgamemaxi.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://excellenceevents.in/urgdvgo">https://excellenceevents.in/urgdvgo</a> of type and scrambled it to make a type specimen book.
environment for players to enjoy the game. Some popular platforms include [Casino Name], [Casino Name], and
<a href="https://aviatorgamemaxi.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://telomontoyo.es/wxoinnn">https://telomontoyo.es/wxoinnn</a> of type and scrambled it to make a type specimen book.
http://autoexpert-group.ru/
Lorem Ipsum has been the industry's standard dummy text <a href="https://dgkservice.it/pkmnrj">https://dgkservice.it/pkmnrj</a> of type and scrambled it to make a type specimen book.
Playing the Aviator Game is a thrilling experience. Players place their bets and watch the plane take off, with
<a href="https://aviatorgamemaxi.com/">aviator game</a>
How to Play the Aviator Game
<a href="https://aviatorgamemaxi.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://fokusklinikken.dk/gfkwwko">https://fokusklinikken.dk/gfkwwko</a> of type and scrambled it to make a type specimen book.
Chasing Losses: Trying to recover losses by betting more can be detrimental.
<a href="https://aviatorgamemaxi.com/">aviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://selfpas.it/floqjmr">https://selfpas.it/floqjmr</a> of type and scrambled it to make a type specimen book.
Wow, this post is nice, my sister is analpyzing these kjnds of things,
so I am going to tell her. https://waste-ndc.pro/community/profile/tressa79906983/
Competitive Tournaments and Events
<a href="https://aviatorgamemaxi.com/">п»їaviator game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://agamagizhan.in/muuvxmx">https://agamagizhan.in/muuvxmx</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://vastuastro.in/wfiaj">https://vastuastro.in/wfiaj</a> of type and scrambled it to make a type specimen book.
Future of the Aviator Game
<a href="https://aviatorgamemaxi.com/">aviator game</a>
social interaction adds a new layer of excitement and competition to the game, making it more engaging and
<a href="https://aviatorgamemaxi.com/">aviator game</a>
Hi! This is my first comment here so I just wqnted tto ive a quick shout out and say I
truly enjoy reading through your articles.
Caan you suggest aany other blogs/websites/forums that cover
the same subjects? Thank you so much! https://ukrain-Forum.biz.ua/
increase the excitement of the game.
<a href="https://aviatorgamemaxi.com/">aviator game</a>
Online Platforms Offering the Game
<a href="https://aviatorgamemaxi.com/">aviator game</a>
http://autolombard-capital.ru/
Bonuses: Online casinos often offer bonuses and promotions, enhancing the gaming experience.
<a href="https://genedmed.com/">viagra</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://btelectricshop.es/uipxe">https://btelectricshop.es/uipxe</a> of type and scrambled it to make a type specimen book.
whether at home or on the go.
<a href="https://genedmed.com/">cialis without prescription</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://you2i.dk/dbdxrv">https://you2i.dk/dbdxrv</a> of type and scrambled it to make a type specimen book.
Join now for thrilling slots casino games. Win big at our online casino and hit the jackpot [url=https://toptdspup.com/oHv4nV82/]pin up giriş türkiye[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://nadpoprzeczka.pl/lqqtv">https://nadpoprzeczka.pl/lqqtv</a> of type and scrambled it to make a type specimen book.
The Aviator Game traces its roots back to the early days of online gambling when developers sought to create
<a href="https://genedmed.com/">erectile dysfunction pills for men</a>
http://progressive-cars.ru/
Signup Bonus-200% up to your first deposit using promo code GGBET93-click the link to collect. The official Pinterest account of the bookmaker and online casino GGBET. Actual login to GGBET website in 2024 [url=https://pl.pinterest.com/ggbetcasinopolska/]ggbet pl[/url]
The Aviator Game uses a Random Number Generator (RNG) to ensure fair play. This technology ensures that each
<a href="https://genedmed.com/">canadian generic erectile dysfunction drugs</a>
the anticipation building as the plane climbs higher. The key is to cash out at the right moment before the
<a href="https://genedmed.com/">erection pills</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://flamencolapaloma.pl/pqhny">https://flamencolapaloma.pl/pqhny</a> of type and scrambled it to make a type specimen book.
<a href=https://www.instagram.com/asiapsiholog_family/>https://www.instagram.com/asiapsiholog_family/</a>
Лизинг спецтехники для юридических лиц – это эффективный способ инвестировать в свою компанию. Условия договора лизинга, такие как срок и график платежей, обычно определяются индивидуально [url=http://spectehnikaleasing.ru/]лизинг спецтехники для физических лиц[/url]
Social Elements: Options for multiplayer gameplay and chat features enhance the social experience.
<a href="https://genedmed.com/">male enhancement gummies</a>
Strategies and Tips
<a href="https://genedmed.com/">red boost</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://biztechnews.in/knogh">https://biztechnews.in/knogh</a> of type and scrambled it to make a type specimen book.
Aviator Game. Notable names in the industry have contributed their expertise to ensure the game is both engaging
<a href="https://genedmed.com/">buy erectile dysfunction medicine</a>
https://nudifyai.net/
Future of the Aviator Game
<a href="https://genedmed.com/">order erectile dysfunction pills online</a>
Купить машины в лизинг от официальных дилеров, автосалонов. Выгодные условия и скидки [url=http://autopodbor-yaroslavl.ru/]автотранспорт в лизинг в россии[/url]
Первая недвижимость Санкт-Петербурга - Про Питер (Pro Piter) -
продажа квартир с обременением спб
В этом что-то есть. Теперь мне стало всё ясно, Большое спасибо за информацию.
for those who appreciate use [url=https://tubidymp4.co.za/]Tubidy MP4[/url], for audio, our mp4 download sites offer high-quality offline playback options.
The Aviator Game offers multiplayer options that allow players to compete against each other in real-time. This
<a href="https://genedmed.com/">can you buy viagra over the counter</a>
Купить машины в лизинг от официальных дилеров, автосалонов. Выгодные условия и скидки [url=http://autopodbor-yaroslavl.ru/]финансовый лизинг автотранспорта[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://betway-casino-app.com/ruhsu">https://betway-casino-app.com/ruhsu</a> of type and scrambled it to make a type specimen book.
History and Development
<a href="https://genedmed.com/">canadian generic erectile dysfunction drugs</a>
https://nudifyai.net
How to Start Playing the Aviator Game?
<a href="https://genedmed.com/">male enhancement pills</a>
Для тех, кто ищет увлекательные пути к развлечениям и возможности испытать удачу в виртуальной среде, существует мир, где представлены бесчисленные варианты игр и азартных развлечений [url=https://centrmedprof40.ru/communication/forum/messages/forum5/message1389/1408-kakie-valyuty-prinimaet-1win-casino?result=new#message1389]https://centrmedprof40.ru/communication/forum/messages/forum5/message1389/1408-kakie-valyuty-prinimaet-1win-casino?result=new#message1389[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://mvdesk.in/bgwpfw">https://mvdesk.in/bgwpfw</a> of type and scrambled it to make a type specimen book.
Interactive Interface: Players can interact with the game in real-time, making decisions that impact their
<a href="https://genedmed.com/">male stamina supplement</a>
<a href=https://www.wildberries.ru/catalog/217171028/detail.aspx>купить ночник с маркером</a>
<a href=https://1wins-mozambique-bonus.com>1win bet</a>
Как показывает практика, сегодня купить лучшее медицинское оборудование и технику в Украине, востребованные для оказания соответствующих услуг на безупречном уровне, точно не является проблемой [url=https://www.niann.ru/?id=598583]https://www.niann.ru/?id=598583[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://loksangharshlivenews.in/lhkik">https://loksangharshlivenews.in/lhkik</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://youthcoop.es/rlncyv">https://youthcoop.es/rlncyv</a> of type and scrambled it to make a type specimen book.
In-Game Bonuses and Rewards
<a href="https://genedmed.com/">men's supplements</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://plaquiste-millau.fr/imbgkmq">https://plaquiste-millau.fr/imbgkmq</a> of type and scrambled it to make a type specimen book.
Game Mechanics
<a href="https://genedmed.com/">canadian ed pills online</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://spahouse.dk/dlrtzjf">https://spahouse.dk/dlrtzjf</a> of type and scrambled it to make a type specimen book.
Реализуя широкий ассортимент оборудования и медицинской техники, мы удовлетворяем запросы врачей различных профилей, косметологов и административного персонала [url=https://www.niann.ru/?id=598583]https://www.niann.ru/?id=598583[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://mobilitatelx.es/ohitej">https://mobilitatelx.es/ohitej</a> of type and scrambled it to make a type specimen book.
Лизинг оборудования открывает новые возможности для развития вашей компании. Это одно из наиболее эффективных финансовых решений для модернизации производственных мощностей и оптимизации работы предприятия [url=https://ofkleasing.ru/]медицинское оборудование в лизинг для юридических лиц[/url]
Лизинг оборудования открывает новые возможности для развития вашей компании. Это одно из наиболее эффективных финансовых решений для модернизации производственных мощностей и оптимизации работы предприятия [url=https://ofkleasing.ru/]оборудование для мойки самообслуживания в лизинг[/url]
Как заказать стриптиз на дом, в лофт, на мальчишник или девичник? Прежде всего выберите сами артиста из каталога и позвоните нам, или наш менеджер самостоятельно подберет Вам хорошего танцора по вашим запросам [url=https://zakazatstriptiz-spb.ru/]Стриптиз[/url]
https://nudifyai.net/
Преимуществами покупки оборудования в лизинг для юридических лиц можно считать: Низкие затраты на получение оборудования в пользование [url=https://chuvashagrolizing.ru/]оборудование для ресторана в лизинг[/url]
Нужна реконструкция деревянного дома в Верее? Наша бригада из опытных строителей из Белоруссии готова воплотить ваши идеи в реальность! Современные технологии, индивидуальный подход, и качество – это наши гарантии. Посетите наш сайт [url=https://rekonstrukciya-doma-v-veree.ru/]реконструкция дома в Верее[/url] и начните строительство вашего уюта прямо сейчас! #БелорусскаяБригада #Шлифовка #Реконструкция #Достройка
Подарок за 100 рублей ребенку и шляпные коробки для цветов оптом.
https://giftbox-3.ru/
Lorem Ipsum has been the industry's standard dummy text <a href="https://instytutts.pl/opvude">https://instytutts.pl/opvude</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://placassolaresmalaga2000.es/vxbrjx">https://placassolaresmalaga2000.es/vxbrjx</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://convido.es/whffid">https://convido.es/whffid</a> of type and scrambled it to make a type specimen book.
https://nudifyai.net/
Lorem Ipsum has been the industry's standard dummy text <a href="https://pubpropaganda.pl/nrvsd">https://pubpropaganda.pl/nrvsd</a> of type and scrambled it to make a type specimen book.
https://rik-estate.ru/
http://remontwasher.ru/
We’ve all made email marketing mistakes: You click send on an email and suddenly your stomach drops. You’ve made a mistake and there’s nothing you can do about it [url=https://david-delavari.shop/blog/content-marketing-essentials-every-marketer-should-know]Content Marketing Essentials Every Marketer Should Know[/url]
https://rik-estate.ru/
In a world where communication is key, having a reliable phone number is essential for both personal and business interactions. However, not everyone needs a permanent number, especially when privacy, convenience, and flexibility are at stake [url=https://www.klamm.de/news/der-leitfaden-zum-kauf-virtueller-handynummern-53N0db4b.html]https://www.klamm.de/news/der-leitfaden-zum-kauf-virtueller-handynummern-53N0db4b.html[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://lacalabrianeifrancobolli.it/ywuzyl">https://lacalabrianeifrancobolli.it/ywuzyl</a> of type and scrambled it to make a type specimen book.
http://nedvizhimostrussa.ru/
In a world where communication is key, having a reliable phone number is essential for both personal and business interactions. However, not everyone needs a permanent number, especially when privacy, convenience, and flexibility are at stake [url=https://www.on-magazine.co.uk/stuff/tech/enhance-your-whatsapp-privacy-with-temporary-virtual-numbers]https://www.on-magazine.co.uk/stuff/tech/enhance-your-whatsapp-privacy-with-temporary-virtual-numbers[/url]
Ciao, new friend! I'm thrilled to meet a potential friend.
It's truly startling, but it seems that I've discovered a site with similar quality to your project <a href=http://metal.tel/>Ferrous metal reclaiming center</a>
Bon voyage, and may your adventures be filled with wonder and delight
<a href=https://sites.google.com/view/discover-glory-play/%D0%B3%D0%BB%D0%B0%D0%B2%D0%BD%D0%B0%D1%8F-%D1%81%D1%82%D1%80%D0%B0%D0%BD%D0%B8%D1%86%D0%B0>Glory Casino</a>
https://redstoneestate.ru/
https://med-blesk.ru
https://nsdentalsolution.com
<a href=https://aoseulado.net/>https://aoseulado.net/</a>
https://redstoneestate.ru/
https://med-blesk.ru
Lorem Ipsum has been the industry's standard dummy text <a href="https://korepetytorek.pl/iekls">https://korepetytorek.pl/iekls</a> of type and scrambled it to make a type specimen book.
https://nsdentalsolution.com
Lorem Ipsum has been the industry's standard dummy text <a href="https://kalexkursy.pl/ozwhuv">https://kalexkursy.pl/ozwhuv</a> of type and scrambled it to make a type specimen book.
https://romashkaclinic.ru
https://psy-medcentr.ru
https://romashkaclinic.ru
https://psy-medcentr.ru
Lorem Ipsum has been the industry's standard dummy text <a href="https://poloneztur.pl/jbeee">https://poloneztur.pl/jbeee</a> of type and scrambled it to make a type specimen book.
I am sure this paragraph has touched all the internet viewers,
its really really fastidious post oon building
up new blog. https://Www.Waste-Ndc.pro/community/profile/tressa79906983/
В сфере азартных игр в интернете особенно важны аспекты защиты данных и обеспечения надежности операций. Это ключевые аспекты, на которых строятся доверие игроков и успешная работа платформ [url=http://j013.koreawebcenter.com/bbs/board.php?bo_table=free&wr_id=681049]http://j013.koreawebcenter.com/bbs/board.php?bo_table=free&wr_id=681049[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://lastresortshop.es/kawagm">https://lastresortshop.es/kawagm</a> of type and scrambled it to make a type specimen book.
Москва Купить Мефедрон? Кристаллы МЕФ?
Где в Москве Купить Мефедрон? САЙТ - https://mephedrone.top/
Hi all! My name is Admin Read:
Ищете место, где ваша безопасность важнее всего? Mega зеркало - лучший выбор! Благодаря новейшим технологиям защиты и удобному дизайну интерфейса <a href=https://xn--megab-mdb.com>mega</a> гарантирует конфиденциальность ваших данных. Пройдите простую регистрацию и изучите широкий выбор категорий. Присоединяйтесь к <a href=https://xn--megab-mdb.com>mega</a> уже сегодня и делайте покупки с уверенностью.
mega зеркало:https://xn--megab-mdb.com
Lorem Ipsum has been the industry's standard dummy text <a href="https://u-rumcajsa.pl/kfpds">https://u-rumcajsa.pl/kfpds</a> of type and scrambled it to make a type specimen book.
<a href=https://seo-7.ru/audit-sajta/>комплексный аудит сайта москва</a>
https://akkred-med.ru
В сфере азартных игр в интернете особенно важны аспекты защиты данных и обеспечения надежности операций. Это ключевые аспекты, на которых строятся доверие игроков и успешная работа платформ [url=http://verkehrsknoten.de/index.php/forum/sozialvorschriften/91153-1win#92117]http://verkehrsknoten.de/index.php/forum/sozialvorschriften/91153-1win#92117[/url]
https://akkred-med.ru
Lorem Ipsum has been the industry's standard dummy text <a href="https://reneborg.dk/tcmyir">https://reneborg.dk/tcmyir</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://mobilwiz.dk/aefomdj">https://mobilwiz.dk/aefomdj</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://mvdesk.in/bfezc">https://mvdesk.in/bfezc</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://blogn97.pl/tgtsx">https://blogn97.pl/tgtsx</a> of type and scrambled it to make a type specimen book.
1win - относительно Молодое виртуальное казино, которое принадлежит компании MFI investments. В перечень предлагаемых услуг входят: ставки на спорт, киберспорт, тв программы, а также подборка совершенных игровых автоматов и присоединение к игровым столам с картами [url=http://torgteh-rzn.ru/index.php?option=com_k2&view=itemlist&task=user&id=11739]http://torgteh-rzn.ru/index.php?option=com_k2&view=itemlist&task=user&id=11739[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://kroatiereis.nl/qqvefzy">https://kroatiereis.nl/qqvefzy</a> of type and scrambled it to make a type specimen book.
<a href=https://www.instagram.com/asiapsiholog_family/>https://www.instagram.com/asiapsiholog_family/</a>
подвесной потолок армстронг <a href=https://armstrong-ceiling24.ru/>https://armstrong-ceiling24.ru/</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://lastresortshop.es/wayzs">https://lastresortshop.es/wayzs</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://pawslo.pl/jhiim">https://pawslo.pl/jhiim</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://ecootechnologies.in/djqtyy">https://ecootechnologies.in/djqtyy</a> of type and scrambled it to make a type specimen book.
Множество пользователей активно ищут удобные и доступные способы развлечения. Это привело к повышению популярности различных онлайн-сервисов [url=http://www.apicarrara.it/modules.php?name=Journal&file=display&jid=4341]http://www.apicarrara.it/modules.php?name=Journal&file=display&jid=4341[/url]
Common mistakes to avoid in the Aviator Game include:
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin purchase</a>
Hi all! My name is Admin Read:
Устали от обыденных покупок в Интернете? Mega зеркало предлагает нечто иное! Благодаря выбору товаров и инновационным функциям <a href=https://xn--megab-mdb.com>mega тор</a> гарантирует, что вы найдете именно то, что вам нужно. Пройдите простую регистрацию и изучите широкий выбор категорий. Присоединяйтесь к <a href=https://xn--megab-mdb.com>mega at</a> сегодня и делайте покупки с удовольствием.
mega ссылка тор:https://xn--megab-mdb.com
Lorem Ipsum has been the industry's standard dummy text <a href="https://maaximizate.es/idafjz">https://maaximizate.es/idafjz</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://tugasmas.es/ukwzc">https://tugasmas.es/ukwzc</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://chamaviva.pt/aypapfw">https://chamaviva.pt/aypapfw</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://osteriagattobianco.it/stzag">https://osteriagattobianco.it/stzag</a> of type and scrambled it to make a type specimen book.
[url=https://pin-up-casino-sv.biz]Pin up sv[/url]
Placera ditt spel hos pin up nu - mest prestigeious bookmaker
<a href=https://pin-up-casino-sv.biz>Pinup</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://sps2015.pl/kvwwsvu">https://sps2015.pl/kvwwsvu</a> of type and scrambled it to make a type specimen book.
[url=https://pin-up-casino-ar.biz]Pin up ar[/url]
Place your bet at pin up online - direct prestigious bookmaker
<a href=https://pin-up-casino-ar.biz>Pinup casino</a>
Практический опыт в SEO с 2008 г. подтверждается датой регистрации моего блога, в котором я частенько пишу о своем понимании в продвижении сайтов. Внедряю стратегию SEO, учитывая алгоритмы поисковиков и использую свои технические skills для достижения наилучших результатов [url=https://leadzavod.com/30-blogov-kotorye-dolzhen-chitat-kazhdyj-arbitrazhnik/]https://leadzavod.com/30-blogov-kotorye-dolzhen-chitat-kazhdyj-arbitrazhnik/[/url]
<a href=https://karimmassimov.com/>https://karimmassimov.com/</a>
[url=https://londraaltuoservizio.com/listing/cattedrale-di-san-paolo/?review-submitted=1]karimmassimov.com[/url] d8aa97e
Замечательно, очень забавное мнение
ми пропонуємо для вас рішення великий асортимент виробів, текстильних виробів, [url=https://eurosiz.ua/product-category/rabochaya-obuv/]https://eurosiz.ua/product-category/rabochaya-obuv/[/url] все необхідне для всієї родини в Одесі оптом і в роздріб за обґрунтованою вартістю.
Lorem Ipsum has been the industry's standard dummy text <a href="https://annacarniz.es/vmpvbns">https://annacarniz.es/vmpvbns</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://lotniskoparking24.pl/cnobsai">https://lotniskoparking24.pl/cnobsai</a> of type and scrambled it to make a type specimen book.
game was designed to provide an adrenaline-pumping experience that mimics the thrill of gambling with a twist.
<a href="https://aviatorgamemaxi.com/demo/">aviator demo</a>
The user interface of the Aviator Game is designed to be intuitive and user-friendly. The clean design and easy
<a href="https://aviatorgamemaxi.com/demo/">aviator app</a>
Нашел сайт с интересующей Вас темой.
даже при будущих мам и дам старшего возраста можно найти пару [url=https://bluedogvideo.com/video-distribution/]https://bluedogvideo.com/video-distribution/[/url] стильных женских джинс.
Player reviews and testimonials are overwhelmingly positive, with many praising the game's exciting gameplay and
<a href="https://aviatorgamemaxi.com/demo/">aviator app</a>
Множество пользователей активно ищут удобные и доступные способы развлечения. Это привело к повышению популярности различных онлайн-сервисов [url=http://www.air119.net/bbs/board.php?bo_table=free&wr_id=687513]http://www.air119.net/bbs/board.php?bo_table=free&wr_id=687513[/url]
the social features, and the quality of the user interface.
<a href="https://aviatorgamemaxi.com/demo/">aviator app</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://kreatoretui.pl/aykur">https://kreatoretui.pl/aykur</a> of type and scrambled it to make a type specimen book.
and the player's goal is to cash out before the plane crashes. This simple yet thrilling concept has made it a
<a href="https://aviatorgamemaxi.com/demo/">п»їaviator game</a>
Safety is paramount when playing online games. Players should ensure they are playing on reputable platforms
<a href="https://aviatorgamemaxi.com/demo/">aviator game demo</a>
Бесплатный промокод на скидку, первый и повторный заказ 2024. Промокод на доставку. Акции и скидки. Халява в телеграм [url=https://t.me/megamarket_promokod_skidka]Скидка на повторный заказ[/url]
Unique Features of the Aviator Game
<a href="https://aviatorgamemaxi.com/demo/">aviator game</a>
Обязательно попробуйте обратиться к газон мск, их направление деятельности это газон в рулонах, качество высочайшее
Промоакции и бонусы для игроков 1win Игроки всегда ищут способы увеличить свои шансы на выигрыш. Бонусные предложения и привлекательные акции помогают сделать игру более захватывающей [url=http://rivertravel.net/viewtopic.php?f=30&t=8643]http://rivertravel.net/viewtopic.php?f=30&t=8643[/url]
favorite among online gaming enthusiasts.
<a href="https://aviatorgamemaxi.com/demo/">aviator game demo</a>
<a href=https://new.gruz200.kz/>https://new.gruz200.kz/</a>
Online Platforms Offering the Game
<a href="https://aviatorgamemaxi.com/demo/">aviator game demo</a>
<a href=https://remonttelefonovnow.ru/>ремонт сотовых рядом</a>
Player Reviews and Testimonials
<a href="https://aviatorgamemaxi.com/demo/">aviator demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://samowystarczalnyzakatek.pl/qxhdmq">https://samowystarczalnyzakatek.pl/qxhdmq</a> of type and scrambled it to make a type specimen book.
Наша компания является передовиком производства измерительного обрудования. Уже долгие годы мы производим и обслуживаем датчики температуры, логгеры данных, регистраторы температуры и влажности и термометры. Наше оборудование помогает осуществлять контроль параметров микроклимата в аптеках, на складах, на производствах и в магазинах [url=http://mix-opt.ru/]инклинометр промышленный[/url]
Наша команда уже более 20 лет проектирует, возводит и обслуживает бассейны в Тюмени, Челябинске и Екатеринбурге. Мы используем только современное и проверенное оборудование и материалы. Даем гарантию выполненных работ. Кроме этого, мы являемся официальными поставщиками химии для бассейнов лучших мировых марок [url=http://aqualand11.ru/]Уточнить[/url]
increase the excitement of the game.
<a href="https://aviatorgamemaxi.com/demo/">aviator demo</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://acidmedia.pl/damhgl">https://acidmedia.pl/damhgl</a> of type and scrambled it to make a type specimen book.
Продвижение сайта в поисковых системах Яндекс, Google. Гарантия выполненных работ. Бесплатный аудит сайта [url=https://seo-steam.ru/]Продвижение в Яндекс[/url]
Уже не удивительно, что кондиционеры становятся неотъемлемым элементом наших домов и офисов. Именно поэтому мы рады предложить вам широкий выбор кондиционеров от лучших мировых брендов по доступным ценам в нашем магазине Enter в Кишиневе [url=https://enter.online/ru/klimaticheskaja-tehnika/conditionery/mobilnye]кондиционер напольный[/url]
<a href=https://slothacker62.com/>https://slothacker62.com/</a>
В критические моменты жизни важно, чтобы похоронное бюро было надежным и профессиональным. Наша статья поможет вам разобраться в разнообразии ритуальных услуг в Алматы и выбрать агентство, которое предложит качественное обслуживание по разумной цене [url=https://teletype.in/@funeralservice/funeralprice2]ритуальные услуги цены[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://vastuastro.in/uexrst">https://vastuastro.in/uexrst</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://placassolaresmalaga2000.es/suinsyy">https://placassolaresmalaga2000.es/suinsyy</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://agescimortara1.it/fvvdw">https://agescimortara1.it/fvvdw</a> of type and scrambled it to make a type specimen book.
LGA Long Term Parking: Find secure & affordable options near LaGuardia Airport. Reviews & details to choose the best fit for your trip [url=https://lga-longtermparking.com/]https://lga-longtermparking.com/[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://impertdesign.pl/gjcuu">https://impertdesign.pl/gjcuu</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://tugasmas.es/kbbvfsp">https://tugasmas.es/kbbvfsp</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://lasparrasdemartin.es/lryjd">https://lasparrasdemartin.es/lryjd</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://dpostigo.es/fllfghx">https://dpostigo.es/fllfghx</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://gastroludki.pl/snsin">https://gastroludki.pl/snsin</a> of type and scrambled it to make a type specimen book.
JFK Long Term Parking: Find secure & affordable options near JFK Airport. Reviews & details to choose the best fit for your trip [url=https://jfk-longtermparking.com/]cheapest long term parking jfk airport[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://minimasvalls.es/ogjqtyd">https://minimasvalls.es/ogjqtyd</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://agamagizhan.in/nryhzx">https://agamagizhan.in/nryhzx</a> of type and scrambled it to make a type specimen book.
EWR Long Term Parking: Find secure & affordable options near EWR Airport. Reviews & details to choose the best fit for your trip [url=https://ewr-longtermparking.com/]long term parking in newark[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://coverly.co.za/gxomyys">https://coverly.co.za/gxomyys</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://derivedsolutions.in/ymoru">https://derivedsolutions.in/ymoru</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://mobilitatelx.es/eirmjil">https://mobilitatelx.es/eirmjil</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://onderhoudsbedrijfpeerdeman.nl/lvbcnhx">https://onderhoudsbedrijfpeerdeman.nl/lvbcnhx</a> of type and scrambled it to make a type specimen book.
<a href=https://remonttelefonovhit.ru/>починить телефон</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://mobilwiz.dk/vpiitm">https://mobilwiz.dk/vpiitm</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://stepsman.cfd/lqazi">https://stepsman.cfd/lqazi</a> of type and scrambled it to make a type specimen book.
крім цього ви можете виявити питанням, [url=https://andrushivka.at.ua/forum/34-3541-1#14425]usdt на наличные доллары в Одессе[/url] коли безпосередньо в лише здатний не бути потрібної суми. так само як не опинитися жертвою аферистів?
<a href=https://mos-los.ru/> Услуги ассенизатора по Дмитровскому району</a> от 750р. за 1 куб. Шланги до 100м. Работаем без выходных.
Наш официальный сайт https://mos-los.ru/
User Interface and Design
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin order</a>
Виртуальные карточные и настольные игры также ждут своих поклонников. От блэкджека до покера – испытайте удачу и стратегию https://kran-info.ru/published/pub/273 - https://kran-info.ru/published/pub/273
Experienced players can benefit from more advanced strategies, such as:
<a href="https://safe-buy-ivermectin-online.weebly.com/">cheap ivermectin</a>
<a href=https://remonttelefonovhit.ru/>ремонт сотовых адреса</a>
excitement it brings to the table.
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin buy</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://sangarciafm.es/krsim">https://sangarciafm.es/krsim</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://minimasvalls.es/ngkdash">https://minimasvalls.es/ngkdash</a> of type and scrambled it to make a type specimen book.
С каждым годом растет количество людей, выбирающих этот вид досуга. Онлайн-платформы предлагают не только развлечение, но и шанс испытать удачу http://fin-molitor.com/forum/viewtopic.php?f=2&t=313603 - http://fin-molitor.com/forum/viewtopic.php?f=2&t=313603
Lorem Ipsum has been the industry's standard dummy text <a href="https://gymnasium-ramsloh.de/qgsvq">https://gymnasium-ramsloh.de/qgsvq</a> of type and scrambled it to make a type specimen book.
офис 65 <a href=https://office-mebel-on-msk.ru/>https://office-mebel-on-msk.ru/</a>
С каждым годом растет количество людей, выбирающих этот вид досуга. Онлайн-платформы предлагают не только развлечение, но и шанс испытать удачу http://jung24express.com/bbs/board.php?bo_table=review&wr_id=109806 - http://jung24express.com/bbs/board.php?bo_table=review&wr_id=109806
Lorem Ipsum has been the industry's standard dummy text <a href="https://trajesmotocross.es/bwzttc">https://trajesmotocross.es/bwzttc</a> of type and scrambled it to make a type specimen book.
Откройте для себя топовые онлайн казино с невероятными бонусами и крупными выигрышами!
<a href="http://xn----7sbbpvlzhhf4ftb.xn--p1ai">Лучшие онлайн казино</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://aptekacalcium.pl/umiwere">https://aptekacalcium.pl/umiwere</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://investeringsgronden.nl/xvesz">https://investeringsgronden.nl/xvesz</a> of type and scrambled it to make a type specimen book.
<a href=https://vmenopauze.ru/aptechka/kompyuternaya-tomografiya-vnutrennego-uha-zaglyani-vnutr-s-pomoschyu-tehnologiy.html/>https://vmenopauze.ru/aptechka/kompyuternaya-tomografiya-vnutrennego-uha-zaglyani-vnutr-s-pomoschyu-tehnologiy.html/</a>
The scoring system in the Aviator Game is based on the multiplier at the time of cashing out. The higher the
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin online</a>
https://tezfiles.cc/
the social features, and the quality of the user interface.
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin online</a>
https://www.themoviedb.org/movie/261903-real-gangsters
Lorem Ipsum has been the industry's standard dummy text <a href="https://taskoo.in/tmnsm">https://taskoo.in/tmnsm</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://durgaspa.in/lcssjzz">https://durgaspa.in/lcssjzz</a> of type and scrambled it to make a type specimen book.
https://www.themoviedb.org/movie/261903-real-gangsters
Lorem Ipsum has been the industry's standard dummy text <a href="https://blogn97.pl/wcyvrgm">https://blogn97.pl/wcyvrgm</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://jainsuperstores.in/woikuu">https://jainsuperstores.in/woikuu</a> of type and scrambled it to make a type specimen book.
that use encryption and secure payment methods to protect their personal and financial information.
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin where to buy</a>
Регистрация на различных ресурсах, форумах или интернет-магазинах сегодня осуществляется только с применением номера телефона. Ранее для этой цели могла использоваться электронная почта, но сегодня правила изменены https://expert-byt.ru/vremennyj-odnorazovyj-nomer-telefona-dlya-sms/ - https://expert-byt.ru/vremennyj-odnorazovyj-nomer-telefona-dlya-sms/
1 куб метр газоблока <a href=https://gazobeton-moskow.ru/>https://gazobeton-moskow.ru/</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://fotoquo.es/bdjpw">https://fotoquo.es/bdjpw</a> of type and scrambled it to make a type specimen book.
Регистрация на различных ресурсах, форумах или интернет-магазинах сегодня осуществляется только с применением номера телефона. Ранее для этой цели могла использоваться электронная почта, но сегодня правила изменены https://wasp.kz/print.php?type=A&item_id=1857 - https://wasp.kz/print.php?type=A&item_id=1857
ensures compatibility across various platforms without the need for additional software downloads.
<a href="https://safe-buy-ivermectin-online.weebly.com/">cheap ivermectin</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://manfred-schnelldorfer.de/gkrmno">https://manfred-schnelldorfer.de/gkrmno</a> of type and scrambled it to make a type specimen book.
Summary of Key Points
<a href="https://safe-buy-ivermectin-online.weebly.com/">cost of ivermectin</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://excellenceevents.in/svcmr">https://excellenceevents.in/svcmr</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://mobilwiz.dk/qtzboz">https://mobilwiz.dk/qtzboz</a> of type and scrambled it to make a type specimen book.
https://www.publico.es/sociedad/publico.es-nancy-fraser-no-dejar-temor-ultraderecha-lleve-feminismo-liberal.html
excitement it brings to the table.
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin purchase online</a>
Excellent blog here! Also your web site loads upp very
fast! What host aare you using? Can I get your affiliate link
to your host? I wish my website loaded up as fast as yours lol https://Odessaforum.Biz.ua/
https://www.publico.es/sociedad/publico.es-nancy-fraser-no-dejar-temor-ultraderecha-lleve-feminismo-liberal.html
Lorem Ipsum has been the industry's standard dummy text <a href="https://palme-net.de/mnefgvw">https://palme-net.de/mnefgvw</a> of type and scrambled it to make a type specimen book.
Bonus bez depozytu lub innymi slowami darmowy bonus to nic innego jak gratis oferowany przez kasyna online dla swoich graczy https://polscekasyno.pl/casino/hitnspin-casino/ - hit n spin opinie
ליווי בחיפה. הן בדיוק הפתרון כאשר מרגישים קצת מדוכאים. והן גם הפתרון כאשר רוצים לחגוג יום מיוחד כמו יום הולדת. הן תמיד בנות הזדמנות לפגוש יופי אקזוטי. הזדמנות לפגוש בחורות ממדינות רחוקות. הזדמנות ליהנות בראש שקט ורגוע. זהו בילוי בלי מחויבות בדיוק כפי <a href=http://sexymule.co.il/>this content</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://spotykids.es/xclkcd">https://spotykids.es/xclkcd</a> of type and scrambled it to make a type specimen book.
<a href=https://mindmeow.com/read-blog/15344>Glory Casino</a>
להעניק עיסוי אירוטי, ועוד הרבה יותר מזה. הן יודעות כיצד לנהוג עם גוף הגבר, היכן לגעת והיכן ללחוץ. נערות ליווי בחיפה מכירות את שיגרום לשניכם להתנשף ולהתרגש מרוב אושר. הנערה יודעת כיצד לפנק את גוף הגבר. היא יודעת היכן לגעת והיכן ללחוץ, והיא תעשה זאת עד <a href=http://www.sexyprice.co.il/>vaw</a>
בדירות דיסקרטיות בחיפה בילוי עם הנערות הוא בילוי שכולו הנאה ורוגע, כך שאתה לא צריך לחשוב יותר מידי ובטח שלא להיות מודאג. כל מה זורמות עם הגבר. אז מה התכניות שלך להערב? להיות לבד או לעשות משהו טוב למען עצמך? נראה לנו שאתה יודע את התשובה! הזמן נערה ותגשים <a href=http://www.sex4sex.co.il/>דירות דיסקרטיות בתל אביב לביקור איכותי</a>
Place Your Bet: Choose the amount you want to bet.
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin cheap</a>
<a href=https://mos-los.ru/> Услуги откачки септиков по Клинскому району</a> от 750р. за 1 куб. Шланги до 100м. Работаем без выходных.
Наш официальный сайт https://mos-los.ru/
Ensuring Safe Gaming Practices
<a href="https://safe-buy-ivermectin-online.weebly.com/">buy ivermectin</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://sanexim.pl/huxdg">https://sanexim.pl/huxdg</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://fokusklinikken.dk/fllopqp">https://fokusklinikken.dk/fllopqp</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://joancanals.es/ehjqm">https://joancanals.es/ehjqm</a> of type and scrambled it to make a type specimen book.
Bonus bez depozytu lub innymi slowami darmowy bonus to nic innego jak gratis oferowany przez kasyna online dla swoich graczy https://polscekasyno.pl/category/bonusy-bez-depozytu/ - casino bonus powitalny bez depozytu
Join <a href=https://www.bass.win/>bass win</a> now and claim your $500 welcome bonus. Play top casino games and win big today!
Lorem Ipsum has been the industry's standard dummy text <a href="https://theofficemakers.in/prunq">https://theofficemakers.in/prunq</a> of type and scrambled it to make a type specimen book.
Dynamic Gameplay: The game's real-time progression keeps players on the edge of their seats.
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin online</a>
Yes, the Aviator Game is compatible with mobile devices. Players can enjoy the game on their smartphones or
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin for sale</a>
Бесплатный сервис по подбору и ведению сделок с недвижимостью в новостройках Москвы и Московской области! Новые квартиры для жизни, дохода или инвестирования от топовых застройщиков с защитой государства https://www.nedvigimost-1.ru/ - ипотека
and fair. These collaborations have helped elevate the Aviator Game to its current status as a beloved online
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin buy</a>
שלו, את הפנטזיות שבוערות בתוכו ואותן הוא רוצה להגשים. כל גבר יכול להגשים את הפנטזיות וזה מה שהוא צריך לעשות בשביל לחיות חיים מרוכז בתחושת הנעימות של הגוף. אז אם בא לך ליהנות הלילה, ולהרגיש חלק מאותו מועדון אקסקלוסיבי של גברים אשר יודעים ליהנות מהחיים, <a href=http://www.livuyescort.co.il/>you could check here</a>
Бесплатный сервис по подбору и ведению сделок с недвижимостью в новостройках Москвы и Московской области! Новые квартиры для жизни, дохода или инвестирования от топовых застройщиков с защитой государства https://www.nedvigimost-1.ru/ - ипотека на выгодных условиях
The ability to play from anywhere, coupled with the variety of games available, has attracted millions of
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin online</a>
$20. The key is to find the right balance between risk and reward.
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin online</a>
נערות אשר יודעות מה הגבר צריך, והן מעניקות לו את הכל במסירות מוחלטת. הבילוי עם הנערות משאיר אחריו תחושה של חופשה נעימה. זיכרון לשכוח מכל הדאגות עם נערות ליווי בתל אביב אז מה לעשות באותם הרגעים בהם אתה מרגיש כי החיים לוחצים עלייך יותר מידי? מה לעשות כאשר <a href=http://strippersclub.co.il/>site</a>
Reputable online platforms offering the Aviator Game are licensed and regulated by governing bodies. This
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin cheap</a>
например, в 2013 году инженер-программист из Лос-Анджелеса (имя не разглашается) выиграл megabucks jackpot - 39 млн. баксов - в [url=https://mamalovesherbargains.com/]marvelbet[/url] Экскалибур.
Player Reviews and Testimonials
<a href="https://safe-buy-ivermectin-online.weebly.com/">where to buy ivermectin</a>
В нашем салоне красоты мы заботимся о ваших волосах, создаем безупречный макияж и подчеркиваем вашу естественную красоту, чтобы вы чувствовали себя уверенно и великолепно каждый день https://ekostil-salon.ru/
Интерьерная печать на самоклеющейся пленке - это процесс создания качественных полноцветных изображений на самоклеющейся пленке, которая может быть наклеена на различные поверхности https://ivolgaphoto.ru/ - печать на пленке интерьерная
Lorem Ipsum has been the industry's standard dummy text <a href="https://onderhoudsbedrijfpeerdeman.nl/pjlixhz">https://onderhoudsbedrijfpeerdeman.nl/pjlixhz</a> of type and scrambled it to make a type specimen book.
Интерьерная печать на самоклеющейся пленке - это процесс создания качественных полноцветных изображений на самоклеющейся пленке, которая может быть наклеена на различные поверхности https://ivolgaphoto.ru/ - интерьерная печать на баннере
game was designed to provide an adrenaline-pumping experience that mimics the thrill of gambling with a twist.
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin for sale</a>
Онлайн-платформа для азартных игр представляет собой разнообразный мир развлечений. Здесь игроки могут наслаждаться множеством опций, которые сделают времяпрепровождение увлекательным и захватывающим http://rudavision.com/bbs/board.php?bo_table=qa&wr_id=11539 - http://rudavision.com/bbs/board.php?bo_table=qa&wr_id=11539
Benefits of Playing Online
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin order</a>
Онлайн-платформа для азартных игр представляет собой разнообразный мир развлечений. Здесь игроки могут наслаждаться множеством опций, которые сделают времяпрепровождение увлекательным и захватывающим https://nlifelab.org/bbs/board.php?bo_table=free&wr_id=2817104 - https://nlifelab.org/bbs/board.php?bo_table=free&wr_id=2817104
Lorem Ipsum has been the industry's standard dummy text <a href="https://alzagaconsulting.es/ahjkhy">https://alzagaconsulting.es/ahjkhy</a> of type and scrambled it to make a type specimen book.
<a href=https://derbayerischelowe.info/>https://derbayerischelowe.info/</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://e-windyk.pl/bxuoymz">https://e-windyk.pl/bxuoymz</a> of type and scrambled it to make a type specimen book.
Variety: Access to a wide range of betting options and gameplay modes.
<a href="https://safe-buy-ivermectin-online.weebly.com/">cheap ivermectin</a>
Кавказская мазь <a href=https://kavkazmaz.ru/>https://kavkazmaz.ru</a> для суставов купить в аптеке. Официальный сайт производителя Кавказской мази от боли в суставах.
заказать сайт под ключ недорого <a href=https://razrabotka-sajtov-pod-klyuch.ru/>https://razrabotka-sajtov-pod-klyuch.ru/</a>
Safety and Fair Play
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin online</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://conceptshop.es/pwjvgjo">https://conceptshop.es/pwjvgjo</a> of type and scrambled it to make a type specimen book.
Aviator Game. Notable names in the industry have contributed their expertise to ensure the game is both engaging
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin order</a>
Чудо Гриб препарат от паразитов <a href=https://chydogrib.ru/>https://chydogrib.ru</a> и ВПЧ. Купите средство по минимальной цене, изучите отзывы и инструкцию по применению.
אליו - בילוי עם בחורה חרמנית וסקסית שרק רוצה לזרום איתו. וזוהי גם הסביבה הנעימה והאינטימית לבילויים מסוג זה. ואמנם אתם לא ליווי זמינות 24 שעות ביממה, והן רק מחכות שתזמין אותן לבית המלון או לדירתך. ושם בין הסדינים הן יעניקו לך בילוי אינטימי מפנק <a href=http://www.sexiline.co.il/>see this</a>
Unique Features of the Aviator Game
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin online</a>
Монтаж системы видеонаблюдения может потребоваться в самых разных ситуациях. Её устанавливают в частных и загородных домах, промышленных предприятиях, офисах, гаражах и многих других помещениях https://uteplimvse.ru/novosti/montazh-sistem-videonablyudeniya-v-kaliningrade.html - https://uteplimvse.ru/novosti/montazh-sistem-videonablyudeniya-v-kaliningrade.html
Lorem Ipsum has been the industry's standard dummy text <a href="https://gymnasium-ramsloh.de/vbadd">https://gymnasium-ramsloh.de/vbadd</a> of type and scrambled it to make a type specimen book.
חוויית אירוח בלתי נשכחת. תוכל להתארח בדירות ממוזגות, נקיות ונעימות בהן מתגוררות נערות קסומות המארחות גברים בביתן. אם בא לך ליהנות מרגעים אינטימיים נעימים במיוחד. יחדיו תוכלו לבלות בנעימים, בלי שאלות ובלי תכניות. פשוט להיהנות מהרגע, להתמסר לכל תחושה <a href=http://www.vipescorts.co.il/>more tips here</a>
For beginners, the key to success in the Aviator Game is to start with small bets and gradually increase as you
<a href="https://safe-buy-ivermectin-online.weebly.com/">ivermectin purchase online</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://dgkservice.it/rdjggi">https://dgkservice.it/rdjggi</a> of type and scrambled it to make a type specimen book.
Lorem Ipsum has been the industry's standard dummy text <a href="https://alpalaphotos.es/impvzlr">https://alpalaphotos.es/impvzlr</a> of type and scrambled it to make a type specimen book.
Article submission websites provide a platform for authors and businesses to publish and promote their content, increasing their online visibility, driving traffic to their websites, and improving their search engine rankings through high-quality backlinks and targeted audience engagement https://globalarticlewarehouse.com
social interaction adds a new layer of excitement and competition to the game, making it more engaging and
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">stromectol without insurance</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://excellenceevents.in/saddchf">https://excellenceevents.in/saddchf</a> of type and scrambled it to make a type specimen book.
There are numerous online communities and forums where Aviator Game enthusiasts can share tips, strategies, and
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">stromectol uk buy</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://childrenfestivalatri.it/ijbop">https://childrenfestivalatri.it/ijbop</a> of type and scrambled it to make a type specimen book.
There are numerous online communities and forums where Aviator Game enthusiasts can share tips, strategies, and
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">order stromectol 12 mg</a>
Мазь для суставов <a href=https://sustalits.ru/>https://sustalits.ru</a> заказать онлайн.
Эта компания предоставляет услуги аварийного вскрытия замков в Москве и готова помочь в любое время суток http://vskrytie-zamkov-moskva.su
Overview of the Aviator Game Experience
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">Stromectol kaufen</a>
Эта компания предоставляет услуги аварийного вскрытия замков в Москве и готова помочь в любое время суток http://vskrytie-zamkov-moskva.su
game was designed to provide an adrenaline-pumping experience that mimics the thrill of gambling with a twist.
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">stromectol generic</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://blogn97.pl/lczfjjs">https://blogn97.pl/lczfjjs</a> of type and scrambled it to make a type specimen book.
Looking for a thrilling gaming experience without spending a dime? Discover the excitement of a https://getb8.us/ - slot machine free, where you can enjoy your favorite games and win big without risking your hard-earned money!
plane crashes, making it a game of both luck and timing. This dynamic gameplay keeps players engaged and coming
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">stromectol tablet</a>
One of the top Bitcoin mixers, Cryptomixer is known for being dependable and quick, which is essential if you want to keep your money safe from https://bitcoinmix.cx/ - Bitcoin Mixer
the social features, and the quality of the user interface.
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">cost of stromectol medication</a>
One of the top Bitcoin mixers, Cryptomixer is known for being dependable and quick, which is essential if you want to keep your money safe from https://bitcoinmix.cx/ - Bitcoin Mixer
Evolution and Technological Advancements
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">stromectol</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://marchstudio.pl/cfgri">https://marchstudio.pl/cfgri</a> of type and scrambled it to make a type specimen book.
You are credited with 123 Free Spins in the game Gonzo's Quest. Promotions in GonzoCasino 200% to your deposit – Min. deposit 50 $ / Bonus size 200% https://gonzo-casino.pl/ - gonzo kasyno
Lorem Ipsum has been the industry's standard dummy text <a href="https://alpalaphotos.es/vwzxhch">https://alpalaphotos.es/vwzxhch</a> of type and scrambled it to make a type specimen book.
Inter Miami <a href=https://usa.intermiami-ar.com/>https://usa.intermiami-ar.com</a> is a professional soccer club based in Miami, founded by David Beckham in 2018.
Social Elements: Options for multiplayer gameplay and chat features enhance the social experience.
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">buy cheap stromectol</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://impertdesign.pl/owvnrvz">https://impertdesign.pl/owvnrvz</a> of type and scrambled it to make a type specimen book.
Gonzo Casino offers an incredible 123 Free Spins with no deposit required on Gonzos Quest from NetEnt when you sign up for a new player account https://gonzo-casino.pl/123-darmowe-spiny/ - gonzo casino 123 free spins
20 Best Onlyfans Pornstar Websites Taking The Internet By Storm
Most popular Pornstars
Gonzo Casino offers an incredible 123 Free Spins with no deposit required on Gonzos Quest from NetEnt when you sign up for a new player account https://gonzo-casino.pl/ - gonzo kasyno
become more comfortable with the gameplay. Observing patterns and understanding the timing of the plane's ascent
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">price of ivermectin tablets</a>
Слимофор <a href=https://slymofor.ru/>https://slymofor.ru</a> инновационное средство для быстрого похудения.
favorite among online gaming enthusiasts.
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">Buy stromectol pills</a>
<a href=https://derglaube.online/>https://derglaube.online/</a>
advances, players can expect even more exciting features and enhancements to the gameplay experience.
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">stromectol online bestellen</a>
All new players that register via our provided link will receive a no deposit bonus from Fountain Casino. There is a chance to claim €$15 free money https://fontan-casino.pl/ - fontan-casino
Lorem Ipsum has been the industry's standard dummy text <a href="https://eduerp4u.in/jtofs">https://eduerp4u.in/jtofs</a> of type and scrambled it to make a type specimen book.
How to Play the Aviator Game
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">Buy stromectol pills</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://liftex.es/voqrdp">https://liftex.es/voqrdp</a> of type and scrambled it to make a type specimen book.
Online casino games have surged in popularity due to their convenience and the immersive experience they offer.
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">stromectol price</a>
Различаться смогут только виды ставок: против [url=https://pin-up-slot02.win/]pinup казино[/url] или против рядовых участников игры. в онлайн казино белоруссии доступны различные типы азартных развлечений, но многие из них показали себя особенно популярными среди клиентов.
that use encryption and secure payment methods to protect their personal and financial information.
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">purchase oral stromectol</a>
environment for players to enjoy the game. Some popular platforms include [Casino Name], [Casino Name], and
<a href="https://cs.astronomy.com/members/buystromectol-6mg-online-without-prescription/default.aspx">where can i buy oral stromectol</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://grupo92.es/owtwzgu">https://grupo92.es/owtwzgu</a> of type and scrambled it to make a type specimen book.
Mostbet, a globally recognized sports betting operator, is now fully accessible to Bangladeshi players. Operating under a Curacao gaming license, Mostbet offers a secure and reliable platform for betting on a wide range of sports https://siamfreestyle.com/ - mostbet
В современном мире цифровые технологии предлагают нам бесконечные возможности. Удобные способы оставаться на связи с тем, что мы любим. Мир развлечений развивается стремительно, предоставляя новые пути для наслаждения любимыми хобби 1вин зеркало http://dianov.bget.ru/forum/thread58878.html#1319253 - http://dianov.bget.ru/forum/thread58878.html#1319253
of course like your webb site however you need to test the spelling on several
off your posts. Several of them are rife with spelling problems and I to find
iit very troublesome to iinform the truth then again I'll certainly come
back again. https://www.waste-Ndc.pro/community/profile/tressa79906983/
Как помочь вашему ребенку выбрать музыкальный инструмент <a href=https://subscribe.ru/group/razgovorchiki-pro-vse/18669624/>https://subscribe.ru/group/razgovorchiki-pro-vse/18669624/</a> для обучения.
Our pharmacy <a href=https://canadarxpharma.com/>https://canadarxpharma.com</a> and international drugstore are committed to providing affordable medications with low-cost shipping and the ease of delivery to your door.
History and Development <a href="https://slotloversonline.com/reviews/wazamba/">wazamba</a>
Purchasing your drugs online <a href=https://pharmacypillsonline.com/>https://pharmacypillsonline.com</a> is one of the modern days’ opportunities that the internet has given us.
Welcome to trusted European Online Pharmacy <a href=https://rxpharmacy-24.com/>https://rxpharmacy-24.com</a> with 24-hour service.
В мире современных технологий и постоянного интернета доступ к любимым игровым платформам стал неотъемлемой частью повседневной жизни. Однако иногда случаются ситуации, когда прямой доступ оказывается невозможным http://xn--jj0bt2i8umnxa.com/bbs/board.php?bo_table=free&wr_id=155890 - http://xn--jj0bt2i8umnxa.com/bbs/board.php?bo_table=free&wr_id=155890
Encontre a melhor maneira de saber a hora exata no Brasil no site <a href=https://horasbrazil2.top/>https://horasbrazil2.top</a>. Nao importa em qual fuso horario voce esteja, nosso site fornece as informacoes mais atuais e precisas sobre o horario. Interface amigavel, acesso rapido e dados exatos - tudo o que voce precisa para estar sempre atualizado. Visite-nos e comprove!
Learn about Shaquille O'Neal's <a href=https://les-lakers-de-los-angeles.shaquille-oneal.com/>https://les-lakers-de-los-angeles.shaquille-oneal.com</a> rise to success with the Los Angeles Lakers, including his three championships and his impact on basketball and culture.
Discover the history <a href=https://france.hockey-fr.com/>https://france.hockey-fr.com</a> of ice hockey in France, from the first clubs to international success and modern achievements.
We explore how television deals <a href=https://amerique.nba-fr.com/>https://amerique.nba-fr.com</a> sponsorships and merchandising have made the NBA one of the most profitable sports leagues in the world.
<a href=https://lebelligerant.io/>https://lebelligerant.io/</a>
LeBron James <a href=https://les-lakers-de-los-angeles.lebron-james.net/>https://les-lakers-de-los-angeles.lebron-james.net</a> from high school star to victory with the Lakers in the 2019-2020 season. Learn about his path to greatness and his impact on basketball and society.
<a href=https://kaputteampel.cc/>https://kaputteampel.cc/</a>
Several key developers and companies have played a significant role in the development and success of the
<a href="https://pro-aviator.com/">play online aviator</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://msizindlela.co.za/qwzfg">https://msizindlela.co.za/qwzfg</a> of type and scrambled it to make a type specimen book.
The LiveChat web app is your all-in-one tool to manage customer interactions from any device without installation. Just open your favorite browser https://in.webcamus.com/ - https://in.webcamus.com/
Discover how medieval <a href=https://france.tennis-fr.com/>https://france.tennis-fr.com</a> monastery tennis became a global sport with Roland Garros in France.
Basketball legend Vince Carter <a href=https://faucons-datlanta.vince-carter.com/>https://faucons-datlanta.vince-carter.com</a> has retired from the Atlanta Hawks, leaving a deep mark on the NBA. Learn about his remarkable career and influence.
Learn about James Harden's <a href=https://clippers-de-los-angeles.james-harden.net/>https://clippers-de-los-angeles.james-harden.net</a> career, from his early days in the NBA to his role with the Los Angeles Clippers and his quest for a championship.
Learn about Anthony Edwards' <a href=https://timberwolves-du-minnesota.anthony-edwards.com/>https://timberwolves-du-minnesota.anthony-edwards.com</a> journey from high school to NBA star and his start with the Minnesota Timberwolves.
Lorem Ipsum has been the industry's standard dummy text <a href="https://yeswemotion.es/cfylhh">https://yeswemotion.es/cfylhh</a> of type and scrambled it to make a type specimen book.
<a href="https://auroracasino.skin">aurora casino</a>
The LiveChat web app is your all-in-one tool to manage customer interactions from any device without installation. Just open your favorite browser https://tr.webcamus.com/ - https://tr.webcamus.com/
LaMelo Ball <a href=https://charlotte-frelons.lamelo-ball.com/>https://charlotte-frelons.lamelo-ball.com</a> went from high school basketball to the NBA with the Charlotte Hornets, overcoming obstacles and finding success.
History and structure of youth football <a href=https://angleterre.football-fr.com/>https://angleterre.football-fr.com</a> in England, training programs, achievements and challenges for further talent development.
Discover the evolution of basketball <a href=https://france.basketball-fr.com/>https://france.basketball-fr.com</a> in France, from its emergence and its infrastructures to the international successes and the influence of French players in the NBA.
How did Lilian Thuram <a href=https://juventus.lilian-thuram.com/>https://juventus.lilian-thuram.com</a> become a Juventus star? Learn about his transition, success and impact on the team in this in-depth look.
Risk Management: Setting limits on how much to bet and when to cash out.
<a href="https://pro-aviator.com/">play online aviator</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://borealstudios.es/nyudf">https://borealstudios.es/nyudf</a> of type and scrambled it to make a type specimen book.
Find out how Jude Bellingham <a href=https://real-madrid.jude-bellingham.net/>https://real-madrid.jude-bellingham.net</a> became a key player for Real Madrid, moving from Birmingham City's academy to the prominence of world football.
Discover the history <a href=https://france.volleyball-fr.com/>https://france.volleyball-fr.com</a> the achievements and prospects for the development of volleyball in France, from the first steps to international triumphs and plans for the future.
If you're looking for a thrilling and unique online casino game, give the Aviator Game a try. Join the millions
<a href="https://pro-aviator.com/">play online aviator</a>
Strasbourg FC is a famous French <a href=https://strasbourg.patrick-vieira.com/>https://strasbourg.patrick-vieira.com</a> football club whose history is closely linked to the legendary footballer Patrick Vieira.
Encontre a melhor maneira de saber a hora exata no Brasil no site horasbrazil2.top. Nao importa em qual fuso horario voce esteja, nosso site fornece as informacoes mais atuais e precisas sobre o horario. Interface amigavel, acesso rapido e dados exatos - tudo o que voce precisa para estar sempre atualizado. Visite-nos e comprove https://horasbrazil2.top
<a href="https://auroracasino.skin">аврора казино
Привет игроки!
Интересуешься самое лучшее онлайн казино ? Заходи на сайт [url=http://80.87.194.225/blogs/1/kakie-nedostatki-imeyutsya-u-populyarnogo-kluba-laki-pari.php]80.87.194.225[/url] Подписывайся на Телеграмм [url=https://t.me/lucky_pari]Лаки Пари[/url] о топ казино сайтов
официальное интернет казино можно
интернет казино
рейтинг казино в россии
самое крутое онлайн казино
лучшие казино на русском
Хороших профитов!
You'll learn about Duncan's <a href=https://san-antonio-spurs.timduncan-fr.com/>https://san-antonio-spurs.timduncan-fr.com</a> contributions to establishing the Spurs as one of the greatest franchises in NBA history.
Platini is a legendary Juventus <a href=https://juventus.michel-platini.com/>https://juventus.michel-platini.com</a> playmaker who won the Golden Boot three times.
Karim Benzema <a href=https://al-ittihad.karim-benzema-fr.net/>https://al-ittihad.karim-benzema-fr.net</a> has left Real Madrid to join Al Ittihad for a record fee of €100 million – the biggest transfer in the history of the Saudi Premier League.
advances, players can expect even more exciting features and enhancements to the gameplay experience.
<a href="https://pro-aviator.com/">play aviator online game</a>
Encontre a melhor maneira de saber a hora exata no Brasil no site horasbrazil2.top. Nao importa em qual fuso horario voce esteja, nosso site fornece as informacoes mais atuais e precisas sobre o horario. Interface amigavel, acesso rapido e dados exatos - tudo o que voce precisa para estar sempre atualizado. Visite-nos e comprove https://horasbrazil2.top
The Aviator Game is a thrilling online casino game that combines chance and strategy. With its unique gameplay,
<a href="https://pro-aviator.com/">play online aviator</a>
Discover Thierry Henry's <a href=https://arsenal.thierry-henry-fr.com/>https://arsenal.thierry-henry-fr.com</a> journey at Arsenal, from his early years to his legendary status, his later struggles and his farewell to the club.
Find out how Olivier Giroud <a href=https://los-angelesfc.olivier-giroud.net/>https://los-angelesfc.olivier-giroud.net</a> went from young talent in France to star of MLS, from Grenoble to Los Angeles FC.
Find out how Eric Cantona <a href=https://manchester-united.eric-cantona.com/>https://manchester-united.eric-cantona.com</a> became a Manchester United legend, his influence on the club, his career, his scandals and his unique style of play.
УК РФ Статья 228.1 <a href=https://statya-228-uk-rf.blogspot.com/2024/01/st-228-228.1-uk-rf.html>Статья 228 УК РФ</a> Незаконные производство, сбыт или пересылка наркотических средств, психотропных веществ или их аналогов.
Fernando Muslera <a href=https://galatasaray.fernandomuslera.net/>https://galatasaray.fernandomuslera.net</a> is one of the important players of Galatasaray. Find out about his contribution to the club's success, his career in Europe and his personal life.
From a young French <a href=https://real-madrid.zinedine-zidane-fr.com/>https://real-madrid.zinedine-zidane-fr.com</a> talent to a Real Madrid legend.
An impressive story that tells the development of Romanian football genius Gheorghe Hagi <a href=https://galatasaray.gheorghe-hagi.net/>https://galatasaray.gheorghe-hagi.net</a> and his extraordinary achievements at the Turkish giant Galatasaray.
Unique Features of the Aviator Game
<a href="https://pro-aviator.com/">aviator</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://mprcode.pl/iopts">https://mprcode.pl/iopts</a> of type and scrambled it to make a type specimen book.
plane crashes, making it a game of both luck and timing. This dynamic gameplay keeps players engaged and coming
<a href="https://pro-aviator.com/">Play Aviator Game</a>
Lorem Ipsum has been the industry's standard dummy text <a href="https://cmedia-design.dk/vlmpwrg">https://cmedia-design.dk/vlmpwrg</a> of type and scrambled it to make a type specimen book.
https://gosznakdublikat.ru/
the opportunity to compete for larger prizes and showcase their skills on a larger stage.
<a href="https://pro-aviator.com/">play game aviator</a>
https://gosznakdublikat.ru/
The fascinating story of Kamit Alt?ntop's <a href=https://galatasaray.hamitaltintop.net/>https://real-madrid.zinedine-zidane-fr.com</a> rise from Germany's youth teams to the legend of Galatasaray and Turkish football.
The brilliant Brazilian's <a href=https://barcelona.ronaldinho-tr.com/>https://barcelona.ronaldinho-tr.com</a> rise to the top of world football with Barcelona in the 2000s.
Christiano Ronaldo <a href=https://real-madrid.robertocarlos-tr.net/>https://real-madrid.robertocarlos-tr.net</a> is a football genius who has become one of the greatest players of our time with his passion, technique and physical prowess.
Social and Community Aspects
<a href="https://pro-aviator.com/">aviator game</a>
Learn how to maximize your results on the popular Sweet Bonanza <a href=https://turkey.sweetbonanza-tr.net/>https://turkey.sweetbonanza-tr.net</a> slot when playing in Turkey. Special tips to conquer peaks in the game.
Slot machines <a href=https://turkey.gatesofolympus-tr.net/>https://turkey.gatesofolympus-tr.net</a> have always attracted the attention of gambling enthusiasts from all over the world, and Gates of Olympus is special among them It has a place.
Kraken darknet - официальная ссылка на зеркало и сайт кракена. Ссылка на кракен онион доступна в любое время! Сделать покупку проще, чем кажется https://krakenpage.com/ - kraken darknet
The fascinating story of how legendary football player Lionel Messi <a href=https://inter-miam.lionelmessi-tr.com/>https://inter-miam.lionelmessi-tr.com</a> opened a new page in his MLS career by leading Inter Miami to the championship.
While the game itself is free to access, playing involves placing bets with real money. Some platforms may offer
<a href="https://pro-aviator.com/">play game aviator</a>
Several key developers and companies have played a significant role in the development and success of the
<a href="https://pro-aviator.com/">aviator</a>
Натяжные потолки <a href=https://stroydim.co.ua/>https://stroydim.co.ua</a> под ключ. Гипоаллергенные, без запаха. Бесплатный замер и визуализация дизайна. Натяжные потолки - всегда выгодные предложения, привлекательные цены
<a href=https://aifon14-ivus.com/iphone-shop/>Apple iPhone 14 купить в Москве</a>, низкие цены на оригинал новый: Iphone Ivus — интернет-магазин оригинальных смартфонов Apple iPhone 14, iPhone 14 Plus, iPhone 14 Pro, iPhone 14 Pro Max.
The gripping story of Stephen Curry's <a href=https://golden-state-warriors.stephencurry-fr.com/>https://golden-state-warriors.stephencurry-fr.com</a> difficult journey to becoming an NBA superstar and the leader of the undefeated Golden State Warriors dynasty.
gama casino сайт <a href=https://barschool.ru/>https://barschool.ru/</a>
For beginners, the key to success in the Aviator Game is to start with small bets and gradually increase as you
<a href="https://pro-aviator.com/">п»їPlay Aviator Game</a>
<a href=https://jadwal-waktu-sholat.online/>jadwal-waktu-sholat.online</a>
The gripping story of Stephen Curry's <a href=https://golden-state-warriors.stephencurry-fr.com/>https://golden-state-warriors.stephencurry-fr.com</a> difficult journey to becoming an NBA superstar and the leader of the undefeated Golden State Warriors dynasty.
Kylian Mbappe <a href=https://real-madrid.kylianmbappe-tr.net/>https://real-madrid.kylianmbappe-tr.net</a> one of the most talented young football players, will join Real Madrid in 2024. He joined. Find out how he quickly rose to the top of world football.
Galatasaray's <a href=https://istanbul.galata-saray.net/>https://istanbul.galata-saray.net</a> path from ups and downs to unconditional dominance in Istanbul. The story of one of Turkey's strongest clubs returning to the top.
winnings.
<a href="https://pro-aviator.com/">play aviator game</a>
<a href=https://telegram-znakomstva.ru/>знакомства в телеграм</a>
F.Bahce <a href=https://istanbul.fenerbahce-haberleri.com/>https://istanbul.fenerbahce-haberleri.com</a> is much more than a football club. It is an integral part of Istanbul's cultural heritage, uniting millions of fans around the world.
Будівельний портал <a href=https://apis-togo.org/>https://apis-togo.org</a> Все про будівництво та ремонт від А до Я.
Найбільший сайт про будівництво <a href=https://d20.com.ua/>https://d20.com.ua</a> пошук замовлень і підрядників, каталог майстрів і бригад, форум про ремонт.
Будівництво та ремонт <a href=https://buildportal.kyiv.ua/>https://buildportal.kyiv.ua</a> будинок та дача, дизайн та нерухомість
<a href=https://mos-los.ru/> Услуги ассенизатора по Клинскому району</a> от 750р. за 1 куб. Шланги до 100м. Работаем без выходных.
Наш официальный сайт https://mos-los.ru/
Найпопулярніший <a href=https://elektrod.com.ua/>https://elektrod.com.ua</a> та авторитетний портал в Україні, присвячений будівництву та заміському життю.
Найбільший портал <a href=https://dsmu.com.ua/>https://dsmu.com.ua</a> з будівництва та ремонту – великий вибір будівельних матеріалів, послуг, оголошень про ремонт від будівельних фірм та приватних фахівців
Будівельний та архітектурний портал <a href=https://inox.com.ua/>https://inox.com.ua</a> все найцікавіше про будівництво та архітектуру - новини архітектури та будівництва, огляди та аналітика, проекти
Будівельний портал <a href=https://furbero.com/>https://furbero.com</a> каталог будівельних компаній, будівельна дошка оголошень, новини, прайс-листи та все про будівництво.
Об'єктивна та різнобічна інформація у сфері будівництва <a href=https://interiordesign.kyiv.ua/>https://interiordesign.kyiv.ua</a> та ремонту, дизайну інтер'єру, ландшафтного дизайну, будинку та дачі.
players globally. The Aviator Game stands out in this crowded market due to its innovative gameplay and the
<a href="https://pro-aviator.com/">play aviator game</a>
navigation enhance the overall gaming experience, making it accessible to players of all skill levels.
<a href="https://pro-aviator.com/">aviator app game</a>
of chance and strategy. Unlike traditional casino games, the Aviator Game involves a virtual plane that ascends
<a href="https://pro-aviator.com/">play online aviator</a>
History and Development
<a href="https://pro-aviator.com/">game aviator online play</a>
Професійний будівельний портал <a href=https://novostroi.in.ua/>https://novostroi.in.ua</a> від будівництва та ремонту, до вибору квітів на дачу.
На порталі представлена ??найкорисніша інформація з будівництва <a href=https://proektsam.kyiv.ua/>https://proektsam.kyiv.ua</a> та ремонту. Будівельні організації, статті та новини будівельної сфери
Будівельний портал <a href=https://newhouse.kyiv.ua/>https://newhouse.kyiv.ua</a> будь-які питання щодо будівництва та ремонту
Все про будівництво <a href=https://poradnik.com.ua/>https://poradnik.com.ua</a> будівельні матеріали, нерухомість, будівельну техніку, дизайн, меблі.
Відповіді на питання щодо ремонту <a href=https://sovetik.in.ua/>https://sovetik.in.ua</a> та будівництва квартири, приватного будинку чи дачі
favorite among online gaming enthusiasts.
<a href="https://pro-aviator.com/">play aviator online game</a>
Поиск горящих туров на море из Москвы лучшие цены, горит 15822 тура http://tourhot.ru/ - поиск горящих туров
Романтикам и любителям казино привет!
Давно изучал сферу дог хаус играть бесплатно и накопил ценную информацию, которую можно прочитать по ссылке [url=http://yatgt.ru/929-rao-ees-ru.html]yatgt.ru[/url] Все актуальные новости на тему 21 как играть в Telegram канале [url=https://t.me/csykaa]Sykaaa [/url]
игровые автоматы бонусы
слот sugar rush на деньги
блэкджек сколько карт
бездепозитный бонус без пополнения
crazy monkey демо версия
Хороших профитов!
increase the excitement of the game.
<a href="https://pro-aviator.com/">play game aviator</a>
Новини будівництва <a href=https://stroyportal.kyiv.ua/>https://stroyportal.kyiv.ua</a> статті та аналіз ринку нерухомості
интим магазин
<a href=http://www.pets-ural.ru/content/forum/viewtopic.php?p=68912>http://www.pets-ural.ru/content/forum/viewtopic.php?p=68912</a>
Будівельний портал <a href=https://start.net.ua/>https://start.net.ua</a> будівельні матеріали, прайс-лист, розцінки на будівельні роботи, будівельні сайти, будівельні фірми, фотографії ремонту квартир, будівельні роботи
Технології будівництва та ремонту <a href=https://vasha-opora.com.ua/>https://vasha-opora.com.ua</a> інформаційно-будівельний портал
Информационный портал о сертификации <a href=http://www.certif-test.ru/>http://www.certif-test.ru</a> и стандартизации продукции и услуг, отказные письма.
дизайн проект бесплатно <a href=https://t.me/r12designhelp>дизайн ванны</a>
<a href=https://yuppe.ru/>https://yuppe.ru/</a>
Safety and Fair Play
<a href="https://pro-aviator.com/">play aviator game</a>
Отказное письмо — официальное подтверждение надлежащего уровня качества и безопасности для людей, животных и экологии https://www.sostav.ru/blogs/30357/41753
Discover key aspects of the future development of the Turkish Super League <a href=https://turkey.superligsitesi.net/>https://turkey.superligsitesi.net</a> including financial stability, infrastructure, youth football and international success.
Efsanevi Turk kulubu Konyaspor, Konya'n?n <a href=https://konya.konyaspor.biz/>https://konya.konyaspor.biz</a> gururu ve Avrupa kupalar?na duzenli olarak kat?lan Turkiye'nin bircok sampiyonudur.
http://sbornik-zakonov.ru/
купить качественные <a href=https://czmicro.cz/>Микронаушник Прага</a> аренда и продажа невидимых нано микронаушников в Праге
Романтикам и любителям казино привет!
Хочу поделиться с вами важной информацией о сайты с бездепозитным бонусом? Переходи на сайт по ссылке: [url=http://goldru.net.ru/2174-sapkowski-su.html]goldru.net.ru[/url] Скорее узнай о bezdepozitni bonus в нашем Телеграм канале [url=https://t.me/csykaa]Сукааа[/url]
рулетка на деньги онлайн с выводом
играть в слот олимпус
баккара игра в карты
crazy monkey играть бесплатно
обезьяна игра автомат играть бесплатно без регистрации
Хороших профитов!
Aftyer looking into a number off the blog articles on your web site,
I honestly like your technique oof blogging.
I saved it to my boolmark website list and will be checking backk soon. Please check out mmy website too and let me know your opinion. https://www.waste-Ndc.pro/community/profile/tressa79906983/
Сертификат соответствия ИСО 9001 – документ, который выдается по результатам экспертной проверки и подтверждает, что система менеджмента качества (СМК) организации соответствует международному стандарту SO 9001 https://www.sostav.ru/blogs/30357/41792
Смелым игрокам посвящается!
Хочу поделиться информацией о казино с бонусом? Переходи на [url=http://b98385gb.beget.tech/2024/07/26/klyuchevye-dostoinstva-izvestnogo-internet-kazino-retro.html]b98385gb.beget.tech[/url] Узнай подробнее о лучшие мировые онлайн казино на [url=https://t.me/NewRetroCasino_promokod]Ретро[/url]
пополнение с карты мир слоты
рейтинг лучшие онлайн казино
топ онлайн казино на реальные деньги в россии
топ казино по выплатам
live казино онлайн
Хороших профитов!
stanze camere in affitto <a href=https://www.stanzeinaffitto.com/>stanze in affitto</a> privati studenti lavoratori uomini donne doppie singole monolocale condivisione a roma milano napoli torino bari palermo bologna annunci subito stanze appartamenti in affitto posti letto coinquilini
Итоговая цена сертификата ИСО 9001 и сроки проведения работ всегда определяются в индивидуальном порядке. Их можно назвать, только когда заказчик предоставит всю необходимую информацию https://www.sostav.ru/blogs/30357/19844
The 10 Most Terrifying Things About Ticktok Pornstars ticktok pornstars
Срочные займы индивидуальным предпринимателям онлайн. Лучшие предложения краудлендинговых платформ по оформлению займов для ИП на развитие бизнеса http://pvcfinougor.ru/ - займ для бизнеса онлайн
<a href=https://cardum.ru/>https://cardum.ru/</a>
кредит под залог покупаемого авто
<a href=http://www.daongil.com/bbs/board.php?bo_table=free&wr_id=306071>http://www.daongil.com/bbs/board.php?bo_table=free&wr_id=306071</a>
В современном бизнес-среде важность виртуальных номеров растёт. Они предлагают гибкость, мобильность и профессиональный имидж. Одним из лидеров на рынке предоставления таких услуг является компания DID Virtual Numbers https://dallasvlwg80359.blogstival.com/49812267/еЏ°ж№ѕи™љж‹џеЏ·з ЃжЋҐж”¶зџдїЎ-ж•°е—ж—¶д»Јйљђз§ЃдїќжЉ¤зљ„ж–°йЂ‰ж‹© - https://dallasvlwg80359.blogstival.com/49812267/еЏ°ж№ѕи™љж‹џеЏ·з ЃжЋҐж”¶зџдїЎ-ж•°е—ж—¶д»Јйљђз§ЃдїќжЉ¤зљ„ж–°йЂ‰ж‹©
Налоговый кодекс Российской Федерации <a href=https://nalogovyykodeks.ru/>https://nalogovyykodeks.ru</a> часть 1 НК РФ ч.1 от 31.07.1998 N 146-ФЗ - действующая редакция со всеми изменениями и дополнениями
Почему при беге болят колени?
<a href=https://e-pochemuchka.ru>https://e-pochemuchka.ru</a>
Цена сертификата соответствия ИСО 9001 всегда рассчитывается индивидуально, так как зависит от ряда факторов: сферы деятельности; количества и местоположения площадок; численности. Сертификат выдается сроком на 3 года, в течение которого организация должна пройти две инспекционные проверки https://teletype.in/@sezdok/stoimost-sertifikata-ISO-9001
Shop the largest selection of balloons <a href=https://buy-balloons-dubai.com/>https://buy-balloons-dubai.com</a> in Dubai. We offer premium balloons for all occasions. Order now and add a touch of fun to your celebration!
Virtual Phone basic information and a brief history. How a company can create a local or international brand with a 1800 number https://waylonuiub54310.59bloggers.com/27833574/жЋўзґўй¦™жёЇи™љж‹џеЏ·з Ѓзє¦дјљзљ„ж–°еҐ‘жњє - https://waylonuiub54310.59bloggers.com/27833574/жЋўзґўй¦™жёЇи™љж‹џеЏ·з Ѓзє¦дјљзљ„ж–°еҐ‘жњє
Узнай где лучше играть в онлайн казино бесплатно на странице
<a href="http://xn----7sbbpvlzhhf4ftb.xn--p1ai">рейтинг онлайн казино</a>
Я изучал билеты ПДД DMV на русском языке на <a href=https://rudmv.com/>https://rudmv.com</a> и получил водительское удостоверение с первого раза в DMV. Очень рекомендую ресурс, коллеги, много кто тоже проходили тесты тут и остались довольны.
Самые популярные игры <a href=https://gamenest.app/>https://gamenest.app</a> для Android, Загрузите самые популярные игры для Android. Скачать топовые игры для вашего Android-устройства и наслаждайтесь эксклюзивным контентом.
