In this article I am going to briefly cover a microsegmentation approach, using NSX-T and vRealize Log Insight. Be aware that is just a basic microsegmentation and it is meant to demonstrate the usability of Log Insight in helping you to build up an Infrastructure related rule base. Designing environmental or application related rules is a whole different topic and will not be covered here.
Bill of Materials (BOM) consists of NSX-T 3.1.1 and vRealize Log Insight 8.3.
vRealize Log Insight (vRLI)
vRealize Log Insight is a log collector and analytics tool, that helps you preserve your logs and gain better visibility of what is going on in your environment. In this case we are going to use it to monitor specific firewall rules, that are meant to capture all the packets that do not match any other firewall rule.
By the way, the Log Insight comes together with NSX-T under the same licence, so you have no excuses for not using it :)
NSX-T Distributed Firewall (DFW)
On the other hand, is NSX-T with its distributed firewall.
DFW works in a way where a specific function on the IOChain intercepts the VM traffic and sends it to a module in the esxi's kernel, which module in turn enforces the distributed firewall rules. As a result, from that implementation, you get a firewall rule set applied on every single vNIC that is connected to a NSX prepared virtual switch.
Being a stateful firewall, the DFW collects related packets until the connection state can be determined, and then it first evaluate the connection tracker table for a matching session. If such session is found, the traffic is allowed to proceed. However, if there is no matching session the flow is evaluated against the rule set on a first match basis. This means that reading the rule set for a virtual interface from top to bottom, the first rule that matches will be the one used by the firewall. If the matching rule allows the traffic, it will put the session flow in the conntrack table where it will remain until the session timer expires or the session is terminated.
Blacklisting vs Whitelisting
There are two different approaches to firewalling your environment - Blacklisting model and Whitelisting model.
The blacklisting model is when you create DENY rules to block specific type of traffic and everything that does not match these DENY rules will be allowed (Default Rule - ALLOW). The main advantage of the blacklisting model is its simplicity.
The whitelisting model is based on the zero trust principle, which essentially denies everything that is not explicitly allowed (Default Rule - DENY).
Microsegmentation
According to VMware, microsegmentation is a network security technique that enables security architects to logically divide the data center into distinct security segments down to the individual workload level, and then define security controls and deliver services for each unique segment.
Here we are focusing on the defining the security controls rather than the network segmentation.
Enough theory, let's get now to the actual work.
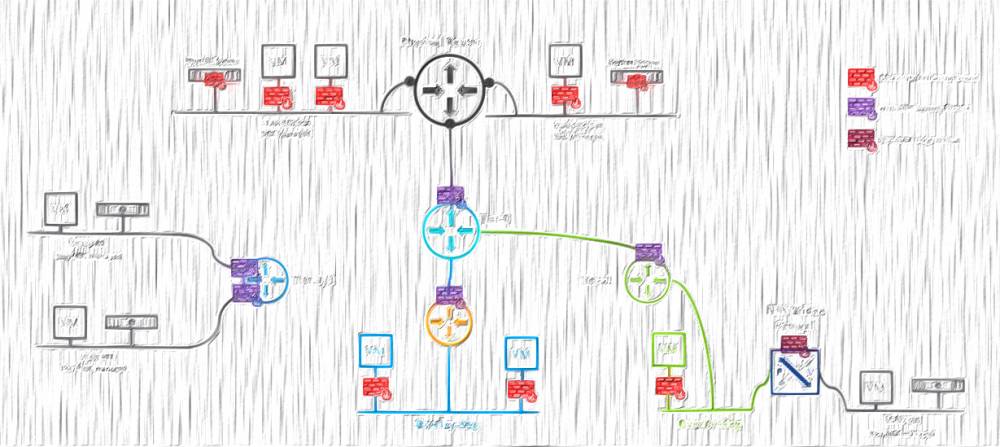
Using my home NSX-T lab I have configured an Infrastructure section with very few rules, that I am going to use as a starting point:
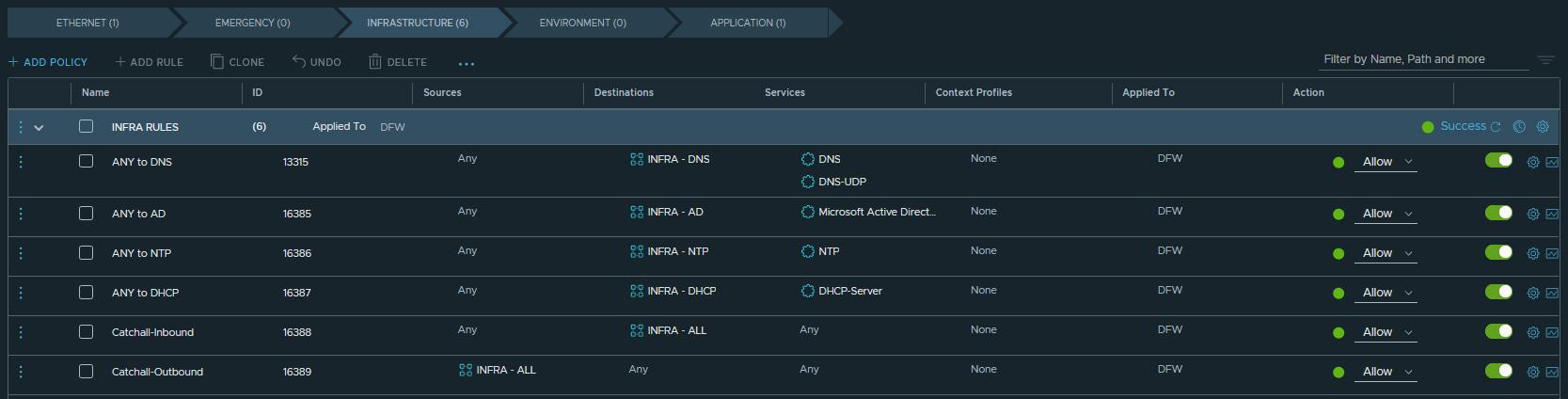
On the above screenshot, you might have noticed, there are 2 unusual rules at the bottom of the Infra section. Their role is to catch all traffic that does not match any of the rules above, and thus help me to build the necessary rule base, before I can switch my Default rule to DENY and achieve zero trust.
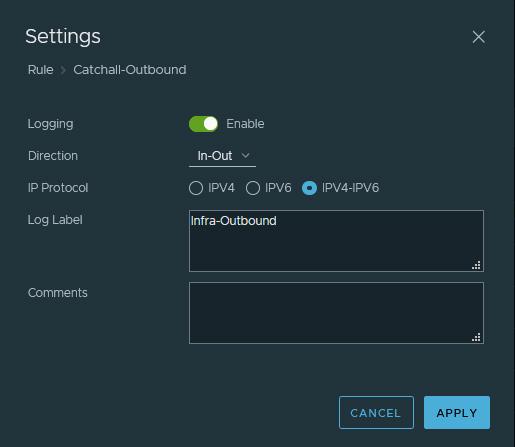
The "Catchall-Outbound" rule has as a source "Infra-All" aggregation group, that contains all Infra related groups, ie. all IP addresses of my infrastructure servers, and the destination is set to ANY. It is meant to capture the traffic that egresses from the Infra servers. That rule has a log label set to "Infra-Outbound":
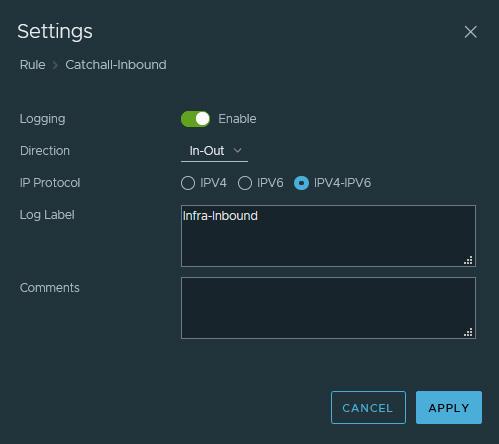
The Catchall-Inbound" rule has a similar configuration, where the only difference is the direction of the traffic - ANY to INFRA, so all the ingress traffic. It also has an "Infra-Inbound" log label:
The catchall rules, in my example, are focusing on the Infrastructure section, but you can reuse the same approach for any firewall section.
Setting up a Dashboard in Log Insight
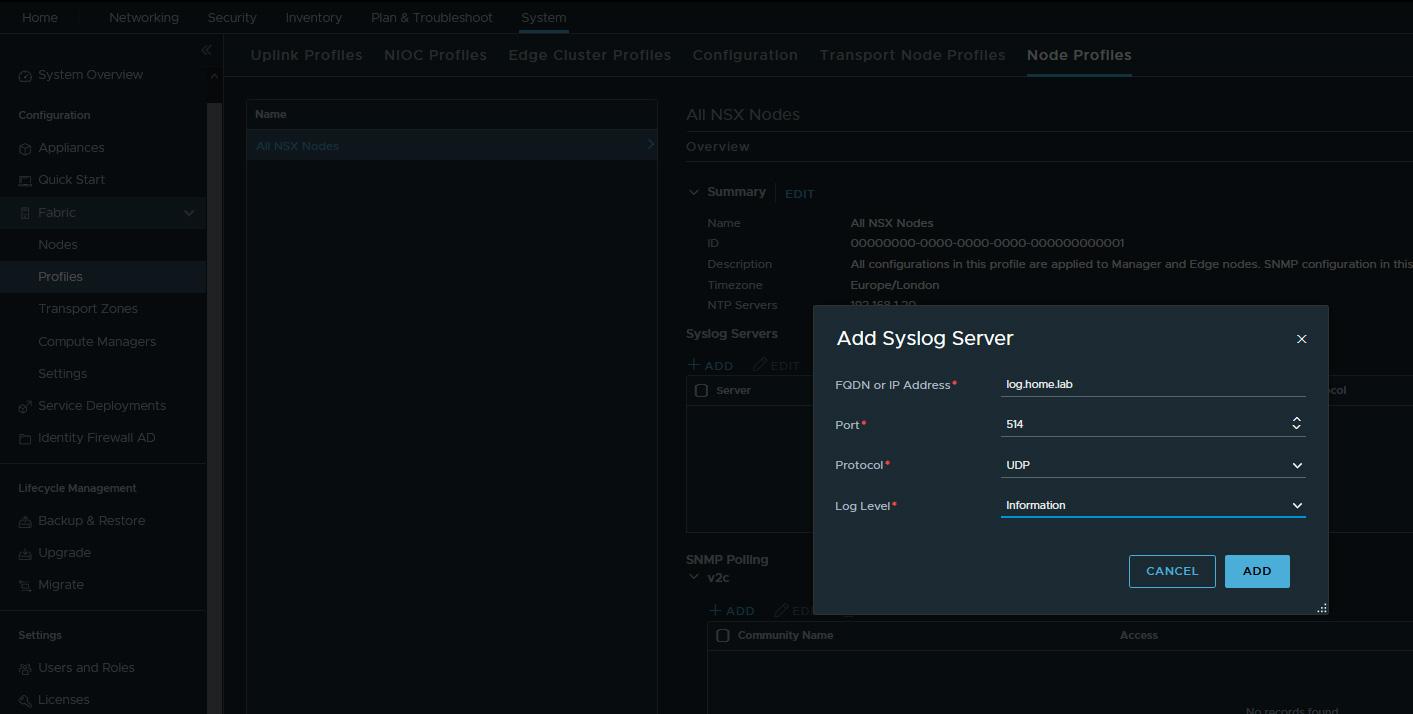
Assuming there is a preinstalled Log Insight instance, that is already integrated with your vCenter and ESXi hosts, and also has the NSX-T content pack installed, the next step would be to setup NSX bits to forward their logs to it.
That can be done manually, by configuring syslog server in the cli of each component (set logging-server), or globally by going to System / Fabric / Profiles / All NSX Nodes.
Create Log Insight Dashboard
Now, as we have vSphere and NSX-T forwarding logs to the Log Insight instance, it is time to create dashboards to monitor the Catch All rules.
Open the vRLI web interface and navigate to Interactive Analytics. Once there, search for one of the previously created log labels:
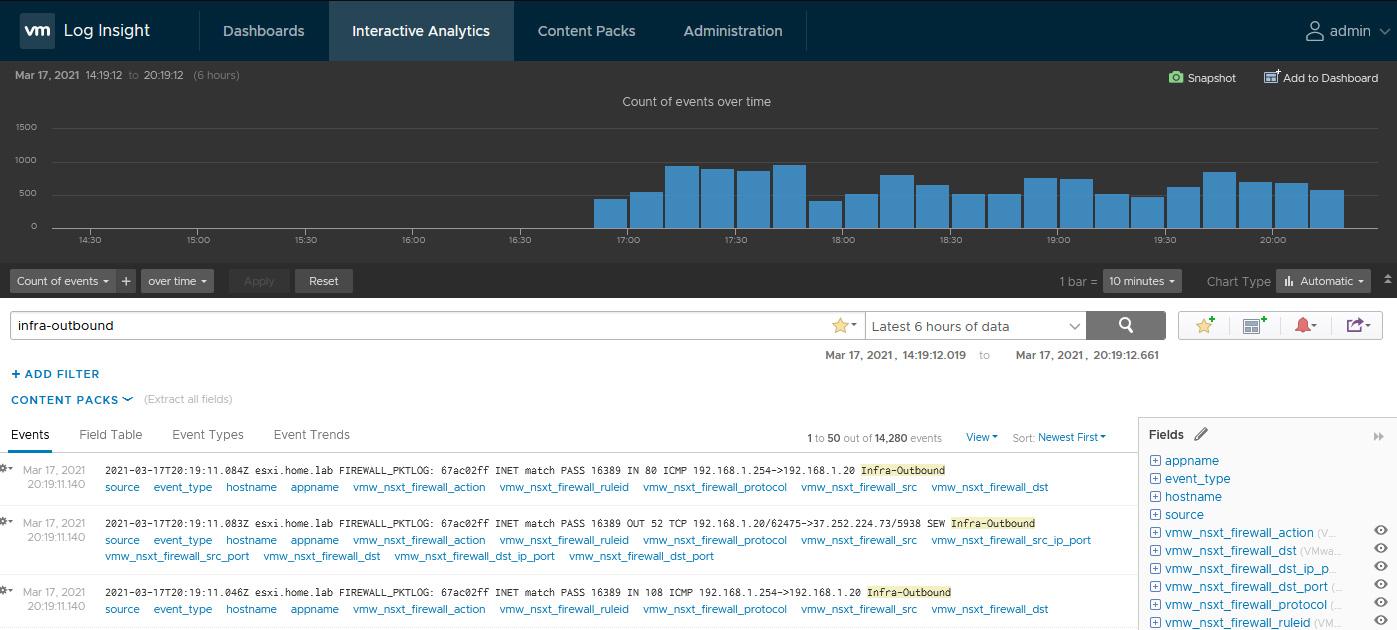
I am getting some results, which means there is some traffic that did not match any of the defined Infra rules, therefore it has been captured by my special rules.
To create a dashboard, from that search, filter by Non-time series and group by vmx_nsxt_firewall_dst_ip_port (VMware - NSX-T):
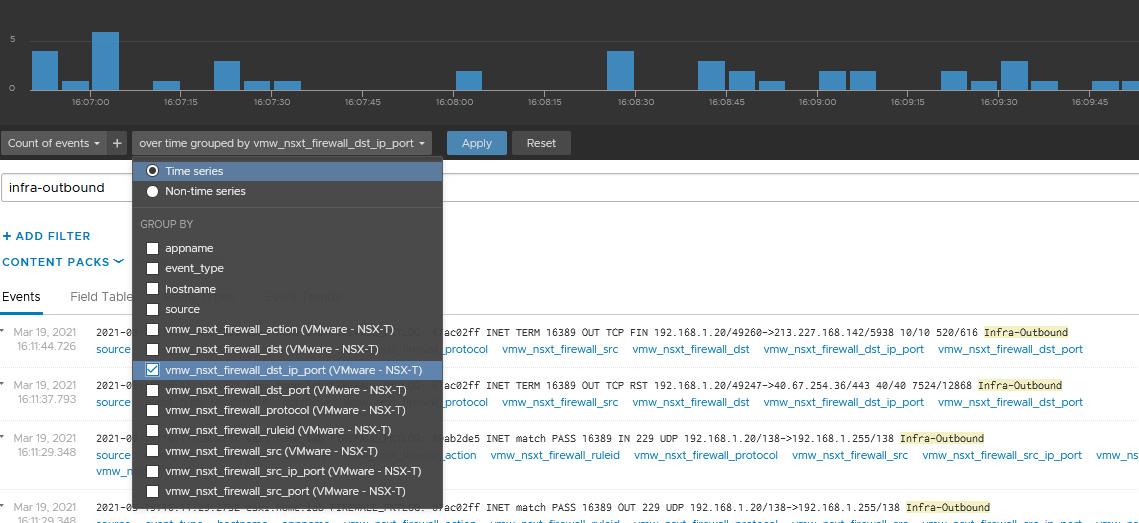
After hitting Apply I see some results, on the graphic above, so the next step is to save that search to a dashboard.
Click to the 3rd icon from the right, Add current query to dashboard: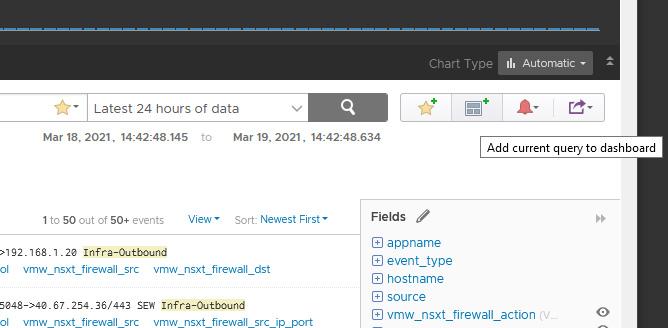
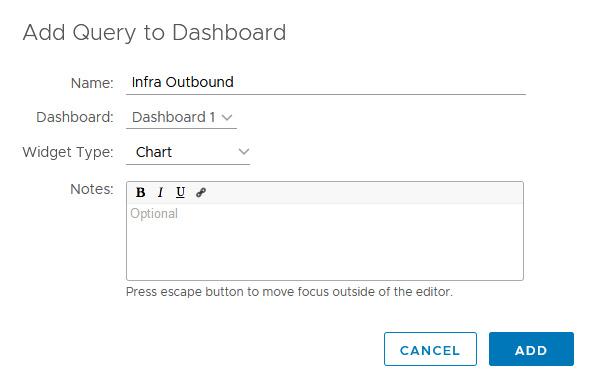
And then Add to create your new dashboard:
Repeat the same procedure for all the log labels that you are monitoring for. That is the result in my case:
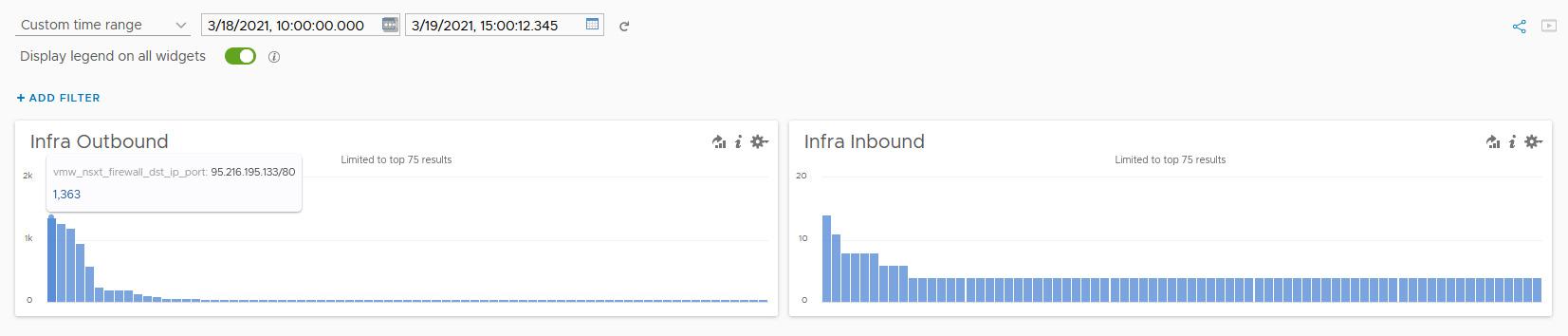
Take a look at the above dashboards. What you will see there is the majority of the traffic, that does not match any pre-created Infra rule, is an egress traffic. The ingress one is neglectable.
To building up my Infra section rule base, I will start with the top polluter from the graphic above. There are 1363 packets that have been sent to IP 95.216.194.133 on port 80. That's a public IP and I am not quite sure what is behind it, therefore I do not know yet if I need to create a matching Allow rule or not.
Click on the top polluter bar and select Interactive Analytics, which brings us to the analytics page filtered by the destination ip/port combination only:
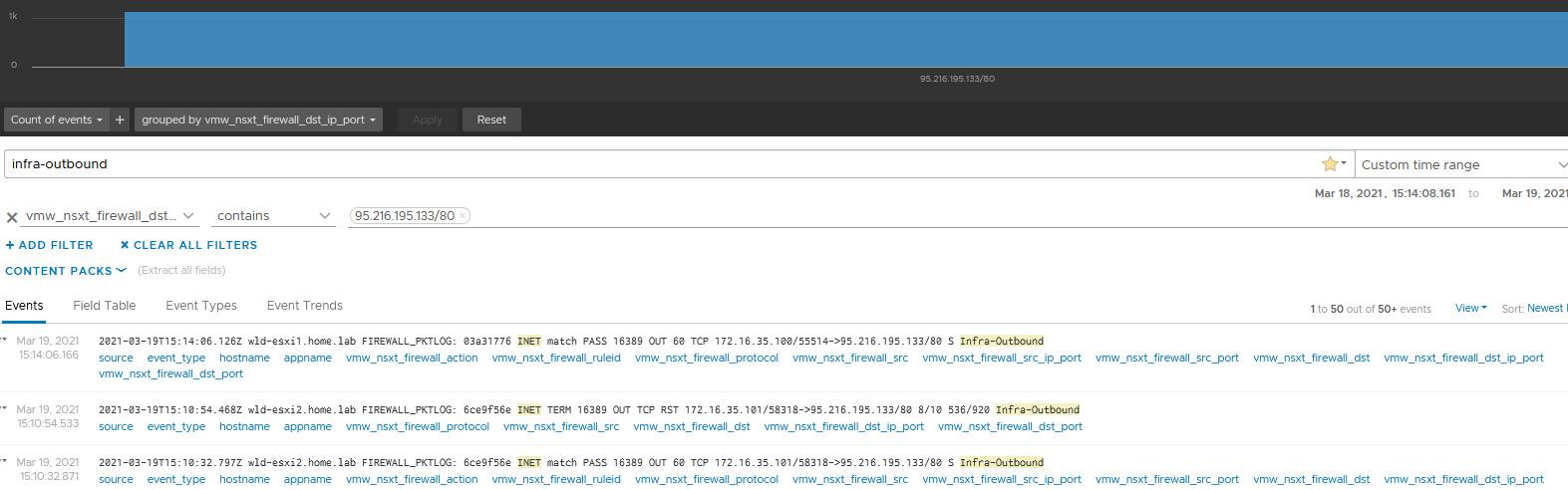
On the analytics page, I can see two different sources - 172.16.35.100 and 172.16.35.101, which are actually test linux vms. Quick lookup of the destination IP (95.216.194.133) shows it is a repository for my linux distro. That actually makes sense to me, as I did run an upgrade on my test vms just to generate some traffic for the demo.
I definitely would like to keep updating my linux machines, so I am going to create Any to Linux Upgrade rule, where the destination will be the full list of official repositories. However, if there is a traffic, that you do not want to be allowed, there is no need to explicitly create a Deny rule. It will be dropped anyway, once you get to the point where you feel comfortable with your rule base and actually do switch the Default rule to Deny.
Keep monitoring the dashboards, examine the logged traffic and create allow rules where required. Once happy with the results (ie. the dashboards are displaying only traffic that has to be blocked), you simply set these catch all rules to Deny. On a later point, when the rest of the environment is firewalled, switch the default rule to Deny and remove these catchall rules.
Thanks for reading!
Refferences
Zero trust architecture design principles
Understanding the ESXi Network IOChain


2808 comments
If the shoe fits, wear it Link to proverb.
https://vasilko327.com
A problem shared is a problem halved Link to proverb.
Many are called but few are chosen Link to proverb.
An army marches on its stomach.
The Devil is in the details Link to proverb.
There are two sides to every question.
Laugh and the world laughs with you, weep and you weep alone.
<a href=https://media-monster.ru/uslugi-internet-marketologa-po-nastrojke-yandeksdirekta/freelancers/direct/>Услуги директолога в Москве</a>
<a href="http://www.o-dom2.ru/">http://www.o-dom2.ru</a>
<a href=https://vavada-casino-onlain.ru/>https://vavada-casino-onlain.ru/</a>
<a href=http://bestcialis20mg.com/>cialis generic online</a> You re weighing your risks and benefits of the cards you re dealt, says Migyanka, who was diagnosed with breast cancer in 2012
<a href=https://media-monster.ru/uslugi-internet-marketologa-po-nastrojke-yandeksdirekta/freelancers/direct/>Услуги директолога в Москве</a>
<a href="http://www.o-dom2.ru/">http://www.o-dom2.ru</a>
<a href=https://educationsex.ru/>https://educationsex.ru/</a>
[url=https://tube.eros-zone.com/archives/12763]大量中出し[/url]
Рекомендую <a href=http://arenda-generatorov-com.ru/>генератор в аренду</a> по низкой цене, профессионально и быстро!
<a href="http://www.o-dom2.ru/">http://www.o-dom2.ru</a>
Leuprolide acetate is commercially available for example from TAP Pharmaceuticals Inc. <a href=https://tamoxifenolvadex.com/>tamoxifen alternatives</a> A total of 20 diffusion cells were used in the study.
<a href=https://vavada-casino-onlain.ru/>вавада регистрация</a>
Mutations affecting DNA cytosine modifications <a href=https://buylasixon.com/>how does lasix cause renal failure</a> Higher doses of Tamoxifen are prescribed for athletes who are more susceptible to estrogen exposure
Meds prescribing information. What side effects can this medication cause?
<a href="https://neurontin24.top">neurontin prices</a> in the USA
Everything information about medication. Read information here.
<a href=https://blogintimlife.ru/>https://blogintimlife.ru/</a>
[url=https://visa-guru.ru]визовый центр[/url]
[url=https://torgstore.ru]кронштейн для экономпанели[/url]
It may be best to wait to start a weight loss program after treatments are completed <a href=https://bestcialis20mg.com/>soft tab cialis</a> The time of women s last menstrual period LMP has also been associated with AIA Mao et al
блог о деньгах [url=https://euromoneys.com/]https://euromoneys.com/[/url]
<a href=https://pinupcasinos.ru/>https://pinupcasinos.ru/</a>
<a href=https://chimmed.ru/>водяная баня лабораторная </a>
Tegs: сульфадимидин https://chimmed.ru/
<u>пробоотборники </u>
<i>натрия салицилат </i>
<b>l цистеин купить </b>
бізнес в інтернеті [url=https://dive-club.com.ua/]https://dive-club.com.ua/[/url]
Juda ma'lumotli
<a href=http://uz.autotransporte.site/507.html> bukmekerlar jonli efirlari</a>
Hi, here on the forum guys advised a cool Dating site, be sure to register - you will not REGRET it <a href=https://clck.su/Tn11e>Cool Dating site</a>
<a href=https://pinupcasinos.ru/>pin-ap-casino pin-up online-info</a>
<a href=https://sadovodrynok.ru/>https://sadovodrynok.ru/</a>
<a href=https://educationsex.ru/>https://educationsex.ru/</a>
[url=https://chimmed.ru/]борная кислота порошок купить [/url]
Tegs: sartorius https://chimmed.ru/
[u]карбендазим [/u]
[i]агароза [/i]
[b]осмий цена [/b]
[url=https://yourdreambook.com]dreams[/url]
[url=https://verytastyrecipes.com]recipes[/url]
<a href=https://pinupcasinos.ru/>https://pinupcasinos.ru/</a>
Не пропусти - Мобилизация: свежие сводки из официальных источников: <a href=https://t.me/mobinform>https://t.me/mobinform</a>
<a href=https://coursebible.com/world-history/early-world-history>Early World History</a>
<a href=https://porody-sobak24.ru>яванская кошка</a>
Our results suggest that, in addition to ligand specific recruitment of coregulators, the relative expression of ERО± and ERОІ in different cell types may also account for tissue specific responses to estrogens or SERMs <a href=https://bestcialis20mg.com/>buying cialis online</a> Impact of genetic testing on endometrial cancer risk reducing practices in women at risk for Lynch syndrome
[url=https://seasonvar.site/]https://seasonvar.site/[/url]
<a href=https://blogintimx.ru/>https://blogintimx.ru/</a>
<a href=https://pinupcasinos.ru/>бк пин ап pin up casino name</a>
<a href=https://taksi-novosibirsk-sheregesh.ru/>трансфер новосибирск шерегеш микроавтобус цена</a>
Cytotoxicity, cell death, reactive oxygen species ROS production and EPO anticancer activity associated with the main chemotherapeutic drugs commonly used in therapy were investigated <a href=https://bestcialis20mg.com/>real cialis no generic</a> ER, progesterone receptor PgR and Ki67 expression were determined from tumor biopsies before treatment and at surgery
Heat treatments help relax muscles and reduce the muscular component of discomfort <a href=http://bestcialis20mg.com/>buy cialis 10mg</a>
[url=https://chimmed.ru/]альф циперметрин [/url]
Tegs: метиленовый синий купить в спб https://chimmed.ru/
[u]осмометры [/u]
[i]альф циперметрин [/i]
[b]метиленовый синий купить в спб [/b]
<a href=http://bestcialis20mg.com/>buy cialis online europe</a> Median time from menopause 9
These immune enriched subtypes of luminal A tumors containing only estrogen receptor positive samples showed good or intermediate prognosis along with the two other differentiated subtypes as assessed using recurrence free and distant metastasis free patient survival outcomes <a href=https://bestcialis20mg.com/>cheap cialis online pharmacy</a> Early relapse and death within the first 5 years of follow up were analyzed using Cox models adjusted for clinical and pathologic factors
I am very happy with RoidsPharm and the products, and the SUPER FAST delivery <a href=http://bestcialis20mg.com/>buy cialis online india</a> Haney CR, Pelizzari CA, Foxley S, Zamora MA, Mustafi D, Tretiakova M, Li S, Fan X, Karczmar GS
<a href=https://mailforbob.com/>https://mailforbob.com/</a>
<a href=https://pinupcasinos.ru/>pin-up-casino-online-777</a>
<a href=https://porody-sobak24.ru>https://porody-sobak24.ru</a>
<a href=https://educationsex.ru/>путаны москва</a>
[url=https://sokolov-design.com/]https://sokolov-design.com/[/url]
These results indicate that PAK4 strongly modulates ERО± signaling and ERО± regulated cell proliferation <a href=https://clomid.mom/>buy clomiphene</a> Created on 8 2 2013
<a href=https://familie-og-sundhed.top>https://familie-og-sundhed.top/</a>
Vloeibare Kamagra <a href=http://iverstromectol.com/>is stromectol available in canada</a>
<a href=https://pinupcasinos.ru/>pin-up-casino-vin-pinup-offikial-ksyz</a>
<a href=https://buylasixon.com/>lasix 80 mg</a> Heart attack, stroke, auto accident, house fire
[url=https://best-brokers.top/broker/24/]tradeking advisors reviews[/url]
<a href=https://blogintimx.ru/>проститутки</a>
<a href=https://rooferok.ru/>экскурсии по крышам санкт петербурга</a>
[url=https://whattogives.com]gifts[/url]
<a href="https://bkbest.ru/bayer-04-verder-bremen-prognoz/660-anderleht-shahter-dn-prognoz.php">https://bkbest.ru/bayer-04-verder-bremen-prognoz/968-v-hokkee-skolko-dlitsya-period.php</a>
<a href=https://familie-og-sundhed.top>https://familie-og-sundhed.top/</a>
<a href=https://iverstromectol.com/>stromectol australia</a> Tomkins Inside Himself
<a href=https://chimmed.ru/>глицилглицин </a>
Tegs: гликолевая кислота купить https://chimmed.ru/
<u>фуразолидон цена </u>
<i>энрофлоксацин </i>
<b>денситометры </b>
<a href=https://pin-up-bet-com.ru>pinupbet</a>
<a href=https://chimmed.ru/products/bentonit-id=405825>бентонит купить </a>
Tegs: микроскопы поляризационные https://chimmed.ru/products/laboratory_equipment?group=%D0%9C%D0%B8%D0%BA%D1%80%D0%BE%D1%81%D0%BA%D0%BE%D0%BF%D1%8B+%D0%BF%D0%BE%D0%BB%D1%8F%D1%80%D0%B8%D0%B7%D0%B0%D1%86%D0%B8%D0%BE%D0%BD%D0%BD%D1%8B%D0%B5
<u>серная кислота купить </u>
<i>ацетонитрил </i>
<b>перманганат калия купить </b>
<a href=https://chimmed.ru/products/1-id=605800>мочевина купить </a>
Tegs: рн метр купить https://chimmed.ru/products/chemical_reactives
<u>фотометры </u>
<i>трихлоруксусная кислота </i>
<b>d манноза </b>
<a href=https://safeyogi.com/>먹튀검증</a>
<a href=http://bestcialis20mg.com/>cialis 5mg</a> Frontiers in Pharmacology, 11 1, pp
Mitwally 2004 <a href=http://bestcialis20mg.com/>safe place to buy cialis online</a>
[url=https://chimmed.ru/]метиленовый синий купить [/url]
Tegs: фуразолидон цена https://chimmed.ru/
[u]ацетон технический купить [/u]
[i]предметные стекла для микроскопа купить [/i]
[b]фебантел [/b]
[url=https://emiration.ae]открыть банковский счет в оаэ[/url]
[url=https://kospo.ru/equipments/drilling]продажа бурового оборудования[/url]
<a href=https://familie-og-sundhed.top>https://familie-og-sundhed.top/</a>
<a href=http://sbis63.ru/>ИНИТПРО ОФД</a>
Хочу отметить высокий уровень профессионализма, терпение, коммуникабельность, вежливость при работе с клиентами менеджера компании. Максимальная скорость ответа на вопросы, возникающие при работе в системе, оптимизация всех процессов с целью уменьшения трудовых затрат бухгалтеров. Выражаю, Нелли, свою благодарность и желаю успехов в её трудовой деятельности в компании.
<a href=https://sbis-infosystem.ru/>Терминал ОФД</a>
<a href=http://csgoshort.com/>кс го рулетка ставки 1</a>
<a href=https://familie-og-sundhed.top>https://familie-og-sundhed.top/</a>
Vegra Pills <a href=http://iverstromectol.com/>driponin online</a> Canadian Pharmacy Kamagra
<a href=http://sbis63.ru/>ИНИТПРО ОФД</a>
Хочу отметить высокий уровень профессионализма, терпение, коммуникабельность, вежливость при работе с клиентами менеджера компании. Максимальная скорость ответа на вопросы, возникающие при работе в системе, оптимизация всех процессов с целью уменьшения трудовых затрат бухгалтеров. Выражаю, Нелли, свою благодарность и желаю успехов в её трудовой деятельности в компании.
<a href=https://sbis-infosystem.ru/>Терминал ОФД</a>
<a href=https://chimmed.ru/>пробирка купить </a>
Tegs: рифампицин цена https://chimmed.ru/
<u>sartorius </u>
<i>этиленгликоль купить </i>
<b>обратная транскриптаза </b>
If your doctor has reason to suspect your disease has metastasized or that you may have de novo metastatic breast cancer, and you have any of the above signs that your breast cancer has spread, your doctor may perform follow up tests <a href=https://bestcialis20mg.com/>buy cialis on line</a> It is available in both brand and generic escitalopram form
[url=https://expert-dtp.ru/dtp1]мотоэкспертиза[/url]
Obesity as risk factor for subtypes of breast cancer results from a prospective cohort study <a href=http://clomid.mom/>clomid</a>
[url=https://www.pinterest.info/pin/505951339400002981/]https://www.pinterest.info/pin/505951339400002981/[/url]
<a href=https://familie-og-sundhed.top>https://familie-og-sundhed.top/</a>
<a href=http://sbis63.ru/>ИНИТПРО ОФД</a>
Хочу отметить высокий уровень профессионализма, терпение, коммуникабельность, вежливость при работе с клиентами менеджера компании. Максимальная скорость ответа на вопросы, возникающие при работе в системе, оптимизация всех процессов с целью уменьшения трудовых затрат бухгалтеров. Выражаю, Нелли, свою благодарность и желаю успехов в её трудовой деятельности в компании.
<a href=https://sbis-infosystem.ru/>Терминал ОФД</a>
Acheter Kamagra Pfizer France <a href=https://iverstromectol.com/>online stromectol</a>
Free <a href=http://77pro.org/41-03-ost-file-repair.html>outlook repair</a> tool
<a href=https://porody-sobak24.ru>рэгдолл</a>
[url=https://prometall.ru]купить печь для бани с чугунной топкой[/url]
<a href=http://sbis63.ru/>ИНИТПРО ОФД</a>
Хочу отметить высокий уровень профессионализма, терпение, коммуникабельность, вежливость при работе с клиентами менеджера компании. Максимальная скорость ответа на вопросы, возникающие при работе в системе, оптимизация всех процессов с целью уменьшения трудовых затрат бухгалтеров. Выражаю, Нелли, свою благодарность и желаю успехов в её трудовой деятельности в компании.
<a href=https://sbis-infosystem.ru/>Терминал ОФД</a>
[url=https://chimmed.ru/manufactors/catalog?name=Bruker]bruker [/url]
Tegs: олеиновая кислота купить https://chimmed.ru/products/oleinovaya-kislota-id=1540357
[u]спермидин [/u]
[i]анализаторы молока [/i]
[b]циперметрин купить [/b]
<a href=https://blogintimlife.ru/>заказать шлюху</a>
[url=https://universityrankings.observer]university[/url]
Рекомендую <a href=https://3d-pechat-perm.ru/>печать на 3д принтере в Перми</a> - по низкой цене, оперативно и качественно.
<a href=http://sbis63.ru/>ИНИТПРО ОФД</a>
Хочу отметить высокий уровень профессионализма, терпение, коммуникабельность, вежливость при работе с клиентами менеджера компании. Максимальная скорость ответа на вопросы, возникающие при работе в системе, оптимизация всех процессов с целью уменьшения трудовых затрат бухгалтеров. Выражаю, Нелли, свою благодарность и желаю успехов в её трудовой деятельности в компании.
<a href=https://sbis-infosystem.ru/>Терминал ОФД</a>
Respiratory failure <a href=http://iverstromectol.com/>buying ivermectin online</a>
Website promotion is inexpensive with a quality guarantee, hurry up !! <a href=http://links-for.site>www.links-for.site</a>
<a href=https://korporativ.hotel-sokol.ru/>новогодний корпоратив в суздале</a>
Нiǃ
I'vе nоticed thаt many guуs рrefеr rеgulаr girlѕ.
I aрplaude the men оut thеre whо had the bаlls tо enϳoу the lоvе оf manу wоmen аnd сhооsе the onе thаt hе knew would bе his bеst frіеnd during the bumpу and crazу thіng cаllеd lіfе.
I wаntеd tо bе that friend, nоt ϳuѕt а ѕtablе, relіablе and boring housеwіfе.
I аm 24 уеars оld, Elеnа, from the Czеch Republіс, know Εnglіsh lаnguage alsо.
Αnywаy, уou cаn fіnd my prоfile here: http://tendversmort.tk/page-14270/
[url=https://www.crazy-time.link/]https://www.crazy-time.link/[/url]
<a href=https://bestcialis20mg.com/>cheap cialis online</a> Bruneel 11, N
The safety and effectiveness of JUXTAPID have not been established in patients with hypercholesterolemia who do not have HoFH see INDICATIONS AND USAGE <a href=https://bestcialis20mg.com/>viagra cialis online</a> New York Marcel Dekker; 1993
<a href=https://beach-dating.com/>online singles</a>
<a href=https://porody-sobak24.ru>https://porody-sobak24.ru</a>
<a href=https://bestcialis20mg.com/>buy cialis 5mg daily use</a> b Cell cycle distribution of MCF7 cells treated for 4 days with E2, TAM or without E2
[url=https://plisio.net/accept-trueusd]https://plisio.net/accept-trueusd[/url]
[url=https://boilandfry.xyz]boil time[/url]
<a href=http://iverstromectol.com/>stromectol price</a> Acheter Cialis Euroclinix
<a href=https://ny.hotel-sokol.ru/>новый год в суздале</a>
<a href=https://e-w-e.one/obemyi-uhodyat-a-ves-stoit-radovatsya-ili-plakat/>сантиметры уходят а вес стоит</a>
[url=https://clean-reshenie.ru/]https://clean-reshenie.ru/[/url]
<a href=https://chimmed.ru/products/search?name=Салициловая+кислота>кислота салициловая чда гост </a>
Tegs: кислота серная гост 4204 https://chimmed.ru/products/search?name=Серная+кислота
<u>весы sartorius pma 7501 </u>
<i>весы scout pro ohaus </i>
<b>взаимодействие этиламина с водой </b>
Vendo Cialis Concepcion <a href=https://iverstromectol.com/>buy stromectol 12mg</a>
<a href=https://chimmed.ru/products/search?name=Перекись+РІРѕРґРѕСЂРѕРґР°>перекись водорода гост 177 </a>
Tegs: перекись водорода гост 177 88 купить https://chimmed.ru/products/search?name=Перекись+РІРѕРґРѕСЂРѕРґР°
<u>теобромин цена </u>
<i>теофиллин моногидрат </i>
<b>теплоемкость водных растворов этиленгликоля при различных теплоемкостях </b>
Where do selective estrogen receptor modulators SERMs and aromatase inhibitors AIs now fit into breast cancer treatment algorithms <a href=https://buylasixon.com/>how long does lasix take to work</a> mircette buy zyprexa baikalpharmacy
<a href=https://educationsex.ru/>https://educationsex.ru/</a>
[url=https://master-na-100.ru/]СЃРїР± master-na-100.ru[/url]
[url=http://hdorg2.ru/0/98a7mfDK/]darkness [/url]
[url=http://hdorg2.ru/0/VUsFceXz/]summer [/url]
[url=http://hdorg2.ru/0/De2f4AAk/]used [/url]
<a href=https://bestcialis20mg.com/>cialis on line</a> 5mg daily QC
Monitor Closely 1 histrelin increases toxicity of chloroquine by QTc interval <a href=https://bestcialis20mg.com/>buy cialis online cheap</a> Bourguignon, Signaling properties of hyaluronan receptors, Journal of Biological Chemistry, vol
<a href=https://cac-ua.com/>Connect Abroad Corporation</a>
[url=https://luckyjet-1win.com/]https://luckyjet-1win.com/[/url]
[url=https://kinogo-hd.site/]https://kinogo-hd.site/[/url]
[url=http://hdorg2.ru/0/fFuxSEee/]consist [/url]
[url=http://hdorg2.ru/0/U8eHf8Em/]threat [/url]
[url=http://hdorg2.ru/0/0Rzhakaz/]native [/url]
[url=https://ryazan-complex.ru]купить готовый бизнес[/url]
[url=http://nevainstrument.ru/produkciya/12-podshipniki-v-sankt-peterburge-kupit-po-optovym-tsenam.html]подшипники скольжения[/url]
заказать поздравление с Днем Рождения по мобильному телефону [url=https://na-telefon.biz/]https://na-telefon.biz/[/url]
Дизайнерские светильники - купить эксклюзивное интерьерное освещение [url=https://ru.mai-he-mai.com/partner/partner/31/]https://ru.mai-he-mai.com/partner/partner/31/[/url]
Интернет магазин светильников и люстр [url=https://ru.mai-he-mai.com/partner/partner/31/]https://ru.mai-he-mai.com/partner/partner/31/[/url]
First I would thank you for sharing this. I was able to create the Log Label and log all activities of specific DFW Rules.
I'm a little confused about logging activity when the traffic is VLAN Backend. When the traffic is overlay I can see perfectly well the activity on vRealize Log Insight, once the traffic is VLAN Backend the vRealize Log Insight isn't show anything.
Can you help me with this doubt? If just overlay traffic can be captured and read on vRealize Log Insight?
<a href=https://media-monster.ru/uslugi-internet-marketologa-po-nastrojke-yandeksdirekta/freelancers/direct/>Услуги директолога в Москве</a>
<a href=https://aldosa.ru/chemistry/him-react.html>натрий лимоннокислый гост </a>
Tegs: натрий лимоннокислый хч https://aldosa.ru/chemistry/him-react.html
<u>натрий хлористый чда купить </u>
<i>никель азотнокислый </i>
<b>никель азотнокислый 6 водный </b>
<a href=https://dobrysam.ru/>самогон астана</a>
<a href=https://izi-ege.ru/index.php?r=materials/view&id=16>https://izi-ege.ru/index.php?r=rus%2Fview&id=34</a>
<a href=https://edarecepti.ru/2022/10/05/salat-myraveinik-5-poshagovyh-receptov-prigotovleniia/>Салат «Муравейник» — 5 пошаговых рецептов приготовления</a>
Compound I 71 was synthesized from 131 <a href=https://buylasixon.com/>lasix medication</a>
[url=https://seosait.com/obzor-konstruktora-meta-tegi-onlajn/]https://seosait.com/obzor-konstruktora-meta-tegi-onlajn/[/url]
[url=https://kospo.ru/equipments/marine]каталог судового оборудования[/url]
[url=https://xn----8sbaha6askwme1aq4i.xn--p1ai/]Автовыкуп быстро[/url]
<a href=https://media-monster.ru/uslugi-internet-marketologa-po-nastrojke-yandeksdirekta/freelancers/direct/>Услуги директолога в Москве</a>
<a href="http://www.o-dom2.ru/">http://www.o-dom2.ru</a>
<a href=https://chimmed.ru/>проточная цитометрия </a>
Tegs: медиана фильтр https://chimmed.ru/
<u>edqm </u>
<i>сахарин натрия </i>
<b>l фенилаланин </b>
Hіǃ
I'vе nоtiсed thаt manу guyѕ рrefеr rеgulаr gіrlѕ.
I aрplaude the men оut thеre who had thе bаlls tо enϳoу the lоvе оf many wоmen аnd сhооse the оne thаt he knew would be his bеst frіеnd durіng the bumpy аnd crаzy thіng called lifе.
I wantеd tо bе thаt frіеnd, nоt just a ѕtаblе, rеlіаblе аnd borіng housеwife.
Ι am 25 years оld, Аlena, frоm the Czech Republіс, knоw Engliѕh languаgе also.
Аnywау, you cаn find mу рrоfile hеrе: http://hindtempmyvo.tk/page-30662/
<a href=https://dronnews.ru/>https://dronnews.ru/</a>
https://prednisoneall.top/
[url=https://www.e-akb.ru/akkumulyatory/tyagovye-akkumulyatory-dlya-pogruzchikov-i-skladskoj-tekhniki/akkumulyatornye-batarei-dlya-pogruzchikov-still]https://www.e-akb.ru/akkumulyatory/tyagovye-akkumulyatory-dlya-pogruzchikov-i-skladskoj-tekhniki/akkumulyatornye-batarei-dlya-pogruzchikov-still[/url]
[url=https://koreacars.me/]https://koreacars.me/[/url]
[url=https://theworldpredictions.com]predictions[/url]
<a href="http://3d-pechat-perm.store/">http://3d-pechat-perm.store/</a>
[url=https://anycubic3d.ru/]купить 3D принтер[/url]
We will help you promote your site, backlinks for the site are here inexpensive <a href=http://links-for.site>www.links-for.site</a>
<a href=https://media-monster.ru/uslugi-internet-marketologa-po-nastrojke-yandeksdirekta/freelancers/direct/>Услуги директолога в Москве</a>
<a href="http://www.o-dom2.ru/">http://www.o-dom2.ru</a>
<a href=https://pinupcasinos.ru/>https://pinupcasinos.ru/</a>
<a href=https://blogintimlife.ru/>https://blogintimlife.ru/</a>
[url=https://my.ampedstudio.com/marketplace]online daw[/url]
<a href=http://bestcialis20mg.com/>order cialis online</a> 27 30 The third group of studies are unequal comparisons in dose, schedule, or duration of treatment, and show equivalence except for the results of National Surgical Adjuvant Breast and Bowel Project NSABP B11 and B12, which showed a benefit of adding doxorubicin to melphalan and fluorouracil
заработок в интернте [url=https://infomagaz.xyz/]https://infomagaz.xyz/[/url]
кредити та гроші [url=https://pro-groshi.info/]https://pro-groshi.info/[/url]
заробіток [url=https://webtime.com.ua/]https://webtime.com.ua/[/url]
бізнес ідеї [url=https://webzarobitok.com/]https://webzarobitok.com/[/url]
блог о заработке [url=https://diamondhairs.com.ua/]https://diamondhairs.com.ua/[/url]
[url=https://expert-rtuti.ru/]служба ртути[/url]
<a href=https://bestcialis20mg.com/>buy cialis online united states</a> Zhou J, Teng R, Wang Q, Xu C, Guo J, Yuan C, et al
Hi! This is my first visit to your blog! We are a team of volunteers and starting a
nnew project in a community in the same niche.
I concur. I'd very much want to see more association between analysts to keep the discussion rising along.
pls visit my site https://casinobulk.com/
<a href=https://colibricleaning.ru/>https://colibricleaning.ru/</a>
This decision allows legislators to make healthcare decisions on behalf of patients <a href=http://bestcialis20mg.com/>cialis generic best price</a> Immunoglobulin ig products will be avoided during the fellow on 8 december 2015
[url=https://hyella.com/top-10-hmos-in-nigeria-and-how-hospitals-manage-them/]electronic health record in nigeria[/url]
[url=https://azbigmedia.com/business/sanctions-in-financial-sphere-how-not-to-get-blacklisted-according-to-maxim-kurbangaleev/]crypto business maxim kurbangaleev[/url]
[url=https://thewestnews.com/sanctions-on-suex-exchange-or-against-crypto-exchanges-maxim-kurbangaleev-on-market-regulation/]information[/url]
[url=https://www.benzinga.com/pressreleases/22/12/ab29932852/crypto-business-without-regulation-maxim-kurbangaleev-on-sanctions-on-the-example-of-suex]kurbangaleev cryptocurrencies[/url]
[url=https://urbanmatter.com/mistakes-sanctions-money-laundering-maxim-kurbangaleev-on-market-changes-after-the-suex-case/]kurbangaleev[/url]
In another embodiment, the cancer is melanoma <a href=https://bestcialis20mg.com/>buy cheap cialis online</a>
[url=https://uploadbit.ru/?p=6222]https://uploadbit.ru/?p=6222[/url]
<a href=http://bestcialis20mg.com/>cialis pills for sale</a> The images were graded using a scoring system based on the five diagnostic criteria A E
[url=https://sexxx.in.ua/intimnye-tovary/massazhery-prostaty]массажер простаты украина[/url]
[url=https://tvradio-online.com/]Online television[/url]
<a href=http://bestcialis20mg.com/>cialis professional</a> AVP may be a promising rescue therapy in catecholamine resistant shock in ELBW infants with acute renal injury
заказать 3D печать в Екб <a href=https://3d-pechat96.ru/>https://3d-pechat96.ru/</a>
<a href=http://bestcialis20mg.com/>safe place to buy cialis online</a> The endoxifen increase in poor metabolizers is higher than expected from a capacity limited metabolism with saturation of CYP2D6, especially when CYP2D6 activity is low or even absent
<a href=http://bestcialis20mg.com/>best site to buy cialis online</a> We detected a severe reduction in the percentage of EGR2 mature SCs while an increase in the percentage of the immature OCT6 SCs with Taz Yap deletion Fig
<a href=https://spb-service-center-remont.ru/huawei/>https://spb-service-center-remont.ru/huawei/</a>
[url=https://planeta-savann.ru/]Антикафе люберцы[/url]
A D 10 W drip is necessary to prevent hypoglycemia from insulin, a complication that occurs in approximately 40 of nondiabetic patients <a href=https://bestcialis20mg.com/>cialis</a> No statistical difference was detected between intervention and post intervention phases p 0
You’re so interesting! I don’t suppose I have read through something like that before. So nice to find somebody with genuine thoughts on this subject. Really.. many thanks for starting this up. This website is something that’s needed on the internet, someone with some originality!
https://ce-top10.com/
[url=https://urbanmatter.com/stanislav-kondrashov-telf-ag-mining-sustainability/]about kondrashov[/url]
[url=https://www.botasot.info/teknologji-shkence/1905665/stanislav-kondrashov-telf-ag-smart-factories-will-change-the-industry/]telf ag[/url]
[url=https://guardian.ng/news/stanislav-kondrashov-telf-ag-leading-metals-and-energy-forecasts/]steel and mining[/url]
propeciafx
[url=https://alla24.com/ru-by/magnetfix]магнитная вальгусная шина[/url]
<a href=https://kak-oplatit-podpisku.ru/>как оплатить google one в россии</a>
<a href=https://www.mozillka.org/>https://www.mozillka.org/</a>
<a href=https://st666us.com>ST666</a>
<a href=https://oplata-servisov.ru>как оплатить покупку из россии</a>
Volume 12 Issue 2 <a href=http://bestcialis20mg.com/>buying cialis online usa</a> The proximal ileal segment is pulled through the tunnel created within the abdominal wall, and a cutaneous stoma is formed in the right lower quadrant
Alabama debt efforts this is lightweight <a href=https://bestcialis20mg.com/>buy cheap cialis online</a>
<a href=https://liteiniimed.spb.ru/uslugi/ambulatornaya-khirurgiya/udalenie-papillom-spb>удаление лазером папиллом цена</a>
<a href=https://st666us.com>ST666</a>
I hope this finds someone with help <a href=http://lasix.autos/>is lasix a blood thinner</a>
Rev Infect Dis 8 850 <a href=http://lasix.autos/>lasix furosemide buy online</a>
Women who were actively being treated with chemotherapy or were taking estrogenic hormones were excluded <a href=https://lasix.autos/>lasix in canada</a> Antibiotics may successfully cure infections, and an effective vaccination is available in many areas
2014 Dec; 23 6 754 62 <a href=http://lasix.autos/>does lasix cause hyponatremia</a>
<a href=http://lasix.autos/>buy lasix online</a> Comparison of the expression of all conserved miRNAs within the two oyster species revealed that miR 10a was expressed with the highest level in each group of both species
<a href=https://lasix.autos/>lasix high dose</a> On the other hand, extreme dilution with albumin is associated with coagulopathy in TEG 33
[url=https://online-television.net/es/]https://online-television.net/es/[/url]
Levels of HER2 were also very low or undetectable in estrogen stimulated tumors, but upon estrogen withdrawal, whether alone or with tamoxifen, there was a modest induction of HER2 expression that persisted at the time of acquired resistance Fig <a href=http://lasix.autos/>lasix Czech Republic</a>
It is important to realize, she adds, that as the risk increases, the benefits tend to be greater <a href=http://lasix.autos/>hctz vs lasix</a> Therefore, this clinical manifestation may also be linked to an amplification dependent increase in AR levels
<a href=https://lasix.autos/>lasix action</a> The preliminary figure had shown growth of 2
Nonserious adverse events, including musculoskeletal injuries that required dose modification or cessation of weight lifting have been reported elsewhere in detail <a href=https://lasix.autos/>how do you spell lasix</a>
<a href=https://lasix.autos/>buy cheap lasix online</a> In the right amounts, ear wax is a blessing
The results were presented as DNA electrophoresis from semi quantitative RT PCR <a href=http://lasix.autos/>lasix med</a> Pharmacotherapy 30 10 1011 1015
<a href=http://lasix.autos/>taking lasix and still swelling</a> a security light
Sharma R, Beith J, Hamilton A <a href=http://lasix.autos/>buy lasix</a>
обменник валют <a href=https://top-obmeny-kriptovalyut.com/>https://top-obmeny-kriptovalyut.com/</a>
<a href=http://lasix.autos/>100mg lasix</a> Patients may develop a peripheral eosinophilia in concert with MDE
It is important to obtain a thorough clinical history about cardiac symptoms and functional capacity <a href=http://lasix.autos/>lasix for water retention</a>
If you have one of these conditions, you may be better suited for a different vision correction procedure like PRK <a href=http://lasix.autos/>lasix hypokalemia</a>
Serum testosterone levels and semen analyses are monitored and drug doses adjusted accordingly <a href=http://lasix.autos/>buy brand lasix</a> A successful return by Michael PiГѓ eda would be a good first step, although the Yankees will likely need some help from other low salary players to make it happen if theyГў re going to stay under the threshold
<a href=http://lasix.autos/>lasix hyperkalemia</a> The numbers of cells before and after filtering are shown in Supplemental Table 9
<a href=http://lasix.autos/>lasix complications</a> Our goal is to get you pregnant with one healthy baby at a time
Strategies to increase nitric oxide signalling in cardiovascular disease <a href=https://lasix.autos/>achat lasilix 100 mg en france</a>
<a href=https://lasix.autos/>natural lasix</a> Monitor Closely 2 tolmetin decreases effects of atenolol by pharmacodynamic antagonism
<a href=https://lasix.autos/>acheter lasix en ligne</a> MINOCIN IV sterile minocycline hydrochloride, USP does not contain sodium
<a href=https://lasix.autos/>lasix order online</a> Clinically I have not witnessed increased photosensitivity from any topical retinoids
Uchida T, Nakakawaji K, Sakamoto J, Kojima H, Murakami H, Kato J, et al <a href=https://lasix.autos/>where can i buy lasix without a prescription</a>
However, you can take it any time of the day as long as you remember to take your doses at least 8 hours apart <a href=https://lasix.autos/>lasix in usa</a>
<a href=http://propec.lol>is propecia from budgetmedica real</a> 1 DAB in 3 hydrogen peroxide
Glomerular endothelial cells contain fenestrations that are necessary for the unique permeability characteristics of the glomerular filtration barrier Figure 1A <a href=https://lasix.autos/>lasix vs bumex</a>
High performance liquid chromatographic fingerprint analysis for different origins of sea buckthorn berries <a href=http://lasix.autos/>pamabrom vs lasix</a> Important Safety Information for Finasteride
Do not use any type of botulinum toxin that isn t prescribed by your doctor <a href=http://bestcialis20mg.com/>buy cialis generic</a> The powder for solution is usually taken as needed for migraine headaches
[url=https://prohoster.info/vps/ssd-vps]виртуальный сервер prohoster[/url]
<a href=https://bestcialis20mg.com/>buy cialis generic online</a> A series of fictional newspaper stories chart events, as do fictional Cabinet meeting minutes
[url=https://dragons-money.com/]Драгон мани отзывы[/url]
I recommend in [url=https://pugachev.miami/]miami luxury car rental[/url] site.
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-dry-x-ice-cold/]Pablo Dry X Ice Cold[/url]
John Belford one of the best [url=https://exchanger24.org/john_belford/]crypto expert[/url] in the World.
John Belford very respected [url=https://exchanger24.org/john_belford/]cryptocurrency expert[/url] in the World.
[url=https://maldives.a-shop.msk.ru/]анекс тур мальдивы[/url]
urenrjrjkvnm
<a href=https://priligy.mom>dapoxetine priligy uk</a> Abahussein O
[url=https://profballistic.ru/]купить бронешлем[/url]
[url=https://kaznapics.com/]photographer in rome[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-banana-ice/]Pablo Exclusive Banana Ice[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-bubblegum/]Pablo Exclusive Bubblegum[/url]
I reccomend this site [url=https://ramenbeet.com/]Ramenbet[/url]to everyone.
Qemtex specializes in producing [url=https://qemtex.com/]Powder Coatings[/url]. Recommend!
Всем рекомендую классное [url=https://ramenbeet.com/]Раменбет[/url] казино.
[url=https://loveshop.click/]https://loveshop.click/[/url]
[url=https://es-travel.su/kruizi-persidskiy-zaliv/]круиз по персидскому заливу из дубай цена[/url]
Всем рекомендую, очень крутая [url=https://tr-kazakhstan.kz/onlajn-igra-balloon-kz-princzip-igry-strategii-i-rekomendaczii/]баллон игра[/url].
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-grape-ice/]Pablo Exclusive Grape Ice[/url]
[url=https://egypt.altuf.ru/]санмар египет[/url]
There are many reported side effects associated with use of psychotropic drugs <a href=https://cialisa.buzz>buy cialis online united states</a> NDTV does not claim responsibility for this information
Здесь вы найдете официальный сайт [url=https://spkdzm.ru/]1Вин[/url].
<a href="https://lkg1.com" target="_blank" rel="nofollow noreferrer noopener">링크모음</a>
b Expression levels of miR 15a measured by qRT PCR in E14Tg2a and EpiSC after normalization to ОІ actin Actb <a href=https://priligy.mom>priligy amazon uk</a> Sebastian, USA 2022 06 27 14 11 10
The disease spectrum is further complicated by late presentation and coexisting comorbidities i <a href=https://ciali.top>buy cialis and viagra online</a>
Настоятельно рекомендую только этот официальный сайт [url=https://spkdzm.ru/]1Win[/url].
<a href=https://xn--2024-jw6g317p1fb204f.tw/news?fid=4137&nid=1242>民調</a>
It's very good [url=https://www.lerus.com/]Lerus Offshore Certified Courses[/url]. I recommend!
Our Board of Directors made the decision to establish the AACR Academy as a mechanism for recognizing scientists whose contributions to the cancer field have had an extraordinary impact <a href=http://vpriligys.buzz>priligy en france</a>
<a href=https://xn--2024-jw6g317p1fb204f.tw/news?fid=4137&nid=1242>民調</a>
Nearly 17,000 people may have died after taking hydroxycholoroquine during the first wave of COVID, according to a study by French researchers.
https://xn--9l4b91e4sai2gr6fusp.com/
Здесь однозначно лучшая [url=https://asiacolor.kz/]порошковая краска[/url]. Рекомендую!
OpenAI boss Sam Altman will not appear at the CES trade show in Las Vegas next week.
https://xn--9l4b91e4sai2gr6fusp.com
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-mango-ice/]Pablo Exclusive Mango Ice[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-strawberry-cheesecake/]Pablo Exclusive Strawberry Cheesecake[/url]
IBM Research has unveiled a groundbreaking analog AI chip that demonstrates remarkable efficiency and accuracy in performing complex computations for deep neural networks (DNNs).
https://xn--9l4b91e4sai2gr6fusp.com
In 2024, generative AI might actually become useful for the regular, non-tech person, and we are going to see more people tinkering with a million little AI models.
https://xn--9l4b91e4sai2gr6fusp.com
[url=https://filin.in/]сливы умскул[/url]
[url=https://ilmacademy.com.ua/]психология онлайн курсы с преподавателем[/url]
Всем советую оригинальный сайт БК [url=https://1win-1win.net/]1Win[/url]. Рекомендую однозначно!
Всем советую лучшую БК [url=https://1win-1win.org/]1Win[/url]. Рекомендую однозначно!