Перечень документов, необходимых для оформления кредита на открытие и развитие бизнеса с нуля, зависит от требований банка. В пакет могут входить: • государственный идентификационный номерhttp://mfcfinance.ru/ - кредиты ип на развитие бизнеса
Независимый рейтинг производителей, изготавливающих пластиковые окна ПВХ и деревянные окна со стеклопакетами в Минске и всей Беларуси под заказ https://oknaplan.ru/bitrix/redirect.php?goto=https://4top.by/okna-pvh/ - заказать окна пвх
Цена сертификата соответствия ИСО 9001 всегда рассчитывается индивидуально, так как зависит от ряда факторов: сферы деятельности; количества и местоположения площадок; численности. Сертификат выдается сроком на 3 года https://teletype.in/@sezdok/optimalnaya-cena-sertifikata-iso09001-v-rossii
Сделаем продающие и качественные фото видео материалы для товаров. <a href=https://mp-photo.ru/>фото для маркетплесов</a> Wildberries, Ozon, Avito и других.
Сертификат соответствия ИСО 9001 – документ, который выдается по результатам экспертной проверки и подтверждает, что система менеджмента качества (СМК) организации соответствует международному стандарту ISO 9001 «Системы менеджмента качества. Требования» либо его национальному аналогу ГОСТ Р ИСО 9001 и своевременно совершенствуется https://vc.ru/u/3200429-marev/1137556-sertifikat-iso-9001-chto-eto-takoe-i-dlya-chego-oformlyayut
Paintings, paintings and artists - Gallerix <a href=https://gallerix.org/>https://gallerix.org</a> online museum. The largest and most visited thematic site about painting in Runet.
The newest casino <a href=https://www.reddit.com/r/BestOnlineCasinosHub/comments/1e7t6bo/basswin_login/>basswin</a> invites you to a quick and secure registration process. Start your adventure today and enjoy exclusive gaming benefits!
Future of the Aviator Game
<a href="https://edmanufacture.com/">best ed pills otc</a>
Having read this I believed it was vvery enlightening. I
appreciate you spending some time and effort to put this article together.
I once again find myself personally spending
a lot of time both reading and posting comments. Buut so what, it was
still worth it! https://Www.waste-ndc.pro/community/profile/tressa79906983/
The scoring system in the Aviator Game is based on the multiplier at the time of cashing out. The higher the
<a href="https://edmanufacture.com/">generic ed medication</a>
угги женские оригинал в москве <a href=https://ugg-original-moskva.ru/>угги женские оригинал в москве</a>
<a href=https://skachat-betera.ru/>скачать бетера</a>
Полный список промокодов Яндекс Путешествий на первый заказ и не только на июль 2024 Актуальные скидки, промокоды и кешбэк на отели и авиабилеты на сервисе https://t.me/sale_travels - скидка яндекс путешествия промокод на первый
cash-out perfectly.
<a href="https://edmanufacture.com/">ed pills cheap</a>
Advanced Tips for Experienced Players
<a href="https://edmanufacture.com/">buy ed pills from india</a>
Готовы к изменениям в сфере интернет-торговли? Mega - это платформа, где важны удобство и безопасность! Благодаря новейшим мерам защиты и незамысловатой процедуре регистрации <a href=https://xn--megsb-5wa.com>m3ga</a> обеспечивает удобство при покупках. Ознакомьтесь с широким выбором категорий и воспользуйтесь гибкими способами оплаты. Присоединяйтесь к <a href=https://xn--megsb-5wa.com>m3ga</a> прямо сейчас и переживите будущее онлайн-шопинга.
мега дарк нет: https://mega-active-links.com
Купить биокамин для квартиры – это создать неповторимую атмосферу уюта и тепла у себя в доме https://biocamin.com/product-category/uglovye/ - Угловой биокамин купить
Numerous online casino platforms offer the Aviator Game. These platforms provide a secure and regulated
<a href="https://edmanufacture.com/">cheap erectile dysfunction pills</a>
Магистерские диссертации на заказ в Москве. магистерская диссертация на заказ. Оформление заказа: Заполните форму на нашем сайте, указав все необходимые детали вашей магистерской диссертации http://dissertaciya-dlya-studentov.ru/ - http://dissertaciya-dlya-studentov.ru/
Achraf Hakimi <a href=https://psg.achraf-hakimi-ar.com/>https://psg.achraf-hakimi-ar.com</a> is a key player for Paris Saint-Germain who signed from Inter in 2021.
From the first film in 1996 to his latest stunt 7.6 kilometers in the air, Tom Cruise <a href=https://mission-impossible.tom-cruise-ar.com/>https://mission-impossible.tom-cruise-ar.com</a> has translated the series into a cultural phenomenon of excellence and passion for cinema.
Nisreen Tafesh <a href=https://the-secret-men-club.nesreen-tafesh-ar.com/>https://the-secret-men-club.nesreen-tafesh-ar.com</a> is a pioneering Algerian actress, whose talent has flourished on the film stage, theater and television.
Explore Selena Gomez's <a href=https://calm-down.selena-gomez-ar.com/>https://calm-down.selena-gomez-ar.com</a> rise to success from child star to global pop icon, plus a review of her song "Calm Down" featuring Rema.
Yasmine Abdel Aziz <a href=https://abu-shanab.yasmin-abdulaziz-ar.com/>https://abu-shanab.yasmin-abdulaziz-ar.com</a> is a famous actress from Egypt.
An exploration of Mona Zaki's <a href=https://perfect-strangers.mona-zaki-ar.com/>https://perfect-strangers.mona-zaki-ar.com</a> career and influence, from her film debut to her starring role in Perfect Strangers, the influential Egyptian television series that received worldwide acclaim.
Discover Ghada Abdel Razek's <a href=https://kalemni-shokran.ghada-abdelrazek-ar.com/>https://kalemni-shokran.ghada-abdelrazek-ar.com</a> rise in Egyptian cinema, which culminated in her famous role in "Talk to Me Thank You" and her influence on Arab film.
Gigi Hadid <a href=https://img-models.gigi-hadid-ar.com/>https://img-models.gigi-hadid-ar.com</a> and IMG models are shining examples of success in the fashion world.
мебельный поролон купить в москве в розницу
plane crashes, making it a game of both luck and timing. This dynamic gameplay keeps players engaged and coming
<a href="https://edmanufacture.com/">cost of erectile dysfunction pills</a>
Shakira <a href=https://waka-waka.shakira-ar.com/>https://waka-waka.shakira-ar.com</a> a Colombian star, conquered the world with her unique voice and energetic performances.
From professional diver <a href=https://the-fate-of-the-furious.jasonstatham-ar.com/>https://the-fate-of-the-furious.jasonstatham-ar.com</a> to iconic action star, here's the story of Jason Statham, his influence on Fast & Furious 8, and the evolution of Deckard Shaw's role in the iconic franchise, including key scenes and contributions to the film's success.
Learn about Brad Pitt's <a href=https://fight-club.brad-pitt-ar.com/>https://fight-club.brad-pitt-ar.com</a> early years and his first steps towards success, from his childhood in Missouri to his breakthrough role in Thelma & Louise and his rise to fame in Hollywood.
We explore Diego Maradona's <a href=https://napoli.maradona-ar.com/>https://napoli.maradona-ar.com</a> contribution and influence at Napoli, his successes, cultural influence and legacy as one of the greatest football figures of all time.
<a href=https://bk-melbet-promocode.ru/>мелбет промокод</a>
environment for players to enjoy the game. Some popular platforms include [Casino Name], [Casino Name], and
<a href="https://edmanufacture.com/">where can i buy over the counter erectile dysfunction pills</a>
enjoyable.
<a href="https://edmanufacture.com/">ed meds generic</a>
Устали искать компромисс между удобством и безопасностью? Mega предлагает оптимальное сочетание! Благодаря передовым средствам защиты и инновационному интерфейсу <a href=https://xn--megab-mdb.com>ссылка на мега тор</a> гарантирует комфортные покупки. Наслаждайтесь простой регистрацией и изучайте широкий выбор категорий. Присоединяйтесь к <a href=https://xn--megab-mdb.com>ссылка на мега</a> прямо сейчас и делайте покупки с уверенностью.
https://mega-active-links.com - mega at
Discover how Dior's <a href=https://france.dior-ar.com/>https://france.dior-ar.com</a> marketing strategy, including positioning, advertising campaigns and celebrity collaborations, helps the brand lead the fashion world.
The basic rule of the Aviator Game is straightforward: place a bet, watch the plane take off, and decide when to
<a href="https://edmanufacture.com/">generic ed pills online</a>
From Mohamed Salah <a href=https://arabic.soccer-ar.com/>https://arabic.soccer-ar.com</a> to Al-Ahly and Al-Hilal, we explore the successes and factors driving the development of Arab football on the global stage.
Discover David Beckham's <a href=https://manchester-united.david-beckham-ar.com/>https://manchester-united.david-beckham-ar.com</a> journey from his youth academy debut to winning the treble with Manchester United.
Learn about the great successes achieved by Arab tennis <a href=https://arabic.tennis-ar.com/>https://arabic.tennis-ar.com</a> players on the international scene, their impact on sports in the region, and the factors that contribute to achieving achievements in this sport.
The amazing story <a href=https://karate-kid.jackiechan-ar.com/>https://karate-kid.jackiechan-ar.com</a> of one of action's most influential actors who combined the skills of acrobatics, comedy and karate.
Преимущества заказа магистерской диссертации. Самый ценный и невосполнимый ресурс – это время. Часто в магистратуру идут взрослые люди, обремененные семьей и работой, не имеющие возможности потратить несколько месяцев на то, чтобы искать литературные источники, собирать эмпирические данные и писать текст диссертации http://dissertaciya-dlya-studentov.ru/ - написание диссертации
Nicole Kidman <a href=https://big-little-lies.nicolekidman-ar.com/>https://big-little-lies.nicolekidman-ar.com</a> reaches new creative heights with her unforgettable portrayal of Celeste Wright in Big Little Lies, the pinnacle of her acting career.
Follow Johnny Depp's <a href=https://pirates-of-the-caribbean.johnnydepp-ar.com/>https://pirates-of-the-caribbean.johnnydepp-ar.com</a> incredible journey to fame and recognition as the iconic Captain Jack Sparrow in the popular pirate franchise.
Рейтинг сайтов кейсов CS2/GO <a href=https://ggdrop.cs2-case.org/>https://ggdrop.cs2-case.org</a> заходи и узнай где выше процент отдачи, большие бонусы и бесплатные кейсы за регистрацию.
Evolution and Technological Advancements
<a href="https://edmanufacture.com/">over the counter pills for ed</a>
Готовы открыть для себя мир удобства и разнообразия? Обратите внимание на <a href=https://xn--krakn4-l4a.com>k9.at</a>! Благодаря удобному интерфейсу, который легко понять и разнообразию товаров <a href=https://xn--krakn4-l4a.com>Krn</a> обеспечивает комфортные покупки. Пройдите легкую регистрацию и воспользуйтесь гибкими возможностями оплаты. Присоединяйтесь к <a href=https://xn--krakn4-l4a.com>кракен сайт</a> прямо сейчас, и делайте покупки с легкостью.
vk2.at: https://xn--krakn4-l4a.com
Discover Jennifer Lopez's <a href=https://fan.jennifer-lopez-fr.com/>https://fan.jennifer-lopez-fr.com</a> journey from dancer to international star, and learn about her fan club and philanthropy.
Evolution and Technological Advancements
<a href="https://edmanufacture.com/">buy ed pills cheap online</a>
Un apercu de la transition de Khabib Nurmagomedov <a href=https://ufc.khabib-nurmagomedov-fr.biz/>https://ufc.khabib-nurmagomedov-fr.biz</a> vers le sport professionnel et de ses debuts a l'UFC, ainsi que des victoires et realisations cles de sa carriere.
The fascinating story of Kanye West's <a href=https://graduation.kanye-west-fr.com/>https://graduation.kanye-west-fr.com</a> musical career, from his groundbreaking beginnings to the culmination of his creative evolution in Graduation.
Jake Paul <a href=https://ufc.jake-paul-fr.biz/>https://ufc.jake-paul-fr.biz</a> began his UFC career facing criticism and doubt, but perseverance and training helped him prove his worth.
How did David Beckham's <a href=https://los-angeles-galaxy.david-beckham-fr.com/>https://los-angeles-galaxy.david-beckham-fr.com</a> move to LA Galaxy change American football and MLS? Discover its impact and successes in our detailed analysis.
Ensuring Safe Gaming Practices
<a href="https://edmanufacture.com/">ed pill over the counter</a>
Discover Zlatan Ibrahimovic's <a href=https://manchester-united.zlatan-ibrahimovic-ca.com/>https://manchester-united.zlatan-ibrahimovic-ca.com</a> journey at Manchester United and the history of the club.
Find out how Lille FC <a href=https://france.lille-fr.com/>https://france.lille-fr.com</a> found success, their achievements and the future. Review of key moments in the club's history and strategy.
Find out how Sergio Ramos <a href=https://real-madrid.sergio-ramos-ca.com/>https://real-madrid.sergio-ramos-ca.com</a> started his career at Sevilla and became a Real Madrid player for a record fee. The story of the transition and the first successes.
Diego Maradona <a href=https://barcelona.diego-maradona-ma.com/>https://barcelona.diego-maradona-ma.com</a> was born in 1960 in a poor neighborhood in Buenos Aires, Argentina.
Ищете платформу, которая ответит на ваши разнообразные потребности в покупках? Kraken поможет вам! Благодаря широкому ассортименту категорий и товаров <a href=https://xn--krken4-x0a.com>2kmp</a> гарантирует, что вы найдете именно то, что ищете. Наслаждайтесь легкой регистрацией и безопасными платежами через Bitcoin. Присоединяйтесь к <a href=https://xn--krken4-x0a.com>кракен ссылка зеркало</a> сейчас и испытайте шопинг в лучшем виде.
ссылка на кракен: https://xn--krken4-x0a.com
Окончания прилагательных? «сызнова» ? почему «а» на конце? <a href=https://e-pochemuchka.ru/okonchaniya-prilagatelnyh-syznova-pochemu-a-na-koncze/>https://e-pochemuchka.ru/okonchaniya-prilagatelnyh-syznova-pochemu-a-na-koncze/</a>
Frequently Asked Questions (FAQs)
<a href="https://edmanufacture.com/">male enhancement pills for ed</a>
Vinicius Junior <a href=https://real-madrid.vinicius-junior-se.com/>https://real-madrid.vinicius-junior-se.com</a> a shining star of modern football, has traveled an impressive journey to become a key player for one of the most prestigious clubs in the world: Real Madrid.
Brazilian midfielder Ricardo Isekson dos Santos Leite <a href=https://milan.kaka-ma.com/>https://milan.kaka-ma.com</a> better known as Kaka, began his rise to stardom in 2001 when he joined Internazionale Milano.
Discover Eden Hazard's <a href=https://real-madrid.eden-hazard-se.com/>https://real-madrid.eden-hazard-se.com</a> journey to success and the rich history, triumphs and challenges of Real Madrid.
Luis Suarez <a href=https://inter-miami.luis-suarez-ca.com/>https://inter-miami.luis-suarez-ca.com</a> was born in 1987 in Uruguay and began his professional career with Nacional in 2005
Gareth Bale <a href=https://milan.kaka-ma.com/>https://milan.kaka-ma.com</a> est un footballeur gallois dont le nom est inscrit a jamais dans l'histoire du Real Madrid et de tout le football mondial.
Florian Wirtz <a href=https://bayer04.florian-wirtz-se.com/>https://bayer04.florian-wirtz-se.com</a> was born on May 3, 2003 in Cologne, Germany. From a young age, he demonstrated exceptional footballing abilities, which did not go unnoticed.
Five Killer Quora Answers To British Porn Stars Xxx british porn stars
xxx
Ignoring Patterns: Failing to observe and learn from the game's patterns can reduce your chances of winning.
<a href="https://edmanufacture.com/">generic ed medication</a>
лучшие кредиты под залог авто
<a href=http://www.gasts.de/modules.php?name=Your_Account&op=userinfo&username=iwazicesi>http://www.gasts.de/modules.php?name=Your_Account&op=userinfo&username=iwazicesi</a>
Купить кислородный концентратор в Спб, низкие цены https://o2life.ru/kislorodnoe-oborudovanie/koncentratori-kisloroda/ интернет-магазин
кредит под залог грузового авто
<a href=https://goodtrading.ru/zajm-pod-pts-v-avtolombarde-bystroe-reshenie-finansovyh-problem/>https://goodtrading.ru/zajm-pod-pts-v-avtolombarde-bystroe-reshenie-finansovyh-problem/</a>
become more comfortable with the gameplay. Observing patterns and understanding the timing of the plane's ascent
<a href="https://edmanufacture.com/">generic drugs for ed</a>
займ под залог авто по стс
<a href=https://50baksov.ru/kak-otkryt-avtolombard-poshagovoe-rukovodstvo/>https://50baksov.ru/kak-otkryt-avtolombard-poshagovoe-rukovodstvo/</a>
интим магазин товары цена
<a href=http://virtvladimir.ru/forum/topic/34520>http://virtvladimir.ru/forum/topic/34520</a>
History and Development
<a href="https://edmanufacture.com/">buy ed pill without presciption</a>
Thiago Silva <a href=https://fluminense.thiago-silva-ma.com/>https://fluminense.thiago-silva-ma.com</a> one of modern football's greatest defenders, began his rise to stardom at modest Brazilian club Fluminense.
Самое свежее и актуальное <a href=http://barbie-games.ru/>http://barbie-games.ru</a> новости техники
«Аутстаффинг Рейтинг» – рейтинг агентсв, предоставляющих клиентам услуги трудоустройства и ведения документооборота по иностранным работникам в России. Помогаем бизнесу выбрать лучшего подрядчика https://outstaffing-rating.ru/
Ousmane Dembele <a href=https://psg.ousmane-dembele-ca.com/>https://psg.ousmane-dembele-ca.com</a> was born in the small town of Vernon in France in 1997. From a young age, he showed extraordinary footballing abilities while playing for his hometown's youth teams.
Emiliano Martinez <a href=https://aston-villa.emiliano-martinez-ma.com/>https://aston-villa.emiliano-martinez-ma.com</a> the Argentinian goalkeeper, joined Aston Villa in 2020 and has since , his career took off.
Strategies and Tips
<a href="https://edmanufacture.com/">ed pills no prescription</a>
Deepnude your photos with our easy-to-use <a href=https://deepnudes.app/>https://deepnudes.app</a>, offering high-quality, realistic results. Try DeepNude App for free today!
Усовершенствуйте свой сайт GameCMS, LR WEB или сервер CS 1.6 и CS GO 2 <a href=https://givecode.ru/>https://givecode.ru</a> с нашими уникальными решениями и возможностями для игровых сообществ.
Marquinhos <a href=https://psg.marquinhos-ca.com/>https://psg.marquinhos-ca.com</a> was born on May 14, 1994 in Sao Paulo, Brazil.
Eduardo Camavinga <a href=https://real-madrid.eduardo-camavinga-se.com/>https://real-madrid.eduardo-camavinga-se.com</a> was born in 2002 in Rennes, France.
Moussa Dembele <a href=https://al-lttifaq.moussa-dembele-ma.com/>https://al-lttifaq.moussa-dembele-ma.com</a> was only 8 years old when he put on his football boots for the first time and took to the pitch.
ensures compatibility across various platforms without the need for additional software downloads.
<a href="https://edmanufacture.com/">ed pills generic</a>
<a href=https://www.youtube.com/watch?v=NntCT5Wllvo>воронин владимир викторович</a>
Lautaro Martinez <a href=https://internationale.lautaro-martinez-ca.com/>https://internationale.lautaro-martinez-ca.com</a> a young and talented Argentinian striker, has won the hearts of fans of Internazionale with his genius, his goalscoring performances and his unwavering determination to become one of the best footballers of his generation.
In the world of football <a href=https://liverpool.luis-diaz-ma.com/>https://liverpool.luis-diaz-ma.com</a> where every step is marked by history and achievements, one of the most inspiring stories is the journey of Colombian striker Luis Diaz in the camp of the formidable Liverpool.
Angel Di Maria <a href=https://benfica.angel-di-maria-se.com/>https://benfica.angel-di-maria-se.com</a> was born on February 14, 1988 in the Argentinian city of Rosario.
Mesut Ozil <a href=https://arsenal.mesut-ozil-ca.com/>https://arsenal.mesut-ozil-ca.com</a> began his football career in the youth teams of German club Schalke 04.
https://kupi-buket63.ru/
Bruno Fernandes <a href=https://manchester-united.bruno-fernandes-ma.com/>https://manchester-united.bruno-fernandes-ma.com</a> was born in 1994 in Portugal and was interested in football from an early age.
Online casino VAVADA <a href=https://vavada-regs.ru/>https://vavada-regs.ru/livegames/</a> review of the best slots, live games for money with a dealer, how to top up and withdraw balance. Bonus for new players 100% to the deposit!
рулонные ворота <a href=https://pinoyflixi.su/>https://pinoyflixi.su</a>
Официальный сайт <a href=https://turbodieselservis.ru/>gama казино</a> только настоящие игровые автоматы онлайн. Играй и выигрывай реальные деньги в онлайн казино.
Warren Zaire Emery <a href=https://psg.warren-zaire-emry-se.com/>https://psg.warren-zaire-emry-se.com</a> was born in 2002 in Paris into the family of professional footballer Daniel Emery, who previously played for PSG and the French national team.
Randal Kolo Muani <a href=https://psg.randal-kolo-muani-ma.com/>https://psg.randal-kolo-muani-ma.com</a> 23 years old, striker Eintracht Frankfurt, have attracted the attention of Europe's top clubs thanks to their impressive performances last season
Frenkie de Jong <a href=https://barcelona.frenkie-de-jong-ci.com/>https://barcelona.frenkie-de-jong-ci.com</a> a young Dutch talent, started his football career at the famous Ajax academy.
Pele <a href=https://santos.pele-ci.com/>https://santos.pele-ci.com</a> rightly considered one of the greatest footballers of all time, began his brilliant career at the legendary Brazilian club Santos.
деньги под залог птс авто остается
<a href=http://krasrec.ru/forum/user/201354/>http://krasrec.ru/forum/user/201354/</a>
деньги под птс
<a href=https://www.c-inform.info/news/id/109716>https://www.c-inform.info/news/id/109716</a>
быстро деньги под птс
<a href=http://onlineboxing.net/jforum/user/profile/296813.page>http://onlineboxing.net/jforum/user/profile/296813.page</a>
деньги под залог машины
<a href=https://tj-service.ru/avto/vidy-i-znachenie-kreditov-v-sovremennom-mire>https://tj-service.ru/avto/vidy-i-znachenie-kreditov-v-sovremennom-mire</a>
Real Madrid FC <a href=https://spain.real-madrid-ma.com/>https://spain.real-madrid-ma.com</a> is one of the most successful football clubs in the world. During its more than a hundred years of history, the team from the Spanish capital has grown from a modest local club to a global football giant.
Manchester City Football Club <a href=https://great-britain.manchester-city-ci.com/>https://great-britain.manchester-city-ci.com</a> was founded in 1880 as St. Mark's (West Gorton).
Arsenal Football Club <a href=https://england.arsenal-ci.com/>https://england.arsenal-ci.com</a> one of the most famous and decorated clubs in English football, has traveled a long and winding road to reach its impressive heights.
The Barcelona Football Club <a href=https://spain.barcelona-ma.com/>https://spain.barcelona-ma.com</a> (Barcelona FC) is today one of the the most famous and successful football clubs in the world.
Обзор новых автомобилей <a href=https://www.auto-dd.ru/>https://www.auto-dd.ru</a> 2024-2025 года с ценами и комплектациями, фото и техническими характеристиками
Магнитно-резонансная томография <a href=https://rg62.info/2024/07/20/rentgen-ili-kt-v-chem-ih-otlichie/>https://rg62.info/2024/07/20/rentgen-ili-kt-v-chem-ih-otlichie/</a> (МРТ) в день обращения с экспертным заключением. Современный МРТ аппарат с высокой диагностической точностью в Москве.
Jason Statham <a href=https://abyss.jason-statham-ci.com/>https://abyss.jason-statham-ci.com</a> British actor and former diving champion, has become one of the most recognizable faces of the action film genre
Al-Hilal Football Club <a href=https://saudi-arabia.al-hilal-ci.com/>https://saudi-arabia.al-hilal-ci.com</a> was founded in 1957 by a group of enthusiasts in Riyadh, the capital of Saudi Arabia.
Discover Bruno Fernandes <a href=https://rio-de-janeiro.brunofernandes-br.com/>https://rio-de-janeiro.brunofernandes-br.com</a> success story: how his journey from Rio de Janeiro led to global recognition and triumphs in football.
Discover how Andreson Silva <a href=https://sao-paulo.andersonsilva.net/>https://sao-paulo.andersonsilva.net</a> became an MMA legend, his path to fame and the most exciting fights that made UFC history.
Basic Rules and Objectives
<a href="https://genedmed.com/blog/red-boost/">red boost supplement</a>
From Championship to Premier League <a href=https://crystal-palace.eberechi-eze.com/>https://crystal-palace.eberechi-eze.com</a> How Eberechi Eze achieved success at Crystal Palace, overcoming adversity and injuries.
Discover the story of Magic Johnson <a href=https://brasilia.magicjohnson.biz/>https://brasilia.magicjohnson.biz</a> from his first steps in martial arts to recognition international in Brasilia.
Find out more about Mikel Merino's <a href=https://real-sociedad.mikel-merino.com/>https://real-sociedad.mikel-merino.com</a> professional career and success at Real Sociedad, from his early years to his main victories at the club.
Discover Nuno Mendes' journey <a href=https://manaus.nuno-mendes.com/>https://manaus.nuno-mendes.com</a> from his first years in Portugal to his success at the Brazilian club Manaus, its adaptation and impact on the local community.
A virtual phone number (sometimes also called a virtual phone line) is a telephone number that's not associated with a specific device or piece of hardware https://wpu24.pl/pl/651_artykuly-sponsorowane/22549_jak-zalozyc-tindera-bez-numeru-telefonu-kompleksowy-przewodnik.html - https://wpu24.pl/pl/651_artykuly-sponsorowane/22549_jak-zalozyc-tindera-bez-numeru-telefonu-kompleksowy-przewodnik.html
A royal pet <a href=https://petroyalportrait.com/>https://petroyalportrait.com</a> portrait is a great gift for a dog or cat owner for any occasion. A funny portrait of a pet dressed as a king or a knight will decorate any interior. To order a portrait, all you need is a photo of your pet, and the designers will turn it into a masterpiece.
Descubra como Connor Gallagher <a href=https://chelsea.conor-gallagher.net/>https://chelsea.conor-gallagher.net</a> passou da academia ao time principal do Chelsea para se tornar um sucesso no futebol mundial.
Ronaldinho <a href=https://ronaldinho.pl/>https://ronaldinho.pl</a> Barcelona - Information, transfer news and statistics.
Discover how Romario <a href=https://barcelona.romario-br.com/>https://barcelona.romario-br.com</a> achieved success at FC Barcelona, ??his playing style and personal life, becoming one of the legends of the club and world football.
From initial success at Tottenham <a href=https://manchester-city.kyle-walker.org/>https://manchester-city.kyle-walker.org</a> to victories at Manchester City and a brilliant international career. Learn about Kyle Walker's accomplishments.
Virtual Phone basic information and a brief history. How a company can create a local or international brand with a 1800 number https://techlogitic.net/maximizing-communication-with-phone-number-rentals/ - https://techlogitic.net/maximizing-communication-with-phone-number-rentals/
From humble Brazilian <a href=https://paris-saint-germain.marquinhos-br.com/>https://paris-saint-germain.marquinhos-br.com</a> to PSG captain: the path of Marquinhos for success, his achievements and influence on the club and national team.
Discover Richarlison's journey <a href=https://tottenham-hotspur.richarlison-br.com/>https://tottenham-hotspur.richarlison-br.com</a> from Brazil to Tottenham Hotspur: his early years , career achievements and influence at the club.
The famous Brazilian footballer Robinho <a href=https://real-madrid.robinho-br.com/>https://real-madrid.robinho-br.com</a> his successful career at Real Madrid, career and achievements, as well as important moments of his time at the club.
Discover Pepe's path <a href=https://porto.pepe-br.com/>https://porto.pepe-br.com</a> to success at Porto: since his transfer, his achievements at Real Madrid, until his return and guidance at Porto.
Gabriel Jesus' football talent <a href=https://arsenal.gabriel-jesus.net/>https://arsenal.gabriel-jesus.net</a> has always been obvious, but his path to success in the Arsenal was full of ups and downs.
Malcolm <a href=https://al-hilal.malcolm-br.com/>https://al-hilal.malcolm-br.com</a> was born in a small town in Brazil, where he showed interest and talent in football since he was a child.
Marcelo Vieira <a href=https://fluminense.marcelo-vieira-br.com/>https://fluminense.marcelo-vieira-br.com</a> was born on May 12, 1988 in Rio de Janeiro, Brazil.
Enzo Fernandez <a href=https://chelsea.enzo-fernandez.com/>https://chelsea.enzo-fernandez.com</a> Argentine football player, began his journey to fame at his home club, River Plate.
Angel Di Maria <a href=https://benfica.angel-di-maria.com/>https://benfica.angel-di-maria.com</a> one of the greatest talents in Argentine football, began his path to glory within the walls of the legendary Benfica.
Watch Out: What Star Porn Kayleigh Wanless Is Taking Over And
What Can We Do About It Adult porn star
attentively the ladies’ profiles. Most of them right about “full services” possibilities. It means, if you ladies working in lovely soft lips and tongue. Secondly, such affection gives men feeling like a real master of the situation. And thirdly, it <a href=http://belfant1.top/>belfast escorts</a>
Carlos Alcaraz <a href=https://roland-garros.carlos-alcaraz-br.com/>https://roland-garros.carlos-alcaraz-br.com</a> the young Spanish talent, is making waves at Roland Garros in 2024.
Alexis Mac Allister's <a href=https://liverpool.alexis-mac-allister.com/>https://liverpool.alexis-mac-allister.com</a> rise in the world of football has been simply breathtaking.
Edinson Cavani <a href=https://roma.leandro-paredes-br.com/>https://roma.leandro-paredes-br.com</a> was born in Salto, Uruguay, in 1987.
experience for players.
<a href="https://genedmed.com/blog/red-boost/">red boost</a>
The name Federico Valverde <a href=https://real-madrid.federico-valverde.com/>https://real-madrid.federico-valverde.com</a> has become an integral part of the history of the great football club Real Madrid.
James Rodriguez <a href=https://sao-paulo.james-rodriguez-br.com/>https://sao-paulo.james-rodriguez-br.com</a> was born in Colombia and showed exceptional football skills from a young age.
Solomon Rondon <a href=https://pachuca.salomon-rondon-br.com/>https://pachuca.salomon-rondon-br.com</a> e um atacante venezuelano nascido em 1989 em Maracaibo, Venezuela. Desde cedo Rondon demonstrou talento e paixao pelo futebol.
Luis Diaz <a href=https://liverpool.luis-diaz-brasil.com/>https://liverpool.luis-diaz-brasil.com</a> was born in the small Colombian city of Barrabacas, located on the Caribbean Sea.
lords.lat - cмотреть фильмы и сериалы бесплатно в хорошем HD качестве https://2022.lords.lat/ - tv1.lords.lat
To play the Aviator Game, you need a device with internet access and a web browser that supports HTML5. This
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">online erectile dysfunction pills</a>
Exploring the Enigmatic World In a realm where luck intertwines with skill and strategy, a mysterious playground beckons. Here, seekers of thrills find themselves drawn into a labyrinthine landscape where fortunes can change in the blink of an eye http://nis.com.tn/index.php?option=com_kunena&view=topic&catid=3&id=7013&Itemid=151 - http://nis.com.tn/index.php?option=com_kunena&view=topic&catid=3&id=7013&Itemid=151
Several key developers and companies have played a significant role in the development and success of the
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">best over the counter erectile dysfunction pills</a>
https://pogba.pl - Paul Pogba apk
Paul Pogba Juventus
<a href=https://pogba.pl>Paul Pogba casino</a>
Watch the Plane Ascend: The plane takes off and starts climbing.
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">cheapest ed pills</a>
Женский онлайн-журнал <a href=https://womontrue.ru/>https://womontrue.ru</a> тренды, мода, красота, отношения
Remove clothes from photo <a href=https://undressai.tech/>undress AI</a> online photo editor
advancements have allowed for improved graphics, smoother gameplay, and more interactive features. These
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">best ed pills prescription</a>
купить секс куклу силикон
<a href=https://sex-shop-domzhelanij.ru>https://sex-shop-domzhelanij.ru</a>
https://ronaldinho.pl - ronaldinho
Ronaldinho Golden Ball
<a href=https://ronaldinho.pl>ronaldinho site</a>
Software Requirements
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">best pills for erectile dysfunction</a>
купить секс куклу для взрослых
<a href=https://sexy-dolls-msk.ru>https://sexy-dolls-msk.ru</a>
секс куклы купить 18
<a href=https://sex-shop-domzhelanij.ru>https://sex-shop-domzhelanij.ru</a>
winnings.
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">ordering generic ed pills</a>
Register an account, make a deposit, and navigate to the Aviator Game to start playing.
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">buy generic ed pills</a>
купить секс куклу dolls
<a href=https://sexy-dolls-msk.ru>https://sexy-dolls-msk.ru</a>
купить недорогую силиконовую секс куклу
<a href=https://sex-shop-domzhelanij.ru>https://sex-shop-domzhelanij.ru</a>
cash-out perfectly.
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">cheap generic ed pills</a>
A first-class cryptomixer service <a href=https://kazna.io/>https://kazna.io</a> that anonymizes your cryptocurrency transactions by mixing Bitcoins with others. This BTC mixer is user-friendly and provides a high level of privacy, making it an ideal choice for protecting your digital assets from being tracked. As a Bitcoin mixer, Kazna.io guarantees the security and privacy of your transactions.
Портал <a href=https://darkneturl.com/>https://darkneturl.com</a> для тех, кто ищет доступ к скрытым уголкам Даркнета. На сайте собраны удобные ссылки на анонимные форумы, закрытые магазины и другие ресурсы, недоступные в обычной сети. Здесь вы сможете исследовать Даркнет с максимальной конфиденциальностью и безопасностью.
секс куклы купить 18
<a href=https://sexy-dolls-msk.ru>https://sexy-dolls-msk.ru</a>
improvements have not only made the game more appealing but also more accessible to a wider audience.
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">over counter pills for ed</a>
of chance and strategy. Unlike traditional casino games, the Aviator Game involves a virtual plane that ascends
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">ed pill over the counter</a>
the anticipation building as the plane climbs higher. The key is to cash out at the right moment before the
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">order cheap ed pills online</a>
laptops, tablets, and smartphones. This flexibility allows players to enjoy the game on their preferred device,
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">mens ed pills</a>
For beginners, the key to success in the Aviator Game is to start with small bets and gradually increase as you
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">where to buy over the counter ed pills</a>
Future of the Aviator Game
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">otc erectile dysfunction pills</a>
https://avenue17.ru/
Future of the Aviator Game
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">best ed pills otc</a>
Бесплатный доступ к онлайн курсам, тренингам и книгам. Большой выбор образовательных курсов. Скачивайте бесплатно уже сейчас https://piratehub.site - Скачать онлайн курсы бесплатно
The best website dedicated to footballer Paul Pogba <a href=https://pogba.pl/>https://pogba.pl</a>. The latest news from the world of football.
Лизинг грузовых автомобилей может стать эффективным решением для ИП, которым необходимо расширение или обновление автопарка без значительных единовременных затрат https://1abakan.ru/forum/showthread-60295/ - https://1abakan.ru/forum/showthread-60295/
Game Mechanics
<a href="https://genedmed.com/blog/erectile-dysfunction-medication/">generic ed drugs</a>
What's The Current Job Market For Top Pornstar Only Fans Professionals Like?
top pornstar only fans
Купить звуковое оборудование <a href=https://zvukovoe-oborudovanie12.ru/>https://zvukovoe-oborudovanie12.ru</a> с доставкой. Широкий ассортимент звукового оборудования, который придется по душе любому, даже самому взыскательному покупателю.
The best <a href=https://nudifier.net/>nudifier</a> for realistic photo transformations. Experience AI nudity with our free nudity credits.
Лизинг автотранспорта на выгодных условиях. Приобретайте легковой, коммерческий транспорт или спецтехнику в лизинг с максимальной выгодой. Выбрать автомобиль https://wagner-automobile.ru/ - автомобили в лизинг для ип в москве
players globally. The Aviator Game stands out in this crowded market due to its innovative gameplay and the
<a href="https://genedmed.com/blog/">generic ed drugs</a>
games that stood out from traditional casino offerings. Inspired by the concept of high-risk, high-reward, the
<a href="https://genedmed.com/blog/">best mens ed pills</a>
https://haaland.com.az - Haaland Haaland Erling
Earling Holand best football player
<a href=https://haaland.com.az>Haaland</a>
Common Mistakes to Avoid
<a href="https://genedmed.com/blog/">ed pills no prescription</a>
players globally. The Aviator Game stands out in this crowded market due to its innovative gameplay and the
<a href="https://genedmed.com/blog/">buy cheap ed pills online</a>
Лизинг оборудования для малого бизнеса. Чтобы расширить или модернизировать бизнес потребуется новое оборудование https://bpz-vostok.ru/ - лизинг печатного оборудования
Steam aauthenticator is a option of two-step authentication on steam. It provides additional step privacy your nicknames and passwords. If this option is enabled, Steam Aauthenticator asks you for one-time passcode every time , when you login to Steam on a unfamiliar device https://playsoftzone.com/SteamDesktopAuthenticator - download steam desktop authenticator
Licensing and Regulation
<a href="https://genedmed.com/blog/">where can i purchase generic ed drugs</a>
<a href="https://s1.sosamba-spb2.ru/">Путаны спб </a>
Online Platforms Offering the Game
<a href="https://genedmed.com/blog/">generic ed pills</a>
заказ интимных товаров
<a href=https://www.unlockers.ru/group.php?discussionid=4684>https://www.unlockers.ru/group.php?discussionid=4684</a>
Explore the world of <a href=https://nudify.software/>nudify app</a>, these undress apps uses AI to remove clothes from images.
Latest news <a href=https://vinicius-junior.pl/>https://vinicius-junior.pl</a> on the Vinicius Junior fan page
Discover the extraordinary journey of Kilian Mbappe <a href=https://kylian-mbappe.pl/>https://kylian-mbappe.pl</a> from his humble beginnings to global fame. Learn about his early years, his meteoric rise through the ranks and his impact on and off the pitch.
not, you lose your bet.
<a href="https://genedmed.com/blog/">best pill for ed</a>
https://www.justmedia.ru/news/russiaandworld/gde-pokatatsya-na-snegokhodakh-v-podmoskovye
Scoring System and Winning Criteria
<a href="https://genedmed.com/blog/">low cost ed pills</a>
The latest and most relevant <a href=https://techwiseblog.com/>https://techwiseblog.com</a> news of cryptocurrency, technology and marketing
Архив Ростова <a href=https://gosarchro.ru/>https://gosarchro.ru</a> организация, которая специализируется на сборе, систематизации, изучении и хранении архивных документов.
On com you'll find the latest news, stats, photos of Mesut Ozil <a href=https://mesut-ozil.pl/>https://mesut-ozil.pl</a> and much more. Get the latest news and information about two of football's greatest players, Mesut Ozil
Online Communities and Forums
<a href="https://genedmed.com/blog/">erectile dysfunction pill</a>
Интерес к недвижимости на живописном острове постоянно растёт. Место это привлекает людей, мечтающих об идеальном уголке для отдыха или постоянного проживания http://home.w3solutions.it/w3solutions/index.php?option=com_kunena&view=topic&catid=3&id=6877&Itemid=140#6877 - http://home.w3solutions.it/w3solutions/index.php?option=com_kunena&view=topic&catid=3&id=6877&Itemid=140#6877
taxi from Tivat airport to Tivat <a href=https://tivat-taxi.com/>taxi from Tivat to Budva</a>
taxi tivat Budva cijena <a href=https://budva-taxi.com/>Budva taxi</a>
Lev Yashin <a href=https://lev-yashin.pl/>https://lev-yashin.pl</a> is a legendary Soviet goalkeeper, the only goalkeeper to receive the Golden Ball.
The Aviator Game boasts several unique features that set it apart from other online casino games:
<a href="https://genedmed.com/blog/">cheap erectile dysfunction pills</a>
Al Nasr <a href=https://al-nasr.pl/>https://al-nasr.pl</a> is your source for news and information about Al Nasr Football Club.
Discover the latest Muhammad Ali <a href=https://muhammad-ali.pl/>https://muhammad-ali.pl</a> news, fights, interviews and more. Details about Ali's boxing career, achievements and personal life.
Welcome to the website dedicated to Michael Jordan <a href=https://michael-jordan.pl/>https://michael-jordan.pl</a> basketball legend and symbol of world sports culture.
Welcome to the website about Diego Maradona <a href=https://diego-maradona.pl/>https://diego-maradona.pl</a> Here you will find information about the career and achievements of the legendary footballer, as well as the latest news and unforgettable moments from his life.
Common Feedback and Suggestions
<a href="https://genedmed.com/blog/">generic ed pills</a>
Get the latest information on Khabib Nurmagomedov <a href=https://khabib-nurmagomedov-ufc.org/>https://khabib-nurmagomedov-ufc.org</a> news and fights.
Al-Nasr <a href=https://al-nasr-match.org/>https://al-nasr-match.org</a> football, club, news, results, transfers, match schedule, matches, interviews, players, coaches, team, updates, events, sports.
Discover the latest news, records and achievements of Usain Bolt <a href=https://usain-bolt.org/>https://usain-bolt.org</a>. Learn more about Bolt's sporting life, interviews and speed.
Welcome to the website dedicated to Michael Jordan <a href=https://michael-jordan-nba.org/>https://michael-jordan-nba.org</a> the basketball legend and symbol of global sports culture.
Это внедорожный путеводитель, карта, на которой размещены интересные маршруты и необходимая информация для путешествий на квадроциклах и снегоходах. Вы сможете: Выбрать интересные маршруты и предварительно свершить по ним виртуальное путешествие http://e-k-h.ru/ - покататься на квадроциклах в щёлковском районе
Staying Calm: Keeping a cool head and avoiding impulsive decisions during gameplay.
<a href="https://genedmed.com/blog/">cheap ed generics</a>
можно сказать, это исключение :)
Welcome to our official website <a href=https://inter-miami-cf.org/>https://inter-miami-cf.org</a> Learn about the history, players and latest news of Inter Miami Football Club.
Welcome to the site about Diego Maradona <a href=https://diego-maradona-ar.org/>https://diego-maradona-ar.org</a> Here you can find information about the legendary footballer's career and achievements, as well as the latest news and unforgettable moments of his life.
Discover the latest Muhammad Ali <a href=https://muhammed-ali.org/>https://muhammed-ali.org</a> news, fights, interviews and more. Details about Ali's boxing career, achievements and personal life.
Ronaldinho <a href=https://ronaldinho-gaucho.org/>https://ronaldinho-gaucho.org</a> Barcelona - Information, news and transfer statistics
Call to Action for Players
<a href="https://genedmed.com/blog/">ed pills online canada</a>
The latest news and information about Marcelo <a href=https://ronaldinho-gaucho.org/>https://ronaldinho-gaucho.org</a> on this website! Find Marcelo's biography, career, game stats and more.
Site with the latest news, statistics, photos of Mesut Ozil <a href=https://mesut-ozil.org/>https://mesut-ozil.org</a> and much more. Get the latest news and information about one of the best football players, Mesut Ozil
Latest news and details about the NBA <a href=https://nba-hoje.org/>https://nba-hoje.org</a> in English. Hot events, player transfers and the most interesting events.
Many online platforms host competitive tournaments and events for the Aviator Game. These events offer players
<a href="https://genedmed.com/blog/">cheap erectile dysfunction pills</a>
Хотите сменить ваше гражданство? Мы готовы оказать <a href=https://vk.com/grazhdanstvo_israel>помощь в получении гражданства Израиля</a> в кратчайшие сроки
Leia as ultimas noticias do Counter-Strike 2 <a href=https://major-cs2.com/>https://major-cs2.com</a>, assista aos torneios de maior sucesso e torne-se o melhor do mundo do jogo no site do CS2.
Водительские права категории А и В. Выгодные цены на обучение управлением автомобилем с МКПП и АКПП в автошколе http://avtopoisk43.ru/ - автошкола белорусская
Common feedback from players includes requests for more in-game bonuses, additional multiplayer options, and
<a href="https://genedmed.com/blog/">best erectile dysfunction pills</a>
Интерес к островным приобретениям привлекает всё больше внимания. Спрос на жильё в этих местах растёт с каждым годом https://aben75.cafe24.com/bbs/board.php?bo_table=free&wr_id=508184 - https://aben75.cafe24.com/bbs/board.php?bo_table=free&wr_id=508184
plane ascends, the higher the multiplier. For example, if you bet $10 and cash out at a 2x multiplier, you win
<a href="https://genedmed.com/blog/">best erectile dysfunction pill</a>
услуги seo оптимизация <a href=https://seo-kazan-nedorogo.ru/>https://seo-kazan-nedorogo.ru</a>
продвижение сайта в топ 10 яндекс цена <a href=https://seo-kazan-zakazat.ru/>заказать интернет рекламу</a>
заказать интернет рекламу <a href=https://seokazan43.ru/>seo продвижение сайта сколько стоит</a>
Play <a href=https://www.onlinecasinopokie.com/real-money-pokies/>Real Money Pokies</a> online slots for 2024. Expert reviews, exclusive bonus offers and top-rated real money games.
<a href=https://okna-otk.ru/>https://okna-otk.ru/</a>
Тайна размолвки: что произошло между Земфирой и Ренатой Литвиновой
<a href=https://imzhpro.ru>https://imzhpro.ru</a>
заказать продвижение сайта seo <a href=https://seo-prodvizhenie43.ru/>https://seo-prodvizhenie43.ru</a>
жк купить квартиру от застройщика <a href=https://novostroyka-43.ru/>https://novostroyka-43.ru</a>
Почему латынь до сих пор используется в медицине
<a href=https://insurance-direct.ru>https://insurance-direct.ru</a>
купить квартиру в новостройке от застройщика <a href=https://kvartiravkazani43.ru/>https://kvartiravkazani43.ru</a>
Почему я не загораю в солярии: возможные причины
<a href=https://imzhpro.ru>https://imzhpro.ru</a>
https://www.cosmopolitan.com/es/moda/consejos-moda/a35634628/emprender-como-crear-tu-negocio-marca-moda/
Музыка в магазине: законодательные ограничения, влияние на покупателей и альтернативные варианты
<a href=https://insurance-direct.ru>https://insurance-direct.ru</a>
Starda Casino, или как его также называют на русском — Казино Старда, представляет собой онлайн платформу для азартных игр и ставок на спорт http://casino-starda-official.top/ - старда казино приложение
Китайские, японские и европейские автомобили. Поставки новых и поддержанных из Китая. Доставка до России с растаможкой и полным юридическим сопровождением http://m-cc.de/index.php?title=Chinese_Cars_17 - гибридные автомобили китайские
купить квартиру в казани от застройщика <a href=https://kupitnovostroyku2.ru/>купить квартиру в казани новостройка от застройщика</a>
I advise you to order sildenafil from this site
<a href="https://sildenafiliums.com/">It’s a smart choice to order sildenafil from this pharmacy</a>
Сертификация ISO 9001 свидетельствует о надежности и является эффективным инструментом управления процессами качества для удовлетворения требований потребителей. Поэтому сертифицированные компании имеют решающие преимущества при привлечении новых клиентов и получении тендеров https://vc.ru/u/3200429-marev/1137556-sertifikat-iso-9001-chto-eto-takoe-i-dlya-chego-oformlyayut
https://epsonl210.com
Рейтинг онлайн казино предоставит информацию о том, как проявил себя каждый гэмблинг-сайт за время своей работы, любому, кто интересуется сферой азартных развлечений. Эти данные полезны не только новым пользователям услуг игорных площадок интернета, но и регулярным игрокам https://yu-k.ru - 10 лучших казино-онлайн
Любое мероприятие <a href=https://truelectronica.ru/>https://truelectronica.ru</a> подготовленное профессионалами, всегда будет отличаться особой атмосферой. К организации вечеринок надо подходить основательно, чтобы наполнить эти дни лишь незабываемыми эмоциями. Если же устроить развлекательную программу, обрадуются все!
A collection of 18-25-year olds from around the UK <a href=https://www.scouts.org.uk/volunteers/running-things-locally/recruiting-and-managing-volunteers/role-descriptions/uk-rep-pool/>https://www.scouts.org.uk/volunteers/running-things-locally/recruiting-and-managing-volunteers/role-descriptions/uk-rep-pool/</a> who are trained to represent the UK Scouts at events in the UK and abroad.
American Heart Association <a href=http://strongmaster.net/>http://strongmaster.net</a> By prioritizing these techniques, men can significantly enhance their sexual health, thereby improving their quality of life as they age. If you have concerns regarding your sexual health, it's always a good idea to consult a healthcare professional. Empower yourself; age gracefully, and enjoy a vibrant life!
W swiecie hazardu w Polsce kasyna online zajmuja szczegolne miejsce, oferujac wygodna mozliwosc przetestowania swojego szczescia i wygrania bez wychodzenia z domu https://grykasynonline.pl/
Program bonusowy kazdego nowego kasyna online w Polsce obejmuje roznorodne promocje https://kasynadarmowespiny.pl/
клиника пластической хирургии <a href=https://minasyanplastic.ru/>https://minasyanplastic.ru</a> в Москве , лучшие врачи-хирурги, современные методы, подтяжка и увеличение груди, маммопластика, ринопластика, липосакция. Индивидуальный подход и безопасный результат для здоровья пациента.
жк казань купить квартиру <a href=https://prodazhanovostroyki-43.ru/>купить квартиру от застройщика</a>
Подробный справочник организаций города Астрахань. У нас вы можете найти все необходимые вам адреса и телефоны организаций. Актуальная информация https://astarakan.ru/ - Справочник Астрахани
Hi there, its good article regarding media print, we all be familiar with mdia is a wonderful source
of information. https://bandurart.mystrikingly.com
купить квартиру в казани от застройщика <a href=https://kvartiraspb2.ru/>https://kvartiraspb2.ru</a>
жк купить квартиру от застройщика <a href=https://novayakvartira2.ru/>купить квартиру в новостройке от застройщика</a>
New sway or a well-forgotten old one - find out right now!
https://www.doktorlee.com/бросить-курить/
Натуральные, экологически чистые алтайские продукты питания известны не только в России, но и далеко за ее пределами https://vitam.pro/product-category/pishhevaja-produkcija/ - Алтайские продукты
Seciva <a href=https://seciva.ru/>https://seciva.ru</a> информационный ресурс, всесторонне освещающий рынок партнёрского маркетинга в России и мире: ключевые события, глобальные тренды, компании, определяющие рынок, лица, формирующие тенденции
Сайт The World Press <a href=https://world-press.org/>https://world-press.org</a> специализируется на переводе самых ярких и актуальных материалов зарубежных СМИ на украинский язык. Мы работаем, чтобы каждый украинец имел возможность прочитать достоверные новости и аналитику об Украине и событиях в мире, которые публикуют авторитетные издания, на понятном и родном для них языке.
Profitoffer <a href=https://profitoffer.ru/>https://profitoffer.ru</a> агрегатор новостей и информационный ресурс, всесторонне освещающий рынок партнерского маркетинга в России и мире
Партнерские программы <a href=https://affiliateinsider.ru/>https://affiliateinsider.ru</a> Обзоры, Советы и Возможности заработка в одном месте
Курсовые работы <a href=https://kupit-kursovuyu1.ru/>https://kupit-kursovuyu1.ru</a> на заказ. Выполнение курсовых на заказ быстро, качественно, недорого
купить квартиру в казани от застройщика <a href=https://novostroyka-2.ru/>жк казань купить квартиру</a>
tigrinho demo grГЎtis
<a href="https://tigrinho1.com/">demo tigrinho</a>
<a href=https://operaciya-varikocele.ru/>варикоцеле яичка</a>
Изделия без маркировки изготовителя либо с маркировкой запрещающей аквачистку, принимаются в чистку только с согласия Клиента и обрабатываются по существующим технологиям, без претензий к качеству и товарному виду изделия https://fabrika-himchistki.ru/khimchistka-matrasov/ - химчистка матраса
Заказать написание реферата <a href=https://kupitreferat1.ru/>https://kupitreferat1.ru</a> недорого. Выполнение на заказ - от 3 часов (срочная работа). Закажите реферат по выгодной цене и с гарантиями!
Купить дипломную работу <a href=https://kupitdiplomnuyu1.ru/>https://kupitdiplomnuyu1.ru</a> недорого в Москве. Гарантия уникальности и конфиденциальности. Заказать помощь в написании дипломной работы.
Закажите решение контрольной работы <a href=https://zakazatkontrolnuyu1.ru/>https://zakazatkontrolnuyu1.ru</a> онлайн через фриланс-биржу, цена написания контрольной на заказ.
Заказать решение задач <a href=https://reshitzadachi1.ru/>https://reshitzadachi1.ru</a> для студентов по любому предмету и любой сложности. Соблюдение требований и сроков.
tigrinho aposta
<a href="https://tigrinho1.com/">jogo do tigrinho</a>
tigrinho jogo
<a href="https://tigrinho1.com/">tigrinho demo grГЎtis</a>
Предоставляем возможность купить авто от прямого поставщика по достойной цене. Высококвалифицированные специалисты всегда помогут выбрать именно ту модель автомобиля, которая будет идеально отвечать всем вашим требованиям и пожеланиям http://vykup-auto02.ru - купить новый китайский автомобиль
if after that, everyone is the same nothing will come out, open the menu "Selected account", [url=https://bordercityrocktalk.ca/2022/04/15/if-i-were-dean-i-would-hit-and-not-pass/]https://bordercityrocktalk.ca/2022/04/15/if-i-were-dean-i-would-hit-and-not-pass/[/url], then click "Log in again and again – and log in to your steam account.
Here is the article about a very widespread slot Crazy Time - [b]https://social.acadri.org/read-blog/42478[/b]
demo tigrinho
<a href="https://tigrinho1.com/">tigrinho aposta</a>
Если вы переезжаете, делаете ремонт или не знаете, куда девать несезонное имущество, то аренда склада для хранения вещей решит проблему. Оказываем услуги физическим лицам, предпринимателям и организациям https://self-storage-msk.ru/ - центр хранения вещей
tigrinho demo grГЎtis
<a href="https://tigrinho1.com/">jogo do tigrinho</a>
I was recommended this website by my cousin I am not sure whether this post is written by him as nobody else know such detailed about my trouble You are amazing Thanks.
https://www.oneidauniversity.com/
I was recommended this website by my cousin I am not sure whether this post is written by him as nobody else know such detailed about my trouble You are amazing Thanks.
https://www.sheffieldstateuniversity.com
demo tigrinho
<a href="https://tigrinho1.com/">jogo do tigrinho</a>
Китайские марки автомобилей список, история и подробное описание популярных китайских авто. Рассказываем о плюсах и минусах http://hyundai-voronezh.ru - lixiang l9 2023 цена
demo tigrinho
<a href="https://tigrinho1.com/">jogo do tigrinho demo</a>
заказать такси <a href=https://vyzvat-taxi-gukovo.ru/>номер такси город</a>
дешевое такси <a href=https://taxi-gukovo.ru/>такси город гуково</a>
tigrinho
<a href="https://tigrinho1.com/">tigrinho jogo</a>
tigrinho jogo
<a href="https://tigrinho1.com/">jogo do tigrinho demo</a>
Amazing! Its actually amazing paragraph, I have got much clear
idea about from this paragraph. https://66bb4c96e165c.site123.me/
tigrinho
<a href="https://tigrinho1.com/">tigrinho demo grГЎtis</a>
jogo do tigrinho demo
<a href="https://tigrinho1.com/">tigrinho demo</a>
tigrinho demo
<a href="https://tigrinho1.com/">tigrinho demo grГЎtis</a>
Купон за 2р. предоставляет скидку до 25% на абонементы в сеть фитнес-клубов «Комета». Купон придет на вашу электронную почту и в личный кабинет https://t.me/promokod_kometa - Промокод Комета
Основные причины протечки воды из клапана водонагревателя
<a href=https://imzhpro.ru>https://imzhpro.ru</a>
<a href=https://udalenie-polipov-endometriya.ru/>удаление полипа эндометрия</a>
tigrinho demo
<a href="https://tigrinho1.com/">tigrinho demo grГЎtis</a>
Пищеварительная система человека: от приема пищи до формирования каловых масс
<a href=https://insurance-direct.ru>https://insurance-direct.ru</a>
купить секс куклу в полный рост
<a href=https://sex-shop-domzhelanij.ru>https://sex-shop-domzhelanij.ru</a>
tigrinho
<a href="https://tigrinho1.com/">jogo do tigrinho demo</a>
купить секс куклу dolls
<a href=https://sexshop-domzhelnij.ru>https://sexshop-domzhelnij.ru</a>
купить недорогую силиконовую секс куклу
<a href=https://sexy-dolls-msk.ru>https://sexy-dolls-msk.ru</a>
demo tigrinho
<a href="https://tigrinho1.com/">demo tigrinho</a>
tigrinho jogo
<a href="https://tigrinho1.com/">tigrinho aposta</a>
jogo do tigrinho
<a href="https://tigrinho1.com/">jogo do tigrinho</a>
CVzen <a href=https://cvzen.it/>https://cvzen.it</a> e il servizio leader per la scrittura di CV e il coaching di carriera, scelto da milioni di candidati globalmente. Offriamo supporto completo: redazione di CV e lettere di presentazione, ottimizzazione di LinkedIn e coaching personalizzato per sbloccare il tuo potenziale e nuove opportunita.
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
https://cometa-cas47.ru
Start winning today, get a no deposit gift or free spins of your choice. Only the top best bonuses!
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
взять кредит под залог птс автомобиля <a href=https://avtolombard-novosibirsk.ru>https://avtolombard-novosibirsk.ru</a> кредит в залог автомобиля
кредит под птс грузового <a href=https://avtolombard-pod-pts-nsk.ru>https://avtolombard-pod-pts-nsk.ru</a> займ под залог авто с правом пользования
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
займ под птс без автомобиля <a href=https://credit-pod-zalog-pts.ru>https://credit-pod-zalog-pts.ru</a> кредит под залог покупаемого авто
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
лучший займ под залог авто <a href=https://novosib-zalog-pts.ru>https://novosib-zalog-pts.ru</a> деньги под залог птс новосибирск круглосуточно
деньги под залог птс срочно <a href=https://zaim-pod-pts-nsk.ru>https://zaim-pod-pts-nsk.ru</a> деньги под залог авто остается у вас
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
займ под птс без авто <a href=https://avtolombard-novosibirsk.ru>https://avtolombard-novosibirsk.ru</a> займ под залог птс
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
AI free online nudifier <a href=https://ai-nudify.online/>nudify online</a> undress any photo with AI! Upload a photo to remove clothes and create deep nude images.
взять кредит под залог авто <a href=https://avtolombard-pod-pts-nsk.ru>https://avtolombard-pod-pts-nsk.ru</a> автоломбард новосибирск под залог птс в новосибирске
автоломбард новосибирск под залог птс в новосибирске <a href=https://credit-pod-zalog-pts.ru>https://credit-pod-zalog-pts.ru</a> деньги под птс сразу
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
Элитный эскорт <a href=https://escort-moskva.com/>https://escort-moskva.com</a> в Москва подбор эскорт моделей для сопровождения встреч, а так же для мероприятий любого формата, выставок, ресторанов, театров.
Какие цветы выбрать для свадебного букета
свадебный букет для невесты https://0gorodnik.ru/ - https://0gorodnik.ru/ .
оформить займ под птс <a href=https://novosib-zalog-pts.ru>https://novosib-zalog-pts.ru</a> деньги под птс без машины
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
Для успешной игры важно учитывать несколько ключевых факторов. Изучите правила, понимание которых поможет вам избежать распространённых ошибок. Не забывайте, что каждый игровой опыт уникален, и не стоит полагаться исключительно на удачу http://artem-energo.ru/forums.php?m=posts&q=19259&n=last#bottom - http://artem-energo.ru/forums.php?m=posts&q=19259&n=last#bottom
автоломбард займ птс <a href=https://avtolombard-pod-pts-nsk.ru>https://avtolombard-pod-pts-nsk.ru</a> займ залог авто взять
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
Прокат экскаватора погрузчика в столице
аренда погрузчика цена https://arenda-ekskavatora-pogruzchika197.ru/ - https://arenda-ekskavatora-pogruzchika197.ru/ .
займ залог птс автомобиля <a href=https://credit-pod-zalog-pts.ru>https://credit-pod-zalog-pts.ru</a> займ под залог авто круглосуточно
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
получить деньги под птс <a href=https://novosib-zalog-pts.ru>https://novosib-zalog-pts.ru</a> автоломбард под займ
деньги под залог птс круглосуточно <a href=https://zaim-pod-pts-nsk.ru>https://zaim-pod-pts-nsk.ru</a> кредит под птс автомобиля в новосибирске
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
Создайте свой уникальный шкаф купе на заказ и выделитесь из толпы
шкаф купе на заказ москва https://shkaf-kupe-nazakaz177.ru/ - https://shkaf-kupe-nazakaz177.ru/ .
Качественные услуги по аренде тракторов,
Безопасная аренда тракторов,
Аренда трактора с оперативной доставкой,
Профессиональные услуги по аренде тракторов для фермеров,
Скидки на аренду тракторов для постоянных клиентов,
Качественные услуги аренды строительных тракторов,
Индивидуальный подход к каждому клиенту в аренде трактора,
Профессиональные водители для аренды трактора,
взять трактор в аренду https://arenda-traktora77.ru/ - https://arenda-traktora77.ru/ .
заказать seo оптимизацию сайта <a href=https://process-seo.ru/>https://process-seo.ru</a>
кредит наличными под птс <a href=https://avtolombard-pod-pts-nsk.ru>https://avtolombard-pod-pts-nsk.ru</a> кредит в залог автомобиля
Лучшие цены на ремонт кофемашин в Москве?
срочный ремонт кофемашин https://remont-kofemashin-las.ru/ - сервисный ремонт кофемашин .
деньги в долг под залог машины <a href=https://credit-pod-zalog-pts.ru>https://credit-pod-zalog-pts.ru</a> кредит под залог птс
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
займ залог птс <a href=https://novosib-zalog-pts.ru>https://novosib-zalog-pts.ru</a> кредит под залог машины
Pin Up Casino <a href=https://pinup.biz.az/>https://pinup.biz.az</a> of the most reliable online game casinos in India available for free with a welcome promo.
частный займ под залог авто <a href=https://zaim-pod-pts-nsk.ru>https://zaim-pod-pts-nsk.ru</a> кредит под залог авто документы
Что важно знать перед заказом кухни
кухни на заказ от производителя https://kuhninazakaz177.ru/ - https://kuhninazakaz177.ru/ .
<a href=https://namazit.ru/>https://namazit.ru/</a>
Pin-up Casino <a href=https://pinup.co.az/>https://pinup.co.az</a> is a great choice among players in Azerbaijan and many other countries around the world.
Excitement and fun at Pin Up <a href=https://pinup.com.az/>https://pinup.com.az</a> Azerbayjan online casino!
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
Pin Up (Pin Up) <a href=https://pinup.net.az/>https://pinup.net.az</a> official website - slot machines licensed in Ukraine.
Explore the exciting gaming experience at the renowned Pin Up <a href=https://pinup.info.az/>https://pinup.info.az</a> online casino in Az?rbaycan.
One of the best ways to improve your reaction time in online games is to practice regularly. The more you play, the more familiar you will become with the game mechanics and the faster your reactions will be https://new.express.adobe.com/webpage/XZyrvuAjzOcta - https://new.express.adobe.com/webpage/XZyrvuAjzOcta
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
Hello, my dear buddy. It's been too long, but it's great to see you again.
Seems like a valuable addition to improve your website <a href=http://metal.tel/>Ferrous material baling</a>
Goodbye, and may your day be as amazing as you are
п»їcasibom
<a href="https://sweet-casibom.co/">п»їcasibom</a>
Что такое роза и почему она так ценится, прекрасное растение, воспеваемое многими поэтами и художниками.
Какие бывают виды роз, правила посадки и ухода за розами.
Как роза влияет на человека и его эмоции, роза в религии и мифологии.
Роза как идеальный подарок для любого случая, почему розы так популярны на свадьбах.
Какие свойства и лечебные качества у роз, секреты сбора и хранения розовых лепестков.
про розы https://roslina.ru/ - https://roslina.ru/ .
Latest medicine news. Latest medication developments.
http://motrin4xl.top - buy generic motrin
Patient pill resource. Drug information available.
Dive into the world of gambling fun: Pin Up Casino <a href=https://app-pinup-az.com/>https://app-pinup-az.com</a> detailed review. Open the door to a world of excitement with Pin Up online casino: full review. Pin Up: where excitement and pleasure meet - casino review.
Pin Up Casino <a href=https://apk-pinup-az.com/>https://apk-pinup-az.com</a> Your Road to Gambling Success - Review and Rating. An exclusive look at the Pin Up online platform: play and win.
Pin Up: hot games and exciting tournaments - casino review. The Road to Victory: Understanding Pin Up <a href=https://bonus-pinup-az.com/>https://bonus-pinup-az.com</a> Online Casino. Pin Up Casino: Gambling entertainment at its highest level - review.
Play and win with Pin Up <a href=https://news-pinup-az.com/>https://news-pinup-az.com</a> online casino: full site review. Pin Up casino: secrets of success and big wins - review.
Best games and promotions: Pin Up online <a href=https://info-pinup-az.com/>https://info-pinup-az.com</a> casino review for professionals. Pin Up Casino: Your Road to Success and Gambling Adventures - Review.
Мы предоставляем полный спектр услуг от А до Я, связанных с ремонтом и обслуживанием современных металлопластиковых, деревянных и алюминиевых окон, а так же предоставляем гарантию на все виды работ. По окончанию ремонтных работ выполним уборку https://vk.com/@-99406379-terra-okna-zheleznodorozhnyi-servis-po-obsluzhivaniu-okon?context=author_page_date&ref=author_page - Ремонт окон Железнодорожный
Нет настроения? ?? Узнайте о физиологических и психологических причинах снижения либидо у женщин и вернитесь к яркой жизни! ?? <a href=https://kladovaya-znanij-2.ru/pochemu-net-vozbuzhdeniya-u-zhenschiny/>https://kladovaya-znanij-2.ru/pochemu-net-vozbuzhdeniya-u-zhenschiny/</a> Почему нет возбуждения у женщины
Espelho oficial do Pin up casino. Registre-se no Pin Up <a href=https://pin-up-bets.com/>https://pin-up-bets.com</a> Casino e receba bonus de cassinos online no seu primeiro deposito.
оборудование приточных вентиляционных систем <a href=https://ventilyacionnoe-oborudovanie-msk.ru/>продажа вентиляционного оборудования</a>
Узнайте, почему в Санкт-Петербурге говорят <a href=https://kladovaya-znanij-3.ru/pochemu-paradnaya-a-ne-podezd/>https://kladovaya-znanij-3.ru/pochemu-paradnaya-a-ne-podezd/</a> Почему «парадная», а не «подъезд»?
Лучшие онлайн казино России 2024
<a href="http://xn----8sbfeahwpm1accey2f.xn--p1ai">Лучшие онлайн казино России
</a>
Узнайте, почему Пермский период, единственный в истории, получил название в честь российского региона! Откройте для себя увлекательную историю геологических открытий в Пермском крае! <a href=https://kladovaya-znanij-4.ru/pochemu-permskiy-period-nazyvaetsya-permskim/>https://kladovaya-znanij-4.ru/pochemu-permskiy-period-nazyvaetsya-permskim/</a> Почему Пермский период называется Пермским
New Touch Design <a href=https://ntdmarinegroup.com/>https://ntdmarinegroup.com</a> Expert Services for Your Marine Needs. Our mobile team can come to your boat and do local service anywhere around Florida
Что такое СЕО продвижение сайтов. Продвижение сайта в поисковых системах - это успех бизнеса и его ежедневное развитие. Профессионально настраиваем, ведем и развиваем рекламные кампании в яндекс: ваш сайт 100% заметят http://ok-context.ru/ - частный сео оптимизатор в москве
Узнайте, как правильно пишется <a href=https://kladovaya-znanij-2.ru/pravopisanie-ne-spesha/>https://kladovaya-znanij-2.ru/pravopisanie-ne-spesha/</a> Правописание не спеша
Sildenafil online shopping
<a href="https://sildenafiliums.com/">How do I order sildenafil discreetly</a>
Узнайте, почему у птиц белые какашки! ??? Всё дело в мочевой кислоте и особенностях их организма. Интересные факты о птичьем помёте ждут вас! <a href=https://kladovaya-znanij-3.ru/pochemu-u-ptits-belye-kakashki-sekrety-ptichego-pometa-i-ego-polza/>https://kladovaya-znanij-3.ru/pochemu-u-ptits-belye-kakashki-sekrety-ptichego-pometa-i-ego-polza/</a> Почему у птиц белые какашки: секреты птичьего помета и его польза
Вспоминаем страстный роман Тимати и Алексы на <a href=https://kladovaya-znanij-4.ru/istoriya-otnosheniy-timati-i-aleksy/>https://kladovaya-znanij-4.ru/istoriya-otnosheniy-timati-i-aleksy/</a> История отношений Тимати и Алексы
I’ve ordered sildenafil from here and highly recommend it
<a href="https://sildenafiliums.com/">Sildenafil online purchase</a>
Узнайте, почему нельзя есть перед наркозом и какие опасности таcит в себе прием пищи перед операцией. ?? Подробно об аспирации и рисках для вашего здоровья! <a href=https://kladovaya-znanij-2.ru/pochemu-nelzya-est-pered-narkozom/>https://kladovaya-znanij-2.ru/pochemu-nelzya-est-pered-narkozom/</a> Почему нельзя есть перед наркозом
Who can recommend where to order sildenafil
<a href="https://sildenafiliums.com/">I recommend ordering sildenafil from this trusted pharmacy</a>
Идеальные шкафы купе на заказ в Москве, Шкафы купе на заказ по вашему эскизу в Москве
изготовить шкаф купе на заказ https://shkafy-kupe-na-zakaz77.ru/ - https://shkafy-kupe-na-zakaz77.ru/ .
?? Не дают ипотеку? Узнайте главные причины отказа банков: плохая кредитная история, низкий доход - это не все! ?? Делимся секретами одобрения. <a href=https://kladovaya-znanij-3.ru/prichiny-otkaza-v-ipoteke/>https://kladovaya-znanij-3.ru/prichiny-otkaza-v-ipoteke/</a> Причины отказа в ипотеке
Необходим автомобильный ремонт <a href=https://camper4x4.ru/dlya-chego-mashinu-pokryvayut-voskom/>сайт автосервиса</a> выгодные цены на услуги ремонта авто. Обслуживание автомобилей в профессиональном СТО. Гарантия качества на автомобильный сервис.
Качественны ремонт авто, любые виды работ <a href=https://droidinformer.org/auto-vehicles/uremont-vse-avtoservisy-pod-rukoy/old-version-1.0.15/>автосервисы рядом со мной на карте</a> обращайтесь в проверенный автосервис с гарантией качества и доступными ценами.
I’ve ordered sildenafil from here and highly recommend it
<a href="https://sildenafiliums.com/">I recommend buying sildenafil from this trusted pharmacy</a>
Список бонусов казино https://spasemdetey.ru/spisok-bonusov/
Получите увлекательные вознаграждения при регистрации, депозите и игре. Уникальные предложения для новичков и постоянных игроков. Забирайте свои выигрыши и наслаждайтесь игрой.
Просыпаетесь с болью в желудке? Узнайте о распространенных причинах утреннего дискомфорта и как с ним бороться. Советы и рекомендации для вашего здоровья! <a href=https://kladovaya-znanij-4.ru/pochemu-po-utram-bolit-zheludok/>https://kladovaya-znanij-4.ru/pochemu-po-utram-bolit-zheludok/</a> Почему по утрам болит желудок
Бонус коды, <a href=https://t.me/promokod_kometa/>Промокод Комета</a> рабочие 100% при регистрации на фриспины и кешбэк актуальные на сегодня!
Here is the article forth a particular popular casino trick Dragon Money Point - [b]https://blogs.rufox.ru/~ikozlov/50400.htm[/b]
Multi-platform desktop version of the authenticator, replacing the mobile app steam https://steamauthenticatordesktop.com/ - скачать steam desktop authenticator
Where can I order sildenafil
<a href="https://sildenafiliums.com/">What’s the most recommended way to order sildenafil</a>
Играй на лучших серверах Lineage 2 <a href=https://medium.com/@L2Top/exploring-lineage-2-essence-your-comprehensive-guide-on-l2-top-ru-57b1694d4707>https://medium.com/@L2Top/exploring-lineage-2-essence-your-comprehensive-guide-on-l2-top-ru-57b1694d4707</a> Наслаждайся классическим игровым процессом и борись за власть в мире интерлюда на серверах легендарной MMORPG Lineage 2.
Instantly remove clothes or dresses from photos online with our free <a href=https://aiclothremover.com/>AI clothes remover</a> one click to erase any clothing from any picture with high quality.
https://101-diplom.top/
This is the best place to order sildenafil online
<a href="https://sildenafiliums.com/">What’s the difference between ordering sildenafil and generic versions</a>
Магазин спецодежды <a href=https://specodezhda-krasnodar.ru/>https://specodezhda-krasnodar.ru</a> купить спец одежду в Краснодаре оптом и в розницу. Низкие цены, доставка.
Как заказать товары через интернет-магазин <a href=http://saverussianretail.ru/>http://saverussianretail.ru</a> на рынке «Садовод». Выбираем онлайн по оптовым и розничным ценам.
I recommend ordering sildenafil from this trusted pharmacy
<a href="https://sildenafiliums.com/">Best place to order sildenafil</a>
Студия оказывает полный комплекс работ по созданию и продвижению лендинг пейдж. Предлагаем большой выбор продающих уникальных и шаблонных дизайнов лендинга https://www.makelanding.ru/ - создание лендинга под ключ
The following is a list of white defendants executed for killing a black victim. Executions of white defendants for killing black victims are rare https://mostbet.game/ - racism
I suggest you buy sildenafil from this highly rated site
<a href="https://sildenafiliums.com/">п»їBuy sildenafil online</a>
Deepnude AI can change any photos to naked photos in a few clicks. Check more <a href=https://deepnudeai.info/>Deepnude AI</a> free tools to create deepnude photos.
The Steam Guard Mobile Authenticator is a feature of the Steam Mobile App that provides an additional level of security to your Steam account https://githab.net/Jessecar96/SteamDesktopAuthenticator/ - steam authenticator
Can I order sildenafil without seeing a doctor
<a href="https://sildenafiliums.com/">What’s the best way to order sildenafil online</a>
1 вин можно пополнить с помощью
I guarantee you’ll be satisfied if you order sildenafil from here
<a href="https://sildenafiliums.com/">Order sildenafil without prescription</a>
Steam Desktop Authenticator is your personal guard for your Steam account, offering an increased level of security and convenience. Steam Desktop Authenticator. Desktop version of the Steam authentication mobile app https://githab.net/Jessecar96/SteamDesktopAuthenticator/ - steam desktop authenticator github
lee bet casino <a href=https://lider-potolok.ru/>leebet casino</a>
зеркало казино либет <a href=https://infostroyadvice.ru/>вход lee bet</a>
leebet <a href=https://accessoires-live.ru/>lee bet casino</a>
Толщина панели https://teplovtermo.ru/
Добавить в избранное https://teplovtermo.ru/
Производители плитки:
Клинкерный тип отделки - преимущества https://teplovtermo.ru/
Утепление дома термопанелями проводится следующим образом:
Виды утеплителя:
вход lee bet <a href=https://s-m3.ru/>leebet casino</a>
Букмекерская контора и оператор казино Mostbet <a href=https://mostbetcasinoapk-kz.kz/>https://mostbetcasinoapk-kz.kz</a> в Казахстане предлагает демонстрацию игровых автоматов и краш-игр, а также тысячи мероприятий: ? новые игроки могут получить 4 бездепозитных бонуса и бесплатно побороться за выигрыш.
What is the best site to order sildenafil
<a href="https://sildenafiliums.com/">Purchase sildenafil</a>
Мастерская занимается восстановлением электронной части ABS. ABS является вспомогательной тормозной системой. Вследствие чего является одной из важнейших систем https://monocle.ru/2017/03/1/kuzovnoj-remont-avtomashinyi-osnovnyie-osobennosti/ - снятие обшивки двери
Присоединяйтесь к казино Mostbet.com <a href=https://mostbetregistration-kz.kz/>https://mostbetregistration-kz.kz</a> лучшей букмекерской конторе и казино Казахстана. Зарегистрируйтесь сейчас и получите бонус 150% по промокоду MOSTBET-KZ24!
Mostbet-AZ90 <a href=https://mostbet.prostoprosport.az/>https://mostbet.prostoprosport.az</a> Join the betting platform, get attractive bonuses during registration, take advantage of a wide catalog of casino games, big winnings guaranteed to win + fast withdrawal possible.
- Широкий выбор игр: Техасский Холдем, PLO, PLO-5, Short Deck и т.д.
Проекты домов с коммуникациями и отделкой - доступные цены и отличные планировки. Строительство дома с коммуникациями и отделкой под ключ в Ярославле и Ярославской области https://stroy-dom-yar.ru/ - строительство домов под ключ
<a href=https://trespor.com/>https://trespor.com/</a>
Who can recommend where to order sildenafil
<a href="https://sildenafiliums.com/">I recommend you order sildenafil from this website</a>
Are there age restrictions for ordering sildenafil online
<a href="https://sildenafiliums.com/">What payment methods can I use to order sildenafil</a>
capital of montenegro <a href=https://www.summer-vacation-in-montenegro.com/>Visit Montenegro</a>
qr code generator business card <a href=https://www.benefits-of-qr-business-cards.com/>qr business cards</a>
Джип туры по Крыму <a href=https://м-драйв.рф/tours/pervyj-krymskij/>https://м-драйв.рф/tours/pervyj-krymskij/</a> уникальные маршруты и яркие эмоции. Погрузитесь в увлекательнее приключение вместе с нами. Горные, лесные, подземные экскурсии, джиппинг в Крыму с максимальным комфортом.
Различные функции, которые еще не встречались в других покерных приложениях.
Where do experts recommend ordering sildenafil
<a href="https://sildenafiliums.com/">Can you recommend a reliable vendor to order sildenafil from</a>
Поради для батьків <a href=https://babyrost.com.ua/>https://babyrost.com.ua</a> заходи для дітей, освіти, покупки, організація дитячих свят
Найактуальніші поради <a href=https://agusha.com.ua/>https://agusha.com.ua</a> та рекомендації батькам
Джип туры по Крыму <a href=https://м-драйв.рф/tours/edu-kuda-hochu/>https://м-драйв.рф/tours/edu-kuda-hochu/</a> уникальные маршруты и яркие эмоции. Погрузитесь в увлекательнее приключение вместе с нами. Горные, лесные, подземные экскурсии, джиппинг в Крыму с максимальным комфортом.
Жіночий онлайн журнал <a href=https://feromonia.com.ua/>https://feromonia.com.ua</a> краса, здоров'я жінки, виховання дітей, стосунки
Жіночий портал <a href=https://magiclady.kyiv.ua/>https://magiclady.kyiv.ua</a> сучасна мода, тренд, стиль; корисні поради; секрети гарної фігури
Доброго!
Быстрое изготовление автомобильных номеров с соблюдением всех стандартов. Заказывайте сейчас!
Быстрое изготовление дубликатов номерных знаков на авто. Закажите онлайн и получите быстро!
Более подробно по ссылке - https://gosnomer-msk77.ru
дубликаты номеров
дубликаты гос номеров
сделать номера на машину
https://gosnomer-msk77.ru - дубликат номера автомобиля цена
Удачи!
How can I verify a site before ordering sildenafil
<a href="https://sildenafiliums.com/">Can I track my order of sildenafil online</a>
Онлайн журнал для женщин <a href=https://otnoshenia.net/>https://otnoshenia.net</a> звезды, мода, красота, любовь, гороскопы, психология, дети и здоровье
Самые новые идеи <a href=https://one-lady.com/>https://one-lady.com</a> дизайна ногтей, советы и рекомендации по уходу за ногтями и выполнению маникюра
Женские полезные советы <a href=https://topwoman.kyiv.ua/>https://topwoman.kyiv.ua</a> на темы: мода, стиль, красота, здоровье, дети, дом, мужчины, секс, интим, любовь, отдых
http://www.pokerstars.bg/assist/
Sildenafil online order
<a href="https://sildenafiliums.com/">Sildenafil online shopping</a>
Who can recommend where to order sildenafil
<a href="https://sildenafiliums.com/">Trust me, you should buy sildenafil from this vendor</a>
How much does it cost to order sildenafil
<a href="https://sildenafiliums.com/">You won’t regret ordering sildenafil from this site</a>
интим магазин цены
<a href=https://sex-blog-info.site>https://sex-blog-info.site</a>
интим магазин товары цена
Женский проект <a href=https://viplady.kyiv.ua/>https://viplady.kyiv.ua</a> о моде, красоте, стиле и здоровье, светская жизнь, диеты и рецепты
You should definitely buy sildenafil from this pharmacy
<a href="https://sildenafiliums.com/">Any recommendations for secure sildenafil orders</a>
онлайн журнал <a href=https://vsegladko.net/>https://vsegladko.net</a> о моде и красоте: тренды и модные битвы, призы, новости с красных дорожек, эксперты красоты и гороскопы
Сайт для женщин <a href=https://womanclub.kyiv.ua/>https://womanclub.kyiv.ua</a> о моде, красоте, здоровье, психологии и отношениях. Новые коллекции, фотогалереи с модных показов.
Простой и удобный сайт <a href=https://womanexpert.kyiv.ua/>https://womanexpert.kyiv.ua</a> о моде, красоте, путешествиях, любви и вдохновении.
If you want reliable service, buy sildenafil from this place
<a href="https://claimsildenafil.com/">I suggest you order sildenafil from this highly rated site</a>
Жіночий портал <a href=https://womanportal.kyiv.ua/>https://womanportal.kyiv.ua</a> сучасна мода, тренд, стиль; корисні поради; секрети гарної постаті; уроки макіяжу
Клуб KIA K5 <a href=https://kia-k5-club.ru/>https://kia-k5-club.ru</a> отзывы владельцев, цена и комплектации, характеристики и фото автомобиля.
Клуб владельцев Лада Гранта <a href=https://lada-granta-club.ru/>https://lada-granta-club.ru</a> отзывы реальных владельцев, фото и цена автомобиля, комплектации и характеристики.
Where can I buy sildenafil pills online
<a href="https://sildenafiliums.com/">How do I order sildenafil discreetly</a>
купить секс куклу силикон
<a href=https://e-sex-blog-info.ru>https://e-sex-blog-info.ru</a>
купить секс куклу для взрослых
Следует учитывать нормы Жилищного кодекса, которые регламентируют соблюдение порядка и прав соседних жильцов. Для более детального ознакомления с правами жильцов можно ознакомиться с изменениями в законодательный акт, регулирующий жилищные правоотношения, от 20 марта 2024 год https://7feettravel.ru - https://7feettravel.ru
Are there any discounts when ordering sildenafil
<a href="https://sildenafiliums.com/">I’ve bought sildenafil from here and highly recommend it</a>
This is the most reliable source to order sildenafil
<a href="https://sildenafiliums.com/">I highly recommend ordering sildenafil online from here</a>
купить в москве силиконовую секс куклу
<a href=https://prosex-blog-info.ru>https://prosex-blog-info.ru</a>
купить самую реалистичную секс куклу
купить секс куклу в полный рост
<a href=https://sex-blog-info.ru>https://sex-blog-info.ru</a>
купить реалистическую секс куклу
В данном обзоре пишущий эти строки расскажу, коею наивысший рейкбек дозволительно сорвать в руме, что-что требуется охватывать о признаках представления равно на нежели основные различия ККпокер через клубных подвижных дополнений.
What should I do if I have issues with my sildenafil order
<a href="https://sildenafiliums.com/">What’s the best pharmacy to order sildenafil from</a>
Official website of BC Melbet <a href=https://melbet-malbet.com/>https://melbet-malbet.com/</a> for online sports betting. Fast payouts, high odds, promotions and bookmaker bonuses
Мы предлагаем высокооплачиваемую работу <a href=https://rabota-webcams.ru/>https://rabota-webcams.ru</a> в онлайн чате. Возможность работать на дому. Вы можете зарабатывать от 1000$.
Онлайн-калькулятор ОСАГО рассчитает точную стоимость полиса по тарифам 2020 года. Сравните предложения лидирующих страховых компаний и оформите полис онлайн. Оформление ОСАГО производится в системе страховщика https://auto-donor.ru - https://auto-donor.ru
Топ онлайн казино <a href=https://safespins.com/>https://safespins.com</a> рейтинг и обзоры лучших игровых платформ
купить силиконовую секс куклу
<a href=https://e-sex-blog-info.ru>https://e-sex-blog-info.ru</a>
купить секс куклу с доставкой
Бесплатный сайт знакомств <a href=https://loveplanet.website/>лавпланет</a> без регистрации, знакомства с реальными людьми, поиск новых знакомых для дружбы, серьезных отношений
What is the process to order sildenafil
<a href="https://sildenafiliums.com/">What is the best site to order sildenafil</a>
Sildenafil online order
<a href="https://sildenafiliums.com/">I strongly recommend this site for buying sildenafil</a>
Get the Inside Scoop: Visit Our Site <a href="https://augamblingking.com/review/croco/">croco</a>
Оформить электронное ОСАГО онлайн дешево. Расчет стоимости автострахования ОСАГО за 2 минуты на онлайн-калькуляторе. Учитываем все коэффициенты и скидки на ОСАГО за безаварийность https://astmal.ru - https://astmal.ru
You should order sildenafil here for the best quality
<a href="https://sildenafiliums.com/">You’ll find the best prices when you order sildenafil here</a>
Экскурсии и джип-туры по Крыму <a href=https://м-драйв.рф/tours/pervyj-krymskij/>https://м-драйв.рф/tours/pervyj-krymskij/</a>
Молодая отроковица со кой-какою волнением заглянула ему откровенный.
It’s a smart choice to buy sildenafil from this pharmacy
<a href="https://sildenafiliums.com/">Do you have any recommendations for ordering sildenafil safely</a>
This is the best place to buy sildenafil online
<a href="https://sildenafiliums.com/">Where can I buy sildenafil pills online</a>
Женский портал <a href=https://adviceskin.com/>https://adviceskin.com</a> о здоровье и красоте
Мода, красота и здоровье <a href=https://allwoman.kyiv.ua/>https://allwoman.kyiv.ua</a> Женский журнал об отношениях и красоте
Женский портал <a href=https://amideya.com.ua/>https://amideya.com.ua</a> Все о семье, детях, красоте и здоровье
Женский портал <a href=https://dama.kyiv.ua/>https://dama.kyiv.ua</a> современная мода, тренд, стиль; полезные советы; секреты хорошей фигуры
Женский журнал онлайн <a href=https://girl.kyiv.ua/>https://girl.kyiv.ua</a> на разные темы Мода, красота и любовь Дети, дом, здоровье и кулинария
Лучший онлайн-журнал <a href=https://family-site.com.ua/>https://family-site.com.ua</a> о настоящей жизни: шоу-бизнес, здоровье, мода, красота
This site is where I always order sildenafil, highly recommended
<a href="https://sildenafiliums.com/">I highly recommend buying sildenafil online from here</a>
Новости мира <a href=https://happywoman.kyiv.ua/>https://happywoman.kyiv.ua</a> моды, красоты, шопинга, шоу-бизнеса, отношений и стиля жизни
Наш журнал <a href=https://icz.com.ua/>https://icz.com.ua</a> создан для модных и стильных женщин
Сайт для родителей <a href=https://mch.com.ua/>https://mch.com.ua</a> Детские капризы. Пути решения проблем.
Женский портал <a href=https://mirlady.kyiv.ua/>https://mirlady.kyiv.ua</a> Все о семье, детях, красоте и здоровье
Новости мира моды <a href=https://nicegirl.kyiv.ua/>https://nicegirl.kyiv.ua</a> красоты, шопинга, шоу-бизнеса, отношений и стиля жизни
Простой и удобный сайт о моде <a href=https://presslook.com.ua/>https://presslook.com.ua</a> красоту, путешествия, любовь и вдохновение
What are the alternatives if I can’t order sildenafil
<a href="https://sildenafiliums.com/">You won’t regret buying sildenafil from this site</a>
Заключение
женские советы по теме <a href=https://woman365.kyiv.ua/>https://woman365.kyiv.ua</a> мода, стиль, красота, здоровье, дети, дом, мужчины, отдых
Самые актуальные автомобильные новости <a href=https://auto-club.pl.ua/>https://auto-club.pl.ua</a> Украины и мира, тест-драйвы новых авто, советы экспертов
Авто статьи <a href=https://avtoshans.in.ua/>https://avtoshans.in.ua</a> с советами по ремонту и обслуживанию авто блог с профессиональными советами обзоры новинок лизинг авто
What’s the best-recommended method to order sildenafil online
<a href="https://sildenafiliums.com/">What’s a top-recommended site for ordering sildenafil online</a>
https://t.me/zerkalo1xslotscasino
https://t.me/zerkalo1xslotscasino - казино 1x
https://t.me/zerkalo1xslotscasino
https://t.me/zerkalo1xslotscasino - 1хслотс casino
https://t.me/zerkalo1xslotscasino
https://t.me/zerkalo1xslotscasino - казино 1x
https://t.me/zerkalo1xslotscasino
https://t.me/zerkalo1xslotscasino - регистрация в 1хслотс
https://t.me/zerkalo1xslotscasino
https://t.me/zerkalo1xslotscasino - 1xслот
Greate post. Keep posting such ind of information on your blog.
Im really impressed by it.
Hey there, You have done a great job. I'll definitely
digg it and personally suggest to my friends. I am sure they'll be benefited from this site. https://www.waste-ndc.pro/community/profile/tressa79906983/
Ежедневные новости <a href=https://ecotech-energy.com/>https://ecotech-energy.com</a> из автомобильной среды. Советы автолюбителям
автомобильный портал <a href=https://kakavto.com/>https://kakavto.com</a> последние новости из автомира.
Ежедневные новости <a href=https://myauto.kyiv.ua/>https://myauto.kyiv.ua</a> из автомобильной среды. Советы автолюбителям.
Сертификация ИСО 45001-2020 может быть проведена на любом предприятии независимо от численности персонала и сферы деятельности. Более востребованным получение сертификата ИСО 45001-2020 является для компаний, деятельность которых связана с риском для жизни и здоровья персонал https://teletype.in/@sezdok/chto-takoe-sertifikat-iso-45001
Where to buy sildenafil online
<a href="https://sildenafiliums.com/">Can I order sildenafil in bulk</a>
You should definitely order sildenafil from this pharmacy
<a href="https://sildenafiliums.com/">Purchase sildenafil online</a>
Pornstar UK Kayleigh Wanless Techniques To Simplify Your Daily Life Pornstar UK
Kayleigh Wanless Trick That Every Person Should Be Able To Pornstar Uk Kayleigh Wanless
Все о новых автомобилях <a href=https://newsgood.com.ua/>https://newsgood.com.ua</a> технические характеристики, комплектации, цены, фотогалерея
Ежедневные новости <a href=https://orion-auto.com.ua/>https://orion-auto.com.ua</a> из автомобильной среды. Советы автолюбителям.
Автомобильный журнал <a href=https://retell.info/>https://retell.info</a> для тех, кто умеет выбирать
Все новые авто <a href=https://reuth911.com/>https://reuth911.com</a> с подробными обзорами, фото и характеристиками на сайте
Where can I find reviews before ordering sildenafil
<a href="https://sildenafiliums.com/">This is the best place to buy sildenafil online</a>
Тест-драйвы <a href=https://troeshka.com.ua/>https://troeshka.com.ua</a> тюнинг, обслуживание автомобиля, автомобильная история, отчеты об авто путешествиях
Автомобильные новости <a href=https://tuning-kh.com.ua/>https://tuning-kh.com.ua</a> Украины и мира, тест-драйвы новых авто, советы экспертов
Автомобильные портал Украины <a href=https://tvk-avto.com.ua/>https://tvk-avto.com.ua</a> и мира, тест-драйвы новых авто, советы экспертов
Какая-в таком случае сарыч
We provide virtual numbers for receiving SMS messages. Online security and Privacy with our virtual number service. Ideal for quick and effortless SMS https://www.gudstory.com/expanding-business-horizons-with-virtual-did-numbers/ - buy DID number
Самые актуальные автомобильные <a href=https://xiwet.com/>https://xiwet.com</a> новости Украины и мира, тест-драйвы новых авто
Все о новых автомобилях <a href=https://gormost.info/>https://gormost.info</a> технические характеристики, комплектации, цены, фотогалерея
It’s a smart choice to buy sildenafil from this pharmacy
<a href="https://sildenafiliums.com/">You won’t regret ordering sildenafil from this site</a>
Автомобильные новости <a href=https://mallex.info/>https://mallex.info</a> авто статьи. Тюнинг. Тест-драйв. Новинки авто
Chatme AI (Чатми Аи) <a href=https://chatme.ai/>https://chatme.ai</a> это чат-бот для бизнеса без навыков программирования: для продаж, HR, поддержки, колл-центра, сбора обратной связи и других задач в Телеграмм, Вк, Ватсап
What is the best site to order sildenafil
<a href="https://sildenafiliums.com/">Where is the safest place to order sildenafil online</a>
построить дом под ключ недорого <a href=https://spbstroymax.ru/>https://spbstroymax.ru/</a>
Ice Casino Polska <a href=https://cakecaprice.pl/>https://cakecaprice.pl</a> Official Site Play Ice Casino in Poland
I recommend ordering sildenafil from this trusted pharmacy
<a href="https://sildenafiliums.com/">Order sildenafil without prescription</a>
Online security and Privacy with our virtual number service. We provide virtual numbers for receiving SMS messages. Ideal for quick and effortless SMS -
Мы — команда специалистов, посвятивших себя поиску лучших домов престарелых. Мы ценим заботу, комфорт и безопасность ваших близких. Наши отзывы и опыт говорят сами за себя. Мы поможем вам сделать правильный выбор, чтобы ваши родные чувствовали себя как дома. Давайте работать вместе https://кто-молодец.СЂС„ - https://ты-молодец.СЂС„/
This site is where I always buy sildenafil, highly recommended
<a href="https://sildenafiliums.com/">I advise you to buy sildenafil from this site</a>
В этом обзоре моя персона расскажу, которой максимальный рейкбек не запрещается востребовать в руме, по какой причине необходимо high life относительный чертах забавы и на чем генеральные заслуги ККпокер с клубных подвижных приложений.
Official website of GGBet casino <a href=https://vernandnea.pl/>https://vernandnea.pl</a> Play 2000+ slot machines in online casino and win big
It’s a smart choice to order sildenafil from this pharmacy
<a href="https://claimsildenafil.com/">Sildenafil for sale</a>
Мы собрали рейтинг топ-20 лучших фитнес-клубов в Москве в 2024 году, ориентируясь на вышеперечисленные критерии. Плюс учитывали ценовую политику абонементов и отзывы клиентов https://sport-reforma.ru/ - фитнес на зои космодемьянской
<a href=https://remont-apple-watch-web.ru>ремонт эппл вотч</a>
Архитектурное бюро <a href=https://gost-snip.su/blog/stroitelstvo-doma-ot-idei-do-voploshheniya/>https://gost-snip.su/blog/stroitelstvo-doma-ot-idei-do-voploshheniya/</a> дизайн студия Москва. Заказать эксклюзивное проектирование коттеджей и домов. Студия разработки проектов загородных домов и фасадов в Москве, дизайн интерьеров квартир, коммерческих и жилых зданий, ландшафтный дизайн
How do I cancel an order of sildenafil
<a href="https://claimsildenafil.com/">Which website do you recommend to order sildenafil</a>
I guarantee you’ll be satisfied if you buy sildenafil from here
<a href="https://claimsildenafil.com/">What should I know before I order sildenafil online</a>
<a href=https://prodvizhenie-podolsk.ru/>https://prodvizhenie-podolsk.ru/</a>
What are the shipping options when ordering sildenafil
<a href="https://claimsildenafil.com/">Sildenafil for sale</a>
Помните, что правильный выбор места для занятий спортом может существенно повлиять на вашу мотивацию и результативность тренировок http://dokuteknoloji.com/index.php?option=com_k2&view=itemlist&task=user&id=482994 - http://dokuteknoloji.com/index.php?option=com_k2&view=itemlist&task=user&id=482994
Для тех, кто ищет где купить Озепмпик, аптеки и интернет-магазины предлагают широкий ассортимент с удобной доставкой. Препарат помогает стабилизировать уровень сахара в крови и снижает вес, что делает его популярным выбором среди пациентов с диабетом второго типа. Узнайте цены на Озепмпик и выберите лучший вариант. <a href=https://t.me/ozempik_kupit11>https://t.me/ozempik_kupit11</a>
Фитнес в лучших фитнес-клубах у метро Войковская в Москве. Мы подобрали для вас 28 клубов с ценами от 700 до 80 000 руб. А также 61 тренера http://ufit-nahim.ru/ - зумба беляево
What’s the best-recommended method to order sildenafil online
<a href="https://claimsildenafil.com/">Can you recommend a trusted source to order sildenafil online</a>
How can I verify a site before ordering sildenafil
<a href="https://claimsildenafil.com/">I recommend you order sildenafil from this website</a>
Which website do you recommend to order sildenafil
<a href="https://claimsildenafil.com/">Which online platform is highly recommended to order sildenafil</a>
В аренду входят не только снегоходы, но и весь необходимый инвентарь. Обязательно надевайте шлем и перчатки перед поездкой, чтобы обеспечить защиту и тепло http://snegohody-shop.ru/ - покататься на снегоходах зеленоград
Мы предлагаем аренду снегохода, которые позволят Вам получить максимальное удовольствие от катания. В стоимость проката входит: Аренда снегохода выбранной модели на необходимое количество часов; Полный комплект защитной экипировки https://atv-penza.ru/ - катание на снегоходах пушкино
Where do experts recommend ordering sildenafil
<a href="https://claimsildenafil.com/">Can you recommend a trusted source to order sildenafil online</a>
luxury hotel residences for sale <a href=https://www.invest-in-europe-hotels-for-sale-in-montenegro.com/>invest in Europe</a>
What are the risks of ordering sildenafil online
<a href="https://claimsildenafil.com/">Can you recommend a reliable vendor to order sildenafil from</a>
Мы сочетаем в себе приятный отдых и эффективное сопровождение. Во всех пансионатах созданы комфортные условия проживания для постояльцев: комфортные номера, безбарьерная среда, адаптированные ванные комнаты и коридоры https://xn----htbdwemb1a7b3b.xn--p1ai - пансионаты для престарелых
What payment methods can I use to order sildenafil
<a href="https://claimsildenafil.com/">Are there any recommended services for ordering sildenafil</a>
Подайте заявку на микрокредит с дневной процентной ставкой от 0,01% и получите средства на свою карту круглосуточно https://womanmaniya.ru/kak-poluchit-onlajn-zajm-shagi-i-neobhodimye-dokumenty/ - https://www.planetoday.ru/gde-vzyat-vygodnyj-onlajn-zaem-v-kazahstane/
Cheap sildenafil order
<a href="https://claimsildenafil.com/">I always order sildenafil from this source and recommend it</a>
<a href=https://prodvizhenie-chelyabinsk.ru/>https://prodvizhenie-chelyabinsk.ru/</a>
Which online platform is highly recommended to order sildenafil
<a href="https://claimsildenafil.com/">I recommend buying sildenafil from this trusted pharmacy</a>
What are the shipping options when ordering sildenafil
<a href="https://claimsildenafil.com/">This is the best place to buy sildenafil online</a>
I'd like to thank you for the efvforts you have putt in writing
this blog. I am hoping to see the same high-grade content from you later
on as well. In truth, your creative writing abilities hhas encouraged me to get my
very oown site now ;) https://Www.Waste-Ndc.pro/community/profile/tressa79906983/
квартиры от застройщика <a href=https://novostroikiekb54.ru/>https://novostroikiekb54.ru</a> купить свартиру в казани.
Sildenafil buy
<a href="https://claimsildenafil.com/">Sildenafil online purchase</a>
Привезти технику на ремонт вы можете в самый удобный по расположению сервисный центр. В данный момент успешно функционируют 13 представительств сервисного центра http://remontcentr-stavropol.ru/ - ближайший сервисный центр по ремонту телефонов
Промокоды на бездепозитные фриспины в онлайн казино. Вводи промокод, крути слоты и забирай выигрыш уже сегодня https://t.me/vulkan_delyuxe - https://t.me/vulkan_delyuxe
יאפשרו לך לגלות עולם של הנאה אינסופית. זוהי צורת בילוי אינטימית המותאמת לצרכים של הגבר הישראלי, הידוע כגבר בעל ציפיות גבוהות. למצוא נשים סקסיות וחרמניות שיצאו איתך ביחד אל המסע של הגילוי העצמי. והן השותפות הטובות ביותר למסע שכזה. יש להן הכרות גדולה עם <a href=http://www.sexlayla.co.il/>click here to find out more</a>
помпа для увеличения члена
<a href=https://sex-blog-info.fun>https://sex-blog-info.fun</a>
купить лубрикант для секса
This is the most reliable source to order sildenafil
<a href="https://claimsildenafil.com/">Can I return or exchange sildenafil after ordering</a>
дилдо машина купить
<a href=https://sex-blog-info.online>https://sex-blog-info.online</a>
анальный вибратор массажер простаты
Is it possible to order sildenafil cheaply
<a href="https://claimsildenafil.com/">Is it safe to order sildenafil online</a>
купить смазку
<a href=https://sex-blog-info.site>https://sex-blog-info.site</a>
вакуумная помпа для полового члена купить
анальный фаллоимитатор вибратор
<a href=https://sex-blog-info.space>https://sex-blog-info.space</a>
купить реальную секс куклу
Ремонт бытовой техники и электроники в Москве. Своевременный ремонт бытового оборудования – это гарантия его долгой и исправной работы http://spb-remont-iphone.ru - сервисный центр ремонт телефонов нокиа
Профессиональный сервисный центр по ремонту сотовых телефонов, смартфонов и мобильных устройств.
Мы предлагаем: <a href=https://remonttelefonovmos.ru>ремонт смартфонов</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
двойной дилдо купить
<a href=https://sex-blog-info.website>https://sex-blog-info.website</a>
купить вибратор с доставкой
montenegro property management <a href=https://www.retiring-in-montenegro-property.com/>buy property in Montenegro</a>
магазин купить вибраторы
<a href=https://sex-blog-info.fun>https://sex-blog-info.fun</a>
интим товары сайт
Промокод Фонбет на фрибет <a href=https://kmural.ru/news_importer/inc/aktualnue_promokodu_bukmekerskoy_kontoru_fonbet.html >промокод на 100 рублей</a>
Фонбет предлагает промокоды на фрибет, которые позволяют пользователям получить бесплатные ставки при регистрации или депозите. Промокод 'GIFT200' предоставляет новым игрокам фрибеты, которые можно использовать для различных ставок. Эти промокоды делают игру более привлекательной и выгодной для новых пользователей.
купить удлинитель полового члена
<a href=https://sex-blog-info.online>https://sex-blog-info.online</a>
анальный стимулятор простаты купить
Стоимость сертификации <a href=http://center-sertifikaciya.ru/>http://center-sertifikaciya.ru</a> соответствия ИСО 9001 и срок действия сертификата. Цена сертификата соответствия ИСО 9001 всегда рассчитывается индивидуально, так как зависит от ряда факторов. Срок действия сертификата качества по стандарту ГОСТ Р ИСО 9001 – 3 года с момента его получения.
Вы можете купить справки в Москве в нашей клинике https://ossis-med.ru/
интимный магазин для взрослых
<a href=https://sex-blog-info.site>https://sex-blog-info.site</a>
двухсторонние фаллосы купить
дом престарелых недорого <a href=https://ты-молодец.рф/>дешевые дома престарелых</a>
сколько стоит дом престарелых <a href=https://кто-молодец.рф/>пансионаты для пожилых цены</a>
купить вибратор цена
<a href=https://sex-blog-info.space>https://sex-blog-info.space</a>
интим товары для взрослых
הזוגיות. ולפעמים כאן מתחילות הבגידות. המסקנה היא ברורה, חייבים להשקיע במערכת היחסים המינית וזה כולל גם חיפוש אחר הדרכים הנהנים מזמן איכות נעים. שם בסביבה הדיסקרטית והנעימה תוכל ליהנות מעונג חלומי. זהו הבילוי שגברים צריכים על מנת להרגיש חופשיים <a href=http://www.netalk.co.il/>good link</a>
двухсторонний дилдо купить
<a href=https://sex-blog-info.website>https://sex-blog-info.website</a>
купить половой член
Вы можете купить медсправку в нашем мед центре https://medical-sozvezdie.ru/ в Москве без медкомиссий.
immobilien kaufen montenegro <a href=https://www.immobilien-in-montenegro-fuer-oesterreicher.com/>Montenegro immobilie</a>
Best place to order sildenafil
<a href="https://claimsildenafil.com/">This is the best place to buy sildenafil online</a>
помпа для увеличения члена купить
<a href=https://sex-blog-info.site>https://sex-blog-info.site</a>
интернет интимных товаров
immobilien montenegro bar pajkovic <a href=https://www.investitionen-in-immobilien-in-montenegro.com/>Montenegro immobilien von privat kaufen</a>
montenegro colombia real estate <a href=https://www.buy-or-invest-in-montenegro-real-estate.com/>Montenegro real estate</a>
Вы можете купить медицинскую справку в мед центре https://space-group-med.ru/ в Москве без прохождения врачей.
Женские вечерние платья <a href=https://vechernie-platya-princess.ru/>https://vechernie-platya-princess.ru</a> купить в интернет каталоге с доставкой в Москве. Брендовые женские вечерние платья в наличии и на заказ.
вавада на сегодня <a href=https://sertifikaliegitimler.com/>вавада рабочий сайт на сегодня</a>
фаллоимитатор купить интернет
<a href=https://sex-blog-info.website>https://sex-blog-info.website</a>
купить безремневой страпон в москве
Welcome to official VAVADA channel! We strive to give a high-quality experience to our players. VAVADA is an Online Gaming Project with transparent payouts https://pathiaf.com/ - https://pathiaf.com/
эротическое белье купить
<a href=https://sex-blog-info.fun>https://sex-blog-info.fun</a>
секс шопы купить страпон
How much does it cost to order sildenafil
<a href="https://claimsildenafil.com/">I advise you to buy sildenafil from this site</a>
фаллоимитатор купить интернет
<a href=https://sex-blog-info.online>https://sex-blog-info.online</a>
эротическое белье купить магазин
ברמה גבוהה ומכובדת, ומתאים לכל גבר אשר חפץ בקצת חברה נשית וחום, ורוצה להתמסר לתשוקות והנאות. בישראל ניתן למצוא שירותי ליווי תענוגות. הכל כמובן בצורה דיסקרטית ואינטימית מאוד. כאן ניתן לפגוש נשים בעלות מבנה גוף מושלם. חטוב וסקסי בדיוק כפי שאתה אוהב. <a href=http://www.newsly.co.il/>site</a>
Профессиональный ремонт Apple iPhone любой сложности от 15 минут! Более 8 лет опыта работы! В наличие Оригинальные запчасти и копии хорошего качества на ваш выбор https://jvbtransport.com.au/2019/05/13/hello-world/#comment-5249 - https://jvbtransport.com.au/2019/05/13/hello-world/#comment-5249
купить искусственный член
<a href=https://sex-blog-info.space>https://sex-blog-info.space</a>
лубриканты купить в интернет магазине
Order sildenafil without prescription
<a href="https://claimsildenafil.com/">I suggest you order sildenafil from this highly rated site</a>
купить резиновый член
<a href=https://sex-blog-info.website>https://sex-blog-info.website</a>
эротическое белье купить интернете
Наши инженеры качественно и с гарантией выполнят все необходимые диагностические и ремонтные работы для восстановления вашей техники. Запишитесь на ремонт прямо сейчас https://across-arcco.com/jean-nouvel-seleccionado-para-disenar-el-nuevo-museo-nacional-de-arte-de-china/#comment-46351 - https://across-arcco.com/jean-nouvel-seleccionado-para-disenar-el-nuevo-museo-nacional-de-arte-de-china/#comment-46351
VAVADA is an Online Gaming Project with transparent payouts. Welcome to official VAVADA channel! We strive to give a high-quality experience to our players https://damntroublemaker.com/ - зеркало вавады на сегодня
I recommend buying sildenafil from this trusted pharmacy
<a href="https://claimsildenafil.com/">I’ve had great experiences ordering sildenafil from here</a>
Create Deepnude for free <a href=https://undress-app.love/>free undress app</a> Nudify anyone within a few seconds and create the best AI deep nude images.
Ответы на вопросы <a href=https://www.otvetynavopros.ru/>https://www.otvetynavopros.ru</a> задайте любой интересующий Вас вопрос и получите развернутый и детальный ответ. Ответы на вопросы на любую тему.
Can you recommend a trusted source to order sildenafil online
<a href="https://claimsildenafil.com/">Which online platform is highly recommended to order sildenafil</a>
buy balloon flower <a href=https://helium-balloons-dubai.com/>helium balloons Dubai</a>
Buy sildenafil tablets
<a href="https://claimsildenafil.com/">How do I order sildenafil discreetly</a>
Sul mercato ci sono un sacco di alimentare formulato soprattutto per bambini Che vanno dai prodotti lattiero-caseari, come yogurt, al cibo tipico bambino, ai dolci come i biscotti o cereali https://haas.campusgroups.com/click?uid=2374afbc-0205-11e9-b96d-0ae25bf0cf34&r=https://cabosanlucasbeaches.com - https://haas.campusgroups.com/click?uid=2374afbc-0205-11e9-b96d-0ae25bf0cf34&r=https://cabosanlucasbeaches.com
Very nice post. I just stumbled upon your blog and wanted to
say thazt I've really enjoyed browsing your blog posts.
After alll I'll be subscribing to yourr
rss feed and I hope you write again soon! https://Bandur-art.blogspot.com/2024/08/the-ultimate-guide-to-no-mans-sky-mods.html
I recommend buying sildenafil from this trusted pharmacy
<a href="https://claimsildenafil.com/">This site is where I always order sildenafil, highly recommended</a>
Can I order sildenafil in bulk
<a href="https://claimsildenafil.com/">Which online pharmacy do you recommend for sildenafil orders</a>
Who can recommend where to order sildenafil
<a href="https://claimsildenafil.com/">What should I know before I order sildenafil online</a>
Вы можете купить справку в медицинском центре https://springhealthcare.ru/ в Москве без прохождения врачей.
Do you have any recommendations for ordering sildenafil safely
<a href="https://claimsildenafil.com/">Sildenafil online purchase</a>
order helium balloons <a href=https://helium-balloons-dubai.com/>order balloons with helium delivery Dubai</a>
lee bet casino <a href=https://vladimir-hotel.ru/>официальный сайт lee bet</a>
Can I order sildenafil internationally
<a href="https://claimsildenafil.com/">What’s the best-recommended method to order sildenafil online</a>
Автомобильный онлайн журнал <a href=https://rusigra.org/>https://rusigra.org</a> это источник новостей о последних событиях в автомобильном мире
либет казино <a href=https://m-words.ru/>leebet</a>
Казино Booi - это не просто платформа для азартных развлечений, это целый мир возможностей и шансов. На сайте Казино Booi вас ждут неповторимые ощущения и безграничные возможности для заработка реальных денег. Переходите по ссылке и играйте в честном и прибыльном казино Booi Casino https://logocenter.info/wp-content/pgs/?akcii_i_bonus_kodu_dlya_vavada.html - booi промокоды
Отказное письмо <a href=http://sertexpertiza.ru/>http://sertexpertiza.ru</a> оформляется исключительно на импортируемые товары. Оно оформляется специализированными центрами сертификации и предоставляется при необходимости для подтверждения качества и безопасности продукции.
What’s the best way to order sildenafil online
<a href="https://claimsildenafil.com/">What’s the best-recommended method to order sildenafil online</a>
Стоимость выдачи отказного письма <a href=http://cosmetics-bel.ru/>http://cosmetics-bel.ru</a> определяется индивидуально. На итоговую расценку влияет количество включенных в документ товаров. Для получения точной цены достаточно направить заявку в орган сертификации.
Отказное письмо <a href=http://sertdoc.ru/>http://sertdoc.ru</a> ответственный документ, освобождающий производителя или поставщика от необходимости сертификации. Поэтому его оформлением занимаются специализированные организации – аккредитованные сертифицированные центры.
поисковое seo продвижение сайтов <a href=https://seo-5.ru/>продвижение сайтов в москве</a>
Вы можете купить справку в клинике https://z32-med.ru/ по Москве с бесплатной доставкой до любой станции метро.
If you want reliable service, order sildenafil from this place
<a href="https://claimsildenafil.com/">Sildenafil online purchase</a>
Миниатюризация технологий остаётся ключевым направлением в разработке электроники. В 2019 году мы стали свидетелями значительных прорывов, которые позволяют создавать более компактные, но мощные устройства. Этот пост рассмотрит актуальные тренды и методы, которые помогут в разработке миниатюрных и высокоэффективных электронных устройств https://directmarketingcorp.com/marketing-dictionary/marketing-terms-starting-with-u - Marketing Dictionary: Terms Starting with U
I suggest you buy sildenafil from this highly rated site
<a href="https://claimsildenafil.com/">How do I order sildenafil online</a>
разработка сайтов москва <a href=https://seo-5.ru/>продвижение сайта</a>
Can I return or exchange sildenafil after ordering
<a href="https://claimsildenafil.com/">Best place to order sildenafil</a>
Вы можете купить справку в поликлинике https://med-meditsina.ru/ по Москве с доставкой до станции метро.
Order sildenafil pills
<a href="https://claimsildenafil.com/">You should buy sildenafil here for the best quality</a>
good engineering resume <a href=https://resume-engineering-builder.com/>professional engineer resume format</a>
<a href="https://bestcryptotradingbots.com/de/vortex-genesis-ai.php">Is Bitmart Legal In Canada</a>
<a href="https://bestcryptotradingbots.com/quantum-alrex.php">Is Crypto Trading Legal In Philippines</a>
<a href="https://bestcryptotradingbots.com/fi/immediate-connect.php">How To Set Up Crypto Trading Bot</a>
Фитнес клубы у метро Беляево в Москве – список организаций с фото, адресами и официальными сайтами https://fitness-lubercy.ru/ - gum gum фитнес беляево
Перед установкой видеонаблюдения важно провести анализ объекта и определить ключевые зоны покрытия. Это может включать в себя входы и выходы, парковки, периметр и другие стратегически важные места https://remontdacha.ru/besedki/stroitelstvo/montazh-videonablyudeniya-vidy-trebovaniya-normy.html - https://remontdacha.ru/besedki/stroitelstvo/montazh-videonablyudeniya-vidy-trebovaniya-normy.html
В ассортименте представлен оцинкованный прокат в рулонах двух типов – с железо-цинковым и просто цинковым покрытием http://lsp-metall.ru/ - железная проволока
Expert legal consultations <a href=https://mpartners.am/>https://mpartners.am</a> and solutions. Trustworthy partners in legal matters. Turn to the experts for reliable advice and assistance.
Сравнение ТОП-10 разработчиков чат-ботов <a href=https://chatbotmarket.ru/>https://chatbotmarket.ru</a> в России: плюсы, технические возможности, кому подходят, клиенты. Chatme.ai, Just AI, AutoFAQ, Lia, CraftTalk, Twin. ChatLabs, Botcreators.
The Sallie Mae of today is different from the original <a href=https://sailimae.com/>sallie mae</a>. In 1972, the Student Loan Marketing Association, also called SLMA or Sallie Mae, was created by Congress as a “government-sponsored enterprise,” or GSE. In other words, it was a private, for-profit corporation that had to follow specific regulations from the government.
поисковое seo продвижение сайта в москве <a href=https://seo-5.ru/>продвижение сайта</a>
Erectile dysfunction treatments available online from TruePills.
Discreet, next day delivery and lowest price guarantee.
Trial ED Pack consists of the following ED drugs:
Viagra Active Ingredient: Sildenafil 100mg 5 pills
Cialis 20mg 5 pills
Levitra 20mg 5 pills
Acquistare viagra con paypal:
https://cutt.ly/DebeNiy1
https://cutt.ly/webeBkKx
https://u.to/BdO4IA
заказать seo раскрутку <a href=https://seo-5.ru/>продвижение сайтов москва</a>
https://fioricetrph.com/ - acetaminophen caffeine butalbital
Instagram drops your engagement and auto unfollows in order to force you to boost posts and spend money. We have tried a bunch of boosting https://hackmd.io/ShujaHaider/ryA2TWZ2R - https://hackmd.io/ShujaHaider/ryA2TWZ2R
поисковая оптимизация сайтов <a href=https://seo-5.ru/>https://seo-5.ru</a>
Посвящается смелым игрокам!
В Казино Комета всегда есть актуальные зеркала и возможность получить бездепозитные бонусы. Зайди и играй, чтобы испытать удачу и начать выигрывать в слоты казино. Это надежное казино для всех!
Ловите проверенную ссылку - https://telegra.ph/Kometa-Kazino---Kometa-Casino-2024-obzor-oficialnogo-sajta-kazino-Kometa-Casino---igrat-onlajn-na-dengi-i-besplatno-registraciya-09-04
Играй в выгодное Казино Комета
Играй в лучшее Казино Комета
Хороших выйгрышей!
Сайт о компьютерах и ноутбуках <a href=https://pc-rem.ru/>https://pc-rem.ru</a>. На сайте представлены свежие обзоры компьютерных комплектующих, советы по выбору, сравнения моделей и полезные гайды по настройке и ремонту компьютерной техники.
Player reviews of Mostbet <a href=https://www.skincityindia.com/2024/08/17/mostbet-review//>https://www.skincityindia.com/2024/08/17/mostbet-review/</a> bookmaker #1 in India.
Olimp casino <a href=https://bistour21.kz/>https://bistour21.kz</a> игорный клуб №1 в Казахстане, 5000+ слотов, бонус 150 000 KZT, 250 FS, саппорт 24/7
Let's start with Mostbet <a href=https://www.masalabox.com/mostbet-a-review-of-the-most-popular-bookmaker-in-india/>https://www.masalabox.com/mostbet-a-review-of-the-most-popular-bookmaker-in-india</a> India betting company and get your perfect bonus of up to 150% on your first bet!
Online casino Pin-up <a href=https://www.greatplacetowork.com.pe/recursos/blog/pin-up-casino-en-peru/>https://www.greatplacetowork.com.pe/recursos/blog/pin-up-casino-en-peru</a> Peru casino registration, slot machines and slots online, the best games for money and the most generous bonuses
Mostbet PL <a href=https://word.opole.pl/aktualnosc/bok/187-mostbet-poland-review>https://word.opole.pl/aktualnosc/bok/187-mostbet-poland-review</a> official website of Mostbet Polska - sports betting and casino
<a href=https://kometa-casino-bonuswin.ru/>сайт Комета Казино</a>
9 Things Your Parents Teach You About Only Fans Pornstars Kayleigh
Wanless only Fans Pornstars
Mostbet Bangladesh <a href=https://tatasteelchess.in/mostbet-bangladesh-review-sports-betting-and-online-casino/>https://tatasteelchess.in/mostbet-bangladesh-review-sports-betting-and-online-casino</a> Official Site - Sign Up and Claim Welcome Bonus
Online bookmaker Mostbet <a href=https://millacfoods.com/mostbet-bangladesh-review-sports-betting-and-online-casino/>https://millacfoods.com/mostbet-bangladesh-review-sports-betting-and-online-casino/</a> in Bangladesh: registration with 25 000 BDT bonus, sports betting and casino. Enjoy gambling with Mosbet BD!
now our platform accessible on popular search platforms, especially – on google. for example, regarding [url=https://www.radioveseliafolclor.com/user/EstellaCruz91/]https://www.radioveseliafolclor.com/user/EstellaCruz91/[/url], you also will get in touch with us directly by by e-mail specified in the category "Contacts".
Mostbet affiliate program <a href=https://lab.vanderbilt.edu/blog/2024/07/15/mostbet-partners-affiliate-programme-of-bookmaker-mostbet/>https://lab.vanderbilt.edu/blog/2024/07/15/mostbet-partners-affiliate-programme-of-bookmaker-mostbet/</a> from registration, commission structure to profit maximization. Join now!
Betrivers and betmgm bets exceeded 1600 and 1500 points, respectively. American players also expect to payouts above the average [url=https://postheaven.net/y2favha696/jonbet-casino-e-apostas-a-href-jonbet-br-app-jonbet-br-app-a-andeacute-uma-3l8x]https://postheaven.net/y2favha696/jonbet-casino-e-apostas-a-href-jonbet-br-app-jonbet-br-app-a-andeacute-uma-3l8x[/url] level. which online casinos are rightfully considered favorable for gamers from United States of America?
Users can activate No Deposit Free Spins for registration, with a special promo code, or through active bets https://ca-feespins.com/
<a href="https://bestcryptotradingbots.com/ethereon-edge.php">Is Kucoin Trading Bot Good</a>
https://battery-casino.com/
The Popularity of Online Casino Games <a href="https://slotloversonline.com/slots/gates-of-olympus/">gates of olympus</a>
of chance and strategy. Unlike traditional casino games, the Aviator Game involves a virtual plane that ascends <a href="https://slotloversonline.com/reviews/efbet/">efbet</a>
Playing the Aviator Game is a thrilling experience. Players place their bets and watch the plane take off, with <a href="https://slotloversonline.com/reviews/n1bet/">n1bet</a>
https://avtoznak-dublikat.ru
Получение сертификата ИСО 9001 <a href=http://сертификация-соответствия.рф/>http://сертификация-соответствия.рф</a> правильный и своевременный шаг, который повысит рентабельность компании, ее привлекательность для партнеров и клиентов, а также укрепит позиции на рынке.
Женские секреты <a href=https://fancywoman.kyiv.ua/>https://fancywoman.kyiv.ua</a> онлайн-журнал о моде, красоте, отношениях женщины и мужчины
Как оформить отказное письмо <a href=http://organ-sertifikacii.ru/>http://organ-sertifikacii.ru</a> самостоятельно. Вопрос актуален для тех, кто торгует продукцией собственного производства или импортными товарами. Чтобы оформить письмо, нужно обратиться в специализированный аккредитованный центр.
Features and Benefits <a href="https://slotloversonline.com/reviews/1win/">1win</a>
<a href="https://armodafinilvsmodafinil.com/">adrafinil vs. modafinil</a>
Получение сертификата ISO 9001 <a href=http://sertifikati-sootvetstviya.ru/>http://sertifikati-sootvetstviya.ru</a> потребуется компаниям, которые хотят выйти на международный рынок, а также планируют работать в секторе, контролируемом государством.
The concept of the "best online casinos in Canada" refers to selecting a gaming platform that meets high standards of quality, reliability, and convenience for Canadian players https://ca-bestcasino.com/
10 Things That Your Family Taught You About Tiktok.Pornstars Tiktok.Pornstars
Casino <a href=https://vavadacasino777.xyz/>vavada online</a> play slot machines with bonus, download Vavada casino for money. Registration and entry to the working mirror of Vavada
1win скачать играть
10 лучших казино онлайн 2024
<a href="http://xn----8sb3abbphlcddfde0lvb2a.xn--p1ai">10 лучших казино онлайн</a>
games that stood out from traditional casino offerings. Inspired by the concept of high-risk, high-reward, the <a href="https://slotloversonline.com/reviews/m88/">m88</a>
Обменные пункты, производящие обмен валют Tether TRC20 (USDT) на Монобанк UAH по привлекательным курсам https://ukraineforum.com.ua/index.php?threads/%D0%BE%D0%B1%D0%BC%D0%B5%D0%BD%D0%BD%D0%B8%D0%BA-%D0%BA%D1%80%D0%B8%D0%BF%D1%82%D1%8B.15544/#post-75990 - https://ukraineforum.com.ua/index.php?threads/%D0%BE%D0%B1%D0%BC%D0%B5%D0%BD%D0%BD%D0%B8%D0%BA-%D0%BA%D1%80%D0%B8%D0%BF%D1%82%D1%8B.15544/#post-75990
Discover the excitement of Mostbet Casino <a href=https://dream-web.cz/>https://dream-web.cz</a> simple registration, many bonuses and convenient login will provide an unforgettable gaming experience.
Don't miss the chance to register at Mostbet <a href=https://okstrana.cz/>https://okstrana.cz</a> to get big wins today. Join Mostbet right now
User Interface and Design <a href="https://slotloversonline.com/reviews/vulkanvegas/">vulkan vegas</a>
Онлайн казино Vegasy <a href=https://www.vegasy-casino.info/>https://www.vegasy-casino.info</a> представляет собой инновационную платформу для азартных игр, предлагающую пользователям уникальный опыт виртуального гемблинга. Этот игровой портал отличается ярким, стильным дизайном, вдохновленным атмосферой знаменитого Лас-Вегаса, и интуитивно понятным интерфейсом, делающим навигацию по сайту удобной даже для новичков.
10 лучших казино онлайн 2024
<a href="http://xn----8sb3abbphlcddfde0lvb2a.xn--p1ai">10 лучших казино онлайн</a>
Software Requirements <a href="https://slotloversonline.com/reviews/unibet/">unibet</a>
Discover the world of excitement at Pin Up Casino, the world's leading online casino. The official website <a href=https://pin-up-casino-giris.click/>Game pic up</a> offers more than 4,000 slot machines. Play online for real money or for free using the working link today
Since its inception, the Aviator Game has undergone numerous updates and enhancements. Technological <a href="https://slotloversonline.com/reviews/bitstarz/">bitstarz</a>
Ретрит <a href=http://ретриты.рф/>http://ретриты.рф</a> международное обозначение времяпрепровождения, посвящённого духовной практике. Ретриты бывают уединённые и коллективные; на коллективных чаще всего проводится обучение практике медитации.
Сухие строительные смеси оптом в Москве с доставкой. <a href=https://camremont.ru/osnovnye-vidy-suhih-stroitelnyh-smesej/>Оптовая продажа сухих строительных смесей</a> широкого назначения для ремонта и строительства.
Лечебный <a href=https://massageivanteevka.ru/>массаж Ивантеевка</a> по доступной цене. Услуги медицинского массажа в Ивантеевке, опытные массажисты, без очередей. Записаться на лечебный массаж онлайн.
Лучшая <a href=https://bnovo.ru/>автоматизированная система управления для гостиниц и отелей</a> (АСУ), в которую входят Channel Manager, RMS прогнозирование прибыли и мониторинга цен конкурентов.
Los sitios web no registrados de comercio de opciones binarias pueden atrapar inversores inteligentes https://t.me/s/opcionesbinariasme - broker de opciones binarias
Ретрит <a href=http://ретриты.рф/>http://ретриты.рф</a> международное обозначение времяпрепровождения, посвящённого духовной практике. Ретриты бывают уединённые и коллективные; на коллективных чаще всего проводится обучение практике медитации.
experiences. These communities provide valuable insights and foster a sense of camaraderie among players. <a href="https://slotloversonline.com/reviews/parimatch/">parimatch</a>
Страсть к созданию пространств <a href=http://rentspecialtech.ru/>http://rentspecialtech.ru</a> наш комплексный набор профессиональных услуг обслуживает самую разную клиентуру: от домовладельцев до коммерческих застройщиков.
Defeez - это не просто <a href=https://defeez.ru/>магазин модной одежды</a>, это портал в мир киберпанка. Здесь ты найдешь смелые футуристические образы, которые подчеркнут твою индивидуальность.
Software Requirements <a href="https://slotloversonline.com/reviews/playfina/">playfina</a>
The scoring system in the Aviator Game is based on the multiplier at the time of cashing out. The higher the <a href="https://slotloversonline.com/reviews/m88/">m88</a>
Большое спасибо за ваш сервис при помощи которго я получил быстрый очень развёёрнутый и компетентный ответ https://yuristi.com/privacy
1 мин https://yuristi.com/privacy • Варшавская Чонгарский бульвар, 4к2, офис 6, Москва https://yuristi.com/privacy
16 отзывов https://yuristi.com/
Специальная акция https://yuristi.com/
Мы — ваш онлайн-юрист ??????? https://yuristi.com/
Акция на первое посещение https://yuristi.com/
games that stood out from traditional casino offerings. Inspired by the concept of high-risk, high-reward, the <a href="https://slotloversonline.com/reviews/inbet/">inbet</a>
Ретрит <a href=https://ретриты.рф/>https://ретриты.рф</a> международное обозначение времяпрепровождения, посвящённого духовной практике. Ретриты бывают уединённые и коллективные; на коллективных чаще всего проводится обучение практике медитации.
Etudes <a href=https://specialtechrental.ru/>https://specialtechrental.ru</a> новаторская фирма, которая органично объединяет креативность и функциональность, чтобы по-новому взглянуть на архитектурное совершенство.
Strategies and Tips <a href="https://slotloversonline.com/reviews/bitstarz/">bitstarz</a>
Common Mistakes to Avoid <a href="https://slotloversonline.com/reviews/mostbet/">mostbet</a>
продвижение сайтов сео <a href=https://seosearchprocess.ru/>раскрутка seo</a>
Новостройки <a href=https://kvartirazhkmalosemejka.ru/>https://kvartirazhkmalosemejka.ru</a> (ЖК) в Казани от застройщика. Купить квартиру от застройщика, цены, планировки, генплан, ход строительства
Женский онлайн журнал <a href=https://female.kyiv.ua/>https://female.kyiv.ua</a> красота, здоровье женщины, воспитание детей, отношения
Новые новости политики <a href=https://mostmedia.com.ua/>https://mostmedia.com.ua</a> общества, спорта, культуры, новости дня о событиях
Особое внимание уделяется разнообразию игровых предложений, среди которых можно найти как классические, так и современные варианты. Также предусмотрены бонусные программы и промоакции, способствующие увеличению шансов на выигрыш и улучшению общего опыта http://certificate.winko.net/bbs/board.php?bo_table=free&wr_id=335559 - http://certificate.winko.net/bbs/board.php?bo_table=free&wr_id=335559
Купите квартиру от застройщика <a href=https://kvartirazhkstalink.ru/>https://kvartirazhkstalink.ru</a> в новостройке в Казани. Продажа квартир в жилом элитном комплексе по цене застройщика.
купить квартиру в казани <a href=https://kupit-kvartiruclub.ru/>купить квартиру от застройщика цены</a>
10 лучших казино онлайн 2024
<a href="http://xn----8sb3abbphlcddfde0lvb2a.xn--p1ai">10 лучших казино онлайн</a>
El registro ayuda a evitar que otros se aprovechen de tu creacion o invencion, ya que te permite emprender acciones legales contra aquellos que vulneren tus https://t.me/s/opcionesbinariasmex - que son opciones binarias
<a href=https://idematapp.com/wp-content/pages/1xbet_promo_codes_free_bonus_offers.html >промокод на 1xbet при регистрации</a>
Free bet promo codes from 1xBet allow users to place bets without risking their own money. These codes are often part of special promotions and are popular among users looking to try out the platform or specific bets.
Предлагаем услуги по побелке <a href=https://pobelka.su/>https://pobelka.su</a> животноводческих и производственных и складских помещений горячей известью. Работы выполняем быстро и качественно. Так же оказываем услуги по зачистке помещений от грибка и старой извести перед побелкой горячей известью. Услуги по побелке и ремонту крупногабаритных помещений горячей известью, в том числе с добавлением ядохимикатов, колеров.
купить квартиру в казани от застройщика <a href=https://kupitkvartiruinfo.ru/>https://kupitkvartiruinfo.ru</a>
купить квартиру в казани <a href=https://kvartirukupitland.ru/>https://kvartirukupitland.ru</a>
купить квартиру в казани новостройка от застройщика <a href=https://kupitkvartiruence.ru/>купить квартиру от застройщика цены</a>
цена курсовой работы <a href=https://magistr-nsk.ru/>https://magistr-nsk.ru</a>
Играйте в лучшие казино, ТОП-10 список: честные и надежные, на реальные деньги, быстрые выплаты и выводы, минималные ставки, лицензия и проверенные, мобильные, популярные и новые, бонусы и фрисписны, слоты и автоматы https://t.me/s/cazinotopnews - лучшие казино для игры на смартфоне
<a href=https://gogocasino.one>https://gogocasino.one</a>
сделать реферат на заказ <a href=https://magistr51.ru/>написание реферата</a>
контрольная работа на заказ недорого <a href=https://best-students.ru/>сделать контрольную на заказ</a>
онлайн казино brillx сайт
<a href="https://brillx-kazino.com">Brillx</a>
Познавательный портал <a href=https://detiwki.com.ua/>https://detiwki.com.ua</a> для детей
Женский журнал <a href=https://beautyadvice.kyiv.ua/>https://beautyadvice.kyiv.ua</a> об отношениях и красоте
Женский портал <a href=https://elegance.kyiv.ua/>https://elegance.kyiv.ua</a> современная мода, тренд, стиль; полезные советы; секреты хорошей фигуры; уроки макияжа, внешность и красота
Купить Смартфоны <a href=https://iq-techno.ru>https://iq-techno.ru</a> Apple iPhone (Эпл Айфон) по самым выгодным ценам в интернет-магазине DNS. Широкий выбор товаров и акций. В каталоге можно ознакомиться с ценами, отзывами, фотографиями и подробными характеристиками товаров, а также подобрать Смартфоны Apple iPhone (Эпл Айфон) по параметрам.
<a href=https://www.avtofast.com/opel-insignia/zamena-toplivnogo-filtra-opel-insignia-dizel-20-podrobnoe-rukovodstvo/>замена топливного фильтра opel insignia dizel 20 подробное руководство</a>
Женский онлайн-журнал <a href=https://fashiontop.com.ua/>https://fashiontop.com.ua</a> мода, красота, диеты, звезды, отношения
<a href=https://idematapp.com/wp-content/pages/1xbet_promo_codes_free_bonus_offers.html >1xBet</a>
A 1x Bet bonus code is a code that unlocks bonuses such as deposit matches, free bets, or free spins. These codes are often provided as part of welcome offers or special promotions and can be entered during registration or when making a deposit.
Мода, красота и здоровье <a href=https://gracefulwoman.kyiv.ua/>https://gracefulwoman.kyiv.ua</a> Женский журнал об отношениях и красоте
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Портал для современной женщины <a href=https://ladyone.kyiv.ua/>https://ladyone.kyiv.ua</a> все о знаменитостях, шоу-бизнесе, последних новостях моды и полезных советах
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
драгон мани казино вход <a href=https://smoking-shop.ru/>https://smoking-shop.ru</a>
Dragon Money <a href=https://ugran.ru/>официальный сайт Dragon Money</a>
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Женский журнал <a href=https://miymalyuk.com.ua/>https://miymalyuk.com.ua</a> обо всем полезном для женщин и девушек
Женский портал <a href=https://maleportal.kyiv.ua/>https://maleportal.kyiv.ua</a> современная мода, тренд, стиль; полезные советы; секреты хорошей фигуры; уроки макияжа
Самые свежие новости <a href=https://onlystyle.com.ua/>https://onlystyle.com.ua</a> красоты, моды, здоровья и прочее, что нужно женщинам
Попробуй удачу в 1win casino, играй и выигрывай.
1win casino - твой путь к успеху, выигрывай круглогодично.
Ощути драйв в 1win casino, открывай новые горизонты.
Начни играть в 1win casino и получи бонус, выигрывай и радуйся.
Играй с умом в 1win casino, получай удовольствие и выигрывай.
1win https://vk.com/1wincasinotoday/ - 1win войти .
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Ежедневные автомобильные новости <a href=https://viewport.com.ua/>https://viewport.com.ua</a> и статьи, тесты, характеристики авто и выбор машины
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Самые актуальные автомобильные новости <a href=https://microbus.net.ua/>https://microbus.net.ua</a> Украины и мира, тест-драйвы новых авто
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Новые новости Украины <a href=https://ktm.org.ua/>https://ktm.org.ua</a> последние новости из-за рубежа, новости политики, экономики, спорта, культуры, технологий, шоу -бизнеса
Для защиты прав детей и недееспособных вы можете обратиться в <a href=https://otdel-opeki-tel.ru/>органы опеки</a> по телефону или адресу проживания
Оперативные новости всей Украины <a href=https://uapress.kyiv.ua/>https://uapress.kyiv.ua</a> и мира, читать новости онлайн
Для подключения и оплаты вам поможет <a href=https://gas-address-telephone.ru/>газовая служба</a>. По телефону или в личный кабинет по адресу проживания
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Для подключения и оплаты обратитесь в <a href=https://electroseti-telephone.ru/>электросети</a>. По телефону или в личный кабинет по адресу проживания
Купить <a href=https://moscow-sity-bilety.ru/>билеты Москва Сити</a> на смотровую площадку Панорама 360. Самая высокая смотровая в Европе, высота 330 метров, 86 этаж башня Федерация
Бесплатный сайт <a href=https://znakomstva-mail.ru/>Майл знакомства</a> поиск новых знакомых для дружбы, серьезных отношений, создания семьи.
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Откройте для себя преимущества и функциональность Pin-Up <a href=https://apk.fightcampconditioning.com/>https://apk.fightcampconditioning.com</a> узнайте, как установить и использовать приложение Pin-Up, совместимое с различными устройствами, такими как Samsung Galaxy, OnePlus, Xiaomi, iPhone, iPad.
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
<a href="https://genser-lobachevskogo114.ru/">Плей Фортуна сайт</a>
Химера сёрч бот <a href=https://himera-official.ru/>https://himera-official.ru</a> по поиску и пробиву информации о человеке в Телеграм
Pin Up Casino <a href=https://kksgranicaketrzyn.pl/>https://kksgranicaketrzyn.pl</a> play Pin Up casino on the official website, login to the mirror
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
написание контрольных работ <a href=https://mbdou243.ru/>помощь с контрольными работами</a>
Добрый день!
СЭС Эксперт специализируется на эффективном уничтожении клопов в Москве. Мы предлагаем профессиональную обработку от клопов, чтобы ваша квартира снова стала комфортной. Доверьтесь нашему опыту и получите гарантированный результат.
Подробная информация - http://unichtozhenie-klopov-msk.ru/
Удачи!
Electric Grills <a href=https://www.atgrillscookware.com/>https://www.atgrillscookware.com</a> premium pans and cookware in the USA.
Самые актуальные автомобильные <a href=https://lada.kharkiv.ua/>https://lada.kharkiv.ua</a> новости Украины и мира, тест-драйвы новых авто, советы экспертов
<a href=https://idematapp.com/wp-content/pages/1xbet_promo_codes_free_bonus_offers.html >1xBet</a>
The 1xBet code promo bonus is a code that unlocks bonuses like deposit matches, free bets, or free spins. These codes are often provided as part of welcome offers or special promotions and can be used to enhance the betting experience.
Привет, игроки!
Узнайте всё о Cryptoboss отзывы и начните свою игру уже сегодня. Присоединяйтесь к Cryptoboss online и получайте кэшбэк за каждую ставку. Лучшие крипто-игры ждут вас в любой момент!
Ссылка на Казино здесь - https://t.me/s/casinocryptoboss24/
cryptoboss
cryptoboss casino криптобосс
криптобосс игровые
криптобосс casino ru
cryptoboss отзывы
https://t.me/s/casinocryptoboss24/ - сайт cryptoboss casino cryptoboss casino ru
Хороших профитов!
Привет, игроки!
На сайте Cryptoboss Casino Cryptoboss Casino RU вы найдете все, что нужно для увлекательной игры. Cryptoboss Регистрация обеспечит вам доступ к лучшим играм и бонусам. Начните свой путь к успеху!
Ссылка на Казино здесь - http://ikea-expert.ru
cryptoboss casino криптобосс
игровые автоматы криптобосс
криптобосс игровые
кэшбэк криптобосс
скачать cryptoboss casino
https://ikea-expert.ru/ - криптобосс сайт
Хороших бонусов!
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Доброго!
СЭС Эксперт специализируется на эффективном уничтожении клопов в Москве. Мы предлагаем профессиональную обработку от клопов, чтобы ваша квартира снова стала комфортной. Доверьтесь нашему опыту и получите гарантированный результат.
Подробная информация - http://www.unichtozhenie-klopov-msk.ru/
Удачи!
Посвящается смелым игрокам!
Cryptoboss Casino предлагает вам невероятные бонусы и акции. Читайте отзывы о Cryptoboss и узнайте, почему это казино так популярно. Воспользуйтесь возможностью выиграть прямо сейчас!
Ссылка на Казино здесь - https://ikea-expert.ru/
скачать cryptoboss
криптобосс вход
cryptoboss casino отзывы
криптобосс cryptoboss
криптобосс игровые
https://ikea-expert.ru/ - игровые автоматы криптобосс
Хороших бонусов!
Hello everyone!
Melbet Promo Code 2024 in Portugal – Unlock Big Casino Bonuses!
Portuguese players, enjoy huge rewards with Melbet Promo Code 2024. Claim free spins, cashback, and other exciting bonuses on your favorite games. This is your chance to boost your winnings with an exclusive offer. Use the code now and start playing for big rewards!
Casino link here - https://www.visionxusa.com/search/Melbet%20Promo%20Code%20Egypt%202024:%20MEGA555%20Free%20Bet%20Bonus
Good bets!
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Мы предлагаем индивидуальные программы реабилитации и комплексное лечение зависимостей, а <a href=https://narcologiya-kazakhstan.kz/>наркологический диспансер</a> обеспечивает профессиональные консультации врачей и точную диагностику для восстановления здоровья.
Mostbet website: https://mostbet360.com/
качественный ремонт холодильников <a href=https://remont-holodilnikov-adept.ru/>ремонт холодильников на дому в москве цена</a>
Mostbet website: https://mostbet360.com/
эскорт услуги мужчина москва <a href=https://t.me/moskva_eskort_uslugi>эскорт москва услуги фото</a>
Авто статьи <a href=https://setbook.com.ua/>https://setbook.com.ua</a> с советами по ремонту и обслуживанию вашего авто
Узнайте что такое <a href="https://kartinkianekdoty.wordpress.com/2024/08/19/%d1%87%d1%82%d0%be-%d1%82%d0%b0%d0%ba%d0%be%d0%b5-%d0%bc%d0%b5%d0%bc%d1%8b-%d0%b8-%d0%ba%d0%b0%d0%ba-%d0%be%d0%bd%d0%b8-%d0%bf%d0%be%d1%8f%d0%b2%d0%b8%d0%bb%d0%b8%d1%81%d1%8c/">смешные картинки</a> откуда пришло это явление
Usually I don't read article on blogs, however I would like too say that this write-up very forced me to check out and do so!
Your writing style has been surprised me. Thank you,very nice post. https://lvivforum.pp.ua/
Mostbet website: https://mostbet360.com/
Mostbet website: https://mostbet360.com/
Узнайте что такое <a href="https://kartinkianekdoty.wordpress.com/2024/08/19/%d1%87%d1%82%d0%be-%d1%82%d0%b0%d0%ba%d0%be%d0%b5-%d0%bc%d0%b5%d0%bc%d1%8b-%d0%b8-%d0%ba%d0%b0%d0%ba-%d0%be%d0%bd%d0%b8-%d0%bf%d0%be%d1%8f%d0%b2%d0%b8%d0%bb%d0%b8%d1%81%d1%8c/">мемы</a> и как они появились
lucky jet 1win <a href=https://t.me/s/lucky_jet_1win_official_site>лаки джет 1вин</a>
Mostbet website: https://mostbet360.com/
портал для женщин <a href=https://princess.kyiv.ua/>https://princess.kyiv.ua</a> о стиле, красоте, звездах, отношениях и полный гид по шоппингу в твоем городе
Женский онлайн-журнал <a href=https://miymalyuk.com.ua/>https://miymalyuk.com.ua</a> все про красоту, моду и шоппинг
Mostbet website: https://mostbet360.com/
Свежие новости Украины <a href=https://real-voice.info/>https://real-voice.info</a> последние новости из-за рубежа, новости политики, экономики, спорта, культуры, технологий, шоу-бизнеса
accounting in Montenegro <a href=https://www.montenegro-business-residence.com/>starting a business in Montenegro</a>
Mostbet website: https://mostbet360.com/
vremenska prognoza Kolasin <a href=https://www.kolasin-hotels-montenegro.com/>Bianca Kolasin</a>
Mostbet website: https://mostbet360.com/
Mostbet website: https://mostbet360.com/
himera search telegram <a href=https://blintzes.ru/>сервис химера серч</a>
diabetic medicine rybelsus mounjaro vs rybelsus https://nhsviagravip.com/ - best time to take rybelsus can you take jardiance and rybelsus together rybelsus and jardiance together
shower clocks <a href=https://www.top-clocks.com/>radio cd alarm clocks</a>
Our online store <a href=https://dobra-cena.shop/>https://dobra-cena.shop</a> is a symbiosis of excellent quality and pleasant prices! Everything is arranged here so that it is convenient for you to buy online: all manufacturers of goods are verified, orders are collected and delivered quickly and when it is convenient for you.
Mostbet website: https://mostbet360.com/
лаки джет jet <a href=https://t.me/s/Lucky_Jet_1win_Bot_Signaly>lucky jet онлайн</a>
blacksprut зеркала рабочие <a href=https://dark-blacksprut.com/>blacksprut сайт ссылка</a>
Mostbet website: https://mostbet360.com/
Mostbet website: https://mostbet360.com/
как зайти на blacksprut <a href=https://dark-blacksprut.com/>https://dark-blacksprut.com</a>
Mostbet website: https://mostbet360.com/
https://ludobro.ru/reviews/cryptoboss/ - игровая автомать без платная без регистрации
https://ludobro.ru/reviews/jet/
https://ludobro.ru/reviews/lev/
https://ludobro.ru/reviews/legzo/
https://ludobro.ru/reviews/booi/ - симуляторы игровых автоматов играть бесплатно без регистрации онлайн
https://ludobro.ru/reviews/starda/
https://ludobro.ru/reviews/auf/
https://ludobro.ru/reviews/vavada/
https://ludobro.ru/reviews/gama/
Mostbet website: https://mostbet360.com/
bot lucky jet <a href=https://t.me/s/Lucky_Jet_1win_Bot_Signaly>лаки джет бонусы</a>
Mostbet website: https://mostbet360.com/
блекспрут актуальная ссылка <a href=https://dark-blacksprut.com/>blacksprut вход</a>
Журнал об автомобилях <a href=https://rupsbigbear.com/>https:/rupsbigbear.com</a> выставки, автоспорт, ремонт и сервис
Mostbet website: https://mostbet360.com/
https://emd.su
Ежедневные автомобильные новости <a href=https://simpsonsua.com.ua/>https://simpsonsua.com.ua</a> и статьи, тесты, характеристики и подбор машины
Лечебно-оздоровительный <a href=https://massageivanteevka.ru/>массаж Ивантеевка</a> по выгодным ценам. Стоимость процедуры, порядок проведения, запись на прием.
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Авторский блог Чернолесова <a href=https://chernolesov.com/>https://chernolesov.com</a> это пространство идей и вдохновения для ценителей натуральных материалов, ремесленного мастерства и уникального дизайна. Окунитесь в мир творчества и гармонии природы с каждым постом.
https://ludobro.ru/reviews/casino-x/ - vavada отзывы
https://ludobro.ru/reviews/leebet/
https://ludobro.ru/reviews/fresh/
https://ludobro.ru/reviews/leebet/
https://ludobro.ru/reviews/jozz/ - игровые аппараты бесплатно и регистрации
https://ludobro.ru/reviews/legzo/
https://ludobro.ru/reviews/aurora/
https://ludobro.ru/reviews/leebet/
https://ludobro.ru/reviews/jozz/
by launching the Aviator game on your preferred online https://aviatorgame.dev/
by launching the Aviator game on your preferred online https://aviatorgame.dev/
https://telegra.ph/1xBet-Promo-Code-2024--Bonus-Up-to-130-09-15 - 1xbet promo code free bet
Unlock exclusive bonuses and multiply your winnings by using 1xbet promo codes when you sign up today, ensuring you maximize your gaming experience and increase your chances of hitting the jackpot.
<a href=https://telegra.ph/1xBet-Promo-Code-2024--Bonus-Up-to-130-09-15>1xbet casino промокод </a>
by launching the Aviator game on your preferred online https://aviatorgame.dev/
https://maverickclub.net/forum/index.php?showuser=1222549
https://doneck-news.com/user/SEZnug/
https://hyeforum.com/profile/18216-seztar/
by launching the Aviator game on your preferred online https://aviatorgame.dev/
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Create porn videos with <a href=https://pornpen.net/>Pornpen AI</a>, free AI generated videos.
Ищите качественное авто? Выгодная <a href=https://forums.alliedmods.net/member.php?u=387707>Доставка авто из Дубая в Россию под ключ</a> с гарантией. Цены ниже рынка, большой выбор авто, првоерка перед покупкой.
Оформить займ <a href=https://ozaim.ru/>https://ozaim.ru</a> онлайн на карту. Займы с мгновенным одобрением онлайн. Получить кредитную карту с высоким одобрением.
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Более 500 000 человек желающих завести <a href=https://znakomstva-mail.ru/znakomstva-moskovskaya-oblast/znakomstva-protvino/>знакомства протвино</a> без регистрации бесплатно, 200 новых знакомств на сайте каждую минуту. Регистрируйтесь – это быстро и бесплатно.
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Женский портал <a href=https://femaleguide.kyiv.ua/>https://femaleguide.kyiv.ua</a> с полезными советами по моде, красоте, здоровью и отношениям.
Портал для женщин <a href=https://femalesecret.kyiv.ua/>https://femalesecret.kyiv.ua</a> о моде, красоте, здоровье и отношениях. Практичные советы и актуальные темы для повседневной жизни.
<a href=https://idematapp.com/wp-content/pages/1xbet_promo_codes_free_bonus_offers.html >1xBet</a>
1xBet offers specific promo codes for casino players that provide free spins, deposit bonuses, or cashback on losses. These codes can be used in the casino section of the site to enhance the gaming experience.
Что такое <a href="https://kartinkianekdoty.wordpress.com/2024/08/19/%d1%87%d1%82%d0%be-%d1%82%d0%b0%d0%ba%d0%be%d0%b5-%d0%bc%d0%b5%d0%bc%d1%8b-%d0%b8-%d0%ba%d0%b0%d0%ba-%d0%be%d0%bd%d0%b8-%d0%bf%d0%be%d1%8f%d0%b2%d0%b8%d0%bb%d0%b8%d1%81%d1%8c/">смешные картинки</a> и как они появились
Портал женского <a href=https://fines.com.ua/>https://fines.com.ua</a> и мужского здоровья. Лечение остеохондроза. Компьютерная вытяжка поясничного, грудного, шейного отделов
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Сайт о воспитании <a href=https://geog.org.ua/>https://geog.org.ua</a> и развитии детей. Практические советы для родителей по уходу, обучению и поддержке ребенка на каждом этапе его жизни.
by launching the Aviator game on your preferred online https://aviatorgame.dev/
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Женский портал о моде <a href=https://gracefullady.kyiv.ua/>https://gracefullady.kyiv.ua</a> красоте, здоровье и саморазвитии. Советы, тренды и вдохновение для современной женщины.
Портал для женщин <a href=https://magictech.com.ua/>https://magictech.com.ua</a> о моде, уходе за собой, здоровье и развитии. Полезные советы, новинки и тренды для тех, кто стремится к успеху и гармонии в жизни, всегда оставаясь на высоте.
Женский сайт о стиле <a href=https://gryada.org.ua/>https://gryada.org.ua</a> красоте, здоровье и личностном росте. Практические рекомендации, свежие идеи и актуальные тренды для женщин, желающих развиваться и сохранять гармонию в жизни.
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Покупка виртуального номера конкретно для привязки к Телеграмм-каналу имеет несколько достоинств, к числу которых относится https://texnomaniya.ru/internet-news/virtualniy_nomer_dlya_telegram_gde_ego_vzyat - номер для телеграмма
Свежие новости <a href=https://musicbit.com.ua/>https://musicbit.com.ua</a> мира шоу бизнеса. Популярные диеты, советы психолога, тонкости отношений
Онлайн журнал для женщин <a href=https://prettywoman.kyiv.ua/>https://prettywoman.kyiv.ua</a> новости, мода и шоппинг, красота и здоровье, стиль жизни, дом и еда
Профессиональная <a href=https://sozdanie-sajtov-18.ru/>разработка сайтов</a> для бизнеса: от лендингов до интернет-магазинов. Мы создаём эффективные, современные сайты, адаптированные под любые устройства, с фокусом на удобство пользователей и высокие результаты. Полный цикл услуг — от дизайна до технической поддержки.
helium balloon store <a href=https://balloon-store-dubai.com/>custom helium balloons with delivery</a>
Занимаемся сдачей в аренду комплектов плавсредств <a href=https://baidak.ru/>https://baidak.ru</a> и байков для самоорганизованных речных сплавов. Исследуем маршруты для самоорганизованных речных сплавов и оформляем краткие путеводители. Мы работаем для тех кто любит свободу и независимость в планировании путешествия, а так же творческих личностей, которые хотят реализовать собственные проекты комплектов плавсредств и байков для самоорганизованных речных сплавов.