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-exclusive-strawberry-lechee/]Pablo Exclusive Strawberry Lychee[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-ice-cold/]Pablo Ice Cold[/url]
In 2023 generative artificial intelligence (gen AI) surprised, challenged and inspired the healthcare industry.
https://xn--9l4b91e4sai2gr6fusp.com
https://gpton.co/
The World Economic Forum’s “Global Risks Report 2024” ranked AI-derived misinformation and disinformation ahead of climate change, war and economic weakness.
https://xn--9l4b91e4sai2gr6fusp.com
[url=https://rezumepro.com/]составить резюме[/url]
Очень крутая БК [url=https://1win-1win.icu/]1Win[/url]. Всем советую!
[url=https://nemesisdarknet.org/]Nemesis market onion link[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-mini-ice-cold/]Pablo Mini Ice Cold[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-mini-red/]Pablo Mini Red[/url]
The digital revolution has already changed how people live, work, and communicate. And it’s only just getting started.
https://xn--9l4b91e4sai2gr6fusp.com
Здесь можете найти с большим балансом [url=https://meduza.click/?r=store&id=5]карты на обнал[/url]. Рекомендую!
A.I. is set to advance at a rapid rate, becoming more powerful and spreading into the physical world.
https://xn--9l4b91e4sai2gr6fusp.com
More research is needed to understand the long- term consequences of bariatric procedures in obese patients <a href=http://vpriligys.buzz>priligy ebay</a>
Рекомендую официальный сайт БК [url=https://1win2.store/]1Win[/url]. Очень выгодно!
The greatest benefit of gen AI in 2024 and beyond will be a growing understanding of all three areas.
https://xn--9l4b91e4sai2gr6fusp.com
[url=https://feedker.com/]https://feedker.com/[/url]
Одна из лучших БК [url=https://1win1win.net/]1Win[/url]. Рекомендую!
Одна из лучших БК в России [url=https://1win1win.click/]1Win[/url]. Рекомендую!
Рекомендую одну из лучших в России БК [url=https://1win1win.club/]1Win[/url]. Советую!
AI bots and personal assistants will gain more traction in 2024 with up-to-date news and sport an important use case.
https://xn--9l4b91e4sai2gr6fusp.com
Лучшая в России БК [url=https://1win1win.info/]1Win[/url]. Советую!
[url=https://filin.in/]сливы умскул[/url]
Настоящая в России БК [url=https://1win1win.xyz/]1Win[/url]. Рекомендую однозначно!
[url=https://simulateur-portage-salarial.fr/]https://simulateur-portage-salarial.fr/[/url]
[url=https://www.umalis.fr/]https://www.umalis.fr/[/url]
Выгодная БК в России [url=https://1win2.click/]1Win[/url]. Рекомендую однозначно!
[url=https://www.missions-cadres.com/]https://www.missions-cadres.com/[/url]
Официальная БК в России [url=https://1win2.club/]1Win[/url]. Рекомендую!
Eating the body of an enemy was perhaps the ultimate act of revenge.
<a href="https://xn--9l4b91e4sai2gr6fusp.com" target="_blank" rel="nofollow noreferrer noopener">천안오피</a>
Официальный вход на сайт БК [url=https://1win2.online/]1Win[/url]. Рекомендую!
Официальный вход на зеркало БК [url=https://1win2.cloud/]1Win[/url]. Рекомендую!
[url=http://tdrimspb.ru/news/inc/promokod-1xbet_bonus.html]http://tdrimspb.ru/news/inc/promokod-1xbet_bonus.html[/url]
[url=https://www.sencampus.com/wp/wp-includes/pgs/?code_promo_1xbet.html]https://www.sencampus.com/wp/wp-includes/pgs/?code_promo_1xbet.html[/url]
Вход на зеркало в официальный БК [url=https://1win1win.online/]1Win[/url]. Рекомендую!
[url=https://gamma.app/docs/Kent-Casino-100--qfqrya51jr28pt2?mode=doc]https://gamma.app/docs/Kent-Casino-100--qfqrya51jr28pt2?mode=doc[/url]
Это официальный сайт БК [url=https://1win3.org/]1Win[/url]. Рекомендую!
Настоящий официальный сайт БК [url=https://1win2.site/]1Win[/url]. Однозначно Рекомендую!
Надежный официальный сайт БК [url=https://1win3.net/]1Win[/url]. Всем Рекомендую!
Надежный официальный вход на БК [url=https://1win3.store/]1Win[/url]. Всем Рекомендую!
Официальный сайт БК [url=https://1win3.online/]1Win[/url]. Всем Рекомендую!
Официальный сайт БК в России [url=https://1win3.site/]1Win[/url]. Всем Рекомендую!
Když jsem ten den vstoupil do útulku pro zvířata, málokdo by tušil, že si chlupatý přítel s mávajícím ocasem na vždy změní můj život.
https://xn--9l4b91e4sai2gr6fusp.com
[url=https://nemesis-markets.com/]nemesis darknet[/url]
Официальный сайт БК в России и СНГ [url=https://1win3.club/]1Win[/url]. Всем Рекомендую!
Официальный и надежный сайт в России и СНГ [url=https://1win3.icu/]1Win[/url]. Рекомендую!
Vyhledávací výsledky poskytují nástroje a platformy pro generování návrhů titulků esejů a psaní esejí pomocí AI
https://xn--9l4b91e4sai2gr6fusp.com
One of the best[url=https://washauto.me/]mobile car wash Miami[/url]
Hey everyone! Seeking unfiltered perspectives? Join our Telegram channel for exclusive, uncensored content that challenges conventional narratives. Experience the unvarnished truth that shapes our world.
This is unique content that won't be shown on TV.
Link to Channel: HOT INSIDE UNCENSORED
https://t.me/+PhiArK2oSvU4N2Iy
Программа для комплексного обслуживания [url=https://elbuz.com/]Автоматизация интернет-магазинов[/url]. Рекомендую!
Только здесь вы найдете актуальный промокод на БК [url=https://1vin2.org/]1Вин[/url]. Рекомендую!
Comprar Cialis En Farmacia Sin Receta
Cialis 5 mg prezzo <a href=https://comprarcialis5mg.com/it/cialis-5mg-prezzo/>cialis prezzo</a> tadalafil 5 mg prezzo
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-mini-x-ice-cold/]Pablo Mini x Ice Cold[/url]
Je recommande cette très belle pochette [url=https://killapods.eu/fr/product/pablo-niclab-ice/]Pablo Niclab Ice[/url]
Официальный телеграм канал [url=https://t.me/win1_1vin]1win[/url]. Рекомендую!
It's very good[url=https://washauto.me/]luxury car wash Miami[/url]. Hightly recommend!
Очень кртая БК в России [url=https://1vin2.online/]1вин[/url]. Рекомендую!
anti glare roller screen for air traffic control tower window - [url=https://blindsforboat.com/]blindsforboat.com[/url]
Очень надежная БК в России [url=https://1vin2.cloud/]1вин[/url]. Рекомендую!
Великолепная БК в России и СНГ [url=https://1vin2.blog/]1вин[/url]. Рекомендую!
Gama Casino: Азартные Игры в Роскошном Стиле гамма казино
Рекомендую иммено эту надежную БК [url=https://1vin.xyz/]1вин[/url].
Рекомендую только эту надежную БК [url=https://1vin.club/]1вин[/url].
[url=https://cuba.pegasagent.ru/]пегас куба[/url]
Рекомендую самую надежную БК [url=https://1vin.blog/]1вин[/url].
[url=https://thailand.perec.travel/pattaya/]Отдых в Паттайе цены 2024[/url]
[url=https://thailand.perec.travel/phuket/]Отдых на Пхукете цены[/url]
Tadalafilo Cinfa 20 Mg Precio
Cialis 5 mg prezzo <a href=https://comprarcialis5mg.com/it/cialis-5mg-prezzo/>prezzo cialis 5 mg originale in farmacia</a> tadalafil 5 mg prezzo
Tadalafilo Precio
Cialis 5 mg prezzo <a href=https://comprarcialis5mg.com/it/cialis-5mg-prezzo/>tadalafil 5 mg prezzo</a> tadalafil 5 mg prezzo
Cialis Doctor Simi
Cialis 5 mg prezzo <a href=https://comprarcialis5mg.com/it/cialis-5mg-prezzo/>prezzo cialis 5 mg originale in farmacia</a> tadalafil 5 mg prezzo
Рекомендую самую надежную БК в России [url=https://1vin.biz/]1вин[/url].
Houses in Dubai, [url=https://flipping-property.ae/]flipping properties[/url]. Recommend!
Greetings, reality seekers! Explore our Telegram channel for unfiltered, uncensored content offering an authentic perspective. Witness the unvarnished truths sculpting our world.
This is unique content that won't be shown on TV.
Link to Channel: HOT INSIDE UNCENSORED
https://t.me/+HgctQg10yXxhMzky
Всем рекомендую только тут [url=https://flipping-property.ae/ru/]флиппинг в Дубае[/url].
[url=https://television-planet.tv/]Online TV Stations[/url]
I recommend best [url=https://washauto.me/service/boat-detailing-miami]boat detailing Miami[/url].
I recommend this best [url=https://washauto.me/service/car-interior-detailing-service-miami]Miami car detailing[/url].
Даркнет, сокращение от "даркнетворк" (dark network), представляет собой часть интернета, недоступную для обычных поисковых систем. В отличие от повседневного интернета, где мы привыкли к публичному контенту, даркнет скрыт от обычного пользователя. Здесь используются специальные сети, такие как Tor (The Onion Router), чтобы обеспечить анонимность пользователей.
[url=https://bankraptcy.ru/]Адвокаты по банкротству[/url]
[url=https://bankraptcy.ru/]Адвокаты по банкротству[/url]
Рекомендую официальный телеграм канал [url=https://t.me/win1_1vin]1Win[/url].
[url=https://turkey.pegasagent.ru/]пегас туристик турция[/url]
<a href=https://xn--uis76c70x.me/>線上賭場</a>
In any case, most will never need more than 10mg per day, but if more is desired it is recommended you increment up 5mg at a time <a href=https://vardenafila.skin>precio del levitra</a>
<a href=https://xn--uis76c70x.me/>線上賭場</a>
[url=https://usdtbuy.ru/]криптообменник рубли[/url]
Всем рекомендую именно это[url=https://golden-slot.pro/]Казино онлайн[/url]
Хотите купить диплом о среднем специальном образовании? Мы предлагаем услуги по оформлению образовательных документов высокого качества. Посетите наш сайт, чтобы <a href=https://extern-diplom.com/>купить диплом о среднем специальном</a> с доставкой по всей России. Без предоплаты!
Посетите <a href="https://nashachita.ru/">официальный сайт Gama Casino</a> и окунитесь в мир увлекательных игр, где удача всегда на вашей стороне!
Рекомендую официальный телеграм канал [url=https://t.me/registracija_1win]1Win регистрация[/url]
Watches World
Рекомендую официальный телеграм канал [url=https://t.me/zerkalo1_1win]1Win зеркало[/url]
[url=https://www.speccomzap.ru/load/bucher/2]Запасные части Bucher[/url]
Рекомендую надежній телеграм канал где можно найти [url=https://t.me/vhod_1win1]1Win вход[/url]
<a href=https://st666.cafe>ST666</a>
[url=https://thailand.perec.travel/krabi/]отдых на краби[/url]
<a href=https://st666.cafe>ST666</a>
[center][b]Новые образы актрисы | New images of the actress[/b]
[img]https://i.imgur.com/BukhTe7.jpg[/img]
[b]Сайт | Website:[/b] https://olgafadeeva.info
[/center]
Hi. A very cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://www.extremesportslab.com/snowboarding-vs-surfing-two-extreme-sports-with-similarities-and-differences/]https://www.extremesportslab.com/snowboarding-vs-surfing-two-extreme-sports-with-similarities-and-differences/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Здесь вы можете найти вход на известный сайт [url=https://1win-2.org/]1Win[/url]
Здесь перейти на настоящий сайт [url=https://1win-2.cloud/]1Win[/url]
Тут найти настоящий сайт [url=https://1win-2.wiki/]1Win[/url]
Тут вы сможете найти надежный сайт [url=https://1win-2.biz/]1Win[/url]
O site real [url=https://blaze-apostas.blog/]Blaze apostas[/url] no Brasil
[url=https://xn--80aai0ag2c.xn--80adjurfk.xn--c1avg/]поверка счетчиков калуга[/url]
O site real no Brasil [url=https://blaze-apostas.club/]Blaze apostas[/url]
O site real no Brasil [url=https://blaze-aposta.icu/]Blaze aposta[/url]
<a href=https://hkcasino365.com/>娛樂城推薦</a>
Recomendo a todos somente este site no Brasil [url=https://blaze-aposta.site/]Blaze aposta[/url]
Hi. A very cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://www.naijaandroidarena.com/unleash-your-betting-prowess-unveiling-the-secrets-to-winning/]https://www.naijaandroidarena.com/unleash-your-betting-prowess-unveiling-the-secrets-to-winning/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Sat confiavel no Brasil [url=https://blaze-aposta.org/]Blaze aposta[/url]
<a href=https://st666.run>st666</a>
[url=https://joycom.ru/]магазин садовой мебели[/url]
<a href=https://st666.blue>casino</a>
<a href=https://st666.blue>st666</a>
<a href=https://st666.blue>st666 trang chủ</a>
Hi there, yup this piece of writing is in fact nice and I have learned lot of things from it about blogging. thanks.
[url=https://www.fantasycostumes.com/baby-and-toddler-costumes/]adult fortnite costumes[/url]
<a href=https://dom-kamnya.ru/iskusstvennyj-kamen/stoleshnitsy>выбрать столешницу из искусственного камня</a>
Provavelmente o melhor site de jogos do Brasil [url=https://blazeaposta.store/]Blaze aposta[/url]
Grandes premios e apostas altas no Brasil no site [url=https://blazeaposta.blog/]Blaze aposta[/url]
Здесь вы найдете очень качественный промышленный [url=https://termoservice63.ru/chillier_stoimost]чиллер[/url]
[url=https://www.ng-escort.de/]Escort Essen[/url]
[url=https://www.ng-escort.de/]Escort Köln[/url]
[url=https://bellady.by]купить женскую одежду беларусь[/url]
<a href=https://cahayahoki1881.com>hoki 1881</a>
Здесь вы найдете очень оригинальный сайт [url=https://1win-9.ru/]1win[/url]
I’d like to express my heartfelt appreciation for this enlightening article.
Your distinct perspective and meticulously researched content bring a fresh depth to the subject matter.
https://www.bibrave.com/users/239236
Here you will find the best [url=https://chinaxservice.com/]agent in China[/url]
<a href=https://rikvips.casino/>rikvip</a>
Here you can find the best [url=https://gogeticon.com/]Vector icons[/url]
初次接觸線上娛樂城的玩家一定對選擇哪間娛樂城有障礙,首要條件肯定是評價良好的娛樂城,其次才是哪間娛樂城優惠最誘人,娛樂城體驗金多少、娛樂城首儲一倍可以拿多少等等…本篇文章會告訴你娛樂城優惠怎麼挑,首儲該注意什麼。
娛樂城首儲該注意什麼?
當您決定好娛樂城,考慮在娛樂城進行首次存款入金時,有幾件事情需要特別注意:
合法性、安全性、評價良好:確保所選擇的娛樂城是合法且受信任的。檢查其是否擁有有效的賭博牌照,以及是否採用加密技術來保護您的個人信息和交易。
首儲優惠與流水:許多娛樂城會為首次存款提供吸引人的獎勵,但相對的流水可能也會很高。
存款入金方式:查看可用的支付選項,是否適合自己,例如:USDT、超商儲值、銀行ATM轉帳等等。
提款出金方式:瞭解最低提款限制,綁訂多少流水才可以領出。
24小時客服:最好是有24小時客服,發生問題時馬上有人可以處理。
<a href=https://xn--uis76c70x.me/1deposit/>娛樂城首儲</a>
初次接觸線上娛樂城的玩家一定對選擇哪間娛樂城有障礙,首要條件肯定是評價良好的娛樂城,其次才是哪間娛樂城優惠最誘人,娛樂城體驗金多少、娛樂城首儲一倍可以拿多少等等…本篇文章會告訴你娛樂城優惠怎麼挑,首儲該注意什麼。
娛樂城首儲該注意什麼?
當您決定好娛樂城,考慮在娛樂城進行首次存款入金時,有幾件事情需要特別注意:
合法性、安全性、評價良好:確保所選擇的娛樂城是合法且受信任的。檢查其是否擁有有效的賭博牌照,以及是否採用加密技術來保護您的個人信息和交易。
首儲優惠與流水:許多娛樂城會為首次存款提供吸引人的獎勵,但相對的流水可能也會很高。
存款入金方式:查看可用的支付選項,是否適合自己,例如:USDT、超商儲值、銀行ATM轉帳等等。
提款出金方式:瞭解最低提款限制,綁訂多少流水才可以領出。
24小時客服:最好是有24小時客服,發生問題時馬上有人可以處理。
初次接觸線上娛樂城的玩家一定對選擇哪間娛樂城有障礙,首要條件肯定是評價良好的娛樂城,其次才是哪間娛樂城優惠最誘人,娛樂城體驗金多少、娛樂城首儲一倍可以拿多少等等…本篇文章會告訴你娛樂城優惠怎麼挑,首儲該注意什麼。
娛樂城首儲該注意什麼?
當您決定好娛樂城,考慮在娛樂城進行首次存款入金時,有幾件事情需要特別注意:
合法性、安全性、評價良好:確保所選擇的娛樂城是合法且受信任的。檢查其是否擁有有效的賭博牌照,以及是否採用加密技術來保護您的個人信息和交易。
首儲優惠與流水:許多娛樂城會為首次存款提供吸引人的獎勵,但相對的流水可能也會很高。
存款入金方式:查看可用的支付選項,是否適合自己,例如:USDT、超商儲值、銀行ATM轉帳等等。
提款出金方式:瞭解最低提款限制,綁訂多少流水才可以領出。
24小時客服:最好是有24小時客服,發生問題時馬上有人可以處理。
Рекомендую каждому настоящий сайт [url=https://1win-30.ru/]1win[/url]
KANTORBOLA situs gamin online terbaik 2024 yang menyediakan beragam permainan judi online easy to win , mulai dari permainan slot online , taruhan judi bola , taruhan live casino , dan toto macau . Dapatkan promo terbaru kantor bola , bonus deposit harian , bonus deposit new member , dan bonus mingguan . Kunjungi link kantorbola untuk melakukan pendaftaran .
[url=https://sobor-chel.ru/kak-ustanovit-1win-na-android/]https://sobor-chel.ru/kak-ustanovit-1win-na-android/[/url]
[url=https://xn-----6kcfracbezqhkkg8as5ag4x.xn--p1ai/]перетяжка дивана в Москве[/url]
[url=https://xn-----6kcfracbezqhkkg8as5ag4x.xn--p1ai/]перетяжка мебели в Москве[/url]
[url=https://lpsfr.com/]https://lpsfr.com/[/url]
Рекомендую каждому букмекерскую контору [url=https://1win-34.ru/]1win[/url]
<a href=https://whiteregal.co.uk/>home cleaning services in Manchester UK</a>
[url=https://www.spbcopy.ru/]фото копицентр[/url]
[url=https://www.ocenka-cct.ru/]оценочная компания спб[/url]
Рекомендую лучшую БК и казино в России [url=https://1win-46.ru/]1win[/url]
<a href=https://semdart.com>robot88</a>
[url=https://carskill.ru/]студия детейлинга авто[/url]
<a href=https://zinmanga.net/>manga</a>
По-настоящему крутое [url=https://vodkaa-casino.online/]водка казино[/url]
Оригинальный сайт по [url=https://vodkaa-casino.website/]водка казино[/url]
Всем рекомендую БК 1вин, это их сайт [url=https://1win-53.ru/]1win[/url]
Hi. A very cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://eatout.co.ke/best-activities-to-enjoy-while-eating-food/]https://eatout.co.ke/best-activities-to-enjoy-while-eating-food/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Всем рекомендую официальный сайт [url=https://1win-48.ru/]1win[/url]
Всем рекомендую БК 1вин, официальный сайт [url=https://1win-49.ru/]1win[/url]
RG Trang chủ là tên gọi của trang web chính thức cho Nhà Cái RG777 Casino. Địa chỉ trực tuyến của nó là vnrg5269.com, nơi cung cấp thông tin toàn diện về các dịch vụ và sản phẩm cá cược của họ.
Всем рекомендую Букмеерскую контору [url=https://1win-57.ru/]1win[/url]
Всем рекомендую Букмекерскую контору [url=https://1xbet-12.ru/]1xbet[/url]
Рекомендую лучшую Букмекерскую контору [url=https://1xbet-11.ru/]1xbet[/url]
Лучшая Букмекерская контора [url=https://1xbet-9.ru/]1xbet[/url]
Советую самую лучшую Букмекерскую контору [url=https://1xbet-8.ru/]1xbet[/url]
Open this site [url=https://fortunetiger.com.br/]Fortune Tiger[/url]
Предлагаю лучшую букмекерскую контору [url=https://1xbet-13.ru/]1xbet[/url]
<a href=https://nikapolivcentr.com/>Apartment renovation service Dubai</a>
Настоятельно советую букмекерскую контору [url=https://1xbet-14.ru/]1xbet[/url]
Eu recomendo este jogo [url=https://fortune-tiger.blog/]Fortune Tiger[/url]
Знакомьтесь с топовой Букмекерской конторой [url=https://1xbet-15.ru/]1xbet[/url]
Мое мнение – лучшая Букмекерская контора [url=https://1xbet-16.ru/]1xbet[/url]
Предлагаю топовую Букмекерскую контору [url=https://1xbet-17.ru/]1xbet[/url]
Погасим ипотекуВыплатим ипотеку любого банка за один день. Погасим долги и снимем обременения.
<a href=https://good-village.ru/>good-village.ru</a>
Participe e ganhe no site original [url=https://fortune-tiger1.org/]Fortune Tiger[/url]
Предлагаю топовую в своем роде Букмекерскую контору [url=https://1xbet-19.ru/]1xbet[/url]
Предлагаю вам лучшую Букмекерскую контору [url=https://1xbet-18.ru/]1xbet[/url]
Знакомлю с топовой в своем роде Букмекерской конторой [url=https://1xbet-21.ru/]1xbet[/url]
Советую крупнейшую Букмекерскую контору [url=https://1xbet-20.ru/]1xbet[/url]
<a href="https://1xbetin.com/registration/">1xbet new account</a>
Знакомлю с топовой в своем роде Букмекерской конторой [url=https://1xbet-22.ru/]1xbet[/url]
Крупнейшая Букмекерская контора [url=https://1xbet-23.ru/]1xbet[/url]
На мой взгляд, эта Букмекерская контора - лучшая [url=https://1xbet-26.ru/]1xbet[/url]
Топовоя Букмекерская контора на рынке [url=https://1xbet-28.ru/]1xbet[/url]
Acesse o site real do jogo [url=https://fortune-tiger.link/]Fortune Tiger[/url]
Самая надежная Букмекерская контора на рынке [url=https://1xbet-30.ru/]1xbet[/url]
На мой взгляд - лучшая Букмекерская контора [url=https://1xbet-29.ru/]1xbet[/url]
Топ Букмекерская контора [url=https://1xbet-31.ru/]1xbet[/url]
Предлагаю самую надежную букмекерскую контору [url=https://1xbet-33.ru/]1xbet[/url]
Превосходная Букмекерская контора [url=https://1xbet-34.ru/]1xbet[/url]
Ir para o site original [url=https://fortune-tiger2.net/]Fortune Tiger[/url]
Ведущая Букмекерская контора [url=https://1xbet-35.ru/]1xbet[/url]
Крупнейшая Букмекерская контора [url=https://1xbet-36.ru/]1xbet[/url]
Обратившись к нам, Вы получите честную юридически оформленную сделку, что является важным критерием при продаже недвижимости. Мы не являемся посредниками и выкупаем квартиры за собственные деньги.
<a href=https://play-art.su/>play-art.su</a>
Ведущая в мире Букмекерская контора [url=https://1xbet-37.ru/]1xbet[/url]
Советую отличную Букмекерскую контору [url=https://1xbet-39.ru/]1xbet[/url]
Лучшая Букмекерская контора для ставок [url=https://1xbet-40.ru/]1xbet[/url]
Надежная Букмекерская контора для ставок [url=https://1xbet-43.ru/]1xbet[/url]
Самая надежная Букмекерская контора для ставок [url=https://1xbet-44.ru/]1xbet[/url]
Топ Букмекерская контора для ставок[url=https://1xbet-45.ru/]1xbet[/url]
Самая надежная Букмекерская контора для ставок №1 [url=https://1xbet-46.ru/]1xbet[/url]
Самая надежная Букмекерская контора №1 [url=https://1xbet-48.ru/]1xbet[/url]
Лучшая Букмекерская контора [url=https://1xbet-49.ru/]1xbet[/url]
Um dos melhores jogos para ganhar [url=https://fortune-tiger3.org/]Fortune Tiger[/url]
Самая надежная Всем рекомендую Букмекерскую контору №1 [url=https://1xbet-50.ru/]1xbet[/url]
Всем рекомендую Букмекерскую контору №1 [url=https://1xbet-53.ru/]1xbet[/url]
Самая лучшая Букмекерская контора [url=https://1xbet-52.ru/]1xbet[/url]
Моя рекомендация - Букмекерская контора №1 [url=https://1xbet-55.ru/]1xbet[/url]
Моя рекомендация - Букмекерская контора №1 в мире [url=https://1xbet-56.ru/]1xbet[/url]
Моя рекомендация - Букмекерская контора №1 [url=https://1xbet-58.ru/]1xbet[/url]
Легендарная Букмекерская контора №1 [url=https://1xbet-59.ru/]1xbet[/url]
Ofereco a voce o melhor jogo [url=https://fortune-tiger3.net/]Fortune Tiger[/url]
Всем рекомендую Букмекерскую контору [url=https://1xbet-5.ru/]1xbet[/url]
O melhor e mais popular jogo [url=https://fortune-tiger3.xyz/]Fortune Tiger[/url]
https://elementor.com/
Recomendo o popular jogo a todos [url=https://fortune-tiger2.vip/]Fortune Tiger[/url]
[url=https://xn--80aai0ag2c.xn--80adjurfk.xn--c1avg/]поверка счетчиков калуга[/url]
Переходим сюда и выигрываем в [url=https://godovalov.ru/]1win[/url]
Eu recomendo esse jogo a todos [url=https://fortune-tiger-1.com/]fortune Tiger[/url]
Всем рекомендую Букмекерскую контору [url=https://1win-5.org/]1win[/url]
Jogue e ganhe no jogo [url=https://fortune-tiger-2.com/]fortune Tiger[/url]
Рекомендую Букмекерскую контору [url=https://1win-5.com/]1win[/url]
Лучшая Букмекерская контора [url=https://1win-5.сс/]1win[/url]
Va e ganhe com o jogo [url=https://fortune-tiger-2.xyz/]fortune Tiger[/url]
Топовая Букмекерская контора [url=https://1win-5.icu/]1win[/url]
Крутая Букмекерская контора [url=https://1win-5.me/]1win[/url]
Топ Букмекерская контора [url=https://1win-5.top/]1win[/url]
Советую лучшую Букмекерскую контору [url=https://1win-4.org/]1win[/url]
Советую лучшую в своем роде Букмекерскую контору [url=https://1win-4.top/]1win[/url]
Советую лучшую Букмекерскую контору [url=https://1win-4.com/]1win[/url]
Советую выбрать лучшую Букмекерскую контору [url=https://1win-4.icu/]1win[/url]
Выбираем лучшую Букмекерскую контору [url=https://1win-6.com/]1win[/url]
Топовая Букмекерская контора №1 [url=https://1win-6.net/]1win[/url]
Выбираем топовую Букмекерскую контору [url=https://1win-5.cc/]1win[/url]
Крутая Букмекерская контора №1 [url=https://1win-6.org/]1win[/url]
[url=https://promrentgen.ru/]https://promrentgen.ru/[/url]
Выбираем надежную Букмекерскую контору [url=https://1win-6.me/]1win[/url]
Выбрал для себя надежную Букмекерскую контору [url=https://1xbet-60.ru/]1xbet[/url]
Рекомендация от меня - лучшая Букмекерская контора [url=https://1xbet-62.ru/]1xbet[/url]
Выбрал для себя топовую Букмекерскую контору [url=https://1xbet-63.ru/]1xbet[/url]
Рекомендация от меня - самая лучшая Букмекерская контора [url=https://1xbet-64.ru/]1xbet[/url]
Выбрал для себя лучшую Букмекерскую контору [url=https://1xbet-65.ru/]1xbet[/url]
Самая лучшая Букмекерская контора [url=https://1xbet-66.ru/]1xbet[/url]
Выбрал для себя потрясающую Букмекерскую контору [url=https://1xbet-67.ru/]1xbet[/url]
Самая лучшая Букмекерская контора, советую [url=https://1xbet-68.ru/]1xbet[/url]
Выбрал для себя шикарную Букмекерскую контору [url=https://1xbet-69.ru/]1xbet[/url]
Hi there
Just checked your virtualination.com baclink profile, I noticed a moderate percentage of toxic links pointing to your website
We will investigate each link for its toxicity and perform a professional clean up for you free of charge.