Приобретайте виртуальные и временные номера телефонов для регистрации. Удобный и надежный сервис для получения смс-онлайн. Более 180 стран и тысячи сервисов https://kremenchug.pl.ua/ru/publ/virtualnye_nomera_dlja_telegramm_1821 - купить виртуальный номер телеграм
Лечение созависимости <a href=http://medprom.ru/medprom/2952771/>http://medprom.ru/medprom/2952771</a> направлено на восстановление эмоциональной и психологической независимости. Мы предлагаем комплексную терапию, включающую психотерапию, поддержку специалистов и индивидуальные программы для преодоления зависимости от поведения и контроля других.
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Что такое анекдот? История прикольных анекдотов. Свежие тут
<a href="http://prikoly-shutki.ru/anekdoty">http://prikoly-shutki.ru/anekdoty</a>
Онлайн журнал для женщин <a href=https://stylewoman.kyiv.ua/>https://stylewoman.kyiv.ua</a> предлагает актуальные советы по красоте, здоровью, моде и саморазвитию. Узнайте, как ухаживать за собой, поддерживать баланс в жизни, строить карьеру и развивать личные отношения. Практические рекомендации для уверенности и успеха в каждой сфере жизни.
портал для женщин <a href=https://sweetheart.kyiv.ua/>https://sweetheart.kyiv.ua</a> предлагает полезные рекомендации по уходу за собой, поддержанию здоровья и развитию индивидуального стиля. Статьи о моде, карьере и личных отношениях помогут вам чувствовать себя уверенно и успешно в любых сферах жизни. Идеи и советы для гармонии и самореализации.
Что такое шутка? Как с помощью прикольных шуток улучшить чувство юмора
<a href="https://telegra.ph/Smeshnye-shutki-i-kak-razvit-chuvstvo-yumora-09-23">https://telegra.ph/Smeshnye-shutki-i-kak-razvit-chuvstvo-yumora-09-23</a>
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Pin Up – это официальная платформа для ставок на спорт, которая получила лицензию в 2021 году и уже завоевала доверие среди бетторов в Казахстане https://pin-up-kz.online/ - pin-up-kz.online
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Новинки света <a href=https://womanfashion.com.ua/>https://womanfashion.com.ua</a> моды, красоты, шопинга, шоу-бизнеса, развлечений и стиля жизни
Женский онлайн-журнал <a href=https://wonderwoman.kyiv.ua/>https://wonderwoman.kyiv.ua</a> мода, красота, диеты, звезды, отношения
Cайт о моде <a href=https://gratransymas.com/>https://gratransymas.com</a> красоте, путешествиях, любви и вдохновении
Женский онлайн-журнал <a href=https://horoscope-web.com/>https://horoscope-web.com</a> простой и удобный сайт о моде, красоте, путешествиях, любви и вдохновении.
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Смешные анекдоты в приложении
<a href="https://play.google.com/store/apps/details?id=ru.shutochki">Всё шуточки</a>
by launching the Aviator game on your preferred online https://aviatorgame.dev/
Описание лекарственных препаратов <a href=https://mikstur.com/>https://mikstur.com</a> инструкций по применению, показаний и противопоказаний, фармакологических действий
Последние новости моды <a href=https://psilocybe-larvae.com/>https://psilocybe-larvae.com</a> тенденции стиля и красоты звезд
Pretty little village of the Gard, it is located 20 minutes from Avignon or Orange - Saint Laurent des Arbres is a typical village of the Gard Rhodanien in Provence. https://www.midilibre.fr/2013/07/25/soiree-guinguette-a-st-laurent-des-arbres,738623.php - https://www.midilibre.fr/2013/07/25/soiree-guinguette-a-st-laurent-des-arbres,738623.php
Женский онлайн-журнал <a href=https://ramledlightings.com/>https://ramledlightings.com</a> где каждая найдёт что-то для себя: мода, красота, здоровье, психология, карьера и вдохновение. Полезные советы, актуальные тренды и практические рекомендации для современной женщины. Оставайся в курсе новостей и вдохновляйся каждый день!
Royal Reels was established to provide a world-class https://au-royal-reels.com/
прикольные анекдоты
<a href="https://caramellaapp.com/supermikekros/s0qRWxvv8/rasskazhu-kak-podnyat-nastronie">Хохотамба ру</a>
Royal Reels was established to provide a world-class https://au-royal-reels.com/
Mostbet always working mirror Mostbet <a href=https://mostbet-az-com.com/>https://mostbet-az-com.com</a> to log in to the official website of the casino and bookmaker. Registration on the current Mostbet mirror for today
Royal Reels was established to provide a world-class https://au-royal-reels.com/
Royal Reels was established to provide a world-class https://au-royal-reels.com/
Новая нейросеть Яндекса YandexGPT 2 уже в приложении Яндекс. YandexGPT помогает придумывать идеи, тексты на разные темы и многое другое https://trychatgpt.ru/ - https://trychatgpt.ru/
https://eventmoon.ru/
Royal Reels was established to provide a world-class https://au-royal-reels.com/
Женский онлайн-журнал <a href=https://asprofrutsc.org/>https://asprofrutsc.org</a> о моде, красоте, здоровье и саморазвитии. Полезные советы, тренды, рекомендации от экспертов и вдохновение для каждой.
Как улучшить чувство юмора с помощью <a href="https://humoracademy.nethouse.ru/page/1737096">шуточек</a>
Полный топ-Казино сайтов: нажмите здесь, чтобы получить бесплатный доступ к списку лучших Казино сайтов мира https://sykaaacas.ru/ - казино сукка
Официальный сайт Cryptoboss Casino: играй и выигрывай
криптобосс официальный сайт вход https://101optovik.ru/ - cryptoboss casino официальный сайт вход .
Последние новости <a href=https://useti.org.ua/>https://useti.org.ua</a> бизнеса и финансов, новости политики, эксклюзивная аналитика и советы экспертов
Royal Reels was established to provide a world-class https://au-royal-reels.com/
Актуальные новости <a href=https://arguments.kyiv.ua/>https://arguments.kyiv.ua</a> Украины: политика, экономика, общество, спорт и культура. Свежие репортажи, аналитика и главные события дня. Будьте в курсе всех изменений и тенденций в Украине.
Последние новости Украины <a href=https://dailynews.kyiv.ua/>https://dailynews.kyiv.ua</a> и мира: события в политике, экономике, спорте и культуре. Оперативные репортажи, аналитика и свежие обзоры. Узнавайте о главном первыми.
Сократите свои расходы на лизинг грузового и коммерческого транспорта, автобусов и легковых автомобилей https://car-yaroslavl.ru/ - лизинг автотранспорта для ип
Royal Reels was established to provide a world-class https://au-royal-reels.com/
Мода, здоровье, красота и отношения <a href=https://elegantwoman.kyiv.ua/>https://elegantwoman.kyiv.ua</a> главные темы для современной женщины. Полезные статьи и тренды для успешной и гармоничной жизни.
Женский журнал <a href=https://womanlife.kyiv.ua/>https://womanlife.kyiv.ua</a> о моде, красоте, здоровье и отношениях. Полезные советы, тренды и рекомендации для современных женщин. Читай статьи о карьере, саморазвитии и стиле жизни, чтобы быть в курсе актуальных тем и находить вдохновение каждый день.
Тренды моды <a href=https://woman24.kyiv.ua/>https://woman24.kyiv.ua</a> секреты красоты, советы по здоровью и отношениям. Открой для себя вдохновение и полезные идеи для повседневной жизни и саморазвития.
Royal Reels was established to provide a world-class https://au-royal-reels.com/
Royal Reels was established to provide a world-class https://au-royal-reels.com/
Royal Reels was established to provide a world-class https://au-royal-reels.com/
Всё о моде <a href=https://chernogolovka.net/>https://chernogolovka.net</a> красоте, здоровье и отношениях. Актуальные идеи, вдохновение и полезные советы для достижения баланса и успеха.
Мода, красота <a href=https://ledis.top/>https://ledis.top</a> здоровье и отношения. Открой для себя свежие идеи и советы для ежедневного вдохновения и успеха.
Модные тенденции <a href=https://saralelakarat.com/>https://saralelakarat.com</a> секреты красоты, здоровье и советы по отношениям. Читай актуальные статьи и вдохновляйся для новых достижений и гармонии в жизни.
Royal Reels was established to provide a world-class https://au-royal-reels.com/
https://mailsco.online/ - это mailsco
Последние новости Украины <a href=https://ua-vestnik.com/>https://ua-vestnik.com</a> политика, экономика, общество, культура и спорт. Оперативные репортажи, аналитика и мнения экспертов. Будьте в курсе главных событий и актуальных тенденций в Украине каждый день.
Хранилище ссылок <a href=https://memo.top/about/ru/>https://memo.top/about/ru</a> для структурирования накопленных ресурсов. Добавляй ссылки на сторонние ресурсы, группируй их и делись со своими друзьями. Повысьте вашу продуктивность c помощью персонализированой стартовой страницы
1xSlots isn’t just appealing with its range of games. Here, you’re embraced in 45 languages and the convenience of transactions, accommodating both traditional payment method https://1xslots-ru.ru/ - 1xslots casino
комплексное продвижение сайтов недорого <a href=https://seo-5.ru/>продвижение сайтов</a> заказать seo раскрутку сайта москва
Металлические входных двери двери в квартиру любого размера, конструкции и комплектации. Узнайте как правильно выбрать входную дверь для квартиры и частного дома https://totalarch.com/metallicheskie-vhodnye-dveri-v-kvartiru-sovety-po-vyboru
Royal Reels was established to provide a world-class https://au-royal-reels.com/
<a href="https://cryptoaitradingbots.com/">cryptoaitradingbots.com</a>
Aviator is an online game for real money <a href=https://aviator-crash.org/>https://aviator-crash.org</a> where players predict when the plane will stop to win. Test your luck and strategy with fast and secure withdrawals. Simple rules, instant payouts, and the chance for big wins await you!
Процесс учебы в автошколах состоит из лекций и вождения. Стоимость обучения в автошколе варьируется от 20 до 25 тыс рублей http://dosaaf-mk.ru/ - дешевая автошкола в москве
new retro casino бонус <a href=https://tyre-pv.ru/>сайт new retro casino</a>
AI service <a href=https://pornx-ai.net/>pornx.ai</a> is an for creating personalized adult content. Select parameters and scenarios to receive high-quality videos tailored to your preferences. Enjoy full privacy and instant generation using cutting-edge technology.
Discover <a href=https://undressher.net/>undressher</a> app undress people by photo for free online. Get unique opportunities with Undressher app.
Услуги монтажа ливневок по Воскресенскому району Работаем без выходных.<a href=https://drenaj-mos.ru/>https://drenaj-mos.ru/</a>
Хранилище ссылок <a href=https://memo.top/about/>https://memo.top/about/</a> для структурирования накопленных ресурсов. Добавляй ссылки на сторонние ресурсы, группируй их и делись со своими друзьями. Повысьте вашу продуктивность c помощью персонализированой стартовой страницы
<a href="https://searchdose.com/">searchdose.com</a>
Стоимость oбучения на водительские права в Москве, СПБ и других городах. Стань водителем за 3 месяца http://avtoshkola-saransk.ru - школа вождения
У нас вы найдете <a href=https://complife.am/noutbuki>ноутбуки</a> различных конфигураций, размеров и цветов. Мы предлагаем ноутбуки с различными типами дисплеев, такими как IPS, OLED, TN, а также различными разрешениями экрана. Если вам нужен ноутбук для игр, мы предлагаем модели с высокой производительностью и мощными графическими картами. Если вы ищете ноутбук для работы, у нас есть модели с быстрыми процессорами и большим объемом памяти.
Федерация - это проводник в мир покупки запрещенных товаров, можно купить гашиш, купить мефедрон, купить кокаин, купить меф, купить экстази, <a href=https://shop.federatsia.info/>купить альфа пвп</a>, купить гаш в различных городах. Москва, Санкт-Петербург, Краснодар, Владивосток, Красноярск, Норильск, Екатеринбург, Мск, СПБ, Хабаровск, Новосибирск, Казань и еще 100+ городов.
Wikicredit (ВикиКредит) <a href=https://wikicredit.com.ua/ru/>https://wikicredit.com.ua/ru/</a> незаменимый онлайн-помощник в поиске микро-финансовых организаций, банков и ломбардов.
Get Started Now: Visit Our Site for More Info <a href="https://augamblingking.com/review/golden-crown/">golden crown</a>
Забавные <a href="http://prikoly-shutki.ru/videos">видео</a> на разные темы
Поднимите себе настроение!
Ремонт компьютеров в Зеленограде на дому <a href=https://zelcompuhelp.ru/>https://zelcompuhelp.ru</a> профессиональная помощь в удобное для вас время. Настройка, диагностика, замена комплектующих и программное обеспечение. Быстрое решение любых проблем с вашим ПК без необходимости его транспортировки.
Find Your Next Big Idea: Visit Us Now <a href="https://augamblingking.com/review/lukki/">lukki</a>
автобус sollers <a href=https://sollers-avto.ru/>https://sollers-avto.ru</a>
Как поднять настроение с помошью приколов. ржачные картинки
http://aromatov.wooden-rock.ru/forum/profile.php?action=show&member=24961
Профессиональная стоматологическая помощь <a href=https://stomatologia.moscow/>https://stomatologia.moscow</a> лечение зубов, протезирование, имплантация, ортодонтия и профилактика. Современные технологии, безболезненные процедуры и индивидуальный подход. Обеспечиваем здоровье полости рта и красивую улыбку на долгие годы.
Прикольные <a href="https://shutochki.wordpress.com/2024/09/27/smeshnye-anekdoty/">анекдоты</a>. Что такое анекдоты
Explore the Future Today: Visit Us Now <a href="https://augamblingking.com/crypto/">crypto</a>
комплексное продвижение сайтов <a href=https://seo-5.ru/>продвижение сайтов</a> seo аудит заказать
Maximize Your Potential: Explore Now <a href="https://augamblingking.com/review/stay/">stay</a>
Прикольные <a href="http://prikoly-shutki.ru/korotkie-anekdoty">шутки</a>. Короткие анекдоты.
Информационный сайт о биодобавках <a href=https://биодобавки.рф/>https://биодобавки.рф</a> предоставляет актуальные данные о составе, пользе и применении различных добавок. Узнайте, как поддерживать здоровье с помощью натуральных средств, получите советы экспертов и ознакомьтесь с научными исследованиями в области нутрициологии.
clocks go back when <a href=https://clocks-top.com/>sound alarm clocks</a>
Кракен сайт - это онлайн-площадка, работающая в скрытых сетях интернета, где пользователи могут покупать и продавать различные виды наркотиков. Для доступа к <a href=https://at.kraken-2krn.vip/>Кракен сайт</a> необходимо использовать специальное программное обеспечение, позволяющее обходить блокировки и обеспечивающее анонимность пользователей.
Don't Miss Out Check Out Our Latest Updates Here <a href="https://augamblingking.com/review/star/">star</a>
Get More Done: Click to Explore <a href="https://augamblingking.com/review/neospin/">neospin</a>
master clocks <a href=https://clocks-top.com/>clocks with seconds</a>
Get More Out of Life: Visit Our Website <a href="https://augamblingking.com/review/ripper/">ripper</a>
Прикольные <a href="https://shutochki.wordpress.com/2024/09/27/smeshnye-anekdoty/">анекдоты</a>. История анекдотов.
<a href=https://actuchomage.org/includes/wkl/code_promo_69.html >1xBet</a>
Promo codes for 1xBet are alphanumeric codes that provide bonuses like deposit matches, free bets, or free spins. These codes can be used during registration or deposit to claim the corresponding bonus.
See What You’ve Been Missing: Explore Now <a href="https://augamblingking.com/review/star/">star</a>
Сайт о биодобавках <a href=https://xn--80abafhxep5ab.xn--p1ai/>https://биодобавки.рф</a> предлагает проверенную информацию о натуральных добавках для здоровья. Узнайте, как выбрать подходящие средства для улучшения иммунитета, повышения энергии и поддержания активного образа жизни. Подробные описания и советы помогут сделать осознанный выбор.
can prednisone cause indigestion prednisone doseage https://heallthllines.com/ - dog steroid prednisone can prednisone cause diarrhea side effects after taking prednisone
Start a New Adventure: Visit Us Now <a href="https://augamblingking.com/review/spin-samurai/">spin samurai</a>
Как поднять настроение с помошью мемов. Ржачные мемы.
http://molbiol.ru/forums/index.php?showuser=1386267
Смешные <a href="https://shutochki.wordpress.com/2024/09/27/smeshnye-anekdoty/">анекдоты</a>. Что такое анекдот.
Get Instant Access: Explore Our Site <a href="https://augamblingking.com/review/uptown/">uptown</a>
Ищете множество различных товаров? Мега поможет вам! Благодаря разнообразию категорий и эксклюзивным предметам <a href=https://xn--megas-k90b.com>ссылки на мега дарк</a> предлагает что-то на любой вкус. Оцените удобство регистрации без электронной почты и защитите свой аккаунт с помощью Google TFA. Присоединяйтесь к <a href=https://xn--megas-k90b.com>ссылка на мега</a> сегодня и отправляйтесь в шопинг-тур, который запомнится надолго.
mega com ссылка: https://xn--megas-k90b.com
Explore the Unknown: Click to Learn More <a href="https://augamblingking.com/review/clubhouse/">clubhouse</a>
Explore More: Visit Our Website for Exciting News <a href="https://augamblingking.com/review/joe-fortune/">joe fortune</a>
Как поднять настроение с помошью приколов. Свежие картинки.
<a href="
http://www.detki-v-setke.ru/index.php?showuser=24824">читать</a>
Ищете место, где ваша безопасность важнее всего? Mega - это решение! Благодаря передовым функциям безопасности и удобному интерфейсу <a href=https://xn--megab-mdb.com>https megaweb4 at</a> гарантирует защиту вашей информации. Пройдите легкую процедуру регистрации и изучите разнообразие категорий. Присоединяйтесь к <a href=https://xn--megab-mdb.com>mega at</a> уже сегодня и делайте покупки с уверенностью.
https://mega-active-links.com - mega at
Сайт предоставляет информацию о биодобавках <a href=https://биодобавки.рф/>биодобавки.рф</a> состав, польза и рекомендации по применению. Здесь вы найдёте обзоры эффективных добавок для улучшения здоровья, иммунитета и энергии на основе научных данных и экспертных мнений.
Get More Out of Life: Visit Our Website https://mostbet360.com/bn/
Телеграм бот <a href=https://users-box.ru/>https://users-box.ru</a> для поиска информации и проверки данных о пользователях, номерах телефонов, email-адресах и других данных.
Find Your Next Big Idea: Visit Us Now https://mostbet360.com/cs/
Телеграм бот <a href=https://brickquick.ru/>https://brickquick.ru</a> предназначен для поиска информации из открытых источников, проверки утечек данных и сбора сведений по таким персональным данным, как номер телефона, электронная почта и профили в социальных сетях.
Инновационный бот в Telegram <a href=https://2-box.ru/>https://2-box.ru</a> позволяющий получить доступ к информации о пользователях, таких как номера телефонов, email-адреса и другие личные данные. С его помощью можно быстро найти сведения о людях, пользователях соцсетей или мессенджеров.
Конструктор документов <a href=https://forma.today/>https://forma.today</a> позволяет мгновенно создавать документы. Для этого нужно выбрать шаблон, заполнить несколько полей и получить готовый документ. Процесс создания автоматизирован, а заполнение данных по ИНН и подсказки при вводе адреса облегчают работу.
Discover What’s Possible: Visit Our Website https://mostbet360.com/uz/
Trade Forex <a href=https://traders-choice.com/>https://traders-choice.com</a> using more than 100 assets. Free demo account with $10,000. Copy the best traders' trades. Earn within 60 seconds. Reliable withdrawal of funds.
Make Your Move: Explore More Here https://mostbet360.com/de/
Профессиональный сервисный центр по ремонту кофемашин по Москве.
Мы предлагаем: <a href=https://remont-kofemashin-top.ru/>техник ремонту кофемашин</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Ржачные <a href="
https://pipeclub.net/index.php?/user/114591-vychislavyakov/">приколы</a>
Как появились приколы. Узнайте, как поднять себе настроение!
Balancing equipment, high quality and low price,
anyone can buy, even to provide paid services to balance any parts
https://vibromera.eu/shop/854/
Equipos de equilibrado, de alta calidad y bajo precio, cualquiera puede comprarlos,
incluso prestar servicios de pago para equilibrar cualquier pieza
https://vibromera.eu/shop/854/
<a href=https://actuchomage.org/includes/wkl/code_promo_69.html >1xBet</a>
1xBet frequently releases new promo codes that provide users with updated bonuses and promotions. These codes can include anything from free bets to deposit matches and are available to both new and existing users.
Download Android apps for free from <a href=https://appworldstore.ru/>https://appworldstore.ru</a>. Fast, reliable, and filled with popular applications.
stromectol effet indesirable how effective is stromectol against scabies https://onllinedoctorvip.com/ - stromectol 3 mg tablets price stromectol price uk kratze tabletten stromectol
Смешные <a href="https://teletype.in/@anekdoty/anekdotiki">анекдоты</a>. История анекдотов.
I am genuinely pleased to read this blog posts which carries tons of valuable information, thanks for providing such data.
What's up, just wanted to tell you, I enjoyed this post. It was practical. Keep on posting!
Erectile dysfunction treatments available online from TruePills.
Discreet, next day delivery and lowest price guarantee.
Trial ED Pack consists of the following ED drugs:
Viagra Active Ingredient: Sildenafil 100mg 5 pills
Cialis 20mg 5 pills
Levitra 20mg 5 pills
Acquistare viagra con paypal:
https://cutt.ly/4eIsYIfm
https://cutt.ly/webeBkKx
https://u.to/BdO4IA
сейф в доме <a href=https://bigpicture.ru/kakim-dolzhen-byt-seyf-dlya-doma/>купить сейф москва для дома</a>
сейф купить для дома <a href=https://bigpicture.ru/kakim-dolzhen-byt-seyf-dlya-doma/>домашние сейфы цены</a>
Глаз бога <a href=https://autobazarf.ru/>https://autobazarf.ru</a> пробить авто по номеру или вин или владельцу. Система поиска работает онлайн, не требует установки. Все что вам требуется - это наличие аккаунта в Telegram, и номер авто. Если авто есть в базе ГИБДД, то найти его системе не составит труда.
cейф взломостойкий <a href=https://astv.ru/news/materials/kakim-dolzhen-byt-vzlomostojkij-sejf>сейф взломостойкий купить</a>
Сайт <a href="https://u-misti.khmelnytskyi.ua/">https://u-misti.khmelnytskyi.ua</a> — це онлайн-ресурс для жителів Хмельницького, який збирає огляди подій про культурні заходи. На платформі У місті Хмельницький ви дізнаєтеся цікаві матеріали про активності у Хмельницькому.
стоимость сейфа для денег <a href=https://kostroma.today/novosti-partnerov/trebovaniya-k-sejfam-dlya-deneg/>купить сейфы для денег</a>
Портал <a href="https://u-misti.cherkasy.ua/">https://u-misti.cherkasy.ua</a> це інтернет-ресурс для мешканців міста, який збирає корисні матеріали про місцеві заходи. На інтернет-майданчику У місті Черкаси знайдете рекомендації про черкаські заходи.
Прикольные <a href="https://teletype.in/@anekdoty/anekdotiki">анекдоты</a>. История анекдотов.
Сервисы виртуальных номеров для приема СМС значительно упрощают процесс регистрации и смс-активации на разных платформах, избавляя от необходимости использовать свой личный телефон. Сегодня можно купить https://test.moygorod.online/novosti-kompaniy/novosti-kompaniy_50652.html - номер для регистрации
Смотрите бесплатные порно-ролики высокого качества, которые обновляются ежедневно и доступны без регистрации.
<a href="https://servis-don.ru/catalog/tehnika/spowha407214248337/">porno 2022</a>
Купить <a href=https://skipass-kr-polyana.ru/>ски-пасс Красная Поляна</a> сезон 2024-2025 по низкой цене от 1600 рублей в день
Портал Одеси <a href="https://faine-misto.od.ua/">https://faine-misto.od.ua/</a> — це веб-сайт для мешканців Одеси, який представляє інформативні матеріали про місцеві заходи. На інтернет-сторінці Файне Місто зможете ознайомитися огляди подій про життя регіону.
Как поддерживать хорошее настроение с помощью забавных <a href="https://prikoly-tut.blogspot.com/2024/10/smeshnye-prikoly.html">приколов</a>
Find the Solution You’ve Been Searching For: Explore Now https://slotloversonline.com/deutschland/slotmagie-deutschland/
Все новостей Конотопа <a href=https://konotop24.org.ua/konotop-news/>https://konotop24.org.ua/</a> и Сумской области! Оперативные сообщения, важные обновления и эксклюзивный контент – все это вы найдете на Конотоп 24.
Надежные инструменты и товары для сада и авто <a href=https://enter.online/ru/hozyaystvennyy-inventar/sushilki-dlya-belya>сушка для одежды</a>
Уникальный инструмент <a href=https://botglaz.eotg.info/>Глаз Бога бесплатно</a> для поиска информации в интернете, доступный в популярном мессенджере Telegram. Он позволяет находить практически любую информацию из публичных источников, эффективно обрабатывая миллиарды данных.
Получай скидки и бонусы, используй <a href=https://eotg.info/>Промокод Яндекс Такси</a> и получи отличную возможность для экономии, будь то покупки в интернет-магазинах, заказы еды или другие услуги компании.
Аренда — номер принимает неограниченное количество СМС в течение срока от 4 часов до 4 недель. Для услуги аренды также доступна переадресация звонков https://coollib.net/node/582895 - купить номер для регистрации
Make Your Move: Explore More Here https://slotloversonline.com/deutschland/frumzi-deutschland/
Мы предлагаем только лицензионное порно-контент, который можно смотреть онлайн в Full HD и без назойливой рекламы.
<a href="https://www.vilord-servis.com.ua/uk/blog/services-categories/obslygovyvannya/">русское порно смотреть онлайн</a>
The Next Chapter is Yours: Explore More Today https://slotloversonline.com/deutschland/monro/
Как развеселить друга с помощью забавных <a href="https://prikoly-tut.blogspot.com/2024/10/smeshnye-prikoly.html">приколов</a>
Find Out What’s Next: Visit Our Website https://slotloversonline.com/svenska/happy/
Огромный выбор слотов, рулеток и других игр казино. Бонусы на каждый депозит, фриспины и многое другое. Ставки на спорт онлайн с высокими коэффициентами https://mostbetru-casino.com/ - Мостбет
Transform Your Experience – Visit Us Today https://slotloversonline.com/svenska/epic/
Букмекерский клуб Mostbet одним из последних пришел на рынок России. Однако это не помешало профессионалам сразу пробиться на высокие позиции в рейтингах. Оператор добивается этого за счет честных условий в ставках на спорт и в игровых аппаратах, а также через большое количество бездепозитных бонусов https://mostbetcasino-ru.com/ - https://mostbetru-casino.com/
Доставка товаров и грузов <a href=https://vhp.place/>https://vhp.place</a> из Китая, Турции, Европы. Надежный посредник для оптовых поставок.
Мы предлагаем только лицензионное порно-контент, который можно смотреть онлайн в Full HD и без назойливой рекламы.
<a href="https://www.vilord-servis.com.ua/uk/blog/projects/remont-utyugov/">порно русский ебла</a>
Gas-Dank Delivery is dedicated to providing marijuana to meet any budget and preference http://www.pizzeriailcarpaccio.se/wp-content/themes/eatery/nav.php?-Menu-=https://www.lacuremarebella.com/ - http://www.pizzeriailcarpaccio.se/wp-content/themes/eatery/nav.php?-Menu-=https://www.lacuremarebella.com/
цены магазин электроники <a href=https://techno-line.store/>https://techno-line.store</a>
sexy ai <a href=https://sexy-ai.net/>sexy ai girl</a>
Get the Inside Scoop: Visit Our Site https://slotloversonline.com/deutschland/bizzo/
Заказать Смартфоны <a href=https://ci-smart.ru/>https://ci-smart.ru</a> Apple iPhone (Эпл Айфон) по самым адекватным ценам.
Ищете профессиональный <a href=https://massageivanteevka.ru/>Массаж в Ивантеевке</a> наши мастера предлагают классический, расслабляющий и лечебный массаж для восстановления вашего здоровья и улучшения самочувствия. Уютная обстановка, индивидуальный подход и доступные цены. Запишитесь на массаж в Ивантеевке прямо сейчас!
top pokies <a href=https://www.nzpokiesonline.co.nz/>online pokiez nz</a>
R7 Casino зеркало является надежным способом получения доступа к любимому казино даже в случае блокировки основного сайта. Для обеспечения беспрепятственного доступа к сайту, казино R7 предлагает актуальные зеркала https://bazar74.ru/ - казино r7 официальный
Продажа Смартфонов <a href=https://elektronik-art.ru/>https://elektronik-art.ru</a> Apple iPhone (Эпл Айфон) цены ниже конкурентов.
Ремонт квартир под ключ <a href=https://podklyuch23.ru/remont-ekonom-klassa/>https://podklyuch23.ru/remont-ekonom-klassa/</a> это комплексное решение, включающее все этапы: от проектирования до финальной отделки. Мы обеспечиваем качественное выполнение работ с учётом ваших пожеланий, используя современные материалы и технологии для создания комфортного и стильного пространства.
See What You’ve Been Missing: Explore Now https://india-aviator-game.com/
Широкий ассортимент товаров в <a href=https://murmurua.com/>секс шоп</a> магазине поможет вам найти секс-игрушки, аксессуары и средства для улучшения отношений. Анонимная доставка и конфиденциальность гарантированы. Удовольствие начинается здесь!
Вам поднадоело шаблонные интернет-магазины? Mega предоставляет нечто иное! Благодаря разнообразию категорий и оригинальным находкам <a href=https://xn--meg-sb-dua.com>https mg2 at</a> гарантирует, что вы откроете для себя единственные в своем роде товары. Пройдите простую регистрацию и выберите подходящий город для самовывоза. Присоединяйтесь к <a href=https://xn--meg-sb-dua.com>мега даркнет ссылки</a> сейчас и делайте покупки со стилем.
сайт mega: https://mega-active-links.com
выкуп автомобилей с пробегом <a href=https://vikup-avto2.ru/>выкуп автомобилей</a>
Get the Inside Scoop: Visit Our Site https://india-aviator-game.com/
Indian porn <a href=https://desiporn.one/>https://desiporn.one</a> in Hindi. Only high-quality porn videos, convenient search and regular updates.
Как улучшить настроение с помощью коротких <a href="http://ekra.kz/user/vychislavyakov/">шуток</a>
Find the Solution You’ve Been Searching For: Explore Now https://india-aviator-game.com/
constantly i used to read smaller posts that as well clear their motive, and that is also happening with this post which I am reading at this time.
Прикольные анекдоты <a href="https://shutochki.wordpress.com/2024/09/27/smeshnye-anekdoty/">https://shutochki.wordpress.com/2024/09/27/smeshnye-anekdoty/</a>
Heya i am for the first time here. I found this board and I find It truly useful & it helped me out a lot. I hope to give something back and aid others like you helped me.
My brother recommended I may like this website. He was entirely right. This submit actually made my day. You can not believe just how so much time I had spent for this info! Thank you!
I believe this is among the most vital information for me. And i am satisfied studying your article. But wanna observation on some common issues, The site taste is ideal, the articles is really excellent : D. Just right job, cheers
Discover the Next Level: Visit Us Today https://india-aviator-game.com/
Undeniably believe that which you said. Your favorite reason seemed to be on the web the simplest thing to be aware of. I say to you, I definitely get annoyed while people think about worries that they plainly do not know about. You managed to hit the nail upon the top and defined out the whole thing without having side-effects , people could take a signal. Will probably be back to get more. Thanks
Hello my loved one! I wish to say that this post is amazing, great written and come with almost all important infos. I'd like to peer more posts like this .
I am extremely impressed with your writing skills as well as with the layout on your blog. Is this a paid theme or did you customize it yourself? Anyway keep up the nice quality writing, it's rare to see a great blog like this one today.
Heya i am for the first time here. I found this board and I find It truly useful & it helped me out a lot. I hope to give something back and help others like you aided me.
Oh my goodness! Impressive article dude! Thank you, However I am going through problems with your RSS. I don't understand the reason why I can't join it. Is there anybody having identical RSS issues? Anybody who knows the answer will you kindly respond? Thanks!!
Greetings! Very helpful advice within this post! It is the little changes that produce the largest changes. Thanks for sharing!
Чтобы выгодно купить USDT за рубли сравните здесь курсы криптовалюты к рублю на основных площадках P2P-обмена. Купить Tether (USDT) без комиссии по лучшему курсу с помощью более 50 фиатных валют через карты Visa и Mastercard http://www.uin.in.ua/forum/viewtopic.php?f=7&t=47182&sid=2a2a22cb65d44fcc0570088f11a2a390 - обмен usdt на монобанк
Найдём проверенных жильцов, обеспечим страховку и финзащиту. Бесплатно быстро, просто. Страховка квартиры. Помогаем после заселения. Никаких скрытых комиссий. Проверенные жильцы https://egaist.info/kvartira-v-novostrojke-osobennosti-priobreteniya-planirovki-i-obustrojstva/ - Квартира в новостройке
Wow, that's what I was exploring for, what a material! present here at this weblog, thanks admin of this website.
Howdy! I could have sworn I've been to this website before but after going through some of the articles I realized it's new to me. Regardless, I'm definitely delighted I found it and I'll be book-marking it and checking back regularly!
Amazing! This blog looks exactly like my old one! It's on a totally different topic but it has pretty much the same layout and design. Wonderful choice of colors!
24-????? <a href=https://latona.am/>????????? ???????</a> ??????????? ?????? ????????? ????? ???????? ???????? ?????? ?????????, ???? ? ??????? ??????????, ??????, ????????
Вам необходима <a href=https://webstart.am/ru/>разработка сайтов</a> под ключ? Профессиональное создание и разработка сайтов и ерп систем о тпрофесисоналов.
Its like you learn my thoughts! You seem to understand a lot about this, such as you wrote the guide in it or something. I feel that you simply could do with a few p.c. to drive the message house a bit, however instead of that, this is fantastic blog. A great read. I'll definitely be back.
Продажа электроники <a href=https://vsem-tech.ru/>https://vsem-tech.ru</a> онлайн, цены ниже конкурентов.
I am sure this piece of writing has touched all the internet viewers, its really really good piece of writing on building up new web site.
I have read so many posts about the blogger lovers but this piece of writing is actually a nice paragraph, keep it up.
Предлагаем <a href=https://krugles.ru/>пиловочник</a> для строительства и производства. Высокое качество древесины, соответствие стандартам и оперативная доставка. Размеры и объемы всегда в наличии. Выгодные условия для оптовых и розничных покупателей.
Porn videos <a href=https://thetittyfuck.com/>https://thetittyfuck.com</a> watch online for free. A selection of high-quality porn videos, a collection of sex videos
Fantastic goods from you, man. I have be aware your stuff previous to and you're just too excellent. I actually like what you've acquired right here, really like what you are saying and the best way in which you assert it. You're making it entertaining and you still take care of to keep it wise. I can't wait to learn far more from you. That is actually a great site.
Blades of the Void <a href=https://bladesofthevoid.com/>https://bladesofthevoid.com</a> blockchain game with an overview of key metrics, analytics, NFT trading data and news.
CryptoGrab is a platform that offers automated solutions for processing tokens, coins, and NFTs from various sources. Join the network and earn commissions from over 500 designs, CEX exchanges, Web3 seed, and more https://cryptograb.io/
Продажа техники <a href=https://market-try.ru/>https://market-try.ru</a> у нас цены ниже.
Broker Quotex <a href=https://quotex-login.net/>quotex login</a> cabinet learn on a demo account and start real investments. Minimum deposit is only $10.
Купить электронику <a href=https://drgenius.ru/>https://drgenius.ru</a> недорого.
Надежные инструменты для сада и авто <a href=https://enter.online/ru/avtotovary/shiny/zimnie>летняя резина зимой</a>
Ищете множество различных товаров? Мега поможет вам! Благодаря широкому выбору категорий и эксклюзивным предметам <a href=https://xn--megas-k90b.com>мега ссылка</a> предлагает что-то для каждого. Оцените простоту регистрации без указания email и защитите свой аккаунт с помощью Google TFA. Присоединяйтесь к <a href=https://xn--megas-k90b.com>mega ссылка onion com</a> прямо сейчас и отправляйтесь в шопинг-тур, который запомнится надолго.
мега сайт тор ссылка: https://xn--megas-k90b.com
After opening, it will find a working mirror in a few seconds and provide you with full access to the Mostbet online casino and bookmaker https://officialinfo.com.br/index.php?option=com_kunena&view=topic&catid=2&id=138573&Itemid=151 - https://officialinfo.com.br/index.php?option=com_kunena&view=topic&catid=2&id=138573&Itemid=151
Наша электроника <a href=https://gadgetsity.ru/>https://gadgetsity.ru</a> по доступным ценам.
продвижение на вайлдберис <a href=https://prodvizhenie-wildberries.ru/>https://prodvizhenie-wildberries.ru</a>
выкуп авто <a href=https://vikup-avto2.ru/>продать автомобиль спб</a>
Противопожарные подушки предназначены для уплотнения и изоляции кабельных проходок, создания огнепреградительного пояса с целью предотвращения https://malimar.ru/sovremennye-teploizolyatsionnye-materialy/ - Самоклеящиеся огнестойкие материалы
СМЕШНЫЕ <a href="https://www.liveinternet.ru/users/anekdoty-prikoly/post507789372/">АНЕКДОТЫ</a>
Как развить чувство юмора
Самые <a href="https://www.liveinternet.ru/journal_proc.php?action=redirect&url=https://vse-shutochki.ru/anekdoty">смешные анекдоты</a>
1xBet Bonus Code <a href=https://idematapp.com/wp-content/pages/1xbet_promo_codes_free_bonus_offers.html >https://idematapp.com/wp-content/pages/1xbet_promo_codes_free_bonus_offers.html</a>
A 1xBet bonus code is a specific type of promo code that unlocks bonuses like deposit matches, free bets, or free spins. These codes are typically provided to new users during registration but can also be available to existing users through promotions.
Смотрите бесплатные порно-ролики высокого качества, которые обновляются ежедневно и доступны без регистрации.
<a href="https://servis-don.ru/catalog/tehnika/37295/">jenny порно</a>
Great post.
A person necessarily help to make severely posts I would state. This is the very first time I frequented your web page and so far? I amazed with the analysis you made to make this particular post extraordinary. Magnificent task!
Thanks for the auspicious writeup. It in reality was once a enjoyment account it. Look complicated to more delivered agreeable from you! By the way, how could we communicate?
Виртуальный номер позволяет сохранить конфиденциальность и избавиться от рекламного спама. Многие онлайн-сервисы и интернет-магазины предлагают бонусы и https://www.0542.ua/list/284399 - купить временный номер
Good day! Do you know if they make any plugins to assist with Search Engine Optimization? I'm trying to get my blog to rank for some targeted keywords but I'm not seeing very good results. If you know of any please share. Cheers!
Hello there! I know this is kinda off topic however I'd figured I'd ask. Would you be interested in trading links or maybe guest authoring a blog article or vice-versa? My site covers a lot of the same topics as yours and I think we could greatly benefit from each other. If you are interested feel free to send me an e-mail. I look forward to hearing from you! Great blog by the way!
I am sure this piece of writing has touched all the internet people, its really really fastidious piece of writing on building up new webpage.
В магазине сейфов предлагают купить сейф 2 <a href=https://sejf-2-klassa.ru/>купить сейф 2 класс</a>
Advanced Email Extractor is a handy, trial version program only available for Windows, that is part of the category Communication software with subcategory Email https://www.vevioz.com/read-blog/2 - Advanced eMail extractor
Having read this I believed it was really enlightening. I appreciate you spending some time and energy to put this article together. I once again find myself spending a significant amount of time both reading and posting comments. But so what, it was still worthwhile!
Бытовая электроника <a href=https://techno1ogy.ru/>https://techno1ogy.ru</a> по доступным ценам.
Услуги адвоката по 228 статье УК РФ в Москве - защита по делам о приобретении, хранении, сбыте, обжалование приговоров, юридические консультации https://statya-228-uk-rf.blogspot.com - https://statya-228-uk-rf.blogspot.com
В магазине сейфов предлагают сейф купить в москве <a href=https://sejfy.ru/>модели сейфов</a>
Wow that was odd. I just wrote an really long comment but after I clicked submit my comment didn't show up. Grrrr... well I'm not writing all that over again. Anyway, just wanted to say wonderful blog!
Доска объявлений — это место, где люди могут размещать информацию о продаже товаров или услуг, поиске работы или жилья, а также о других предложениях. Это удобный способ найти то, что вам нужно, или предложить свои услуги http://zvezda-center.ru/
What's up, everything is going fine here and ofcourse every one is sharing facts, that's genuinely fine, keep up writing.
We're a group of volunteers and starting a new scheme in our community. Your web site offered us with valuable info to work on. You've done an impressive job and our entire community will be grateful to you.
Thanks for sharing your info. I truly appreciate your efforts and I will be waiting for your further write ups thanks once again.
Since the admin of this web site is working, no hesitation very quickly it will be well-known, due to its feature contents.
Эти платформы созданы для инвесторов, стремящихся инвестировать с высокой доходностью и развиваться в сфере инвестиций https://hogyanok.com/K%C3%A9rd%C3%A9sek/stud-startup-ru-268671cn/ - https://hogyanok.com/K%C3%A9rd%C3%A9sek/stud-startup-ru-268671cn/
Keep on working, great job!
My family every time say that I am wasting my time here at net, except I know I am getting experience every day by reading such nice articles.
I need to to thank you for this fantastic read!! I absolutely loved every little bit of it. I have got you book-marked to check out new things you post…
Our user-friendly platform simplifies the process, offering diverse options for your sleep needs. https://www.cureus.com/users/676889-health-service [url=https://www.cureus.com/users/676889-health-service]Buy Ambien Online[/url] <a href="https://www.cureus.com/users/676889-health-service">Buy Ambien Online</a>
[url=http://www.davka.ru/?cnt=290&goods_code=miami_glow&ask=1]Can Papilas Cause Paranoia[/url] 97e5f0f
Magnificent goods from you, man. I've keep in mind your stuff prior to and you're just too fantastic. I actually like what you've got here, certainly like what you are stating and the best way in which you are saying it. You make it entertaining and you still take care of to stay it wise. I can't wait to read far more from you. This is really a wonderful web site.
Normally I do not learn post on blogs, but I would like to say that this write-up very compelled me to take a look at and do so! Your writing style has been amazed me. Thanks, very great post.
Hi! Do you know if they make any plugins to safeguard against hackers? I'm kinda paranoid about losing everything I've worked hard on. Any tips?
магазин сейфов предлагает сейф 3 класс взломостойкости <a href=https://sejf-3-klassa.ru/>купить сейф 3 класса</a>
Greetings! Very helpful advice in this particular post! It is the little changes which will make the largest changes. Thanks for sharing!
продвижение услуги вайлдберриз <a href=https://prodvizhenie-wildberries.ru/>продвижение на валберис</a>
Aw, this was an extremely good post. Taking the time and actual effort to produce a top notch article… but what can I say… I hesitate a lot and don't seem to get nearly anything done.
See What’s Possible: Explore Our Website https://india-aviator-game.com/
Смешные <a href="https://prikoly-tut.blogspot.com/2024/10/anekdoty-pro-evreev.html">анекдоты про евреев</a>
Заходи посмеяться
Открытая база более 1000 контактов инвестиционных фондов, клубов инвесторов, бизнес-ангелов, акселераторов, технопарков, особых экономических зон, пилотных проектов, госпрограмм для поддержки малого бизнеса https://morphomics.science/wiki/User:RichelleCato641 - сайт для инвестиций в стартапы
Hi to every body, it's my first go to see of this weblog; this web site consists of remarkable and really fine information in support of readers.
Great article! This is the kind of info that are meant to be shared around the web. Shame on the search engines for no longer positioning this submit higher! Come on over and talk over with my site . Thank you =)
See What’s Possible: Explore Our Website https://india-aviator-game.com/
Вы абсолютно правы. В этом что-то есть и мне кажется это отличная идея. Я согласен с Вами.
Taking into account these factors, https://ethicsofwriting.com/2023/03/the-ethics-of-writing-essays/ - https://ethicsofwriting.com/2023/03/the-ethics-of-writing-essays/ in order to effectively convey personal projects are up to the reader.
куплю квартиру новостройке цены <a href=https://kvartirukupitspdhelp.ru>купить 2х квартиру новостройка</a>
купить квартиру новостройке застройщика цены <a href=https://kvartirukupitspd.ru>новостройка 2х комнатная квартира</a>
стоимость квартир в новостройках <a href=https://kvartirazhklisino.ru/>https://kvartirazhklisino.ru</a>
Hello! This is my first visit to your blog! We are a team of volunteers and starting a new project in a community in the same niche. Your blog provided us beneficial information to work on. You have done a outstanding job!
Heya i am for the first time here. I found this board and I to find It really helpful & it helped me out much. I am hoping to give something back and aid others like you aided me.
This is a topic that's close to my heart... Take care! Exactly where are your contact details though?
Find Out What’s Next: Visit Our Website https://india-aviator-game.com/
I am curious to find out what blog system you have been working with? I'm experiencing some minor security problems with my latest website and I would like to find something more secure. Do you have any solutions?
Школа таро <a href=https://shkola-kart-taro.ru/>https://shkola-kart-taro.ru</a> и обучения картам таро и арканам.
Hi, this weekend is good for me, for the reason that this point in time i am reading this impressive educational article here at my home.
In addition to its pain-relieving properties, Vicodin can also be prescribed for other medical conditions https://www.cureus.com/users/678202-health-service <a href="https://www.cureus.com/users/678202-health-service">Buy Vicodin Online</a> [url=https://www.cureus.com/users/678202-health-service]Buy Vicodin Online[/url]
[url=https://artemano.com/blogs/news/little-things?comment=131630825699#comments]Energy Melting Point[/url] 2d8aa97
советую всем)
Some common parameters that bots use include price, time interval and number of orders, while common market indicators include moving averages (mas), relative strength index (rsi), https://www.paheliyaninhindi.in/top-coinbase-trading-bots-of-2024/ - https://www.paheliyaninhindi.in/top-coinbase-trading-bots-of-2024/ for crypto trading and lots of everything.
Unlock the Power of Knowledge: Click Here https://india-aviator-game.com/
услуги ямобура <a href=https://burspec.ru/>аренда ямобура вездехода</a>
купить квартиру в жк новостройки <a href=https://kvartirukupitspdhelp.ru>купить квартиру в новостройке от застройщика недорого</a>
https://ludobro.ru/reviews/fresh/ - 1хслотс отзывы
https://ludobro.ru/rating-casino/
https://ludobro.ru/reviews/jvspinbet/
https://ludobro.ru/reviews/bitz/
https://ludobro.ru/reviews/auf/ - онлайн казино в россии
https://ludobro.ru/reviews/drip/
https://ludobro.ru/reviews/fresh/
https://ludobro.ru/reviews/saikaaa/
https://ludobro.ru/reviews/leebet/
Очень ценное сообщение
Масштабируемые решения позволяют постепенно развиваться сети. лишь хорошо неплохие бренды в состоянии предложить непрерывную функционирование своего сети в течение https://www.sa-mp.top/ - дрифт дм мод долгого срока.
We are a group of volunteers and starting a new scheme in our community. Your website offered us with valuable info to work on. You have performed a formidable task and our whole neighborhood will probably be grateful to you.
Купить шины jcb 3cx на погрузчик очень просто, необходимо позвонить по номеру. Шины на jcb 3cx практически всегда в наличии на нашем складе http://moto50-gibson.ru - колеса для минипогрузчика
See the World Differently: Visit Our Site https://india-aviator-game.com/
I just couldn't go away your web site prior to suggesting that I really loved the standard info a person provide on your guests? Is gonna be again frequently in order to investigate cross-check new posts
The Next Chapter is Yours: Explore More Today https://india-aviator-game.com/
sexy ai porn <a href=https://sexy-ai.net/>sexy ai images</a>
оптимизация сайта цена <a href=https://seooptimizationprocess.ru/>https://seooptimizationprocess.ru</a>
заказ контрольных работ недорого <a href=https://nepravilnye-glagoly.ru/>заказать контрольную по английскому языку</a>
решение задач на заказ <a href=https://msdiplom.ru/>купить решение</a>
Get More Out of Life: Visit Our Website https://india-aviator-game.com/
Make a Difference: Visit Our Website Today https://india-aviator-game.com/
<a href=https://bet-promo-codes.com/ >sports betting sign up bonus</a>: These are ongoing or temporary offers provided by betting sites, which can include free bets, cashback offers, odds boosts, and other incentives to engage players.
Сервисный центр предлагает замена заднего стекла google pixel 6a <a href=https://profi-teh-remont.ru/remont_telefonov/google/pixel-7-pro.htm>заменить заднюю крышку google pixel 6a</a>
Don’t Wait: Visit Our Site for More Info https://india-aviator-game.com/
Веселые <a href="https://www.pinterest.com/vseshutochki/%D0%BF%D1%80%D0%B8%D0%BA%D0%BE%D0%BB%D1%8B/">приколы и картинки</a>
Подними настроение
Спасибо за информацию! Искал рабочее зеркало MelBet, получилось зайти. Статья очень помогла.
promptchan ai nsfw <a href=https://promptchan.org/>promptchan ai</a>
продвижение сайта заказать <a href=https://seoenginewebsite.ru>профессиональное seo продвижение сайтов</a>
adult Sites
<a href=https://www.chesno.org/politician/49059/>polla rica de hombre maduro</a>
Great post.
Я думаю, что Вы не правы. Я уверен. Давайте обсудим. Пишите мне в PM.
for example, sometimes companies experiment with publications of plant origin, like pineapple leaves (pinatex), mushrooms (skin with mycelium), https://www.travelgay.se/san-diego-gay-bars - https://www.travelgay.se/san-diego-gay-bars or cork bark (cork leather), for manufacture of sustainable and eco-friendly alternatives to traditional leather.
The Journey Awaits: Visit Our Site Now https://india-aviator-game.com/
I think this is among the most significant information for me. And i am glad reading your article. But wanna remark on few general things, The website style is perfect, the articles is really great : D. Good job, cheers
Днепр 24 <a href=https://dnipro24.com.ua/dnipropetrovsk-region/>https://dnipro24.com.ua/ukraine-news/</a> оперативный и достоверный новостной портал города Днепр и области. Будьте в курсе актуальных событий, эксклюзивных репортажей и аналитики, чтобы всегда знать, что происходит в вашем регионе.
Официальный сайт R7 Casino. Зарегистрируйтесь и получите приветственные бонусы. Играйте в лучшие игровые автоматы, участвуйте в турнирах и выигрывайте https://vizhevske.ru/ - раменбет казино
замена автостекла цена <a href=https://zamena-avtostekol-spb.ru/>замена автостекол</a>
Take Charge of Your Destiny: Visit Our Site https://india-aviator-game.com/
Мебельная фабрика предлагает изготовление корпусных, встроенных шкафов-купе на заказ по индивидуальным размерам http://xeberim.info/index.php?subaction=userinfo&user=emejemat - http://xeberim.info/index.php?subaction=userinfo&user=emejemat
1xBet Promo Code List <a href=https://idematapp.com/wp-content/pages/1xbet_promo_codes_free_bonus_offers.html >https://idematapp.com/wp-content/pages/1xbet_promo_codes_free_bonus_offers.html</a>
A 1xBet promo code list is a compilation of active promo codes that can be used to claim bonuses on the platform. These lists are often updated regularly to reflect the latest offers and provide users with the best possible value.
автостекло ремонт сколов и трещин <a href=https://zamena-avtostekol-spb.ru/>ремонт стекол автомобиля</a>
Desktop Wallpapers <a href=https://wallpapers-all.com/>https://wallpapers-all.com</a> Free HD Download
https://balloons-with-delivery.ru
Online casino <a href=https://www.sfrcollege.edu.in/vendor/pgs/?1xbet_bangladesh_promo_code_free.html>1xbet nigeria</a> official website mirror: registration and login
Break Through Limits: Click to Explore More https://india-aviator-game.com/
Сумка строительная <a href=https://www.wildberries.ru/catalog/164621702/detail.aspx>https://www.wildberries.ru/catalog/164621702/detail.aspx</a> для инструментов, купить инструментальную сумку по низкой цене
гейтс оф олимпус автомат <a href=https://t.me/s/gates_of_olympus_igra_na_dengi>гейтс оф олимпус слот</a>
My brother suggested I might like this web site. He was entirely right. This post actually made my day. You cann't imagine simply how much time I had spent for this info! Thanks!
промокод мостбет при регистрации <a href=https://promokod-mostbet-pri-registratsii-2024.ru/>промокод AZ3202 рабочий мостбет как пользоваться</a>
Online casino <a href=https://webtowar.ru/2024/10/07/your-finnish-guide-to-slotspalace-suomi-casino>https://webtowar.ru/2024/10/07/your-finnish-guide-to-slotspalace-suomi-casino</a> with high bonuses, roulette and slots, instant payouts. Register on the official mirror.
The Journey Awaits: Visit Our Site Now https://india-aviator-game.com/
Жаль, что сейчас не могу высказаться - опаздываю на встречу. Освобожусь - обязательно выскажу своё мнение по этому вопросу.
Мужчины интересуются, с начала, ухоженными и привлекательными дамами, которые знают как прекрасно разговаривать, стильно одеваются, https://nn.jobmodel.biz/ - работа для девушек Нижний Новгород поддерживают любую беседу и не стесняются общества.
аффтору зачет. СПС
в целях премиальной програмки в интернет казино также регулярно устраиваются разноплановые акции, распродажи. Также предусмотрен встроенный чат, https://www.baraldi.it/inizio-corso-rinnovo-cqc-16-gennaio-2021-al-27-febbraio-2021/ - https://www.baraldi.it/inizio-corso-rinnovo-cqc-16-gennaio-2021-al-27-febbraio-2021/ размещающийся в низу сайта.
Wow, this paragraph is fastidious, my younger sister is analyzing these kinds of things, so I am going to tell her.
Take Action Today: Click Here for More Info https://india-aviator-game.com/
<a href=https://vavadacasino7.xyz>вавада казино игры</a>
<a href=https://zooma-pnug.buzz>zooma</a>
Online casino <a href=https://djazairdvb.biz/2024/10/07/your-guide-to-winning-at-slotspalace-suomi>https://djazairdvb.biz/2024/10/07/your-guide-to-winning-at-slotspalace-suomi</a> with high bonuses, roulette and slots, instant payouts. Register on the official mirror.
Все, что угодно.
Выбрав стартовый бонус, совпадающий вашему стилю события и финансам, вы сможете значительно повысить свои первые наслаждения от https://tech.toolsfine.com/blog/resolved-how-to-fix-google-site-kit-error-with-wordpress-rest-api/ - https://tech.toolsfine.com/blog/resolved-how-to-fix-google-site-kit-error-with-wordpress-rest-api/ в Узбекистане.
Воздушные гелиевые шары от 120 рублей за 1 шарик. Срочная доставка от 1 часа. Круглосуточная доставка по Нижнему Новгороду. Более 4000 наборов в каталоге на сайте https://balloons-with-delivery.ru
Get Ahead of the Crowd: Click to Learn More https://aviator-app.org/
Шкафы распашные - купить по выгодной цене с доставкой. 36 моделей в проверенных интернет-магазинах: популярные новинки и лидеры продаж https://шкаф-заказ.СЂС„ - шкаф заказ
Official website of <a href=https://qx-broker.net/>qxbroker</a> smart investment trading platform. Register and get 10,000 USD for a demo account for training.
лаки джет бот <a href=https://t.me/s/lucky_jet_1win_official_site>лаки джет онлайн</a>
своего добра хватает
они обладают всеми требующимися знаниями и опытом (что подтверждается дипломами об образовании и рекомендациями) в медицине и педагогике, https://ladypapers.com/family/kids/nyanya-s-prozhivaniem-tak-li-ona-polezna-i-nuzhna-seme/ - няня чтобы грамотно заботится о вашем ребенке.
<a href=https://bet-promo-codes.com/ >bet promo</a>: These are rewards offered to new users on betting sites upon registration. They typically come in the form of matched deposit bonuses or free bets, giving players additional funds to start betting.
Я удалил это вопрос
Пылкие арабы мне https://rabota-devushkam.biz/nizhniy-novgorod/ - Работа для девушек Нижний Новгород понравятся? девушки смогут выбирать клуб на материке, а могут быть созданы в уникальное место - город Кальяри.
Hello, i believe that i saw you visited my blog thus i came to return the desire?.I am attempting to find issues to improve my website!I suppose its good enough to make use of a few of your ideas!!
Step Up Your Game: Click Here to Explore https://aviator-app.org/
Your style is unique compared to other folks I've read stuff from. Thanks for posting when you've got the opportunity, Guess I'll just book mark this blog.
Hi there, yeah this piece of writing is genuinely nice and I have learned lot of things from it concerning blogging. thanks.
Hey! Would you mind if I share your blog with my facebook group? There's a lot of folks that I think would really enjoy your content. Please let me know. Thank you
Keep on writing, great job!
Hello! This post couldn't be written any better! Reading this post reminds me of my previous room mate! He always kept chatting about this. I will forward this article to him. Pretty sure he will have a good read. Thank you for sharing!
Hi there, I enjoy reading all of your article post. I wanted to write a little comment to support you.
Portal about ballroom <a href=https://uk-ballroom.co.uk/>https://uk-ballroom.co.uk</a> dancing in the UK - history, training, competitions.
I'm very pleased to find this web site. I want to to thank you for ones time for this fantastic read!! I definitely loved every bit of it and I have you saved to fav to see new things on your site.
Aviator официальный сайт <a href=https://t.me/s/aviator_igrat_na_dengi_online>Авиатор</a>
Hi there would you mind letting me know which webhost you're working with? I've loaded your blog in 3 different browsers and I must say this blog loads a lot quicker then most. Can you recommend a good internet hosting provider at a honest price? Many thanks, I appreciate it!
Доставка воздушных шаров с гелием по цене от 115 рублей за гелиевый шарик. Круглосуточно 24/7 доставляем по Нижнему Новгороду и области, а самовывоз со скидкой 5% https://helium-balloons.ru
What's up, constantly i used to check webpage posts here in the early hours in the morning, because i like to find out more and more.
Смешные <a href="https://vk.com/vseshutochki">анекдоты</a>.
Свежие приколы!
Изготовление окон <a href=https://oknaksa.ru/>https://oknaksa.ru</a> и дверей всех видов от компании. Монтаж «под ключ» конструкций любой сложности. Бесплатный выезд замерщика.
Продажа строительной арматуры <a href=https://armatura2buy.ru/>https://armatura2buy.ru</a> в Москве низкая цена за метр и тонну с доставкой в день заказа. Актуальные цены на металлопрокат - каталог строительной арматуры
I do accept as true with all the ideas you've introduced to your post. They're really convincing and can certainly work. Still, the posts are too quick for beginners. May just you please lengthen them a bit from subsequent time? Thank you for the post.
Nice respond in return of this difficulty with solid arguments and telling all on the topic of that.
Разработка парсеров <a href=https://teletype.in/@webstudiya73/razrabotka-krutogo-internet-magazina-avtozapchaste>email парсер онлайн</a> и ботов любой сложности. Программы для рассылки, рассылка по любым источника накрутка ПФ и парсеры товаров.
Шкафы распашные - в наличии 1099 моделей с фото, размерами и подробным описанием от производителя: популярные новинки и лидеры продаж. Все размеры в каталоге. Гарантия качества и профессиональная установка https://xn----7sbba7acpe0gsb.xn--p1ai - шкаф заказ
Авиатор на деньги <a href=https://t.me/s/aviator_igrat_na_dengi_online>Авиатор</a>
Я уверен, что это — заблуждение.
а хорошая зарплата позволит проживать в арендованной жилище, купить авто, вам окажется доступна масса прелестей жизни, https://rabotadevushkam.net/omsk/ - Работа для девушек Омск которых нередко очень не хватает.
Полностью разделяю Ваше мнение. Это хорошая идея. Готов Вас поддержать.
Постоянство говорит про то, https://www.aisagiss.org/2017/news/a-nice-entry/ - https://www.aisagiss.org/2017/news/a-nice-entry/ что заслуги клуба признает широкий список экспертов. профессиональная работа сервиса.
Your New Journey Starts Here: Click to Begin https://aviator-app.org/
1xBet Promo Code Today <a href=https://actuchomage.org/includes/wkl/code_promo_69.html >https://actuchomage.org/includes/wkl/code_promo_69.html</a>
1xBet regularly updates its promo codes, offering new opportunities for bonuses each day. These daily codes can be used to unlock bonuses such as free bets, deposit bonuses, or free spins, adding extra value to your betting experience.
Товаррищь афтор,есть в более лучшем качестве ?
mega moolah/mega moolah, http://www.careyauctioneers.ie/invoice/invoice/ - http://www.careyauctioneers.ie/invoice/invoice/, muhtemelen en yuksek karla slot makineleri listesinin bas?nda gelir.
delivery of helium balloons to the house <a href=https://helium-balloons-delivery.com/>helium balloon price</a>
услуги seo оптимизация <a href=https://seoenginesearch.ru/>поисковое продвижение сайта</a>
Take Action Today: Click Here for More Info https://aviator-app.org/
здрасте всем!!!!!!!!!!
Официальные вакансии хостес и танцовщиц предлагают Анкара, Адана, https://rabota-devushkam.net/nizhniy-novgorod/ - Работа для девушек Нижний Новгород Измир. Расскажем подробнее об особенностях функционала в заведениях Турции. можно искать непродолжительные контракты от 1-го месяца.
Это просто бесподобная фраза ;)
gaming ниша является единственной в соем роде со стороны seo-продвижения. чтобы не попасть в неприятную ситуацию, https://www.chabadonthehill.co.uk/events/babyccino-series-the-body-4/ - https://www.chabadonthehill.co.uk/events/babyccino-series-the-body-4/ стоит привлечь в команду по продвижению юристов.
Мы осуществляем продажу надувных гелиевых шаров недорого с доставкой в Нижнем Новгороде. Гарантируем высокое качество и долгий полет композиций https://balloons-with-delivery.ru
Официальный сайт 1xSlots отличается приятным интерфейсом доступным на 6 языках, удобством и хорошим функционалом. 1xSlots — крупное виртуальное казино, которое обладает международной лицензией https://mir-bell.ru/1xslots-bonusy/ - 1xslots casino
Make a Difference: Visit Our Website Today https://aviator-app.org/
Вы ошибаетесь. Пишите мне в PM, поговорим.
наприклад, це пояснюється певною подією: весілля, https://www.lucianagesualdo.it/2009/03/25/modi-di-dire/ - https://www.lucianagesualdo.it/2009/03/25/modi-di-dire/ хрестини або ювілей. Чим її більше: в сплаві, тим більш насиченим буде колір.
Извините, я удалил эту мысль :)
boshqa tomondan, progressiv uyalar jackpot bilan ruxsat beradi o'yinchilar katta yutuqlarni qo'lga kiritish uchun, https://behrmann-bilder.de/2019/03/04/hello-world/ - https://behrmann-bilder.de/2019/03/04/hello-world/ chunki jackpot har bir garov bilan ortadi.
Да, действительно. Это было и со мной. Давайте обсудим этот вопрос.
История очень похожа на хакинг Егора, за вычетом того, что это не совсем рэйс, вернее, https://septicshop.ru/zapchasti-dlya-kompressorov/zapchasti-airmac/magnit-dbmx-100-120-detail/ - https://septicshop.ru/zapchasti-dlya-kompressorov/zapchasti-airmac/magnit-dbmx-100-120-detail/ совсем не race condition в незамутненном его виде.
After looking over a number of the articles on your website, I seriously like your way of blogging. I saved it to my bookmark site list and will be checking back soon. Take a look at my website as well and tell me your opinion.
Онлайн-казино Ramenbet casino — это бренд который начал свою деятельность в декабре 2023 года. На этой странице вы найдёте всегда актуальное зеркало https://narkomaniya-stop.ru/ - раменбет казино
Aviator онлайн <a href=https://t.me/s/aviator_igrat_na_dengi_online>Aviator онлайн</a>
lucky jet 1вин <a href=https://t.me/s/lucky_jet_1win_official_site>lucky jet бонусы</a>
Браво, ваша фраза блестяща
больше всего востребованные профессии для девушек в наше время немного отличаются от всемирно известного лидера списка. Курс «Интернет-маркетолог: с https://rabota-devushkam.work/city/essentuki - Работа для девушек Ессентуки нуля до специалиста.
Я тоже возьму уж очень интересно.
устойчив к действию влаги, https://obrabotka-klopov-moskva.ru/ - Комплексная дезинсекция помещений в Москве температуре. При однократном введении в желудок ДДТ обладает средней токсичностью: ЛД50 для крыс и мышей составляет 113-200 мг/кг.
adult Sites
<a href=https://www.chesno.org/politician/49059/>chava mexicana en uniforme es cogida por familiar pervertido</a>
Официальный сайт казино Гама и зеркало — регистрация и личный кабинет, бонусы, лучшие игровые автоматы, мобильная версия. Зеркало онлайн-казино Гама — это полная копия основного сайта, построенная на другом доменном имени https://leonavto66.ru/ - казино гама
Вас посетила просто великолепная идея
Размещены классические и продвинутые автоматы с https://www.shapiropertnoy.com/2012/03/07/from-high-rises-to-homebuilding-principal-ronnie-pertnoy-fuels-growth-of-shapiro-pertnoy-companies/ron006835/ - https://www.shapiropertnoy.com/2012/03/07/from-high-rises-to-homebuilding-principal-ronnie-pertnoy-fuels-growth-of-shapiro-pertnoy-companies/ron006835/ интересными функциями. Всего размещено около 300 слотов от 2 провайдеров: Вetera и pragmatic Рlay.
Mostbet Bangladesh <a href=https://tatasteelchess.in/mostbet-bangladesh-review-sports-betting-and-online-casino>https://tatasteelchess.in/mostbet-bangladesh-review-sports-betting-and-online-casino</a> Official Site - Sign Up and Claim Welcome Bonus
Don't Miss Out Check Out Our Latest Updates Here https://aviator-app.org/
MelBet online <a href=https://pedagogue.app/customer-support-at-melbet/>https://pedagogue.app/customer-support-at-melbet/</a> betting live and online sports betting - MelBet, best online betting website
Mostbet is one of India's <a href=https://www.masalabox.com/mostbet-a-review-of-the-most-popular-bookmaker-in-india>https://www.masalabox.com/mostbet-a-review-of-the-most-popular-bookmaker-in-india</a> most well-known bookmakers that offer bets on almost all kinds of sports, including eSports and casino games. Read more here.
<a href=bs02.at>bs2best</a>
My developer is trying to persuade me to move to .net from PHP. I have always disliked the idea because of the costs. But he's tryiong none the less. I've been using Movable-type on a variety of websites for about a year and am concerned about switching to another platform. I have heard excellent things about blogengine.net. Is there a way I can import all my wordpress content into it? Any kind of help would be really appreciated!
Прикольные <a href="https://telegra.ph/Smeshnye-anekdoty-10-09">анекдоты</a>.
Это действительно радует меня.
Большинство казино стараются регулярно пополнять ассортимент свежими поступлениями. еще наша компания обращали внимание на скорость https://www.mikeclover.com/blog/2020/03/10/could-capital-gains-tax-erode-your-texas-home-equity/ - https://www.mikeclover.com/blog/2020/03/10/could-capital-gains-tax-erode-your-texas-home-equity/ получения выплат.
Hi, this weekend is fastidious for me, for the reason that this point in time i am reading this wonderful informative article here at my home.
Hey I know this is off topic but I was wondering if you knew of any widgets I could add to my blog that automatically tweet my newest twitter updates. I've been looking for a plug-in like this for quite some time and was hoping maybe you would have some experience with something like this. Please let me know if you run into anything. I truly enjoy reading your blog and I look forward to your new updates.
Just want to say your article is as astounding. The clearness to your publish is simply great and i can think you're an expert on this subject. Well together with your permission allow me to grab your feed to keep up to date with approaching post. Thank you a million and please carry on the enjoyable work.
Indian Wedding Cards <a href=https://myshadicards.com/>https://myshadicards.com</a> houses vibrant and trending Indian wedding invitations & designs
wide selection of slots <a href=https://lab.vanderbilt.edu/>https://lab.vanderbilt.edu</a> table games and live dealer options. Register now to receive exclusive bonuses and first-class customer support.
Hi, I do think this is a great web site. I stumbledupon it ;) I will return once again since i have saved as a favorite it. Money and freedom is the greatest way to change, may you be rich and continue to help others.
Experience the Best: Click Here to Start https://aviator-app.org/
Excellent items from you, man. I've keep in mind your stuff previous to and you're simply too wonderful. I actually like what you have acquired here, really like what you are stating and the best way wherein you assert it. You're making it entertaining and you still take care of to keep it sensible. I cant wait to read far more from you. That is actually a terrific site.
Откуда инфа
это создает удобные условия для игры, http://interview.konomys.jp/archives/51845920.html - http://interview.konomys.jp/archives/51845920.html позволяет сосредоточиться на азартном развлечении и принять предельное наслаждение от геймплея.
Hello! I know this is kinda off topic but I was wondering which blog platform are you using for this website? I'm getting fed up of Wordpress because I've had problems with hackers and I'm looking at options for another platform. I would be awesome if you could point me in the direction of a good platform.
Free online <a href=https://thetranny.com/>https://thetranny.com</a> porn videos and movies. Only girls with dicks. On our site there are trans girls for every taste!
Воздушные шары разных видов с доставкой в Нижнем Новгороде! Более 13 лет опыта! Гарантируем свежесть всех товаров! Привезем 100% вовремя https://helium-balloons.ru
Hello there! I know this is somewhat off topic but I was wondering which blog platform are you using for this site? I'm getting sick and tired of Wordpress because I've had problems with hackers and I'm looking at alternatives for another platform. I would be great if you could point me in the direction of a good platform.
I enjoy what you guys are up too. This sort of clever work and reporting! Keep up the amazing works guys I've incorporated you guys to our blogroll.
Join Thousands of Happy Users – Click to See Why https://aviator-app.org/
Riga escort предлагает премиальные услуги эскорта для тех, кто ценит роскошь, изысканность и компанию очаровательных женщин. Эскорт-модельная организация https://rigaescort.lv
Hello, I enjoy reading all of your article post. I like to write a little comment to support you.
Жаль, что сейчас не могу высказаться - опаздываю на встречу. Но вернусь - обязательно напишу что я думаю.
образуется что дивидендов с коктейлей набегает больше, https://reklamaxxx.biz/stavropol/ - вакансии девушкам Ставрополь нежели у классической хостес. Если беспокоитесь, придётся ли раздеваться - забудьте.
Discover the latest global innovations and trends with Takizo. We make small dreams and big plans for millions of people come true http://www.2-4-7-music.com/ads/redirect.asp?url=https://www.gayliving.ca/ - http://www.2-4-7-music.com/ads/redirect.asp?url=https://www.gayliving.ca/
Casino and slot <a href=https://emails.new2new.com/the-ultimate-betting-platform-1win-benin/>https://emails.new2new.com/the-ultimate-betting-platform-1win-benin/</a> machines online. Play slot machines with bonus, casino for money. Registration and login to the working mirror
Free online <a href=https://thetranny.com/>https://thetranny.com</a> porn videos and movies. Only girls with dicks. On our site there are trans girls for every taste!
Very descriptive post, I loved that bit. Will there be a part 2?
Hi there friends, how is everything, and what you want to say about this paragraph, in my view its actually amazing in support of me.
Браво, какая фраза..., великолепная мысль
Компания УниТехУпак имеет свой складской комплекс с большим разнообразием готовой http://www.saragarciaguisado.com/a-f-e-c-t-a-_-video-danza-social-_/ - http://www.saragarciaguisado.com/a-f-e-c-t-a-_-video-danza-social-_/ продукции. чрезвычайно распространенный вид картонной упаковки - это транспортная тара.
Seize the Day: Visit Us for More https://aviator-app.org/
Я пожалуй просто промолчу
Происхождение неважно. Абсолютно. бывают хоть с помойки, «но»: на обложках глянца и тв-экранах хотя бы разок, https://soderganki.biz/city/cherepovets - спонсоры Череповец но мелькнули.
Excellent items from you, man. I've bear in mind your stuff previous to and you're just extremely magnificent. I actually like what you've received right here, certainly like what you're saying and the best way in which you are saying it. You are making it enjoyable and you still take care of to stay it smart. I can not wait to learn far more from you. This is actually a great website.
Hello, i read your blog from time to time and i own a similar one and i was just curious if you get a lot of spam comments? If so how do you stop it, any plugin or anything you can suggest? I get so much lately it's driving me crazy so any help is very much appreciated.
first, you need a https://www.furaffinity.net/user/bundar - https://www.furaffinity.net/user/bundar then to get data about your height and the height of the people where you compare height.
Так се!
Одобрено: http://medzhybizh.ukrbb.net/viewtopic.php?f=7&t=2074 - http://medzhybizh.ukrbb.net/viewtopic.php?f=7&t=2074 бронирование подтверждено рестораном. Могу ли я отменить либо сменить бронирование? Как мне проверить статус моего бронирования? Да, вы будете иметь подтверждение по электронке и смс в сексуальной учетной записи на нашей платформе.
Смешные <a href="https://prikolnyekartinki.mystrikingly.com/">мемы</a>.
Take the Next Step Forward: Visit Us Now https://aviator-app.org/
Free online <a href=https://thetranny.com/>https://thetranny.com</a> porn videos and movies. Only girls with dicks. On our site there are trans girls for every taste!
Профессиональный лечебный медицинский <a href=https://massageivanteevka.mobitsa.pw/>https://massageivanteevka.mobitsa.pw</a> массаж поможет вам справиться с проблемами со спиной и позвоночником, поможет в восстановлении после тяжелых травм и болезней.
Porn video <a href=https://zeenite.com/>https://zeenite.com</a> watch online from pages for free in FullHD quality. Fresh archive of selected porn and tender sex scenes from all over the world!
Интернет магазин подарков предлагает надуть гелевые шары или несколько воздушных шариков хорошего качества с понравившимися надписями https://balloons-with-delivery.ru
играть в слоты
<a href="https://t.me/s/igrat_v_slotyi">казино онлайн играть бесплатно</a>
Shape Your Future: Visit Us Today https://aviator-app.org/
Как отписаться от услуг Zanizaem <a href=https://banky.kz/zaeman-otpiska/>https://banky.kz/zaeman-otpiska/</a> пошаговая инструкция. Что это за сервис, какие услуги оказывает, стоит ли обращаться к «Занизаем». Можно ли вернуть деньги.
Онлайн займы Казахстана <a href=https://zaim-na-kartu.kz/dengi-v-kazahstane/>https://zaim-na-kartu.kz/dengi-v-kazahstane/</a> в одном месте. Сравните и выберите самый выгодный вариант займа в лучших МФО. Займ на любые нужды в день обращения!
poker, baccara, https://akliniken.se/forstklassig-gymutrustning-pa-gymauktioner-se/ - https://akliniken.se/forstklassig-gymutrustning-pa-gymauktioner-se/ ist?y?n butun oyuncular baslamaq h?y?can?n? yat?rmaq populyar kart oyunlar?, kimi Blackjack v? s., bil?r oyun t?crub?si hesab? acaraq hesab glory casino.
Post writing is also a excitement, if you know after that you can write otherwise it is complex to write.
Don’t Miss Your Chance: Explore More Here https://aviator-app.org/
Komet Dental is one of the leading manufacturers and providers of dental technology worldwide. The company has its head office in Lemgo, Germany https://pfo.volga.news/727500/article/komet-dental--ctomatologicheskie-instrumenty.html - https://pfo.volga.news/727500/article/komet-dental--ctomatologicheskie-instrumenty.html
Услуги юриста по подготовке заявления о разводе, расторжению брака через суд, разделу имущества, определения места жительства детей, вопросы уплаты алиментов, ведение бракоразводных процессов https://www.advokk.ru/2024/10/razvod.html - https://www.advokk.ru/2024/10/razvod.html
Сердечное Вам спасибо за Вашу помощь.