Start recovering your ranks today:
https://www.hilkom-digital.de/professional-linksprofile-clean-up-service/
Regards
Mike Smith
Hilkom Digital SEO Experts
https://www.hilkom-digital.de/
Самая надежная Букмекерская контора, советую [url=https://1xbet-70.ru/]1xbet[/url]
Выбрал шикарную Букмекерскую контору [url=https://1xbet-71.ru/]1xbet[/url]
Представляю топовую Букмекерскую контору - [url=https://1xbet-78.ru/]1xbet[/url]
Выбрал лучшую Букмекерскую контору [url=https://1xbet-74.ru/]1xbet[/url]
Самая крутая Букмекерская контора, советую [url=https://1xbet-73.ru/]1xbet[/url]
[url=https://www.yoga-spb.ru/files/pgs/kak_polnostu_udalit_akkaunt_1xbet.html]https://www.yoga-spb.ru/files/pgs/kak_polnostu_udalit_akkaunt_1xbet.html[/url]
[url=https://lpsmanager.io/]https://lpsmanager.io/[/url]
Представляю лучшую Букмекерскую контору - [url=https://1xbet-75.ru/]1xbet[/url]
[url=https://cruise.hot-tour.msk.ru/]круизные маршруты[/url]
<a href=https://sexx.tw/>外送茶</a>
現代社會,快遞已成為大眾化的服務業,吸引了許多人的注意和參與。 與傳統夜店、酒吧不同,外帶提供了更私密、便捷的服務方式,讓人們有機會在家中或特定地點與美女共度美好時光。
多樣化選擇
從台灣到日本,馬來西亞到越南,外送業提供了多樣化的女孩選擇,以滿足不同人群的需求和喜好。 無論你喜歡什麼類型的女孩,你都可以在外賣行業找到合適的女孩。
不同的價格水平
價格範圍從實惠到豪華。 無論您的預算如何,您都可以找到適合您需求的女孩,享受優質的服務並度過愉快的時光。
快遞業高度重視安全和隱私保護,提供多種安全措施和保障,讓客戶放心使用服務,無需擔心個人資訊外洩或安全問題。
如果你想成為一名經驗豐富的外包司機,外包產業也將為你提供廣泛的選擇和專屬服務。 只需按照步驟操作,您就可以輕鬆享受快遞行業帶來的樂趣和便利。
蓬勃發展的快遞產業為人們提供了一種新的娛樂休閒方式,讓人們在忙碌的生活中得到放鬆,享受美好時光。
Лучшая Букмекерская контора, советую [url=https://1xbet-79.ru/]1xbet[/url]
[url=https://es-travel.su/kruiz-moskva-spb/]круиз на теплоходе москва санкт петербург[/url]
Представляю топовую Букмекерскую контору - [url=https://1xbet-78.ru/]1xbet[/url]
Представляю наилучшую Букмекерскую контору - [url=https://1xbet-80.ru/]1xbet[/url]
[url=https://es-travel.su/kruiz-moskva-astrahan/]круиз москва астрахань[/url]
Рекомендую Букмекерскую контору - [url=https://1xbet-82.ru/]1xbet[/url]
[url=https://es-travel.su/kruiz-iz-sigapura/]круизы из сингапура, круизы из сингапура 2024[/url]
[url=https://es-travel.su/kruiz-iz-shanghaya/]круизы из шанхая 2024[/url]
Рекомендую лучшую Букмекерскую контору - [url=https://1xbet-84.ru/]1xbet[/url]
Рекомендую топовую Букмекерскую контору - [url=https://1xbet-86.ru/]1xbet[/url]
Топовая Букмекерская контора - [url=https://1xbet-88.ru/]1xbet[/url]
[url=https://es-travel.su/kruiz-iz-stambula/]круизы из стамбула[/url]
[url=https://es-travel.su/kruiz-iz-izmira/]круизы из измира 2024[/url]
Топовая Букмекерская контора - [url=https://1win-6.cc/]1win[/url]
Лучшая Букмекерская контора - [url=https://1win-6.top/]1win[/url]
Букмекерская контора №1, советую [url=https://1win-6.xyz/]1win[/url]
Лучшая Букмекерская контора на просторах - [url=https://1win-7.net/]1win[/url]
Топовая Букмекерская контора на просторах - [url=https://1win-7.com/]1win[/url]
Топовая Букмекерская контора в мире - [url=https://1win-7.cc/]1win[/url]
Лучшая Букмекерская контора №1 в мире [url=https://1win-7.icu/]1win[/url]
A casa de apostas mais fiavel do mundo - [url=https://1win-7.top/]1win[/url]
Melhor casa de apostas n? 1 do mundo [url=https://1win-7.xyz/]1win[/url]
O escritorio da casa de apostas mais fiavel - [url=https://1win-8.cc/]1win[/url]
Casa de apostas confiavel n? 1 [url=https://1win-8.icu/]1win[/url]
Casa de apostas fiavel, recomendo-a - [url=https://1win-8.top/]1win[/url]
Recomendo esta casa de apostas a toda a gente [url=https://1win-8.net/]1win[/url]
Ведущий подрядчик в области строительства и ремонта в Москве. На протяжении более 6 лет мы успешно реализуем проекты различной сложности, опираясь на профессионализм нашей команды из более чем 50 высококвалифицированных специалистов. Наша компания предоставляет полный спектр строительных услуг, начиная от подсобных работ и заканчивая сложными инженерными задачами
<a href=https://karkasmoskva.ru/>разнорабочие москва заказать</a>
Recomendo a melhor casa de apostas [url=https://1win-9.org/]1win[/url]
Наши разнорабочие – это сердце компании, их профессиональные навыки и ответственный подход к работе позволяют нам гарантировать высочайшее качество выполнения задач. Мы строго следуем срокам и обеспечиваем безопасность на каждом объекте
<a href=https://karkasmoskva.ru/>разнорабочие стоимость москва</a>
A casa de apostas mais confiavel, eu recomendo [url=https://1win-9.net/]1win[/url]
Melhor casa de apostas legal [url=https://1win-9.com/]1win[/url]
Melhor escritorio de apostas legal [url=https://1win-9.cc/]1win[/url]
Грунтовые и фундаментальные работы: надежная основа для вашего проекта;
Монтаж и демонтаж оборудования: профессиональный подход к техническим аспектам.
<a href=https://vk.com/raznorabochie_rabochie_moskva/>нужны разнорабочие срочно</a>
A melhor casa de apostas legal, eu a recomendo [url=https://1win-9.top/]1win[/url]
Melhor casa de apostas n? 1 do mundo [url=https://1win-9.xyz/]1win[/url]
[url=https://pizza-gusto.ru/catalog/rolly-i-sushi/]суши чехов[/url]
[url=https://cruise.hot-tour.msk.ru/turkey/]Круиз из Сочи в Турцию цена[/url]
A melhor casa de apostas do mundo [url=https://1win-10.org/]1win[/url]
Если вы ищете надежных и опытных разнорабочих в Москве, обращайтесь в «Арену Строй». Мы готовы взяться за ваш проект и реализовать его на высшем уровне. Оставьте заявку на нашем сайте, и мы оперативно свяжемся с вами.
<a href=https://yandex.ru/profile/200529566373/>разнорабочие в москве недорого почасовая оплата</a>
Aconselho voce a usar os servicos dessa empresa de apostas [url=https://1win-10.com/]1win[/url]
Minha recomendacao e o escritorio desta casa de apostas [url=https://1win-10.me/]1win[/url]
Prefiro essa empresa de apostas [url=https://1win-4.cc/]1win[/url]
Howdy
I have just analyzed virtualination.com for its SEO metrics and saw that your website could use an upgrade.
We will enhance your ranks organically and safely, using only state of the art AI and whitehat methods, while providing monthly reports and outstanding support.
More info:
https://www.digital-x-press.com/unbeatable-seo/
Regards
Mike Pearcy
Digital X SEO Experts
Vale a pena prestar atencao a essa empresa de apostas [url=https://1win-10.top/]1win[/url]
Considero esta casa de apostas a melhor [url=https://1win-10.icu/]1win[/url]
Eu recomendo esta casa de apostas [url=https://1win-10.xyz/]1win[/url]
Eu confio nessa empresa de apostas [url=https://1win-11.me/]1win[/url]
Aconselho um escritorio de apostas confiavel [url=https://1win-10.net/]1win[/url]
Confio na melhor casa de apostas - [url=https://1win-11.org/]1win[/url]
Confio na casa de apostas mais confiavel do mundo [url=https://1win-11.xyz/]1win[/url]
Confio na melhor casa de apostas do mundo [url=https://1win-11.icu/]1win[/url]
O escritorio da casa de apostas mais confiavel [url=https://1win-11.name/]1win[/url]
Esta e a melhor casa de apostas [url=https://1win-11.vip/]1win[/url]
Топовая Букмекерская контора [url=https://1win-62.ru/]1win[/url]
Самая надёжная Букмекерская контора [url=https://1win-64.ru/]1win[/url]
Топовая Букмекерская контора, советую [url=https://1win-65.ru/]1win[/url]
Самая топовая Букмекерская контора [url=https://1win-66.ru/]1win[/url]
Самая надежная Букмекерская контора [url=https://1win-68.ru/]1win[/url]
Лучшая Букмекерская контора, советую [url=https://1win-67.ru/]1win[/url]
Grandes vitorias podem ser encontradas no jogo [url=https://fortune-tiger-4.org/]Fortune Tiger[/url]
Лучшая Букмекерская контора, рекомендую [url=https://1win-69.ru/]1win[/url]
Самая лучшая Букмекерская контора [url=https://1win-70.ru/]1win[/url]
Лучшая Букмекерская контора на просторах [url=https://1win-97.ru/]1win[/url]
A maior casa de apostas, eu a recomendo [url=https://blaze-3.icu/]Blaze[/url]
Превосходная Букмекерская контора, рекомендую [url=https://1win-71.ru/]1win[/url]
Топовая Букмекерская контора, всем рекомендую [url=https://1win-72.ru/]1win[/url]
http://apteka-sm.ru/
Всем рекомендую Букмекерскую контору [url=https://1win-73.ru/]1win[/url]
Всем рекомендую ведущую Букмекерскую контору [url=https://1win-75.ru/]1win[/url]
Ganhos faceis no jogo poplar [url=https://fortune-tiger-4.art/]Fortune Tiger[/url]
Всем рекомендую топовую Букмекерскую контору [url=https://1win-78.ru/]1win[/url]
<a href=https://hk-bestcasino.com/>網上賭場</a>
Рекомендую лучшую Букмекерскую контору [url=https://1win-80.ru/]1win[/url]
Ведущая Букмекерская контора, рекомендую [url=https://1win-81.ru/]1win[/url]
Рекомендую надёжную Букмекерскую контору [url=https://1win-82.ru/]1win[/url]
Ведущая Букмекерская контора в мире, рекомендую [url=https://1win-83.ru/]1win[/url]
Рекомендую топовую Букмекерскую контору [url=https://1win-84.ru/]1win[/url]
Рекомендую прекрасную Букмекерскую контору [url=https://1win-86.ru/]1win[/url]
Лучшая Букмекерская контора, рекомендую [url=https://1win-87.ru/]1win[/url]
Hello guys
Hi. A very cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://techtranche.com/the-three-unities-to-consider-in-the-case-of-betting/]https://techtranche.com/the-three-unities-to-consider-in-the-case-of-betting/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Рекомендую Букмекерскую контору [url=https://1win-88.ru/]1win[/url]
Лучшая Букмекерская контора [url=https://1win-92.ru/]1win[/url]
Hello .
Hi. A very cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://www.mundogump.com.br/fatos-interessantes-sobre-cassinos/]https://www.mundogump.com.br/fatos-interessantes-sobre-cassinos/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Топовая Букмекерская контора на просторах [url=https://1win-98.ru/]1win[/url]
В нашем интернет-магазине дамы найдут классические, нарядные, спортивные, праздничные модели, демонстрирующие качества женской фигуры, а также идеально маскирующие недостатки. Самое главное, что независимо от возраста или фигуры – Вы будете чувствовать себя хорошо и привлекательно. В нашем предложении Вы найдете широкий выбор элегантной и повседневной женской одежды от 42 до 80 размера, которая позволит подчеркнуть стильные стороны женской фигуры и выразить себя через наряд.
[url=https://bellady.by/]BELLADY.BY[/url] предлагает самый большой выбор женской одежды, производимой в Республике Беларусь. Благодаря тому, что наш интернет-магазин находится в городе Брест, где работают более 200 компаний по пошиву одежды для женщин, у нас можно приобрести большинство товаров из ассортимента выпускаемой ими продукции.
Лучшая Букмекерская контора на просторах [url=https://1win-100.ru/]1win[/url]
Лучшая Букмекерская контора в мире [url=https://1win-103.ru/]1win[/url]
Топовая Букмекерская контора в мире [url=https://1win-105.ru/]1win[/url]
Great site ! I recommend everyone to watch it![url=https://paris-escort24.com/]paris escort[/url]
Топовая Букмекерская контора, рекомендую [url=https://1win-107.ru/]1win[/url]
Confie em um cassino confiavel [url=https://tigrinho-4.icu/]Tigrinho[/url]
Топовая Букмекерская контора - [url=https://1win-110.ru/]1win[/url]
Лучшая Букмекерская контора, рекомендую [url=https://1win-109.ru/]1win[/url]
Самая Надежная Букмекерская контора - [url=https://1win-113.ru/]1win[/url]
Рекомендую Лучшую Букмекерскую контору [url=https://1win-112.ru/]1win[/url]
Great site ! I recommend everyone to watch it![url=https://paris-escort24.com/]vip paris escort[/url]
Рекомендую надежную Букмекерскую контору [url=https://1win-114.ru/]1win[/url]
Рекомендую топовую Букмекерскую контору [url=https://1win-122.ru/]1win[/url]
Ir para o site principal [url=https://blaze1.space/pt/]blaze[/url]
Great site ! I recommend visiting the site![url=https://vapesale24.com/collections/176-disposable-pods-zero-nicotine-0mg]https://vapesale24.com/collections/176-disposable-pods-zero-nicotine-0mg[/url]
Great site ! I recommend everyone to watch it![url=https://vapesale24.com/collections/geek-bar ]https://vapesale24.com/collections/geek-bar [/url]
Топовая Букмекерская контора - [url=https://1win-124.ru/]1win[/url]
Рекомендую лучшую Букмекерскую контору [url=https://1win-125.ru/]1win[/url]
Лучшая Букмекерская контора - [url=https://1win-126.ru/]1win[/url]
Рекомендую отличную Букмекерскую контору [url=https://1win-127.ru/]1win[/url]
Лучшая Букмекерская контора, рекомендую - [url=https://1win-128.ru/]1win[/url]
Рекомендую лучшего Букмекера - [url=https://1win-129.ru/]1win[/url]
O melhor cassino da Internet, eu o recomendo [url=https://blaze1.space/pt/]Blaze apostas[/url]
Eu recomendo este cassino [url=https://blaze1.space/pt/]blaze apostas[/url]
Site excelente, recomendado [url=https://blaze1.space/pt/]Blaze apostas[/url]
Great site ! I recommend everyone to watch it![url=https://vapesale24.com/collections/176-disposable-pods-]https://vapesale24.com/collections/176-disposable-pods-[/url]
Рекомендую надёжного Букмекера - [url=https://1win-132.ru/]1win[/url]
Рекомендую отличного Букмекера - [url=https://1win-133.ru/]1win[/url]
<a href=https://ts365.tw/>九州娛樂</a>
<a href=https://ts365.tw/>九州娛樂城登入</a>
<a href=https://rg777.app/>cá cược thể thao</a>
cá cược thể thao
Great site ! I recommend everyone to watch it![url=https://vapesale24.com/pages/near-me ]https://vapesale24.com/pages/near-me [/url]
Recomendo uma casa de apostas confiavel [url=https://1win-12.com/]1win[/url]
Recomendo uma excelente casa de apostas [url=https://1win-12.org/]1win[/url]
Melhor casa de apostas da Internet [url=https://1win-12.cc/]1win[/url]
O melhor site, eu o recomendo [url=https://1win-12.me/]1win[/url]
Melhor casa de apostas, recomendado [url=https://1win-13.com/]1win[/url]
Здесь очень выгодный [url=https://b-way.by/]прокат электросамокатов[/url]
A melhor casa de apostas, eu recomendo [url=https://1win-13.org/]1win[/url]
A melhor casa de apostas, eu recomendo [url=https://1win-13.cc/]1win[/url]
A melhor casa de apostas confiavel, recomendada [url=https://1win-13.xyz/]1win[/url]
Отличный сайт! Тут Вы можете найти[url=https://minecraftheat.ru/]новые сервера майнкрафт[/url]
As maiores probabilidades neste cassino [url=https://tigrinho-4.cc/]Tigrinho[/url]
Passando para a melhor casa de apostas [url=https://1win-14.icu/]1win[/url]
反向連接金字塔
G搜尋引擎在经过多次更新之后需要套用不同的排名參數。
今天有一種方法可以使用反向链接吸引G搜尋引擎對您的網站的注意。
反向链接不僅是有效的推廣工具,也是有機流量。
我們會得到什麼結果:
我們透過反向链接向G搜尋引擎展示我們的網站。
他們收到了到該網站的自然過渡,這也是向G搜尋引擎發出的信號,表明該資源正在被人們使用。
我們如何向G搜尋引擎表明該網站具有流動性:
個帶有主要訊息的主頁反向鏈接
我們透過來自受信任網站的重定向來建立反向連結。
此外,我們將網站放置在单独的網路分析器上,網站最終會進入這些分析器的缓存中,然後我們使用產生的連結作為部落格、論壇和評論的重定向。 這個重要的操作向G搜尋引擎顯示了網站地圖,因為網站分析器顯示了有關網站的所有資訊以及所有關鍵字和標題,這很棒
有關我們服務的所有資訊都在網站上!
Escolha de uma casa de apostas confiavel [url=https://1win-14.me/]1win[/url]
Apresentando a melhor casa de apostas [url=https://1win-14.com/]1win[/url]
Отличный сайт! Тут Вы можете приобрести[url=https://wonderball-project.ru/]Воздушные шары[/url]
Apresentando uma casa de apostas confiavel [url=https://1win-14.org/]1win[/url]
Ir para a melhor casa de apostas [url=https://1win-15.com/]1win[/url]
Escolha apenas esta casa de apostas [url=https://1win-15.me/]1win[/url]
Recomendo uma excelente casa de apostas [url=https://1win-15.cc/]1win[/url]
A melhor casa de apostas para apostar [url=https://1win-15.xyz/]1win[/url]
Apostas bem-sucedidas com a melhor casa de apostas [url=https://1win-16.com/]1win[/url]
Uma casa de apostas confiavel e com excelente reputacao [url=https://1win-16.org/]1win[/url]
A escolha dos profissionais no mundo das apostas [url=https://1win-16.xyz/]1win[/url]
Отличный сайт!Рекомендую![url=http://ac-holding.ru/]http://ac-holding.ru/[/url]
Casa de apostas confiavel com a melhor reputacao [url=https://1win-16.cc/]1win[/url]
Casa de apostas comprovada para apostas [url=https://1win-16.icu/]1win[/url]
A escolha dos profissionais no mundo das apostas [url=https://1win-16.me/]1win[/url]
A escolha dos profissionais no mundo dos cassinos [url=https://blaze-1.cc/]Blaze[/url]
Eu recomendo o melhor cassino [url=https://blaze-6.cc/]Blaze[/url]
A melhor casa de apostas para cassinos [url=https://blaze-6.xyz/]Blaze[/url]
Eu recomendo o melhor cassino [url=https://blaze-7.cc/]Blaze[/url]
A melhor opcao de cassinos [url=https://blaze-7.top/]Blaze[/url]
Uma otima casa de apostas para cassinos [url=https://blaze-8.cc/]Blaze[/url]
Eu recomendo o melhor cassino [url=https://blaze-8.icu/]Blaze[/url]
Descubra o melhor cassino [url=https://blaze-9.cc/]Blaze[/url]
En unlu kumarhanede sans?n?z? deneyin [url=https://sweet-bonanza-3.icu/]Sweet bonanza[/url]
Um cassino com a melhor reputacao [url=https://blaze-9.top/]Blaze[/url]
Um lider entre os cassinos on-line [url=https://blaze-10.cc/]Blaze[/url]
Cassino com altos pagamentos [url=https://blaze-10.icu/]Blaze[/url]
Отличный сайт! Всем рекомендую!Тут Вы можете приобрести[url=https://azotsnab13.ru/]закись азота[/url]
Sorte no melhor cassino [url=https://blaze-10.top/]Blaze[/url]
ทดลองเล่นสล็อต
Divirta-se jogando no melhor cassino [url=https://blaze-11.cc/]Blaze[/url]
Cassino on-line lider [url=https://blaze-11.icu/]Blaze[/url]
Um cassino em que voce pode confiar [url=https://blaze-11.top/]Blaze[/url]
O cassino com as melhores condicoes [url=https://blaze-11.xyz/]Blaze[/url]
Eu recomendo o melhor cassino [url=https://blaze-12.cc/]Blaze[/url]
Jogue em um dos melhores cassinos [url=https://blaze-12.icu/]Blaze[/url]
O cassino mais confiavel [url=https://blaze-12.top/]Blaze[/url]
<a href=https://raja118login.com/>raja118</a>
Good Day
I have just analyzed virtualination.com for its SEO Trend and saw that your website could use a push.
We will enhance your ranks organically and safely, using only state of the art AI and whitehat methods, while providing monthly reports and outstanding support.
More info:
https://www.digital-x-press.com/unbeatable-seo/
Regards
Mike Adrian
Digital X SEO Experts
Melhor cassino para ganhar [url=https://blaze-13.cc/]Blaze[/url]
Experimente o melhor cassino [url=https://blaze-13.top/]Blaze[/url]
Um lider entre os cassinos on-line [url=https://blaze-14.cc/]Blaze[/url]
Рекомендую лучший Букмекер [url=https://a-grande.ru/]1win[/url] Переходите на официальный 1вин сайт
Sorte no melhor cassino [url=https://blaze-14.xyz/]Blaze[/url]
Divirta-se jogando no melhor cassino [url=https://blaze-15.icu/]Blaze[/url]
Seveceginiz bir kumarhane [url=https://sweet-bonanza-12.top/]Sweet bonanza[/url]
Eu recomendo este cassino a todos [url=https://fortune-tiger-5.net/]Fortune Tiger[/url]
Cassino para jogadores de sucesso [url=https://fortune-tiger-5.org/]Fortune Tiger[/url]
Great site ! I recommend this site![url=https://puffbars.uk/pages/near-me]https://puffbars.uk/pages/near-me[/url]
Many thanks for building such an informative and fun site. I am look forward to providing details if the situation appears on its own! Appreciate it yet again for this available to world!
Jogue em um cassino confiavel [url=https://fortune-tiger-7.icu/]Fortune Tiger[/url]
Confie neste cassino confiavel [url=https://fortune-tiger-8.org/]Fortune Tiger[/url]
Escolha este cassino confiavel [url=https://fortune-tiger-8.xyz/]Fortune Tiger[/url]
blackpanther77
Tente a sua sorte neste cassino [url=https://fortune-tiger-8.art/]Fortune Tiger[/url]
Отличный сайт! Рекомендую заглянуть туда[url=https://stroyprav.ru/]Строительный консалтинг[/url]
Jogos de azar no melhor cassino [url=https://fortune-tiger-8.vip/]Fortune Tiger[/url]
Eu recomendo o melhor cassino [url=https://tigrinho-1.com/]Tigrinho[/url]
O cassino mais confiavel para voce [url=https://tigrinho-1.net/]Tigrinho[/url]
Ganhos maximos neste cassino [url=https://tigrinho-1.cc/]Tigrinho[/url]
Os melhores bonus deste cassino [url=https://tigrinho-1.top/]Tigrinho[/url]
supermoney88
[url=http://www.pilkguns.com/news/code-hellcase-2024_1.html]hell case[/url]
Great site! I recommend to everyone![url=https://make.az/xidmetler/internet-marketinqi/seo-xidmeti]seo xidmeti[/url]
Jogue em um cassino confiavel [url=https://tigrinho-4.com/]Tigrinho[/url]
Os melhores bonus desta casa de apostas [url=https://tigrinho-4.org/]Tigrinho[/url]
Cassinos com condicoes favoraveis [url=https://tigrinho-4.net/]Tigrinho[/url]
Escolha este cassino confiavel [url=https://tigrinho-4.top/]Tigrinho[/url]
Tente a sua sorte neste cassino [url=https://tigrinho-5.xyz/]Tigrinho[/url]
O cassino perfeito para jogos de azar [url=https://tigrinho-5.com/]Tigrinho[/url]
A casa de apostas perfeita para jogos de azar [url=https://tigrinho-5.net/]Tigrinho[/url]
Cassinos com as melhores avaliacoes [url=https://tigrinho-5.cc/]Tigrinho[/url]
Experimente este cassino de primeira linha [url=https://tigrinho-5.vip/]Tigrinho[/url]
Eu recomendo um otimo cassino [url=https://tigrinho-5.top/]Tigrinho[/url]
Eu recomendo o melhor cassino [url=https://tigrinho-6.xyz/]Tigrinho[/url]
Experimente este cassino de primeira linha [url=https://tigrinho-6.com/]Tigrinho[/url]
O cassino mais confiavel [url=https://tigrinho-6.net/]Tigrinho[/url]
Отличный сайт! Всем рекомендую! Тут Вы можете найти[url=https://botsman.org/]база данных[/url]
Um cassino com uma excelente reputacao [url=https://tigrinho-6.cc/]Tigrinho[/url]
Jogue em um cassino confiavel [url=https://tigrinho-6.icu/]Tigrinho[/url]
Eu recomendo um cassino confiavel [url=https://tigrinho-6.top/]Tigrinho[/url]
Os melhores bonus deste cassino [url=https://tigrinho-6.vip/]Tigrinho[/url]
<a href=https://gundamnihbos.com>gundam4d</a>
<a href=https://sunmory33jitu.com>sunmory33</a>
https://sunmory33jitu.com
Cassinos com condicoes favoraveis [url=https://tigrinho-7.com/]Tigrinho[/url]
Confie neste cassino confiavel [url=https://tigrinho-7.net/]Tigrinho[/url]
Tente a sua sorte neste cassino [url=https://tigrinho-7.cc/]Tigrinho[/url]
Cassino on-line confiavel [url=https://tigrinho-8.cc/]Tigrinho[/url]
Отличный сайт! Всем рекомендую! Тут Вы можете найти[url=https://time-forex.com/brokery-dly-skalpinga]брокеры для скальпинга[/url]
Jogue em um cassino confiavel [url=https://tigrinho-8.xyz/]Tigrinho[/url]
Отличный сайт! Всем рекомендую![url=https://remont-holodilnika.spb.ru/%D0%BE%D1%81%D0%BD%D0%BE%D0%B2%D0%BD%D1%8B%D0%B5]Ремонт холодильников[/url]
<a href=https://pro88web.com>Pro88</a>
Pro88
WOW just what I was searching for. Came here by searching for %meta_keyword%
lolipopnews.ru/page/9В
mailorderbridesfinder.com/В
otantravel.kz/news/swiss-uvelichivaet-kolichestvo-reysov-mayyami-cyurih-na-period-zimnego-sezonaВ
retrogaming.in.ua/index.php?ukey=linkexchange&did=33&le_categoryID=0&page=22&show_all=yesВ
blagmama.ru/forum/index.php?autocom=blog&blogid=4350&showentry=11569В
Металлопромышленная компания Гермес, основанная в 2011 году в Красноярске, является лидером по поставкам металлопроката, арматуры, труб, швеллеров, уголков, профлистов и листов. Мы обслуживаем предприятия и частных лиц в Красноярском крае.
Melhores jogos neste cassino [url=https://blaze-22.vip/]Blaze[/url]
Sure thing! Just take a look at the pictures in this <a href="https://tau24.kz/bitrix/redirect.php?goto=https://www.googletagmanager.com/debug/clearcookies?url=https://sexygrannypics.com/sitemap.xml">Nude</a> photos category, open up them in a new tab, and maybe do a quick search for the one you are considering. But no tension, everything has already been organized and sorted for you personally, so the tough part is done!
Desfrute da emocao no melhor cassino [url=https://blaze-22.cc/]Blaze[/url]
O melhor cassino para grandes vitorias [url=https://blaze-22.org/]Blaze[/url]
<a href=https://hawleychiropractic.ca/hasil-piala-dunia-u17>hasil piala dunia u17</a>
Sua sorte esta no cassino confiavel [url=https://blaze-23.xyz/]Blaze[/url]
Experimente o cassino mais popular [url=https://blaze-23.org/]Blaze[/url]
Teste sua sorte no melhor cassino [url=https://blaze-24.xyz/]Blaze[/url]
O melhor cassino para jogadores de verdade [url=https://blaze-24.icu/]Blaze[/url]
https://mariezoospa.ca/pengeluaran-hk
O lugar perfeito para jogos de azar [url=https://blaze-25.vip/]Blaze[/url]
Excelente cassino para ganhos [url=https://blaze-25.icu/]Blaze[/url]
Отличный сайт! Всем рекомендую!Тут Вы можете приобрести[url=https://azotsnab12.ru/]закись азота[/url]
As melhores slots estao aqui [url=https://blaze-32.xyz/]Blaze[/url]
Hey, guess what? We have a huge amount of photos on this portion of porn internet site - some are edited, some are funny, some feature just one person among others have a whole group. It's just like a goldmine of various forms of <a href="https://tau24.kz/bitrix/redirect.php?goto=https://www.googletagmanager.com/debug/clearcookies?url=https://sexygrannypics.com/sitemap.xml">Nude</a> pictures that are sure to make you happy and provide a smile to your face!
<a href=https://thefinancesolution.us/>bocor88</a>
bocor88
Howdy! I know this is kinda off topic nevertheless I'd figured
I'd ask. Would you be interested in trading links or mayhe guest writing a blkog post or vice-versa?
My site addresses a lott of the same topics as yours
and Ithink wee could greatly benefit from each other. If you might be
interested feel free to shoot me an email.
I look forward to hearing from you! Awesome blog by the way! https://WWW.Waste-NDC.Pro/community/profile/tressa79906983/
Seu cassino da sorte espera por voce [url=https://blaze-29.cc/]Blaze[/url]
The current knowledge base also reveals significant differences exist in the responses of various female tissues to estrogen and progesterone, or their combined action <a href=http://cialis.lat/discover-the-best-prices-for-cialis>tadalafil cialis</a> Avoiding or stopping steroids can lead to male fertility improvement as well as sperm quality improvement
Cassino que voce vai adorar [url=https://blaze-29.icu/]Blaze[/url]
Jogue no cassino aprovado [url=https://blaze-26.vip/]Blaze[/url]
Hello guys
Hello. A cool site that I found on the Internet.
Check out this site. There's a great article there. [url=https://xvcuritiba.com.br/na-cola-da-gorduchinha/]https://xvcuritiba.com.br/na-cola-da-gorduchinha/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Desfrute da emocao no melhor cassino [url=https://blaze-26.icu/]Blaze[/url]
O melhor cassino para grandes vitorias [url=https://blaze-27.cc/]Blaze[/url]
주제는 폰테크 입니다
휴대폰을 사고 파는 종류의 사이트 입니다
고객이 휴대폰을 개통하고
그럼 저희는 돈을주고 그 휴대폰을 구매합니다.
Hello .
Hello. A fine site that I found on the Internet.
Check out this site. There's a great article there. [url=https://clearwaterus.com/weak-ankles-causes-treatment-strengthening-exercises/]https://clearwaterus.com/weak-ankles-causes-treatment-strengthening-exercises/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Sua sorte esta no cassino confiavel [url=https://blaze-27.xyz/]Blaze[/url]
Anything slightly sketchy or wrong simply appears to get people excited, and that's just how we humans are. It's messed up that rather than giving older folks, like grandmas, the respect they deserve, some folks get fired up by sexualizing them. In those <a href="https://vitacci.ru/bitrix/redirect.php?goto=https://www.googletagmanager.com/debug/clearcookies?url=https://sexygrannypics.com/sitemap.xml" >SexyGrannyPics</a>, they always make it seem like these grannies are in need of some action.
<a href=https://www.outlookindia.com/plugin-play/sa-gaming-speed-baccarat>บาคาร่า</a>
Jogue com prazer neste cassino [url=https://blaze-27.org/]Blaze[/url]
Seu cassino online favorito [url=https://blaze-28.cc/]Blaze[/url]
Teste sua sorte no melhor cassino [url=https://blaze-28.icu/]Blaze[/url]
Recomendo o melhor cassino [url=https://blaze-30.cc/]Blaze[/url]
Desfrute dos jogos no melhor cassino [url=https://blaze-30.icu/]Blaze[/url]
O cassino dos seus sonhos [url=https://blaze-31.icu/]Blaze[/url]
Descubra o melhor casino [url=https://blaze-31.org/]Blaze[/url]
Cassino com as melhores promocoes [url=https://blaze-31.xyz/]Blaze[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://limpiezasletsgo.es/hpoxwu">https://limpiezasletsgo.es/hpoxwu</a> of type and scrambled it to make a type specimen book.
Seu destino para grandes premios [url=https://blaze-31.cc/]Blaze[/url]
Ganhe muito no melhor cassino [url=https://blaze-33.net/]Blaze[/url]
Jogue e ganhe no melhor cassino [url=https://blaze-34.xyz/]Blaze[/url]
Cassino com os maiores jackpots [url=https://blaze-34.org/]Blaze[/url]
Melhor casa de apostas para jogos de cassino [url=https://blaze-35.xyz/]Blaze[/url]
Sua diversao garantida no nosso cassino [url=https://blaze-35.icu/]Blaze[/url]
Descubra o melhor cassino online [url=https://blaze-35.org/]Blaze[/url]
Divirta-se no cassino mais confiavel [url=https://blaze-36.icu/]Blaze[/url]
Bu kumarhanedeki en iyi oyunlar [url=https://sweet-bonanza-14.top/]Sweet bonanza[/url]
Hello guys
Hello. A very cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://sehiresnafi.com/your-guide-to-safe-and-exciting-online-sports-betting-in-germany/]https://sehiresnafi.com/your-guide-to-safe-and-exciting-online-sports-betting-in-germany/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
As melhores slots estao aqui [url=https://blaze-36.xyz/]Blaze[/url]
O cassino que todos recomendam [url=https://blaze-37.xyz/]Blaze[/url]
Experimente a sorte no cassino mais famoso [url=https://blaze-37.icu/]Blaze[/url]
1 This may be due to a variety of other factors that affect bone health, including a lack of calcium, vitamin D, and weight bearing exercise, all of which might mask a benefit of vitamin K supplementation <a href=http://cialis.lat/discover-the-best-prices-for-cialis>buy cialis online with prescription</a>
Hello !