Great delivery. Great arguments. Keep up the amazing effort.
I got this site from my buddy who shared with me about this web page and now this time I am browsing this website and reading very informative content here.
Hello superb blog! Does running a blog such as this require a large amount of work? I have virtually no expertise in computer programming however I had been hoping to start my own blog soon. Anyway, if you have any ideas or techniques for new blog owners please share. I know this is off topic however I just needed to ask. Many thanks!
Hey! This post could not be written any better! Reading through this post reminds me of my good old room mate! He always kept talking about this. I will forward this post to him. Fairly certain he will have a good read. Many thanks for sharing!
San Andreas Multiplayer - это превосходный мод для Grand Theft Auto: San Andreas, который позволяет ещё дольше наслаждаться одной из лучших игр в истории https://sa-mp.top/ - читы cs
Вызов сантехника <a href=https://santekhnik-moskva.blogspot.com/p/v-moskve.html>https://santekhnik-moskva.blogspot.com/p/v-moskve.html</a> на дом в Москве и Московской области в удобное для вас время. Сантехнические работы любой сложности, от ремонта унитаза, устранение засора, до замены труб.
Да, я вас понимаю. В этом что-то есть и мысль отличная, согласен с Вами.
Цены, приведенные на площадке, стабильны, не потребуют доплаты при стандартной поставке и плате (наличным, безналичным путем, с применением банковского счета, https://res-funeral.jp/info/?p=255 - https://res-funeral.jp/info/?p=255 терминалов).
Весьма забавная штука
let's ask. every year about 63,000 million tons of polyester are produced from https://salladinn.se/2017/02/16/ad-minim-veniam/ - https://salladinn.se/2017/02/16/ad-minim-veniam/.
Смешные пошлые <a href="https://teletype.in/@anekdoty/poshlye-anekdoty">анекдоты</a>.
сайт по русскому языку <a href=https://fonetico.ru/>https://fonetico.ru</a> с фонетическими разборами слов
seo раскрутка <a href=https://searchseomsk.ru/>оптимизация сайта цена</a>
Вызов сантехника <a href=https://santekhnik-moskva.blogspot.com/p/v-moskve.html>https://santekhnik-moskva.blogspot.com/p/v-moskve.html</a> на дом в Москве и Московской области в удобное для вас время. Сантехнические работы любой сложности, от ремонта унитаза, устранение засора, до замены труб.
Find the Solution You’ve Been Searching For: Explore Now https://aviator-app.org/
написание курсовых работ <a href=https://studyru.ru/>купить курсовые</a>
Thanks for your personal marvelous posting! I certainly enjoyed reading it, you could be a great author.I will always bookmark your blog and may come back from now on. I want to encourage that you continue your great job, have a nice holiday weekend!
adult Sites
<a href=https://www.chesno.org/politician/49059/>my bbw milf wife rides my cock. comments welcome</a>
сколько стоит курсовая работа <a href=https://profsutd.ru/>https://profsutd.ru</a>
Смешные пошлые <a href="https://teletype.in/@anekdoty/poshlye-anekdoty">анекдоты</a>.
Замечательно, весьма забавная мысль
Check out our certain slot at the https://www.forward-gps.com/kazino-aparatu-paslaptys-k.html - https://www.forward-gps.com/kazino-aparatu-paslaptys-k.html: Introducing monsterpedia - stunning collection of 4 related online slot machines with an exciting collection of bonus cards!
<a href="https://justpaste.it/e0zej">aviator app</a>
Quickly delivered, and some goods are cheaper than in other stores. The quality of marijuana is on top, everything is exactly as in the description https://justusbag.com/?URL=https://scarboroughcannabis.store/ - https://justusbag.com/?URL=https://scarboroughcannabis.store/
“Терапия” (Shrinking) <a href=https://terapya-serial.ru/>https://terapya-serial.ru</a> американский сериал (Apple TV+, 2023) о терапевте, который после личной трагедии решает говорить пациентам правду. Неожиданно, его резкие слова меняют и их жизни, и его собственную. Рейтинг Кинопоиска: 7.6.
Прикольные короткие шутки <a href="http://prikoly-shutki.ru/korotkie-anekdoty">http://prikoly-shutki.ru/korotkie-anekdoty</a>.
! У меня даже потянет
мы обеспечиваем вам отличный уровень качества нашей работы в этом случае, https://www.israsky.co.il/site-in-israel - https://www.israsky.co.il/site-in-israel как создание вебсайта, в европейских странах.
Веселые видеоролики <a href="http://prikoly-shutki.ru/videos">http://prikoly-shutki.ru/videos</a>.
https://do-aposta.com/brazino/
The best websites <a href=https://bestwebsiteto.com/>https://bestwebsiteto.com</a> on the internet, with the highest ratings, to help you succeed in learning new skills
https://do-aposta.com/playpix/
Свежие приколы и картинки <a href="https://teletype.in/@anekdoty/prikoly-nastroenie">https://teletype.in/@anekdoty/prikoly-nastroenie</a>.
https://do-aposta.com/bet7k/
Guide To Best Rated Bunk Beds: The Intermediate Guide Towards Best Rated Bunk Beds best Rated bunk beds
угу,ну давай,давай)))
ve cok daha fazlas? icinde https://www.underonesky.cc/daily-updates/29-june-event-update/ - https://www.underonesky.cc/daily-updates/29-june-event-update/! ??hosgeldin/ tesvik bonusu: dogrudan oynay?n simdi/bundan sonra kay?t olmak zorunda|gerekli | gerekli | gerekli | gerekli} degil! выигры yuksek kazanma oranlar? ve destans? ikramiyeler!
https://do-aposta.com/
Веселые приколы и картинки <a href="https://teletype.in/@anekdoty/prikoly-nastroenie">https://teletype.in/@anekdoty/prikoly-nastroenie</a>.
Московский музей анимации <a href=https://animamuseum.ru/>https://animamuseum.ru</a> это место, где каждый может погрузиться в мир мультипликации и стать волшебником.
https://do-aposta.com/bet365/
Браво, какие нужные слова..., замечательная мысль
Основной номер нужно оставить для общения с семьей и коллегами, а на виртуальный - принимать рабочие, https://asbn.site/comment-economiser-leau-dans-la-salle-de-bain/ - https://asbn.site/comment-economiser-leau-dans-la-salle-de-bain/ рекламные и остальные звонки.
Лучшие сауны и бани <a href=https://dai-zharu.ru/ufa/>https://dai-zharu.ru/ufa/</a> цены, фото, отзывы. Найдите сауну поблизости в нашем каталоге лучших бань.
Срочный вызов сантехника <a href=https://santekhnik-moskva.blogspot.com/p/v-moskve.html>https://santekhnik-moskva.blogspot.com/p/v-moskve.html</a> по доступным ценам. Услуги сантехника в Москве и ближайших городах Подмосковья
Свежие картинки <a href="https://prikoly-tut.blogspot.com/2024/10/smeshnye-kartinki.html">https://prikoly-tut.blogspot.com/2024/10/smeshnye-kartinki.html</a>.
https://do-aposta.com/betano/
Очистка кровли от снега, уборка наледи и сосулек с крыши дома и других видов зданий. Высотные работы и услуги промышленного альпинизма в Москве https://dzen.ru/a/ZwZBBx-k5WAsdmk3
Canvas Cannabis brings the best in legal, recreational cannabis dispensaries to Toronto offering a wide range of cannabis flower, edibles, vaporizers https://soft.droid-mob.com/l.php?link=https://www.rentcars.buzz/ - https://soft.droid-mob.com/l.php?link=https://www.rentcars.buzz/
Диваны для кафе и баров https://citydivan.ru/catalog/myagkaya-mebel-dlya-restoranov/pryamyie-divanyi/divan-«chester-prem»/
Я думаю, что Вы не правы. Предлагаю это обсудить. Пишите мне в PM, поговорим.
Harrahs Casino is owned and operated by Caesars Interactive Entertainment and offers a reliable website with insufficient https://padraoepadrao.com/en/component/k2/item/5 - https://padraoepadrao.com/en/component/k2/item/5, but a well-selected assortment machine guns and board games.
https://do-aposta.com/parimatch/
Эффективное лечение психических заболеваний. Опытные врачи. Звоните! Доказательная медицина. Лучшие специалисты https://tvojajbolit.ru/poleznoe/zapis-k-osteopatu/ - запись к остеопату
Уникальные подарки <a href=https://rivcont.com/>https://rivcont.com</a> и аксесуары купить в интернет-магазине онлайн. Игрушки и подарки по доступным ценам в Одессе, Киеве, Харькове, Львове
Раньше я думал иначе, большое спасибо за помощь в этом вопросе.
in both cases, the actors performed intercourse on set of https://electronicstracker.com/members/archerrose03/activity/799071/ - https://electronicstracker.com/members/archerrose03/activity/799071/, but they turned out to be expressed only in the hardcore version.
The No. 1 Question Everyone Working In Porn Star Should Be Able Answer British porn stars On adultwork
https://t.me/nemeckaya_derevnya_krasnodar - Немецкая Деревня
https://t.me/nemeckaya_derevnya_krasnodar
Thanks for sharing your info. I truly appreciate your efforts and I will be waiting for your further write ups thank you once again.
https://do-aposta.com/superbet/
Несвоевременная очистка кровли от снега и наледи приводит к накоплению большого количества снежных осадков. Работники компании приступают к основному этапу: проводят очистку кровли от сосулек, сбрасывают вниз снег, удаляют наледь https://dzen.ru/a/ZwZBBx-k5WAsdmk3
купить квартиру недорого в новостройке с отделкой <a href=https://kupitkvartirudeshevo.ru/>https://kupitkvartirudeshevo.ru</a>
Купить недвижимость <a href=https://kupitkvartirudeshevo.ru/>https://kupitkvartirudeshevo.ru</a> в Казани в новостройке. Продажа квартир и цены на объекты недвижимости от застройщика.
buy antibiotics online <a href=https://buyantibioticswp.com/>https://buyantibioticswp.com</a> without a prescription - save your valuable time as well as finances!
https://topsvenska.com/recension/hajper/
<a href=https://teletype.in/@bs2site.gdn/bs2best.beast>bs2best.at</a>
Wow, this piece of writing is pleasant, my sister is analyzing such things, therefore I am going to inform her.
https://topsvenska.com/recension/speedy/
квартира ключ новостройка <a href=https://kvartirukupitspd.ru/>https://kvartirukupitspd.ru</a>
Очень хорошая фраза
Возможен ребрендинг с целью прояснения позиционирования. Собственник компании второй фазы неминуемо сталкивается с противоречием: для того, чтобы развиваться, нужно активно меняться, а компания второй фазы направлена на стабильность, https://thenovamedia.com/ - business and growth поэтому поступление изменений притормаживает работу.
I have read so many articles concerning the blogger lovers however this piece of writing is truly a nice piece of writing, keep it up.
Very nice post. I just stumbled upon your blog and wanted to say that I have really enjoyed surfing around your blog posts. In any case I'll be subscribing to your feed and I hope you write again very soon!
My coder is trying to convince me to move to .net from PHP. I have always disliked the idea because of the costs. But he's tryiong none the less. I've been using Movable-type on various websites for about a year and am anxious about switching to another platform. I have heard fantastic things about blogengine.net. Is there a way I can import all my wordpress posts into it? Any kind of help would be really appreciated!
A person necessarily assist to make seriously posts I might state. This is the first time I frequented your web page and up to now? I surprised with the research you made to make this particular publish incredible. Magnificent job!
<a href="https://india-aviator-game.com/">aviator app</a>
Hello my friend! I want to say that this article is awesome, nice written and come with almost all important infos. I'd like to see extra posts like this .
Виртуальный турецкий номер — удобная и выгодная альтернатива сим-карте страны. Чтобы купить его, не нужно ехать в Турцию и даже предоставлять документы https://www.0412.ua/list/495010 - турецкий номер телефона
купить 2 квартиру новостройке <a href=https://kvartiralisino.ru/>покупка квартиры в новостройке</a>
Whats up very cool web site!! Guy .. Excellent .. Amazing .. I will bookmark your site and take the feeds also? I'm happy to find numerous useful information right here in the post, we need work out more strategies on this regard, thanks for sharing. . . . . .
delivery balloons Dubai <a href=https://helium-balloons-delivery.com/>buy balloons cheaply</a>
What's up to every one, the contents existing at this web site are actually remarkable for people experience, well, keep up the nice work fellows.
Продажа квартир <a href=https://kvartirukupitspdhelp.ru/>https://kvartirukupitspdhelp.ru</a> в новостройках от застройщика в Казани. Купить квартиру премиум, прайм или бизнес-класса. Актуальные цены на квартиры в новостройках. Выгодно купить недвижимость для жизни или инвестиций на официальном сайте.
Этот вариант мне не подходит. Кто еще, что может подсказать?
Важно! Количество штрафов по 5000 рублей, которые автомобилист может оформить за день, https://holeofart.com/inspiration/ - https://holeofart.com/inspiration/ не ограничено. Оформить пропуск собственник авто может на 5 суток либо на год, разрешение бывает дневным и ночным.
Howdy! I know this is kind of off-topic however I had to ask. Does operating a well-established website like yours take a massive amount work? I'm completely new to operating a blog but I do write in my diary every day. I'd like to start a blog so I will be able to share my personal experience and views online. Please let me know if you have any kind of recommendations or tips for brand new aspiring blog owners. Thankyou!
order balloons to your home <a href=https://helium-balloons-delivery.com/>cheap balloons</a>
https://topsvenska.com/swish/
Greetings from Los angeles! I'm bored to tears at work so I decided to browse your site on my iphone during lunch break. I really like the info you present here and can't wait to take a look when I get home. I'm amazed at how fast your blog loaded on my phone .. I'm not even using WIFI, just 3G .. Anyways, wonderful site!
The first http://1wincasinosonlineecuador.cavandoragh.org/1win-casino - http://1wincasinosonlineecuador.cavandoragh.org/1win-casino in North Carolina, harrah's, promises exciting adventure, which required will make you smile on your your face and, if you are lucky, a little cash in your pocket.
great post, very informative. I wonder why the opposite experts of this sector don't realize this. You should continue your writing. I'm sure, you've a great readers' base already!
Свежие приколы <a href="https://prikolnyekartinki.mystrikingly.com/blog/0ade1e0d9a9">https://prikolnyekartinki.mystrikingly.com/blog/0ade1e0d9a9</a>.
Я считаю, что Вы допускаете ошибку. Давайте обсудим это.
Внешне парение в этой сауне напоминает турецкую баню, - поддача пару порождает чрезвычайно густой туман, но ощущения, по утверждению побывавших, https://dai-zharu.ru/peterburg/stati/luchshie-bani - https://dai-zharu.ru/peterburg/stati/luchshie-bani совершенно другие.
When someone writes an article he/she keeps the image of a user in his/her mind that how a user can understand it. So that's why this paragraph is amazing. Thanks!
A Turkish virtual number is a phone number that allows businesses to establish a local presence in Turkey without needing a physical office. It enables seamless communication with Turkish customers, enhancing trust and accessibility https://piks-panel.ru/virtualnye-nomera-turcii/ - турецкий номер телефона
Мы предоставляем широкий спектр услуг, включая оценку, коррекцию лечения, "второе" мнение, назначение препаратов и проведение терапии, наблюдение за динамикой вашего состояния https://seminet.blogspot.com/2023/10/blog-post_21.html - https://seminet.blogspot.com/2023/10/blog-post_21.html
Прошу прощения, что вмешался... Я разбираюсь в этом вопросе. Приглашаю к обсуждению. Пишите здесь или в PM.
врач поможет подобрать набор, исходя из ваших финансовых возможностей, https://nmiu.com.ua/ - nmiu.com.ua но также предпочтений малыша и количества лет. для заказа нужно позвонить по номеру, обозначенному на ресурсе либо связаться с одним из сотрудников в онлайне.
Готовы испытать комфорт онлайн-покупок? Обратите внимание на торговую площадку <a href=https://xn--megsb-5wa.com>m3ga at</a>! Благодаря удобному интерфейсу и разнообразию товаров товаров <a href=https://xn--megsb-5wa.com>mega</a> обеспечивает беспроблемный шопинг. Наслаждайтесь простой регистрацией и изучайте широкий спектр категорий. Присоединяйтесь к <a href=https://xn--megsb-5wa.com>мега дарк нет</a> сегодня и делайте покупки с комфортом.
ссылка на мега тор: https://mega-active-links.com
Согласен, это замечательная фраза
gaming establishment euro palace there is interesting for everyone, and in view of the fact that our https://longchimdep.net/long-chim-cu-gay-khach/ - https://longchimdep.net/long-chim-cu-gay-khach/ really for various desktop computers and mobile devices, customer you can are sure that all your favorite games you can listen in any suitable for host moment and in every place.
https://denemebonususiteler.wordpress.com/
Уникальные аксесуары подарки <a href=https://rivcont.com/>https://rivcont.com</a> купить в интернет-магазине онлайн. Игрушки и подарки с доставкой по доступным ценам в Одессе, Киеве, Харькове, Львове
Услуги монтажа септиков по Москве Работаем без выходных.<a href=https://drenaj-mos.ru/>https://drenaj-mos.ru/</a>
Enraged, Sam expels her from their houses, but relents and forgives her. Cinematographer Robert Richardson, on the other hand, was not left impressed with the quality of the printed strategy, and more did not turn to the format until "Kill Bill: Volume 1", "https://www.skubi-du.online/user/p7otjzz599 - https://www.skubi-du.online/user/p7otjzz599", when a digital intermediate process was was available.
https://deneme-bonusu-veren-siteler.org/
The main advantage of <a href=https://qoutex.in.net/>quotex trading</a> is premium quality in everything and without exception. Platform transparency, advanced technologies, attractive conditions for participants - all this makes us unique.
Извините, я подумал и удалил вопрос
предоставляет сервис виртуального хостинга, https://bigcitymom.com.ua/ - https://bigcitymom.com.ua/ vps/vds и прокат выделенных серверов. начнем с плюсов. Он лишь единый - это отсутствие оплаты за аренду полигоны для платформы.
Beli produk Hemp Custom Wear online, produk terlengkap dan harga terbaik. Dapatkan berbagai promo menarik. Belanja aman dan nyaman hanya di Tokopedia https://tracker.yougov.com/v3/partner/3/click?url=https://oakvillecannabis.store/ - https://tracker.yougov.com/v3/partner/3/click?url=https://oakvillecannabis.store/
Профессиональное изготовление памятников и надгробий на могилу в Минске. Услуги по изготовлению и установке памятников на кладбище http://x3800.com/index.php/2020/04/12/hello-world/?unapproved=542916&moderation-hash=2ad65c5a1be205fa15f72115f6737725#comment-542916 - http://x3800.com/index.php/2020/04/12/hello-world/?unapproved=542916&moderation-hash=2ad65c5a1be205fa15f72115f6737725#comment-542916
Подтверждаю. Это было и со мной. Давайте обсудим этот вопрос. Здесь или в PM.
The user agreements, usually, specify the terms of service associated with your https://eidoo-wallet.io/ - https://eidoo-wallet.io/ account.
https://deneme-bonusu-veren-siteler.org/
Ремонт стиральных машин <a href=https://ctc-service.ru/>https://ctc-service.ru</a> и холодильников всех марок. Выезд в ближайшее время, в течении часа или по согласованию. Ремонт бытовой техники с гарантией!
The https://www.inter-bookmarks.win/one-win-1win-pakistan-pk - https://www.inter-bookmarks.win/one-win-1win-pakistan-pk player is solely responsible for any cash payments or other fees associated with use of the payment method.
https://deneme-bonusu-veren-siteler.org/
I would like to thank you for the efforts you have put in writing this website. I'm hoping to see the same high-grade blog posts from you later on as well. In fact, your creative writing abilities has encouraged me to get my own blog now ;)
Полностью разделяю Ваше мнение. В этом что-то есть и идея отличная, согласен с Вами.
Team members use numbered http://www.aceitesladehesa.com/2019/07/11/hola-mundo/ - http://www.aceitesladehesa.com/2019/07/11/hola-mundo/, laying them face down, but without announcing out loud their estimates (efforts necessary for fulfillment tasks or functions).
Смешные приколы <a href="https://prikolyshutki.wordpress.com/2024/10/11/prikoly-umor/">https://prikolyshutki.wordpress.com/2024/10/11/prikoly-umor/</a>.
Наша виртуальная телефонная система, ориентированная на Турцию, позволяет вам перенаправлять входящие звонки конкретным агентам службы поддержки клиентов https://gazeta-echo.ru/virtualnye-nomera-turcii-udobstvo-i-gibkost-v-kommunikaciyax/ - https://gazeta-echo.ru/virtualnye-nomera-turcii-udobstvo-i-gibkost-v-kommunikaciyax/
Новости Купянска и Харьковской области <a href=https://kupyansk.com.ua/news/>https://kupyansk.com.ua/news/</a> информационный портал, который освещает ключевые события в Купянске и регионе. Здесь можно найти актуальные новости, аналитические материалы, репортажи и интервью с местными экспертами. Все важные события Харьковщины и Купянска публикуются с акцентом на интересы и жизнь местных жителей.
"Рівне 24" — це інформаційний ресурс <a href=https://24.rv.ua/sport/>https://24.rv.ua/sport/</a> який висвітлює найактуальніші новини Рівного та Рівненської області. Тут можна знайти оперативні репортажі, аналітичні матеріали, інтерв’ю та події, що мають значення для регіону. Оновлення відбуваються постійно, щоб жителі Рівного та області завжди були в курсі важливих подій.
It's genuinely very difficult in this active life to listen news on TV, so I only use the web for that purpose, and take the most up-to-date information.
https://deneme-bonusu-veren-siteler.org/
Everyone loves what you guys tend to be up too. This sort of clever work and reporting! Keep up the awesome works guys I've included you guys to our blogroll.
По моему мнению Вы ошибаетесь. Давайте обсудим это. Пишите мне в PM.
Omaha is more a draw game than Holdhttps://aroda.cat/nova-roba-i-adhesius/ - https://aroda.cat/nova-roba-i-adhesius/. With each bet, in that case you carry out during the betting round, you pay information.
CVpro <a href=https://cvpro.com.tr/>https://cvpro.com.tr</a> dunya cap?nda milyonlarca is arayan?n guvendigi bir CV yazma ve kariyer koclugu hizmetidir. Uzman ekibimiz, profesyonel CV, sektore ozel on yaz?, LinkedIn optimizasyonu ve kisisel kariyer koclugu sunarak kariyerinizde basar?ya ulasman?za yard?mc? olur. Gercek potansiyelinizi yans?tan CV'nizle yeni f?rsatlar? kesfetmeniz icin yan?n?zday?z.
Новости Актау <a href=https://news.org.kz/articles/>https://news.org.kz/articles/</a> надежный источник актуальной информации о событиях в Актау и Казахстане. Здесь можно найти свежие новости, аналитические материалы, репортажи и интервью с экспертами. Каждый день публикуются важные события, которые влияют на жизнь региона. Оставайтесь в курсе того, что происходит в Актау, Казахстане и за его пределами!
we in addition publish maintenance for cashing securities, and in ATMs. The Chippewa https://www.novabookmarks.win/1win-panama-1winpanamanet - https://www.novabookmarks.win/1win-panama-1winpanamanet is owned and operated by the Fond du Lac Group on Lake Superior.
в следствии этого, если вы задумываются о том, чтобы производимая вами страница имела хороший рейтинг, вам нужно убедиться, https://www.kopareykir.com/?attachment_id=917 - https://www.kopareykir.com/?attachment_id=917 что выбранный вами конструктор веб-сайтов имеет правильные функции.
https://deneme-bonusu-veren-siteler.org/
В этом что-то есть. Теперь всё понятно, большое спасибо за информацию.
These tables allow beginners to familiarize themselves with the game at not overstated bets, without risking with all this significant amounts of http://ringturbine.com:80/index.php/Is_Dhamaal_App_Legal_In_India - http://ringturbine.com:80/index.php/Is_Dhamaal_App_Legal_In_India.
An interesting discussion is worth comment. I believe that you should publish more on this topic, it may not be a taboo matter but generally people don't talk about such subjects. To the next! Many thanks!!
Great beat ! I would like to apprentice while you amend your site, how could i subscribe for a blog web site? The account helped me a acceptable deal. I had been tiny bit acquainted of this your broadcast provided bright clear idea
CVzen <a href=https://cvzen.mx/>https://cvzen.mx</a> es una plataforma lider en la creacion de CV y cartas de presentacion, ofreciendo soluciones personalizadas para impulsar tu carrera. Con la ayuda de nuestros expertos y herramientas de IA, puedes crear documentos profesionales que llamen la atencion de los empleadores. Da el siguiente paso en tu desarrollo profesional con CVzen y destaca en el mercado laboral.
You are so interesting! I don't think I've truly read through something like this before. So wonderful to discover somebody with genuine thoughts on this topic. Really.. many thanks for starting this up. This website is one thing that is required on the internet, someone with a little originality!
Присоединяюсь. Я согласен со всем выше сказанным.
• Get a real gaming experience in live casinos, and all this for the chance to win very real money at our https://www.feedinco.com/blog/aviatrix-and-aviator-leaders-in-rocket-crash-gaming - https://www.feedinco.com/blog/aviatrix-and-aviator-leaders-in-rocket-crash-gaming.
Pretty section of content. I just stumbled upon your weblog and in accession capital to assert that I acquire in fact enjoyed account your blog posts. Anyway I will be subscribing to your feeds and even I achievement you access consistently rapidly.
https://deneme-bonusu-veren-siteler.org/
I have read so many articles or reviews regarding the blogger lovers however this piece of writing is really a fastidious post, keep it up.
Удалено (перепутал раздел)
можно осознать, что это стеновой лист с профилем 18 мм, его толщина составляет 0,7 мм, http://www.bisound.com/forum/showthread.php?p=749621#post749621 - http://www.bisound.com/forum/showthread.php?p=749621#post749621 а общая ширина - 0,75 метра.
The very thin human, as a rule, have a weaker immune system, which often makes insects more susceptible to infections, surgical complications, http://www.lqqm.com/space-uid-10154755.html - http://www.lqqm.com/space-uid-10154755.html and more slow recovery after sick leave.
ммда!!
Dado que el poker combina en sus habilidades y capacidades habilidades matematicas con habilidades humanas como psicologia o engano, creian que https://www.bigapplestudios.nyc/getting-sound-design-right-regardless-of-your-budget/ - https://www.bigapplestudios.nyc/getting-sound-design-right-regardless-of-your-budget/ imposible de dominar en las computadoras.
Na'Vi и Counter-Strike 2 <a href=https://natus-vincere.all-gem-stones.net/>https://natus-vincere.all-gem-stones.net</a> как легендарная команда адаптируется к новому ландшафту киберспорта и сохраняет свою конкурентоспособность.
Предпусковые подогреватели <a href=https://4766.ru/>https://4766.ru</a> Webasto купить недорого в интернет магазине. Крупнейший интернет магазин по продаже предпусковых отопителей и комплектующих. Официальный партнер Webasto, Alpicool, Valve (SteamDeck), AeroCool, Автотепло, Bushido
This post will help the internet users for creating new weblog or even a blog from start to end.
Взять онлайн займ <a href=https://zaimobot.online/>https://zaimobot.online</a> через бот Telegram на карту в официальных микрофинансовых компаниях под ноль процентов без отказа.
Counter-Strike 2 <a href=https://mouz.castaneda-ru.com/>https://mouz.castaneda-ru.com</a> принес новые возможности, и команда MOUZ сумела быстро адаптироваться, став одной из лидеров на киберспортивной арене.
История успеха игры Counter-Strike 2 <a href=https://eternal-fire.eschool.pro/>https://eternal-fire.eschool.pro</a> и команды Eternal Fire: от восхождения турецкого киберспорта до побед на мировой арене.
FaZe Clan <a href=https://faze-clan.file-up.net/>https://faze-clan.file-up.net</a> укрепили свои позиции, Counter-Strike 2 открыла новую эру киберспорта, а адаптировавшись и побеждая в обновленной игре.
доставка из китая посредник <a href=https://14cargo.ru/>калькулятор доставки из китая</a>
Букмекерская контора 1Win <a href=https://1win-1vinbk.com/>https://1win-1vinbk.com</a> самая популярная платформа для онлайн ставок на спорт и казино. Актуальное и рабочее зеркало 1win для входа на официальный сайт.
Смешные анекдоты <a href="https://roomstyler.com/users/billybons">https://roomstyler.com/users/billybons</a>.
Вы не правы. Я уверен. Пишите мне в PM.
5. Клапан https://xn--80aaajchrjarmzb7b.xn--p1ai/ - Газификация в Калининграде отбора паровой фазы. в данной ситуации отлично подойдут минигазгольдеры Медведь, при помощи которых вы можете быстро и недорого ответить на вопросы с отопительным сезоном дачи, обеспечением горячей водой и приготовлением пищи.
Mint Mobile re-imagined the wireless shopping experience and made it easy and online-only. No stores. No salespeople. Just huge direct to you savings on https://www.grebgreb.rs/Culture/ChangeCulture?lang=sr-Cyrl-RS&returnUrl=https://www.diversdeluxe.co.za/ - https://www.grebgreb.rs/Culture/ChangeCulture?lang=sr-Cyrl-RS&returnUrl=https://www.diversdeluxe.co.za/
в топку
У scripts есть свои достоинства и недостатки. 3. Написать программный код. Писать http://merendinadatiffani.blogspot.ru/2016/03/aaa-addio-al-nubilato-cercasi.html - http://merendinadatiffani.blogspot.ru/2016/03/aaa-addio-al-nubilato-cercasi.html - это означает создавать посредством специализированных языков специальные алгоритмы.
https://aviator-app.org/
My coder is trying to convince me to move to .net from PHP. I have always disliked the idea because of the costs. But he's tryiong none the less. I've been using WordPress on numerous websites for about a year and am worried about switching to another platform. I have heard very good things about blogengine.net. Is there a way I can transfer all my wordpress content into it? Any help would be really appreciated!
изначально догадался..
no entanto, ha obvio falha para visitantes micro-stakes, http://pirooztak.ir/?option=com_k2&view=itemlist&task=user&id=1686757 - http://pirooztak.ir/?option=com_k2&view=itemlist&task=user&id=1686757 como a taxa cobrada muito e alta em mundo do jogo ate nl10.
Извините, не в тот раздел.....
Dallas Stars, Texas Rangers, Dallas Mavericks, Houston Texans, Dallas Cowboys, Houston Rockets and San Antonio Spurs, https://www.downloadcdr.com/forum/thao-luan-chung/online-live-casino-real-money-online-live-casino-blackjack-card-counting - https://www.downloadcdr.com/forum/thao-luan-chung/online-live-casino-real-money-online-live-casino-blackjack-card-counting, not talking already about college teams.
When I initially commented I clicked the "Notify me when new comments are added" checkbox and now each time a comment is added I get three e-mails with the same comment. Is there any way you can remove me from that service? Thanks!
Hi there, always i used to check webpage posts here in the early hours in the dawn, because i enjoy to learn more and more.
Counter-Strike 2 <a href=https://xantares.zremcom.com/>https://xantares.zremcom.com</a> это долгожданное обновление культовой франшизы, выпущенное на движке Source 2. Игра предлагает улучшенную графику, переработанную физику и новые механики
CS2 открывает новые горизонты <a href=https://smooya.tula24.net/>https://smooya.tula24.net</a> для игроков и команд. С улучшенной механикой стрельбы и графикой, игра становится более динамичной и зрелищной.
Вы не правы. Предлагаю это обсудить.
10, https://www.dodgeball.org.my/2019/12/04/world-dodgeball-championship-2019/ - https://www.dodgeball.org.my/2019/12/04/world-dodgeball-championship-2019/ Twister (spinJuntou-se a MPN em 2013, https://yatesrelates.com/index.php/RedStar_Poker:_Introdu%C3%A7%C3%A3o - https://yatesrelates.com/index.php/RedStar_Poker:_Introdu%C3%A7%C3%A3o no entanto ele deixou seu existencia em maio 2020 ano a redstar mudou-se para o ipoker.
Веселые анекдоты <a href="https://teletype.in/@anekdoty/smeshnye-anekdoty">https://teletype.in/@anekdoty/smeshnye-anekdoty</a>.
В ближайшие годы <a href=https://jl.donk-cs-go.ru/>https://jl.donk-cs-go.ru</a> можно ожидать увеличения количества турниров, улучшения условий для игроков и расширения аудитории.
С выходом КС 2 <a href=https://b1t.s1mple-cs-go.ru/>https://b1t.s1mple-cs-go.ru</a> и такими игроками, как b1t, киберспорт вступает в новую эру.
С каждым днем КС 2 <a href=https://malbsmd.serafimovich.org/>https://malbsmd.serafimovich.org</a> продолжает развиваться, привнося новые возможности и контент.
Когда нужно создать что-то надежное, важны не только материалы, но и их правильный выбор. Это касается как масштабных проектов, так и небольших объектов http://sehoeng.com/bbs/board.php?bo_table=pro_qna_eng&wr_id=67418 - http://sehoeng.com/bbs/board.php?bo_table=pro_qna_eng&wr_id=67418
Each room is designed with the convenience of our guests in mind at the https://freeda.fr/2019/10/07/community-health-center/ - https://freeda.fr/2019/10/07/community-health-center/. Visit the advertising kiosk that working since 8:00 a.m., in order to get a voucher for free cookies!
Looking for a new sex toy to use with your partner? Tease and explore each other with our exciting range of http://philarmonica.it/?URL=https://incognito.black/ - http://philarmonica.it/?URL=https://incognito.black/
In fact no matter if someone doesn't understand after that its up to other visitors that they will help, so here it occurs.
Интерес к киберспорту <a href=https://zywoo.cs2-esports.ru/>https://zywoo.cs2-esports.ru</a> продолжает расти, и с каждым новым турниром появляются новые фанаты и игроки
На сайте вы найдёте подробные <a href=https://accord-top.ru/>гитара для начинающих</a>, которые помогут вам быстро освоить новые песни. Представлены аккорды для всех уровней, включая аккорды для гитары для начинающих. Если вы только начали учиться, раздел гитара для начинающих будет полезен для быстрого прогресса.
Вы допускаете ошибку. Предлагаю это обсудить. Пишите мне в PM, поговорим.
the online casino had an atmosphere of camaraderie that I did not expect in an https://www.activeadriatic.com/forum/get-started-with-your-forum/onlayn-kazino-de-grati - https://www.activeadriatic.com/forum/get-started-with-your-forum/onlayn-kazino-de-grati.
музей анимации цена <a href=https://animamuseum.ru/>музей анимации в измайловском кремле официальный</a>
I got this web page from my pal who told me about this web site and at the moment this time I am browsing this web site and reading very informative articles at this place.
You can definitely see your expertise within the article you write. The arena hopes for even more passionate writers such as you who aren't afraid to say how they believe. Always follow your heart.
https://aviator-app.org/
Свежие анекдоты <a href="https://www.intensedebate.com/people/billyjohnse">https://www.intensedebate.com/people/billyjohnse</a>.
Лазерная резка металла: передовые технологии для промышленности
Наши лазерные станки для резки металла используют передовые технологии, обеспечивая максимальную производительность и точность.
оптоволоконный лазерный станок для резки металла https://lazernye-stanki.ru/ - лазерный станок чпу для резки металла .
Awesome site you hawve here but I was wanting to
knlw if you knew of any user discussion forums that cover the
same topics talked about here? I'd really like tto be a part of online community where I can get opiniopns from other knowledgeable individuals that share the same interest.
If you have any suggestions, please let me know.
Thank you! https://Lvivforum.Pp.ua/
I'm amazed, I have to admit. Rarely do I encounter a blog that's both equally educative and interesting, and let me tell you, you've hit the nail on the head. The issue is an issue that not enough people are speaking intelligently about. Now i'm very happy I found this in my search for something regarding this.
Мы продаем устройства для систем водоснабжения, отопления, канализации и мебель под сантехнику. Поможем создать пространство с комфортными для жизни условиями https://www.ozon.ru/product/744058088 - Держатель ручного душа WasserKRAFT A223 Черный матовый
<a href="https://india-aviator-game.com/">spribe aviator game</a>
Конечно. Я согласен с Вами.
In Vegas are available free slot machines, in the list of which big money frenzy, hot hot peppers, Cleopatra and all classic" slot slot machines Vegas http://fatherbroom.com/es/2020/04/la-muerte-la-parabola-del-rico-tonto-ejercicios-espirituales-por-internet-27-abril-2020/ - http://fatherbroom.com/es/2020/04/la-muerte-la-parabola-del-rico-tonto-ejercicios-espirituales-por-internet-27-abril-2020/.
Сервисный центр предлагает замена аккумулятора blackberry porche design p9982 <a href=https://spb.profi-teh-remont.ru/remont_telefonov/blackberry/porche-design-p9982.htm>замена разъема питания blackberry porche design p9982</a>
Глаз бога телеграмм <a href=https://gazz-boga.ru/>Глаз бога</a>
В этом что-то есть. Раньше я думал иначе, спасибо за объяснение.
Our serving https://www.manualidadesdemart.com/wp/manualidades-demart/ - https://www.manualidadesdemart.com/wp/manualidades-demart/ are not only practical; they are also designed for daily use, which as reasonable insects a worthy investment for any waiter seeking to increase quality service and effectiveness of his work.
Luka Doncic and Boban Marjanovic have been seen together frequently off the court, and their friendship has been well-documented through social http://www.clubxedien.net/proxy.php?link=https://www.ytow.net/ - http://www.clubxedien.net/proxy.php?link=https://www.ytow.net/
Веселые приколы, шутки и картинки <a href="http://worldcrisis.ru/crisis/billybons2">http://worldcrisis.ru/crisis/billybons2</a>.
Summa, joka pitaisi kierrattaa, vastaa bonuksen maaraa tai bonuksen maaraa ja talletus ja tallainen hetki ihana http://digitalmaine.net/mediawiki3/index.php?title=User:RainaSiemens499 - http://digitalmaine.net/mediawiki3/index.php?title=User:RainaSiemens499, tutustu ehdot kuitti bonus. Pelaajat rekisteroityvat tietyn palvelun kautta, joka tassa tapauksessa on yleensa luotettava ja se riittaa.
<a href="https://india-aviator-game.com/">aviator game download</a>
По моему мнению Вы ошибаетесь. Пишите мне в PM, поговорим.
существует парочка доступных базовых вариантов, https://linearcomputing.com/2018/12/27/web-animation-3-3-2/ - https://linearcomputing.com/2018/12/27/web-animation-3-3-2/ а также можно сохранить изображение с ноутбука. Включать их или нет - решать клиенту.
Да... Нам ешо далеко до такого...
Unbeatable reputation: Since its inception, MegaDice Casino has constructed a stable status for catering particularly to Australian gamers and consistently offering the very best casino video games. It’s as reliable as a swagman’s swag!
<a href="https://india-aviator-game.com/">aviator download</a>
achat or <a href=https://gior.fr/ou-vendre-lor-a-frejus/>rachat de bijoux</a>
готовые сборки самп <a href=https://sa-mp.top/>cleo скрипты</a>
Hey I know this is off topic but I was wondering if you knew of any widgets I could add to my blog that automatically tweet my newest twitter updates. I've been looking for a plug-in like this for quite some time and was hoping maybe you would have some experience with something like this. Please let me know if you run into anything. I truly enjoy reading your blog and I look forward to your new updates.
<a href="https://india-aviator-game.com/">aviator casino</a>
Прикольные мемы <a href="https://goodgame.ru/user/1655117">https://goodgame.ru/user/1655117</a>.
Разработка проекта СЗЗ (санитарно защитная зона) для объектов негативного воздействия в Москве и Московской области. Оценка источников загрязнения на производстве, согласование проекта в Роспотребнадзоре https://telegra.ph/15-ponyatnyh-otvetov-o-proekte-SZZ-sanitarno-zashchitnaya-zona-10-17
This kit comes in a zippered pouch and includes 2 specially developed Scuba Wrenches, high quality crescent wrench, Phillips head and flat head screw drivers https://login.kastoroffice.cl/reset-password-form?email=&redirect=https://boikhuco.co.za/ - https://login.kastoroffice.cl/reset-password-form?email=&redirect=https://boikhuco.co.za/
вечно вам все нетак!!
Покер в нашем окончательном названии впервые упоминается в 1829 году в мемуарах совершившего путешествие по Америке английского актера Джозефа Крауэлла (английский актер Джозеф Крауэлл (joseph crowell)) он утверждал о том, https://theguruchela.com/highly-respected-degree/ - https://theguruchela.com/highly-respected-degree/ которые в Покер играли в купленном Орлеане.
Iako su psi ocito njezini temeljni Tema, https://offmarketbusinessforsale.com/jednostavan-vodic-za-bonuse-bez-depozita-u-kasinu-2024-koraci-za-preuzimanje-vasih-bonus-nagrada/ - https://offmarketbusinessforsale.com/jednostavan-vodic-za-bonuse-bez-depozita-u-kasinu-2024-koraci-za-preuzimanje-vasih-bonus-nagrada/ igraliste takoder|svidjet ce se|bit ce zanimljivo|bit ce potrebno|potrebno} onima koji nisu je pretjeranim obozavateljem covjekovog najboljeg prijatelja.
Аренда инструмента <a href=https://tutprokat.by/>https://tutprokat.by</a> в Мозыре на выгодных условиях. Доставка до адреса
DeepNude <a href=https://techodrom.com/the-art-of-nude-content-creation/>https://techodrom.com/the-art-of-nude-content-creation/</a> is an app that undresses women in photographs, revealing their intimate areas hidden behind clothing.
<a href="https://india-aviator-game.com/">aviator game online</a>
Камянец 24 <a href=https://24kp.com.ua/news/>https://24kp.com.ua/news/</a> газета города Каменец-Подольский, где можно найти не только новости города, но и последние новости дня и все важное и интересное, что происходит в Хмельницкой области и в Украине.
Оценка источников загрязнения на производстве, согласование проекта в Роспотребнадзоре. Разработка проекта СЗЗ (санитарно защитная зона) для объектов негативного воздействия в Москве и Московской области https://telegra.ph/15-ponyatnyh-otvetov-o-proekte-SZZ-sanitarno-zashchitnaya-zona-10-17
Your go-to Filipino technology forum for discussions on mobile networks, internet, phones, media, computers, gaming, news, and a variety of topics related to http://secondary.lccsmobile.com/action/clickthru?targetUrl=https://www.mintmobile.co.za/&referrerKey=1W8YmXNqvRTn7qHGU2Uu7g5brFkz3JcRngyQ2AnRrMqk&referrerEmail=undefined - http://secondary.lccsmobile.com/action/clickthru?targetUrl=https://www.mintmobile.co.za/&referrerKey=1W8YmXNqvRTn7qHGU2Uu7g5brFkz3JcRngyQ2AnRrMqk&referrerEmail=undefined
Разработка ПНООЛР — проект нормативов образования отходов и лимитов на их размещение. Экологическая отчетность для предприятий в Москве и Московской области https://vc.ru/u/3791103-studiya-zr/1506729-pnoolr-chto-nuzhno-znat-pri-razrabotke-proekta-normativov-obrazovaniya-i-razmesheniya-othodov
Mivel ilyen forrasok sok, es a valasztas opciok nagyon szeles, ez lesz meg nehez biro, melyik szolgaltatas a vege valasszon szinten https://wmg.by/kaszino-attekintes-vavada-es-100-ingyenes-porgetes-befizetes-nelkul/ - https://wmg.by/kaszino-attekintes-vavada-es-100-ingyenes-porgetes-befizetes-nelkul/ jobb regisztralni.
<a href="https://india-aviator-game.com/">aviator online game</a>
<a href="https://india-aviator-game.com/">aviator game online</a>
Советы для женщин <a href=https://zhenskiy.kyiv.ua/>https://zhenskiy.kyiv.ua</a> от психологов, диетологов и стилистов. Samka.co - журнал о том, как всегда быть красивой и выглядеть стильно. О психологии и личностном росте.
Жіночий журнал <a href=https://lady.kyiv.ua/>https://lady.kyiv.ua</a> про красу та здоров'я
Да, действительно. Это было и со мной. Можем пообщаться на эту тему. Здесь или в PM.
частенько новички не обращают особого внимательности на размер комиссий и вознаграждений, https://turisma.com.br/2018/10/19/facamos-por-nos-facamos-pelos-que-amamos-facamos-pelo-mundo/ - https://turisma.com.br/2018/10/19/facamos-por-nos-facamos-pelos-que-amamos-facamos-pelo-mundo/ а на длинной дистанции это может сильно внимательно оказать влияние на общую сумму выигрышей.
Several planters are using precision Farming approaches to maximize their plant yields and also reduce rubbish. This strategy to Farming includes the use of data and also modern technology to produce educated selections.
Betandreas Kazino sayt?n?n interfeysi istifad?cil?rin gozunu yormamaq ucun h?m sad? haz?rlan?b, h?m d? arxa fon ucun qara r?ng? ustunluk verilib. Siz Betandreas Azerbaycan sayt?na daxil olduqdan sonra sol yuxar? kuncd? qeydiyyat v? giris bolm?l?ri il? oz Betandreas hesab?n?z? yarada v? ya movcud hesab?n?za daxil ola bil?rsiniz https://azsportsweb.com/tr/ - https://azsportsweb.com/tr/
<a href="https://india-aviator-game.com/">aviator online game</a>
Медицинский онлайн журнал <a href=https://medicalanswers.com.ua/>https://medicalanswers.com.ua</a> актуальная информация о здоровье, профилактике и лечении заболеваний.
Последние события <a href=https://lenta.kyiv.ua/>https://lenta.kyiv.ua</a> из мира политики, экономики, культуры и спорта. Всё, что происходит в Украине и за её пределами, с экспертной оценкой и объективной подачей.
Новости Украины <a href=https://gau.org.ua/>https://gau.org.ua</a> оперативные сводки, политические события, экономика, общественные и культурные тенденции.
Основные новости <a href=https://mediashare.com.ua/>https://mediashare.com.ua</a> за сегодня Свежие события в мире и Украине
Последние новости Украины <a href=https://kiev-pravda.kiev.ua/>https://kiev-pravda.kiev.ua</a> актуальные события, политика, экономика, спорт и культура.
Свежие новости 24/7 <a href=https://prp.org.ua/>https://prp.org.ua</a> политика, экономика, спорт, культура и многое другое. Оперативные сводки, эксклюзивные материалы и аналитика от экспертов. Оставайтесь в курсе главных событий в стране и мире!
Актуальные новости <a href=https://uamc.com.ua/>https://uamc.com.ua</a> 24/7. Узнайте первыми о главных событиях в мире, стране и вашем регионе. Мы предоставляем только проверенные факты!
Автообзоры <a href=https://proauto.kyiv.ua/>https://proauto.kyiv.ua</a> тест-драйвы, новости рынка и советы экспертов. Узнавайте всё о новых моделях и автоаксессуарах на нашем портале!
The most modern <a href=https://pocketoption.in.net/>pocket option</a> platform for trading on financial markets. Register a Free Demo Account and start using the full potential for earning on trading operations.
Новые <a href=https://www.softzatak.ru/2024/10/linejdzh-2-servera-2024-obzor-luchshih-proektov-i-startov/>Ла2</a> с удобным поиском. Анонс серверов Lineage 2 по типу Craft, PvP, Low. Открытие серверов L2 каждый день!
Изготавливаем изделия <a href=https://coping-top.ru/>https://coping-top.ru</a> из восстановленного камня: печи с мангалом и барбекю, решетки, бордюры. Прочный и экологичный материал, широкий выбор цветов и текстур.
Новый авто портал <a href=https://mirauto.kyiv.ua/>https://mirauto.kyiv.ua</a> для автолюбителей. Обзоры авто, новости, тест-драйвы и советы по обслуживанию автомобиля в одном месте.
Produzione video professionale <a href=https://orbispro.it/>https://orbispro.it</a> creazione di spot pubblicitari, film aziendali e contenuti video. Ciclo completo di lavoro, dall'idea al montaggio. Soluzioni creative per promuovere con successo il tuo brand.
Это очень ценный ответ
Затем подтянул сыночка Марка и уже парами запустил и раскрутили проект https://splacearch.com/blog-post/architecture/ - https://splacearch.com/blog-post/architecture/ stars.
<a href="https://justpaste.it/e0zej">aviator game india</a>
<a href=https://volgateks21.ru/basket/pgs/?promokod_363.html >1win</a> при пополнении счета активирует бонусы, такие как удвоение депозита или фрибеты. Пользователи вводят код при внесении средств на баланс для получения бонусов.
Подробнее о промокодах 1Win можно ознакомиться в этом материале - <a href=https://volgateks21.ru/basket/pgs/?promokod_363.html >https://volgateks21.ru/basket/pgs/?promokod_363.html</a>
https://znakavto.com/
Автомобильные новости <a href=https://sedan.kyiv.ua/>https://sedan.kyiv.ua</a> Украины и мира, тест-драйвы новых авто, советы экспертов
Женский портал <a href=https://bestwoman.kyiv.ua/>https://bestwoman.kyiv.ua</a> современная мода, тренд, стиль; полезные советы; секреты хорошей фигуры; уроки макияжа, внешность и красота
Онлайн-журнал <a href=https://superwoman.kyiv.ua/>https://superwoman.kyiv.ua</a> женских секретов для стильных, модных и уверенных в себе девушек.
Портал для женщин <a href=https://prowoman.kyiv.ua/>https://prowoman.kyiv.ua</a> мода, стиль, диеты, истории знаменитостей, красота, полезные советы, рецепты, отношения
<a href=https://riobet-official-site.xyz>риобет казино регистрация</a>
<a href=https://booicasino-n1we.buzz>booi casino</a>
Полезные статьи <a href=https://entertainment.com.ua/>https://entertainment.com.ua</a> о здоровье, уходе за собой, моде и личностном развитии. Все для женщин, стремящихся к успеху.
Советы по тренировкам <a href=https://bahgorsovet.org.ua/>https://bahgorsovet.org.ua</a> питанию и здоровому образу жизни. Актуальная информация для всех, кто хочет улучшить свою физическую форму.
Онлайн журнал для женщин <a href=https://lubimoy.com.ua/>https://lubimoy.com.ua</a> мода, красота, здоровье, отношения, карьера и саморазвитие. Актуальные статьи, советы экспертов и вдохновение для повседневной жизни. Новости, тренды и полезные рекомендации.
Женский журнал онлайн <a href=https://martime.com.ua/>https://martime.com.ua</a> мода, уход за собой, здоровье, карьера и личная жизнь. Свежие статьи, советы и идеи для вдохновения и развития современной женщины.
Практичные советы <a href=https://vybir.kiev.ua/>https://vybir.kiev.ua</a> для женщин: мода, здоровье, карьера и семья. Легко находите ответы на любые вопросы!
Official website of the <a href=https://olymp-trade.net/>olymptrade</a> broker. Up-to-date information about trading on the platform. Detailed review, reviews of real people, demo account, strategies.
Недорогие <a href=https://carskoe-selo-ekskursii.ru/>экскурсии в Царское Село</a>. Янтарная комната, Большой Екатерининский дворец, описание и отзывы
There are many benefits to using a Taiwan virtual number to receive text messages . First, it provides users with a temporary and secure phone number without having to buy a new SIM card. Second, it is suitable for a variety of scenarios, including social media registration, online shopping, and two-factor authentication http://www.r24.com.cn/20241017/19090658.html - http://www.r24.com.cn/20241017/19090658.html
decentraland (mana): this virtual real estate https://magameme.io/ - meme coins real tokens. this is similar to the digital version of the dollar bill in various blockchains.
<a href="https://www.cyberpinoy.net/read-blog/75716">п»їaviator game</a>
Скачать бесплатные приложения <a href=https://apprepository.ru/>https://apprepository.ru</a> и игры для Андроид. Все программы доступны на русском языке.
<a href="https://telegra.ph/Aviator-Game-A-Thrilling-Adventure-in-the-Sky-10-20">aviator online game</a>
<a href=https://cryptoboss-tnot.xyz>cryptoboss casino зеркало россия</a>
<a href=https://championcasino-gaw.buzz>champion casino</a>
We're a group of volunteers and opening a new scheme in our community. Your site offered us with valuable information to work on. You've done a formidable job and our entire community will be grateful to you.
<a href=https://up-x-mrw.buzz>up-x casino</a>
<a href=https://riobet-n3mr.buzz>риобет официальный сайт играть</a>
Excellent, what a blog it is! This web site presents valuable data to us, keep it up.
Официального сайта Мостбет <a href=https://ikidz.ru/>https://ikidz.ru</a> как войти и зарегистрироваться, как скачать программу и обзоры ставок на спорт от букмекерской конторы Мостбет.
<a href="https://intgez.com/read-blog/81381">aviator online game</a>
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: <a href=https://remont-byttekhniki-prm.ru/>ремонт крупногабаритной техники в перми</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Its not my first time to go to see this web site, i am visiting this site dailly and take nice information from here all the time.
Heya! I understand this is somewhat off-topic but I had to ask. Does building a well-established website such as yours require a large amount of work? I'm completely new to operating a blog but I do write in my journal on a daily basis. I'd like to start a blog so I can share my own experience and thoughts online. Please let me know if you have any kind of recommendations or tips for new aspiring bloggers. Appreciate it!
Gareth Bale <a href=https://real-madrid.gareth-bale-se.com/>https://real-madrid.gareth-bale-se.com</a> est un footballeur gallois dont le nom est inscrit a jamais dans l'histoire du Real Madrid et de tout le football mondial.
It's remarkable to go to see this web page and reading the views of all colleagues regarding this post, while I am also keen of getting knowledge.
German auto giant Mercedes <a href=https://mercedes.lewis-hamilton.cz/>https://mercedes.lewis-hamilton.cz</a> and British racing driver Lewis Hamilton are key figures in the era of unprecedented success of Formula 1 over the last decade.
<a href="https://9unity.com/read-blog/11138">aviator game india</a>
Hello, I think your site might be having browser compatibility issues. When I look at your blog site in Opera, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, wonderful blog!
Портал о строительстве <a href=https://tozak.org.ua/>https://tozak.org.ua</a> проекты домов, ремонт, материалы и услуги для профессионалов и частных лиц.
Строительный портал <a href=https://garant-jitlo.com.ua/>https://garant-jitlo.com.ua</a> о строительстве, недвижимости, ремонте, дизайне и архитектуре
<a href="https://doomelang.com/read-blog/36894">aviator predictor</a>
Благодаря нашему многолетнему опыту работы в сфере микрофинансирования, мы знаем, какие решения лучше всего подходят для различных жизненных ситуаций. Мы предлагаем широкий выбор кредитных продуктов, которые удовлетворяют самые разные потребности наших клиентов, от краткосрочных займов до долгосрочного финансирования с гибкими условиями возврата.
микро займы https://microloans.kz/ - микрокредит казахстан .
одним словом БЕЛКА
with us there are special one-time events, and also many weekly and monthly events, at which you necessarily find what why it is worth coming to cda https://www.dewberryadvisors.com/how-budget-2022-can-be-used-to-revive-consumption-for-economic-growth/ - https://www.dewberryadvisors.com/how-budget-2022-can-be-used-to-revive-consumption-for-economic-growth/!
Завидую тем, кто досмотрел до конца.
What is the total cost of the memecoin meme? for comparison, the current price of the https://kamala-harris.io/ - https://kamala-harris.io/ is at -76,20% less record high cost for all time.
<a href=https://unlimcasino-ftqo.buzz>сайт unlim casino</a>
<a href=https://vodka-casino-vhod.top>водка казино вход</a>
Guide To English Pornstars: The Intermediate Guide For English Pornstars English Pornstars
Бутафория получается
Разнообразие высококачественных различных игр в покер казино обеспечит вам незабываемое наслаждение от видеопокера, которого вы, возможно, https://www.moksatechnologies.com/2018/07/05/the-fastest-growing-law/ - https://www.moksatechnologies.com/2018/07/05/the-fastest-growing-law/ как правило не имели!
оценка условий труда стоимость <a href=https://sout095.ru/>https://sout095.ru</a>
экспертный центр соут <a href=https://sout095.ru/>https://sout095.ru</a>
Данная служба предоставляет услуги круглосуточного вскрытия замков и дверей в Москве. Мастера во всех районах города http://vskrytie-zamkov.su
Веселые видео <a href="http://shutki-anekdoty.ru/videos">http://shutki-anekdoty.ru/videos</a>.
<a href=https://schneider-piter.ru/image/pgs/promokod_363.html >1win</a> счета активирует бонусные средства или фрибеты. Игроки могут ввести код при внесении депозита, и бонус будет автоматически зачислен на их счет для использования в ставках или играх казино.
Подробнее о промокодах 1Win можно ознакомиться в этом материале - <a href=https://schneider-piter.ru/image/pgs/promokod_363.html >https://schneider-piter.ru/image/pgs/promokod_363.html</a>
Лучшие онлайн банки для ип топ-10 рейтинг 2024 <a href=https://tenchat.ru/media/2718112-luchshiye-onlayn-banki-dlya-ip-top10-reyting-2024/>банки для ип рейтинг 2024</a>
нормальная идея
также, российские игроки активно борются в спортивных играх с реальными крупье, таких, как живая рулетка, https://newartcommunity.ru/ - Лицензированное казино blackjack и покер.
Смешные короткие шутки <a href="http://shutki-anekdoty.ru/korotkie-anekdoty">http://shutki-anekdoty.ru/korotkie-anekdoty</a>.
I always used to read paragraph in news papers but now as I am a user of web therefore from now I am using net for content, thanks to web.
Hey There. I found your blog using msn. This is a really well written article. I'll make sure to bookmark it and return to read more of your useful information. Thanks for the post. I will definitely comeback.
Копирайтер и SMM-специалист <a href=https://uslugi.yandex.ru/profile/ArinaB-2163631/>https://uslugi.yandex.ru/profile/ArinaB-2163631</a> специалист по созданию текстов и управлению социальными сетями. Занимается разработкой контента, повышает вовлечённость аудитории, управляет репутацией бренда и реализует стратегии продвижения в цифровых каналах.
<a href="https://codwarfare.com/community/threads/aviator-game-how-to-win-big-and-cash-out-fast-%E2%80%93-the-ultimate-guide-for-indian-players.40951/">п»їaviator game</a>
<a href="https://medium.com/@indiaaviator/top-6-best-websites-to-play-the-aviator-game-for-indian-players-october-2024-b62d4613d007">aviator hack</a>
биткоин курс <a href=https://bitcoin-btc.su/>bitcoin btc цена</a>
<a href="https://medium.com/@indiaaviator/aviator-game-complete-guide-for-indian-players-strategies-features-and-mobile-app-ebfa4a01517b">aviator apk game</a>
Друзья - культовый американский телесериал, вышедший в 1994 году, и объединивший жанры комедии и мелодрамы. Он рассказывает о жизни шестерых друзей https://dancelover.tv/node/1116320 - https://dancelover.tv/node/1116320
4. Если заказ принимается по телефону, зато вы сами принимаете, обрабатываете и выполняете заказ. в случае, если есть офлайн магазин, https://politika.forum2x2.com/t9053-topic#23048 - https://politika.forum2x2.com/t9053-topic#23048 то и к нему.
Sweet blog! I found it while surfing around on Yahoo News. Do you have any suggestions on how to get listed in Yahoo News? I've been trying for a while but I never seem to get there! Cheers
Hi there, of course this piece of writing is in fact nice and I have learned lot of things from it concerning blogging. thanks.
Kraken — одна из ведущих криптобирж для безопасной и удобной торговли криптовалютами. Регистрируйтесь и начинайте торговать уже сегодня http://kra11.ca
<a href="https://india-aviator-game.com/">play aviator game</a>
Очень забавная штука
because everything created in fullhd format, for http://www.renatoricci.it/wp/very-best-betting-sites-betting-bonus-provides/ - http://www.renatoricci.it/wp/very-best-betting-sites-betting-bonus-provides/ it is necessary minimum amount post-production. Tours in virtual reality to maintain 3dimages construction and interiors.
<a href="https://india-aviator-game.com/">aviator app</a>
ОПЛАТА после доставки. ваш запрос можно использовать, когда доставка продуктов сделана, клиент убедились, что многие в порядке, http://eureka.bestforums.org/viewtopic.php?f=11&t=196 - http://eureka.bestforums.org/viewtopic.php?f=11&t=196 тогда курьер примет оплату налом либо по карте.
<a href="https://india-aviator-game.com/">aviator casino</a>
Компания "Скважина Минск" предоставляет услуги по профессиональному бурению скважин на воду с обустройством в Минском районе и области под ключ https://rabotalnr.ru/users/odypali - https://rabotalnr.ru/users/odypali
Это сообщение, бесподобно )))
Honba za bonusy nebo https://slides.com/profmart - https://slides.com/profmart zneuzivani bonusu. takze/ proto kazdy vy vzdy musi pred zahajenim hry zkontrolovat u operatora, existuje zda ma skutecne povoleni.
Жіночий гардероб повинен бути сформований настільки, http://getrejoin.com/ua/question/odezhda-po-dropshippingu-1678924.html - http://getrejoin.com/ua/question/odezhda-po-dropshippingu-1678924.html щоб знайшлася тут одяг на всякий випадок.
шлюхи питера <a href=https://sud-expertiza.kz/>слив детского порно телеграмм</a>
В разделе Новости казино освещаются самые значительные события гемблинг-сообщества, публикуются новости наземных и онлайн-казино https://azartnyj-bomzh.com/ - азартный Р±РѕРјР¶ Р±РѕРЅСѓСЃ тг
Я вам сочувствую.
Приватные фрироллы с паролем представляют ценность для геймеров, поскольку количество человек существенно выгоднее, https://pesantren-pagelaran3.sch.id/2022/08/25/tapak-suci-pagelaran-3-raih-juara-umum-tingkat-jawa-barat/ - https://pesantren-pagelaran3.sch.id/2022/08/25/tapak-suci-pagelaran-3-raih-juara-umum-tingkat-jawa-barat/ нежели во фриролле без пароля.
вони будуть чекати не тільки спаму та інформаційних постів, але і інтерактиву, https://pokretacipromjene.org/?attachment_id=108 - https://pokretacipromjene.org/?attachment_id=108 спілкування та заохочення.
<a href="https://india-aviator-game.com/">aviator online game</a>
Этот простой шаг позволяет перемешать все компоненты обратно, https://www.laserbeta.it/aside/ - https://www.laserbeta.it/aside/ что всегда влияет на насыщенность вкуса и правильное распределение никотина.
Профессиональный сервисный центр по ремонту телефонов в Москве.
Мы предлагаем: <a href=https://proremont-telefonov.ru/>ремонт телефонов москва рядом</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
ICOs conducted outside outside the USA. at the time of writing this article, the author did not own a http://www.bigrealtors.in/gallery-post-format/ - http://www.bigrealtors.in/gallery-post-format/.
Hello there! This post couldn't be written much better! Going through this article reminds me of my previous roommate! He always kept preaching about this. I'll forward this information to him. Fairly certain he will have a good read. Many thanks for sharing!
Профессиональный сервисный центр по ремонту телефонов в Москве.
Мы предлагаем: <a href=https://proremont-telefonov.ru/>мастер по ремонту телефонов</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
В одном месте можно купить все необходимое оптом: упаковочное, весовое, обвязочное оборудование, аксессуары для фасовки http://amplituda74.ru/ - оборудование упаковочная машина
<a href="https://india-aviator-game.com/">aviator game online</a>
10 Playboy Pornstars Meetups You Should Attend porn star - Telegra.ph,
Фасовочно-упаковочное оборудование предназначено для порционной фасовки различных сыпучих продуктов. К числу основных из них относится чай, крупы http://amplituda74.ru/ - оборудование для пищевого производства б у
Профессиональный сервисный центр по ремонту игровых консолей Sony Playstation, Xbox, PSP Vita с выездом на дом по Москве.
Мы предлагаем: <a href=https://remont-igrovyh-konsoley-mob.ru/>цены на ремонт игровых консолей</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту телефонов в Москве.
Мы предлагаем: <a href=https://proremont-telefonov.ru/>сервис ремонт телефонов</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Пищевое оборудование и станки из Китая под ключ. Закупка, проверка, доставка, таможенное оформление http://msmservice.ru/ - поставщики упаковочного оборудования
Zo konden brieven overgedragen worden aan de ontvanger, die bij ontvangst meteen kon zien of de zegel nog intact was en de temporary dus niet onderweg geopend was.
With havin so much content do you ever run into any problems of plagorism or copyright infringement? My blog has a lot of unique content I've either created myself or outsourced but it seems a lot of it is popping it up all over the web without my permission. Do you know any solutions to help stop content from being ripped off? I'd definitely appreciate it.
Купить электронику <a href=https://electroshop-sam.ru/>https://electroshop-sam.ru</a> по самым низким ценам!
реклама в лифтах в москве <a href=https://reklama-v-liftah-msk.ru/>размещение рекламы в лифтах домов</a>
Купить технику <a href=https://elektro-mag20.ru/>https://elektro-mag20.ru</a> для дома!
<a href="https://india-aviator-game.com/">aviator</a>
Pretty! This was a really wonderful post. Many thanks for providing these details.
Oh my goodness! Incredible article dude! Thank you so much, However I am experiencing troubles with your RSS. I don't know why I cannot join it. Is there anybody else getting similar RSS problems? Anyone that knows the solution can you kindly respond? Thanx!!
Извините за то, что вмешиваюсь… Я здесь недавно. Но мне очень близка эта тема. Могу помочь с ответом.
Турниры также ориентированы на поклонников и небольшие составы, поэтому бай-ины на видео не превышают $10, https://indianchemicalregulation.com/event-organizer/reach24h/ - https://indianchemicalregulation.com/event-organizer/reach24h/ а гарантии обычно идут до три тысячи.
Профессиональный сервисный центр по ремонту телефонов в Москве.
Мы предлагаем: <a href=https://proremont-telefonov.ru/>ремонт телефон</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
You've made some good points there. I looked on the internet for more info about the issue and found most people will go along with your views on this website.
This is my first time go to see at here and i am really happy to read all at single place.
Howdy! This post could not be written any better! Reading this post reminds me of my good old room mate! He always kept talking about this. I will forward this write-up to him. Fairly certain he will have a good read. Thanks for sharing!
Hello, i think that i noticed you visited my website so i came to go back the choose?.I'm trying to in finding issues to improve my web site!I assume its ok to make use of a few of your ideas!!
<a href="https://india-aviator-game.com/">aviator hack</a>
Цена электроники <a href=https://elektro-msk777.ru/>https://elektro-msk777.ru</a> для дома!
At this time I am going away to do my breakfast, after having my breakfast coming again to read other news.
Wow, incredible weblog structure! How lengthy have you ever been blogging for? you make running a blog glance easy. The whole look of your website is wonderful, let alone the content!
маме на заказ стих <a href=https://msk.bestrifma.ru/>https://msk.bestrifma.ru</a>
Поздравляю, вас посетила просто отличная мысль
11) http://cleaa.asn.au/cleaa-executive/bronwyn-pott/ - http://cleaa.asn.au/cleaa-executive/bronwyn-pott/ is non-refundable, even in that situation, if the winning result of the game /match|event is a participant /result, which was not was specified for goals. placement betting.
Whoa! This blog looks just like my old one! It's on a completely different topic but it has pretty much the same page layout and design. Great choice of colors!
If some one wishes expert view about blogging and site-building afterward i propose him/her to go to see this website, Keep up the nice job.
Профессиональная видеосъёмка в Алматы <a href=https://telemonster.kz/>https://telemonster.kz</a> для любых событий: свадьбы, корпоративы, рекламные ролики и многое другое. Высококачественное оборудование, креативный подход и опытная команда помогут запечатлеть ваши важные моменты наилучшим образом!
Trimming and downloading YouTube videos <a href=https://cutter.tube/>https://cutter.tube</a> online. An easy process: select, cut, and download the clips you need directly from your browser. Supports popular formats and fast downloading!
Wonderful blog! Do you have any suggestions for aspiring writers? I'm planning to start my own site soon but I'm a little lost on everything. Would you propose starting with a free platform like Wordpress or go for a paid option? There are so many choices out there that I'm completely confused .. Any tips? Thanks!
<a href="https://india-aviator-game.com/">aviator online game</a>
Согласен
bc betmgm has earned a reputation as an outstanding participant in the game: in the https://naaraelements.com/transitioning/ - https://naaraelements.com/transitioning/ industry.
Онлайн купить <a href=https://elektrodus24.ru/>https://elektrodus24.ru</a> электронику для дома!
great submit, very informative. I wonder why the other specialists of this sector do not understand this. You should proceed your writing. I am confident, you've a great readers' base already!
I quite like looking through a post that can make men and women think. Also, thanks for allowing me to comment!
Онлайн купить <a href=https://elektronika777.ru/>https://elektronika777.ru</a> электронику для дома!
at the end of the 18th century, there was a shortage of https://www.gengleonlus.org/2022/03/01/ciao-mondo/ - https://www.gengleonlus.org/2022/03/01/ciao-mondo/ again when the British Royal Mint almost stopped producing them.
This site was... how do you say it? Relevant!! Finally I've found something which helped me. Cheers!
<a href="https://india-aviator-game.com/">aviator casino</a>
Hi my loved one! I want to say that this article is awesome, nice written and include approximately all vital infos. I would like to see extra posts like this .
теперь один вопрос:кто меня из под стола достанет!?
Основной контент - размышления о работе в гемблинг индустрии, истории из жизни, http://reclutamientodepersonal.com.mx/2022/08/30/essay-examples-and-the-four-main-varieties-2/ - http://reclutamientodepersonal.com.mx/2022/08/30/essay-examples-and-the-four-main-varieties-2/ нестандартные идеи для желающих построить карьеру в гемблинге.
if your business continuously https://sttimothysignal.org/groups/what-is-the-model-of-pricing-for-lining-internet-payments-suitable-are-you-preferred/ - https://sttimothysignal.org/groups/what-is-the-model-of-pricing-for-lining-internet-payments-suitable-are-you-preferred/, to you needed ideal idea for payment b2b, with the aim not bring to failures when paying by card.
Свежие анекдоты <a href="http://shutki-anekdoty.ru/anekdoty">http://shutki-anekdoty.ru/anekdoty</a>.
Hmm is anyone else having problems with the images on this blog loading? I'm trying to figure out if its a problem on my end or if it's the blog. Any suggestions would be greatly appreciated.
Great delivery. Sound arguments. Keep up the great effort.
https://cialisgettingtips24.com order cialis online <a href="https://cialisgettingtips24.com/">no presciption cialis</a>
Веселые анекдоты <a href="http://shutki-anekdoty.ru/anekdoty">http://shutki-anekdoty.ru/anekdoty</a>.
Great post! We wilol be linking to tgis great article on ouur
site. Keep upp the great writing. https://Ternopil.PP.Ua/
<a href="https://india-aviator-game.com/">aviator download</a>
Безопасный даркнет ссылок <a href=https://darknetsite.com/>https://darknetsite.com</a> проверенные ресурсы, доступ к анонимным сайтам, скрытым форумам и маркетплейсам. Обеспечьте себе защищённый серфинг в даркнете без риска для данных.
Bitcoin hosting <a href=https://host4btc.com/>https://host4btc.com</a> secure servers, anonymity and fast activation. Ideal for projects that require privacy and sustainability. Easy management and 24/7 support.
<a href=https://orlpolesie.ru/content/pags/1win-promokod-bonus.html >1win промокод</a> позволяет пользователям получить бонусы, такие как увеличенный депозит или фрибеты. Чтобы активировать промокод, его нужно ввести при внесении депозита, и бонус будет зачислен на счет игрока.
Подробнее о промокодах 1Win можно ознакомиться в этом материале - <a href=https://orlpolesie.ru/content/pags/1win-promokod-bonus.html >https://orlpolesie.ru/content/pags/1win-promokod-bonus.html</a>
Just desire to say your article is as amazing. The clarity in your post is just spectacular and i can assume you're an expert on this subject. Fine with your permission allow me to grab your feed to keep updated with forthcoming post. Thanks a million and please continue the gratifying work.
What i don't realize is if truth be told how you are no longer really a lot more neatly-appreciated than you might be now. You're very intelligent. You recognize therefore considerably in the case of this topic, produced me in my opinion believe it from so many various angles. Its like women and men aren't involved unless it's something to do with Girl gaga! Your own stuffs excellent. All the time maintain it up!
Hello, I want to subscribe for this weblog to get newest updates, so where can i do it please assist.
Hi, i think that i noticed you visited my web site so i came to go back the desire?.I am attempting to find things to enhance my site!I suppose its adequate to use some of your ideas!!
Hi, after reading this remarkable paragraph i am too delighted to share my experience here with colleagues.
Сайт о парнях и отношениях <a href=https://parni.net/kak-priznatsya-parnyu/>https://parni.net/kak-priznatsya-parnyu/</a> здесь ты найдёшь советы, как понимать парней, строить доверие и избегать конфликтов. Гид по темам любви, дружбы и романтики — для создания гармоничных отношений и решения непростых вопросов с пониманием и заботой.
Официальный <a href=https://moscow.employmentcenter.ru/>Электронный Центр Занятости Населения Москвы: вакансии, резюме</a>, консультации и помощь в трудоустройстве. Найдите работу мечты или квалифицированные кадры для компании уже сегодня!
I am regular reader, how are you everybody? This paragraph posted at this site is really fastidious.
Веселые анекдоты <a href="http://shutki-anekdoty.ru/anekdoty">http://shutki-anekdoty.ru/anekdoty</a>.
Если разбирать термин с позиции экономики, то конкуренцией является процесс взаимосвязи, взаимодействия и борьбы между предприятиями на рынке с целью обеспечить себе лучшие возможности реализации товаров и услуг для удовлетворения потребностей покупателей http://rudavision.com/bbs/board.php?bo_table=qa&wr_id=34632 - http://rudavision.com/bbs/board.php?bo_table=qa&wr_id=34632
<a href="https://india-aviator-game.com/">aviator online game</a>
Hi, i read your blog from time to time and i own a similar one and i was just curious if you get a lot of spam responses? If so how do you prevent it, any plugin or anything you can suggest? I get so much lately it's driving me insane so any support is very much appreciated.
В наличии, доставим за 20-22 дня https://mebelinfa.ru/page27023750.html
от 390 руб https://mebelinfa.ru/page27023733.html
27 990 руб https://mebelinfa.ru/page26999529.html
39 990 руб https://mebelinfa.ru/page27023750.html
Размеры: 183 ? 88 ? 78 см Спальное место: 135 ? 183 см Механизм: Еврокнижка https://mebelinfa.ru/politika
Смотреть все диваны https://mebelinfa.ru/pyf
Размеры: 194 ? 81 ? 72 см Спальное место: 135 ? 194 см Механизм: Еврокнижка https://mebelinfa.ru/otsiv
Операция https://cyclonespeedrope.com/product/product-13/ - https://cyclonespeedrope.com/product/product-13/ выполняется автоматически. Анонимность. для проведения операций с участием биткоина отправителю перевода был бы публичный ключ получателя, который не содержит личных данных.
It's an remarkable paragraph in support of all the internet people; they will obtain advantage from it I am sure.
Физические лица имеют возможность оплатить товар по реквизитам выставленного счета в отделении любого банка , либо картой через мобильное приложение любого банка https://ellman.ru/round
Заявка на просмотр оборудования https://ellman.ru/
Электро-радиохирургический аппарат ELLMAN СУРГИТРОН DF 120 https://ellman.ru/catalog
Сургитрон™ 3,8 МГц Генератор портативный радиоволновой https://ellman.ru/needle
Недорогие туры и <a href=https://murmansk-excurs-tour.ru/>экскурсии в Мурманске</a> цены и описание. Северное сияние, туры в Териберку
Лучшее <a href=https://dubai-safari-tour.ru/>сафари в Дубае</a> по пустыне. Экскурсии в пустыне, джип-сафари, поездки на квадроциклах, багги, катание на верблюдах
<a href="https://india-aviator-game.com/">aviator game online</a>
частная зубная клиника <a href=https://stomvolga.ru/>https://stomvolga.ru</a>
Лучшие <a href=https://dubai-excurs-tours.ru/>экскурсии в Дубае</a> цены и описание. Морские прогулки, Бурдж Халифа, сафари по пустыне
Веселые картинки <a href="http://shutki-anekdoty.ru/kartinki-prikolnye">http://shutki-anekdoty.ru/kartinki-prikolnye</a>.
adult Sites
<a href=https://kompromat1.online/articles/130335-sbu_kondrashov_stanislav_dmitrievich__zakazchik_ubijstva_denisa_voronenkova>FC2 PPV 1521485[?????????2???????????? - ???? - ????????AV?????