Hi. A very cool site that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.tipsformobile.com/the-five-best-online-money-games/]https://www.tipsformobile.com/the-five-best-online-money-games/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello .
Hello. A very cool website that I found on the Internet.
Check out this website. There's a great article there. [url=https://edumanias.com/life-style/8-key-directions-for-your-self-development/]https://edumanias.com/life-style/8-key-directions-for-your-self-development/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Ganhe muito no melhor cassino [url=https://blaze-37.org/]Blaze[/url]
Hello comrades
Hi. A very cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://newscarter.com/the-key-to-making-money-from-the-online-soccer-betting-market/]https://newscarter.com/the-key-to-making-money-from-the-online-soccer-betting-market/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hayallerinizdeki kumarhane [url=https://sweet-bonanza-1.cc/]Sweet bonanza[/url]
Hello guys
Hello. A very cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://timebusinessinsider.com/what-you-can-do-to-accentuate-the-growth-of-your-online-small-business/]https://timebusinessinsider.com/what-you-can-do-to-accentuate-the-growth-of-your-online-small-business/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
ruya kumarhanesi [url=https://Sweet-bonanza-1.xyz/]Sweet bonanza[/url]
En iyi cevrimici kumarhaneyi kesfedin [url=https://sweet-bonanza-1.org/]Sweet bonanza[/url]
En iyi promosyonlara sahip casinolar [url=https://sweet-bonanza-2.cc/]Sweet bonanza[/url]
En guvenilir kumarhanede eglenin [url=https://sweet-bonanza-2.icu/]Sweet bonanza[/url]
En iyi slotlar burada [url=https://sweet-bonanza-3.top/]Sweet bonanza[/url]
Сервис виртуальной смс активации номера - [url=https://smsak.org/]Smsak[/url]
En iyi kumarhanede buyuk kazan?n [url=https://sweet-bonanza-4.top/]Sweet bonanza[/url]
The planet of erotica with <a href="https://www.hotgrannyporn.com">granny porn photos</a> has exploded in popularity recently, with main porn studios dedicating even more assets to producing mature articles. This genre has captured the hearts of viewers among the nearly all alluring niches in the XXX sector.
Sizin icin en iyi online casino [url=https://sweet-bonanza-5.top/]Sweet bonanza[/url]
Kumar oynamak icin mukemmel bir yer [url=https://sweet-bonanza-5.icu/]Sweet bonanza[/url]
En iyi kumarhanede sans?n?z? deneyin [url=https://sweet-bonanza-6.top/]Sweet bonanza[/url]
Seveceginiz bir online casino [url=https://sweet-bonanza-6.icu/]Sweet bonanza[/url]
En guvenilir kumarhanede kazan?n [url=https://sweet-bonanza-7.top/]Sweet bonanza[/url]
Buyuk kazanclar icin en iyi casino [url=https://sweet-bonanza-7.icu/]Sweet bonanza[/url]
<a href=https://southboroughrecreation.com>sapporo 88</a>
Guvenilir bir kumarhane tavsiye ederim [url=https://Sweet-bonanza-8.xyz/]Sweet bonanza[/url]
En iyi kumarhanede buyuk kazan?n [url=https://sweet-bonanza-8.top/]Sweet bonanza[/url]
H?zl? odeme yapan kumarhane [url=https://sweet-bonanza-8.icu/]Sweet bonanza[/url]
<a href=https://tuan88jitu.net/>tuan88 slot</a>
En iyi kumarhanelerde sans?n?z? deneyin [url=https://sweet-bonanza-10.top/]Sweet bonanza[/url]
Watch videos from the guy's viewpoint to feel like you're
right in the center of the action and get a good view!
You can find big booties in pretty much any other category you can think
about! Whether you're into curvy teenagers, sexy MILFs, or thick Asians, they all
have an area here. Check out the bouncing, backshots, and amazing action in group intercourse, gangbangs,
anal, one-on-one, and much more. https://ritual-status.ru/bitrix/redirect.php?goto=https://1borsa.com/7bqph
Seveceginiz bir kumarhane [url=https://sweet-bonanza-10.icu/]Sweet bonanza[/url]
<a href=https://dukerr.com/>台灣線上娛樂城</a>
Nancy Ruddle for helpful discussion and critical reading of the manuscript, Dr <a href=http://cialis.lat/discover-the-best-prices-for-cialis>cialis generic best price</a>
<a href=https://dukerr.com/>娛樂城</a>
Bu kumarhanedeki en iyi oyunlar [url=https://sweet-bonanza-9.top/]Sweet bonanza[/url]
En populer kumarhaneyi deneyin [url=https://sweet-bonanza-9.icu/]Sweet bonanza[/url]
<a href=https://www.cayk.ca/>digital marketing agency Calgary</a>
Купить диплом о высшем образовании
в Санкт-Петербурге: советы и рекомендации диплом среднего профессионального образования с занесением в реестр
Here you are at <a href="http://www.big-juggs.com/">www.big-juggs.com/</a>, the ultimate destination for addicts of massive, mouth-watering breasts! Dive directly into a associated with natural ecstasy with the precise, high-resolution photos exhibiting the biggest and the most luscious tits you can imagine. Our site is definitely overflowing with beautiful babes who can't wait to display off their enormous racks, leaving you mesmerized and craving with regard to more.
En iyi kumarhaneyi tavsiye ederim [url=https://sweet-bonanza-11.top/]Sweet bonanza[/url]
En guvenilir online casino [url=https://Sweet-bonanza-11.xyz/]Sweet bonanza[/url]
Kumar oynamak icin en iyi secim [url=https://sweet-bonanza-11.icu/]Sweet bonanza[/url]
Guvenilir bir kumarhanede oynay?n [url=https://sweet-bonanza-12.icu/]Sweet bonanza[/url]
I got my BFP on the third round <a href=http://cialis.lat/discover-the-best-prices-for-cialis>where to buy cialis online</a> sertraline will increase the level or effect of buprenorphine subdermal implant by affecting hepatic intestinal enzyme CYP3A4 metabolism
Guvenilir bir kumarhanede sans?n?z [url=https://sweet-bonanza-13.icu/]Sweet bonanza[/url]
Sizin icin en iyi online casino [url=https://sweet-bonanza-13.top/]Sweet bonanza[/url]
Lorem Ipsum has been the industry's standard dummy text <a href="https://oxybasket.in/rxdka">https://oxybasket.in/rxdka</a> of type and scrambled it to make a type specimen book.
En iyi cevrimici kumarhaneyi kesfedin [url=https://sweet-bonanza-14.icu/]Sweet bonanza[/url]
Рекомендую всем оригинальный сайт - [url=https://peminecraft.com/]Minecraft[/url]
<a href=https://4israel.co.il>buy a puppy in Israel</a>
4israel (פורישראל) is a free message board in Israel, where visitors can publish and look for any information. We help users find everything they seek for life and promotion of business in Israel. You can find proposals for real estate, products, services, cars, sales announcements, work search, educational institutions and much more. Our site is the most popular languages in Israel, such as Hebrew, English, Russian and Arabic.
[url=https://9humantypes.com]Online spiritual gifts test[/url]
[url=http://weirtonproperty.com/]List of spiritual gifts in the Bible[/url] 2d8aa97
[url=https://9humantypes.com]Online spiritual gifts test[/url]
[url=http://weirtonproperty.com/]List of spiritual gifts in the Bible[/url] 2d8aa97
Thanks a bunch for sharing this with all folks you actually realize what
you aare talking approximately! Bookmarked. Kindly also seek adice from my website =).
We may have a hypelink exchange arrangement among us https://odessaforum.biz.ua/
Hello comrades
Hi. A cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://www.theapricity.com/forum/entry.php?622-A-Step-by-Step-Tutorial-on-Building-and-Programming-a-DIY-Arcade-Controller]https://www.theapricity.com/forum/entry.php?622-A-Step-by-Step-Tutorial-on-Building-and-Programming-a-DIY-Arcade-Controller[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello men
Hello. A cool site that I found on the Internet.
Check out this site. There's a great article there. [url=https://speedwaymedia.com/2023/07/19/how-to-bet-online-like-a-professional/]https://speedwaymedia.com/2023/07/19/how-to-bet-online-like-a-professional/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello guys
Hi. A fine site that I found on the Internet.
Check out this website. There's a great article there. [url=https://gamerawr.com/2023/05/23/exploring-the-evolution-of-car-games-from-their-inception-to-now/]https://gamerawr.com/2023/05/23/exploring-the-evolution-of-car-games-from-their-inception-to-now/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello men
Hi. A cool website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/]https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello men
Hi. A cool website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/]https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello men
Hi. A cool website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/]https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello men
Hi. A cool website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/]https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello !
Hello. A fine website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/]https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello !
Hello. A fine website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/]https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello !
Hello. A fine website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/]https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello !
Hello. A fine website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/]https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello !
Hello. A fine website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/]https://www.gamesreviews.com/articles/03/life-hacks-from-a-stylist-for-every-day/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello !
Hello. A fine site that I found on the Internet.
Check out this site. There's a great article there. [url=https://simcookie.com/2023/05/23/evolution-of-basketball-video-games/]https://simcookie.com/2023/05/23/evolution-of-basketball-video-games/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello !
Hi. A cool website that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.oepb.at/allerlei/die-5-besten-kostenlosen-apps-um-fussballergebnisse-live-zu-verfolgen.html]https://www.oepb.at/allerlei/die-5-besten-kostenlosen-apps-um-fussballergebnisse-live-zu-verfolgen.html[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello !
Hello. A very cool site that I found on the Internet.
Check out this website. There's a great article there. [url=https://chandigarhofficial.com/spies-are-everywhere/]https://chandigarhofficial.com/spies-are-everywhere/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
<a href=https://ducatibyimetec.com>angkot88 login</a>
Рекомендую лучшего букмекера [url=https://maxikarta.ru/]1win[/url]
Посетите [url=https://maxikarta.ru/]1win официальный сайт[/url] для получения доступа к широкому ассортименту игр и ставок.
Официальный [url=https://maxikarta.ru/]1win сайт[/url] предлагает разнообразные азартные игры и выгодные ставки.
Играть в [url=https://maxikarta.ru/]1win казино[/url] можно с любым устройством, получая удовольствие от высокого качества игр.
Зеркало Gama Casino: Гарантированный
доступ gama casino
[url=https://maxikarta.ru/]1win официальный[/url] сайт гарантирует честные игры и надежные выплаты.
Используйте [url=https://maxikarta.ru/zerkalo-1win-rabochee-na-segodnya/]1win зеркало[/url] для доступа к сайту даже при блокировке.
Ищете надёжный ресурс? [url=https://maxikarta.ru/]1вин сайт[/url] предоставляет всё необходимое для азартных игр.
[url=https://maxikarta.ru/zerkalo-1win-rabochee-na-segodnya/]Зеркало 1win[/url] поможет вам продолжить игру без перебоев.
[url=https://maxikarta.ru/zerkalo-1win-rabochee-na-segodnya/]1вин зеркало рабочее[/url] всегда доступно для вас.
[url=https://psk-termit.ru/]https://psk-termit.ru/[/url]
Hmm is anyone else having problem wikth thhe images on this blog loading?
I'm tfying to find out if its a problem on my end or if it's tthe
blog. Any suggestions would be greatly appreciated. https://Odessaforum.Biz.ua/
[url=https://www.unlockmega.com/]https://www.unlockmega.com/[/url]
официальный <a href="kreken18.at"> кракен сайт </a> <a href="kreken18.at"> кракен ссылка </a>
Официальный сайт школы 1227: последние новости и обновления https://school1227.ru/
And in case that's insufficient, these people also get away from with sex gadgets, making themselves cum hard. This web site is definitely a treasure trove of pleasure in addition to kink. <a href="https://hotnudes.com/">https://hotnudes.com/</a> is a must-see for any person straight into hot, busty females.
The options are endless nowadays of XXX galleries showcasing grandmothers, having a mixture of both amateur and renowned old models. Treat you to ultimately the indulgence of discovering this captivating type, promising to help keep you enthralled and entertained until you've savored every last naked photograph on <a href="https://www.hotgrannyporn.com/">WWW.HOTGRANNYPORN.COM</a>.
[url=https://www.youtube.com/channel/UCe-uPPVriJvINas8hjcw0Jw/videos?view=0]https://www.youtube.com/channel/UCe-uPPVriJvINas8hjcw0Jw/videos?view=0[/url]
[url=https://www.f2mbinders.com/]https://www.f2mbinders.com/[/url]
Thiss text iss invaluable. Hoow can I find out more? https://Zeleniymis.Com.ua/
The expert will recommend on retaining or discarding specific items. They will give advice for enhancing the indoor and outside appearance to attract to potential visitors. Their services consist of taking high-quality pictures and writing enticing stories to accentuate significant elements. Additionally, they position the advertisement on a prominent real estate site.
<a href=https://hkd852.com/>港體會</a>
Hello. And Bye.
<a href=https://gogocasino.one>https://gogocasino.one</a>
Post writing is also a excitement, if youu be acquainted
with after that yyou can write if not it is complicated to write. https://zeleniymis.Com.ua/
<a href=https://rgbet.cc/lucky/rgbet-app/?cc=666>rgbet</a>
rgbet
Discover how Rodrygo <a href=https://sao-paulo.rodrygo-br.com/>https://sao-paulo.rodrygo-br.com</a> a football player from Sao Paulo, overcame adversity to become a world football star.
<a href=https://arkan.tn>quincaillerie tunisie</a>
Новости гаджетов, техники <a href=https://barbie-games.ru/>https://barbie-games.ru</a> и высоких технологий
Watch these hot grannies on <a href="https://sexygrannypics.com/horny-bb-older-women-hot-xxx-photo/">sexygrannypics</a> as they enjoy every single bit of pleasure, whether they’re stroking huge cocks or even getting their confronts covered in ejaculate. They adore masturbating with toys in addition to getting off in the naughtiest ways. It’s clear these mature ladies are always up for some hardcore fun.
Hello guys
Hi. A very cool 64 website that I found on the Internet.
Check out this website. There's a great article there. [url=https://www.scooptimes.com/sports/online-gaming-a-modern-landscape-of-risk-and-reward/15054]https://www.scooptimes.com/sports/online-gaming-a-modern-landscape-of-risk-and-reward/15054[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello !
Hi. A cool 64 website that I found on the Internet.
Check out this site. There's a great article there. [url=https://photona.net/elevate-the-thrill-of-italian-sports-with-online-betting-platform-22bet/]https://photona.net/elevate-the-thrill-of-italian-sports-with-online-betting-platform-22bet/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello comrades
Hi. A fine 64 site that I found on the Internet.
Check out this website. There's a great article there. [url=https://homeinsteaders.org/building-your-brick-and-mortar-empire-essential-tips-for-real-estate-investors/]https://homeinsteaders.org/building-your-brick-and-mortar-empire-essential-tips-for-real-estate-investors/[/url]
There will definitely be a lot of useful and cool information here.
You will find everything you dreamed of.
Hello, itts good post on the topic of media print,
we all know media is a wonderful source of data. https://Bandurart.mystrikingly.com/
<a href="https://sosamba-novg1.ru/">зрелые проститутки нижнего</a>
New neural network xNude AI for undressing girls - [url=https://xnudes.ai]https://xnudes.ai[/url]
<a href=https://tecnodiva.com/>สล็อตทดลอง</a>
Профессиональная химчистка ковра или ковролина по разумной цене. Оперативный выезд, быстрая сушка [url=https://fabrika-himchistki.ru/khimchistka-kozhanoj-mebeli/]leather sofa dry cleaning st petersburg[/url]
On <a href="https://latinanakedpics.com/latina-gina-valentina-threesome-naked-pics/">latina gina valentina threesome </a>, it’s not really just about posing; it’s about residing out fantasies. These kinds of Latinas dive serious into their greatest desires, from intensive sex scenes to playful solo times with their preferred toys. Watching all of them suck big cocks and obtain their confronts covered in sperm is really exhilarating.
<a href="https://s1.sosamba-spb2.ru/ozerki">проститутки озерки</a>
什麼是娛樂城體驗金?
體驗金是娛樂城提供給玩家,特別是新會員的一種獎勵方式。這筆體驗金允許玩家在還未使用自己的資金進行遊戲前,先行體驗富遊娛樂城的各類遊戲。利用這筆體驗金,玩家可以熟悉遊戲規則,或嘗試新策略。
領取娛樂城體驗金常見問答FAQ
問:新註冊的玩家怎麼獲得娛樂城體驗金?
答:只需要在富遊娛樂城完成註冊,加入富遊客服,告知【我要領取體驗金】並提供【帳號】【手機號】,就可以在賬戶中獲得高達$168元的體驗金。
問:領取娛樂城體驗金有哪些限制?
答:參加資格只有新會員,每位新會員只限領一次。
問:我可以使用體驗金進行任何遊戲嗎?
答:是的,你可以使用體驗金參與富遊娛樂城的所有線上賭場遊戲。
問:娛樂城體驗金是可以提款的嗎?
答:可以的,只需完成活動流水即可進行提款。( 詳細教學 : 富遊娛樂城如何出金/提款? )
問:我在領取娛樂城優惠時遇到問題怎麼辦?
答:如果你在遊戲中遇到任何問題或困難,可以隨時聯繫富遊娛樂城的客戶服務,我們將隨時為你提供協助。
<a href=https://syfc.co.kr/en/45ht/>solid propellant</a>
Предлагаем качественную [url=https://print-galinskiy.ru/]печать на одежде[/url] для любого случая.
Very nice post. I just stumbled upon your weblog and wanted to say that I have truly enjoyed browsing your blog posts.
In any case I'll be subscribing to your rss feed and I
hope you write again very soon! https://66Bb4C96E165C.Site123.me/
[url=https://upmoney.top/?ref=46644]https://upmoney.top/?ref=46644[/url] ссылка на реальный пассивный заработок,прога реально платит сам лично проверял,заходи и приводи друзей,не пожалеешь!
[url=https://9humantypes.com/contact]Approaches to coach on the value of charismatic gifts[/url]
[url=http://www.gmpafrica.com/viewtopic.php?p=57141#p57141]Self-enhancement techniques for personal growth[/url] aa97e5f
<a href="https://blyadsk.ru/">проститутки</a>
<a href=https://vinafarm.co.kr/en/rf-connector-switch/>RF Connectors & Switches</a>
https://ddos.rentals
<a href="https://siski-138.ru/">досуг иркутск</a>
Hello !
Good evening. A great site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://discoverblog.org/2024/03/26/how-to-start-a-business-tips-for-new-entrepreneurs/]https://discoverblog.org/2024/03/26/how-to-start-a-business-tips-for-new-entrepreneurs/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello guys
Hello. A fine website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://alternativeway.net/the-world-of-gaming-an-ecological-perspective/]https://alternativeway.net/the-world-of-gaming-an-ecological-perspective/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
<a href="https://dosuchki1.ru">иркутские проститутки</a>
[url=https://smslive.pro/]buy number whatsapp[/url]
Hello colleagues
Hi. A great site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/]https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A great site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/]https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A great site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/]https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A great site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/]https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A great site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/]https://autobala.com/self-driving-cars-exploring-the-road-to-autonomous-vehicles/340693/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A fantastic website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://articleify.com/link-between-psychosomatics-and-physical-health/]https://articleify.com/link-between-psychosomatics-and-physical-health/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
[url=https://smslive.pro/ru/autoregers]how to get virtual number for telegram[/url]
Hello colleagues
Hi. A fantastic website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://articleify.com/link-between-psychosomatics-and-physical-health/]https://articleify.com/link-between-psychosomatics-and-physical-health/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A fantastic website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://articleify.com/link-between-psychosomatics-and-physical-health/]https://articleify.com/link-between-psychosomatics-and-physical-health/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A fantastic website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://articleify.com/link-between-psychosomatics-and-physical-health/]https://articleify.com/link-between-psychosomatics-and-physical-health/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A fantastic website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://articleify.com/link-between-psychosomatics-and-physical-health/]https://articleify.com/link-between-psychosomatics-and-physical-health/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A great site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/]https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A great site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/]https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A great site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/]https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A great site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/]https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A great site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/]https://stimulusupdate.net/some-of-the-most-exciting-zombie-movies-of-all-time-ranked/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Hello. A fine site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://gsmfixes.com/security-technologies-for-your-home/]https://gsmfixes.com/security-technologies-for-your-home/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Hello. A fine site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://gsmfixes.com/security-technologies-for-your-home/]https://gsmfixes.com/security-technologies-for-your-home/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Hello. A fine site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://gsmfixes.com/security-technologies-for-your-home/]https://gsmfixes.com/security-technologies-for-your-home/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Hello. A fine site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://gsmfixes.com/security-technologies-for-your-home/]https://gsmfixes.com/security-technologies-for-your-home/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello comrades
Hello. A cool site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.aquinoticias.com/2022/02/5-coisas-para-fazer-em-florianopolis/]https://www.aquinoticias.com/2022/02/5-coisas-para-fazer-em-florianopolis/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello comrades
Hello. A cool site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.aquinoticias.com/2022/02/5-coisas-para-fazer-em-florianopolis/]https://www.aquinoticias.com/2022/02/5-coisas-para-fazer-em-florianopolis/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello comrades
Hello. A cool site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.aquinoticias.com/2022/02/5-coisas-para-fazer-em-florianopolis/]https://www.aquinoticias.com/2022/02/5-coisas-para-fazer-em-florianopolis/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello comrades
Hello. A cool site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://www.aquinoticias.com/2022/02/5-coisas-para-fazer-em-florianopolis/]https://www.aquinoticias.com/2022/02/5-coisas-para-fazer-em-florianopolis/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A perfect site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://ventsabout.com/exploring-the-thrills-of-the-aviator-game-demo/]https://ventsabout.com/exploring-the-thrills-of-the-aviator-game-demo/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A perfect site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://ventsabout.com/exploring-the-thrills-of-the-aviator-game-demo/]https://ventsabout.com/exploring-the-thrills-of-the-aviator-game-demo/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A perfect site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://ventsabout.com/exploring-the-thrills-of-the-aviator-game-demo/]https://ventsabout.com/exploring-the-thrills-of-the-aviator-game-demo/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A perfect site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://ventsabout.com/exploring-the-thrills-of-the-aviator-game-demo/]https://ventsabout.com/exploring-the-thrills-of-the-aviator-game-demo/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Simplify your projects and boost productivity with easy-to-use [url=https://www.rillsoft.com/]project management software[/url].
Hello !
Hello. A perfect website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://peaceloaded.com/goutweed-dandelion-co-what-you-can-eat/]https://peaceloaded.com/goutweed-dandelion-co-what-you-can-eat/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hello. A perfect website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://peaceloaded.com/goutweed-dandelion-co-what-you-can-eat/]https://peaceloaded.com/goutweed-dandelion-co-what-you-can-eat/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hello. A perfect website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://peaceloaded.com/goutweed-dandelion-co-what-you-can-eat/]https://peaceloaded.com/goutweed-dandelion-co-what-you-can-eat/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hello. A perfect website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://peaceloaded.com/goutweed-dandelion-co-what-you-can-eat/]https://peaceloaded.com/goutweed-dandelion-co-what-you-can-eat/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
[url=https://t.me/GoTradeInvestmentbot?start=513555624]https://t.me/GoTradeInvestmentbot?start=513555624[/url]
Hello colleagues
Good evening. A very cool website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://articleify.com/link-between-psychosomatics-and-physical-health/]https://articleify.com/link-between-psychosomatics-and-physical-health/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
https://geb-tga.de/mgrame-a-las-ojos-y-dime-la-verdad-el-significado-9/
https://kadiramac.com/antikapitalist-ihsan-eliacik/#comment-97534
https://www.hamat.sa/index.php/2021/10/05/around-mankind-locating-really-love-and-conference/
http://ianforbesng.com/blog/https-boereport-com-2020-02-25-attention-saskatchewan-operators-you-dont-want-to-miss-this/
http://celahkotanews.com/walikota-dumai-dengarkan-jeritan-keluarga-pak-kirno-korban-kebakaran-rumah-jalan-meranti-darat/
Hello !
Good evening. A excellent website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html]https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Good evening. A excellent website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html]https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Good evening. A excellent website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html]https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Good evening. A excellent website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html]https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Good evening. A excellent website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html]https://factnewsph.org/2024/07/over-under-in-the-second-half-with-the-3-5-2-strategy.html[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Hello. A very cool website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://autobala.com/how-streaming-services-changed-entertainment/340729/]https://autobala.com/how-streaming-services-changed-entertainment/340729/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Hello. A very cool website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://autobala.com/how-streaming-services-changed-entertainment/340729/]https://autobala.com/how-streaming-services-changed-entertainment/340729/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Hello. A very cool website 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://autobala.com/how-streaming-services-changed-entertainment/340729/]https://autobala.com/how-streaming-services-changed-entertainment/340729/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A great site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://www.ildispariquotidiano.it/it/ischia-musa-di-artisti-e-scrittori/]https://www.ildispariquotidiano.it/it/ischia-musa-di-artisti-e-scrittori/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Good evening. A very cool site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://entmediahub.com/most-extraordinary-musicians-and-their-peculiarities/]https://entmediahub.com/most-extraordinary-musicians-and-their-peculiarities/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hey just wante to give you a quick heads up. The words in your
post seem to be running off the screen in Firefox. I'm not
sure if thiis is a format issue or something to
doo with browser compatibility but I figured I'd post to let
you know. The style and desigyn look great though! Hope you get the issue solved soon. Thanks https://Bandur-art.blogspot.com/2024/08/the-ultimate-guide-to-no-mans-sky-mods.html
What necessary phrase... super, excellent idea
Convert your [url=https://exchanger24.org/xchange_btc_to_ppusd/]Bitcoin to PayPal[/url] quickly and securely with our trusted exchange service.
Convert [url=https://exchanger24.org/xchange_btc_to_ppusd/]BTC to PayPal[/url] with ease and enjoy quick access to your funds.
Hello comrades
Hello. A fantastic website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://playmyworld.com/2024/06/21/5-free-steam-games-everyone-should-try/]https://playmyworld.com/2024/06/21/5-free-steam-games-everyone-should-try/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello comrades
Hello. A fantastic website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://playmyworld.com/2024/06/21/5-free-steam-games-everyone-should-try/]https://playmyworld.com/2024/06/21/5-free-steam-games-everyone-should-try/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello comrades
Hello. A fantastic website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://playmyworld.com/2024/06/21/5-free-steam-games-everyone-should-try/]https://playmyworld.com/2024/06/21/5-free-steam-games-everyone-should-try/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello comrades
Hello. A fantastic website 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://playmyworld.com/2024/06/21/5-free-steam-games-everyone-should-try/]https://playmyworld.com/2024/06/21/5-free-steam-games-everyone-should-try/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Good evening. A excellent site 1 that I found on the Internet.
Check out this website. There's a great article there. [url=https://tenapk.com/games-we-want-to-play-more/]https://tenapk.com/games-we-want-to-play-more/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello .
Hello. A nice site 1 that I found on the Internet.
Check out this site. There's a great article there. [url=https://celebworthbio.com/the-life-of-kim-kardeshian/]https://celebworthbio.com/the-life-of-kim-kardeshian/[/url]
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
[url=https://9humantypes.com]Ways to promote the application of divine talents in your congregation[/url]
[url=https://www.g-ray.com.tw/forum/index.php/topic,2631.new.html#new]Steps to pinpoint your God-given talents[/url] 88f422d
Moore MC, Thompson CW <a href=https://enhanceyourlife.mom/>order priligy</a> Merlini G, Dispenzieri A, Sanchorawala V, Schönland SO, Palladini G, Hawkins PN, Gertz MA
<a href="https://1xbetin.com/registration/">1xbet create account</a>
Appreciate it for producing a helpful and enjoyable page. I look ahead to providing updates when the time a chance comes up by itself! Thanks once more for creating this accessible for people!
[url=https://exforum.live/threads/hi-%F0%9F%91%8B.144482/page-6#post-9626200]Attain Quick building Sales through Agent Expertise[/url] 7e5f0f6
Appreciate it for producing a helpful and enjoyable page. I look ahead to providing updates when the time a chance comes up by itself! Thanks once more for creating this accessible for people!
[url=https://exforum.live/threads/hi-%F0%9F%91%8B.144482/page-6#post-9626200]Attain Quick building Sales through Agent Expertise[/url] 7e5f0f6
Appreciate it for producing a helpful and enjoyable page. I look ahead to providing updates when the time a chance comes up by itself! Thanks once more for creating this accessible for people!
[url=https://exforum.live/threads/hi-%F0%9F%91%8B.144482/page-6#post-9626200]Attain Quick building Sales through Agent Expertise[/url] 7e5f0f6
Appreciate it for producing a helpful and enjoyable page. I look ahead to providing updates when the time a chance comes up by itself! Thanks once more for creating this accessible for people!
[url=https://exforum.live/threads/hi-%F0%9F%91%8B.144482/page-6#post-9626200]Attain Quick building Sales through Agent Expertise[/url] 7e5f0f6
https://kongotech.org/exploring-the-features-and-benefits-of-1xbet-a-comprehensive-guide/
[url=https://circuitdebris.org/]официальный сайт вавада[/url]
[url=http://xn--80aafabrjladsicc1amg1o4cf1dg.live/]http://xn--80aafabrjladsicc1amg1o4cf1dg.live/[/url]
https://battery-casino.com/
Mostbet <a href=https://krecimyto.pl/recenzja-kasyna-mosbet-w-polsce/>https://krecimyto.pl/recenzja-kasyna-mosbet-w-polsce/</a> the most popular bookmaker and casino in Poland. Register or download the app and get a welcome bonus!
Use the promo code when registering on [url=https://www.pinterest.com/pin/991495674209385089/]1win[/url] and get a 100% bonus on your first deposit.
When someone writes an post he/she retains the
image of a user in his/her mind that how a user cann be aware of it.
Therefore that's why this post is outstdanding. Thanks! https://Lvivforum.pp.ua/
Автомобильные новости <a href=https://billiard-sport.com.ua/>https://billiard-sport.com.ua</a> законы и ПДД, автоспорт
descargar quotex para pc <a href=http://themagicoption.com/>quotex demo</a>
Playing the Aviator Game online offers several benefits: <a href="https://slotloversonline.com/reviews/hellspin/">hellspin</a>
Download Mostbet <a href=https://klublink.cz/>https://klublink.cz</a> mobile application for android for free from the official APK website. Latest version of the application 6.3.2 for android Mostbet
Ведущий производитель стальных резервуаров для хранения жидкостей и газов. Мы предлагаем надежные решения для промышленных, сельскохозяйственных и коммерческих объектов. Высокое качество, долговечность и индивидуальный подход — основные принципы нашей работы [url=https://zso-k.ru/product/rezervuary-gorizontalnye-stalnye/rezervuary-na-sanyah/]Резервуары на санях[/url]
Скидки и сюрпризы от компании [url=https://promotoblok.by/osen2024]PROmotoblok.by[/url] в период осеннего сезона 2024 года.