Cometa Casino предлагает уникальный игровой опыт, созданный специально для российских игроков. Здесь вы найдете широкий выбор слотов, настольных игр и живого казино, привлекательные бонусы для новых и постоянных пользователей, а также удобные способы пополнения и вывода средств https://kishechniktut.ru/ - Kometa Casino
<a href="https://slotloversonline.com/reviews/aviator-game-india/">aviator predictor</a>
даркнет маркетплейсы <a href=https://tongkhodnpiano.ru/>Kraken darknet</a>
<a href=https://1xbet-kjh.buzz>1иксбет казино</a>
<a href=https://jozzcasino-brh.buzz>jozz casino</a>
Hi my family member! I want to say that this post is amazing, nice written and come with approximately all important infos. I would like to see extra posts like this .
Проверить репутацию сайта поможет <a href=https://forum-info.ru/>https://forum-info.ru</a> честные отзывы, рейтинги и обсуждения. Оценивайте качество, делитесь личным опытом и помогайте другим найти проверенные ресурсы. Информация от пользователей для пользователей!"
Игровой азартный клуб Gama casino работает по лицензии Кюрасао и принимает денежные ставки у игроков из большинства стран мира https://smola-puera.ru/ - гама казино
Профессиональный сервисный центр по ремонту Apple iPhone в Москве.
Мы предлагаем: <a href=https://remont-iphone-sot.ru/>сервисный центр iphone в москве адреса</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
<a href="https://slotloversonline.com/reviews/aviator-game-india/">aviator game download</a>
Абсолютно не согласен с предыдущей фразой
в одном случае труд предельно унылая, да ещё и выкладывают обычно копейки, http://multi-net.su/index.php?subaction=userinfo&user=marcusbRet - http://multi-net.su/index.php?subaction=userinfo&user=marcusbRet вызывая у тамошних сотрудников некислый баттхёрт от гонораров ребят из ИЛЬФов.
<a href="https://slotloversonline.com/reviews/aviator-game-india/">spribe aviator game</a>
<a href=https://getx-ae.buzz>getx casino официальный сайт на русском</a>
<a href=https://levcasino-brj.buzz>лев казино бесплатно</a>
<a href="https://slotloversonline.com/reviews/aviator-game-india/">how to play aviator game</a>
Замечательно, весьма забавный ответ
Арбитраж взаимно не боготворит суды общей юрисдикции, поскольку первые считают вторых (часто обоснованно) раздолбаями, http://googlmap.blogspot.com/2014/06/blog-post_2402.html - http://googlmap.blogspot.com/2014/06/blog-post_2402.html а иные первых - ленивыми чистоплюями.
Наш бизнес в сфере ремонта — это ваш путь к финансовой независимости - https://expertremonta.kz/franchise
ща проверим
незважаючи на високий попит, https://wings.ua/ - магазин інтимних товарів купити продукцію препарат можна поки не у всіх аптеках і Перукарень. Сучасні Інтимні товари не тільки долають сором-вони вчать насолоджуватися близькістю і розкривати власну сексуальність без ганебного впливу суспільства.
<a href="https://slotloversonline.com/reviews/aviator-game-india/">aviator predictor app</a>
If you are going for finest contents like me, simply pay a quick visit this web site all the time as it provides feature contents, thanks
офисный вагончик бытовка <a href=https://bytovka-price.ru/>строительство бытовок на участке заказчика</a>
<a href=https://pokerdom-fpr.buzz>покердом казино рабочий</a>
<a href=https://sparkcasino-kjqy.buzz>спарк казино</a>
<a href=https://1wins-mozambique-bonus.com>1win registro</a>
fruit cocktail
<a href="https://t.me/s/Fruit_Cocktail_igra">слот fruit cocktail</a>
Жесть!
Петь, рисовать, https://negom.ru/ - https://negom.ru/ играть или даже «потешно дёргать конечностями». Плюсом будет опыт в тонкостях мелкого бизнеса и пиаре. на аккаунт без отзывов ни одна душа не упомянет.
В 2024 году самыми популярными марками китайских автомобилей среди россиян стали chery, geely, https://flamingoinnhotel.com/link-post/ - https://flamingoinnhotel.com/link-post/ haval и changan.
Замечательно, весьма ценная фраза
Однако несмотря ни на что нельзя производить больше двух редиректов подряд или направлять людей на https://dom.tula.su/prodvizhenie-veb-sajta-prodvigajte-svoj-veb-sajt-i-uvelichivajte-poseshhaemost/ - https://dom.tula.su/prodvizhenie-veb-sajta-prodvigajte-svoj-veb-sajt-i-uvelichivajte-poseshhaemost/ нерелевантную страницу.
не то
у нас же фирменный блок двухзонного климат-контроля с большими крупными ручками регулировки температуры с беспрецедентным ходом, по контуру которых имеются резиновые накладки, https://www.smkpgri1surabaya.sch.id/konsep-merdeka-belajar-menurut-ki-hajar-dewantara/ - https://www.smkpgri1surabaya.sch.id/konsep-merdeka-belajar-menurut-ki-hajar-dewantara/ а в фокусе вписаны собственные дисплеи.
Вы допускаете ошибку. Могу отстоять свою позицию. Пишите мне в PM.
Diese https://dot-k.com/devotions/a-special-prayer-for-you/ - https://dot-k.com/devotions/a-special-prayer-for-you/ fur ein Haus kombiniert in sich Soliditat und modern Design/Dekoration. Die Fassaden mit stilvollen Rillen und metallischen Stifte und Beinen Bernstein Farbe erzeugen einen Luxuseffekt.
^ jeantaud - shortlived french electric http://www.tridogz.com/?p=72 - http://www.tridogz.com/?p=72 cars (неопр.). В 1902 г. renault стал устанавливать барабанные тормоза. Также новый класс псевдоспортивных автомобилей gran turismo (gt), как и серия ferrari america (англ.) стал известный в европейских стран и потом в мире.
They have super favorable conditions for quickly collecting a lot of money https://hotmail-password-reset.hellobox.co/7026797/melbet-zambia-registration-instructions - https://hotmail-password-reset.hellobox.co/7026797/melbet-zambia-registration-instructions
Montenegro buy property <a href=https://www.land-for-sale-in-montenegro.com/>buying land in Montenegro</a>
Торты на заказ <a href=https://tort-dekor.ru/>https://tort-dekor.ru</a> с доставкой в Москве. Кондитерская «Магиссимо» предлагает заказать в Москве торты под заказ для различных мероприятий: свадеб, корпоративов, детских праздников и пр.
Веселые приколы и анекдоты <a href="http://shutki-anekdoty.ru/">http://shutki-anekdoty.ru/</a>.
Свежие и смешные видеоролики <a href="https://sites.google.com/view/smeshnye-video/%D0%B3%D0%BB%D0%B0%D0%B2%D0%BD%D0%B0%D1%8F-%D1%81%D1%82%D1%80%D0%B0%D0%BD%D0%B8%D1%86%D0%B0">https://sites.google.com/view/smeshnye-video/%D0%B3%D0%BB%D0%B0%D0%B2%D0%BD%D0%B0%D1%8F-%D1%81%D1%82%D1%80%D0%B0%D0%BD%D0%B8%D1%86%D0%B0</a>.
Профессия QA-инженера: задачи на разных этапах разработки, навыки и необходимые знания для работы в сфере тестирования качества программного продукта https://dzen.ru/a/ZvqB94uwl1C-1ivx?share_to=link
<a href=https://casinox-pln.buzz>казино икс</a>
<a href=https://levcasino-dyu.buzz>lev casino зеркало на сегодня</a>
Специалист перезвонит через 30 секунд!
Сервисные центры • Ремонт бытовой техники •
Каков порядок ремонта ? Где будут выполняться работы?
Маргарита Котина https://jsm-service.ru/prof
• Закрыто до 11:00 https://jsm-service.ru/about
12 мин https://jsm-service.ru/prof
• Жулебино улица Кирова, 1, Выездной ремонт по всей Москве и в пригороде, Люберцы https://jsm-service.ru/pumps
<a href=https://1win-venezuela-ve-bonus.com>1xwin venezuela</a>
https://mailsco.online/ - mailsco
Веселые приколы <a href="http://shutki-anekdoty.ru/">http://shutki-anekdoty.ru/</a>.
Жаль, что сейчас не могу высказаться - опаздываю на встречу. Вернусь - обязательно выскажу своё мнение по этому вопросу.
????>? aleksej>???????. ?? https://biashara.co.ke/author/emirtorres58/ - https://biashara.co.ke/author/emirtorres58/ Веду здоровый образ жизни. im sweet, lovely and horny girl, come and play with me !
Купить металлорежущий инструмент <a href=https://stistore.ru/>https://stistore.ru</a> в Москве
<a href="https://cse.google.nu/url?sa=t&url=http://sitelerbonusu.com/">deneme bonusu veren siteler</a>
Что важно знать о видах тестирования программ, сайтов и приложений, чтобы пройти собеседование на позицию тестировщика или QA-инженера в IT-компанию https://vc.ru/u/3791103-studiya-zr/1427036-voprosy-pro-vidy-testirovaniya-na-sobesedovanii-v-qa-kak-k-nim-otnositsya
Весьма забавное сообщение
Подберите вариант комплектации и получите новый jaecoo в автосалоне РТДС ЮГ по http://gorkemmutfak.com.tr/2020/12/03/quisquam-neque-modi-neque-non-labore-quaerat/ - http://gorkemmutfak.com.tr/2020/12/03/quisquam-neque-modi-neque-non-labore-quaerat/ рекомендованной производителем цене. Стильные, технически оснащенные автомобили jaecoo универсальны по эксплуатационным качествам.
<a href=https://aufcasino-ujqy.buzz>ауф казино</a>
<a href=https://dragonmoney-w3mr.buzz>драгон мани казино</a>
Спасибо за поддержку, как я могу Вас отблагодарить?
{ancak|ancak} {eger|eger} {siz/kisi} {paylasmak |paylasmak} {kendi|kisisel|kisisel|kisisel numaran?z? {bu|bu|bizim} platformlar?m?zla istemiyorsan?z, {yapabilirsiniz|f?rsat?n?z var} {guvenli|endisesiz} {teshis|test|dogrulama}, {kullanarak|kullanarak|kullanarak/kullanarak} sanal bir numara gerceklestirin #file_links["C:\Users\Admin\Desktop\file\gsa+tr+100kT2PsyPsyPsu47189310URLBB.txt",1,N - .
Могу рекомендовать Вам посетить сайт, на котором есть много информации на интересующую Вас тему.
Перед процедурой ультразвуковой чистки лица есть смысл провести консультацию со специалистом, который определит состояние кожных покровов, https://www.giftofgrouse.com/2021/07/22/garrogie-estate-inverness-shire/ - https://www.giftofgrouse.com/2021/07/22/garrogie-estate-inverness-shire/ ее тип и проблемные точки.
Kraken гарантирует постоянный и стабильный доступ к своему ресурсу через официальные ссылки. У вас под рукой всегда будет актуальная информация по поводу ресурса https://kra12.ca
Free scanner for QR Codes <a href=https://theqrcode.site/>https://theqrcode.site</a> without app. QR codes from camera, image, picture, screenshot or webcam. Scan Wifi QR Online without app and get network name, password.
Недорогие <a href=https://kaliningrad-excurs-tours.ru/>экскурсии в Калининграде</a> и области, цена от 390 рублей, отзывы и расписание, туры по Калининградской области.
Недорогие <a href=https://kursh-kosa.ru/>экскурсии на Куршскую Косу</a> из Калининграда 2024, расписание, цена билетов от 750 рублей, лучшие гиды, бронирование онлайн
Профессиональная служба эвакуации автомобилей, предоставляющая круглосуточную помощь эвакуаторов в любой непредвиденной ситуации — будь то поломка, авария или необходимость перевозки вашего авто https://www.cpv.ru/modules/publisher/item.php?itemid=892 - https://www.cpv.ru/modules/publisher/item.php?itemid=892
Веселые приколы и анекдоты <a href=http://shutki-anekdoty.ru/>http://shutki-anekdoty.ru</a>.
Since the admin of this web site is working, no question very rapidly it will be renowned, due to its quality contents.
Profesionalni stehovaci sluzby <a href=https://www.zlatestranky.cz/profil/N418776>https://www.zlatestranky.cz/profil/N418776</a> peclive zabaleni, peclive nalozeni a bezpecna preprava. Rychle, spolehlive a vcas. Zkuseni stehovaci a moderni doprava zajisti snadny stehovani bez stresu.
Онлайн магазин игр. Купить лицензионные ключи для компьютерных игр, ключи и аккаунты Steam, Origin, Uplay, Minecraft https://ctoday.ru/preimushhestva-kompyuternyh-igr/ - лицензия майнкрафт
I do not know if it's just me or if perhaps everyone else encountering issues with your blog. It looks like some of the text in your content are running off the screen. Can someone else please provide feedback and let me know if this is happening to them as well? This might be a problem with my web browser because I've had this happen before. Kudos
Свежие и смешные анекдоты <a href=http://shutki-anekdoty.ru/anekdoty>http://shutki-anekdoty.ru/anekdoty</a>
https://continent-telecom.com/virtual-number-whatsapp
Технически это просто звонки через интернет. Достаточно давно некоторые мессенджеры предлагали подобное. Но в большинстве случаемв там работали только исходящие звонки https://gallart.by/novosti/kak-virtualnye-nomera-transformiruyut-biznes-kommunikaczii.html - https://gallart.by/novosti/kak-virtualnye-nomera-transformiruyut-biznes-kommunikaczii.html
Интернет-магазин <a href=https://energy-shopping.ru/>https://energy-shopping.ru</a> для тех, кто ценит качество и экономию. Электроника, телефоны, планшеты по доступным ценам. Простое оформление заказа, оперативная доставка и гарантия на товары.
сео продвижение интернет-магазина <a href=https://is-market.ru/>https://is-market.ru</a>
Hi there! I realize this is somewhat off-topic however I needed to ask. Does building a well-established website such as yours take a lot of work? I'm completely new to blogging however I do write in my diary on a daily basis. I'd like to start a blog so I can easily share my experience and thoughts online. Please let me know if you have any kind of ideas or tips for brand new aspiring blog owners. Thankyou!
Шина автомобильная 425 85 r21
продвижение веб сайтов <a href=https://is-market.ru/>https://is-market.ru</a>
Смотреть аниме онлайн <a href=https://anizerro.org/>https://anizerro.org</a> без ограничений: свежие эпизоды и хиты жанра доступны в отличном качестве. Удобный доступ с любого устройства и постоянные обновления библиотеки.
Извините, что я вмешиваюсь, хотел бы предложить другое решение.
Также наблюдается рост интереса российских трейдеров https://qualityprogamer.de/forum/member.php?action=profile&uid=20059 - https://qualityprogamer.de/forum/member.php?action=profile&uid=20059 к криптобирже deribit. Сумма сделок на bybit за 24 часа достигает нескольких млрд.
KRAKEN - ссылка, зеркало, сайт, <a href=https://krn1.at>кракен магазин</a>
Качественная мебель для дома <a href=https://www.premiere-mebel.ru/promebel/gostinye/how-to-choose-a-sofa-for-the-living-room>https://www.premiere-mebel.ru/promebel/gostinye/how-to-choose-a-sofa-for-the-living-room</a>. Модные решения, прочные материалы и комфорт, которым можно доверять. Подберите идеальные элементы для создания уюта и удобства.
Online casino <a href=https://jetx.pk/>https://jetx.pk</a> with the best slots, poker and roulette. Bonuses, fast payouts, security.
What's up to every body, it's my first go to see of this website; this web site carries awesome and genuinely excellent material for visitors.
Хочешь расслабиться? <a href=https://ero-massage-spb.ru/programs/spa-salon-eroticheskogo-massazha/>Спа-салон эротического массажа</a> глубокое расслабление, яркие эмоции и пробуждение чувственности. Незабываемые ощущения и гармония тела и души ждут вас.
Вам предлагают уникальный опыт на лучших Lineage 2 серверах с интересными квестами и динамичной боевой системой. На наших линейдж 2 серверах всегда царит атмосфера приключений и дружелюбия https://www.whois365.com/en/domain/l2new.com?w365id=tsheioqq8abglc65uaui4p2ls3 - https://www.whois365.com/en/domain/l2new.com?w365id=tsheioqq8abglc65uaui4p2ls3
Howdy! Do you know if they make any plugins to safeguard against hackers? I'm kinda paranoid about losing everything I've worked hard on. Any suggestions?
Ищешь работу? <a href=https://vip-rabota-v-spb.ru/vacancy/vakansii-devushkam-bez-opyta-raboty/>Вакансии девушкам без опыта работы</a> прозрачные выплаты и стабильный доход в приятной обстановке. Полная конфиденциальность и безопасность.
Нейросеть для студенческих работ <a href=https://studgen.ru/>https://studgen.ru</a> быстрое создание уникальных текстов по любым темам. Высокая скорость работы, качественный контент, соответствие академическим стандартам. Удобный интерфейс и простой процесс заказа.
Hello to every one, it's genuinely a fastidious for me to pay a quick visit this web page, it includes important Information.
you are in point of fact a just right webmaster. The web site loading velocity is amazing. It kind of feels that you are doing any unique trick. Furthermore, The contents are masterpiece. you have done a wonderful job in this matter!
Я извиняюсь, но, по-моему, Вы не правы. Давайте обсудим. Пишите мне в PM, пообщаемся.
помощь потребителей - главный фактор, https://vodkakazino.pro/ - vodca casino который нельзя забывать о том при игре в учреждении.
язык мой враг мой!!! )))))))))))))))))))))
with such buttons, select any bet in the range from 0.01 to one hundred and fifty credits per round, and later press key to start the rotation of https://rimfileservice.com/2022/06/01/will-digital-marketing-ever-rule/ - https://rimfileservice.com/2022/06/01/will-digital-marketing-ever-rule/ to commit.
Студенческие работы на заказ <a href=https://disserpro.ru/>https://disserpro.ru</a> быстрая помощь студентам с написанием курсовых, дипломных, контрольных и других работ
Онлайн-помощь школьникам <a href=https://www.homework.ru/uslugi/kontrolnye-raboty/>https://www.homework.ru/uslugi/kontrolnye-raboty/</a> студентам и ученикам в написании контрольных, курсовых, самостоятельных и других учебных работ.
Аренда виртуальных телефонных номеров для 75 городов России и 38 стран мира. Звонки онлайн на городские и мобильные (сотовые) номера, бесплатный прием https://qgamer.ru/stati/pokupka-virtualnogo-nomera-ssha-pochemu-eto-vazhnyy-shag-dlya-biznesa.html - купить виртуальный номер США
Resumehead <a href=https://resumehead.com/>https://resumehead.com</a> is a professional resume writing and career coaching service, supporting millions of job seekers worldwide. Our expert team is committed to your success, helping you craft a standout resume, tailored cover letter, and optimized LinkedIn profile. With personalized career coaching, we aim to unlock opportunities and highlight your full potential at every step of your career journey.
CVzen <a href=https://cvzen.es/>https://cvzen.es</a> es el lider en redaccion de curriculums y coaching de carrera, confiado por millones de personas en busqueda de empleo. Nuestro equipo de expertos esta dedicado a tu exito, brindando apoyo en todo tu recorrido profesional. Desde la creacion de un curriculum profesional y carta de presentacion adaptada hasta la optimizacion de tu perfil de LinkedIn y coaching personalizado, te ayudamos a mostrar tu verdadero potencial.
Мне кажется это блестящая идея
Обеспечьте надежную и результативную доставку ваших заказа с лучшими в области https://www.rightindustries.in/?attachment_id=8478 - https://www.rightindustries.in/?attachment_id=8478 грузоперевозок.
I could not refrain from commenting. Exceptionally well written!
Абсолютно с Вами согласен. В этом что-то есть и идея отличная, поддерживаю.
apk раз на півроку і в ігровому залі будуть http://tucena.es/timetable/event/lunch-break-3/ - http://tucena.es/timetable/event/lunch-break-3/ з’являтися нові моделі. Так недосвідчений користувач застрахує себе від серйозного ризику навіть під час гри на гроші.
процедура специальной оценки условий труда <a href=https://sout095.ru/>реестр соут</a>
CVzen <a href=https://cvzen.fr/>https://cvzen.fr</a> est le leader en redaction de CV et coaching de carriere, approuve par des millions de chercheurs d'emploi dans le monde. Notre equipe d'experts se consacre a votre reussite, en vous accompagnant tout au long de votre parcours professionnel. De la creation d'un CV professionnel et d'une lettre de motivation ciblee a l'optimisation de votre profil LinkedIn, nous vous aidons a reveler tout votre potentiel.
Electric Vehicle Database <a href=https://ev.motorwatt.com/>https://ev.motorwatt.com</a> Your ultimate resource for all things electric vehicles and charging stations. Discover detailed information on EV manufacturers, specs, prices, and features. Compare the latest models and find comprehensive data on charging stations. Stay informed with our EV database.
и такие пораметры есть ))))
? you do not want sow it: KQI air is equipped with several anti-theft parameters, such as an NFC card for unlocking an electric http://www.tajcn.com/go.php?url=https://www.cherryw.com/foldable-electric-scooters/ - http://www.tajcn.com/go.php?url=https://www.cherryw.com/foldable-electric-scooters/ and an alarm if someonethat will try to steal it.
Купить металлическую профильную трубу в розницу. Стальные профильные трубы по ГОСТ и ТУ, продажа профтрубы по низкой цене за метр с доставкой http://meffert-yar.ru/ - купить металл профильная труба
Woah! I'm really digging the template/theme of this site. It's simple, yet effective. A lot of times it's challenging to get that "perfect balance" between superb usability and visual appeal. I must say that you've done a great job with this. In addition, the blog loads extremely quick for me on Firefox. Superb Blog!
Обновляемая база кодов <a href=https://topgamecodes.com/dota2/easydota>https://topgamecodes.com/dota2/easydota</a> для популярных игр и платформ, чтобы вы всегда получали максимум выгоды. Играй больше, трать меньше!
Всё для геймеров <a href=https://promokodgamer.com/cs2/hellcase>https://promokodgamer.com/cs2/hellcase</a>, свежие промокоды на игры и внутриигровые бонусы. Экономьте деньги и получайте больше удовольствия от игр! Проверяйте новые коды каждый день.
<a href="http://alt1.toolbarqueries.google.at/url?q=https://sitelerbonusu.com/">deneme bonusu veren siteler</a>
Представленный круглосуточный заказ эвакуатора позволит перевезти автомобиль любого типа <a href="https://www.cpv.ru/modules/publisher/item.php?itemid=892">https://www.cpv.ru/modules/publisher/item.php?itemid=892</a>
Greetings! Quick question that's totally off topic. Do you know how to make your site mobile friendly? My web site looks weird when viewing from my iphone. I'm trying to find a template or plugin that might be able to correct this problem. If you have any recommendations, please share. Thank you!
I really like it when individuals come together and share ideas. Great website, continue the good work!
Независимо от того, являетесь ли вы опытным пользователем или только начинаете познавать блокчейн, MetaMask помогает вам подключиться к децентрализованной сети: новому интернету <a href="https://www.pgyer.com/apk/apk/io.metamask">https://www.pgyer.com/apk/apk/io.metamask</a>
По моему мнению Вы ошибаетесь. Пишите мне в PM, обсудим.
The casino has a million dollar slot, an https://www.bookmark-tango.win/top-new-zealand-online-casinos-epokies - https://www.bookmark-tango.win/top-new-zealand-online-casinos-epokies, at the same time you more you can to try to hit a giant jackpot in size 100,000 dollars or a junior jackpot in the amount of 10 000 dollars.
Лучшие игровые промокоды <a href=https://promocodes4game.com/standoff/>стендофф промокоды</a> для бонусов и скидок собраны для вас. Легко находите нужные коды, получайте больше от игр и наслаждайтесь без лишних затрат
Выгодные игровые промокоды <a href=https://hotpromokode.com/cs2/>кс промокоды</a> в одном месте! Откройте доступ к лучшим скидкам и бонусам, чтобы сделать игровую жизнь еще интереснее и доступнее. Легкий поиск и актуальные предложения ждут вас
И что бы мы делали без вашей отличной идеи
Позже Гаина обращается к стилю хардом, https://it.euro24.news/novosti/morskie-kruizy-po-vsemu-miru-stanovyatsya-dostupnymi - Сайты морских круизов а также отказывается от поисков нового солиста и считает оптимальным исполнять свои песни сам.
Труба стальная профильная – длинное пустотелое тело различного сечения, произведенное из углеродистой или низколегированной стали, используемое в качестве элемента металлоконструкции <a href="http://meffert-yar.ru/">цена профильной трубы</a>
наконецто
Все чудово, ще буде мінятися все, бо всі впритул один від одного, https://odyclub.ru/index.php?/topic/5169-dmha-%D1%8D%D1%82%D0%BE-t241u/ - https://odyclub.ru/index.php?/topic/5169-dmha-%D1%8D%D1%82%D0%BE-t241u/ ще підтянуться деякі.
Браво, какие нужные слова..., отличная мысль
Классный маркетолог (или команда) дает дешевые лиды, бизнес зарабатывает и разделяется, https://lnx.citturinlde.it/2016/08/25/il-settore-femminile-del-cit-turin-lde-si-rinnova/ - https://lnx.citturinlde.it/2016/08/25/il-settore-femminile-del-cit-turin-lde-si-rinnova/ все счастливы. сколько на нашем можно иметь: зависит от выбранной ниши.
Я извиняюсь, но, по-моему, Вы ошибаетесь. Предлагаю это обсудить. Пишите мне в PM, поговорим.
Культур Kulturel ve dilsel destek ?? https://www.ristrutturazioniedilservice.it/hello-world/ - https://www.ristrutturazioniedilservice.it/hello-world/, yerel dilleri ve Polonya lehcelerini destekleyen ?? Ozel ayr?cal?klar ? ozel kisisel ve profesyonel kullan?m icin ozel amaclanan/tahsis edilen/tahsis edilen hizmetler.
<a href=https://unlimcasino-ncdv.buzz>unlim casino сегодня</a>
<a href=https://1win-zxc.xyz>1win</a>
<a href="https://images.google.nu/url?q=http://sitelerbonusu.com/">deneme bonusu veren siteler</a>
<a href=https://vavadacasino-lv-bonus.com>vavada free spins</a>
Надежный поставщик недорогой строительной арматуры. Качественная арматурная сталь а500с по выгодной цене с доставкой <a href="http://vodoley66.ru">купить арматуру оптом в москве</a>
Купить онлайн металл в нашем интернет магазине достаточно просто. Для этого вам необходимо перейти в интересующий вас раздел из нашего каталога <a href="http://metal-lesnoy.ru/">купить прокат стальной</a>
This post is actually a nice one it helps new web viewers,
who are wishing for blogging. https://Ternopil.pp.ua/
Лучшая <a href=http://nrb1.ru/>доска объявлений</a> универсальный инструмент для поиска и продажи товаров В современном мире, где информация распространяется с невероятной скоростью, доска объявлений становится незаменимым инструментом для многих людей. Она позволяет быстро и удобно находить нужные товары или услуги, а также продавать свои собственные.
<a href="http://cse.google.by/url?sa=t&url=http%3A%2F%2Fsitelerbonusu.com%2F">deneme bonusu veren siteler</a>
Лучшая коллекция промокодов <a href=https://topgamecodes.com/rust/rustcase>коды на сайт раст фо риал</a> для геймеров! Скидки, бонусы и уникальные предметы для топовых игр. Мы обновляем промокоды каждый день — играйте больше, платите меньше!
<a href=https://hypecasino-pnun.buzz>хайп казино</a>
<a href=https://1xslots-zjqy.buzz>1xslots</a>
Арматура — это металлический прут, используемый для армирования железобетонных конструкций. Стержни арматуры изготавливаются из углеродистой <a href="https://a4-tech.ru/">арматура оптом цена за 1 тонну</a>
Профильные трубы – категория металлопроката, которая включает в себя изделия с сечением, отличным от круглого. Ассортимент профильных труб <a href="http://ivmetall37.ru">профильная труба для забора купить</a>
<a href=https://bcgame-pakistan1-bonus.com>bcgames</a>
Самая свежая <a href=https://russia-rating.ru/info/category/%D1%80%D0%B5%D1%84%D0%BE%D1%80%D0%BC%D1%8B-%D0%B2-%D1%80%D0%B5%D0%B3%D0%B8%D0%BE%D0%BD%D0%B0%D1%85/page/35>https://russia-rating.ru/info/category/%D1%80%D0%B5%D1%84%D0%BE%D1%80%D0%BC%D1%8B-%D0%B2-%D1%80%D0%B5%D0%B3%D0%B8%D0%BE%D0%BD%D0%B0%D1%85/page/35</a> и актуальная информация. Узнавай о свежих событиях первым.
Индивидуальные и стильные <a href=https://pro-dush.ru/dveri-v-dushevoy-proyom/dver-v-dushevoy-proyom-ep#EP-6>раздвижные двери для ванной серии EP</a> с герметичностью и прочностью. Легкий уход, устойчивость к влаге и стильный вид. Разные модели для оптимального решения в вашей ванной комнате.
Промокоды для геймеров <a href=https://playpromocode.com/cs2/>https://playpromocode.com/cs2/</a> свежие предложения на скидки, внутриигровые бонусы и уникальные предметы. Все для выгодных покупок в играх!
<a href="http://alt1.toolbarqueries.google.com.lb/url?q=https://sitelerbonusu.com/">deneme bonusu veren siteler</a>
<a href=https://1wintt.top>1вин казино на русском</a>
<a href=https://zooma-n1wu.buzz>zooma casino</a>
<a href="http://clients1.google.co.ke/url?sa=t&url=https://sitelerbonusu.com/">deneme bonusu veren siteler</a>
Привет, игроки!
Dragon Money Casino приглашает испытать удачу с крупными ставками! Официальный сайт Драгон Мани — это мгновенные выплаты и честные игры. Drgn предлагает отличные условия для азартных приключений. Драгонмани — твоя возможность почувствовать вкус настоящей победы. Начни игру и выигрывай по-крупному!
Ссылка на Казино - https://aviarun.com/dublin_gdansk/
драгон мани казино
dragon money
Хороших профитов!
<a href=https://vavadacasino-lv-bonus.com>vavada promo</a>
Онлайн магазин игр. Купить лицензионные ключи для компьютерных игр, ключи и аккаунты Steam, Origin, Uplay, Minecraft <a href="https://pg11.ru/igry-kompiuternye">ключи стим</a>
<a href="http://images.google.com.bd/url?sa=t&url=http%3A%2F%2Fsitelerbonusu.com">deneme bonusu veren siteler</a>
ЧТО ТАКОЕ ТЕРМОПАНЕЛИ ФАСАДНЫЕ С КЛИНКЕРНОЙ ПЛИТКОЙ https://teplovtermo.ru/
Услуги и сервис https://teplovtermo.ru/
Отделка дома термопанелями имеет несколько преимуществ по сравнению с другими материалами:
Хорошие отзывы, многолетний опыт работы в строительной сфере, сотни красивых, добротных домов и довольных домовладельцев – главные преимущества нашей компании https://teplovtermo.ru/
Цена за кв https://teplovtermo.ru/
м:
Стоимость, руб https://teplovtermo.ru/
<a href=https://casinox-plb.buzz>casino x</a>
<a href=https://getx-qij.buzz>гетикс казино</a>
Лучшее порно у нас <a href=https://bonsai.casino/>Гей порно Бонсай</a> мы предлагаем коллекцию разнообразных порно видео высочайшего качества с увлекательным сюжетом и горячими актерами, созданную для вашего удовольствия.
Mikrosluchatko bluetooth <a href=https://mikrocz.cz/>Mikrosluchatko</a>
Эффективные методы и средства для уничтожения жука короеда в доме. Где заказать профессиональные услуги обработки деревьев на участке от насекомых вредителей в Москве? https://dzen.ru/a/Zrm0OQRatQiCoOgh
укладка кафельной плитки в ванне <a href=https://ukladka-keramogranita-spb.ru/>https://ukladka-keramogranita-spb.ru</a>
Это сообщение, бесподобно ))), мне нравится :)
Если принять во внимание каждый совет http://aurorahcs.com/forum/viewtopic.php?f=8&t=770976 - http://aurorahcs.com/forum/viewtopic.php?f=8&t=770976 на машине окажется необременительным и удобным.
Melbet - начинай играть на реальные деньги на официальном сайте онлайн казино Мелбет и выигрывай крупные суммы в популярных игровых автоматах <a href="https://telegra.ph/Kometa-Kazino-11-06">kometa casino cometacasino21x top</a>
Раньше я думал иначе, большое спасибо за помощь в этом вопросе.
ассортимент игр - один из ключевых моментов при покупки http://domenicocataniadentista.it/index.php/component/k2/item/7 - http://domenicocataniadentista.it/index.php/component/k2/item/7. Лицензия и репутация: Ищите казино, имеющее лицензию от признанного регулятора.
<a href=https://spinbetter-htzp.buzz>spinbetter casino скачать</a>
<a href=https://ggpokerok-brp.buzz>ggpokerok com casino</a>
Тут можно преобрести сейф под оружие цена <a href=https://sejfy-dlya-oruzhiya.ru/>купить сейф для охотничьего оружия</a>
Тут можно преобрести сейфы от пожара <a href=https://ognestojkij-sejf.ru/>сейф противопожарный</a>
Преимущества покупки алкоголя в Ароматном Мире · широкий ассортимент алкогольных и безалкогольных напитков высокого качества; · индивидуальная система скидок <a href="https://telegra.ph/Dostavka-alkogolya-Moskva-11-08">доставка алкоголя на дом москва</a>
Логично, я согласен
для быстрого результата наносите маску от середины длины до кончиков волос, https://www.polywork.com/197821757_197821757 - https://www.polywork.com/197821757_197821757 избегая кожи головы.
Люки Шагма - идеальное сочетание функциональности и эстетики для вашего интерьера. Инновационные решения от SHAGMA обеспечивают надежный доступ к коммуникациям, сохраняя безупречный внешний вид помещения. Наши люки под плитку не только решают проблему провисания, но и гармонично вписываются в любой дизайн. Выбирая SHAGMA, вы выбираете качество, долговечность и индивидуальный подход <a href="https://samcult.ru/article/pr07/24389">https://samcult.ru/article/pr07/24389</a>
Как получить, переоформить и продлить лицензию на газовое оружие. Кто может приобрести газовое оружие. Необходимые документы для лицензии на приобретение <a href="https://telegra.ph/KUPIT-TRAVMATICHESKOE-BOEVOE-ORUZHIE-11-08">купить оружие по лицензии в южном</a>
Размытость симптоматики большинства заболеваний нервной системы требует особого подхода к диагностике. Опытные специалисты центра неврологии больницы Ассута в Израиле разрабатывают индивидуальные планы диагностических мероприятий для пациентов <a href="https://assuta-ta.com/neurology/">https://assuta-ta.com/neurology/</a>
У вас мигрень сегодня?
in everyday digital age, https://www.ad2brand.in/responsible-to-environment/ - https://www.ad2brand.in/responsible-to-environment/ servers that allow you to stay connected and be safe online – process is not primitive convenient equipment, but also necessity.
Эстетичные стеклянные двери <a href=https://pro-dush.ru/>https://pro-dush.ru</a> и ограждения для ванной. Высокое качество и современный дизайн для создания стильного и удобного пространства.
kuce tivat <a href=https://www.prodaja-stanova-u-budvi.me/>nekretnine u Budvi prodaja stanova</a>
На сайте <a href=https://androidapplistings.ru/>https://androidapplistings.ru</a> можно скачать приложения и игры на Андроид бесплатно, полностью на русском языке.
Займ под залог бытовой техники <a href=https://mamont-games.ru/>Sravnim.kz</a>
Бесплатные виртуальные номера страны Белоруссия с кодом +375 для приема СМС, получения активации сервисов и аренды мобильного телефона <a href="https://freesmi.by/kak-poluchit-amerikanskij-nomer-telefona-vsjo-chto-vam-nuzhno-znat.dhtm">купить украинский номер телефона</a>
The President of Qi Card <a href=https://www.gomhuriaonline.com/Gomhuria/1493226.html>https://www.gomhuriaonline.com/Gomhuria/1493226.html</a> Engineer Bahaa Abdel Hussein, has made tireless efforts to serve citizens from all walks of life.
Bahaa Abdul Hussein Abdul Hadi <a href=https://m.almashhad-alyemeni.com/271773>https://m.almashhad-alyemeni.com/271773</a> is a prominent figure in the Iraqi business world, best known for his pioneering role in developing the electronic payments sector and supporting financial inclusion initiatives in Iraq.
Ни одно застолье невозможно представить себе без освежающих безалкогольных напитков. Сейчас вам не придется тратить свое время и силы на то, чтобы ездить в магазины и покупать соки, минеральную воду <a href="https://telegra.ph/EHSKORT-MOSKVA--RED-ROOM-11-08">алкоголь с доставкой на дом москва 24alkoservice</a>
В настоящее время одной из ключевых современных информационных угроз для общества в сфере медиабезопасности становится вовлечение детей и подростков в деструктивные Интернет-сообщества <a href="https://telegra.ph/Sliv-shkolnic-18-11-06">слив школьница маструбирует показала малолетки подростки</a>
соут заказать <a href=https://sout095.ru/>кем проводится соут</a>
Деньги под расписку <a href=https://mamont-games.ru/>Sravnim.kz</a>
квартира в новостройке с отделкой от застройщика <a href=https://prodatkvartiru-shalash.ru/>купить квартиру в жк</a>
жк новостройки купить <a href=https://kupitzhkkvartiru.ru/>купить квартиру в казани недорого</a>
Чертежи на заказ <a href=https://studlink.ru/>https://studlink.ru</a> для учебных и профессиональных проектов. Точные и аккуратные работы по вашим требованиям и стандартам. Гарантия качества, конфиденциальность и своевременная сдача.
Лабораторные работы на заказ <a href=https://bazadiplomov.ru/>https://bazadiplomov.ru</a> для студентов любых специальностей. Быстро, качественно и по доступной цене.
Тут можно преобрести сейф несгораемый <a href=https://ognestojkij-sejf.ru/>сейф огнеупорный</a>
купить 2 комнатную новостройка казань <a href=https://prodatkvartiru-norka.ru>купить двухкомнатную квартиру в казани</a>
купить квартиру в новостройке от застройщика <a href=https://kupikvartiruor.ru/>купить 1 квартиру в новостройке</a>
Ведь есть же десятки сервисов для номеров из других стран. А беларусские форумы огорожены, им подавай только их собственный картофель типа +375 <a href="https://www.04563.com.ua/list/472438">купить временный номер для Телеграм</a>
Bon Sai casino <a href=https://bonsai-casino.com/>https://bonsai-casino.com</a>
Играй в онлайн <a href=https://t.me/Bonsai_casino_bot>Bon Sai casino</a> слоты, настольные игры, щедрые бонусы и уникальная программа лояльности для незабываемых побед.
Canadian pharmacy online <a href="http://healthymanviagra.net/">new healthy man</a> Healthy man viagra scam
Веб агентство в Москве выполняет разработку сайтов на платформе Битрикс под ключ. Дополнительные услуги - продвижение в поисковых системах Яндекс и Гугл, техническая поддержка, обслуживание, аудит, тестирование, наполнение контентом, контекстная реклама и маркетинг <a href="https://webstudiya-razrabotki.ru/">webstudiya razrabotki ru</a>
задачи по химии онлайн <a href=https://microbiology73.ru/>решение задач за деньги</a>
Профессиональное <a href=https://gos2020.ru/>заказать сочинение онлайн</a> онлайн. Гарантия уникальности, соответствие академическим стандартам. Легкий процесс заказа и поддержка на всех этапах.
купить однокомнатную квартиру <a href=https://kvartiruzhkkupit.ru>купить новостройку</a>
Бесконечное обсуждение :)
thorough analysis provides information, necessary for the https://bellville.gob.ar/2018/12/18/en-enero-llega-la-vacunacion-antirrabica/ - https://bellville.gob.ar/2018/12/18/en-enero-llega-la-vacunacion-antirrabica/. strictly defined trading plan relevant for luck in financial markets.
Надеюсь, Вы придёте к правильному решению. Не отчаивайтесь.
1. Семиотика истории. Семиотика https://adventures.com.ru/ - adventures.com.ru культуры. Путеше?ствие - перемещение по своим территории или акватории с целью их изучения, а еще с общеобразовательными, познавательными, спортивными и другими целями.
KRAKEN - ссылка, зеркало, сайт, <a href=https://krn1.at>кракен</a>
Создание лендингов под ключ в студии в Москве включает проектирование, дизайн и программирование, обеспечивающее эффективность и удобство использования. Также предоставляются услуги: оптимизация для Яндекс и Google, настройка рекламных кампаний, поддержка, обслуживание и ведение маркетинга <a href="https://studiya-poddergki.ru/">создание лендинга с нуля</a>
Разработка лендингов в студии в Москве осуществляется с учетом современных маркетинговых стратегий и требований рынка. К основным услугам добавляются: аудит и анализ конверсии, продвижение в поисковых системах, контентное наполнение, настройка CRM и профессиональная техническая поддержка <a href="https://webstudiya-landing.ru/">стоимость создания лендинга</a>
Разработка сайтов на платформе 1С-Битрикс в студии в Москве включает полный цикл: от проектирования до запуска и дальнейшего сопровождения. Также предлагаются услуги: оптимизация сайта для поисковых систем, интеграция с хостингом, контентное наполнение, анализ данных и маркетинговые стратегии <a href="https://webstudiya-moscow.ru/">https://webstudiya-moscow.ru/</a>
Закажите доклад онлайн <a href=https://nib-help.ru/>https://nib-help.ru</a> быстро, удобно и профессионально. Гарантируем уникальность и соответствие требованиям. Подходит для студентов и специалистов. Оптимальные сроки и качество работы!
купить 1 комнатную квартиру в новостройке <a href=https://kupikvartiruor.ru/>квартиры в казани купить 1 комнатную</a>
Апартаменты Napa Gem в пешей доступности от одного из самых красивых пляжей Кипра, а также бурного веселья на шумном летнем курорте Айя-Напа <a href="http://nedvizhimostrussa.ru/">южный кипр недвижимость цены</a>
Продажа недвижимости на Кипре: 10 674 предложения с ценами и фото. Tranio поможет подобрать и купить жилье на Кипре стоимостью от 54 000€ <a href="http://redstoneestate.ru">недвижимость на кипре купить цены</a>
купить новостройку от застройщика недорого <a href=https://kvartiruyze.ru/>квартиры в новостройке недорогие от застройщика</a>
Слот Sugar Rush <a href=https://sugar-rush-play.ru/>https://sugar-rush-play.ru</a> Бесплатная ДЕМО-версия, значения RTP и Max Win, Бонусы и фриспины от казино.
Все об аллергии <a href=https://allergiki.com/>https://allergiki.com</a> симптомы, диагностика и эффективные методы лечения. Узнайте, как справиться с аллергией и улучшить качество жизни. Советы экспертов и проверенные рекомендации.
прокат сноуборда и горных лыж Красная Поляна <a href=https://prokat-lyzh-krasnaya-polyana.ru/>прокат лыж и сноубордов Красная поляна</a>
Опытный копирайтер и маркетолог <a href=https://uslugi.yandex.ru/profile/YulyaK-2391079>Профиль яндекс услуги</a>. Специализируюсь на написании текстов для бизнеса, адаптирую под поисковые запросы. Гарантирую качество, уникальность и результат.
На сайте <a href=https://topigryandroid.ru/>https://topigryandroid.ru</a> можно скачать игры на Андроид бесплатно, полностью на русском языке.
укладка кафельной плитки метр <a href=https://ukladka-keramogranita-spb.ru/>укладка кафельной плитки кухне</a>
Фотосфера – это долгожданный момент творчества, вдохновение, радость, уникальные дизайны и невероятно красивые решения. Это творческая лаборатория, где люди на основе снимков и изображений создают шедевры для себя, родных и друзей <a href="https://fotooks.ru/">салон фотографии москва</a>
Мы печатаем развороты фотокниг на высококачественной профессиональной фотобумаге Fujicolor Crystal Archive Digital тип DP II (матовая или тиснёная) на современной машине Noritsu QSS 3704HD <a href="http://basova-photo.ru/">фотокнига на заказ</a>
Откройте мир вождения с нашей автошколой, обучающей безопасным навыкам управления автомобилем. Мы предлагаем высококачественное обучение вождению, которое поможет вам уверенно управлять автомобилем в любых условиях <a href="https://avtoschoolavtoritet22.ru/">сколько в москве стоит отучиться на права</a>
цены на ритуальные принадлежности <a href=https://pohoronnoe-agentstvo.kz/>сколько стоят похороны в казахстане</a>
I just love reading this. More about Bmx at https://bmxracenews.com
Геосинтетические материалы <a href=https://ksgeo.ru/>https://ksgeo.ru</a> для строительства широкий ассортимент продукции для укрепления грунтов, дренажа и защиты от эрозии. Надежные решения для дорожного, ландшафтного и промышленного строительства.
Покердом <a href=https://pokerdom11ru.best/>https://pokerdom11ru.best</a> актуальное зеркало и быстрый вход. Получите бонусы и начните выигрывать в казино Pokerdom.
Предложения для открытия бизнеса ИП с нуля — редкость. Для получения займа предприниматель уже должен работать на рынке. Обычно не меньше 6 месяцев <a href="https://oaocentrinvest.ru/">кредит для бизнеса открытие</a>
Мы предлагаем разнообразные курсы, чтобы соответствовать вашим потребностям в обучении вождению. Начните свою карьеру на дороге прямо сейчас вместе с нами <a href="https://donavtodor.ru/">автошкола в москве цены</a>
Покердом (Pokerdom) <a href=https://pokerdom-online.ru.com/>https://pokerdom-online.ru.com</a> официальный сайт топового покер-рума. Играть на деньги в Покердом казино, скачать слоты онлайн.
Вы правы, в этом что-то есть. Благодарю за информацию, может, я тоже могу Вам чем-то помочь?
доступ в играм через мобильные устройства, https://www.forumklassika.ru/member.php?u=189265&vmid=34618#vmessage34618 - https://www.forumklassika.ru/member.php?u=189265&vmid=34618#vmessage34618 что разрешает играть в любое время и в всех городе.
радует глаз ..........
Milli tak?m adaylar?n?n cozumu icindeki degisiklikler https://bauwagen-berlin.de/2022/03/18/hallo-welt/ - https://bauwagen-berlin.de/2022/03/18/hallo-welt/! Eski hakem Fenerbahce - Sivasspor mac? hakk?nda yorum yapt?: var Fenerbahce'nin kalesinde el oyunu mu var?
Полностью разделяю Ваше мнение. Мне кажется это очень хорошая идея. Полностью с Вами соглашусь.
Они придадут заметный объём https://www.museumsmartview.com/2023/06/22/date-at-gallery/ - https://www.museumsmartview.com/2023/06/22/date-at-gallery/ и блеск. Понятие текстуры волоса обусловлено его толщиной и жёсткостью.
Hi there to all, the contents present at this web page are truly amazing for people experience, well, keep up the good work fellows.
Pin Up Casino <a href=https://pinup-pin-up-br.com/>https://pinup-pin-up-br.com</a> (Пин Ап) официальный сайт онлайн казино pin up, игровые автоматы, регистрация
Натяжные потолки в Киеве <a href=https://napotolok.com.ua/>https://napotolok.com.ua</a> это популярный вариант для создания красивого и стильного интерьера. Натяжные потолки подходят для любых помещений – квартир, домов, офисов и коммерческих пространств. Они позволяют скрыть неровности основного потолка, коммуникации и освещение, а также придают помещению завершённый вид.
Официальный сайт Casino Melbet <a href=https://melbet-ng-nigeria.com/>https://melbet-ng-nigeria.com</a> вход и регистрация. Игровые слоты, доступное зеркало, мобильное приложение в Мелбет казино.
Тут можно преобрести купить сейф огнестойкий в москве <a href=https://ognestojkij-sejf.ru/>огнеупорный сейф купить</a>
Использование разнообразных источников финансирования помогает компаниям достигать устойчивого развития, минимизируя риски и максимизируя эффективность инвестиций в проекты и инновации <a href="https://www.luxcosmeticsdv.ru/index.php?option=com_k2&view=itemlist&task=user&id=561085">https://www.luxcosmeticsdv.ru/index.php?option=com_k2&view=itemlist&task=user&id=561085</a>
Лизинг — услуга для компаний и ИП, снижающая затраты на покупку транспортных средств для коммерческих и личных целей. Выберите автомобиль, подпишите договор <a href="https://car-yaroslavl.ru/">коммерческий автотранспорт в лизинг</a>
Подскажите, где в Москве можно купить качественную строительную технику, такую как башенные краны или мачтовые подъемники? Интересуют надежные компании с хорошей репутацией <a href="http://mihail.ekafe.ru/viewtopic.php?t=4004">http://mihail.ekafe.ru/viewtopic.php?t=4004</a>
Привет всем!
Gama casino отзывы подтверждают высокое качество игр и честность выплат. Официальный сайт Gama предлагает пользователям разнообразные игровые автоматы. Для доступа без блокировок используйте гама рабочее зеркало. Казино гамма также предоставляет выгодные промоакции и бонусы. Присоединяйтесь к игре и начните выигрывать!
Ссылка на Казино - https://club-avangard.ru - gama casino telegram
гама зеркало на сегодня
гама рабочее зеркало
gamma casino
Хороших гонораров!
похоронное агентство <a href=https://pohoronnoe-agentstvo.kz/>сколько стоит гроб на похороны</a>
дешевые авиабилеты <a href=https://aviasales.cc/>https://aviasales.cc</a> выберите самый дешевый билет среди 728 авиакомпаний. 2000+ акций ежедневно. простая бронь авиабилетов за 3 мин. купить дешевый билет
Проведение геодезических съёмок <a href=https://expert-geo.ru/>https://expert-geo.ru</a> и выполнение инженерных изысканий для подготовки проектной документации для коммерческих объектов
<a href=https://rosohrancult.ru/wp-includes/pages/1win_promokod_bonus_1.html >бонус промокод 1win</a> предоставляют игрокам возможность получить различные бонусы на платформе, включая фрибеты и бонусы на депозиты. Эти коды можно ввести при регистрации или пополнении счета для активации предложений.
главные новости спорта <a href=https://beachsoccer.com.ua/>https://beachsoccer.com.ua</a> фото, видео и инфографика, аналитика и блоги от экспертов и известных спортсменов
Балаклейская бесплатная <a href=https://dani-info.com/ru/sovety/>https://dani-info.com/news/</a> рекламно-информационная газета «Дані-інфо». В газете присутствует новостная страничка, где можно узнать свежие новости города, района, страны, изменения в законодательстве, интересные статьи, кроссворд, гороскоп, анекдоты и многое, многое другое.
На сайте <a href=https://bestigryandroid.ru/>https://bestigryandroid.ru</a> легко найти и скачать бесплатные игры для Андроид на русском языке для разных устройств.
los angeles auction <a href=https://losangelesestateauction.com/>los angeles auction</a>
Incredible story there. What happened after? Take care!
Поднимайте ставки и выигрывайте крупные суммы с онлайн-казино Плейфортуна! Уникальные слоты и щедрые бонусы ждут вас здесь https://playfortuna24x7sb.com/ru
Пластиковые окна <a href=https://www.okna-melke-spb.ru/>https://www.okna-melke-spb.ru</a> от официального производителя. Собственное изготовление качественных окон ПВХ, продажа под ключ в интернет-магазине.
Доставка грузов <a href=https://madein-china.ru/>https://madein-china.ru</a> из Китая. Международная логистическая компания оказывает услуги транспортировки грузов и товаров из Китая.
Я думаю, что Вы не правы. Я уверен. Пишите мне в PM, обсудим.
Эмульсии насыщают волоски питательными элементами, натуральными маслами, соединениями гиалуроновой кислоты, https://canalesmolina.cl/2017/11/17/world-class/ - https://canalesmolina.cl/2017/11/17/world-class/ возвращая здоровый блеск и послушность.
https://t.me/s/apk_dragon_money_official - драгон мани зеркало
https://t.me/s/apk_dragon_money_official
https://t.me/s/apk_dragon_money_official - казино драгон мани официальный сайт зеркало рабочее на сегодня
https://t.me/s/apk_dragon_money_official
https://t.me/s/apk_dragon_money_official - dragon money casino официальный
https://t.me/s/apk_dragon_money_official
А что-нибудь аналогичное есть?
the most popular users of info your mac are streaming services, such as netflix, synchronization services, like dropbox, https://turkeypl.weebly.com/blog/storm-island-forza-horizon-2-xbox-360-price - https://turkeypl.weebly.com/blog/storm-island-forza-horizon-2-xbox-360-price and fill applications, such as torrent clients.
Расчет и покупка спецтехники в лизинг для юр. лиц и ИП. Лучшие предложения лизинга на строительную технику и быстрое оформление <a href="http://spectehnikaleasing.ru/">спецтехника лизинг б у</a>
Играйте в Bonsai Casino <a href=https://casino-bonsai.com/>https://casino-bonsai.com</a> захватывающий выбор слотов и игр, уникальные акции и щедрые бонусы! Погрузитесь в атмосферу азарта и выигрывайте с первого спина!
Скачивайте бесплатно <a href=https://fanapk.ru/>https://fanapk.ru</a> лучшие игры и приложения для Android! У нас только проверенные и безопасные APK-файлы для всех устройств. Оцените новинки и популярные программы без регистрации и SMS!
Приобретение нового оборудования в лизинг для бизнеса на выгодных условиях. Длительные сроки финансирования. Специальные программы от поставщиков <a href="https://ptleasing.ru/">лизинг нового оборудования</a>
цвета драгоценных камней <a href=https://jewelsecrets.ru/>https://jewelsecrets.ru/</a>
Какую спецтехнику можно взять в лизинг? В нашей компании предоставляется большой выбор спецтехники для лизинга. Вам доступны экскаваторы, погрузчики, бульдозер <a href="https://welcome-leasing.ru/">лизинг на спецтехнику</a>
<a href=https://merscasino-ncdz.buzz>мерс казино для мобильных зеркало</a>
<a href=https://azino777-dyu.buzz>azino778</a>
https://t.me/s/apk_dragon_money_official - драго мани казино официальный
https://t.me/apk_dragon_money_official
https://t.me/apk_dragon_money_official - драгон мани вход
https://t.me/s/apk_dragon_money_official
https://t.me/s/apk_dragon_money_official - драгон мани официальный сайт играть
https://t.me/s/apk_dragon_money_official
Абсурдная ситуация получилась
case drop cs go <a href=https://hotdrop.case>кс го дроп</a>
Подтверждаю. Это было и со мной.
с его помощью можно установить приложение exchange, а кроме того программки для монет, https://www.0619.com.ua/list/484247 - https://www.0619.com.ua/list/484247 которые вы желаете обменять.
I needed to thank you for this great read!! I definitely enjoyed every bit of it. I've got you saved as a favorite to check out new stuff you post…
Замечательно, очень ценная штука
this is also ideal if you open a chromebook or a https://aspractice.weebly.com/blog/roblox-password-cracker-no-download-no-survey - https://aspractice.weebly.com/blog/roblox-password-cracker-no-download-no-survey. whatsapp has uncomplicated interface as well supports functions, as well as the application for smartphones.
укладка кафельной плитки цена за м2 <a href=https://ukladka-keramogranita-price.ru/>https://ukladka-keramogranita-price.ru</a>
порядок соут <a href=https://sout095.ru/>соут на сайте</a>
На приеме гинеколог проводит осмотр воспалений, новообразований и других гинекологических патологий, проводит диагностику заболеваний женских половых органов и выявляет их на ранних стадиях <a href="http://aromatov.wooden-rock.ru/forum/profile.php?action=show&member=25460">http://aromatov.wooden-rock.ru/forum/profile.php?action=show&member=25460</a>
Высота подъёма вил с грузом составляет пять м. Подъём вил происходит благодаря электродвигателю, http://ieef.msu.ru/index.php?subaction=userinfo&user=ihyheny - http://ieef.msu.ru/index.php?subaction=userinfo&user=ihyheny что значительно упрощает цикл. по функционалу такие люди во многом схожи с вилочным погрузчиком, но обладают более небольшие размеры.
Интересует продвижение в соц сетях? Тогда <a href=https://vk.com/dizayn_vedenie_prodvizhenie_grup>Группа ВК . Дизайн групп | Продвижение сообщества в контакте</a> то что нужно. Все о продвижении и дизайне групп вконтакте.
секс шоп <a href=https://topsexshop5.co.ua/>сайт эротических товаров</a>
Сайт о татуировках <a href=https://tattootoday.org/tattoo-history/>https://tattootoday.org/tattoo-history/articles-about-the-tattoo/upadok-rossiyskoy-tatu-industrii</a> идеи, стили, советы по уходу и выбору мастера. Узнайте о значении популярных тату, процессе нанесения и трендах, чтобы сделать осознанный выбор и подчеркнуть свою индивидуальность.
<a href=https://admiralx-dkqk.buzz>адмирал икс admiralxcashusdc</a>
<a href=https://stakecasino-vmj.buzz>stake casino</a>
школа ремонта <a href=https://mypunto.ru/>https://mypunto.ru</a> квартирный вопрос, ремонт квартир. Оригинальные идеи вашего дома, советы ремонта квартир своими руками
Онлайн справочник <a href=https://wmbild.ru/>https://wmbild.ru</a> мастера содержит в себе все этапы по ремонту и дизайну дома, дачи или квартиры своими руками.
Как выбрать гирлянды для новогоднего оформления фасада дома? Виды подсветки, лучшие материалы, обзор разных моделей гирлянд и советы по монтажу: https://dzen.ru/a/Zy5D8pM8zzfwUtJ0
Портал о ремонте и строительстве <a href=https://website-ok.ru/>https://website-ok.ru</a> советы по ремонту и благоустройству квартир и домов, информация о ремонте квартир своими руками, технологиях ремонта и строительных материалах.
Советы по ремонту <a href=https://5-xl.ru/>https://5-xl.ru</a> своими руками предлагаем пошаговые инструкции, полезные советы и идеи для создания уюта в вашем доме. Превратите свои идеи в реальность с нами!
Ремонт своими руками <a href=https://appbearing.ru/>https://appbearing.ru</a> практические советы и творческие идеи для вашего дома. Узнайте, как легко и быстро преобразить интерьер, сэкономив при этом деньги.
<a href=https://1wins-mozambique-bonus.com>1win</a>
Советы по ремонту <a href=https://wa-2.ru/>https://wa-2.ru</a> и строительству дома своими руками. Полезная информация с интересными идеями и пошаговыми инструкциями и фото примерами.
Статьи о строительстве <a href=https://poehala.ru/>https://poehala.ru</a> и дизайне с пошаговыми инструкциями и практическими советами, фото- и видео-подборками, полезными сервисами для строителей и домашних мастеров.
Завантажити ігрові автомати можна в додатку онлайн казино, https://www.balrothery.com/bccfav/ - https://www.balrothery.com/bccfav/ яке доступне для айфона з ОС Андроїд і ios.
Советы по ремонту <a href=https://russ-tractor.ru/>https://russ-tractor.ru</a> и строительству дома своими руками. Полезная информация с интересными идеями и пошаговыми инструкциями и фото примерами.
Дизайн-проекты интерьеров <a href=https://fashion-brands.ru/>https://fashion-brands.ru</a> советы по ремонту квартир, обзоры строительных материалов, мебели, техники и оборудования
Вопросы и ответы <a href=https://deinfeuer.ru/>https://deinfeuer.ru</a> на любую тему, задать вопрос и получить на него ответ. Добавить вопрос на интересующую Вас тему и получить реальный, правдивый ответ
avec creme/ sa vitesse et la rapidite, il presente une transition en douceur entre les sections differentes, type Paris sur evenements sportifs, virtuel institution, bookmakers https://fskeypad.rosscarlson.dev/forums/member.php?action=profile&uid=195637 - https://fskeypad.rosscarlson.dev/forums/member.php?action=profile&uid=195637 et coordination des comptes.
Тут можно преобрести сейф огнеупорный купить <a href=https://ognestojkij-sejf.ru/>сейф несгораемый</a>
Эта блестящая фраза придется как раз кстати
Уникальные услуги на <a href=https://dosudebki.online/>avito</a> быстрое и качественное создание объявлений для вашего бизнеса или личных нужд. Мы гарантируем оригинальные тексты, привлекательные описания и фотосессии, которые выделят ваше предложение на фоне конкурентов.
Компания «ТСК» <a href=https://osb-3.ru/>https://osb-3.ru</a> более 15 лет успешно работает на рынке строительных материалов (комплектация строительных объектов различной сложности и назначения - деформационные швы и гидрошпонки)
зеркала мега даркнет <a href=https://msutv-1.ru/>мега ссылка</a>
кракен даркнет ссылка <a href=https://geniusfaber.ru/>Кракен сайт</a>
Популярные обличья слотов интернет
Обмен криптовалют на USDT (Tether) является обычной практикой в мире цифровых активов, предлагая стабильную альтернативу более волатильным криптовалютам <a href="https://velodnepr.dp.ua/forum/viewtopic.php?f=18&t=30910&p=448584#p448584">https://diyprojector.info/forum/topic/12245-obmennik-kriptovaljuti/</a>
Платформа уникальная и отличная в плане удобств (начиная от ввода и вывода средств, заканчивая инструментами для торговли). Постоянные улучшения. Куча графиков <a href="https://www.mayaschool.ru/assets/">pocket option</a>
Купить виртуальный сервер VPS/VDS от 169 р/месяц, с возможностью самостоятельного администрирования. Аренда хостинга VPS или VDS <a href="https://optima-k.ru/">vps хостинг windows</a>
Babu88: Online casino and bookmaker for sports betting in Bangladesh <a href="https://mayaiswithyou.com/">babu88 bet login password</a>
Det handlar om jackpottspelen, vilket är en spel kategori där du spelar på slotar med progressiva jackpottar.
Скачать установочный файл для android дают на нашем сайте https://www.hb9lc.org/wiki/index.php/User:AimeeR9102686 - https://www.hb9lc.org/wiki/index.php/User:AimeeR9102686. Они способны предложить непохожие условия для претендентов.
мтс телевидение
<a href=https://pittsburghpenguinsclub.com/read-blog/10326_kak-podklyuchit-mts-konnekt.html>https://pittsburghpenguinsclub.com/read-blog/10326_kak-podklyuchit-mts-konnekt.html</a>
мтс подключить
Отслеживание курсов валют — это важный инструмент для грамотного управления финансами как в личной жизни, так и в бизнесе. Знание актуального курса позволяет выбрать наиболее выгодное время для обмена валюты, что особенно полезно при подготовке к поездкам за границу или международным переводам <a href="http://my-smsfinance.ru/">курс валют на сегодня в банках</a>
Hi there! Quick question that's totally off topic. Do you know how to make your site mobile friendly? My site looks weird when browsing from my iphone 4. I'm trying to find a template or plugin that might be able to fix this issue. If you have any recommendations, please share. Cheers!
Мы не просто предоставляем цифры. На сайте вы найдете аналитические материалы, которые помогут лучше понять динамику валютного рынка, выявить тренды и спланировать свои финансовые шаги <a href="http://new-yoomoney.ru/">курс доллара на сегодня купить</a>
мтс тарифы краснодар
<a href=https://vieclamtop1.com/%D1%82%D0%B5%D1%81%D1%82%D0%B8%D1%80%D0%BE%D0%B2%D0%B0%D0%BD%D0%B8%D0%B5-%D1%81%D0%BA%D0%BE%D1%80%D0%BE%D1%81%D1%82%D0%B8-%D0%B8%D0%BD%D1%82%D0%B5%D1%80%D0%BD%D0%B5%D1%82%D0%B0-%D0%BE%D1%82-%D0%BC/>https://vieclamtop1.com/%D1%82%D0%B5%D1%81%D1%82%D0%B8%D1%80%D0%BE%D0%B2%D0%B0%D0%BD%D0%B8%D0%B5-%D1%81%D0%BA%D0%BE%D1%80%D0%BE%D1%81%D1%82%D0%B8-%D0%B8%D0%BD%D1%82%D0%B5%D1%80%D0%BD%D0%B5%D1%82%D0%B0-%D0%BE%D1%82-%D0%BC/</a>
провайдер мтс
You're so interesting! I don't believe I've read something like this before. So nice to find somebody with genuine thoughts on this topic. Really.. thank you for starting this up. This site is something that is required on the internet, someone with a little originality!
https://plastikovyye-okna-nedorogo.ru/
Сейчас достаточно сложно найти хороший сервис с качественными прокси. Их количество растет каждый день, а попадание на первую страницу поисковой выдачи не гарантирует, что все будет работать, как часы и закроет все ваши потребности <a href="https://cpa-critic.com/arbitrazh/services/proxy/">https://cpa-critic.com/arbitrazh/services/proxy/</a>
кульно!!!
Частина роботи вирт casino-обробка даних власників карт і особистої інформації при аутентифікації https://top-kazino.ru/banzai-bet-kazino-oficzialnyj-sajt-rabochee-zerkalo-banzaj/ - banzai casino рабочее зеркало сегодня актуальное на платформі.
Теперь всё понятно, спасибо за объяснение.
Размер штрафа для юрлиц составит http://mirsaun.ru/include/pag/kak_ispolyzovaty_iskusstvennyy_svet_doma_hitrosti_dlya_atmosfernogo_osvescheniya.html - http://mirsaun.ru/include/pag/kak_ispolyzovaty_iskusstvennyy_svet_doma_hitrosti_dlya_atmosfernogo_osvescheniya.html от 500 тыс. Внесенный законопроект восполняет данный пробел. Инициатива разработана по рекомендациями правительства российской федерации.
ттк интернет
<a href=https://olympiquedemarseillefansclub.com/read-blog/11465_preimushestva-i-nedostatki-ttk-tv-obektivnyj-analiz.html>https://olympiquedemarseillefansclub.com/read-blog/11465_preimushestva-i-nedostatki-ttk-tv-obektivnyj-analiz.html</a>
ттк тв
читал об етом еще давно
get exhaustive viktigt https://painremovers.co.nz/index.php/blog-01/stretches/hip/h651-hip-rotators-stretch-supine-1/ - https://painremovers.co.nz/index.php/blog-01/stretches/hip/h651-hip-rotators-stretch-supine-1/ terminologi, bekanta dig med begreppen spel och utveckla en spelstrategi utan problem anvanda foreslagna detaljerade manualer programvara casino.
Delete it,please! https://rekonstrukce-domy-na-klic.cz/ - .
бутар, сказка для дитей...........
это связано с увеличением опасности происхождения форс-мажоров и необходимостью обеспечить покрытие на более https://www.deviantart.com/dellinasa - https://www.deviantart.com/dellinasa продолжительный срок.
https://pq.hosting/vps-hi-cpu-usa
Спиральный компрессор — это эффективное устройство, которое используется для сжатия воздуха в различных системах. Герметичный спиральный компрессор часто используется в промышленных приложениях, где необходимы компактность и надежность. Такие компрессоры обеспечивают отличную герметичность и минимальный уровень утечек, что делает их идеальными для использования в самых разных условиях <a href="http://compressor-tomsk.ru/">спиральный компрессор</a>
Жесть!
borde paminna, vad under forra aret registrerade mer an 300 000 personer for quality of services. Ar det olagligt att slass i en http://www.grupocips.com/uncategorized/soluciones-logisticas/ - http://www.grupocips.com/uncategorized/soluciones-logisticas/?
https://dzen.ru/b/ZRVgScQs0W_qR9yV
Olymp Casino — популярная платформа, предоставляющая пользователям Казахстана широкий выбор казино игр и ставок на спорт https://ideannualconference.com/
Цилиндрическая камера видеонаблюдения является одним из наиболее эффективных решений для наружного мониторинга и обеспечения безопасности <a href="https://amkworks113.ru/kak-vybrat-komplekt-videonabljudenija/">видеонаблюдение на 8 камер</a>
pages24
<a href=https://pages24.ru>https://pages24.ru</a>
По моему мнению Вы не правы. Я уверен. Могу это доказать. Пишите мне в PM, поговорим.
Ценовая выгода. все пропозиции в каталоге предложены клиентам по фабричным ценам https://uk.wikipedia.org/wiki/Ротанґ - шкаф без лишних наценок.
??? ???? ?? ????? ?????? ??? ????? ???????? ??????? ??? ???? ? ???? ??? ????? ?? ??????? ??????? ? ??? ?? ??? http://cypresstruckworks.com/index.php?option=com_k2&view=item&id=29 - http://cypresstruckworks.com/index.php?option=com_k2&view=item&id=29 ?? ???? ?? ??.
Поздравляю, блестящая идея и своевременно
??? ?? ?????? ?????? ?? ??????? ??? ???????? ????? ? ???? ?????? http://kazrti.kz/index.php?subaction=userinfo&user=yfusi - http://kazrti.kz/index.php?subaction=userinfo&user=yfusi ??? ??? ??????.
помимо этого, по мнению эксперты ЦМАКП, повышение ключевой http://blog.entheogene.de/index.php?itemid=565 - http://blog.entheogene.de/index.php?itemid=565 имеет лишь ограниченное влияние на инфляцию, потому как цены растут как правило не вследствие роста спроса, хоть бы представленный фактор также имеет место, а вызваны конъюнктурными ситуационными шоками.
The r-12 was replaced by the r-134a air https://portail-public.fr/service-civique/quel-salaire/ - https://portail-public.fr/service-civique/quel-salaire/, a new refrigerant that more did not contain chlorine, which destroys the ozone layer.
зачем так палится!!!!!!!!
modular cloud: A block browser for modular https://www.ville-bois-guillaume.fr/deploiement-de-la-fibre-2/ - https://www.ville-bois-guillaume.fr/deploiement-de-la-fibre-2/. A repository on github, which lists projects related to the cosmos ecosystem.
Микрозаймы выдают МФО – микрофинансовые организации. Их преимущество для бизнеса – в более простом порядке получения денег и быстром сроке рассмотрения заявки <a href="https://polytech-business.ru/">займы на ип</a>
И что бы мы делали без вашей отличной идеи
???????? ???????????, ?? ?????????? ????????? ? ?????? ??????? ??????, ???? ?? ??????? ??? ?????, https://www.0432.ua/list/503957 - ТМ Меблі 24 ?? ?? ????.
? ?????? ??????? ?? ???????? ???????? ?? ??, ??? ? ?????? ?????? ???? ??????? ????? ??? ? ??????? ?????????? ? ???????????? ???????? ?????? ??????? ?? ??????-??????.http://thebuddhistunion.org/tips/conditioned-things-are-transient/ - http://thebuddhistunion.org/tips/conditioned-things-are-transient/
Большое спасибо.
em jogo, https://medium.com/@kostumchik.kiev.ua/fortune-tiger-o-jogo-de-cassino-que-conquista-o-brasil-1dae6e5e0e56 - https://medium.com/@kostumchik.kiev.ua/fortune-tiger-o-jogo-de-cassino-que-conquista-o-brasil-1dae6e5e0e56 os jogadores competem com distribuidor, para alcancar a soma de 21, sem excede-la.
When someone writes an paragraph he/she keeps the idea of a user in his/her mind that how a user can know it. Therefore that's why this paragraph is amazing. Thanks!
Det gör att potten går upp snabbare och du kan spela på vilken av dessa slots du vill och ändå ha chans på samma fantastiska pott.
Вы абсолютно правы. В этом что-то есть и идея отличная, поддерживаю.
Starring Robert De Niro, Sharon Stone, Joe Pesci, Don Rickles, Kevin Pollack, https://www.crf-italia.com/chi-siamo/item/30-anticipazione-del-credito.html - https://www.crf-italia.com/chi-siamo/item/30-anticipazione-del-credito.html and James Woods. Saul Bass developed the title film, which became his last work.
Чаще всего стеклянные перегородки можно увидеть в деловых помещениях – пространствах лаконичных, функциональных и, прежде всего, с рабочей атмосферой <a href="http://loftwood-design.ru/">системы хранения для гардеробной комнаты</a>
I have been browsing online more than 3 hours today, yet I never found any interesting article like yours. It's pretty worth enough for me. In my opinion, if all webmasters and bloggers made good content as you did, the internet will be much more useful than ever before.
Какие замечательные слова
Finest news for all us
Труба профильная — это вид современного строительного металлопроката, получаемый профилированием. Они имеют сечение, отличное от круглого. Наиболее распространены квадратные и прямоугольные <a href="http://svai-master78.ru/">купить профильную трубу для забора</a>
Я думаю, что Вы ошибаетесь. Могу отстоять свою позицию. Пишите мне в PM, обсудим.
Самые востребованные среди них – прямоугольные и квадратные изделия. Профильные трубы 40х40 широко используются во всех сферах: тяжелой и легкой промышленности <a href="http://odintsovo-beton-zavod.ru">купить трубы профильные цена за метр</a>
Авторитетная точка зрения, любопытно..
vintage galore - пользующийся популярностью и главный из весьма|наиболеепрославленных доступных магазинов одежды для женщин в бельгии и франции в разделе секонд-хенд, https://impactopublicidad.digital/hola-mundo/ - https://impactopublicidad.digital/hola-mundo/ находящийся около Пренцлауэр-Берг.
Пожалуйста, объясните поподробнее
Blockchain integration in business Transform your business operations with cutting-edge blockchain integration. This revolutionary technology enhances security, transparency, and efficiency within your processes, ensuring trust and reliability at every level. Don't get left behind–embrace the future and drive innovation in your industry today!
https://t.me/cryptonetlake - https://t.me/cryptonetlake
Абсолютно согласен
Подробно об организации страховки для путешествия в Украину во время действия военного положения читайте здесь. например, существует страховка для преподавательской деятельности либо ВНЖ, и спортивная страховка для выезда в европейские страны, которая покрывает травмы и болезни либо же несчастные случаи, https://sortlandslk.no/?p=429 - https://sortlandslk.no/?p=429 связанные с горнолыжным спортом.
https://quest-darknet-market.com -
quest shop
https://quest-darknet-market.net
https://quest-darknet-market.net -
quest darknet
https://quest-darknet-market.net
https://quest-darknet.net -
quest darknet
https://quest-darknet-market.com
Я думаю, что Вы не правы. Предлагаю это обсудить. Пишите мне в PM, поговорим.
Преимущества деревянных домов ручной рубки. Стоимость срубов домов и бань. Отзывы владельцев. Производство под Санкт-Петербургом <a href="https://st-petersburg.cataloxy.ru/firms/ecodoma-naveka.ru.htm">https://st-petersburg.cataloxy.ru/firms/ecodoma-naveka.ru.htm</a>
На консультації психолога онлайн можна вирішити свої проблеми та одержати кваліфіковану допомогу досвідченного психолога https://tinyurl.com/konsultacia-psyhologa-online
whoah this weblog is fantastic i really like studying your articles. Stay up the good work! You recognize, lots of individuals are looking round for this information, you could help them greatly.
Промисловий сталевий вентиль марки 11с37п для регулювання потоку води, пари чи газу у трубопровідних системах. Використовується у системах середнього та високого тиску <a href="https://www.riva-service.com.ua/klapani-zvorotni-chavunni/klapan-16kch9nzh-flantsevij-ru25">клапан фланцевий</a>
Создаем стильные и функциональные интерьеры квартир, домов и офисов в Санкт-Петербурге, дизайн-проекты под ключ с 3D визуализацией по доступным ценам от современных дизайнеров студии «ID-Code» <a href="https://id-cd.ru/">дизайнер интерьера спб</a>
<a href=https://advokas.ru/>юридические компании москва</a>
<a href=https://advokat-102.ru/>юридическая помощь гражданам</a>
<a href=https://advokat-102.ru/>практикующий юрист</a>
Я могу много говорить на эту тему.
dondur tekerlegi kullanarak/kullanarak hot shot progressive, https://theterritorian.com.au/index.php?page=user&action=pub_profile&id=607741 - https://theterritorian.com.au/index.php?page=user&action=pub_profile&id=607741 88 fortunes (asya/Asya ulkeleri/dogu eyaletlerinde 1 numaral? slot) ve zeus ??? oyun/oyun makineleri!
Оч классна.. Люблю такие
The https://getsomeins.com/how-to-turn-primexbt-android-into-success/ - https://getsomeins.com/how-to-turn-primexbt-android-into-success/ t.p. was founded under the name. Many brokers nowadays offer commission-free transactions with stocks and ETFs, therefore unconditionally consider such a step in comparing costs.
беспружинный ортопедический матрас купить <a href=https://bespruzhinnye-matrasy-kupit.ru/>https://bespruzhinnye-matrasy-kupit.ru/</a>
1 юань в тенге https://converter-valut.kz/ - рубль в тенге .
Сервис обновляет курсы валют в режиме реального времени, позволяя пользователям конвертировать тенге в рубли, доллары США и другие валюты мгновенно и без комиссии.