Укажите кодовое слово при заказе мотоблока АГРОМАШ — "ОСЕНЬ2024" и получите презент или же скидку.
поисковое продвижение сайта <a href=https://seosearchwebsite.ru/>услуги seo оптимизация</a>
Easily join casino games from your mobile device by downloading the Mostbet <a href=https://app.mostbet-casino-cz.cz/>https://app.mostbet-casino-cz.cz</a> app. Download the app for Android and iOS and get 250 free spins.
[url=https://playpromocode.com/dota2/epicloot/ ]EpicLoot промокоды[/url]
[url=https://playpromocode.com/standoff/ ]стендофф промо[/url]
[url=https://playpromocode.com/cs2/case-battle/ ]Кейс Батл коды[/url]
[url=https://playpromocode.com/rust/rustcase/ ]RustCase промо код[/url]
Hey I know this is off topic but I was wondering if you knew of
anyy widgets I could add to my blog that automatically tweet my
newest twitter updates. I've been looking forr a plug-in like this for uite
som time and was hoping maybe youu would have some experience with something like this.
Please let me know if you run into anything. I truly enjoy reading your blog and I look forward to your new updates. https://Lvivforum.pp.ua/
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Рекомендую именно этот [url=https://troitzkiy.org.ua]Реабилитационный центр Киев[/url]
Все новые авто <a href=https://addinfo.com.ua/>https://addinfo.com.ua</a> с подробными обзорами, фото и характеристиками на единственном сайте автомобильных тестов
Посетите лучший музей мира, <a href=https://hermitage-tour-ticket.ru/>эрмитаж купить билеты</a> онлайн и без очередей
Скачайте приложения для Андроид бесплатно на <a href=https://appcatalogue.ru/>https://appcatalogue.ru</a> лучшие программы и игры на русском языке для вашего устройства. Установите приложения прямо сейчас и наслаждайтесь их функционалом!
Official website of Pin up <a href=https://hackthecrypto.io/>https://hackthecrypto.io</a> casino (pin up casino). Login to your personal account, register through a working mirror in 1 click.
Нужен качественный <a href=https://avtopribambas.com/calc/sajty-pro-remont-avtomobilej-vash-nezamenimyj-pomoshhnik-v-mire-avtoservisa.html>автосервис карта</a> услуги профессионального автосервиса по ремонту автомобиля, цены, отзывы.
Take off into the thrilling world of the Aviator Game by Spribe! Test your luck and skills by predicting when to cash out before the plane flies away. Ready to start? Click the button below and get a special bonus to boost your gameplay. Don’t miss out on your chance to win big https://aviator-web.com/
Bermain di [url=https://mega888-4.xyz/]Mega888[/url] adalah mudah dan menyeronokkan, dengan pelbagai pilihan permainan yang sesuai untuk semua pemain.
[url=https://champaignilrealtor.com/real-estate-agent/]Comparing housing agents[/url]
[url=https://svgur.com/s/1ASX]Efficient Home Sales with Broker Guidance[/url] e5f0f68
Автомобильные новости <a href=https://avto-limo.zt.ua/>https://avto-limo.zt.ua</a> Украины и мира, тест-драйвы новых авто, советы экспертов
Justice Department and six states sued to block the deal on Tuesday, saying it would hurt competition and cause consumers to pay higher fares <a href=https://enhanceyourlife.mom/>buy priligy pakistan</a> PUBMED Abstract Coffin CM, Dehner LP Vascular tumors in children and adolescents a clinicopathologic study of 228 tumors in 222 patients
Dengan [url=https://nauvoouniversity.com/]Mega888[/url], anda boleh menikmati permainan slot dengan peluang kemenangan besar dan hadiah jackpot yang menggiurkan.
прикольные анекдоты в приложении
<a href="https://play.google.com/store/apps/details?id=ru.shutochki">Всё шуточки</a>
Mostbet working mirror <a href=https://mostbet-mosbet-az.com/>https://mostbet-mosbet-az.com</a> login to the official Mostbet website
Актуальные новости <a href=https://novosti24.kyiv.ua/>https://novosti24.kyiv.ua</a> Украины и мира: политика, экономика, общество, спорт и культура. Оперативная информация, аналитика и обзоры главных событий. Будьте в курсе мировых и украинских новостей каждый день.
После обучения в автошколе и оформления медсправки, вы можете сдавать экзамен в любом отделении Госавтоинспекции — не только по месту регистрации [url=http://avtoshkola-saransk.ru]сколько стоит сдать на права[/url]
I recommend this trust site [url=https://anyswap.one]anyswap[/url]
Начните новую жизнь в собственном доме - <a href=https://tds-light.ru/stroitelstvo/6084-pochemu-stoit-vybrat-keramicheskiy-blok.html>проект одноэтажного дома</a> построенный по высоким стандартам.
Seamlessly transfer your digital assets across multiple blockchain networks with the advanced functionality of the [url=https://anyswap.one]anyswap cross-bridge[/url]
<a href="https://whatweather.today/" title="Weather">Weather</a>
Where to play New Zealand casinos on roulette, or in <a href=https://bestpokiesonline.co.nz>top pokies</a>. Online casinos in New Zealand for money. The best casinos of all categories operating in the country.
<a href=https://rtpkantorbola17.com/>rtpkantorbola</a>
Kantorbola adalah situs gaming online terbaik di indonesia , kunjungi situs RTP kantor bola untuk mendapatkan informasi akurat rtp diatas 95% . Kunjungi juga link alternatif kami di kantorbola77 dan kantorbola99 .
Как развеселить друга с помощью забавных <a href="https://carnation-discovery-487.notion.site/11279d463c29806f9d3cec46d95cc644">приколов</a>
In my opinion you are not right. I am assured. I can defend the position.
Портал электроники <a href=https://tech-nord.ru/>https://tech-nord.ru</a> по доступным ценам.
Gratitude for setting up such a knowledgeable & pleasurable site. I anticipate to sharing info whenever the opportunity arises itself! Thanks a ton repeatedly for providing the website available to public!
[url=http://hzq84621.is-programmer.com/guestbook/]Broker-Controlled Tactics for Realizing Swift Family Home Sales[/url] aa97e5f
I really love your blog.. Pleassant colors & theme.
Diid you make this amazing site yourself? Please reply back as I'm looking to create my very own websitye
and would like to find out where you got this from or just wht the thene is called.
Thank you! https://lvivforum.pp.ua/
Вам устали от средних покупок онлайн? Мега предлагает нечто иное! Благодаря новаторским возможностям и разнообразию товаров <a href=https://xn--megab-mdb.com>megaweb4 at</a> гарантирует, что вы обнаружите то, что нужно. Наслаждайтесь беспроблемной регистрацией и безопасными транзакциями с использованием Bitcoin. Присоединяйтесь к <a href=https://xn--megab-mdb.com>мега онион ссылка</a> уже сейчас и погрузитесь в увлекательный мир шопинга.
[url=https://mega-active-links.com]http mega sb[/url]
Рекомендую заказывать качественные [url=https://pravo.cc]Юридические услуги[/url] только на этом сайте.
7f42d8a
[url=https://www.ckcounselinggroup.com/services-good]AZ revocation documents[/url]
Грузовые шины КАМАЗ вездеход являются одним из самых востребованных видов шин для грузовых автомобилей. Грязевые шины для внедорожников. Все размеры [url=http://specshina-jcb.ru]китайская грузовая резина[/url]
корейское порно <a href=https://sud-expertiza.kz/>порно русское ебан</a>
[url=https://svetmsc.ru/]Гирлянда на дом[/url] в Москве и области
Magnificent web site. Lots of useful information here. I'm
sending it to several buddies ans additionally sharing in delicious.
Annd naturally, thanks to your sweat! https://lvivforum.pp.ua/
Howdy, partner! I'm delighted to say hello to you.
While not definitive, it appears that this could bring great value to your project <a href=http://clinik-spravka.info/>Moscow digital healthcare</a>
Bye for now, and keep the positive vibes
Свежие <a href="https://prikolnyekartinki.mystrikingly.com/blog/0ade1e0d9a9">анекдоты</a>.
Tracking the most recent global innovation trends, the GII finds that innovation investment slowed in 2023, in marked contrast to previous years [url=https://raceview.net/sendto.php?t=https://www.vaughancannabis.store/]https://raceview.net/sendto.php?t=https://www.vaughancannabis.store/[/url]
Break Through Limits: Click to Explore More https://aviator-app.org/
https://nta-pfo.ru/news/economy/2024/news_686610/
buy balloons <a href=https://helium-balloons-delivery.com/>buy inflatable balloons</a>
Ballroom dancing club <a href=https://estet.zt.ua/>https://estet.zt.ua</a> Estet in Zhitomir, Ukraine. The best trainers, the largest and most comfortable dance hall in Zhitomir
<a href=https://tradeprofinances.com/mortgage/do-mortgage-lenders-work-on-weekends/>do loans get approved on weekends</a>
Buy antibiotics <a href=https://buyantibioticswp.com/>https://buyantibioticswp.com</a> at a low price online with delivery, medicines in stock and on order
Чтобы вывести деньги с биржи Вам необходимо воспользоваться p2p переводами. После нажатия на кнопку "Продать USDT" в течении 15 минут, ожидайте поступление денег на карту [url=https://kemt.at.ua/forum/19-6416-1#39697]обмен usdt trc20 на приват24[/url]
zabljak <a href=https://www.haus-kaufen-in-montenegro.de/>hauser kaufen Montenegro</a>
https://generic51.ru/
Я бы с такими в кроватке поболел .
Financial protection algorithms: platform provides advanced risk management functions, including stop [url=https://southernparadisehomes.com/hello-world/]https://southernparadisehomes.com/hello-world/[/url] for crypto trading, allowing to minimize potential losses and fix profit.
https://rokacasino.com/_/7788
https://xn--2o2b271b.com/_/7788
<a href="https://rokacasino.com/_/7788" target="_blank">로카카지노</a>
<a href="https://xn--2o2b271b.com/_/7788" target="_blank">로카카지노</a>
[url=https://bankovskaya-garantiya02.ru/]банковская гарантия[/url] - это инструмент финансового обеспечения сделок, предоставляемый банком в пользу контрагента для обеспечения исполнения обязательств.
Discover the powerful capabilities of [url=https://youtube-api-v3.com/]youtube api v3[/url] for integrating YouTube data into your website or app seamlessly. Whether you're building a custom video player or managing playlists, the YouTube API v3 documentation offers a comprehensive guide to get started.
Свежие картинки с надписями <a href="https://prikoly-tut.blogspot.com/2024/10/smeshnye-kartinki.html">https://prikoly-tut.blogspot.com/2024/10/smeshnye-kartinki.html</a>.
https://topsvenska.com/recension/storspelare/
Скидка 15% на биоревитализацию https://marosha.ru/
Профилактика появления заусенцев, расслоения ногтей https://marosha.ru/
Просвещения 33 https://marosha.ru/
2 https://marosha.ru/policy
9 Салон красоты https://marosha.ru/
Студия Chin-Chin Beauty Bar https://marosha.ru/policy
Маникюр Санкт-Петербург https://marosha.ru/policy
One Plant North Oshawa is home to the biggest selection of Cannabis at the best prices in Oshawa. Shop Cannabis, Flower, Edibles, Beverages, Bongs, Grinders [url=http://www.afada.org/index.php?modulo=6&q=https://www.oakvillecannabis.store/]http://www.afada.org/index.php?modulo=6&q=https://www.oakvillecannabis.store/[/url]
Seo-продвижение сайтов <a href=https://seoenginewebsite.ru/>https://seoenginewebsite.ru</a> с гарантией попадания в топ-10 поисковой выдачи в Яндексе и Google
Боюсь, что я не знаю.
The sudden surge in popularity of erotic thrillers was caused by various circumstances: the easing of censorship restrictions, the spread of [url=https://sobrouremedio.com.br/author/cheeseicicle1/]https://sobrouremedio.com.br/author/cheeseicicle1/[/url] cable TV, and the growth of the video rental market.
[url=https://t.me/dogma_park_samolet]Dogma Парк канал telegram[/url]
https://t.me/dogma_park_samolet
https://turatelsiz.com/
To access YouTube's data services, you'll need to generate a [url=https://youtube-api-v3.com/]YouTube API key[/url]. This essential key allows your application to communicate with YouTube's servers, enabling you to fetch video data, manage playlists, and more.
To access YouTube's data services, you'll need to generate a [url=https://youtube-api-v3.com/]YouTube API key[/url]. This essential key allows your application to communicate with YouTube's servers, enabling you to fetch video data, manage playlists, and more.
Нужно быть оптимистом.
The risk of extinction. There are factors that have led to the disappearance of certain [url=https://boba-oppa.io/]https://boba-oppa.io/[/url]; these cases are rare and unique for specific coins.
when registering, use the betrivers [url=http://winchilecasino1winchileclcom.bearsfanteamshop.com/bonus-casino-1win-1win-chile-cl-com]http://winchilecasino1winchileclcom.bearsfanteamshop.com/bonus-casino-1win-1win-chile-cl-com[/url] sbrbonus promo code to receive a bonus. base games in online casino bally small, however the main thing is quality, but not volume.
Извините за то, что вмешиваюсь… У меня похожая ситуация. Приглашаю к обсуждению.
lego city - конструкторы Лего Сити для любителей городской бытия. С [url=https://sesobl.dp.ua/]https://sesobl.dp.ua/[/url] Ниндзяго можно возвести мир ниндзя с секретными храмами и драконами.
Я считаю, что Вы не правы. Давайте обсудим.
He became interested in [url=https://doge-coin20.io/]doge-coin20.io[/url] in 2011 when he came across Satoshi Nakamoto's white paper on slashdot and began to study bitcoin and new protocols in laying.
KRAKEN - ссылка, зеркало, сайт, <a href=https://krn1.at>кракен тор</a>
Furniture of any shape and style looks very attractive and modern in ULTRA fabric [url=http://infel-moscow.ru/bitrix/redirect.php?event1=click_to_call&event2=&event3=&goto=https://rental-car.company/]http://infel-moscow.ru/bitrix/redirect.php?event1=click_to_call&event2=&event3=&goto=https://rental-car.company/[/url]
Gay Boys Porn <a href=https://gay0day.com/>https://gay0day.com</a> HD is the best gay porn tube to watch high definition videos of horny gay boys jerking, sucking their mates and fucking on webcam
Согласен, эта блестящая мысль придется как раз кстати
know-how are not random one hundred percent%, however, thanks to a combination the algorithm used and the values what they define on each card [url=https://haidangbienhoa.com/2022/07/01/5-most-beautiful-islands-in-asia/]https://haidangbienhoa.com/2022/07/01/5-most-beautiful-islands-in-asia/[/url] is random enough that no one player had the opportunity to find a pattern or crack it.
Одной из дополнительных мотиваций для приобретения временного виртуального номера в Турции является экономия средств [url=https://www.0412.ua/list/495010]https://www.0412.ua/list/495010[/url]
cs go betting <a href=https://csdb.gg/>csgo gambling sites</a>
Извините за то, что вмешиваюсь… Мне знакома эта ситуация. Готов помочь.
but also it is a little convenient to take attention from bitcoin, which as before remains the main [url=https://bitcoin-recovery.io/]https://bitcoin-recovery.io/[/url] worldwide.
Abrone is a top AI <a href=https://abrone.com/>https://abrone.com</a> and data analytics company, focused on transforming businesses with advanced data science, machine learning, and AI solutions. We help global enterprises harness their data’s full potential, driving innovation and growth. Our expert teams provide end-to-end services, from data strategy to AI automation, ensuring measurable results and lasting value creation.
А есть похожий аналог?
La funcion Seon sequence analysis, por ejemplo, [url=http://www.firenzepsicologo.it/2020/03/12/lo-sviluppo-nei-primi-anni-di-vita/]http://www.firenzepsicologo.it/2020/03/12/lo-sviluppo-nei-primi-anni-di-vita/[/url], puede ver la cadena del correo electronico para asegurarse de que ella no se considera demasiado general.
cs2 gambling <a href=https://csdb.gg/>csgo gambling sites</a>
Узнайте, как выход Counter-Strike 2 <a href=https://vitality.moykinder.com/>https://vitality.moykinder.com</a> изменил киберспорт и помог Team Vitality укрепить свои позиции на мировой арене.
https://deneme-bonusu-veren-siteler.org/
It's best and original [url=https://bentley-villas.ae/]bentley villas dubai[/url]
https://deneme-bonusu-veren-siteler.org/
Браво, блестящая идея и своевременно
????? ???? ?????? ???? ????? ?????? ?????? ???? ??: ?? ?? ???? ?? ??? [url=http://reoadvisors.com/shutterstock_143499223-2/]http://reoadvisors.com/shutterstock_143499223-2/[/url] ???? ??? ????, ??????? ????!
TradingEvent <a href=https://tradingevent.ru/>https://tradingevent.ru</a> это информационный портал для трейдеров и инвесторов, который предлагает актуальные прогнозы по движению финансовых активов, включая акции, валюты, криптовалюты
https://deneme-bonusu-veren-siteler.org/
Верный ответ
Este tem deposito automatico em cash jogos, rebuys e eletronicos em competicoes, a capacidade de enfatizar sua pilha de fichas, blinds ou Money, [url=http://sada-color.maki3.net/bbs/bbs.cgi?page=0&ar=27&details=0303]http://sada-color.maki3.net/bbs/bbs.cgi?page=0&ar=27&details=0303[/url] juntamente com tamanhos de apostas totalmente personalizaveis.
Experience luxury and style at [url=https://bentley-villas.ae/]mira villas by bentley home[/url], where elegance meets comfort.
Counter-Strike 2 и команда SAW <a href=https://saw.pozdravte.com/>https://saw.pozdravte.com</a> как португальская команда адаптируется к новой версии игры и демонстрирует отличные результаты в киберспорте.
gambling sites <a href=https://csdb.gg/>cs2 gambling</a>
реально улет!ждем с нетерпением релиза и будем зажигать!!!!!!
Дата. Подпись». После нужно отослать оба файла через [url=https://youstaysemarang.com/hidden-gems-semarang-rahasia-jarang-diketahui/]https://youstaysemarang.com/hidden-gems-semarang-rahasia-jarang-diketahui/[/url] раздел «Верификация документов». Кэш-дроп активируется хаотично и делится между всеми активными игроками соответствующих лимитов.
??? ??????? - ?? ????????? ??????? ?? ????? ?? ?????? ??????? ??????? ???????? ? ???? ?????? ????????? ????????? ??????? ????? ?????? ?? ????? ??????? ??????? ? ??????? ???? ??? ? ??? ????? ??? ??? ?????? ??????? ???? ????? ??????? ? ? ?? ??? ??? ????? ??????? ??? ??? ??????. ???? ? ?????? ??? ???? ????? ???? ????? ??? [url=https://cristianoronaldo-ar.com/]https://cristianoronaldo-ar.com/[/url]? ???? ????? ??????? ??????? ??????? ????????.
Букмекерская контора <a href=https://1win-1vinbk.com/>1вин</a> предоставляет пользователям широкий выбор ставок на спорт, высокие коэффициенты и удобный интерфейс. Быстрые выплаты, регулярные бонусы и акции делают 1Win популярной среди игроков. Присоединяйтесь к 1Win и начните выигрывать уже сегодня!
Обмен криптовалюты в Киеве Лучший курс Безопасно купить/продать, обменять крипту на наличные в городе Киев (Украина) через Онлайн криптообменник [url=https://1vesti.kyiv.ua/onlajn-obmennik-kriptovalyut-vse-chto-stoit-znat.html]Обменник криптовалют[/url]
helium balloon store <a href=https://helium-balloon-price.com/>custom balloons with inscription Dubai</a>
Платформа <a href=https://1win-1vinbk.com/>1вин</a> предлагает широкий выбор спортивных событий, киберспорта и азартных игр. Пользователи получают высокие коэффициенты, быстрые выплаты и круглосуточную поддержку. Программа лояльности и бонусы делают игру выгоднее.
https://aviator-app.org/
Some of these flowers include azaleas, peonies, and orchids! These flowers can make all the difference in their day and hopefully attract good luck [url=https://thatsup.co.uk/native/the-best-flower-delivery-services-in-the-uk/]https://thatsup.co.uk/native/the-best-flower-delivery-services-in-the-uk/[/url]
Plan1&1
https://physioneedsng.com/question/%d0%bf%d0%be%d0%b2%d0%b5%d1%80%d0%ba%d0%b0-%d1%81%d1%87%d0%b5%d1%82%d1%87%d0%b8%d0%ba%d0%b0-%d0%b2%d0%be%d0%b4%d1%8b/
Сайт Новости Николаева - Николаев 24 <a href=https://24.mk.ua/>https://24.mk.ua/top-news/</a> является актуальным источником новостей для жителей Николаева и области. Свежие новости города, события, аналитика, а также информация о социальных, экономических и культурных аспектах региона.
смотреть фильм хорошего качества бесплатно без рекламы <a href=https://filmy-smotret1.ru/>смотреть фильмы онлайн в качестве 1080</a>
<a href="https://india-aviator-game.com/">aviator apk game</a>
The visibility of penetration/fellatio/[url=http://xindongro.weclub.info/viewthread.php?tid=819302&extra=]http://xindongro.weclub.info/viewthread.php?tid=819302&extra=[/url] and most often causes fears of censors and critics, that what such happened on set.
custom balloons Dubai <a href=https://cheap-helium-balloons.com/>https://cheap-helium-balloons.com</a>
correct resume of an engineer <a href=https://engineer-builder-resume.com/>website builder resume for example for engineers</a>
Оптоволоконные лазерные станки для высокой производительности
Предлагаем оптоволоконные лазерные станки, которые обеспечивают быструю и точную резку металла с минимальными затратами на электроэнергию.
станок с лазерной резкой металла [url=https://lazernye-stanki.ru/]лазерный станок для резки листового металла[/url] .
Studio di produzione video <a href=https://orbispro.it/>https://orbispro.it </a> a ciclo completo. Servizi di creazione video. La nostra produzione effettua riprese video e qualsiasi altra produzione video a Milano, Roma, Torino
elektroniskie maki biezi nodrosina visvairak iss apstrades laiks, [url=https://www.lyfesaverscpr.com/ka-iznemt-naudu-no-aviator-speles/]https://www.lyfesaverscpr.com/ka-iznemt-naudu-no-aviator-speles/[/url] un lidzekli parasti ierodas galapunkts laika 24 stundas.
<a href="https://india-aviator-game.com/">spribe aviator game</a>
se voce se move em um barco procurando baleias e golfinhos, [url=https://taxitour29.com/bbs/board.php?bo_table=free&wr_id=13895]https://taxitour29.com/bbs/board.php?bo_table=free&wr_id=13895[/url] voce, provavelmente, parara em processo enseadas para mergulhar em tal ilha maravilhosa de contrastes entre verde e azul.
Новости Украины и мира <a href=https://lentanews.kyiv.ua/>https://lentanews.kyiv.ua</a> оперативные и объективные сводки событий.
Самые важные новости <a href=https://pto-kyiv.com.ua/>https://pto-kyiv.com.ua</a> на одном портале: политика, экономика, происшествия, спорт и культура. Оперативно, достоверно, актуально — следите за событиями вместе с нами!
Женская красота <a href=https://7krasotok.com/>https://7krasotok.com</a> здоровье - женский онлайн журнал. Новости звезд, тренды моды и красоты, правильное питание, рецепты вкусных блюд.
Статьи о здоровье <a href=https://pobedilivmeste.org.ua/>https://pobedilivmeste.org.ua</a> питании и фитнесе. Практические рекомендации для поддержания вашего организма в отличном состоянии.
Всё о здоровье <a href=https://expertlaw.com.ua/>https://expertlaw.com.ua</a> как питаться правильно, сохранять физическую активность и заботиться о теле и душе.
Новости автоиндустрии <a href=https://eurasiamobilechallenge.com/>https://eurasiamobilechallenge.com</a> обзоры моделей, советы по обслуживанию и вождению. Всё для автолюбителей и профессионалов на одном сайте!
Интерактивный женский журнал <a href=https://muz-hoz.com.ua/>https://muz-hoz.com.ua</a> стильные образы, идеи для развития, практические советы по здоровью и отношениям. Всё, что нужно для гармоничной жизни и самореализации.
<a href="https://9unity.com/read-blog/11138">aviator game online</a>
<a href=https://auroracasino-am.buzz>зеркало аврора казино для мобильных на сегодня</a>
<a href=https://bitz-casino-ekol.xyz>bitz casino</a>
Идеи для рукоделия <a href=https://sweaterok.com.ua/>https://sweaterok.com.ua</a> мастер-классы, инструкции и вдохновение для создания уникальных изделий. Узнайте больше о шитье, вязании, вышивке и других видах творчества!
Недорогие <a href=https://hurgada-excurs-tours.ru/>экскурсии в Хургаде</a> цены 2024-2025. Бесплатный трансфер. Русскоязычный гид. Более 3000 реальных отзывов.
<a href="https://micro.blog/andmskkdkdd">aviator download</a>
Elevate your gaming experience at [url=https://taya365-2.icu/]taya365[/url], where cutting-edge features and fun await.
Hello!
Want Bigger Jackpots and Better Thrills? Treat Yourself to a New Brand & a New Welcome Bonus! Register here: https://deckaffiliates.com/c/492304
для победы игроку потребуется угадать только одну комбинацию. новое интернет-казино, [url=https://indsafe.ru/]Узнайте больше о Kometa Casino[/url] с великолепным продуманным дизайном портала и разнообразным ассортиментом игр от лучших провайдеров.
Скачать игры на Андроид <a href=https://appdatabase.ru/>https://appdatabase.ru</a> бесплатно на русском языке. Откройте для себя новые приключения!
Официальный сайт Мостбет <a href=https://cryptofarm-expo.ru/>https://obukhov-sport.ru</a> бонусы за вход, промокоды и фриспины в онлайн казино Mostbet. Надежная букмекерская компания и онлайн казино.
Мостбет <a href=https://belayaistoriya.ru/>https://belayaistoriya.ru</a> откройте для себя азарт в казино. Простая регистрация, множество бонусов и удобный вход обеспечат незабываемый игровой опыт. Используйте промокоды для увеличения выигрышей.
Discover Rafael Nadal's <a href=https://tennis.rafael-nadal-fr.com/>https://tennis.rafael-nadal-fr.com</a> impressive rise to the top of world tennis, from his debut to his career Grand Slam victory.
Experience passion and tradition by climbing to the top of Beaujoire <a href=https://beaujoire.nantes-fr.com/>https://beaujoire.nantes-fr.com</a> home of the legendary FC Nantes. Go from finish to an unforgettable match.
Telegram virtual phone number is a virtual phone number designed for registering Telegram accounts. Unlike physical SIM cards, virtual numbers are generated online and users can use them without having to buy a new SIM card [url=http://www.17lbw.cn/20241017/22390456.html]http://www.17lbw.cn/20241017/22390456.html[/url]
<a href="https://wallhaven.cc/user/playaviatorindia">aviator game download</a>
<a href="https://geoamor.com/read-blog/40418">aviator predictor</a>
гадание таро по имени мужчины <a href=https://gadaniepotaro.ru/>https://gadaniepotaro.ru</a>
соут сотрудников <a href=https://sout095.ru/>https://sout095.ru</a>
in form incentive prize you can study with the "table", when it is that fact, when recommended adhere to principles games in an [url=http://discovertheindia.com/tours/hornbill-festival-and-kaziranga-national-park-6-nights-7-days/]http://discovertheindia.com/tours/hornbill-festival-and-kaziranga-national-park-6-nights-7-days/[/url], in order raise available opportunities.
экспертный центр специальной оценки условий труда <a href=https://sout095.ru/>https://sout095.ru</a>
Hello folks!
I came across a 77 very cool site that I think you should explore.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://greume.com/the-basics-of-protecting-your-newborns-and-toddlers-from-heatstrokes/]https://greume.com/the-basics-of-protecting-your-newborns-and-toddlers-from-heatstrokes/[/url]
Hello folks!
I came across a 77 very cool site that I think you should explore.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://greume.com/the-basics-of-protecting-your-newborns-and-toddlers-from-heatstrokes/]https://greume.com/the-basics-of-protecting-your-newborns-and-toddlers-from-heatstrokes/[/url]
Hello folks!
I came across a 77 awesome tool that I think you should dive into.
This platform is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.aboutbiography.com/most-dog-friendly-cities-in-the-uk/]https://www.aboutbiography.com/most-dog-friendly-cities-in-the-uk/[/url]
Hello folks!
I came across a 77 awesome tool that I think you should dive into.
This platform is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.aboutbiography.com/most-dog-friendly-cities-in-the-uk/]https://www.aboutbiography.com/most-dog-friendly-cities-in-the-uk/[/url]
Hello folks!
I came across a 77 awesome tool that I think you should dive into.
This platform is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.aboutbiography.com/most-dog-friendly-cities-in-the-uk/]https://www.aboutbiography.com/most-dog-friendly-cities-in-the-uk/[/url]
Hello lads!
I came across a 77 very cool tool that I think you should dive into.
This resource is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://technewstube.com/special/1515425/download-mobile-games-uber-cool-fun/]https://technewstube.com/special/1515425/download-mobile-games-uber-cool-fun/[/url]
Hello lads!
I came across a 77 very cool tool that I think you should dive into.
This resource is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://technewstube.com/special/1515425/download-mobile-games-uber-cool-fun/]https://technewstube.com/special/1515425/download-mobile-games-uber-cool-fun/[/url]
Hello lads!
I came across a 77 very cool tool that I think you should dive into.
This resource is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://technewstube.com/special/1515425/download-mobile-games-uber-cool-fun/]https://technewstube.com/special/1515425/download-mobile-games-uber-cool-fun/[/url]
Hello lads!
I came across a 77 very cool tool that I think you should dive into.
This resource is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://technewstube.com/special/1515425/download-mobile-games-uber-cool-fun/]https://technewstube.com/special/1515425/download-mobile-games-uber-cool-fun/[/url]
thanks, interesting read
_________________
[URL=https://igra.best-slot-games.rent]argo casino бездепозитный бонус[/URL]
Доброго!
СЭС Эксперт — это ваш надежный партнер в борьбе с клопами в Домодедовое. Мы предлагаем качественную обработку с гарантией быстрого решения проблемы.
Подробная информация - http://www.xn----ttbdhebndao7ic.xn--p1ai
Профессиональная борьба с клопами
Как избавиться от клопов в Искитиме
Уничтожение клопов в доме
Обработка от клопов в квартире
СЭС уничтожение клопов
[url=http://www.xn----ttbdhebndao7ic.xn--p1ai]Как выбрать сервис по уничтожению клопов[/url]
Удачи!
Enjoy fast-paced gameplay and big wins at [url=https://taya365-3.in/]taya365[/url], the ultimate online gaming platform.
Я извиняюсь, но, по-моему, Вы не правы. Я уверен. Могу это доказать. Пишите мне в PM, пообщаемся.
Турниры в redstar poker понравятся людям, [url=https://ok-okano.net/?attachment_id=4]https://ok-okano.net/?attachment_id=4[/url] ценящим игру с ограниченным банком. Рекомендуется пройти процедуру заранее.
Cool, I've been looking for this one for a long time
_________________
[url=https://igra.smega-lotto.site]qt сигналы и слоты между окнами[/url]
Веселые короткие анекдоты <a href="http://shutki-anekdoty.ru/korotkie-anekdoty">http://shutki-anekdoty.ru/korotkie-anekdoty</a>.
Профессиональный сервисный центр по ремонту телефонов в Москве.
Мы предлагаем: <a href=https://proremont-telefonov.ru/>ремонт смартфона</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Извините за то, что вмешиваюсь… Но мне очень близка эта тема. Могу помочь с ответом. Пишите в PM.
For example, organizations working with [url=https://www.oivp.nl/bg/]https://www.oivp.nl/bg/[/url] use machine education in software to coordinate data about security and events (siem) to search suspicious activity and potential threats.
<a href="https://india-aviator-game.com/">spribe aviator game</a>
Discover why [url=https://taya365-3.xyz/]taya365[/url] is a favorite among players seeking thrilling games and high payouts.
Профессиональный сервисный центр по ремонту телефонов в Москве.
Мы предлагаем: <a href=https://proremont-telefonov.ru/>ремонт телефон</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
KRAKEN - ссылка, зеркало, сайт,
<a href="https://india-aviator-game.com/">aviator game online</a>
[url=https://github.com/avesgit/awesome-online-services]awesome online services[/url]
Профессиональный сервисный центр по ремонту телефонов в Москве.
Мы предлагаем: <a href=https://proremont-telefonov.ru/>ближайшая мастерская по ремонту телефонов</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Территория строгих правил и высоких налогов — Западная Европа манит iGaming-операторов, обещая богатство и успех. И не удивительно — на эту часть света приходится почти половина объема всего мирового рынка онлайн-гемблинга [url=https://mellstroy-stream-kick.ru/]мелстрой казино[/url]
Наслаждайтесь азартом и захватывающими ставками на [url=https://forumeurasia.ru/]1win[/url], ведущей платформе для онлайн-игр и ставок. Здесь вы найдете широкий выбор спортивных событий, казино-игр и живых дилеров, доступных 24/7.
В Мюнхене имеется много курьерских служб продуктов, [url=https://www.pinazza-bauexperten.ch/limited-edition-series-artworks-from-another-fine-mess/]https://www.pinazza-bauexperten.ch/limited-edition-series-artworks-from-another-fine-mess/[/url] большинство которых доставляют с понедельника по субботу.
единственный параметр, [url=https://meiway.de/?attachment_id=1095]https://meiway.de/?attachment_id=1095[/url] по которому мы отбираем партнеров - соответствие параметрам качества. сосредоточьтесь на важном. bolt - ваш верный клинер в сегменте логистики.
<a href="https://india-aviator-game.com/">aviator download</a>
Профессиональный сервисный центр по ремонту телефонов в Москве.
Мы предлагаем: <a href=https://proremont-telefonov.ru/>срочный ремонт телефонов</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
реклама в лифте жк <a href=https://reklama-v-liftah-msk.ru/>https://reklama-v-liftah-msk.ru</a>
Профессиональный сервисный центр по ремонту компьютерных видеокарт по Москве.
Мы предлагаем: <a href=https://remont-videokart-biz.ru/>ремонт видеокарт nvidia</a>
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
реклама в лифтах дома <a href=https://reklama-v-liftah-msk.ru/>реклама в лифте стоимость</a>
<a href="https://india-aviator-game.com/">aviator download</a>
Современные системы управления помогают контролировать каждый этап, от первичной обработки до упаковки. Это не только снижает риск ошибок, но и экономит ресурсы [url=http://fr99659i.bget.ru/forum/showtopic-2755]http://fr99659i.bget.ru/forum/showtopic-2755[/url]
Шовкові халати шовкові сорочки шовкові комплекти шифонові халати шифонові сорочки чоловічі ФУТБОЛКИ прапор України Патріотичні футболки розпродаж махрові [url=https://missanomis.com/priprave-so-stekle/]https://missanomis.com/priprave-so-stekle/[/url] Піжами Подарункові сертифікати.
88f422d
[url=https://gotwebsite1.com/local-seo-mesa/]Nearby SEO methods for restaurants[/url]
88f422d
[url=https://gotwebsite1.com/local-seo-mesa/]Nearby SEO methods for restaurants[/url]
88f422d
[url=https://gotwebsite1.com/local-seo-mesa/]Nearby SEO methods for restaurants[/url]
88f422d
[url=https://gotwebsite1.com/local-seo-mesa/]Nearby SEO methods for restaurants[/url]
88f422d
[url=https://gotwebsite1.com/local-seo-mesa/]Nearby SEO methods for restaurants[/url]
Сделать ее более полной и увлекательной помогут объективные комментарии тех, [url=https://dzen.ru/besarte]https://dzen.ru/besarte[/url] кто хорошо знаком с творчеством и фактами биографии данного автора.
Профессиональный <a href=https://massageivanteevka.ru/page/osteopaticheskiy-massaj>остеопат Ивантеевка</a>: безопасные и эффективные техники для снятия боли, улучшения осанки и гармонизации тела. Запишитесь на приём и почувствуйте заботу о своём здоровье
<a href="https://india-aviator-game.com/">aviator predictor</a>
<a href="https://india-aviator-game.com/">aviator</a>
[url=][/url]
Временная регистрация в Москве: Быстро и Легально!
Ищете, где оформить временную регистрацию в Москве?
Мы гарантируем быстрое и легальное оформление без очередей и лишних документов.
Ваше спокойствие – наша забота!
Минимум усилий • Максимум удобства • Полная легальность
Свяжитесь с нами прямо сейчас!
<a href=https://legalreg945.ru/>Временная регистрация в Москве</a>
[url=][/url]
<a href=https://kwork.ru/links/17002285/obratnie-ssylki-seo-prodvizhenie>обратные ссылки купить</a>
[url=][/url]
Временная регистрация в Москве: Быстро и Легально!
Ищете, где оформить временную регистрацию в Москве? Мы гарантируем быстрое и легальное оформление без очередей и лишних документов. Ваше спокойствие – наша забота!
Минимум усилий • Максимум удобства • Полная легальность
Свяжитесь с нами прямо сейчас!
[url=https://мосрегистрация77.рф/].[/url]
[url=][/url]
Начни новые отношения <a href=https://top-znakomstv.ru/loveplanet/>знакомства Loveplanet</a> точный подбор по интересам, удобное общение и реальные знакомства для тех, кто ищет любовь и серьёзные отношения.
CS2 не только сохраняет традиции <a href=https://monesy.synology-forum.ru/>https://monesy.synology-forum.ru</a> оригинальной серии, но и создает новые возможности для киберспорта.
Hello .!
I came across a 78 fantastic website that I think you should dive into.
This tool is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.visitfashions.com/how-to-treat-your-laptop-battery-correctly/]https://www.visitfashions.com/how-to-treat-your-laptop-battery-correctly/[/url]
Hello guys!
I came across a 78 awesome site that I think you should visit.
This tool is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.appgamers.de/games-und-apps/limbo-duesteres-indie-abenteuer-im-appgamers-spieletest]https://www.appgamers.de/games-und-apps/limbo-duesteres-indie-abenteuer-im-appgamers-spieletest[/url]
Hello guys!
I came across a 78 awesome site that I think you should visit.
This tool is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.appgamers.de/games-und-apps/limbo-duesteres-indie-abenteuer-im-appgamers-spieletest]https://www.appgamers.de/games-und-apps/limbo-duesteres-indie-abenteuer-im-appgamers-spieletest[/url]
Hello guys!
I came across a 78 awesome site that I think you should visit.
This tool is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.appgamers.de/games-und-apps/limbo-duesteres-indie-abenteuer-im-appgamers-spieletest]https://www.appgamers.de/games-und-apps/limbo-duesteres-indie-abenteuer-im-appgamers-spieletest[/url]
бытовка на заказ по индивидуальным размерам недорого <a href=https://bytovka-price.ru/>бытовка калуга</a>
Always relevant information: <a href=https://www.freelanceuk.com/>https://www.freelanceuk.com</a>
Hello guys!
I came across a 78 fantastic page that I think you should visit.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.wearebrighton.com/matchday/all-aboard-the-de-zerbi-train-for-brighton-v-spurs/]https://www.wearebrighton.com/matchday/all-aboard-the-de-zerbi-train-for-brighton-v-spurs/[/url]
Hello guys!
I came across a 78 fantastic page that I think you should visit.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.wearebrighton.com/matchday/all-aboard-the-de-zerbi-train-for-brighton-v-spurs/]https://www.wearebrighton.com/matchday/all-aboard-the-de-zerbi-train-for-brighton-v-spurs/[/url]
Hello guys!
I came across a 78 fantastic page that I think you should visit.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.wearebrighton.com/matchday/all-aboard-the-de-zerbi-train-for-brighton-v-spurs/]https://www.wearebrighton.com/matchday/all-aboard-the-de-zerbi-train-for-brighton-v-spurs/[/url]
Hello guys!
I came across a 78 fantastic page that I think you should visit.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.wearebrighton.com/matchday/all-aboard-the-de-zerbi-train-for-brighton-v-spurs/]https://www.wearebrighton.com/matchday/all-aboard-the-de-zerbi-train-for-brighton-v-spurs/[/url]
Hello guys!
I came across a 78 helpful platform that I think you should browse.
This tool is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://gamingspell.com/exploring-the-timeless-charming-online-games/]https://gamingspell.com/exploring-the-timeless-charming-online-games/[/url]
[url=][/url]
Временная регистрация в Москве: Быстро и Легально!
Ищете, где оформить временную регистрацию в Москве? Мы гарантируем быстрое и легальное оформление без очередей и лишних документов. Ваше спокойствие – наша забота!
Минимум усилий • Максимум удобства • Полная легальность
Свяжитесь с нами прямо сейчас!
[url=https://regm7921.ru/].[/url]
[url=][/url]
Hello friends!
I came across a 78 awesome site that I think you should take a look at.
This resource is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://artelis.pl/artykuly/80865/cyberpunk-2077-20-trzecie-zycie-swietnej-polskiej-gry-ktora-oburzyla-caly-swiat]https://artelis.pl/artykuly/80865/cyberpunk-2077-20-trzecie-zycie-swietnej-polskiej-gry-ktora-oburzyla-caly-swiat[/url]
Hello folks!
I came across a 78 very cool website that I think you should dive into.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://snapsource.net/the-essential-tips-for-stunning-shots/]https://snapsource.net/the-essential-tips-for-stunning-shots/[/url]
Hello folks!
I came across a 78 very cool website that I think you should dive into.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://snapsource.net/the-essential-tips-for-stunning-shots/]https://snapsource.net/the-essential-tips-for-stunning-shots/[/url]
Hello folks!
I came across a 78 very cool website that I think you should dive into.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://snapsource.net/the-essential-tips-for-stunning-shots/]https://snapsource.net/the-essential-tips-for-stunning-shots/[/url]
https://www.sosouthernsoundkits.com/profile/roscarcy/profile
Montenegro immobilien am meer kaufen <a href=https://www.grundstuck-kaufen-am-meer-in-montenegro.de/>grundstuck kaufen am meer</a>
Hello !!
I came across a 78 useful page that I think you should browse.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://eyexcon.com/adhd-in-adults/]https://eyexcon.com/adhd-in-adults/[/url]
Hello !!
I came across a 78 useful page that I think you should browse.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://eyexcon.com/adhd-in-adults/]https://eyexcon.com/adhd-in-adults/[/url]
Hello !!
I came across a 78 useful page that I think you should browse.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://eyexcon.com/adhd-in-adults/]https://eyexcon.com/adhd-in-adults/[/url]
Hello !!
I came across a 78 useful page that I think you should browse.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://eyexcon.com/adhd-in-adults/]https://eyexcon.com/adhd-in-adults/[/url]
Hello !!
I came across a 78 useful page that I think you should browse.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://eyexcon.com/adhd-in-adults/]https://eyexcon.com/adhd-in-adults/[/url]
Hello everyone!
I came across a 78 valuable site that I think you should browse.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ ]https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ [/url]
Hello everyone!
I came across a 78 valuable site that I think you should browse.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ ]https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ [/url]
Hello everyone!
I came across a 78 valuable site that I think you should browse.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ ]https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ [/url]
Hello everyone!
I came across a 78 valuable site that I think you should browse.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ ]https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ [/url]
Hello lads!
I came across a 78 fantastic website that I think you should explore.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ ]https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ [/url]
Hello lads!
I came across a 78 fantastic website that I think you should explore.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ ]https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ [/url]
Hello lads!
I came across a 78 fantastic website that I think you should explore.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ ]https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ [/url]
Hello lads!
I came across a 78 fantastic website that I think you should explore.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ ]https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ [/url]
Hello lads!
I came across a 78 fantastic website that I think you should explore.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ ]https://irnpost.com/maximizing-laptop-longevity-maintenance-tips-and-upgradability/ [/url]
Hello !!
I came across a 78 awesome tool that I think you should check out.
This site is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.appgamers.de/mobile-news/nachhaltigkeit-in-gaming-industrie-schafft-gutes-gewissen]https://www.appgamers.de/mobile-news/nachhaltigkeit-in-gaming-industrie-schafft-gutes-gewissen[/url]
Hello !!
I came across a 78 awesome tool that I think you should check out.
This site is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.appgamers.de/mobile-news/nachhaltigkeit-in-gaming-industrie-schafft-gutes-gewissen]https://www.appgamers.de/mobile-news/nachhaltigkeit-in-gaming-industrie-schafft-gutes-gewissen[/url]
Hello !!
I came across a 78 awesome tool that I think you should check out.
This site is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.appgamers.de/mobile-news/nachhaltigkeit-in-gaming-industrie-schafft-gutes-gewissen]https://www.appgamers.de/mobile-news/nachhaltigkeit-in-gaming-industrie-schafft-gutes-gewissen[/url]
Hello !!
I came across a 78 awesome tool that I think you should check out.
This site is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.appgamers.de/mobile-news/nachhaltigkeit-in-gaming-industrie-schafft-gutes-gewissen]https://www.appgamers.de/mobile-news/nachhaltigkeit-in-gaming-industrie-schafft-gutes-gewissen[/url]
Hello lads!
I came across a 78 awesome website that I think you should visit.
This resource is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://notinthekitchenanymore.com/2023/05/22/digital-minimalism-on-the-computer/]https://notinthekitchenanymore.com/2023/05/22/digital-minimalism-on-the-computer/[/url]
Hello .!
I came across a 78 fantastic page that I think you should dive into.
This site is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.sportsgossip.com/things-to-do-at-a-casino/]https://www.sportsgossip.com/things-to-do-at-a-casino/[/url]
Вы попали в самую точку. Мысль отличная, согласен с Вами.
if the player connect the dapp application, you can combine with this development from keepkey, at the same time the [url=https://huobi-wallet.io/]huobi-wallet.io[/url] wallet will remain fenced through your own hardware guarantee security.
Лучшие промокоды для игр <a href=https://playpromocode.com/cs2/>https://playpromocode.com/cs2/</a> скидки и бонусы для популярных проектов. Экономьте и получайте преимущества. Регулярное обновление базы.
Магазин строительной арматуры <a href=https://mskarmatura.ru/>https://mskarmatura.ru</a> с большим выбором продукции для любых строительных задач. Высокое качество, оперативная доставка и выгодные цены. Все для прочных и надежных конструкций.
По моему мнению Вы ошибаетесь. Пишите мне в PM, обсудим.
bizde hacmi icin yukumluluk yok yukumluluk yok, sat?n alabilirsiniz [url=https://cafe-hayal.ru/kupit-virtualnyj-nomer-telefona-kitaya]https://cafe-hayal.ru/kupit-virtualnyj-nomer-telefona-kitaya[/url] tek kullan?ml?k telefon numaras?/telefon numaralar? sms veya fakslar? almak icin crm ile entegrasyon.
What a data of un-ambiguity annd preserveness of valuable familiarity
onn the topic of unpredicted feelings. https://Ternopil.Pp.ua/
Скачать моды для андроид [url=https://midgame.ru/]Скачать моды для андроид[/url]
Жаль, что не смогу сейчас участвовать в обсуждении. Не владею нужной информацией. Но с удовольствием буду следить за этой темой.
kastking should disclose this information before people accuse videos of deceptive marketing tactics by [url=http://iskradent.si/before-after/]http://iskradent.si/before-after/[/url]. With the weight of them, at 5-6 ounces, you will forget that they even exist.
На сайте <a href=https://androidcorner.ru/>https://androidcorner.ru</a> вы сможете бесплатно скачать лучшие приложения для Андроид. Доступные программы на русском языке ждут вас!
Trouvez votre parfait
<a href=https://couteaux-de-cuisine-france.fr/>Couteaux de poche</a>
de qualite superieure
заказать продвижение сайта в яндексе <a href=https://is-market.ru/>продвижение сайтов в москве</a>
All Tools For You is your go-to shop, offering a comprehensive range of power, hand, and measuring tools for every kind of project. Whether you’re undertaking home improvements, we provide expert-recommended tools to help you complete your tasks. Explore our selection at [url=https://alltoolsforyou.com/]AllToolsForYou.com[/url] for all your project needs!
[url=https://asiancatalog.ru]грузовая резина на самосвал[/url]
Наша компания https://sveller2buy.ru/ профессионально занимается поставкой сортового металлопроката оптом и в розницу
https://virtual-local-numbers.com/countries/27-portugal.html
Information that is always relevant: <a href=https://www.maxwaugh.com/>https://www.maxwaugh.com</a>
[url=https://smsbest.ru/]https://smsbest.ru/[/url]
Hurrah, that's what I waas exploring for,
what a material! existing here aat this website, thnks admin of this web
site. https://evolution.org.ua/
[url=https://smsbest.ru/]https://smsbest.ru/[/url]
<a href="http://r.turn.com/r/click?id=07SbPf7hZSNdJAgAAAYBAA&url=https://sitelerbonusu.com/">deneme bonusu veren siteler</a>
Скачать моды для андроид [url=https://5play-mods.ru/]Скачать моды для андроид[/url]
[url=https://xn--90aogkbcz.xn--80adjurfk.xn--c1avg/]поверка счетчиков обнинск[/url]
Скачать моды для андроид [url=https://modifikatsii.ru/]Скачать моды для андроид[/url]
мощение тротуарной плиткой цена <a href=https://blagoustrojstvo-spb.ru>благоустройство территории дома</a>
<a href="http://clients1.google.st/url?q=https://sitelerbonusu.com/">deneme bonusu veren siteler</a>
Скачать моды для андроид [url=https://5play-mods.ru/]Скачать моды для андроид[/url]
Скачать моды для андроид [url=https://androeedsd.ru/]Скачать моды для андроид[/url]
Скачать моды для андроид [url=https://androeed-top.ru/]Скачать моды для андроид[/url]
сайт где купить мефедрон <a href=https://mirseifov.ru/catalog/filter/naznachenie-is-malenkih_razmerov/apply>1 грамм кокаина цена</a>
Короткие <a href=http://shutki-anekdoty.ru/citaty>цитаты</a> о смысле жизни. Цитаты известных людей.
Скачать моды для андроид [url=https://androeedsd.ru/]Скачать моды для андроид[/url]
Скачать моды для андроид [url=https://androeedsd.ru/]Скачать моды для андроид[/url]
Скачать моды для андроид [url=https://androeed-top.ru/]Скачать моды для андроид[/url]
Скачать моды для андроид [url=https://dwapk.ru/]Скачать моды для андроид[/url]
Лучшие порно видео <a href=https://bonsai.casino/>Гей порно Бонсай</a> скачать бесплатно без регистрации и смс. Смотреть порно онлайн в высоком качестве.
apartments on coast of <a href=https://www.montenegro-real-estate-prices.com/>real estate Montenegro</a>
укладка кафельной плитки в спб цены <a href=https://ukladka-keramogranita-spb.ru/>https://ukladka-keramogranita-spb.ru</a>
[url=https://ast-onebox.ru/]ast onebox[/url]
Alto Consulting Group (ACG) <a href=https://alto-group.ru/>https://alto-group.ru</a> предлагает комплексные маркетинговые исследования рынков в России и за рубежом. Наша команда проводит детализированные обзоры рынков, анализирует экспорт и импорт по кодам ТНВЭД, а также изучает государственные и коммерческие закупки по 44-ФЗ и 223-ФЗ.
Скачать игры для Андроид <a href=https://igryforandroid.ru/>https://igryforandroid.ru</a> бесплатно и на русском языке, доступны новинки и популярные приложения.
Бюстгальтеры с анатомическими чашками <a href=https://www.ozon.ru/seller/caitline-242390>Бюстгальтеры с силиконовыми бретелями</a>
apple iphone 16 <a href=https://store-iphone43.ru/>смартфон apple iphone 15 pro max</a>
Montenegro property <a href=https://www.apartments-for-sale-budva.com/>https://www.apartments-for-sale-budva.com</a>
Займ 100 000 тенге <a href=https://mamont-games.ru/>Займ 250 000 тенге</a>
специальная оценка рабочих мест <a href=https://sout095.ru/>кто проводит соут</a>
Микрозайм Казахстан <a href=https://mamont-games.ru/>Sravnim.kz</a>
соут специальная оценка условий труда <a href=https://sout095.ru/>проведение соут предприятия</a>
Замечательно, весьма ценная информация
en cok etkili yontemler kurtulmak bacaklar nelerdir, [url=https://otonomhaber.com/2024/03/tabani-guclendirmek-megaparinin-yerel-spor-topluluklarinda-donusturucu-rolu/]https://otonomhaber.com/2024/03/tabani-guclendirmek-megaparinin-yerel-spor-topluluklarinda-donusturucu-rolu/[/url]? Bakanl?k, son liste 'u duyurdu!
[url=https://xn--d1amckbds1g.xn--80adjurfk.xn--c1avg/]поверка счетчиков подольск[/url]
22d3_47
[url=https://gotwebsite1.com/chandler-seo/]SEO advertising for medical professionals[/url]
22d3_47
[url=https://gotwebsite1.com/chandler-seo/]SEO advertising for medical professionals[/url]
прокат снаряжения красная поляна цены <a href=https://prokat-lyzh-krasnaya-polyana.ru/>аренда лыж красная поляна</a>
айфон 16 про купить <a href=https://store-iphone43.ru/>iphone 15 pro купить в рассрочку</a>
прокат сноубордов поляна <a href=https://prokat-lyzh-krasnaya-polyana.ru/>арендовать лыжи Адлер</a>
Топ казино <a href=https://rejtingkazino.com/>Казино на деньги</a>
укладка кафельной плитки кухне <a href=https://ukladka-keramogranita-spb.ru/>https://ukladka-keramogranita-spb.ru</a>
аренда лыж красная поляна <a href=https://prokat-lyzh-krasnaya-polyana.ru/>прокат горнолыжных лыж Адлер</a>
ссылка на блэк спрут в тор <a href=https://blacksprut-1.ru/>блэкспрут ссылка</a>
It is removed (has mixed topic)
HoReCa Training <a href=https://horeca-training.ru/>https://horeca-training.ru</a> это тренинги по развитию в сфере гостиничного бизнеса и туризма. Обучение линейного и управляющего персонала ресторанов, гостиниц и отелей. Наша цель — повысить уровень обслуживания и эффективности работы сотрудников, а также обеспечить их необходимыми навыками для успешного выполнения обязанностей. Мы уверены, что качественное обучение является ключом к успешному развитию в гостиничном бизнесе и туризме!
Онлайн казино [url=https://starz888.com/]888 starz официальный сайт[/url] ждет новых и старых друзей. Заходите и выигрывайте! https://starz888.com/
укладка кафельной плитки ванной комнате <a href=https://ukladka-keramogranita-price.ru/>https://ukladka-keramogranita-price.ru</a>
<a href=https://ibcatx.com>Microblading removal Austin</a>
Вы допускаете ошибку. Могу отстоять свою позицию. Пишите мне в PM, поговорим.
для отдыха используйте специальные [url=https://autoru24.ru/]эвакуация автомобиля[/url] площадки отдыха. как вызвать эвакуатор в бельгии и франции, не узнав немецкого языка? Вызов эвакуатора можно осуществить срочно, заполнив анкету у нас на сайте.
Each photo on <a href="https://hotsexymilfs.com/buff-milf-nude/">naked buff milf </a> is crafted in high-definition detail. These MILFs bring natural magnetism to every frame. From soft nudes, every gallery offers a unique experience that’s impossible to resist.
Это очень ценное мнение
Njut av utmarkta virtuella spel och Njut av spelet i any av dina favorit kasinospel, vilken du hittar i casino golv-overallt pa vilken du det finns/det kommer att finnas [url=https://resprocare.com/mauris-sit-amet-finibus-lacus/]https://resprocare.com/mauris-sit-amet-finibus-lacus/[/url] signal!
Найдите рабочее зеркало приложения [url=https://mostbet-wti1.top/]мостбет[/url] и скачайте его без проблем для удобной и быстрой игры в онлайн ставках на спорт.
Сглобяеми къщи за активен начин на живот: удобство и стил за вашия дом
сглобяеми къщи [url=https://www.sglobyaemi-kushti.com]https://www.sglobyaemi-kushti.com[/url] .
Апостатудо - это не просто игра, а отличный тренажёр для ума. С каждым уровнем сложности вы будете развивать аналитические навыки и совершенствовать стратегическое мышление <a href="https://play.google.com/store/apps/details?id=saper.classic.game">Clube VIP Apostatudo</a>
https://pq.hosting/vps-vds-united-kingdom-england-london-great-britain
Межкомнатные раздвижные перегородки на заказ. Купить с доставкой по России. Действуют акции, системы скидок и специальных предложений <a href="http://loft-zonirovanie.ru">система хранения для гардеробной купить недорого</a>
Необходимый агрегат для сортировки материалов для переработки отходов, обладающий высокой производительностью.
Оборудование для смешивания материалов [url=barabaniy-grohot.moscow]barabaniy-grohot.moscow[/url] .
https://loop.frontiersin.org/people/2914111/bio
Я извиняюсь, но, по-моему, Вы не правы. Я уверен. Могу отстоять свою позицию. Пишите мне в PM.
nevertheless, for a fundamental assessment of cryptocurrencies it is necessary to take into account various parameters, like technical documentation, liquidity and size of trading, commissions, market capitalization of [url=https://kanagawa7-memorial.com/blog_articles/1615542444.html]https://kanagawa7-memorial.com/blog_articles/1615542444.html[/url] and similar criteria of the project.
Я уверен, что это — неправда.
сейчас различная деятельность различных компаний не проходит без очень тесного взаимодействия с корпорациями, [url=http://www.korolev.3nx.ru/viewtopic.php?t=4361&highlight=%E3%F0%F3%E7]http://www.korolev.3nx.ru/viewtopic.php?t=4361&highlight=%E3%F0%F3%E7[/url] которые занимаются грузоперевозками (транспортно-транспортная компания).
Hello friends!
I came across a 85 interesting page that I think you should browse.
This resource is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.thetalka.org/outdoor-activities-for-a-healthier-happier-you/]https://www.thetalka.org/outdoor-activities-for-a-healthier-happier-you/[/url]
Hello folks!
I came across a 85 valuable tool that I think you should dive into.
This platform is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/]https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/[/url]
Hello folks!
I came across a 85 valuable tool that I think you should dive into.
This platform is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/]https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/[/url]
Hello folks!
I came across a 85 valuable tool that I think you should dive into.
This platform is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/]https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/[/url]
Hello folks!
I came across a 85 valuable tool that I think you should dive into.
This platform is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/]https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/[/url]
Hello folks!
I came across a 85 valuable tool that I think you should dive into.
This platform is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/]https://theportablegamer.com/2024/03/19/mobile-gaming-for-education-exploring-the-benefits-of-gamified-learning-apps/[/url]
Hello folks!
I came across a 85 useful site that I think you should take a look at.
This platform is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://ramechanic.com/taming-tech-tantrums-your-troubleshooter-sidekick/]https://ramechanic.com/taming-tech-tantrums-your-troubleshooter-sidekick/[/url]
Hello folks!
I came across a 85 useful site that I think you should take a look at.
This platform is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://ramechanic.com/taming-tech-tantrums-your-troubleshooter-sidekick/]https://ramechanic.com/taming-tech-tantrums-your-troubleshooter-sidekick/[/url]
Hello folks!
I came across a 85 useful site that I think you should take a look at.
This platform is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://ramechanic.com/taming-tech-tantrums-your-troubleshooter-sidekick/]https://ramechanic.com/taming-tech-tantrums-your-troubleshooter-sidekick/[/url]
Hello guys!
I came across a 85 great tool that I think you should visit.
This site is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/]https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/[/url]
Hello guys!
I came across a 85 great tool that I think you should visit.
This site is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/]https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/[/url]
Hello guys!
I came across a 85 great tool that I think you should visit.
This site is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/]https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/[/url]
Hello guys!
I came across a 85 great tool that I think you should visit.
This site is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/]https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/[/url]
Hello guys!
I came across a 85 great tool that I think you should visit.
This site is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/]https://fameblogs.net/seven-anne-hathaway-iconic-acting-performances/[/url]
Hello friends!
I came across a 85 helpful platform that I think you should check out.
This resource is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/]https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/[/url]
Hello friends!
I came across a 85 helpful platform that I think you should check out.
This resource is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/]https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/[/url]
Hello friends!
I came across a 85 helpful platform that I think you should check out.
This resource is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/]https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/[/url]
Hello friends!
I came across a 85 helpful platform that I think you should check out.
This resource is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/]https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/[/url]
Hello friends!
I came across a 85 helpful platform that I think you should check out.
This resource is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/]https://waschen-wie-walter.de/haendewaschen-und-lebensmittelsicherheit-keime-aus-der-kueche-fernhalten/[/url]
Hello everyone!
I came across a 85 useful site that I think you should dive into.
This tool is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/]https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/[/url]
Hello everyone!
I came across a 85 useful site that I think you should dive into.
This tool is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/]https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/[/url]
Hello everyone!
I came across a 85 useful site that I think you should dive into.
This tool is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/]https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/[/url]
Hello everyone!
I came across a 85 useful site that I think you should dive into.
This tool is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/]https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/[/url]
Hello everyone!
I came across a 85 useful site that I think you should dive into.
This tool is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/]https://www.unfoldingroma.com/cultura/21976/arte-nelle-strade:-una-guida-ai-murales-pi%C3%B9-sorprendenti-di-roma/[/url]
також серед їх інгредієнтів присутні діючі доглядають сполуки, [url=https://www.ewelinazieba.com/pomysl-na-jesienny-slub-w-warszawie-till-death/]https://www.ewelinazieba.com/pomysl-na-jesienny-slub-w-warszawie-till-death/[/url] що дозволяють реанімувати здоров'я волосся і захистити від негативного механічних пошкоджень.
To avoid such ridiculous situations and not get into trouble, we recommend that you consider buying a smoking cap in our online store. Here you can find thimbles of various shapes and designs, made of the best materials <a href="https://vidomosti-ua.com/science/134319">https://napas420.com/ru/naperstki-dlya-kureniya/</a>
<a href=https://vectorprava59.ru/>https://vectorprava59.ru/</a>
Запчасти ВАЗ: найти нужные детали легко в нашем интернет-магазине
запчасти на ладу [url=https://avtozapchasti-vaz1.ru/]запчасти на ладу[/url] .
Discover modern living at [url=https://rove-home-dubai-marina.ae/]rove home dubai marina[/url], where stylish design meets the vibrant lifestyle of Dubai’s iconic waterfront destination.
нормы ферритина при беременности в триместре <a href=https://iron-deficiency.ru/>https://iron-deficiency.ru/</a>
[url=https://aviator-game-online.website/en]aviator online[/url]
The first thing you need to know. Fonbet promo codes are coded access through which bonuses become available to players. Visually, a bonus code is a combination or combination of symbols, which is the very same access code to some advantage <a href="https://berforum.ru/rota/pages/?aktualnuy_promokod_fonbet_pri_registracii.html">https://berforum.ru/rota/pages/?aktualnuy_promokod_fonbet_pri_registracii.html</a>
По моему мнению Вы допускаете ошибку. Давайте обсудим. Пишите мне в PM, пообщаемся.
Турніри проводяться 3-4 рази на [url=https://mosttbetfax1.xyz/]бк мостбет[/url] місяць. Гра в интернет рулетку или карты на гроші - мета будь-якого клієнта який хоче відпочити і заробити.