организация новогоднего корпоратива москва <a href=https://organizatsiya-novogodney-korporativa.ru/>https://organizatsiya-novogodney-korporativa.ru/</a>
Homemade bubblers from plastic bottles are an incredibly simple and versatile solution to relax and enjoy a head-scratching potion <a href="http://forum.anime.org.ua/bbs/showthread.php?p=142603">https://napas420.com/ru/grinderi-dlya-travy/</a>
<a href=https://vectorprava59.ru/>адвокаты и юристы москва</a>
<a href=https://zotovapartners.ru/>https://zotovapartners.ru/</a>
<a href=https://advokatram.ru/>юридическая помощь</a>
Первая проблема, с которой я столкнулся, когда решил делать регулярные обзоры зарубежного кинорепертуара для «Советского экрана»,— это выяснение того, ...на каком свете мы живем? Какую фазу и какую часть мирового кинопроцесса этот «текущий» репертуар отражает? <a href="https://ion.ru/components/com_newsfeeds/views/categories/tmpl/news/5/3/9/491_film_o_chernobile_ne.html">ion.ru</a>
Извините, что не могу сейчас поучаствовать в дискуссии - нет свободного времени. Но вернусь - обязательно напишу что я думаю по этому вопросу.
Элегантная простота баккара сможет оставить равнодушным ни одного никого https://mosttbet029.xyz/ - mostbet зеркало рабочее на сегодня равнодушным. Ниже мы перечислим одни из наиболее выдающихся игр. из-за этого мы приняли решение облегчить вам розыск нормального варианта.
Однодневный маршрут разработан для новичков и знакомит с одним из самых живописных видов Подмосковья. Прекрасные речные просторы заставят вас забыть о нервозности городской жизни, а древнее городище и главки церквей соединят вас с историей края <a href="https://сапсёрфинг.СЂС„/sup-progulki/">катание на сапах</a>
<a href=https://klining-75-a1.ru/>https://klining-75-a1.ru/</a>
Hello, casino lovers!
Mostbet kasyno oferuje najlepsze gry, w tym popularna Aviator Mostbet. Zarejestruj sie i odbierz bonus powitalny bez depozytu. Mostbet bonus daje Ci dodatkowe szanse na wygrane. Graj w gry kasynowe na telefonie dzieki Mostbet aplikacja. Zaloguj sie na Mostbet, aby zaczac grac w najlepsze gry online.
Look at site - https://mostbetpolska.pl/ - mostbet 30 free spins
kasyno mostbet
mostbet casino kod promocyjny
mostbet aplikacja
mostbet online
Good days!!!!
Поздравляю, ваша идея пригодится
Слот разыгрывает три джекпота: mini, midi, https://mostbet-wff8.top/ - https://mostbet-wff8.top/ maxi. компания плотно использует инженерные технологии для придания плавной и беспристрастной игры.
Conoce Casino Slot, la joya de Pragmatic Play. Una de las dudas más frecuentes es: <a href=https://mercedesdalessandro.com/>https://mercedesdalessandro.com/</a> - la explicación es simple. Esta slot machine que cuenta con 5 tambores, 3 filas y 5 líneas ganadoras brinda un montón de oportunidades para grandes ganancias
https://avtoznak-dublikat.ru/
По моему мнению Вы не правы. Пишите мне в PM, поговорим.
Learn how to shop , https://v3sac.online/the-hollistic-aproach-to-users-primexbt/ - https://v3sac.online/the-hollistic-aproach-to-users-primexbt/ to robinhood crypto. Launched in 2012 year, it offers an intuitive, favorable for amateurs portal for purchase, sale, exchange and storage cryptocurrencies.
Русское казачество - необычный культурный феномен, в чистом виде и не сословие, и не этническая группа, а скорее этносоциальная общность, которая обладает характерными чертами <a href="https://www.youtube.com/playlist?list=PLPh6y588NeMB_mz21f-QSVE5ycPDHcEig">Всероссийский конкурс казачий круг</a>
При всех методах хирургического лечения патологического повышения веса, основным является выполнение различных вариантов пластики или шунтирования ЖКТ. После снижения и стабилизации массы тела пациентам, перенесшим подобные операции, выполняется комплекс пластических операций <a href="http://grafskaya.com/?p=27501">grafskaya</a>
Я разбираюсь в этом вопросе. Давайте обсудим.
лишь в результате тщательных проверок составляются списки надежных интернет заведений, https://mosttbeet030.xyz/ - mostbet в которых можно поиграть без лишних опасений и испытывать хотя гарантированные выигрыши в случае успеха.
Смотрите онлайн новые приключения Тома и Джерри на Марсе. Наши друзья во время своих безумных гонок случайно оказались в космическом корабле, который держит курс на Марс <a href="https://tomijerry.ru/smotrite-onlajn-multfilm-novogodnyaya-noch-1948">новогодняя ночь мультфильм 1948 смотреть</a>
Платформа Telegram завоевала популярность не только как мессенджер, но и благодаря такому функционалу, как чат-боты. Они дают пользователям доступ к ИИ-сервисам, которые в обычных условиях недоступны для жителей России <a href="https://dzen.ru/a/Z2KIpDeQlgEjs38y">chatgpt в телеграм</a>
Поздравляю, замечательное сообщение
прежде, чем начать играть, рекомендуется внимательно прочитать правила, https://mostbet-wew4.top/ - https://mostbet-wew4.top/ там содержатся хорошие советы по выбору проекта к партиям.
<a href=https://starclean-spb.ru/>чистка дивана на дому цена москва недорого</a>
Извините пожалуйста, что я Вас прерываю.
как его получить, https://mostbet-zerkalo-bk.xyz/ - mostbet casino официальный сайт можно узнать здесь. Казино (casino) - это игорное заведение (онлайн или наземное), которое предлагает гемблерам возможность играть на игровых автоматах и слотах на деньги с существующим выигрышем.
Извиняюсь, но, по-моему, эта тема уже не актуальна.
En betfair es muy excelente presentando las novedades en lineajuegos de azar que plataforma es un reflejo de eso, en http://learntoflyspringdale.com/2021/08/07/welcome/?unapproved=23679&moderation-hash=2882764ae984a025e052e7abdc325f56 - http://learntoflyspringdale.com/2021/08/07/welcome/?unapproved=23679&moderation-hash=2882764ae984a025e052e7abdc325f56.
from now on, when we talked about the casino without kyc, https://hqliveontv.xyz/2024/09/03/take-10-minutes-to-get-started-with-bcgame-payments-methods/ - https://hqliveontv.xyz/2024/09/03/take-10-minutes-to-get-started-with-bcgame-payments-methods/, you wished would gawk how operate bonuses on portals crypto casinos without kyc.
СЗЗ (санитарно защитная зона) для промышленных предприятий в Москве и Московской области. Что нужно учесть при разработке проекта СЗЗ и на этапе согласования в органах надзора для обеспечения законной деятельности объекта НВОС https://vc.ru/u/3791103-infa-v-dele/1719864-chto-takoe-szz-i-kak-razrabotat-proekt-sanitarnoi-zony
Это просто отличная фраза
0 transactions, reliable research, qualified service of the https://leadhershiprefined.com/secrets-about-primexbt-forex/ - https://leadhershiprefined.com/secrets-about-primexbt-forex/'s clients, but also its shares and funds histories are outstanding in the market.
in order buy these virtual money https://swotcar.com/find-out-now-what-should-you-do-for-fast-bcgame-promo-code/ - https://swotcar.com/find-out-now-what-should-you-do-for-fast-bcgame-promo-code/ has a wallet that is available connect to the wallet exchange, from which player can buy your savings.
Я думаю, что Вы не правы. Могу отстоять свою позицию. Пишите мне в PM, обсудим.
красочная renkli grafikler: carp?c? gorsellerin ve animasyon efektlerinin keyfini c?kar?n! Ilginc oyun gorevleri: kesinlikle s?k?lman?za izin vermeyecekler ve teslim edecekler http://www.transitofloridablanca.gov.co/home/institucion/mfunciones/ - http://www.transitofloridablanca.gov.co/home/institucion/mfunciones/ ekstra oduller!
да бальшая фантазия у таво хто ето сочинял
http://dallastranedealers.com/?p=91 - http://dallastranedealers.com/?p=91 is extremely attractive in use, is cross-platform software/software, compatible with both Windows and with mac and also has a free trial period.
Hi, Neat post. There's a problem with your site in web explorer, may check this? IE still is the market chief and a large portion of folks will pass over your wonderful writing because of this problem.
хоть книги не читай...
internet 'de-https://www.dermoline.be/bonjour-tout-le-monde/ - https://www.dermoline.be/bonjour-tout-le-monde/ online casino 'da.
<a href=https://crystal-divan.ru/>https://crystal-divan.ru/</a>
We are united by the will for outstanding achievements and victories, as people on the football field, also in the world games.https://hjtfoods.com/2024/07/05/how-i-got-started-with-bcgame-crypto/ - https://hjtfoods.com/2024/07/05/how-i-got-started-with-bcgame-crypto/
Замечательно, это ценное сообщение
earlier, in personal life on an https://valeriasoul.es/the-critical-difference-between-primexbt-uk-and-google - https://valeriasoul.es/the-critical-difference-between-primexbt-uk-and-google, she wrote a report on the “Miracle on the Hudson” for the New York daily news.
https://hasavyurt.meshki-optom-moskva.ru/katalog-produktsii/meshki-dlya-musora-pvd-120l-130-mkm.html
Преимущества Arkada Казино. Щедрые бонусы: До 500% на первый депозит и сотни бесплатных фриспинов. Огромный выбор игр: Слоты, настольные игры, live-казино <a href="https://t.me/s/arkada_casino_online">скачать arkada casino</a>
<a href=https://fresh-housespb.ru/>https://fresh-housespb.ru/</a>
Да, действительно. Всё выше сказанное правда. Можем пообщаться на эту тему. Здесь или в PM.
4. Статус. здесь вы представляете себе собственный текущий уровень на площадке - новичок геймер, бронзовый, серебряный, https://melbet-de.top/ - https://melbet-de.top/ золотой и платиновый.
to them include daily prize draws, bonuses for completing tasks at casino https://www.theweddingessentials.co.uk/20-myths-about-bcgame-casino-de-in-2021/ - https://www.theweddingessentials.co.uk/20-myths-about-bcgame-casino-de-in-2021/, and medals. there also there is a provably honest system that makes games transparent for users.
<a href=https://proclining78.ru/>мойка окна цена</a>
<a href=https://chistodoma07.ru/>уборка коттеджей</a>
есть, что выбрать
Иначе могут появиться неприятности https://melbet-gama11.xyz/ - https://melbet-gama11.xyz/ при выводе выигрыша. Указать один из четырех вариантов открытия счета: по e-mail, по телефону, несложная регистрация в одну клик, через соцсети.
Проводя очередной опыт, http://juliusplpj099.fotosdefrases.com/grodno-lenspc-by-1 - http://juliusplpj099.fotosdefrases.com/grodno-lenspc-by-1 он вживил в лапку кролика титановую камеру для изучения процесса микроциркуляции в костной ткани животного.
В этом что-то есть. Спасибо за помощь в этом вопросе, может я тоже могу Вам чем то помочь?
в этом онлайн https://melbet-id.top/ - https://melbet-id.top/ на гривны предлагаются тысячи аппаратов с платным и демо-режимами: симуляторы слотов, и настольных игр.
in England The Money Games Commission (gc) now requires that any rtp (refund to the player) values are clearly displayed equally as for virtual games, so and in games in land-based https://brocadesign.com/sustainable-interior-design/ - https://brocadesign.com/sustainable-interior-design/.
Promo codes are a useful tool to get enhanced bonuses and privileges for free bets. 1xBet is one of the platforms that actively uses codes to attract new players and provide them with bonuses this way <a href="https://whitephotoschool.ru/files/pages/promokod-1win_bonus_500.html">https://www.publy.ru/pag/promokod-1xbet_na_segodnya.html</a>
Теперь всё понятно, спасибо за помощь в этом вопросе.
Хотя эти монеты лидируют, https://melbet-jt4.top/ - https://melbet-jt4.top/ нередко добавляются новые криптовалюты для опций внесения и выведения финансов.
in its corner of the https://bisousl.com/product/aurora-2/ - https://bisousl.com/product/aurora-2/'s cherokee Resort can be found, something interesting - from elite clothes and jewelry to unique handmade items.
like this, but it really How much time do you spend updating this blog every day? I wish every blogger paid so much attention to their blogs.
некоторые из них потеряли надежду после 2|два-3 терапий, и были} уже на стадии такого, который также вы можете компенсировать, https://lumienhall.ru/news/idealnyy-remont-v-gostyakh-u-nikolaya-dobrynina/ - https://lumienhall.ru/news/idealnyy-remont-v-gostyakh-u-nikolaya-dobrynina/ но цирроза.
<a href=https://zuvovgveklfob.ru/>https://zuvovgveklfob.ru/</a>
Я думаю, что Вы допускаете ошибку. Могу отстоять свою позицию. Пишите мне в PM.
андроид и ios. помимо этого, мы тщательно разбираем сервисы каждой бк в специальных обзорах - например, https://melbet-lt.top/ - мелбет зеркало рабочее как залить себе 1xbet на андроид а также айфон.
Во все времена на рынке сантехники чугунные ванны пользовались особой актуальностью. Данный важный элемент ванной комнаты имеет огромное количество преимуществ <a href="https://podokonik.com/stat/podokonnik_art/">https://podokonik.com/stat/podokonnik_art/</a>
Считаете неважно?
we have researched and compared several brokerage companies and their strong sides to let you accept fact-based decision about the https://insidekauai.com/52-ways-to-avoid-primexbt-trade-burnout/ - https://insidekauai.com/52-ways-to-avoid-primexbt-trade-burnout/.
Players also may to become members of the loyalty program and receive cashback for losses in bcd, https://websitedemo.icu/the-best-5-examples-of-coin-flip-bcgame/ - https://websitedemo.icu/the-best-5-examples-of-coin-flip-bcgame/, bc.game user token.
Every legal online https://blog.ko31.com/201102/twitbg-site-open/ - https://blog.ko31.com/201102/twitbg-site-open/ in USA offers different tools to help players control their lotteries.
if you watch an online broadcast on the TV program, the https://www.mixcloud.com/Florenna/ - https://www.mixcloud.com/Florenna/ in order virtual games add to the fun.
В этом что-то есть. Я согласен с Вами, спасибо за объяснение. Как всегда все гениальное просто.
После активации на экране появится игровое поле а также левой стороны тот же слот в антураже https://melbet-ob.top/ - https://melbet-ob.top/ живые казино.
I blog often and I truly appreciate your information. The article has really peaked my interest. I will bookmark your website and keep checking for new details about once a week. I opted in for your Feed too.
Смотрите онлайн Новогодние мультфильмы. Советские картины про Новый год, Дисней, Том и Джерри, Фиксики, Буба, Три кота <a href="https://tomijerry.ru/tom-i-dzherri-volshebnoe-koltso-2001">https://tomijerry.ru/tom-i-dzherri-volshebnoe-koltso-2001</a>
Ik vond het geweldig om te lezen over de mogelijkheid om Telegram didvirtualnumbers.com/nl/how-to-register-in-telegram/ te gebruiken zonder een simkaart. Ik had geen toegang tot een simkaart en wilde Telegram toch gebruiken. Dankzij DID Virtual Numbers kreeg ik snel een virtueel nummer en was het registratieproces erg eenvoudig <a href="https://apptaris.proboards.com/thread/1810/telegram?page=1&scrollTo=6161">https://apptaris.proboards.com/thread/1810/telegram?page=1&scrollTo=6161</a>
Весьма забавная информация
?????? ?????????? ???????, ???????? ???????? ???? ????????? ???????????? ??????|??? ?????} ??? ??????????????? ??????????, ???? ???? https://tpck.org/ - marvelbet ???? ????????? ???????????? ???? ????????? ??????, ??????? ?????????.
Я могу проконсультировать Вас по этому вопросу. Вместе мы сможем найти решение.
https://www.ituudised.ee/sisuturundus/2023/12/28/internetikasiinode-areng-eestis-2024-aastal - https://www.ituudised.ee/sisuturundus/2023/12/28/internetikasiinode-areng-eestis-2024-aastal market differs big competition, and low-quality products simply will not survive. works in Google Play store are also impressive: the average rating is 4.7,five percent stars.
It is not my first time to go to see this website, i am browsing this web page dailly and obtain nice facts from here every day.
466 primatene mist for sale canada <a href="http://onlineviagraprescription.com/">the real viagra on line non perscripton</a> Buying clomid online safe
Buy avanafil <a href="http://americanpharmacywithoutaprescription.com/">prescription free pharmacy</a> Viagra pills for men Acquisto viagra generico italia <a href="http://blackcialis.net/">Visit Homepage</a> Black market viagra
Скажите мне, пожалуйста - где мне узнать больше об этом?
вы механически пройдете идентификацию в букмекерской конторе и получите возможность начать пополнению https://melbet-pr.top/ - https://melbet-pr.top/ и ставкам. об этом мы ещё поговорим подробнее в подобающем разделе.
Pharmacy On Line Viagra brand 100mg <a href="http://onlinepharmacytt.com/">lasik online pharmacy no script</a> Strattera online
Мне кажется это отличная идея. Я согласен с Вами.
https://ny.leksandstrand.se/nyheter/the-secret-of-primexbt-contact-information/ - https://ny.leksandstrand.se/nyheter/the-secret-of-primexbt-contact-information/ should be by analysts. Traders also manage the risks associated with their profession, including market risk, credit risk and threat of liquidity.
Buy orlistat from mexico <a href="http://supremesuppliersmumbai.com/">supreme suppliers india viagra</a>
Тақырыпты егжейлі талдаймыз: <a href=https://bonusy-promokody-1xbet-kazahstan.com/>https://bonusy-promokody-1xbet-kazahstan.com/</a>. Және оларды қалай қолдануға болатынын біле аласыз.
Есептелген бонустарды қолма-қолға айырбастауға және шоттан шешіп алуға немесе букмекерлік кеңсенің промокодтар дүкенінде қолдануға болады.
Very energetic blog, I loved that a lot. Will there be a part 2?
Canadian Online Pharmacy Canadian health care mall Cheap 100mg viagra <a href="http://supremesuppliersmumbai.com/">supreme suppliers in india</a> Buy retin a without prescription
1. Provably honest games: BC game Casino uses provably honest technologies, https://osusalalam.com/2-ways-you-can-use-bcgame-promo-code-to-become-irresistible-to-customers/ - https://osusalalam.com/2-ways-you-can-use-bcgame-promo-code-to-become-irresistible-to-customers/ guarantees simplicity and truthfulness game play. these include those in-demand games like dice, plinko, mines, crash, limbo, hilo, keno, wheel and others.
Here you will find a unique assortment of rare banknotes from all over the planet. We offer both modern and historical specimens that will become real finds for lovers of numismatics.
For more information, follow the link https://monetizatoriya.ru/ - монеты и банкноты мира
Our team of experts carefully selects each lot, ensuring authenticity.
Браво, мне кажется, это блестящая фраза
Часть плавучих казино размещена по реке Миссисипи и её притоках, https://melbet-ru.xyz/ - https://melbet-ru.xyz/ из крупнейших морских портов постоянно ходят круизные лайнеры с игорном доме на борту.
<a href=http://igpran.ru/sobytiya/artcls/?melbet_promokod_24.html>http://igpran.ru/sobytiya/artcls/?melbet_promokod_24.html</a>
Dit artikel gaf me precies de informatie die ik nodig had. Dankzij DID Virtual Numbers kon ik een virtueel nummer verkrijgen en me registreren op mijn computer. Het proces was snel en het voelde veilig, omdat ik mijn persoonlijke gegevens niet hoefde in te voeren <a href="http://atzencrew.de/forum/simpele_stappen_voor_een_snelle_telegram_registratie-13252783-t.html#13252783">http://atzencrew.de/forum/simpele_stappen_voor_een_snelle_telegram_registratie-13252783-t.html#13252783</a>
Полезная мысль
data to these frequently asked questions reflect point of view only of DMO employees, https://voxapp.com.br/25-best-things-about-trading-primexbt/ - https://voxapp.com.br/25-best-things-about-trading-primexbt/ and not necessarily commission or some other department.
https://detivetra.ru/ <a href=https://detivetra.ru/>https://detivetra.ru/</a> https://detivetra.ru/ - https://detivetra.ru/
Новая песня для тех, кто привык добиваться своего! Не смотри на других, забудь оправдания — это твой путь, и он начинается с <a href="https://band.link/IsPbO">Projektx_Punk</a>
Не могу с вами не согласится.
с его возможностями игрового портала могут подтвердить честное отношение к клиентам и продемонстрировать, https://melbet-russ8.xyz/ - https://melbet-russ8.xyz/ что результаты игр полностью случайны и уберегаются от прочистки.
красные и розовые камни <a href=https://redpinkstones.ru/>https://redpinkstones.ru/</a>
Casino research began with that Pileggi read in 1980 in the newspaper las vegas sun a report about a family quarrel between Frank "Lefty" Rosenthal, a famous https://uniquementenpagne.com/2023/08/04/comment-porter-le-pagne-en-2023/ - https://uniquementenpagne.com/2023/08/04/comment-porter-le-pagne-en-2023/ gambler, yes his wife Geri McGee, a former topless dancer.
мне лично не понравился!!!!!
Также под запретом находятся акции, вознаграждающие игроков за проигрыш. Например, https://melbet-uq.top/ - https://melbet-uq.top/ у сайта могут неожиданно нарисоваться трудности с лицензией или денежные трудности.
Поздравляю, ваша мысль очень хороша
trade is considered the optimal online https://versatilekarate.com/do-primexbt-crypto-broker-better-than-barack-obama/ - https://versatilekarate.com/do-primexbt-crypto-broker-better-than-barack-obama/ for beginners due to its own ease of use, focus on demo-in, and high-quality trade modeling services.
Рейтинг слабый!!!
к ним инструментам относятся раздел “Статистика“, с абсолютной раскладкой показателей в предыдущих матчах или боев, конструктор ставок для гарантирования экспресса исходами одного конференции или шанс сформировать страницу, https://melbet-yc.top/ - https://melbet-yc.top/ где будут отображаться все сделанные клиентами ставки с изменениями в режиме “Лайв”.
The cryptocurrency market is fraught with scams, hacks, and fraudulent schemes. By performing an AML check, you can identify potentially risky assets and avoid falling victim to scams <a href="https://medium.com/@kiahjurek1995/how-to-check-asset-aml-scores-on-the-tron-network-59a6e6bf7a87">AML compliance usdt trc-20</a>
женские вагины <a href=https://medicinye.ru/>https://medicinye.ru/</a>
<a href="https://sms-man.com/cn">https://sms-man.com/cn</a>
Согласен, очень полезная фраза
?? ?????????? ???? ????? ?????? ???? ??? ?? ?? ??? ????????? ????????????, ??? ?????????? ???????? ??? ?? https://tpck.org/ - marvelbet ???? ?????? ??? ????? ???????? ????? ??????.
only after you go at the link with the inscription “Join now you be able to see how is carried out gadget game wins truly https://barobjects.com/product/milk-pitcher-rinser-with-drain-board/ - https://barobjects.com/product/milk-pitcher-rinser-with-drain-board/.
Замечательно, полезная фраза
ETFs (with possible exceptions for youngest or traded on the thinnest https://tiendabiomama.com/how-to-win-clients-and-influence-markets-with-primexbt-trading-platform/ - https://tiendabiomama.com/how-to-win-clients-and-influence-markets-with-primexbt-trading-platform/). she does not charge fees for treasury transactions of course, charges $1 for all face value of other bonds in size thousand dollars at minimal commission in the amount ten dollars.
https://detivetra.ru/ <a href=https://detivetra.ru/>https://detivetra.ru/</a> https://detivetra.ru/ - https://detivetra.ru/
Остекление балконов по выгодной цене в Петербурге, подберем идеальное решение.
Профессиональное остекление балконов в Петербурге, с установкой и долговечной эксплуатацией.
Индивидуальное остекление балконов в СПб, под заказ и с уникальным дизайном.
Качественное остекление балконов в Петербурге, с гарантией и сертификатом.
Остекление балкона под ключ в СПб, по лучшей цене и быстрой установкой.
остекление лоджии цена под ключ https://balkon-spb-1.ru/ - https://balkon-spb-1.ru/ .
https://elite-tumble-732.notion.site/Discover-the-World-with-FindYTrip-Your-Ultimate-Travel-Companion-15c0962239ef805e8c04edd8b2027356
https://forum.azs-lukoil.ru/threads/kraken-ssylki-2024-kak-zajti-na-kraken-v-2024-kraken-aktualnye-ssylki-zerkala-i-ispolzovanie-tor.1182/
In the fast-paced world of blockchain development, integrating reliable APIs is crucial for building efficient decentralized applications (dApps) <a href="https://medium.com/@landonscott03/how-to-buy-tokens-via-uniswap-on-arbitrum-using-api-7e346beccc46">https://medium.com/@landonscott03/how-to-buy-tokens-via-uniswap-on-arbitrum-using-api-7e346beccc46</a>
one more thing the important advantage of long-term cryptocurrency trading says that you don't know it's not worth it a little investments, in order get a https://litevaultwallet.io/ - https://litevaultwallet.io/ wallet.
https://steamdesktopauthenticator.me/ - steam guard mobile authenticator plans to use bandwidth that provides transmission of up to 50/50% of all two-way communication and up to ten% of local web traffic, in places with high population density.
Canada Pharmacy 24 Hour Drug Store Canadian pharmacies online
<a href="http://mednowca.com/">list of legitimate canadian pharmacies</a>
<a href="http://aionlinepharmacy.com/">online pharmacy no prescription canada</a> Generic Cialis Online Pharmacy Reviews 452 toronto drug store reviews
Thanks for the auspicious writeup. It in fact used to be a amusement account it. Look complex to far added agreeable from you! By the way, how can we be in contact?
The capsules are operating in mode of "aging" priority and contingent of views in scale of each priority segment of https://steamdesktopauthenticator.me/ - steam desktop authenticator sda.
This page is dedicated for ASF configuration. It serves as a complete documentation of config directory, allowing you to tune ASF to your needs <a href="https://steamauthenticator.ru/">steam mobile authenticator</a>
Steam aauthenticator is a option of two-step authentication on steam. It provides additional step privacy your nicknames and passwords. If this option is enabled, Steam Aauthenticator asks you for one-time passcode every time , when you login to Steam on a unfamiliar device <a href="https://steamdesktopauthenticator.me/">steam guard mobile authenticator</a>
Somebody was posting that setting up the authenticator works on 1.0.11, and then upgrade to 1.0.13 for confirmations to work. Idk, something like that, haven't tried it <a href="https://steamdesktopauthenticator.io/">steam authenticator скачать</a>
https://detivetra.ru/ <a href=https://detivetra.ru/>https://detivetra.ru/</a> https://detivetra.ru/ - https://detivetra.ru/
Нада добавить еще пункт
service of this insurance enterprise "Name your price" allows possible customers to build their car insurance policy depending on the http://floridalifes.com/?p=2770 - http://floridalifes.com/?p=2770, what is capable be useful for bikers with reduced budget.
Долгие годы мы производим сувениры, подарки и рекламную продукция как для больших корпораций, так и для среднего и малого бизнеса <a href="https://gglive.org/en/live">лучшие беттинг сайты</a>
Прохождение игры GTA 5. В контрольном списке GTA V есть пять основных категорий целей: чтобы достичь 100% выполнения в GTA 5 Вам необходимо выполнить 69 сюжетных миссий <a href="https://rutube.ru/video/86e29395c5513cee14fb9b61370032ec/">https://rutube.ru/video/86e29395c5513cee14fb9b61370032ec/</a>
Согласен, очень полезная мысль
почти все лучшие бк готовы предоставить новичкам на старт поощрительный бонус, https://melbet-officiale.top/ - https://melbet-officiale.top/ который удвоит сумму начального восполнения счета.
<a href=https://eyebrow-tattoo-md.com/>смм прайс</a>
Woah! I'm really enjoying the template/theme of this website. It's simple, yet effective. A lot of times it's very difficult to get that "perfect balance" between usability and visual appearance. I must say you've done a great job with this. Additionally, the blog loads extremely quick for me on Chrome. Excellent Blog!
Tadalafil for sale <a href="http://supremesuppliersmumbai.com/">online pharmacy</a> Cialis mazatlan mexico
Check your email for the availability of a welcome letter from https://www.cartergroupland.com/articles/what-s-hot-what-s-not - https://www.cartergroupland.com/articles/what-s-hot-what-s-not. If only Anubis had woken up and assumed his mortal form to pick at the remains of my breakfast.
{if|when} you {haven't {done|done} it yourself, {an error notification|message} will appear in #file_links["C:\Users\Admin\Desktop\file\gsa+en+100ksteam999484276943URLBB.txt",1,N - ; update it! {if|in the situation where} you {correctly|correctly|competently|intelligently} initialized submodules, {you need|should|should|need|you should} see two tree hierarchies on the left side of {the screen|window}, one labeled steamdesktopauthenticator, and {another|the other} steamauth.
8. Thanks to the significant range of guarantee the quality , including cards and electronic accounts, winbay Plinki http://malikaenglishschool.edu.np/experience-authentic-first-person-blackjack-in-english-at-online-casinos/ - Winbay enables easy deposit and withdraw money.
Температура ночью 3-8° мороза, https://fragglerockcrew.com/performances/fraggle-rock-crew-school-performance/ - https://fragglerockcrew.com/performances/fraggle-rock-crew-school-performance/ днем 2-7° тепла. Температура ночью в диапазоне 0° около пяти° мороза, днем 4-9° тепла.
Viagra From Usa Pharmacy Sildenafil online
<a href="http://24hourcanadianpharmacy.com/">pacific care pharmacy</a>
<a href="http://woldwidewithoutaprescription.com/">www.prescriptionpillspharmacyrx.ru</a> 4 Corners Pharmacy Where to get viagra cheap
Viagra online india <a href="http://onlineviagraprescription.com/">viagra no perscription</a> Buying clomid online safe Aldactone <a href="http://supremesuppliersmumbai.com/">canada pharmacy online</a> Canadian pharmacy without prescritption
Я извиняюсь, но, по-моему, Вы не правы. Могу отстоять свою позицию. Пишите мне в PM, пообщаемся.
полученные в рамках акций и турниров награды и призы могут быть пущены в дело для ставок в интимных шалостях на https://melbet-1r.xyz/ - https://melbet-1r.xyz/ ресурсе казино.
Infants may temporary issues with muscle tone or self-control| willpower| self-control}, which not be difficult confused with cerebral palsy, permanent https://www.zlivematter.com/10-reason-why-roofing-are-factmake-easier-7/ - https://www.zlivematter.com/10-reason-why-roofing-are-factmake-easier-7/.
Так долго ждал и вот -=)
одной из уникальных особенностей 1win является программа кэшбэка, https://sc-3.ru/test/pgs/zagolovok_aktualynyy_trend_v_interyere_fotoprint_kak_ispolyzovaty.html - https://sc-3.ru/test/pgs/zagolovok_aktualynyy_trend_v_interyere_fotoprint_kak_ispolyzovaty.html которая дает возможность игрокам выводить до 30% возврата проигранных средств довольно-таки часто.
Быстро, качественно, надёжно! Лучшие!
<a href=https://dostavka-cvetov56.ru/>букеты томск</a>
Лучшие девушки Адлера готовы познакомиться с вами на сайте для знакомств 18+. Вы сможете выбрать из множества привлекательных девушек, готовых к общению и увлекательному досугу. Не упустите шанс провести время в компании интересных собеседниц и создать незабываемые воспоминания: <a href=http://sochi-night.vip/>сочи проститутки</a>
Я думаю, что Вы не правы. Я уверен. Давайте обсудим. Пишите мне в PM, пообщаемся.
меню Свит Бонанза находится в нижней части (под главным экраном с https://kagro.kz/ - sweet bonanza леденцами).
Букет для свекрови – лед тронулся!
<a href=https://tauflowers.ru/>купить розы в томске</a>
весна!!!
kostenlos Spins/Spins platziert auf Spielautomaten netent, https://verde-casino-bonus.de/boni/index.html - https://verde-casino-bonus.de/boni/index.html pragmatic und spinomenal. 4. Verwenden Sie den erhaltenen Link per E-Mail|E-Mail}, um aktivieren Seite im verde Casino|Glucksspiel zu aktivieren.
Просто постоянно делайте акцент на том, что у вас чрезвычайно вежливые и компетентные менеджеры, они не только лишь помогут разумно выбрать одежду, но и проконсультируют по любым вопросам, https://majorhomeimprovements.com/are-solar-panels-a-good-idea-for-your-new-roof-google-knows/ - https://majorhomeimprovements.com/are-solar-panels-a-good-idea-for-your-new-roof-google-knows/ расскажут о вариантах приготовления продуктов и исцеляющих свойствах.
Согласен, это отличная мысль
коли ви будете бути звичайним користувачем, який готовий кинути палити або просто підшукуєте малому кількості пара, https://most.forum2x2.com/t4226-topic - https://most.forum2x2.com/t4226-topic модний бокс-мод не є хорошим варіантом!
<a href="https://vk.com/club229712323">Воздушные шары Липецк на ДР</a">
Все, что поможет каждому разобраться в огромном количестве софта, драйверов, конвертеров и веб-сервисов. Мы публикуем в нашем блоге материалы о проблемах "синих экранов", полезных программах, технологиях и многом ином <a href=https://chopen.net/>https://chopen.net/</a>
Напротив, https://d-wigy.com/amazon-fire-tv/ - https://d-wigy.com/amazon-fire-tv/ при грамотной ценах они разве что увеличат вашу прибыль. помимо прочего существуют еще вегетарианцы, сотрудники, которые соблюдают православные посты…
<a href="https://admiralx-zn.xyz">Admiral X</a>
<a href="https://admiralx-n9ra.buzz">Адмирал икс</a>
Блог, посвященные всем видам сварочных работ с интересными и полезными публикациями <a href=https://svarkalegko.com/>https://svarkalegko.com/</a>
https://vc.ru/
Меня тоже волнует этот вопрос. Скажите мне пожалуйста - где я могу об этом прочитать?
Кожна підсистема-це простота в використанні. Девайси за характеристиками можуть опціонально відрізнятися: кальянні затяжки, сигаретні затяжки, кількість затяжок, колір, ємність акумулятора, http://eureka.bestforums.org/viewtopic.php?f=12&t=407 - http://eureka.bestforums.org/viewtopic.php?f=12&t=407 вбудовані дисплеї і т. д.
Ветеринары и изготовители кормов разделяют их на несколько видов - эконом, премиум, https://www.isabelkronenberger.de/test - https://www.isabelkronenberger.de/test супер-премиум и холистик.
<a href="https://vk.com/club229712323">Гелиевые шарики Липецк дешево</a">
<a href="https://1winu.xyz">1win</a>
<a href="https://fairspin-xxv.xyz">фаирспин</a>
Want to recharge instantly - select a gorgeous woman, man or shemale!
There is a vast choice of juicy shapes for you - teen, gorgeous, hot!
https://psee.io/663bfw - Fuck their now!
Букет пережил перелёт – встречали как героя!
<a href=https://tauflowers.ru/>заказ цветов томск с доставкой</a>
<a href="https://t.me/alexshar48">Воздушные шары Липецк онлайн</a">
<a href="https://vk.com/club229712323">Воздушные шары на свадьбу</a">
С плеч долой! Скатертью дорога! Тем лучше!
3. Каковы осадки? для большинства представителей человечества здание приятные бонусы - к примеру, возможность переехать на пенсию в максимально теплую страну. спустя 3 годика он продал ее за 300 https://drheshamabdalla.com/services/alssasi/ - https://drheshamabdalla.com/services/alssasi/ 000 евро!
Я считаю, что Вы допускаете ошибку. Могу это доказать. Пишите мне в PM, обсудим.
вы никогда не только лишь получаете вид на жительство - вам каждый момент есть куда прибыть и каким образом обосноваться, http://fande.jp/higashiura/bbs2015/bbs18.cgi - http://fande.jp/higashiura/bbs2015/bbs18.cgi если потребуется покинуть родную страну.
<a href=https://sejf-pod-oruzhie.ru/>купить оружейный сейф доставка</a>
We are hesitating about the risk of dangerous consequences and the harm leading to the termination of treatment, because in addition to the differences in application of stem tissues in numerous studies and the absence of results in other dimensional studies, https://student.uog.edu.et/introducing-dr-deniz-zeynep-2/ - https://student.uog.edu.et/introducing-dr-deniz-zeynep-2/ was carried out in very small number cases.
Although the results achieved by schett for patients with SLE were unprecedented, https://www.sgomberimilano.eu/2021/01/11/hello-world/ - https://www.sgomberimilano.eu/2021/01/11/hello-world/ has serious flaws/shortcomings in the application of standard car-T cell therapy for patients with autoimmune diseases.
Какие слова... супер, блестящая фраза
в настройках смартфона следует разрешить установку https://dermatologist-capetown.co.za/tips-how-to-apply-prescription-topicals-containing-retinoids/ - https://dermatologist-capetown.co.za/tips-how-to-apply-prescription-topicals-containing-retinoids/ неизвестных программ. 3. живые геймы для ценителей играть в настольные и карточные игры с конкретными противниками.
Your mode of describing everything in this piece of writing is actually nice, every one be capable of effortlessly be aware of it, Thanks a lot.
Hi, I think your site might be having browser compatibility issues. When I look at your blog site in Safari, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, wonderful blog!
Hello There. I found your blog using msn. This is a very well written article. I will make sure to bookmark it and return to read more of your useful information. Thanks for the post. I'll certainly return.
Hello, i think that i saw you visited my weblog thus i came to “return the favor”.I'm trying to find things to enhance my web site!I suppose its ok to use some of your ideas!!
Magnificent beat ! I wish to apprentice while you amend your website, how could i subscribe for a blog site? The account helped me a acceptable deal. I had been a little bit acquainted of this your broadcast provided bright clear idea
Жаль, что не смогу сейчас участвовать в обсуждении. Очень мало информации. Но с удовольствием буду следить за этой темой.
???? {??????????|??????????} {????? ???|???? ??????}, ?? #file_links["C:\Users\Admin\Desktop\file\gsa+bn+Phoenix5k10k20k40k603POP2URLBB.txt",1,N - {????|???????|?????? ?? ????} {??? ???????????|???????????|???????????} {5 | ??? ???????? ????? ???? ???? ??? {??????? ????|??????????? ????} ??????? ???? ??? ?? {??|??} {??|1}, 4 {????|????} {4 ??????|30 ???}.
Планетарные события. Ежедневные актуальные новости про самые важные события в мире и России. Также публикация аналитических статей на тему общества, экономики, туризма и автопрома <a href=https://telemax-net.ru/>https://telemax-net.ru/</a>
Конечно, само собой разумеется.
??????payment made2?????? ?- https://onlinecasinobtc.jp/ - ???? ??? ???????????????-2011??wordpress?????????????????????????
Нужно попробовать все
among world slot machines|machines|aggregates|machines} - a night with Cleo, Golden Buffalo and five times Vegas, an https://joshrimer.com/mr-gay-canada-party/ - https://joshrimer.com/mr-gay-canada-party/ that satisfies the most diverse preferences of the players.
В этом что-то есть и это отличная идея. Я Вас поддерживаю.
это место, https://singapore-company.ru/ - https://singapore-company.ru где инвесторы могут найти возможности для воплощения в жизнь перспективных разработок и стартапов. Правительство заключило сеть двусторонних налоговых соглашений с любыми государствами, что гарантирует гибкие условия для международного бизнеса.
Прошу прощения, что вмешался... Я разбираюсь в этом вопросе. Давайте обсудим. Пишите здесь или в PM.
потім, щоб задовольнити побажання наших клієнтів, ми зібрали фірмовий автошоп, на якому знайдеться як оригінальні https://www.vo5.org/news/auto/zapchasti-na-renault-megane-3-reno-megan-3 - https://www.vo5.org/news/auto/zapchasti-na-renault-megane-3-reno-megan-3, так і популярні замінники.
<a href=https://plastictek.ru/>анкерные листы</a>
Конечно. Всё выше сказанное правда. Можем пообщаться на эту тему.
there is big fluctuation of stuff so the process is one of the best reasons why many agents are missing professional https://infodubaikv.wixsite.com/dubaikv - агентство элитной недвижимости ОАЭ в Эстонии selling skills.
Stem cell therapy is {not|at all| at all} not {necessarily|only} the treatment of symptoms, {but also|but also| the possibility of {treating diseases | curing diseases | healing ailments}, the #file_links["C:\Users\Admin\Desktop\file\gsa+en+10k40kGeorgiy1903251P2URLBB.txt",1,N - for which was previously considered incurable.
Рекомендую Вам посетить сайт, с огромным количеством информации по интересующей Вас теме.
these statistics lead to increase in the number of bets placed. Our guide for betting on tennis will help you start bet money on the https://formosa.house/twenty-five-free-spins-no-deposit-current-affirmed-now-offers-for-2024/ - superbaji vip.
12.Beltrami A.P., Bartucci L., Torella D., #file_links["C:\Users\Admin\Desktop\file\gsa+en+10k20kGeorgiy19032512P2URLBB.txt",1,N - , and {others|etc|etc|etc}. For example, the ability to form whole joints in mouse models27 was achieved {with|starting with} mesenchymal stem cells, {they|which} {give|will give rise to bones and cartilage.
Извините, я удалил этот вопрос
against other https://www.evergreenbusinessfunding.com/cazinou-bonus-depozit-exclusiv-65-de-coduri-gratuite-pe-bani-reali-2024/ - sloturi book of ra - betus, bovada and mybookie, which are known for their convenient platforms and taste options bookmakers.
{along with|together with} the use of advanced {cell #file_links["C:\Users\Admin\Desktop\file\gsa+en+10k20kGeorgiy1903251P2URLBB.txt",1,N - .
Available data says about the fact that in neurological diseases, the introduction of stem cells into damaged tissue reduces inflammation and physical improves function, http://e49.us/stemcelltreatment32728 - http://e49.us/stemcelltreatment32728 can promote healing and the return of tissue growth.
Я разбираюсь в этом вопросе. Можно обсудить.
this experience makes us leaders in area of high-quality virtual scenery and https://www.aniarticles.com/48115-home-staging-in-los-angeles-sell-faster-and-for-top-dollar - professional home staging, here we every time get flawless images.
Эксклюзивные бездепозитные премии: доступны только избранным игрокам или только в https://www.mauropellizzi.com/coincidenze/img_9198iouou/ - https://www.mauropellizzi.com/coincidenze/img_9198iouou/ определенных каналах.
Добро пожаловать на новый сайт знакомств в Сочи! Здесь каждый может найти интересные знакомства и завести новые дружбы с девушками. Не упустите шанс открыть для себя новый мир общения и отношений. Ваша любовь уже ждёт вас за углом: <a href=https://t.me/sochinightt>проститутки сочи</a>
1 currently http://traeger.cl/hello-world/ - http://traeger.cl/hello-world/ are the only medicines from stem cells approved by the FDA for kindling America, have a composition of hematopoietic stem cells (also known as as hematopoietic progenitor cells), which receive from umbilical cord blood.
493 625 руб http://emshape.ru/catalog/kosmetika/
862 500 руб https://emshape.ru/catalog/kosmetika/maslo-antiejdzh/
24 900 руб https://emshape.ru/catalog/kosmetika/maslo-dlya-potyazhki-kozhi/
19 900 руб http://emshape.ru/catalog/kosmetika/
ХИТ ПРОДАЖ! ВЫГОДНО!
Неодимовый лазер Nd:YAG Y9 https://emshape.ru/статьи/page/2/
Pretty nice post. I just stumbled upon your weblog and wanted to say that I've truly enjoyed surfing around your blog posts. In any case I will be subscribing to your feed and I hope you write again soon!
there are many private cord blood banks that https://electric-lyubertsy.ru/2019/02/22/privet-mir/ - https://electric-lyubertsy.ru/2019/02/22/privet-mir/ and ucb storage. they too note that when discussing your options, you need ask whether your attending physician has a financial or other conflict of interest with some a private commercial bank.
study in the field stem cells and multiple sclerosis (n.d.). you also will need follow-up visits during a couple years. Miller A.E., the https://gpaeburgas.org/GSL/2018/03/27/lets-think-ecological-about-the-future/ - https://gpaeburgas.org/GSL/2018/03/27/lets-think-ecological-about-the-future/ and other.
Заказываю уже пятый раз – всегда безупречно и с душой!
<a href=https://tauflowers.ru/>букет невесты</a>
Если вам нужно прописаться по адресу для устройства на работу, мы обеспечим надежный вариант: <a href=https://reg-v-msk.ru/>регистрация</a>
South Korea has become in demand brand of medical tourism, especially in area of stem cell research and therapy, the https://carmencarrazquez.es/product/rucksack/ - https://carmencarrazquez.es/product/rucksack/ mainly is due to relatively competitive prices and the unique quality of medical services.
Доставили аккуратно и бережно. Благодарю!
<a href=https://dostavka-cvetov56.ru/>букет цветов томск</a>
<a href=https://www.prozdor.ru/zabolevaniya/mir-zvukov-prostye-shagi-k-luchshemu-vospriyatiju-rechi-i-muzyki/>https://www.prozdor.ru/zabolevaniya/mir-zvukov-prostye-shagi-k-luchshemu-vospriyatiju-rechi-i-muzyki/</a>
<a href=https://www.prozdor.ru/zabolevaniya/nevidimye-bolezni-pod-pricelom-kak-mrt-nahodit-opuholi-na-rannej-stadii/>https://www.prozdor.ru/zabolevaniya/nevidimye-bolezni-pod-pricelom-kak-mrt-nahodit-opuholi-na-rannej-stadii/</a>
For those who are intrigued by the potential of stem cell therapy and strive to explore method of treatment, consider the possibility of contacting to the regeneration https://mxexpert.gr/%CE%B1%CF%81%CF%87%CE%B9%CE%BA%CE%B7/r1-chain-main-2/ - https://mxexpert.gr/%CE%B1%CF%81%CF%87%CE%B9%CE%BA%CE%B7/r1-chain-main-2/ Center in Huntsville, Alabama.
Букет с эустомами - нежность в каждом лепестке!
<a href=https://cvetokispanskie.ru/>купить цветы томск</a>
A meta-analysis which was conducted in 2007 year showed that therapy with animals was associated with moderate improvement in the results of https://massage-verrassing.nl/waar-vind-ik-goede-hot-stone-massages/ - https://massage-verrassing.nl/waar-vind-ik-goede-hot-stone-massages/".
500 бесплатных https://www.mzrenegades.cz/planovana-akce/motodovolena/ - https://www.mzrenegades.cz/planovana-akce/motodovolena/ вращений в течении регистрировании. в данном случае, есть условие, что потребуется сделать небольшой депозит для снятия блокировки с денег - подобные промо-кампании называются "липкими".
<a href=https://bartabsf.com/>криптобосс регистрация</a>
отзывы пользователей. Важной параметром какого угодно игрового проекта https://nutridianaferegrino.com/the-big-design-wall-likes-pictures/ - https://nutridianaferegrino.com/the-big-design-wall-likes-pictures/ являются отзывы пользователей. 3. Лицензирование всех видов азартной деятельности, даже и в виртуальном мире, без каких бы то ни было жестких ограничений.
Символьные комбинации регулярно обновляются и меняются, http://stainlemer.ch/index.asp?inc=blog/index.asp&typ=nav2&cat=140&id=642&page - http://stainlemer.ch/index.asp?inc=blog/index.asp&typ=nav2&cat=140&id=642&page что должны принимая во внимание все гемблеры. Депозитные - такие поощрения распространены практически во всех клубах.
Упаковка не промокла под дождем - цветы сухие!
<a href=https://cvetokispanskie.ru/>букет пионов</a>
Хоть убей, не знаю.
в общем – все этапы максимально займут 9-12 месяцев, но чаще всего, http://therapist-dent.lucialpiazzale.com/professionalnye-trebovania-k-stomatologam-terapevtam - http://therapist-dent.lucialpiazzale.com/professionalnye-trebovania-k-stomatologam-terapevtam намного дешевле. фактически дела - это конус с винтовой резьбой.
<a href=https://rusrek.com/news/eshhe/avto/kak-sdat-teoreticheskii-test-v-dmv/>https://rusrek.com/news/eshhe/avto/kak-sdat-teoreticheskii-test-v-dmv/</a>
in other cases, for http://energau.com/blog/item/7-anssi-certifica-y-da-una-clasificacion-al-conmutador-ethernet-industrial-scalance-xm408-8c?USER=Pieroweb&L=0 - http://energau.com/blog/item/7-anssi-certifica-y-da-una-clasificacion-al-conmutador-ethernet-industrial-scalance-xm408-8c?USER=Pieroweb&L=0, they are processed on upcoming business day due to the difference in time.
Понятно, спасибо за помощь в этом вопросе.
10. Вывод: https://1winql.xyz/ - https://1winql.xyz - это оптимальное зоны для тех, кто уважает количество игр, современный дизайн, щедрые премии и топовый уровень безопасности.
The letter of credit will become a guarantee that the person will make a payment for a certain amount by https://gulfindex.org/2022/02/08/technical-requirements/ - https://gulfindex.org/2022/02/08/technical-requirements/ on certain day.
Ищете проверенную помощь в наведении порядка вашей в Санкт-Петербурге? Наша команда специалистов гарантирует чистоту и и порядок в вашем доме! Мы применяем только безопасные для здоровья и эффективные средства, чтобы вы могли вкушать свежестью без хлопот. Переходите https://profuslugi24.ru/ Не упустите шанс сделать свою жизнь проще и удобнее.
Это точно, идеалов нет
precise number and types of games always will be different, depending on which https://www.ismagolf.com/best-online-casinos-top-payout-online-casinos-2025-144/ - https://www.ismagolf.com/best-online-casinos-top-payout-online-casinos-2025-144/ you choose in favor of.
Я думаю, что Вы допускаете ошибку. Предлагаю это обсудить.
Спільна діяльність може підвищити мотивацію та сприяти більш активному засвоєнню знань. Спрощення організації. один з вас може виступати в ролі організатора, https://doodleordie.com/profile/arsenkomarov - https://doodleordie.com/profile/arsenkomarov що знижує вага на всякого учасника.
Роскошные шторы для любого интерьера
сшить шторы на заказ https://zakaz-shtor-msk.ru/ - сшить шторы на заказ . Ткацкий
Нада сё на заметку взять!!!!
Das Menu ist gro?er/kuhler, als/als nur eine Liste von Gerichten ist die Idee von dir https://pensionampark.com/shopdaddy-studio-eu - https://pensionampark.com/shopdaddy-studio-eu in Restaurants oder/oder Cafes/Restaurants.
Конечно. Всё выше сказанное правда.
Дата, до которой действует сертификат либо лицензия, https://www.hidden-street.net/forum/members/174039-JAANAS - https://www.hidden-street.net/forum/members/174039-JAANAS ежели их потребуется продлять/обновлять. Иногда работодатель может требовать наличие предусмотренных сертификаций у вероятных работников.
я тоже возьму.
????? https://1xbet-apk.app/ - ?? ????? 1xbet- ????????? ? ???? ?? ???? ????. ??? ? ?????? ?????????? ?????? ??????? ? ??? ?? ??? ????? ???? ??????? ?????? ? ??????? ?? ?????? ?????? ??????|??? ?????? ??????????.
nur perfekt Qualitat geeignet fur Ihre Kuche oder Backerei. Funktionen und Aussehen mussen einfach ubereinstimmen und harmonieren/kombinieren mit http://kamadobono.se/se/component/k2/item/38 - http://kamadobono.se/se/component/k2/item/38.
Unser erfahrener Kundendienst/Begleitung Kunden/Kunden wird gerne irgendwelche Fragen durch den Manager wahrend der Arbeitszeit, und per E-Mail beantworten|beleuchten.http://www.crb7.org.br/2020/10/20/anuidade-2021-resolucao-no-227-fixacao-de-valores/ - http://www.crb7.org.br/2020/10/20/anuidade-2021-resolucao-no-227-fixacao-de-valores/
Эксклюзивные шторы на заказ
пошив штор на заказ https://shtory-na-zakaz-moscow.ru/ - пошив штор на заказ .
1917 - в калифорнии принят первый акт о лицензировании риелторов. все-таки, http://www.geraldica.ru/agentstvo-nedvizhimosti-balashiha/ - http://www.geraldica.ru/agentstvo-nedvizhimosti-balashiha/ в государстве рынок риэлторских услуг активно сотрудничает и раскручивается.
Римские шторы на заказ — комфорт и стиль
римские шторы на заказ https://rimskie-shtory-na-zakaz.ru/ - римские шторы на заказ .
<a href="https://t.me/alexshar48">Гелиевые шарики Липецк фольгированные</a">
Букет свежее некуда, будто только что из сада!
<a href=https://cvetokispanskie.ru/>заказать цветы томск</a>
ולקחה את זמנה, והגבילה את עצמה רק לקחת את האשכים שלי וללטף את פניה עם צבעוני, עליז, גם פתוח, אבל עם תחתונים המכסים את התחת של הילדה, אם כי <a href=http://www.hanut-sex.co.il/>דירות דיסקרטיות בטבריה</a>
Плюсом идут навыки продвижения, позволяющие вывести объявление в десятку. Деятельность агента подразумевает учет любых пожеланий клиента, http://neoncity.gtaserv.ru/viewtopic.php?f=38&t=2970&p=3018#p3018 - http://neoncity.gtaserv.ru/viewtopic.php?f=38&t=2970&p=3018#p3018 подбор наилучших предложений и юридическая чистота заключаемого договора.
Ищете надежную помощь в наведении порядка вашей в Санкт-Петербурге? Наша группа специалистов дает гарантию чистоту и порядок в вашем доме! Мы применяем только безопасные и эффективные средства, чтобы вы могли наслаждаться свежестью без хлопот. Двигайтесь к https://klining-uslugi24.ru Не прозевайте уникальную возможность сделать свою жизнь проще и комфортнее.
<a href="https://t.me/alexshar48">Воздушные шары Липецк на 23 февраля</a">
העניין האמיתי של אשתי בקסם המתוק הזה, וזה הדליק אותי עוד יותר. גם ובמניקור שלי. החלת בעדינות, לק אדום על הציפורניים שלי. הרגשתי כמו <a href=http://www.maxpenis.co.il/>visit this page</a>
Вы попали в самую точку. Мне кажется это хорошая мысль. Я согласен с Вами.
distintivo betway es el equilibrio de tradicional, y moderno juegos prestar este tipo juegos como joker poker moderna de red rake gaming con una impresionante tasa de rtp del 98,59%, en linea-http://www.suertia-casino.com/ - Prueba la ruleta online y la mejor seleccion de maquinas tematicas de tales proveedores como pragmatic play y microgaming..
По-моему это очевидно. Советую Вам попробовать поискать в google.com
Decaris brought her vision to life by presenting https://www.discolamaddalena.it/2019/01/16/ferie-in-vista/ - https://www.discolamaddalena.it/2019/01/16/ferie-in-vista/ with diamond-shaped gray pleasures and textured gold inserts.
<a href=https://novosti-politiki.ru/>последние новости переговоров сша и украины</a>
Что-то так не получается
fondos/ dinero se agregaran inmediatamente a cualquier cuenta en https://fueraya.es/ - fueraya.es. entonces todo lo que en tales circunstancias necesita hacer es cuidar el juego, en tal caso usted aspira a intentarlo.
Книги про отношения. Эмоциональные качели в отношениях.
Что такое отношения.
Доверьтесь профессионалам: автоматика Somfy
Автоматика Somfy https://somfy-avtomatika.ru/ - Автоматика Somfy . Прокарниз
В этом что-то есть. Спасибо за помощь в этом вопросе. Все гениальное просто.
{also|deshalb|in diesem Zusammenhang gibt es ein grunes|smaragdgrunes Licht fur die kostenlose Registrierung von {unserer/unserer} Seite. Ab 2022 #file_links["C:\Users\Admin\Desktop\file\gsa+de+Phoenix40k80k150k300k643URLBB.txt",1,N - betonred ist Eigentum von uno digital media b.v.
Деревянные горизонтальные жалюзи с электроприводом: функциональность и дизайн
Деревянные горизонтальные жалюзи с электроприводом https://derevo-gorizont-motor.ru/ - Деревянные горизонтальные жалюзи с электроприводом . Прокарниз
По моему мнению Вы не правы. Давайте обсудим это. Пишите мне в PM, поговорим.
moreover, the https://costofstemtherapy.com/ - https://costofstemtherapy.com, the number of cells injected and that fact, are stem cells considered environmentally friendly pure and viable, also involve the cost of stem cell therapy.
значок металлический с надписью <a href=https://metallicheskie-znachki-zakaz.ru/>изготовление корпоративных значков</a>
Я извиняюсь, но, по-моему, Вы не правы. Давайте обсудим это.
now , for example, during application https://trustedstemcellcost.com/ - https://trustedstemcellcost.com medic can to preserve blood from the umbilical cord after discharge from the hospital for furnace the future.
<a href="https://avtovikup-lipetsk.ru">Продать машину быстро</a>
https://toolbarqueries.google.com.fj/url?q=https://www.xxxfrance.ink/coco/xxx-photo-vaginal-327319.html
https://yarmarka.com/bitrix/redirect.php?goto=https://www.xxxfrance.ink/r/nik3arbi/
https://cse.google.ru/url?sa=t&url=https://www.xxxfrance.ink/coco/nik-tounsi-rajel-w-9a7ba-488121.html
https://a.parva.blue/iframe/hatena_bookmark_comment?canonical_uri=https://www.xxxfrance.ink/coco/xxn-segale-477350.html
o657g
к вам всегда будут относиться с максимальной заботой и вниманием. для кого-то семейств это получается значить соблюдение традиционным церемониям, https://blackrose.com.ua/krematsija-v-zaporozhe - https://blackrose.com.ua/krematsija-v-zaporozhe некоторым нужна более современная организация.
<a href="https://www.avito.ru/lipetsk/predlozheniya_uslug/vykup_avto_srochnyy_247_4211757789">Продать Машину Под Залогом банк</a>
очевидно вы ошиблись...
among key contenders at the present time are betus, bovada, betonline, mybookie, betnow, sportsbetting, everygame, thunderpick and xbet. similar resources like bovada sportsbook are characterized certain helpful and specialized support for buyers, and the http://bksranchi.org/agriculture/ - http://bksranchi.org/agriculture/ provides: effective solving difficulties of users.
<a href=https://expertmiele.ru/>https://expertmiele.ru/</a>
Извините, что не могу сейчас поучаствовать в дискуссии - очень занят. Вернусь - обязательно выскажу своё мнение по этому вопросу.
you can to study with the most diverse latest (and optimal!) The news of https://www.bitlocker.data-recovery.software/blog/best-online-casino-games-for-big-wins-7/ - https://www.bitlocker.data-recovery.software/blog/best-online-casino-games-for-big-wins-7/ is here!
Pekin https://samsunspor.info/ - samsunspor.info Recel. "1966-67 Turkiye 2. Futbol Ligi". 2015-16 sezonunda ligi 44 puanla bitiren tak?m, s?ralamalarda 9. nis/sektor/ s?ra oldu. birinci/lider yer/konum 'u isgal etti.
Аренда автомобиля с водителем в Иркутске https://dreamcars54.ru/politik
Тел.: +7 (914) 899-92-05 https://dreamcars54.ru/
На нашем сайте Вы можете заказать в Иркутске поездку на море на комфортабельном автобусе или микроавтобусе отправившись в увлекательное путешествие всей семьей или с друзьями https://dreamcars54.ru/politik
· нет водительских прав;
SKODA RAPID https://dreamcars54.ru/
Тел.: +7 (924) 612-58-17 https://dreamcars54.ru/politik
Galatasaray Futbol Kulubu antrenman yap?yor https://galatasarayfutbol.com/ - https://galatasarayfutbol.com/ Burhan Felek Spor Kompleksi'nde bulunan kapal? spor salonu /spor salonu salon /kulup, Ergun Gursoy ise Galatasaray Olimpiyat Yuzme Havuzu'nda antrenman yap?yor.
kuluplerin birbirlerinden yararlanmalar?n? saglamak icin endiseliyiz. simdi/bundan sonra https://goztepe-tr.org/ - TR Goztepe Spor Republikas?.
Hi! I could have sworn I've visited this web site before but after going through many of the posts I realized it's new to me. Regardless, I'm definitely delighted I came across it and I'll be bookmarking it and checking back regularly!
Лучшие системы автоматизации от Somfy
Автоматика Somfy https://somfy-avtomatika.ru/ - Автоматика Somfy . Прокарниз
Крайне советую <a href=https://a23ahskqsdbkl33.ru/>https://a23ahskqsdbkl33.ru/</a>
<a href="https://avtovikup-lipetsk.ru">Продать Машину Если Птс В Банке</a>
Дизайн штор для коттеджа: тренды 2025
шторы для коттеджа https://kottedzh-shtory.ru/ - шторы для коттеджа .
https://marketer-online.pro/ digital marketing training for beginners
<a href="https://t.me/lipetsk_auto">Битые и аварийные машины</a>
<a href="https://avtovikup-lipetsk.ru">Продать Авто Купленное В Кредит</a>
<a href="https://t.me/lipetsk_auto">Скупка машин</a>
Полностью разделяю Ваше мнение. В этом что-то есть и мне кажется это хорошая идея. Я согласен с Вами.
The ledger hardware wallet stores your individual keys and signs transactions offline, which does the https://myceliumwallet.io/ - https://myceliumwallet.io resistant to malicious attacks and threats.
<a href="https://www.avito.ru/lipetsk/predlozheniya_uslug/vykup_avto_srochnyy_247_4211757789">Выкуп кредитных авто дорого</a>
<a href="https://avtovikup-lipetsk.ru">Микроавтобусы и коммерческий транспорт</a>
Возьму на свойстрах и риск)))
є одноразки з різноманітними уподобаннями (elf bar, vaal, https://www.toplegacy.com/krashhij-magazin-elektronnih-sigaret-vash-shljah/ - https://www.toplegacy.com/krashhij-magazin-elektronnih-sigaret-vash-shljah/ chill up). відмінно від сигаретного диму, пар не містить смол і продуктів горіння, які осідають в легенях.Gorenje.
Преимущества https://ooo-opalubka-msk.ru/services/kupit-opalubku-v-moskve/
Обратный выкуп опалубки на взаимовыгодных условиях https://ooo-opalubka-msk.ru/services/opalubka-perekrytiy-kupit-v-moskvestenovaya-opalubka/
Обратившись к нам, можно:
2) Балочно-ригельная опалубка, которая позволяет создавать колоны и стены любой высоты https://ooo-opalubka-msk.ru/
Выезд специалиста (при необходимости)
<a href="https://bcgame-khht.xyz">бц гейм казино</a>
<a href="https://admiralx-keo.buzz">Адмирал икс</a>
что бы небыло нада глянуть...
as {awareness of {the ecological situation|environment} grows|grows|rises, {mostly|mostly|more|mostly|as a rule} {customers|consumers|buyers|visitors|believers}, {can|are able|manage} to #file_links["C:\Users\Admin\Desktop\file\gsa+en+seomaster30k20525URLBB.txt",1,N - . The brand's reputation significantly {affects|affects|is effective against} {prices for|prices for} {his|our} {products|products|offers}.
Какой бесподобный топик
Instalator zostanie pobrany do https://forum.armacenter.pl/viewtopic.php?f=12&t=15123 - https://forum.armacenter.pl/viewtopic.php?f=12&t=15123 folder downloads. bedziesz musial przewinac w dol i znajdz/ znajdz linijke z napisem " dodatki Nie istnieje osobiste Rejestracja".
<a href="https://avtovikup-lipetsk.ru">Продать автомобиль без птс</a>
Тема интересна, приму участие в обсуждении. Вместе мы сможем прийти к правильному ответу. Я уверен.
в свою очередь, не слишком опытные беттеры стараются угадать исходы футбольных матчей, http://kumangadanga.nnov.org/novosti-legalnogo-bettinga/kto-vigraet-ligy-chempinov-2025.html - http://kumangadanga.nnov.org/novosti-legalnogo-bettinga/kto-vigraet-ligy-chempinov-2025.html делая ставки на кон оптимальные деньги.
мне сильно понравилось
в эгоистичных целях, чаще, изготовитель ведет заводские испытания, что показывают качество товара, хотя изготовитель смотрит на задачи, http://stavtr.ru/ - http://stavtr.ru/ которые были поставлены для выпуска данного стройматериала.
Get a massive 200% bonus on your first deposit and boost your starting balance up to $ 200. <a href=https://bet-promo-codes.com/sportsbook-reviews/betwinner-registration/ >how to play betwinner</a>, Betwinner splits your bonus between sports and games to double your chances of winning.
However, one day, http://gomezromeo.ar/index.php/component/k2/item/9 - http://gomezromeo.ar/index.php/component/k2/item/9 becomes become more specialized and may to develop exclusively in specific types of cells.
Замечательная фраза
Интимная пластика (лабиопластика), в процессе которой меняются размеры половых губ, https://www.elitedenteam.co.il/ - пересадка волос мелких и больших. Врожденные дефекты внешности, которые влияют на самооценку и мешают вести полноценную социальную жизнь.
Я извиняюсь, но, по-моему, Вы не правы. Я уверен. Предлагаю это обсудить.
Автомат обеспечивает лёгкое переключение передач, https://www.orderviewdocs.online/doku.php?id=solenoidtester - https://www.orderviewdocs.online/doku.php?id=solenoidtester постоянный контроль мощности двигателей без усилий на первый взгляд водителя. Как соединяется АКПП с двигателем?
Браво, отличная идея и своевременно
The United Nations. Secretary of State Marco Rubio will now serve as Donald Trump's national security adviser, while continuing to head the State https://thietbivesinhgiahan.com/san-pham/sen-cay-tam-cao-cap-sc7070/ - https://thietbivesinhgiahan.com/san-pham/sen-cay-tam-cao-cap-sc7070/ Department.
<a href="https://unlimcasino-tyub.top">unlim casino</a>
<a href="https://vavadacasino-n7bg.buzz">вавада</a>
<a href="https://avtovikup-lipetsk.ru">Срочно Продать Авто В Залоге</a>
На мой взгляд, это актуально, буду принимать участие в обсуждении.
они способны легко адаптироваться к растущим потребностям в бизнес-информации, без серьезных https://iclei.org/wp-content/pgs/intervu_s_osnovatelyami_kompanii_ezcash_pobeditelyami_premii__iclei_2025.html - https://iclei.org/wp-content/pgs/intervu_s_osnovatelyami_kompanii_ezcash_pobeditelyami_premii__iclei_2025.html ошибок или простоев.
не треба)
Create an account in application without opening portal 888starz for https://888-starz.world/ - 888-starz.world. Verification maybe implemented from your cabinet and if professional filling out, it will open the possibility of timely receipt winnings.
Я удалил это вопрос
nowadays each company can be sure that She will choose a 1-year-https://1win-zerkalo.buzz/ - 1вин зеркало system. legal web resource company with this name was created in the spring of 2018 year.
Regenamex stem cell therapy offers a promising solution that focuses on regeneration of tissues to improve functions, and reduce the http://empira.ru/index.php?option=com_jcomments - http://empira.ru/index.php?option=com_jcomments.
Заказала сюрприз для жены — она была в полном восторге!
<a href=https://t.me/cvetaevatomskru/488>заказать цветы томск</a>
2018). Electrophysiological biomarkers predict clinical improvement in an unobstructed study evaluating the effectiveness of autologous cord blood for the http://L.Iv.Eli.Ne.S.Swxzu@Hu.Feng.Ku.Angn.I.Ub.I..Xn--.U.K37@cgi.members.interq.or.jp/ox/shogo/ONEE/g_book/g_book.cgi - http://L.Iv.Eli.Ne.S.Swxzu@Hu.Feng.Ku.Angn.I.Ub.I..Xn--.U.K37@cgi.members.interq.or.jp/ox/shogo/ONEE/g_book/g_book.cgi.
Это переходит все границы.
Стойкость гораздо ниже, https://duhisuper.ru/ - парфюмерия что-то около 8 часов. Одеколон - ароматическая композиция наподобие 60% спирта или водки и 4-6 эфирных масел.
<a href="https://www.avito.ru/lipetsk/predlozheniya_uslug/vykup_avto_srochnyy_247_4211757789">Скупка машин любых марок и состояний</a>
Esta funcionalidad no se limita solo al futbol; hay transmisiones de tenis, baloncesto en https://wiki.eqoarevival.com/index.php/M%C3%83%C2%B3vil_Establecimiento_De_Juegos_William_Hill-diccionario_Ingl%C3%83_s-Espa%C3%83%C2%B1ol_-_Wordreference.com - https://wiki.eqoarevival.com/index.php/M%C3%83%C2%B3vil_Establecimiento_De_Juegos_William_Hill-diccionario_Ingl%C3%83_s-Espa%C3%83%C2%B1ol_-_Wordreference.com y otros variedades de deportes.
After issuing http://www.oltony.ardoboz.hu/r.php?b=aHR0cHM6Ly93d3cuY2MxNDIuY29tL2NvbXBvbmVudC9rMi9pdGVtLzE3LWRvbmVjLXB1bHZpbmFyLW5pc2ktdml0YWUtb2Rpby1zdXNjaXBpdA - http://www.oltony.ardoboz.hu/r.php?b=aHR0cHM6Ly93d3cuY2MxNDIuY29tL2NvbXBvbmVudC9rMi9pdGVtLzE3LWRvbmVjLXB1bHZpbmFyLW5pc2ktdml0YWUtb2Rpby1zdXNjaXBpdA, the recovery phase begins. The day if you take stem cells is commonly considered “zero day". The stem cells will be injected into you through an intravenous catheter.
Букет собрали именно в той гамме, какую я просила. Очень красиво!
<a href=https://t.me/cvetaevatomskru/566>купить цветы в томске</a>
<a href="https://www.avito.ru/lipetsk/predlozheniya_uslug/vykup_avto_srochnyy_247_4211757789">Выкуп битых автомобилей</a>
Therefore, further molecular studies are needed for https://hoteltaroa.com/hola-mundo/ - https://hoteltaroa.com/hola-mundo/ in order to fully understand the degree of contribution of each of this kind segmentos to the observed orthopedic effect.
<a href="https://t.me/lipetsk_auto">Продать машину если птс в банке</a>
large set of account types for all levels of experience, including cent, pro, and besides that – probability to use the raw spread, what does https://wolvesbaneuo.com/wiki/index.php/User:Denice96Z4 - https://wolvesbaneuo.com/wiki/index.php/User:Denice96Z4 is ideal for day traders.
Спасибо за индивидуальный подход! Букет собрали именно под мои пожелания.
<a href=https://www.instagram.com/p/DI5huw_KR-y/?igsh=MWt6MTdpYWlja2I4eA==>доставка цветов томск</a>
they among other things help the user understand why ensuring the security of his personal registration in https://365.expresso.blog/question/online-bc-game-casino-in-the-philippines/ - https://365.expresso.blog/question/online-bc-game-casino-in-the-philippines/ necessary. Complete the work by clicking add in the upper-right corner of the dialog box.
Я думаю, что Вы допускаете ошибку. Могу отстоять свою позицию. Пишите мне в PM.
https://mostbet1.app/ - mostbet old version app download in India provides rich assortment of sports services, betting and online broadcasts, as well as is becoming legal in India.
Заказываю цветы только здесь, потому что уверена в качестве!
<a href=https://t.me/cvetaevatomskru/540>доставка цветов</a>
We were persistent and during as a result we finally got the opportunity to chat with an agent of http://forums.cgb.designknights.com/member.php?action=profile&uid=31457 - http://forums.cgb.designknights.com/member.php?action=profile&uid=31457, who quickly reacted and produced exact information.
Вы не правы. Пишите мне в PM.
The platform, launched on August 28, 2023, integrates the advanced features of velodrome v2. Before placing aero on portal uphold, https://aerlifi.org/ - aerodrome finance uphold conducted a comprehensive audit of aero and came to the conclusion that aero practically not maybe a security or derivative instrument respectively the relevant securities legislation.
Букет был настолько красив, что даже прохожие оборачивались!
<a href=https://www.instagram.com/p/DIyGYlxq5Ni/?igsh=MWN1M2oyZnZsMWMxZQ==>заказать цветы с доставкой в томске</a>
We will will be able to demonstrate to you about the application and the abundance of http://wiki.die-karte-bitte.de/index.php/The_System_Of_Reviews_In_Search_Google_And_Your_Website - http://wiki.die-karte-bitte.de/index.php/The_System_Of_Reviews_In_Search_Google_And_Your_Website.
Весьма полезная штука
и вообще, люди отправляются на автомобилях, https://vc.ru/u/1064498-nikita-eremov/455900-gde-mozhno-razmestit-naruzhnuyu-reklamu - https://vc.ru/u/1064498-nikita-eremov/455900-gde-mozhno-razmestit-naruzhnuyu-reklamu им некогда особо просматривать по сторонам. Стандартные. Имеют размер трех 6 метров.
Автоматические системы от Somfy — качество и инновации
Автоматика Somfy https://somfy-avtomatika.ru/ - Автоматика Somfy . Prokarniz
Цветы пришли свежие и ароматные, как будто только что срезаны!
<a href=https://vk.com/wall-61709230_7343>купить цветы томск</a>
Замечательно
и так по кругу,не рекомендую никому делать депозит,потом хрен выведите, https://pokerdom-casino.me/ - https://pokerdom-casino.me/ это покер рум а лохотрон.
Ваша идея блестяща
Team members are provided with our personal mobile phone, because our company are acceptable to visitor 24 hours a dayround the clock day, week in one week process execution of the http://www.ruifind.com/reliable-taxi-larnaca-your-ultimate-guide-to.html - http://www.ruifind.com/reliable-taxi-larnaca-your-ultimate-guide-to.html the conference.
Классс=)
The roulette section is represented by classic, European, French, https://neotenyapparel.com/river-belle-registration/ - riverbelle login and similar types of roulette.
Спасибо за объяснение. Я не знал этого.
{dafur/zu diesem Zweck} in #file_links["C:\Users\Admin\Desktop\file\gsa+de+10kRalferr51918665URLBB.txt",1,N - sie {zahlen|schreiben} {Konto|Einzahlung} ein und {erhalten|kaufen} 1 Ticket fur jeweils 30 Euro. mit {jedem/jedem} Geschenkniveau wird {jedes Jahr} {immer gro?er|gro?er|gro?er und gro?er|noch gro?er|viel gro?er}, und {mehr|mehr|langer}, {was|was|und ihr Wert wird {jedes Jahr} hoher und hoher.
Воздержусь от комментариев.
Im nft Casino {Sie/Benutzer} haben {verwenden|anwenden|verwenden|verwenden|konnen/in Gang setzen/konnen} nft {als/Rolle} Einsatze verwenden, #file_links["C:\Users\Admin\Desktop\file\gsa+de+10kRalferr51918615URLBB.txt",1,N - um nft {oder|oder} {zu gewinnen, um exklusive {Vorteile|Vorteile|Vorteile|Vorteile|Boni} {im System|im Rahmen von Treueprogrammen} zu erwerben/zu erhalten.
В этом что-то есть. Я согласен с Вами, спасибо за помощь в этом вопросе. Как всегда все гениальное просто.
in what is imperfection? The bonus structure is perhaps, a bit confusing, https://world-games.online/ - free canadian casino slots and not all of these games uniformly affect on wagering.
Я твёрдо уверен, что Вы не правы. Время покажет.
2. Step 2. navigate to page advertising promotions, in order access the service promo promotions in the general menu of the https://aphidapp.com/river-belle-no-deposit-bonus/ - riverbelle casino bonus on the first page.
уматово
https://cashbackcasinojp.com/ - ????? ??? ????? ??? ???????????????????????????????????????????????
Замечательно, весьма забавная фраза
Newcomers receive a lucrative package of bonuses from the https://www.letsgoprofessional.co.uk/revolutionizing-marketing-the-power-of-the-advertising-platform/ - marketing and advertising synergy, including cash payouts and free spins.
ха-ха пацталом)))))
Early printing houses placed printing plates in trays or drawers called typesetting boxes, in which there were compartments for each letter of the https://typetype.org/fonts/macedonian/ - macedonian font.
<a href="https://vavada-fastgame.buzz">vavada зеркало</a>
<a href="https://vavada-eeo.buzz">vavada зеркало</a>
В этом что-то есть и мне кажется это очень хорошая идея. Полностью с Вами соглашусь.
http://snilde.dk/aroniabaer-kompot-med-lun-halloumi-og-vild-salat/ - http://snilde.dk/aroniabaer-kompot-med-lun-halloumi-og-vild-salat/ ??????????????????????????????????????????????????????????????????????????????????? ????????????????????????????????????????????
Новости Киева <a href=https://u-misti.kyiv.ua/>https://u-misti.kyiv.ua</a> события, обзоры, произшествия
По моему мнению, это — большая ошибка.
HAWAII: Benutzer/Spieler erhalten/haben bis zu 110 frei https://quakerhungerclock.com/no-deposit-bonus/ - stay casino no deposit bonus codes. WELLINGTON: Benutzer/Spieler erhalten/haben 2% Cashback. das stay Casino ist ein sicherer und angenehmer Raum fur Spiele online.
Hi there just wanted to give you a quick heads up. The text in your content seem to be running off the screen in Opera. I'm not sure if this is a formatting issue or something to do with browser compatibility but I figured I'd post to let you know. The style and design look great though! Hope you get the issue fixed soon. Many thanks
Мне очень жаль, ничем не могу Вам помочь. Я думаю, Вы найдёте верное решение. Не отчаивайтесь.
https://casino-lukki.net/login/ - ????????????? ??????????????????????????????|?????}? ??????????????????????????????????
Прикольно! Улыбнуло! Афтару - респект!
ab jetzt/von nun an, wenn/wenn Sie beabsichtigen, den Bonus virtuelles Casino zu verwenden, haben Sie alles gleich notwendig wissen https://seoulplayers.com/wild-tokyo-no-deposit-bonus-dein-kompletter-guide-fur-spieler/ - wild tokyo free spins. was es braucht funktioniert/passiert.
Правда!!!
4. parol daxil edin - qrafik kodu daxil edin, Hans?/ kimi hesab?n?z? daxil etm?k hesab https://pinco.website.yandexcloud.net/ - http://pinco.website.yandexcloud.net et.
По-моему это уже обсуждалось.
Neben den wichtigsten Debit- und Kreditkarten/Kreditkarten konnen dies sein maestro, mastercard und visa sein, https://labventuregames.com/staycasino-mobile-app/ - stay casino applicatie, Euro, norwegische Kronen und US-Dollar.
As a pioneer in field of http://www.aa.cyberhome.ne.jp/~ryuba/cgi-bin/diary/diary.cgi?offset_month=0&dispevent=20131111 - http://www.aa.cyberhome.ne.jp/~ryuba/cgi-bin/diary/diary.cgi?offset_month=0&dispevent=20131111 for the treatment of various diseases.
Новости Винницы <a href=https://u-misti.vinnica.ua/>https://u-misti.vinnica.ua</a> события, статьи, происшествия в Виннице и области
Новини Житомир <a href=https://u-misti.zhitomir.ua/>https://u-misti.zhitomir.ua</a> события и новости Житомира и области.
Какие замечательные слова
5.4 Pramie am Spieltisch cadoola, nicht das, was in aktuellen plots/Angebote nicht enthalten ist.
In otherwise, by https://sanju.at/index.php?option=com_k2&view=item&id=1 - https://sanju.at/index.php?option=com_k2&view=item&id=1 the 888starz app, contact Arbitration or resort to the mobile version of ali. To establish your identity and current place of residence, provide your driver's license, utility bills, and other documentation.
<a href="https://riobet-gya.buzz">riobet</a>
<a href="https://1winxf.top">1win</a>
Извините, очищено
detaillierter/detaillierter uber https://thetacostandbook.com/wild-tokyo-login/ - wild tokyo online casino lesen Sie unten. wenn Sie unsicher sind, konnen Sie immer zu 100% anrufen Support, um zu klaren, was genau das Problem ist.
What relates to the https://jeroenpaling.nl/2020/02/10/hello-world/ - https://jeroenpaling.nl/2020/02/10/hello-world/? During so-called periods of the year, some clinics may give bonuses and special offers.
Сайт Одесса <a href=https://faine-misto.od.ua/>https://faine-misto.od.ua</a> новости, события Одессы и области, обзоры мест
Я конечно, прошу прощения, но это мне совершенно не подходит. Может, есть ещё варианты?
Simplification of borrowing and lending procedures is the inevitability of https://aavplifi.com/ - aave protocol through defi. however also to be found out, is is this specifics sustainable in the long term?
<a href="https://pharmavisuals.com/lisinopril.html">lisinopril prinivil tablet</a> https://pharmavisuals.com/lisinopril.html - lisinopril
<a href="https://pharmavisuals.com/nitrofurantoin.html">nitrofurantoin</a> https://pharmavisuals.com/nitrofurantoin.html - nitrofurantoin
since then, more research has been conducted whose goal is to identify evidence of the phenomenon that https://hasanieltsbanglay.com/ielts-reading-recent-exam-1/ - https://hasanieltsbanglay.com/ielts-reading-recent-exam-1/ potentially can raise the control of blood sugar and reduce the need for diabetes medications.
Прошу прощения, что я Вас прерываю, но не могли бы Вы дать больше информации.
become a user of the largest worldwide Internet gaming establishment https://bsblifi.net/ - Base bridge eth. Become a member - download and install our programs.
Неплохо-мне понравилось,но как-то грустновато!(
How does ethena ensure the profitability of https://ethena.forum/ - ethena finance for usde? separately from traditional stablecoins, USDE does not rely on fiat reserves, instead using cryptographic machines to maintain stability, staying at this resistant to censorship.
Hello there! This blog post couldn't be written much better! Looking through this article reminds me of my previous roommate! He always kept preaching about this. I'll send this article to him. Pretty sure he'll have a very good read. Many thanks for sharing!
they can help deal with privacy considerations and select you for the http://Hu.Feng.Ku.Angn.I.Ub.I.xn.xn.U.K37@cgi.members.interq.or.jp/ox/shogo/ONEE/g_book/g_book.cgi - http://Hu.Feng.Ku.Angn.I.Ub.I.xn.xn.U.K37@cgi.members.interq.or.jp/ox/shogo/ONEE/g_book/g_book.cgi or clinical inspections in an accredited location. 2023). Mesenchymal stem cell therapy in multiple sclerosis: a systematic review and meta-analysis.
<a href="https://1winxf.top">1РІРёРЅ</a>
<a href="https://vavadacasino-p7bg.buzz">vavada регистрация</a>
Браво, ваша идея пригодится
diligently study all interior items before release, in order to avoid difficulties. during the https://galxe.forum/ - galxe app, we will do a cors check, and request will not can done, if data parameters are configured incorrectly.
Fibroblast growth factor 2, made from breast cancer cells, and vascular endothelial growth factor are chemoattractants for the https://yogaasanas.science/wiki/Potentially_Unsafe_Methods_Of_Getting_Rid_Of_The_Disease_With_Low_Evidence:_Adam_Marks_Laura_Taylor_And_Jill_Schneiderhan - https://yogaasanas.science/wiki/Potentially_Unsafe_Methods_Of_Getting_Rid_Of_The_Disease_With_Low_Evidence:_Adam_Marks_Laura_Taylor_And_Jill_Schneiderhan with stem cells.
Я думаю, что Вы не правы. Могу это доказать. Пишите мне в PM.
in addition, https://rhinofi.us/ - rhino fi provides you realize "that a person are not alone. I was talking to a friend, who is the CEO of a private equity firm.
Важное: некоторые операторы предлагают купить номера гражданам определённых стран, http://shun.hippy.jp/gorobbs/mkakikomitai.cgi - http://shun.hippy.jp/gorobbs/mkakikomitai.cgi указанный момент, придется выяснять подробности. из рекомендуемых операторов такой только один - mango office.
Я извиняюсь, но, по-моему, Вы ошибаетесь. Могу это доказать. Пишите мне в PM, пообщаемся.
https://penthouse5401.pocketlisting.io/2025/05/16/page-51/ - https://penthouse5401.pocketlisting.io/2025/05/16/page-51/ ??? ?????? ?? ? ?????????????,??/?????? ??/??.
Howdy! Someone in my Facebook group shared this website with us so I came to check it out. I'm definitely enjoying the information. I'm book-marking and will be tweeting this to my followers! Fantastic blog and superb style and design.
Извините за то, что вмешиваюсь… Я разбираюсь в этом вопросе. Можно обсудить. Пишите здесь или в PM.
?/?????/??????/??/??/????/???/?????????,????,??,????? ??????????,????/????:??/??/??/?? https://govindashrservices.com/page-149/ - https://govindashrservices.com/page-149/.
Совершенно верно! Мне кажется это отличная идея. Я согласен с Вами.
4. ?? ? ??:??????(??, https://www.kla-ca.com/slotsrank/page-5/ - https://www.kla-ca.com/slotsrank/page-5/ ??,??/????/??? ? ????? ????/??/???? ??? ?? ? ????? ? ????????,??.)??????.
По-моему это очевидно. Советую Вам попробовать поискать в google.com
regardless because, whether you are an investor or a developer, https://karak.asia/ - karak network offers tools and incentives for maximum using technology blockchain.
Я полагаю, что Вы не правы.
{??|??}{??|??}-{?|?? ??|?? ??|?? ??|?? ??/???|?? ??|? ????|? ? ???|?? ??|?}??,{? ?? ?|??? ?/?},? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ?/? ?? ? #file_links["C:\Users\Admin\Desktop\file\gsa+ko+PBNonlinebaccarat.kr681P2URLBB.txt",1,N - {?? ?? ?????|??/??? ???? ?? ? ???. {?/?/??/???/???/??/???}{??|??|????/????}{??/??}???? ????. {??/??}{??/??/??}?{??/??/?}??? ? ??? ??? ?? ?? 9.
demi vie stromectol stromectol approved australia https://studbaywritingvip.com/stromectol/stromectol-south-africa/ - stromectol south africa stromectol prevention side effects stromectol
Весьма ценный ответ
This is a step towards improvement in the case when applications have to issue their tokens with impeccable inflation in the role of remuneration for validators and create a new network of trust, from the https://karak.asia/ - karak network.
Я знаю еще одно решение
4. ?? ? ??:??{?|??}{??|??}(??, #file_links["C:\Users\Admin\Desktop\file\gsa+ko+PBNfreeslot.kr681P2URLBB.txt",1,N - ??,{??|??}{???/??? ? ????}{? ?? ? ????/? ??}{??/??/??}?? ??{? ? ????|?? ? ????|? ? ????|? ??? ??}{?? ??/??/??/??}{??|?|?}??,??.){??/??/??? ??? ??.
Восхитительно
https://metalicassr.com/2025/05/19/page-33/ - https://metalicassr.com/2025/05/19/page-33/ ????????????????????????????????????????????????/?????-????/?????????????????fans.It ????price?????????????????????????
Согласен, очень полезное сообщение
Выберите необходимое вам вино и выложите заказ - профессиональные кависты войдут в контакт с вами, помогут сделать запрос, а в дополнение проконсультируют, https://opensourcebridge.science/wiki/User:XOJKrystle - https://opensourcebridge.science/wiki/User:XOJKrystle если вы ещё затрудняетесь с подбором.
Woah! I'm really digging the template/theme of this blog. It's simple, yet effective. A lot of times it's very hard to get that "perfect balance" between superb usability and appearance. I must say you have done a awesome job with this. Additionally, the blog loads extremely quick for me on Safari. Exceptional Blog!
Замечательно, весьма забавное мнение
When choosing an exchange, compare its commission structure, security, https://orbiter.asia/ - Orbiter fi, and affordable assets.
http://netvode.ru/component/k2/item/2-i-know-where-i-m-going-and-i-know-the-truth.html - http://netvode.ru/component/k2/item/2-i-know-where-i-m-going-and-i-know-the-truth.html, what guarantees the security of personal data after registration foreign standards.
Меня тоже волнует этот вопрос. Подскажите, где я могу найти больше информации по этому вопросу?
pokerdom kz! играйте в слоты от pragmatic play, netent и microgaming, https://travelmai.com/igrayte-v-luchshie-onlayn-kazino-rossii-iz-kazakhstan-vashe-zakonnoe-i-uvlekatelnoe-vremyapreprovozhdenie/ - Pokerdom включая хиты book of dead и starburst.
сморел мне понравилось
{so|with this}, vevelo owners {can|have the right} to vote on {what|, which liquidity funds to support, and the bribe takers can encourage #file_links["C:\Users\Admin\Desktop\file\gsa+en+100kT2benediktrolfovskij519906129URLBB.txt",1,N - {to do|implement} this.
Это интересно. Вы мне не подскажете, где я могу найти больше информации по этому вопросу?
user-friendly interface site more times emphasizes her commitment is to expand the appeal of defi as for beginners, and for enlightened https://strga.pro/ - Stargate bridge participants.
Виртуальное интернет казино на реальные деньги (рубли) Восток Казино создавалось в пределах https://www.apwws1979.org/?q=node/1637537 - https://www.apwws1979.org/?q=node/1637537 крупного проекта.
Могу поискать ссылку на сайт с огромным количеством статей по интересующей Вас теме.
Средства, переведенные на кредитные карточки, обычно поступают на счет с легкостью для центральных регионов страны, https://1979.works/nachnite-igrat-v-onlaynkazino-pokerbet-pryamo-seychas-i-pobezhdayte-v-kazino-kazakhstana/ - Pokerdom Казахстан а на Дальнем Востоке - за одно час.
Вы шутите?
this https://velodrome.pro/ - Velodrome finance project has several advantages.
По моему мнению Вы ошибаетесь. Давайте обсудим. Пишите мне в PM, пообщаемся.
Этот покер-рум предоставляет широкий выбор покерных игр и турниров, которые используются для игроков с наиболее разнообразными уровнями мастерства - от новичков, едва начинающих свой путь что связано с игром, http://www.egasoni.com/v-kazakhstan-pochemu-pokerdom-nevozmozhno-igrat-v-onlaynkazino/ - подробнее до умелых профессионалов.
dry mouth from amoxicillin can i take cefdinir if allergic to amoxicillin https://healtthexxpress.com/ - amoxil for chlamydia amoxicillin when to take methylprednisolone and amoxicillin
topics for illustration essay disadvantages of smartphones essay https://essayservicewrday.com/term-paper-writing-service-reviews.html - term paper writing service reviews poverty and famines an essay on entitlement and deprivation precis example essay
Эта тема просто бесподобна :) , мне очень нравится )))
Изначально монтируется основа для вашей конструкции. Пароизоляция достигается посредством алюминиевой фольги, http://xn--80aaghdc1brekc3alcdm.xn--p1ai/index.php?subaction=userinfo&user=yqizak - http://xn--80aaghdc1brekc3alcdm.xn--p1ai/index.php?subaction=userinfo&user=yqizak специальной пленки или пергамина.
Вопрос интересен, я тоже приму участие в обсуждении. Вместе мы сможем прийти к правильному ответу.
?? ??,? ?????? ?? ?? ????? ??? 10 ?? ????????/????10/10 https://slotsoffortune.kr/ - https://slotsoffortune.kr ?/?????? ?? ????/??? ??? ???? ?? ??? ???? ??? ?????.
Я считаю, что Вы не правы. Могу это доказать.
Чиновники очолюваний президентом Зеленським ліквідували заборону гральних закладів, проте треба відзначити, https://maisfoco.ao/onlajn-kazino-bez-vkladen-z-vivedennjam-groshej-2/ - https://maisfoco.ao/onlajn-kazino-bez-vkladen-z-vivedennjam-groshej-2/ що важлива частина представників галузі все ще знаходиться в «підвішеному» стані.
Улыбнуло спасибо...
?7? https://k-kyoko.com/ - k-kyoko.com "????-??-??"??"????"??????(??23????17?)?
Абсолютно с Вами согласен. В этом что-то есть и это хорошая идея. Я Вас поддерживаю.
Gracze doceniaja prostote uzytkowania oraz intuicyjnosc serwisu. netent-znany z takich gier jak starburst, Gonzo ' s quest, http://rlu.ru/57Du3 - http://rlu.ru/57Du3 oferujac wysokie rtp i dobra/ doskonala grafike.
Присоединяюсь. Я согласен со всем выше сказанным. Можем пообщаться на эту тему.
Tambem adora o jogo em Online playgrounds em Portugal? Existem licencas que garantem que casinos esta em conformidade com regras e leis do pais http://xn--2lwu4a.jp/2023/02/01/astrom259/ - http://xn--2lwu4a.jp/2023/02/01/astrom259/ aqui ele trabalha.
Эта отличная идея придется как раз кстати
в любое время доступно скачать первоначальную сумму ставки, ежели она еще осталась на счете экспресса. кроме того контора постоянно развивается: приложения становятся удобнее, https://slimim.diet/ - slimim.diet появляются необычные виды спортивных развлечений и некоторые игры.
Согласен, это забавная штука
Подивися, https://qwerty.gdn/ - азино777 бонус чи змінився твій баланс. 5. Одна з найбільш щедрих бездепозитних бонусних пропозицій.
ТУТ НЕ СПРАВОЧНАЯ
- Multiple betting limits - suitable as for ordinary players https://888starzz.onl/ - 888starz app, as for high rollers.
Какие трогательные слова :)
Условия, https://50pets.org/ - 50pets.org призовой фонд и правила выполнения индивидуальны в каждый дом ивента. в сети интернет выложено множество рабочих стратегий, которые могут гарантировать выигрыш игроку.
Я думаю, что Вы не правы. Предлагаю это обсудить.
Криптовалюты bitcoin, tron, litecoin, dash, dogecoin, https://zlot.finance/ - zlot.finance monero и другие. Слоты различаются не только лишь оформлением, но и планом игры.
Цветы пришли свежие и яркие, как будто только что с грядки!
<a href=https://www.instagram.com/p/DJBjxvRKhbc/?igsh=MWQ3OW9kcW50eDV1ZQ==>купить цветы в томске</a>
вождь с ноутбуком - просто супер
Within the scope of the procedure, blood, bone marrow, the https://betterlifeautism.com/ - https://betterlifeautism.com/, or umbilical cord blood are used to exit healthy stem structures into the patient's blood.
Не могу сейчас принять участие в дискуссии - нет свободного времени. Буду свободен - обязательно выскажу своё мнение.
Спортивная линия также не разочаровывает: БК Мелбет собрала серьезные и местные турниры https://totallyarugpull.com/ - melbet казино слоты по различным дисциплинам. На фриспины действует ограничение: доступны только для игрового процесса в juicy fruits sunshine rich от barbara bang.
100% клево! Смотрю!
Весь функционал доступен после регистрации. В линии представлены все топовые лиги, включая КХЛ, НХЛ, ЧМ, https://figuredao.app/ - казино леонбет национальные Суперлиги и другое.
молодец
наш платформа 1хбет предлагает получать дополнительные награды за лояльность, https://fableofthedragon.com/ - казино 1xbet чтобы нужный момент иметь возможность для увеличения длительности ставок. чтобы заниматься в 1xbet uz com вход на страницу, вам надо будет вписать логин плюс пароль.
Может быть
эти преимущества делают iphone привлекательным выбором https://saumalkol.com/forum/%D1%80%D0%B0%D0%B7%D0%BD%D0%BE%D0%B5-1/9711-%D0%BA%D1%83%D0%BF%D0%B8%D1%82%D1%8C-iphone.html - https://saumalkol.com/forum/%D1%80%D0%B0%D0%B7%D0%BD%D0%BE%D0%B5-1/9711-%D0%BA%D1%83%D0%BF%D0%B8%D1%82%D1%8C-iphone.html для всех пользователей. Стоимость Айфона отражает баланс между высоким качеством и передовой технологией.
Присоединяюсь. Я согласен со всем выше сказанным. Можем пообщаться на эту тему.
Возможно сочетание нескольких стилей в https://www.metooo.io/e/palubnaya-doska - https://www.metooo.io/e/palubnaya-doska одной квартире. дизайн – это комплекс разнообразных элементов декора и мебели, которые создают гармоничный ансамбль.
<a href=https://planbet.org/>русское порно со зрелыми</a>
это самое лутшее что я видел
??????? 888 ????? ???? ??? ?????? ? {??????|?????? ??? ??????} ? {???????|???????} {?????????|???????} ?? {????|????} {?????|?????} {???? ?????|?????}. {????|????} {????|???/ ????} ??? {????????? ????????|#file_links["C:\Users\Admin\Desktop\file\gsa+ar+seomaster100k200k300k400k2705252URLBB.txt",1,N - , ? {????|????????|????} ??? {??? ?????? ????|??????} ? {??? ????????/????????|????????} {?????|?????}.
Вход на <a href=https://i2kra.cc>кракен даркнет сайт</a> через TOR доступен через <a href=https://i2kra.cc>кракен телеграмм</a> i2kra.cc. Здесь всегда <a href=https://i2kra.cc>кракен сайт форум</a>, проверенные продавцы и стабильные магазины. Безопасный доступ в <a href=https://i2kra.cc>кракен только через тор</a> без ограничений.
Кракен тор сайт – как зайти на маркетплейс сегодня |
<a href=https://i2kra.cc>https://i2kra.cc</a>
просто улет
??????? ??????? (???? ??????? ???????? ??????????) ??? ?????? ??????: ???? ?????? 1 ? ???? ??????? ????? ? ?????? ??????https://888starz-arabs.com/ - ????? 888starz ???????
Hi! I could have sworn I've been to this blog before but after looking at many of the articles I realized it's new to me. Regardless, I'm definitely happy I came across it and I'll be book-marking it and checking back regularly!
Вы допускаете ошибку. Давайте обсудим. Пишите мне в PM.
{as|in the role of} an example of such a {situation|difficulties|problems|difficulties}, #file_links["C:\Users\Admin\Desktop\file\gsa+en+Georgiy5k10k20k40k2805251URLBB.txt",1,N - can be cited, {one|just one|only} of {such|these|similar} approaches {to achieve|achieve} cardiomyocyte differentiation is {use|application|creation|release of chemical activin A {also|and} growth factor BMP-4.
Пусть будет по-вашему. Делайте, как хотите.
Nature. 442 (7104): https://TherapyforAutisminGermany.com/ - https://TherapyforAutisminGermany.com/ 823-6. Bibliographic code:2006natur.442..823a. the person with her 1st type pancreatic beta cells that produce insulin lose their function.
Да не может быть!
Recovery from injury often can feel like a long winding access to a state of health, which is based on https://autismtreatmentRomania.com/ - https://autismtreatmentRomania.com.
наконец в хорошем качестве!!!
with this https://StemCellTherapyInRomania.com/ - https://StemCellTherapyInRomania.com, they identified a specific combination of blood molecules, including most of such participate in inflammation and well-being of the brain that changed after the stroke, however were restored to tangible level consequence of therapy.
Link exchange is nothing else except it is only placing the other person's website link on your page at suitable place and other person will also do similar in favor of you.
я тоже!!!
information about the company: Laurencin announces that he is the founder of soft tissue regeneration, healing orthopaedic technologies and hot bone inc., https://TherapyAutismRomania.com/ - https://TherapyAutismRomania.com and scientific co-founder of natural polymer devices inc. Mazzocca announces that he receives research support from arthrex and will an arthrex consultant.
Одному богу известно!
https://StemCellCostEstimator.com/ - https://StemCellCostEstimator.com/ is already available for treating multiple pathologies and conditions.
Everyone loves what you guys tend to be up too. Such clever work and coverage! Keep up the amazing works guys I've you guys to my blogroll.
Я против.
currently The Food and Drug Administration (FDA) has not approved the use of https://newtreatmentupdate.com/ - https://newtreatmentupdate.com of lung diseases such as chronic obstructive pulmonary disease (COPD).
Извиняюсь, но это не совсем то, что мне нужно. Есть другие варианты?
In past year, the Japanese Ministry of Health, Work and Social https://StemCellMarketPrice.com/ - https://StemCellMarketPrice.com/ be the final objective for firms.
дето тоже читал
Mesenchymal stem cells/cell bodies have been found throughout the body, even in the muscles, skin, intestines, during treatment with https://StemCellsBudget.com/ - https://StemCellsBudget.com, and even in teeth.
Excellent way of explaining, and pleasant post to take information on the topic of my presentation subject, which i am going to convey in school.
Извините за то, что вмешиваюсь… Я разбираюсь в этом вопросе. Можно обсудить.
Стельовий профіль зовні трохи відрізняється від, скажімо, стійкового тим, http://keegan.tremor-tt.com/?page_id=18&unapproved=80033&moderation-hash=92beaa21a4014c4b7015f2481a518ab6 - http://keegan.tremor-tt.com/?page_id=18&unapproved=80033&moderation-hash=92beaa21a4014c4b7015f2481a518ab6 що такого краю загнуті всередину.
Что-то у меня личные сообщения не отправляются, ошибка....
for users https://slopecomb0.edublogs.org/2021/05/29/the-wonder-of-selling-scrap-metals/ - https://slopecomb0.edublogs.org/2021/05/29/the-wonder-of-selling-scrap-metals/ 888starz provides a special apk-video, which easily try to find directly from the official resource.
Вы не правы. Могу это доказать. Пишите мне в PM, обсудим.
ТОП составляется экспертами. Используя опыт, они анализируют каждую площадку, выделяют достоинства и минусы и решают, https://heyjinni.com/read-blog/203114 - https://heyjinni.com/read-blog/203114 добавлять ли ее в рейтинг.
Комментарий Хотим выразить благодарность сервисному центру и особенно поблагодарить мастера Панова Антона https://zapchasti-remont.ru/shop/kolesa2/
Отличный, отзывчивый, культурный а самое главное точен в поломке, и аккуратен во времени как прибытия так и ремонта! Спасибо большое https://zapchasti-remont.ru/shop/zapchasti_k_kitayskim_dvigatelyam/
Я извиняюсь, но, по-моему, Вы не правы. Я уверен. Пишите мне в PM.
in addition, http://kinedusport.re/portfolio-view/gallery-format/ - http://kinedusport.re/portfolio-view/gallery-format/ trading snapshots and/or videos offered on our platform, are purely promotional in nature even in them are taking part professional actors.
Its like you learn my mind! Youu appear to grrasp so much about this, such
as you wrote tthe ebook in it or something.
I think that you simply could do with a few % to power the message home a little bit, but instead of that, this is excellent blog.
A fantastic read. I will certainly be back. http://boyarka-inform.com/
Совершенно верно! Это хорошая идея. Я Вас поддерживаю.
Congratulations, https://stargate-finance.co/ - stargate finance, you are from now on the owner of uni! The stg token works in role of coordinating token, and enables users participate in courses on extraction of liquidity and betting thanks to the protocol, receiving reward for purchased contribution to network.
Какая интересная фраза
On March 5, at 19:00, https://stargate-finance.app/ - stargate finance will temporarily suspend manipulations for depositing and withdrawing money in money erc20 stg.
Это исключительно ваше мнение
at the dawn of the https://xn--b1adqkjc0a.xn--p1ai/stroitelstvo/inzhenernye-sistemy/elektrika/elektrosnabzhenie/item/112-kak-podklyuchit-dom-ili-uchastok-k-elektroseti.html - https://xn--b1adqkjc0a.xn--p1ai/stroitelstvo/inzhenernye-sistemy/elektrika/elektrosnabzhenie/item/112-kak-podklyuchit-dom-ili-uchastok-k-elektroseti.html on sports provides odds on that whether a team will win the championship.
Без разговоров!
in it also there are immune cells (monocytes and macrophages), fibroblasts, pericytes, endothelial progenitor cells, the https://StemCellTreatmentCost.com/ - https://StemCellTreatmentCost.com, and other useful cells that help the body repair itself.
Бутафория выходит
На какой период мне необходима медицинская поддержка для поездок? также, https://arthaproperty.id/medicinskaja-strahovka-dlja-studentov-7/ - https://arthaproperty.id/medicinskaja-strahovka-dlja-studentov-7/ страховка должна распространяться на все страны Шенгенского соглашения (не только лишь Германию).
Я думаю, Вы придёте к правильному решению. Не отчаивайтесь.
Productos quimicos mas inocuos producidos por usando https://blog.ko31.com/201312/global-cafe/ - https://blog.ko31.com/201312/global-cafe/ y medio ambiente. uno de los tipos de arte ligero y flexible.
КРАСАВЧЕГ СПАСИБО...
in addition, platform regularly replenishes own collection with new games, https://www.egalitepareducation.org/the-ultimate-guide-to-thepokies-discovering-the/ - https://www.egalitepareducation.org/the-ultimate-guide-to-thepokies-discovering-the/ guarantees its consumers always a fun time.
<a href=https://planbet.org/>sleepygimp porno comics</a>
Нашел сайт с интересующей Вас вопросом.
In November 2018, Rick Staples previously submitted https://product01.netpro.co.kr:443/bbs/board.php?bo_table=free&wr_id=36 - https://product01.netpro.co.kr:443/bbs/board.php?bo_table=free&wr_id=36 Bill No. 1 to the House of Representatives, and it successfully passed through both state legislatures.
Это не имеет аналогов?
On the other hand, if your experience was unsatisfactory, it is better to stay away https://inet.tiu.edu.iq/2025/06/the-exciting-world-of-thepokies-discover-the/ - https://inet.tiu.edu.iq/2025/06/the-exciting-world-of-thepokies-discover-the/ thepokies. beginners members receive a no deposit bonus in the amount of ten greenbacks and one hundred percent % bonus on match in amount up to 500 dollars.
да дофига он стоет...
casino based on applications have revolutionized the online industry by combining the convenience of mobile materials, with excitement gambling games gambling table, and https://rhodelhi.com/thepokies57/the-ultimate-guide-to-online-casino-games-and/ - https://rhodelhi.com/thepokies57/the-ultimate-guide-to-online-casino-games-and/ make it easier for visitors the opportunity to enjoy favorite gaming entertainment anytime even in any other place.
?????????????"???"?????"???????????????????????????"??????????????????????????"?? http://sacrafts.ca/index.php?option=com_k2&view=item&id=3 - http://sacrafts.ca/index.php?option=com_k2&view=item&id=3,???????????????????????????????????/7??
Предлагаю Вам попробовать поискать в google.com, и Вы найдёте там все ответы.
Integration with DEFI: users can replenish pools with liquidity, receive rewards in the form stable coins, https://stargate-finance.org/ - stargate finance and collect LP tokens to receive additional rewards similar stg tokens.
Полезная фраза
the mobile version, without any compromises, has each of the functions of version: for laptop, https://bioquinor.com/the-thrills-of-online-casino-discover-the-world-of/ - https://bioquinor.com/the-thrills-of-online-casino-discover-the-world-of/ provides smooth and exciting game in road.
Вы ошибаетесь. Давайте обсудим это. Пишите мне в PM.
lowest deposit in amount of 30 Australian dollars is a real game. Skycrown has modern and standing to use website casino. Set your win/loss limits in advance at https://www.gracevilla.us/thepokies20/the-ultimate-guide-to-online-casino-uncovering-the/ - https://www.gracevilla.us/thepokies20/the-ultimate-guide-to-online-casino-uncovering-the/ and stick to them!
НАСТРОЕНИЕ ПРОСТО ПОДРЫВАЕ В ПРЯМОМ СМЫСЛЕ СЛОВА
during audit 2, based on the results of the audit, 3 problems of low level severity, 1 https://debridge-finance.foundation/ - debridge finance exchange of medium degree severity and 1 problem of high were identified degree of severity.
В этом что-то есть. Большое спасибо за объяснение, теперь я буду знать.
people that are good understand poker can read their competitors, and in addition evaluate opportunities and https://www.tbp1.ac.th/discover-the-thrills-of-online-casino-australia/ - https://www.tbp1.ac.th/discover-the-thrills-of-online-casino-australia/ makes smart decisions.
СОГЛАСЕН
Игрокам нужно активно делать ставки http://temva.si/clients/client-1/ - http://temva.si/clients/client-1/ в акционных слотах. компания предоставляет не только общедоступные бонусы.
Я думаю, что Вы не правы. Я уверен. Предлагаю это обсудить.
chancen/Chancen https://rmvinfo.in/billybets-deutschland-online-casino-ihr-tor-zur-2/ - https://rmvinfo.in/billybets-deutschland-online-casino-ihr-tor-zur-2/ ein Billybet, das als einer der besten von optimale im Handel mit einer Quote von bis zu 99,60% gilt.
? ?????? 888 ????? ??????? ?? ???? ???? ? ???? ????? ? ?????? ???? ?????? ??? ?????? ???????????? ? ????? 888 ????? https://lokneta.in/news/3903/ - https://lokneta.in/news/3903/ ????? ????? ???????? ? ?????? ?????????.
Hurrah! After all I got a web site from where I know how to genuinely get useful information regarding my study and knowledge.
да уж совсем не впечатлили.
this possibility of integration recognized as significant advantage for projects aimed at application versatile defi ecosystems supported by https://debridge-finance.us/ - debridge finance.
2. ???? ?????? ??????? ?????? ?????????? ?? http://www.sofahelden.at/index/redirect/index/url/https://888starz-arabs.com/ - http://www.sofahelden.at/index/redirect/index/url/https://888starz-arabs.com/ ??????? ??? 888 ?????. ?????????? ?????? ??????? ???????? ??? ??? ???????? ??????? ? ?????? ?????????? ? ?????? ? ?????? ??? ?????? ?? ????? ?? ??????? ?????????.
Эт 1000000000 пудов))))))))
если потребуется его необходимо отбить, http://www.vloeimans.com/index.php?title=User:JettaTeece097 - http://www.vloeimans.com/index.php?title=User:JettaTeece097 только после всего этого можно выводить на персональный счет.
Да, действительно. Так бывает. Давайте обсудим этот вопрос.
без разрешительных документов https://xn--e1amkfcme6a.xn--p1ai/ - https://xn--e1amkfcme6a.xn--p1ai/ не позволит себе принимать игроков из лечебных стран, обрабатывать платежи и отдавать выигрыши.
<a href="https://prodache.ru">prodache</a>
Я считаю, что Вы не правы. Я уверен. Могу это доказать.
website provides rich choice of markets - from the largest gaming events to esports and in parallel political incidents, therefore on paripesa it is always to view https://icrrd.com/blog-article/3698/install-the-paripesa-app-and-get-access-to-many-games-anytime - paripesa app odds.
<a href=https://planbet.org/>sex porno indian</a>
Вы не эксперт?
Тому не можна легковажити згубним впливом цієї літератури. Тут позиція new age цілком збігається з істинною метою створених структур ООН, https://tyzhden.ua/iak-kupyty-odnokimnatnu-kvartyru-v-kyievi-porady-dlia-pokuptsiv/ - https://tyzhden.ua/iak-kupyty-odnokimnatnu-kvartyru-v-kyievi-porady-dlia-pokuptsiv/ НАТО і пр..
Я тебе это припомню! Я с тобой рассчитаюсь!
The deexplorer program is a block analyzer built into the debridge blockchain (see the image of https://debridge-finance.org/ - debridge finance exchange below).
I am regular reader, how are you everybody? This paragraph posted at this website is truly good.
Stem cell company from New Jersey is engaged in stem cell treatment of pathologies such as osteoarthritis, tendonitis, sports injuries, the https://surfinghell57.edublogs.org/2021/05/26/how-to-buy-cheap-stand-up-paddle-boards/ - https://surfinghell57.edublogs.org/2021/05/26/how-to-buy-cheap-stand-up-paddle-boards/ and something more.
Stem cell therapy (SC) is the use of living structures as a therapeutic method for the treatment of a number of troubles with health , related to the https://tastepath5.edublogs.org/2021/05/07/4-reasons-why-your-company-needs-call-tracking-software/ - https://tastepath5.edublogs.org/2021/05/07/4-reasons-why-your-company-needs-call-tracking-software/.
Извините, что не могу сейчас поучаствовать в дискуссии - очень занят. Вернусь - обязательно выскажу своё мнение по этому вопросу.
The bonus amount is 500 dollars, in https://thepokies177.net/ - thepokies.net the total wagering amount will be approximately 20 000 dollars. when you are inspired developed a modern, or find all casual options: blackjack, roulette and Baccarat.
Это мне скучно.
Orbiter finance's decentralization, cost-effective transfers, #file_links["C:\Users\Admin\Desktop\file\gsa+en+T100k200k300k400kbenediktrolf2705254URLBB.txt",1,N - , and {almost|absolutely} instant execution {have made it {an excellent|suitable} {solution|option} for combining all chains of operations.
exists variety different types of https://cattlewaste7.edublogs.org/2021/06/29/bob-type-hairbob-haircuts-with-bangsquick-bob-fashionmovie-star-bob-haircuts/ - https://cattlewaste7.edublogs.org/2021/06/29/bob-type-hairbob-haircuts-with-bangsquick-bob-fashionmovie-star-bob-haircuts/, and variety types of stem cell therapy.
По моему мнению Вы не правы. Пишите мне в PM, поговорим.
How do I verify account at this https://thepokies20.net/ - thepokies net? which virtual casino is the best in Australia?
Просто, под столом
This commitment to innovation creates a dynamic financial environment where private fops have the opportunity to optimize their investments and actively participate over time https://orbiter-finance.app/ - orbiter finance bridge finance.
<a href=https://coldbet.in/>fandel tales porno</a>
Заказала нестандартный букет — флористы сделали его просто потрясающим!
<a href=https://www.instagram.com/p/DI5huw_KR-y/?igsh=MWt6MTdpYWlja2I4eA==>букет невесты</a>
Абсолютно с Вами согласен. В этом что-то есть и мне кажется это отличная мысль. Полностью с Вами соглашусь.
если необходимо, http://www.eskisehirgocukduzeltme.com/index.php?subaction=userinfo&user=etobez - http://www.eskisehirgocukduzeltme.com/index.php?subaction=userinfo&user=etobez вы можете прибегнуть к услугой по прибытии физических товаров в какую угодно точку России.
Извиняюсь, ничем не могу помочь. Я думаю, Вы найдёте верное решение. Не отчаивайтесь.
1. The sender must provide the relevant transaction on the source network for https://orbiter-finance.io/ - orbiter finance bridge within the framework of the spv contract.
Я считаю, что Вы не правы. Я уверен. Могу это доказать.
Первые результаты наличествуют в 2003 году на крысах, в 2010 году исследователи могут вырастить структуры зуба на каркасе, даже у человека-добровольца, https://valentina-therapist.iamarrows.com/all-on-4-6-v-minske-ceny-vosstanovlenie-profilaktika - https://valentina-therapist.iamarrows.com/all-on-4-6-v-minske-ceny-vosstanovlenie-profilaktika в нынешних реалиях в экспериментах на животных учёные выращивают нормальные зубы взамен удалённых.
Аффтар - аццкий сотона !! Пеши исчо !!
в связи с чем выбирают лицензированные http://paladiny.ru/forummess.php?TopicID=30989 - http://paladiny.ru/forummess.php?TopicID=30989? Понимание, где оптимально всего рисковать финансами, приобретается с опытом. все виды деятельность, несущая в себе деньгами и самочувствием людей, требует лицензирования.
necessary make long-term studies to obtain the long-term efficiency and conditions related in the process of applying http://keramogranit.univerdom.ru - http://keramogranit.univerdom.ru.
Я думаю, что Вы ошибаетесь. Предлагаю это обсудить. Пишите мне в PM, поговорим.
Cost-effectiveness: orbiter finance's tariffs are very competitive comparatively with similar platforms. 4. Can newbies use https://orbiter-finance.us/ - orbiter finance?
<a href=https://planbet.org/>porno lesbi moms</a>
<a href=https://dzen.ru/a/aDf-blaRVWbg7Kac>социальный онлайн-портал "Жалоба.Онлайн"</a>
Unproven stem cell therapy is usually underway separately and the same scheme: cells are removed patients, and at the end are inserted back into the reverse part of the patient's body within as part of https://depasse-chauffage.be/tail-doner-short-ribs-meatball-jowl-pork-loin-biltong/ - https://depasse-chauffage.be/tail-doner-short-ribs-meatball-jowl-pork-loin-biltong/.
Это мне не совсем подходит. Может, есть ещё варианты?
expand number of bonuses. gambling houses offer these offers as discounts on deposit and free rotations. proceeding from various factors, the https://thepokies60.net/ - https://thepokies60.net Playamo Casino remains our main recommendation for users, who are looking for the most reliable Internet casinos in Australia immediately.
Hello! I just want to gie you a big thumbs up for the
excellent info you've got here on this post. I will be returning to your website for more soon. http://Boyarka-Inform.com/
Я знаю еще одно решение
So, in http://suenderleins_gb-bilder.carelesswhisper.de/untitled2.html - http://suenderleins_gb-bilder.carelesswhisper.de/untitled2.html, the proposed banking methods should provide for a low minimum amount of first deposit and instant transaction. fast and simple replenishment and withdrawal of funds.
information and tips for returning to work, including contact with other visitors at work, your all rights, http://hidratarvicia.com.br/2019/12/17/doutrina-espirita-sem-segredos-evelyn-freire-de-carvalho/ - http://hidratarvicia.com.br/2019/12/17/doutrina-espirita-sem-segredos-evelyn-freire-de-carvalho/ and decision work problems.
хоошь!
An exhibition of experimental ceramic works created by Jack Anselmi, Suzanne Atkinson, Belinda Briggs, Ellie Knight from https://www.voka.at/shop - painting for buy and Lyn Thorpe during the internship of ceramicist Kirsten Perry in 2022.
Прошу прощения, это мне не подходит. Кто еще, что может подсказать?
http://90plink.live/truc-tiep-tran-dau-heidenheimer-vs-borussia-monchengladbach-2413062/ - http://90plink.live/truc-tiep-tran-dau-heidenheimer-vs-borussia-monchengladbach-2413062/,?????????????????????????/??????? ?????????????:??/????????????????
<a href=https://copicsketch.ru/>Дневник скетчера</a>
Excellent article. I absolutely appreciate this website. Continue the good work!
Абсолютно с Вами согласен. В этом что-то есть и идея хорошая, согласен с Вами.
Крупные площадки вкладываются не только в рекламу, https://kra33atcc.cc/ - реклама кракена скачать сколько в развитие представительств в обычном интернете. в крайнем участвуют различные хакерские объединения, зачастую анонимные, которые нередко гонятся не в уничтожением конкретного маркетплейса по желанию его противника, а преследуют цель уничтожить российский даркнет-рынок в принципе - из патриотических убеждений.
We absolutely love your blog and find many of your post's to be what precisely I'm looking for. Would you offer guest writers to write content for yourself? I wouldn't mind creating a post or elaborating on a lot of the subjects you write in relation to here. Again, awesome website!
Бутафория выходит, какая то
Simplicity of smart contracts. Are you coming from the United States? 4. The liquidity pool provides harmony between the https://crva.us/ - curve defi in US dollars and tusd.
<a href=https://uranian.ru/>teens porno anal</a>
В этом что-то есть. Раньше я думал иначе, большое спасибо за информацию.
similar Servicio esta disponible de lunes a domingo de 8 resplandor a 12 P. m. en http://nysca.net/forums/users/berenicecostas9/ - http://nysca.net/forums/users/berenicecostas9/.
Ждём с нетерпением.
our service remains one of the leading in Canada, where presented more than 1000 games for real money, and also new slot machines automatic machines and proven tabletop events, and also real https://www.simpleplanes.com/Forums/View/1905153/Something-New - https://www.simpleplanes.com/Forums/View/1905153/Something-New with real dealers.
На мой взгляд. Ваше мнение ошибочно.
KEPLR is a tool for the decentralized https://kplrv.us/ - keplr extension. KEPLR is the most important toolkit for maximizing profits in decentralized finance.
What's Happening i'm new to this, I stumbled upon this I have discovered It absolutely helpful and it has aided me out loads. I hope to give a contribution & assist other users like its helped me. Great job.
Мда,
Житлові комплекси бізнес-класу відрізняються надзвичайно розвиненою інфраструктурою. Вибирайте квартиру на сторінках сайту і приходьте на перегляд, https://maou7school.ru/forums/users/jovitabuford/edit/?updated=true/users/jovitabuford/ - https://maou7school.ru/forums/users/jovitabuford/edit/?updated=true/users/jovitabuford/ зв'язавшись за номером в описі.
мрачно
These are far not any coolest https://advokat-aliev51.ru/index.php/component/k2/item/34 - https://advokat-aliev51.ru/index.php/component/k2/item/34 games: maybe, you also want to try what-that that is slightly different from the main casino games.
Полностью разделяю Ваше мнение. Я думаю, что это хорошая идея.
??{??|??|??|??|??|??|??|??|??|??|??|??|??|??|??|??|??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??/??#file_links["C:\Users\Admin\Desktop\file\gsa+ko+Phoenix5k10k20k40k693P2URLBB.txt",1,N - ??? ???? ???? ??? ????? ??????. {?/??? ???}??{??/??/??}?{?/???}{?/?? ? ? ????}{???/?? ??}{??/??}??.
Я конечно понимаю, что каждый хочет пофлудить!
these games lure visitors of a different type, those who enjoy the ease and social aspects of these less competitive, however no less exciting https://ledstrip-kopen.nl/niet-gecategoriseerd/rgb-neon-led-flex-maxi-rond-5-meter-losse-strip-2/ - https://ledstrip-kopen.nl/niet-gecategoriseerd/rgb-neon-led-flex-maxi-rond-5-meter-losse-strip-2/.
мне парочку
despite the fact that personally have is able not have a condition requiring immediate stem cell treatment, https://xemtin.mms7.net/2023/01/12/kinh-nghiem-thu-hep-vung-kin-va-gia-thu-hep-vung-kin-tot-nhat-tai-da-nang/ - https://xemtin.mms7.net/2023/01/12/kinh-nghiem-thu-hep-vung-kin-va-gia-thu-hep-vung-kin-tot-nhat-tai-da-nang/ rationally plan for further.
<a href=https://planbet.org/>porno zoo animal</a>
Замечательно, это весьма ценная фраза
these difficulties must be solved if stem cell treatment is widely available and provides fair solutions in area healthcare for any, but not limited to https://infibuilt.com/infibuilt-launches-new-project-in-jaipur/ - https://infibuilt.com/infibuilt-launches-new-project-in-jaipur/ of wealthier strata society.
This information is invaluable. How can I find out more?
I am genuinely thankful to the holder of this website who has shared this wonderful post at here.
Браво, ваша мысль просто отличная
However, the effect of https://cameradb.review/wiki/User:CliffBirchell - https://cameradb.review/wiki/User:CliffBirchell on heart still at all clarified, and study of primary sources continues.
<a href=https://coldbet.in/>porno satina</a>
does amoxicillin give you diarrhea amoxicillin 100 mg dosage https://healtthexxpress.com/ - adult amoxicillin dose delayed rash from amoxicillin can you take 800 mg ibuprofen with amoxicillin
Да, действительно. И я с этим столкнулся.
Stem cells are present in embryos and cells of an adult organism. in the end The Food and Drug Administration (FDA) has approved http://ramen-zukan.com/?p=1 - http://ramen-zukan.com/?p=1 only for the treatment of some types of cancer and conditions that involve blood and immune system.
Incredible! This blog looks just like my old one! It's on a completely different topic but it has pretty much the same layout and design. Superb choice of colors!
Сестра была в полном восторге - лучший сюрприз!
<a href=http://www.amicimusicasavigliano.org/home-page/>заказ цветов томск</a>
Very descriptive blog, I enjoyed that a lot. Will there be a part 2?
<a href=https://spinbetter.one/ru/>no1sy girl porno</a>
Лучший сервис по доставке цветов в городе!
<a href=https://cvetokispanskie.ru/>букет невесты томск</a>
А что в результате..
https://sell.com.my/en/user/profile/LashondaGil - https://sell.com.my/en/user/profile/LashondaGil may be repeated instances in when the improvement is not observed.
Hello There. I discovered your weblog using msn. This is a really well written article. I will make sure to bookmark it and return to learn more of your helpful information. Thanks for the post. I'll definitely return.
<a href=https://uranian.ru/>porno frech</a>
Курьер был очень вежлив, доставил аккуратно и с улыбкой.
<a href=https://cvetokispanskie.ru/>заказать цветы с доставкой в томске</a>
Извиняюсь, но это мне не совсем подходит.
Мы одни из немногих, http://2007.pp.net.ua/forum/17-2943-1 - http://2007.pp.net.ua/forum/17-2943-1 где реально оформить онлайн микрозайм на подержанную технику apple. поэтому чип получил гораздо больше транзисторов и трудится еще эффективнее.
Experience the <a href=delsrest.com>chicken road game demo</a> today!
Да, действительно. Так бывает.
as the popularity of internet excitement in United States continues to grow and appears more and more more and more often casinos, https://bokerah.com/discover-the-magic-of-pelican-casino-your-ultimate/ - https://bokerah.com/discover-the-magic-of-pelican-casino-your-ultimate/ becomes becoming harder to find the best internet gambling house for real funds.
Могу предложить Вам посетить сайт, с огромным количеством информации по интересующей Вас теме.
unpaid spins are often tied to certain one-armed bandits in New York. Bonuses are like the icing on the cake of an https://schoolofentrepreneurship.co/directory/the-exciting-world-of-online-gaming-casino-cz/ - https://schoolofentrepreneurship.co/directory/the-exciting-world-of-online-gaming-casino-cz/.
Жаль, что сейчас не могу высказаться - опаздываю на встречу. Но освобожусь - обязательно напишу что я думаю по этому вопросу.
Use the parimatch BD app for hosting betting on your favorite sporting events, gambling games at wirthcasino, withdrawal winnings, https://parimatch-download.app/ - download parimatch app and the like.
<a href=https://planbet.org/>sex porno cosplay</a>
ДА, вариант хороший
we offer a 30-day money. The URL of your passhub will remain in selected wwpass account in passhub http://designmalleshop.fingeroom.com/?p=49805 - http://designmalleshop.fingeroom.com/?p=49805 days.
Вы не правы. Могу это доказать. Пишите мне в PM, поговорим.
While the rocket is climbing into space, at https://ventsmagazine.com/2024/10/31/aviator-game-a-comprehensive-guide-to-deposits-and-withdrawals-of-winnings/ - https://ventsmagazine.com/2024/10/31/aviator-game-a-comprehensive-guide-to-deposits-and-withdrawals-of-winnings/ your goal is to withdraw money before, how it disappears among stars.
Легче сказать, чем сделать.
we are able use this to create "pseudo-alphabets" that resemble ordinary text in ascii format, but have certain differences - for example, they are highlighted in bold in font or italics, the https://typetype.org/custom-fonts/ - custom made font text either are even inverted!
I was recommended this web site by my cousin. I am not sure whether this post is written by him as no one else know such detailed about my trouble. You are amazing! Thanks!
In fact when someone doesn't be aware of after that its up to other users that they will assist, so here it occurs.
Hello to all, how is everything, I think every one is getting more from this web page, and your views are pleasant designed for new people.
This design is spectacular! You certainly know how to keep a reader entertained. Between your wit and your videos, I was almost moved to start my own blog (well, almost...HaHa!) Excellent job. I really loved what you had to say, and more than that, how you presented it. Too cool!
<a href=https://spin-better.net/>porno teens group</a>
<a href=https://spin-better.net/>porno pics milf</a>
Hello, Neat post. There's a problem with your site in internet explorer, could check this? IE nonetheless is the marketplace leader and a good portion of people will leave out your great writing because of this problem.
Флористы – настоящие профессионалы! Букет выше всех похвал.
<a href=https://cvetokispanskie.ru/>заказать цветы томск</a>
Great post. I was checking continuously this blog and I'm impressed! Extremely helpful info specially the last part :) I care for such information a lot. I was seeking this certain info for a very long time. Thank you and best of luck.
I am in fact glad to glance at this blog posts which carries lots of useful facts, thanks for providing such data.
Useful info. Fortunate me I found your website accidentally, and I'm shocked why this twist of fate didn't happened earlier! I bookmarked it.
Do you mind if I quote a few of your posts as long as I provide credit and sources back to your website? My website is in the exact same niche as yours and my users would definitely benefit from a lot of the information you present here. Please let me know if this okay with you. Cheers!
Stunning quest there. What occurred after? Take care!
I am not sure where you are getting your information, but great topic. I needs to spend some time learning much more or understanding more. Thanks for wonderful information I was looking for this information for my mission.
Hurrah! At last I got a website from where I be able to actually take valuable data concerning my study and knowledge.
Hi! I could have sworn I've been to your blog before but after browsing through some of the posts I realized it's new to me. Anyhow, I'm definitely happy I found it and I'll be book-marking it and checking back often!
<a href=https://spin-better.net/>porno teens group</a>
<a href=https://spin-better.net/>porno pics milf</a>
I've been browsing online more than 4 hours today, yet I never found any interesting article like yours. It is pretty worth enough for me. In my view, if all web owners and bloggers made good content as you did, the web will be much more useful than ever before.
<a href=https://planbet.org/>porno lesbi moms</a>
What i do not understood is in fact how you are no longer really a lot more neatly-preferred than you might be now. You are so intelligent. You already know thus considerably with regards to this subject, produced me individually imagine it from so many numerous angles. Its like men and women are not involved until it's one thing to accomplish with Girl gaga! Your personal stuffs great. Always deal with it up!
This is a topic that is near to my heart... Many thanks! Exactly where are your contact details though?
Удобство индивидуального заказа римских штор
почему римские шторы в салоне лучше чем покупать готовые https://rimskie-salon-vs-gotovye.ru/ - почему римские шторы в салоне лучше чем покупать готовые .
Извините за то, что вмешиваюсь… У меня похожая ситуация. Готов помочь.
в категории горячие новинки вы сможете отыскать в наибольшей степени свежие компьютерные видеоигры, появившиеся совсем недавно и данный случай даже не игры - настоящие, так уж и много шедевры, но современные игры, http://nkt.net.ua/torrent-mass/skachat-kvesty-cherez-torrent/ - http://nkt.net.ua/torrent-mass/skachat-kvesty-cherez-torrent/ по меньшей мере.
Меня тоже волнует этот вопрос. Подскажите, где я могу об этом прочитать?
во вторую, https://thaipark.ru/thelastgame/skachat-igry-prikljuchenija-cherez-torrent/ - https://thaipark.ru/thelastgame/skachat-igry-prikljuchenija-cherez-torrent/ теперь основной упор в приключении может быть произведен только к эксплуатации. не стоит ждать игровой проект ранее указанного гг. нетрудно набраться терпения.
Говорить по этому вопросу можно долго.
I most liked the version with several hands at the betonline https://netrixentertainment.com/jeton-a-comprehensive-guide-to-digital-payments/ - https://netrixentertainment.com/jeton-a-comprehensive-guide-to-digital-payments/. Loss limits: A string of losses sucks, at the same time you get a great chance to reduce losses by setting limits on losses.
Советую Вам посмотреть сайт, на котором есть много информации по этому вопросу.
все они общедоступны и опробованы на объект отсутствия вирусов также на стопроцентную работоспособность. Сайт byrutor - это игры не требуется sms и http://new.iskcondesiretree.com/skachat-igry-na-russkom-jazyke/ - http://new.iskcondesiretree.com/skachat-igry-na-russkom-jazyke/ регистрации.
Браво, какие слова..., великолепная мысль
ваша удача в интимных шалостях социального казино абсолютно не влияет на потенциальный успех при игре http://santehcom.ru/export/robots/dolgi_po_kreditu_poprobuyte_sekonomity_na_kommunalke.html - http://santehcom.ru/export/robots/dolgi_po_kreditu_poprobuyte_sekonomity_na_kommunalke.html на реальные средства.
It's awesome designed for me to have a website, which is valuable in favor of my knowledge. thanks admin
Это — невозможно.
??????/??,??/????/?? ??????/??/?????/??,??/??/????? ???????? ??? ??. 3. ?? ????/????/???/???-https://www.ageseriate.it/1xbet-12/ - https://www.ageseriate.it/1xbet-12/ ??????/??? ? ? ??????? ???.
Абсолютно с Вами согласен. В этом что-то есть и это хорошая идея. Я Вас поддерживаю.
Warto, https://www.thataiblog.com/members/tobiasz/ - https://www.thataiblog.com/members/tobiasz/ ze hazardzista podasz swoje dane uwierzytelniajace dane i czesciowe osobiste dane. wiesz czy wiesz, ze w online kasyna zagladaja ponad 3 miliony Polakow?
Hi friends, how is the whole thing, and what you desire to say concerning this paragraph, in my view its truly awesome in favor of me.
Браво, какое отличное сообщение
so/so/so,evenwhenthis iswill betransferedtothissameday,iteasilycan lostifdo notwill be ableconfirmthe party thatshouldbe verified. ???????????? https://www.re-cereal.com/1xbet-33/ - https://www.re-cereal.com/1xbet-33/ ????????????
There is certainly a lot to learn about this topic. I really like all of the points you made.
Thanks for your marvelous posting! I actually enjoyed reading it, you are a great author.I will remember to bookmark your blog and definitely will come back later in life. I want to encourage you to continue your great work, have a nice evening!
Every weekend i used to visit this web page, as i want enjoyment, since this this web page conations actually good funny information too.
<a href=https://spinbetter.one/ru/>mood casting porno</a>
It's the best time to make some plans for the longer term and it is time to be happy. I have learn this publish and if I could I wish to counsel you few interesting issues or suggestions. Perhaps you can write next articles regarding this article. I desire to read even more things about it!
В этом что-то есть. Спасибо за объяснение. Все гениальное просто.
tus juegos favoritos en casino disponibles metodos liquidacion o personal nivel de experiencia sera clave al emparejar cual http://ijuego-casino.com/ - Prueba la ruleta online. por lo tanto consideraremos otros detalles que debe recordar en caso de elegir su favorito virtual casino.
На мой взгляд тема весьма интересна. Предлагаю Вам это обсудить здесь или в PM.
такая деятельность может способствовать повышению настроя и общей удовлетворенности жизнью. Снижение нагрузки на семью: Долговременный уход бывает крайне утомительным и эмоционально сложным https://patronage-service.ru/ - Сиделка с проживанием для родственников.
What's up, after reading this awesome article i am also cheerful to share my experience here with colleagues.
есть некоторые нормальные
если же очень хочется кататься на сноуборде без инструктора (денехнет, но вы держитесь) - самое главное сначала научиться на сноуборде падать, тормозить, контролировать скорость сноуборда, очень наблюдать за остальными катающимися, https://forum.i.ua/topic/23861 - https://forum.i.ua/topic/23861 выучить наизусть правила поведения на склоне.
I was abloe to find good advice from your articles. http://boyarka-Inform.com/
Lo mas importante al usar el codigo promocional 1win: <a href=https://lazosdeamormariano.net/modules/pages/?c_digo_promocional_112.html>https://lazosdeamormariano.net/modules/pages/?c_digo_promocional_112.html</a> es introducirlo a tiempo. Este codigo te da derecho a recibir un bono del 500% por un importe total de hasta $1025.
<a href=https://spinbettercasino-uz.com/>porno xxx hot</a>
ути-пути
для устранения солидных сумм требуется их отыгрыш с вейджером х35 в https://topcasinowin.xyz/ - WinWin слоты течение первой недели.
Давно искал такой ответ
в практику можно эффективно и комфортно интегрировать чрезвычайно популярные и востребованные в среде игроков игры, https://winwin-zerkal0.top/ - https://winwin-zerkal0.top и другие актуальные платежные системы.
долго вы будите искать такого чуда
about twenty years ago, the industry turned decades of scientists https://StemCellCostAnalysis.com/ - https://StemCellCostAnalysis.com researchers invented by man that low calorie intake dictated an increase in the life expectancy of people, and other organisms.
Случайно нашел сегодня этот форум и специально зарегистрировался, чтобы поучаствовать в обсуждении.
несмотря на минимальный время работы, https://winwintop.lol/ - winwintop.lol у казино уже есть идеальное приложение для андроид и партнерская кампания с призами за приглашение новых клиентов.
Я думаю, что Вы не правы. Я уверен. Могу это доказать. Пишите мне в PM.
I can just imagine how negligent student will take this https://kleenseeswindows.com/menu-covers - https://kleenseeswindows.com/menu-covers".
Тема Рулит
Researchers steadily strive find out: how stem cells can treat certain conditions, and select new possibilities of using https://AutismTreatmentSpain.com/ - https://AutismTreatmentSpain.com many pathologies.
Today, while I was at work, my sister stole my iPad and tested to see if it can survive a 30 foot drop, just so she can be a youtube sensation. My iPad is now broken and she has 83 views. I know this is totally off topic but I had to share it with someone!
<a href=https://spin-better.net/>black wife porno</a>
Могу предложить Вам посетить сайт, с огромным количеством статей по интересующей Вас теме.
upon completion of the https://MedicalStemCellCost.com/ - https://MedicalStemCellCost.com/ procedure, the patient will be tired and able to sleep a couple of hours. recent research shows that ASD may be related to autoimmune disorders.
Всё ещё ржу!
ESC showed a cell cycle with a highly shortened g1 phase, https://StemCellPriceInfo.com/ - https://StemCellPriceInfo.com, which provide the opportunity for cells to quickly switch between the m phase and the s phase.
Как пошить римские шторы: шаг за шагом, с целью.
Пошив римских штор: простой
пошить римские шторы https://poshit-rimskie-shtory.ru/ - пошить римские шторы .
Я извиняюсь, но, по-моему, Вы не правы. Давайте обсудим.
Please always consult with a reliable and certified doctor to discuss whether your car is suitable for https://TreatmentCostStemCell.com/ - https://TreatmentCostStemCell.com.
Прелестная мысль
It was the most difficult period in my existence and I did not know what kind of future awaits Dylan with https://StemCellsHelpAutism.com/ - https://StemCellsHelpAutism.com.
По моему мнению Вы не правы. Давайте обсудим это. Пишите мне в PM, пообщаемся.
to determine the hla compliance of https://StemTherapyAutism.com/ - https://StemTherapyAutism.com/, blood tests are performed on both the patient and at all the potential donor.
<a href=https://spinbettercasino-uz.com/>porno xxx hot</a>
В этом что-то есть. Теперь всё понятно, спасибо за объяснение.
Die Kommission fur Glucksspiele|Geldspiele von Gibraltar gibt auch die begehrten Lizenzen aus https://amedasie.com/uncategorized/die-besten-giropay-casinos-im-jahr-2023/ - https://amedasie.com/uncategorized/die-besten-giropay-casinos-im-jahr-2023/ die erlauben Spielautomaten|einarmige Banditen zu spielen} in Institution non-stop.
Как раз то, что нужно. Я знаю, что вместе мы сможем прийти к правильному ответу.
The league, consisting of 32 teams, is divided equally between the National Football Conference (NFC) and the American Football Conference (AFC), https://print-on.by/2025/06/28/bilete-de-avion-chisinau-londra-gsete-cele-mai-2/ - https://print-on.by/2025/06/28/bilete-de-avion-chisinau-londra-gsete-cele-mai-2/any of which includes four divisions.
It's a shame you don't have a donate button! I'd most certainly donate to this superb blog! I guess for now i'll settle for book-marking and adding your RSS feed to my Google account. I look forward to brand new updates and will talk about this website with my Facebook group. Chat soon!
Что он может иметь в виду?
Masaz od wewnatrz Na Zewnatrz, https://gdynia.net.pl/rollershop - https://gdynia.net.pl/rollershop zawsze w kierunku w gore. Masaz trzeba przeprowadzic po aplikacji oleju lub kremu.
так хотел посмотреть....а теперь растроен...я ожидал чего-то большего...
Каталог деревообрабатывающих станков jet имеет множество исполнительниц от столярных https://rutuby.ru/2025/06/27/ruchnye-opryskivateli-jacto-6/ - https://rutuby.ru/2025/06/27/ruchnye-opryskivateli-jacto-6/ до реставрационных. Все станки имеют официальную защиту от jet.
В этом что-то есть. Понятно, спасибо за помощь в этом вопросе.
вы имеете возможность связаться с нами помощи по телефону, https://cbdnewsbreak.com/torgshop/avto-tovary-5/ - https://cbdnewsbreak.com/torgshop/avto-tovary-5/ электронной почте либо через форму обратной связи на нашем сайте.
Вне всякого сомнения.
любой из них обладает собственными уникальными потенциалом и нюансами, https://lk.staritsa.ru/pylesosy-i-struzhkootsosy-jet-23/ - https://lk.staritsa.ru/pylesosy-i-struzhkootsosy-jet-23/ как работает инсектов идеальным выбором для различных задач.
Теперь мне стало всё ясно, благодарю за помощь в этом вопросе.
и такая ситуация не все. на мой взгляд, все абсолютно немного не так обнадеживающе, http://gadjievo.mosmart.ru/ - gadjievo.mosmart.ru как в компании пытаются представить.
Согласен, весьма полезная штука
звучит как идеальный план первого дня в другом городе! Итак, https://www.bernardinonuriel.online/2025/06/28/jekskursii-po-kazani-otkrojte-dlja-sebja/ - https://www.bernardinonuriel.online/2025/06/28/jekskursii-po-kazani-otkrojte-dlja-sebja/ экскурсии разобрали. о чем еще поговорим?
Я извиняюсь, но, по-моему, Вы не правы. Пишите мне в PM, обсудим.
Таргетинг (targeting) - сегментный выбор таргет группы при выпуске рекламы по конкретным https://helpdesk.templatemonsterdev.com/farm-akkauntov-fejsbuk-strategii-i-riski/ - https://helpdesk.templatemonsterdev.com/farm-akkauntov-fejsbuk-strategii-i-riski/ характеристикам. присутствует своя техническая поддержка и внутренний топ.
Вы мне не подскажете, где мне узнать больше об этом?
при обнаружении факта нарушений, включая насилие, отбирание удостоверений личности, https://eastern.in/vakansii-dlja-stroitelej-v-germanii-21/ - https://eastern.in/vakansii-dlja-stroitelej-v-germanii-21/ стоит немедленно обратиться за данной услугой в посольство и правоохранительные органы.
Этот вариант мне не подходит.
Обучение дорогостоящее, https://tmb-renovation.ru/ - Посадка газона однако для этого и живет общий фонд. 5. Монтаж металлоконструкций промышленного цеха. 6. Покраска вышки сотовой связи.
Я считаю, что Вы не правы. Я уверен. Давайте обсудим это. Пишите мне в PM.
однако реструктуризация задолженности перед поставщиками также была проведена на в достаточной степени http://krasnovishersk.mosmart.ru/ - krasnovishersk.mosmart.ru жестких условиях. прочитать все советы у вас есть возможность нажав здесь.
раз позыреть можно
Ми - місце, де застосовують спогади з малих років і юності: коли літо пахло шипучкою, на ділянці будували курені з простирадл, https://xn----7sbkbccbcwghxctgec8vra.xn--p1ai/sovremennye-gadzheti-nastojashhee-i-budushhee/ - https://xn----7sbkbccbcwghxctgec8vra.xn--p1ai/sovremennye-gadzheti-nastojashhee-i-budushhee/ а будівлі крутили одні і ті ж кліпи по телевізору.
denticore reviews I have actually observed a significant decrease in plaque accumulation since I started
utilizing DentiCore. My gum tissues are healthier,
and my teeth really feel more powerful. The chewable tablets are
very easy to take, and the outcomes are remarkable. DentiCore is a wonderful enhancement to my oral
care routine.
БАЯН
вони можуть мати особливі пропрієтарні роз'єми, https://bestbuycase.com.ua/redmi-note-redmi-note-11/c-73-2573-2020.html - Чохли для Redmi Note 11 купити недорого у зв'язку з цим, перед придбанням слід заздалегідь потурбуватися про цей факт.
Муж растрогался - сказал, что это самый душевный подарок!
<a href=https://nuquo.com/nusletters-2021-12/>букет пионов</a>
<a href=https://dixontriallawyer.com/>porno teens group</a>
Мирка не кипятись!!!
весьма часто снимаются выигрыши на счет, так как не обращая внимания на возможные задержки с языковой адаптацией, https://xmelbet.top/ - https://xmelbet.top/ это в наибольшей степени долговечный и безвредный вариант.
Настоящий шедевр флористики!
<a href=https://www.instagram.com/p/DKbWi37qRG6/?igsh=MXhyN2Zua3Zwc2d6MA==>доставка цветов</a>
Я думаю, что Вы допускаете ошибку. Пишите мне в PM, пообщаемся.
вы получаете шанс обратиться в поддержку или просто кликните на кнопку Войти. «Играю на https://melbet-off1cial.top/ - мелбет регистрация Ваваде каждый день.
Извините, что я Вас прерываю, но, по-моему, есть другой путь решения вопроса.
????/? ????? ????????????????????/??. ?????/???? ???? ???? ?? ????? https://pragmaticplaykorea.kr/ - ??????? ???
Специально зарегистрировался на форуме, чтобы сказать Вам спасибо за поддержку, как я могу Вас отблагодарить?
This figure shows notable activity in American markets, and https://result-sgp.net/key-parameters-to-set-up-your-virtual-ai-girlfriend/ - ai gf highlights Germany's role in the growing trend towards virtual relationships.
И все, а варианты?
citrus bergamia: bergamot and https://carnerbars.ru/ - парфюмерная вода its derivatives (англ.). agriculture diversification: problems and perspectives (англ.).
сказка чтоли?
making emphasis on real formulas, oak essentials comprehensively cares for the skin - moisturizes, balances, https://www.mmmoreiralaw.com/exploring-the-world-of-premium-skincare-haircare/ - https://www.mmmoreiralaw.com/exploring-the-world-of-premium-skincare-haircare/ and regenerates the complexion.
Ценю пунктуальность - привезли минута в минуту!
<a href=https://fightbox.gr/home-parallax/new_bg_3/>заказ цветов томск</a>
Отличное и своевременное сообщение.
??? ??:4096 ??? https://spassoparabens.com.br/page-9/ - https://spassoparabens.com.br/page-9/ ??/??250??/??? ??/????/???? 4 ?? ?????.
Я извиняюсь, но, по-моему, Вы допускаете ошибку. Давайте обсудим это. Пишите мне в PM, пообщаемся.
у нас выложены классические запонки и зажимы для галстука, респектабельные печатки и серьезные перстни с бриллиантами. если необходимо, будут выполнены уточнения в стандартных моделях, https://inparis.co.il/kolca-na-zakaz-idealnoe-reshenie-dlja-vashego/ - https://inparis.co.il/kolca-na-zakaz-idealnoe-reshenie-dlja-vashego/ либо будет создан самобытный оформление.
Да, вполне
from time to time admire the fast payouts https://winspiritbonuscode.com/ - winspirit casino promo code code, in that time how others are dissatisfied difficult conditions for acquiring the bonus.
Я считаю, что Вы не правы. Я уверен. Давайте обсудим это. Пишите мне в PM, поговорим.
Выполняя такие задания, http://www.sskyn.com/home-uid-90686.html - http://www.sskyn.com/home-uid-90686.html ребенок будет развивать свои интеллектуальные возможности и радушно проводить время!
а мне даже очень понравились...
1982. - № 3. - С. Играя, ребёнок осваивает новые роли, http://komerc.mineralgroup.ru/index.php?subaction=userinfo&user=ulosula - http://komerc.mineralgroup.ru/index.php?subaction=userinfo&user=ulosula развивает навыки и расширяет жизненный опыт.
I think this is among the most significant info for me. And i am glad reading your article. But should remark on some general things, The site style is ideal, the articles is really excellent : D. Good job, cheers
Полностью разделяю Ваше мнение. Идея отличная, поддерживаю.
СПб.: Изд-во Санкт-Петербургского гос. Игры могут принимать разные формы, http://noobtype.ru/index.php?title=webcamm - http://noobtype.ru/index.php?title=webcamm начиная от спортивных соревнований и заканчивая настольными и играми для компьютера.
<a href=https://xn-----6kcalbcicjejewb8dicoam4aruzb2yf2e.xn--p1ai/>porno pics milf</a>
Собрали именно такой букет, как я просила - молодцы!
<a href=https://a2a.org.au/demoevents/september-2021-leaders-together/>цветы</a>
Да, бывает же...
Говорящая кошечка https://www.vertex-st.ru/product/atv-8c/reviews/ - https://www.vertex-st.ru/product/atv-8c/reviews/ Анджела вернулась! toca boca world. Мир Тока Бока - создавайте свою историю!
Коллеги офигели от красоты!
<a href=https://2gis.ru/tomsk/geo/422741746604144>101 роза</a>
Это мне не нравится.
повседневность современных граждан, сопряжена с компьютером. бесплатные онлайн http://www.inline.spb.ru/in/index.php?option=com_comprofiler&task=userProfile&user=6575 - http://www.inline.spb.ru/in/index.php?option=com_comprofiler&task=userProfile&user=6575, рекомендованные на этом сайте, помогут решить не только эти трудности.
прикольно, но смысла нет!!!
^ Евгений Курт. Нейросети нам помогут: как внедрение обучаемых технологий скажется https://telegra.ph/Avto-iz-SSHA-v-Minsk-06-26 - купить авто из америки в минске на онлайн-маркетинге (неопр.).
Бесплатная открытка с теплыми словами - приятный сюрприз!
<a href=https://feedback.bistudio.com/p/cvetaevatomsk/>доставка цветов томск</a>
Я извиняюсь, но, по-моему, Вы ошибаетесь. Пишите мне в PM, поговорим.
^ Источник (неопр.). Дата обращения: 24 декабря 2022. Архивировано 24 декабря 2022 года. games animals play (англ.). Фабри К. Э. Игры ваших питомцев и https://notebooks.ru/forum/user/164800/ - https://notebooks.ru/forum/user/164800/ детей (сравнительно-психологические аспекты) // Вопросы психологии.
Свежесть как после утренней росы - потрясающе!
<a href=https://www.wellbeingcollective.co/6-spring-wellness-trends/>доставка цветов</a>
<a href=https://delphinperle.com/br/>Dolphins Pearl Jogue com dinheiro real</a>
мда придумали ж
Мы гордимся чем-то, что с 2024 года предоставляем игрокам оптимальные обстоятельства для беттинга, https://www.aerialteknology.com/fairspin-no-casino-em-portugal-continental-tudo-o-que-necessita-saber-sobre-sites-de-apostas-online/ - https://www.aerialteknology.com/fairspin-no-casino-em-portugal-continental-tudo-o-que-necessita-saber-sobre-sites-de-apostas-online/ обеспечивая исключительный удобство и без обмана игру.
Мгновенная доставка - это просто магия какая-то!
<a href=https://vanproosdijenvandebunt.nl/2022/04/19/controversial-article-find-out-more/>купить пионы томск</a>
Индивидуальный подход - это ценно!
<a href=https://vk.com/wall-61709230_7282>заказать цветы томск</a>
Срочный заказ за 30 минут - это фантастика!
<a href=https://www.artstation.com/cvetaevatomsk8>заказать цветы с доставкой в томске</a>
Thanks , I've recently been looking for info about this topic for a long time and yours is the greatest I have discovered so far. However, what concerning the bottom line? Are you certain in regards to the supply?
Это не так.
in window there is an "Order to buy a pocket option" from you there is an opportunity introduce positive substitutions – to personal a pocket option purchase order by trading a https://new.kraftekdesign.com/unlocking-opportunities-your-guide-to-pocket/ - Pocket Option Guide, starting with the order volume (lot size) and continuing by setting up a Stop-loss pocket option or a Take-profit pocket option.
<a href=https://dixontriallawyer.com/>rape girl porno</a>
Восхитительный букет! Получила именно то, что хотела. Спасибо!
<a href=https://www.instagram.com/reel/DGqJWhdSxfV/?igsh=Y3JyZnIxZ285YjF0>букет пионов</a>
Огромный выбор букетов на любой вкус!
<a href=https://vk.link/cvetaevatomsk>купить цветы в томске</a>
Доставили в область - все в идеальном состоянии.
<a href=https://www.thinglink.com/scene/1975912287172559716>розы томск</a>
Надо поглядеть!!!
в численних релігіях та обрядах в різні історичні епохи відношення до летального результату було https://www.ritual24.kiev.ua/tovari/vinki-jivi-kviti/ - https://www.ritual24.kiev.ua/tovari/vinki-jivi-kviti/ неоднозначний.
Вы ошибаетесь. Пишите мне в PM.
These apps assign you a number with which you get a great chance to make free local phone orders, and send text notifications to any https://www.topmostblog.com/get-portugals-sms-number-online/ - https://www.topmostblog.com/get-portugals-sms-number-online/.
люблю такое
«Фонтанка» - петербургское сетевое издание, где можно найти не только лишь новости Петербурга, но также последние https://biwork.ru/ - новости бийска сегодня свежие дня и все увлекательное и весьма сложное, что творится в российской федерации также в на земле.
Use <a href=https://stpaulspeabody.com>crazy time game prediction</a> for better bets!
<a href=https://spinbetter-au.com/>rape girl porno</a>
Спасли день рождения - доставили вовремя!
<a href=https://automobilist.forum24.ru/?1-5-0-00001581-000-0-0-1752049408>заказать цветы с доставкой в томске</a>
<a href=https://spinbetter-au.com/>rape girl porno</a>
https://uztm-ural.ru/catalog/redkozemelnye-i-redkie-metally/
<a href=https://spinbetter.org.pl/>porno teens</a>
Cancel
Leave a Comment
Your email address will not be published. Required fields are marked *