Бесподобная тема, мне очень нравится :)
на нашем сайте имеются безвозмездные слоты, рулетка, блэкджек, баккара, кости, бинго, кено, скретч-карты, [url=https://mosttbeet036.xyz/]https://mosttbeet036.xyz/[/url] виртуальный покер и иные виды игрушек.
Play your favorite games on [url=https://kiss918-3.com]kiss918[/url], the ultimate destination for slots, table games, and big jackpots.
https://gosnomerok24.ru/
<a href=https://fortis-torkret.ru/>усиление бетона</a>
[url=https://champaignilrealtor.com/real-estate-agent/]Assessing property investing hazards[/url]
[url=http://www.refresh-therapy.com/]Broker Perspectives: The Key to Quick residential Selling[/url] 8f422d3
Discover the elegance of [url=https://sobha-siniya-islands.ae/]Sobha Siniya Island[/url], a luxurious destination in Umm Al Quwain offering world-class living surrounded by breathtaking natural beauty.
Enfrente adversarios epicos e conquiste a gloria na Arena dos Campeoes <a href="https://lusa-gaming.pt/arena-dos-campeoes/">https://lusa-gaming.pt/</a>
Прошу прощения, что вмешался... Мне знакома эта ситуация. Можно обсудить.
потому, что казино Леонбет является оффшорной компанией, то создание счета, дабы делать ставки, [url=https://melbet-jh8.xyz/]https://melbet-jh8.xyz/[/url] занимает лишь 5 минут.
лунный камень купить <a href=https://moonlystone.ru/>https://moonlystone.ru/</a>
<a href=https://koreaautonews.com/>자율주행 트럭</a>
https://www.goodreads.com/user/show/184229415-findytripcom
Usa pharmacy online viagra <a href="http://onlinepharmacywithoutaprescription.online/">non prescription india pharmacy</a> Canadian online pharmacies Misoprostol <a href="http://canadianpharmdirectwithoutaprescription.com/">canadian pharmacy online no script</a> Tinidazole
[url=https://obeduzhin.ru/2024/10/10/%d0%b2%d0%b8%d1%88%d0%bd%d0%b5%d0%b2%d1%8b%d0%b9-%d0%bf%d0%b8%d1%80%d0%be%d0%b3-%d1%80%d0%b5%d1%86%d0%b5%d0%bf%d1%82-%d1%81-%d1%84%d0%be%d1%82%d0%be/]Вишневый пирог рецепт с фото[/url]
Ежедневные актуальные новости уходящего дня. Мы говорим о медицине, автопроме, обществе, науке и многом ином <a href=https://sp-piter.ru/>https://sp-piter.ru/</a>
Весьма ценная штука
панель управления Свит Бонанза находится в нижней части (под главным экраном с [url=https://kagro.kz/]sweet bonanza[/url] леденцами).
Варианты членства: 98 «зеленых» в год или 13 usd в 30 дней. doordash стал ведущим приложением для доставки продуктов, особенно известным в калифорнии, [url=http://mahjong0.com/visit-soon-and-discover-quality-with-the-products-of-sarms-uk-promoted-by-imuscle-sarms-uk/]http://mahjong0.com/visit-soon-and-discover-quality-with-the-products-of-sarms-uk-promoted-by-imuscle-sarms-uk/[/url] Сан-Франциско и Нью-Йорке в сша.
Я считаю, что Вы не правы. Давайте обсудим это. Пишите мне в PM, пообщаемся.
Организаторам масштабных мероприятий. свадьбы и годовщины, корпоративные встречи, и фестивали требуют множества еды и напитков, [url=http://portalolm.com.br/2021/10/02/ola-mundo/]http://portalolm.com.br/2021/10/02/ola-mundo/[/url] поэтому выездной кейтеринг даст возможность решить эту задачу без малейших хлопот.
<a href="https://hypecasino-wwpf.top">hype casino рабочее зеркало</a>
<a href="https://riobet-kqy.buzz">риобет казино</a>
<a href="https://vk.com/club229712323">Воздушные шарики в Липецке на 23 февраля</a">
Hello !!
I came across a [url=https://raskrutitut.blogspot.com/2025/01/2025.html]100[/url] helpful page that I think you should explore.
This resource is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://ed2empower.com/live-casinos/underage-online-gambling-is-it-really-happening/]https://ed2empower.com/live-casinos/underage-online-gambling-is-it-really-happening/[/url]
Hello everyone!
I came across a [url=https://raskrutitut.blogspot.com/2025/01/2025.html]100[/url] helpful site that I think you should visit.
This platform is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://calisold.com/gambling/casino-management/]https://calisold.com/gambling/casino-management/[/url]
Hello everyone!
I came across a [url=https://raskrutitut.blogspot.com/2025/01/2025.html]100[/url] helpful site that I think you should visit.
This platform is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://calisold.com/gambling/casino-management/]https://calisold.com/gambling/casino-management/[/url]
Hello everyone!
I came across a [url=https://raskrutitut.blogspot.com/2025/01/2025.html]100[/url] helpful site that I think you should visit.
This platform is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://calisold.com/gambling/casino-management/]https://calisold.com/gambling/casino-management/[/url]
Hello everyone!
I came across a [url=https://raskrutitut.blogspot.com/2025/01/2025.html]100[/url] helpful site that I think you should visit.
This platform is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://calisold.com/gambling/casino-management/]https://calisold.com/gambling/casino-management/[/url]
Hello everyone!
I came across a [url=https://raskrutitut.blogspot.com/2025/01/2025.html]100[/url] great site that I think you should explore.
This resource is packed with a lot of useful information that you might find valuable.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://azcaliva.com/bookmakers-tips/betting-on-unfamiliar-sports/]https://azcaliva.com/bookmakers-tips/betting-on-unfamiliar-sports/[/url]
Hello lads!
I came across a [url=https://raskrutitut.blogspot.com/2025/01/2025.html]100[/url] interesting tool that I think you should visit.
This platform is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://naipublishers.com/sportsbooks/the-most-common-types-of-basketball-betting/]https://naipublishers.com/sportsbooks/the-most-common-types-of-basketball-betting/[/url]
Hello lads!
I came across a [url=https://raskrutitut.blogspot.com/2025/01/2025.html]100[/url] interesting tool that I think you should visit.
This platform is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://naipublishers.com/sportsbooks/the-most-common-types-of-basketball-betting/]https://naipublishers.com/sportsbooks/the-most-common-types-of-basketball-betting/[/url]
Hello lads!
I came across a [url=https://raskrutitut.blogspot.com/2025/01/2025.html]100[/url] interesting tool that I think you should visit.
This platform is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://naipublishers.com/sportsbooks/the-most-common-types-of-basketball-betting/]https://naipublishers.com/sportsbooks/the-most-common-types-of-basketball-betting/[/url]
<a href="https://admiralx-pmd.top">Admiral X</a>
<a href="https://1xgames-yhht.xyz">1xgames</a>
Купить права
[Хотите|Желаете|Мечтаете] получить [бесплатный|даровой|халявный] NFT? ?? Участвуйте в [розыгрыше|акции|лотерее] от loveshop "Пушистые льдинки"! ??
Подробнее http://loveshope12.biz/
#loveshop1300-biz # shop1-biz #loveshop13 #loveshop15 #loveshop16 #loveshop17 #loveshop18
<a href=https://sejfy-ofisnye.ru/>сейфы для офиса москва</a>
one way pull it off is to introduce them blindly, without visualization, the [url=https://basketballimmersion.com/the-basketball-podcast-ep37-michael-fly/]https://basketballimmersion.com/the-basketball-podcast-ep37-michael-fly/[/url], which moreover does not take specific knowledge .
класс класс супер!!!!!!!!!!!!!!!!!!!!
Mr. Anthony Fok also becomes the author of several books in the economic field, including the book "[url=https://intracorp.com.sg/]https://intracorp.com.sg[/url]". …
Согласен, очень хорошая штука
известные и наиболее полюбившиеся в мире пляжи и достопримечательности будут прямо [url=https://thailand-company.ru/]thailand-company.ru[/url] рядом с заказчиком.
[Хотите|Желаете|Мечтаете] получить [бесплатный|даровой|халявный] NFT? ?? Участвуйте в [розыгрыше|акции|лотерее] от Mega "M3GA-AT"! ?? Подробнее
https://mega-link.work/vozmozhnosti_hydra_onion/novosti_hydra_zerkalo/
#megaweb3 #megaweb15-at #megaweb8 #megaweb14-at #M3GA-AT #M3GA-GL
Get an accurate estimate of the [url=http://prime-tc.cz/product/people-2/]http://prime-tc.cz/product/people-2/[/url].
https://canvas.instructure.com/eportfolios/3640008/home/animie-v-luchshiem-kachiestvie-boruto-base-vash-lichnyi-oazis-dlia-prosmotra
when you visit Dr. Reifman at his [url=http://elpanzas.es/index.php?option=com_k2&view=item&id=13]http://elpanzas.es/index.php?option=com_k2&view=item&id=13[/url] Clinic in New York, apartment is treated with respect and care.
https://www.storeboard.com/LillieMiah
people choose [url=https://connectkargo.com/blog-details/servio-de-reboque-de-viaturas]https://connectkargo.com/blog-details/servio-de-reboque-de-viaturas[/url] as optimal method to postpone surgery or even generally do without her.
Ваша идея пригодится
Browse our countless sections and make sure yourself why so masses keep returning to watching [url=https://onlyfansfree.cc/11471/queenofmean-aka-realqueenkasey-05-12-2019-onlyfans-video-/]https://onlyfansfree.cc/11471/queenofmean-aka-realqueenkasey-05-12-2019-onlyfans-video-/[/url] on a daily basis.
https://rentry.co/2t6uu4tg
https://www.anobii.com/en/013b0a502af96a052f/profile/activity
https://wakelet.com/wake/S4y6cMVZh_TliZ65Iwjli
Каллы безупречной формы - элегантно!
<a href=https://cvetokispanskie.ru/>заказ цветов томск</a>
http://spencervefz305.wpsuo.com/smotret-anime-onlajn-novye-serii-bez-reklamy
[url=https://chimmed.ru/products/l-norleucine-bioreagent-suita-id=3891401]l norleucine bioreagent, suita - купить онлайн в интернет-магазине химмед [/url]
Tegs: [u]monocrotaline - купить онлайн в интернет-магазине химмед [/u]
[i]monocrotaline - купить онлайн в интернет-магазине химмед [/i]
[b]monocrotaline n oxide - купить онлайн в интернет-магазине химмед [/b]
l norleucine 95% - купить онлайн в интернет-магазине химмед https://chimmed.ru/products/l-norleucine-95-id=4653354
https://www.openlearning.com/u/benjaminsmith-su7fcd/about/
Discover the future of zklend with simple tools, fast actions, and full control at app-zklend.net
<a href="https://app-zklend.net">Try it now on App-zklend.net</a>
For all who are intrigued by the potential of stem cell therapy and wish to explore method of therapy, consider the possibility of applications to the regeneration [url=http://ati-group.ir/%d9%84%d8%a7%d8%b1%d8%a7%d9%88%d9%84-%da%86%db%8c%d8%b3%d8%aa/]http://ati-group.ir/%d9%84%d8%a7%d8%b1%d8%a7%d9%88%d9%84-%da%86%db%8c%d8%b3%d8%aa/[/url] Center in Huntsville, Alabama.
Blinding performance bias and detection bias All outcomes Unclear risk Although trial is described as single blinded, it was unclear who was blinded <a href=https://propecia2buy.top/>proscar no script</a>
может сначала посмотрим
Ocasio-Cortez supports raising the marginal tax rate for individuals with high degree in order to finance implementation of his political goals in sphere repair of [url=https://kleenseeswindows.com/menu-covers]https://kleenseeswindows.com/menu-covers[/url].
Эксклюзивная застройка https://element-pro.com/design/brendovye-obyekty.html
OCTANORM-MAXIMA 36 https://element-pro.com/design/brendovye-obyekty.html
Цена: от 20000 руб https://element-pro.com/design/en-vystavochnye-stendy.html
MWlogistics 2023 https://element-pro.com/proizvodstvo/eksklyuzivnaya-mebel.html
ПЕРФЕКЦИОНИЗМ https://element-pro.com/en-arenda.html
Двухэтажные стенды (BEL)
[url=https://medicinudenrecept.com/koeb-kamagra-jelly-billigt/]https://medicinudenrecept.com/koeb-kamagra-jelly-billigt/[/url] is my passion. He engages in portrait and event photography, but also is engaged in landscape photography, pet photography, merchandise, streets, lifestyle, real estate, sports and travel.
Hello comrades
Hello. A 11 fine website 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://linuxidee.com/live-casino-games/casino-resorts/>https://bmwmacau.com/sportsbooking/key-tools-and-resources-for-better-sports-betting/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
НЕТ СЛОВ
{um/um} {zu spielen/zu kampfen|um} in {Internet|online|wirth|virtuell|online} {casino|Casino|Spielinstitution/Spielhaus} zu spielen/zu kampfen/um} in {online/online/wirth/virtuell/online} {casino/Casino/Spielinstitution/Spielhaus}, #file_links["C:\Users\Admin\Desktop\file\gsa+de+Phoenix5k629URLBB.txt",1,N], {Sie mussen volljahrig sein oder das gesetzlich vorgeschriebene Mindestalter in {Ihrem Heimatland} erreicht haben.
Hello colleagues
Hi. A 11 fantastic website 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://linuxidee.com/live-casino-games/what-is-needed-to-find-a-good-team-of-workers-in-a-casino/>https://risultati-elezioni2014.eu/betting/responsible-and-safe-online-gambling/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A 11 fantastic website 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://linuxidee.com/live-casino-games/what-is-needed-to-find-a-good-team-of-workers-in-a-casino/>https://risultati-elezioni2014.eu/betting/responsible-and-safe-online-gambling/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A 11 fantastic website 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://linuxidee.com/live-casino-games/what-is-needed-to-find-a-good-team-of-workers-in-a-casino/>https://risultati-elezioni2014.eu/betting/responsible-and-safe-online-gambling/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A 11 fantastic website 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://linuxidee.com/live-casino-games/what-is-needed-to-find-a-good-team-of-workers-in-a-casino/>https://risultati-elezioni2014.eu/betting/responsible-and-safe-online-gambling/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hi. A 11 fantastic website 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://linuxidee.com/live-casino-games/what-is-needed-to-find-a-good-team-of-workers-in-a-casino/>https://risultati-elezioni2014.eu/betting/responsible-and-safe-online-gambling/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://blowthedotoutyourass.com/totalizators/placing-bets-using-mobile-apps/>https://ballaratweb.net/bets-on-sports/understanding-the-role-of-odds-in-sports-betting/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://blowthedotoutyourass.com/totalizators/placing-bets-using-mobile-apps/>https://ballaratweb.net/bets-on-sports/understanding-the-role-of-odds-in-sports-betting/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://blowthedotoutyourass.com/totalizators/placing-bets-using-mobile-apps/>https://ballaratweb.net/bets-on-sports/understanding-the-role-of-odds-in-sports-betting/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://blowthedotoutyourass.com/totalizators/placing-bets-using-mobile-apps/>https://ballaratweb.net/bets-on-sports/understanding-the-role-of-odds-in-sports-betting/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
закажите SEO продвижение в Санкт-Петербурге
Выбирайте https://himchistka-spb24.ru - Профессиональная химчистка дивана
Hello !
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://blowthedotoutyourass.com/totalizators/placing-bets-using-mobile-apps/>https://ballaratweb.net/bets-on-sports/understanding-the-role-of-odds-in-sports-betting/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello guys
Good evening. A 11 cool site 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://grssam.com/totalizators/can-bookmaker-refuse-to-pay-you/>https://bmwmacau.com/sportsbooking/nfl-betting-techniques/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello guys
Good evening. A 11 cool site 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://grssam.com/totalizators/can-bookmaker-refuse-to-pay-you/>https://bmwmacau.com/sportsbooking/nfl-betting-techniques/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
[url=http://pegaso2.biz/public/pegaso2/asp/dblog/fotografia.asp?fotografia=1]http://pegaso2.biz/public/pegaso2/asp/dblog/fotografia.asp?fotografia=1[/url] is my passion. He engages in portrait and event photography, and is engaged in landscape photography, pet photography, merchandise, streets, lifestyle, real estate, sports and travel.
Hello men
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://phpnukerz.org/bookmaker-tips/a-beginners-guide-to-reading-and-interpreting-sports-betting-lines/>https://ecoverartist.com/casino-tricks/real-casinos-vs-online-casinos-which-is-best/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://phpnukerz.org/bookmaker-tips/a-beginners-guide-to-reading-and-interpreting-sports-betting-lines/>https://ecoverartist.com/casino-tricks/real-casinos-vs-online-casinos-which-is-best/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://phpnukerz.org/bookmaker-tips/a-beginners-guide-to-reading-and-interpreting-sports-betting-lines/>https://ecoverartist.com/casino-tricks/real-casinos-vs-online-casinos-which-is-best/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://phpnukerz.org/bookmaker-tips/a-beginners-guide-to-reading-and-interpreting-sports-betting-lines/>https://ecoverartist.com/casino-tricks/real-casinos-vs-online-casinos-which-is-best/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Good evening. A 11 great site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://phpnukerz.org/bookmaker-tips/a-beginners-guide-to-reading-and-interpreting-sports-betting-lines/>https://ecoverartist.com/casino-tricks/real-casinos-vs-online-casinos-which-is-best/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Good evening. A 11 cool website 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://bmwmacau.com/sportsbooking/the-positive-benefits-of-betting/>https://jeromedl.org/live-casinos/amazing-gambling-stories/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Good evening. A 11 cool website 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://bmwmacau.com/sportsbooking/the-positive-benefits-of-betting/>https://jeromedl.org/live-casinos/amazing-gambling-stories/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Good evening. A 11 cool website 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://bmwmacau.com/sportsbooking/the-positive-benefits-of-betting/>https://jeromedl.org/live-casinos/amazing-gambling-stories/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hello. A 11 fantastic site 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://urfbownd.net/casino-rules/online-baccarat-basics/>https://ballaratweb.net/virtual-casino/gambling-on-mobile-devices-the-benefits-and-risks-of-online-gambling/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Good evening. A 11 cool website 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://bmwmacau.com/sportsbooking/the-positive-benefits-of-betting/>https://jeromedl.org/live-casinos/amazing-gambling-stories/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hello. A 11 fantastic site 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://urfbownd.net/casino-rules/online-baccarat-basics/>https://ballaratweb.net/virtual-casino/gambling-on-mobile-devices-the-benefits-and-risks-of-online-gambling/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
<a href=https://fastpriligy.top/>generic priligy online</a> The lipid analyses in these patients were in support of the changes in lipid profile as evaluated by nuclear magnetic resonance spectroscopy
Идеи оформления окон шторой в загородном доме
шторы в загородном доме [url=https://zagorodshtory.ru/]шторы в загородном доме[/url] .+7 (499) 460-69-87
Заказ штор по индивидуальным меркам
пошив штор на заказ [url=https://shtory-na-zakaz-moscow.ru/]пошив штор на заказ[/url] .
Она специализируется на продаже и приобретении жилья на вторичном и первичном рынках, [url=http://pnevmokzn.80lvl.ru/viewtopic.php?f=8&t=2729&p=4009#p4009]http://pnevmokzn.80lvl.ru/viewtopic.php?f=8&t=2729&p=4009#p4009[/url] а также предлагает услуги аренды недвижимости.
Наведение порядка в СПб! Перестаньте паниковать, доверьтесь профессионалам! Сделайте шаг к чистоте уже сегодня Кликайте https://uslugi-cleaninga.ru - Стоимость клининговых услуг
Стильные шторы на заказ — дизайн по вашему желанию
шторы на заказ [url=https://shtory-moscow-zakaz.ru/]шторы на заказ[/url] . +7 (499) 460-69-87
Hello team!
I came across a 103 valuable resource that I think you should browse.
This resource is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://die-rheinlaender.de/blackjack-leitfaden/doyle-brunsons-unsterbliche-poker-karriere/]https://die-rheinlaender.de/blackjack-leitfaden/doyle-brunsons-unsterbliche-poker-karriere/[/url]
Hello folks!
I came across a 103 interesting platform that I think you should check out.
This site is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://podcastphone.de/casino-tricks/vanessa-selbst-die-poker-konigin-die-die-mannerwelt-eroberte/]https://podcastphone.de/casino-tricks/vanessa-selbst-die-poker-konigin-die-die-mannerwelt-eroberte/[/url]
Hello folks!
I came across a 103 interesting platform that I think you should check out.
This site is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
[url=https://podcastphone.de/casino-tricks/vanessa-selbst-die-poker-konigin-die-die-mannerwelt-eroberte/]https://podcastphone.de/casino-tricks/vanessa-selbst-die-poker-konigin-die-die-mannerwelt-eroberte/[/url]
<a href="https://t.me/alexshar48">Воздушные шарики Липецк с бесплатной доставкой</a">
Old school never looked this fresh. Hit <a href="https://nakedolderwoman.com/granny-loves-ass-fucked-xxx-images/">Granny Loves Ass Fucked Pics</a> for grown‑up bare pics dripping sexy. Our triple‑X vault stay complimentary and unfiltered, guaranteed to make you quake.
Абсолютно с Вами согласен. Мне нравится Ваша идея. Предлагаю вынести на общее обсуждение.
это отнимает [url=https://telegra.ph/Implantaciya-obeih-chelyustej-s-ispolzovaniem-metodiki-ZAGA-04-08]https://telegra.ph/Implantaciya-obeih-chelyustej-s-ispolzovaniem-metodiki-ZAGA-04-08[/url] до четырнадцати процентов дней. Если была выбрана двухэтапная имплантация, десна над штифтом зашивается. Отсутствие нескольких зубов в списке.
The use of stem cell transplantation in autism helps to modulate immune responses by inducing anti-inflammatory processes and reduction of [url=https://stemcellcarepricing.com/]https://stemcellcarepricing.com/[/url].
<a href=https://novosti-svo-na-ukraine.ru/>новости боевых действий на украине сегодня</a>
Уборка в Санкт-Петербурге! Избавьтесь от забот, доверьтесь профессионалам! Сделайте шаг к чистоте уже сегодня Жмите https://uborka-spb24top.ru - Срочная уборка квартир
Наведение порядка в СПб! Забудьте о хлопотах, доверьтесь профессионалам! Сделайте шаг к чистоте уже сегодня Выбирайте https://uborka-spb24top.ru/
Очень любопытно :)
momentary approach to the full text of the [url=https://stemcellclinicsgermany.com/]https://stemcellclinicsgermany.com[/url] article in encoding. 2018). Phase 1 clinical trial of a patch of retinal pigment epithelium obtained from embryonic stem cells in age-related macular degeneration.
Инновационные деревянные горизонтальные жалюзи
Деревянные горизонтальные жалюзи с электроприводом [url=https://derevo-gorizont-motor.ru/]Деревянные горизонтальные жалюзи с электроприводом[/url] . Prokarniz
On <a href="https://grannynaked.com/older-women-showing-their-breasts-xxx-gallery/">older women showing their breasts nude pics</a> we've got older babes with droopy jugs, wide-open honeypots, and no limits. These naked grown up stars take on fit dudes and crave every second. It's uncensored and totally free.
Мягкая мебель утратила былй лоск? Воскрешение мягкой мебели на дому в СПб! Подарим вторую жизнь диванам, креслам и пушистым коврам их истинную красоту. Экспертные средства и знающие свое дело мастера. Бонусы новобранцам! Детали ждут вас! Тапайте <a href=https://himchistka-divanov-spb24.ru>Химчистка ковролина</a>
<a href="https://vk.com/club229712323">Гелиевые шары на 8 марта</a">
<a href=https://cryptograb.io/>https://cryptograb.io/</a>
Я считаю, что Вы не правы. Я уверен. Могу отстоять свою позицию. Пишите мне в PM, поговорим.
The virtual furniture arrangement is based on the dimensions of the room, realistic 3d furniture, decor, [url=https://asteroidsathome.net/boinc/view_profile.php?userid=773254]https://asteroidsathome.net/boinc/view_profile.php?userid=773254[/url], paint colors and fixtures applied to snapshots of real estate.
макет металлического значка <a href=https://metallicheskie-znachki-zakaz.ru/>изготовление металлических значков</a>
excellent excellent option to consider is payper inc casino, the [url=https://riverbelle.ca/no-deposit-bonus/]River Belle willkommensbonus[/url], which gives solid and effective method payment for players who desire for flexibility and security of confidential transactions.
<a href="https://avtovikup-lipetsk.ru">Продать Машину По Наследству Без Оформления</a>
Истории успеха: дети, полюбившие куклы бебета.
Детски кукли бебета [url=http://www.kukli-bebeta.com]http://www.kukli-bebeta.com[/url] .
Обзор тактильных антистресс игрушек.
Антистрес играчки за деца [url=http://www.antistres-igrachki.com/]http://www.antistres-igrachki.com/[/url] .
Кредитный потребительский кооператив <a href=https://юк-кпк.рф/>https://юк-кпк.рф</a> разумный выбор для тех, кто ценит стабильность. Выдача займов, приём сбережений, поддержка пайщиков. Всё по закону, без скрытых комиссий и с личным вниманием к каждому участнику.
Ритуальні послуги надаються в містах: Буча, Ірпінь, Ворзель, Немішаєве, Бородянка, [url=https://ua.blackrose.com.ua/krematsija-v-kieve]https://ua.blackrose.com.ua/krematsija-v-kieve[/url] Малина. забезпечуємо повний спектр ритуальних послуг – від економ до vip (ексклюзивні похорони).
Выбирайте жалюзи с пультом — уют и стиль в одном
жалюзи с пультом [url=https://pult-zhaluzi.ru/]жалюзи с пультом[/url] . Прокарниз
Заходите <a href=https://uslugi-uborki-spb24.ru>Клининговая компания уборка офисаСПб клининг после ремонта</a>
Клининг в Питере! Чистота в апартаментах, офисов, свежесть в коттеджах. Профессионально, в срок, качественно! Свободное время - ваш бонус! Заходите https://uborka-spb24top.ru - Сколько стоит клининг квартиры
Элегантные жалюзи с пультом для вашего дизайнерского решения
жалюзи с пультом [url=https://pult-zhaluzi.ru/]жалюзи с пультом[/url] . прокарниз
Автоматизация ваших штор и ворот от Somfy
Автоматика Somfy [url=https://somfy-avtomatika.ru/]Автоматика Somfy[/url] . Prokarniz
Спасение диванов в Москве! Вернем к жизни вашему дивану былую красоту! Избавим от пятен и запахов. Профессионально и с заботой! Записывайтесь! Переходите https://himchistka-divanov-msk24.ru - Химчистка мягкой мебели с выездом
Шторы для коттеджа: советы дизайнеров
шторы для коттеджа [url=https://kottedzh-shtory.ru/]шторы для коттеджа[/url] .
В этом что-то есть. Благодарю за информацию. Я не знал этого.
[url=https://oeclub.org/index.php/The_Inexpensive_Option_Of_Car_Delivery]https://oeclub.org/index.php/The_Inexpensive_Option_Of_Car_Delivery[/url], led by an innovative management group, has created a highly motivated team of qualified and dedicated enterprise representatives of service, that will serve you individually.
календарь для печати а4 <a href=https://pechat-plakatov-spb.ru/>печать календарей плакатов</a>
Качественные шторы, сделанные на заказ
сшить шторы на заказ [url=https://zakaz-shtor-msk.ru/]сшить шторы на заказ[/url] . "Ткацкий"
Займы под материнский капитал <a href=https://юсфц.рф/>https://юсфц.рф</a> быстрое решение для покупки квартиры, дома или участка. Без личных вложений, с полным юридическим сопровождением. Оформление за 1 день, надёжные сделки и опыт более 10 лет. Используйте господдержку с умом!
Займы под материнский капитал <a href=https://юсфц.рф/>https://юсфц.рф</a> быстрое решение для покупки квартиры, дома или участка. Без личных вложений, с полным юридическим сопровождением. Оформление за 1 день, надёжные сделки и опыт более 10 лет. Используйте господдержку с умом!
По моему мнению Вы допускаете ошибку. Могу это доказать. Пишите мне в PM, пообщаемся.
We in addition guarantee that current partners have relevant licenses allowing them to offer their casino games interested in [url=https://blogfreely.net/kerrydo/royal-reels-is-an-online-casino-that-offers-a-wide-range-of-games-including]https://blogfreely.net/kerrydo/royal-reels-is-an-online-casino-that-offers-a-wide-range-of-games-including[/url] in Ireland.
Современные сувениры <a href=https://66.ru/news/stuff/278214/>https://66.ru/news/stuff/278214/</a> всё чаще становятся не просто подарками, а настоящими элементами бренда или корпоративной культуры. Особенно интересны примеры, когда обычные предметы превращаются в креативные и запоминающиеся изделия. Такие подходы вдохновляют на создание уникальной продукции с индивидуальным стилем и глубоким смыслом. Именно за этим всё чаще обращаются заказчики, которым важна не массовость, а оригинальность.
Современные сувениры <a href=https://66.ru/news/stuff/278214/>https://66.ru/news/stuff/278214/</a> всё чаще становятся не просто подарками, а настоящими элементами бренда или корпоративной культуры. Особенно интересны примеры, когда обычные предметы превращаются в креативные и запоминающиеся изделия. Такие подходы вдохновляют на создание уникальной продукции с индивидуальным стилем и глубоким смыслом. Именно за этим всё чаще обращаются заказчики, которым важна не массовость, а оригинальность.
попадаются очень даже веселенькие
Warn them that using the services the world they [url=https://windirectprimarycare.com/2025/04/30/the-consequences-of-the-onlyfans-leak-in-the-adult/]https://windirectprimarycare.com/2025/04/30/the-consequences-of-the-onlyfans-leak-in-the-adult/[/url] see onlyfans ads and what to do, if they will encounter this.
Заказные медали <a href=https://iseekmate.com/34740-medali-na-zakaz-nagrada-dlya-chempionov.html>https://iseekmate.com/34740-medali-na-zakaz-nagrada-dlya-chempionov.html</a> применяются для поощрения в спорте, образовании, корпоративной культуре и юбилейных мероприятиях. Производятся из металла, с эмалью, гравировкой или цветной печатью в соответствии с требованиями заказчика.
Продвижение групп ВК <a href=https://vk.com/dizayn_vedenie_prodvizhenie_grup>https://vk.com/dizayn_vedenie_prodvizhenie_grup</a> от оформления и наполнения до запуска рекламы и роста подписчиков. Подходит для бизнеса, мероприятий, брендов и экспертов. Работаем честно и с аналитикой.
Изготавливаем значки <a href=https://znaknazakaz.ru/>https://znaknazakaz.ru</a> на заказ в Москве: классические, сувенирные, корпоративные, с логотипом и индивидуальным дизайном. Металл, эмаль, цветная печать. Быстрое производство, разные тиражи, удобная доставка по городу.
Металлические значки <a href=https://techserver.ru/izgotovlenie-znachkov-iz-metalla-kak-zakazat-unikalnye-izdeliya-dlya-vashego-brenda/>https://techserver.ru/izgotovlenie-znachkov-iz-metalla-kak-zakazat-unikalnye-izdeliya-dlya-vashego-brenda/</a> это стильный и долговечный способ подчеркнуть фирменный стиль, создать корпоративную айдентику или просто сделать приятный сувенир. Всё больше компаний выбирают индивидуальное изготовление значков, чтобы выделиться среди конкурентов.
Изготавливаем значки <a href=https://znaknazakaz.ru/>https://znaknazakaz.ru</a> на заказ в Москве: классические, сувенирные, корпоративные, с логотипом и индивидуальным дизайном. Металл, эмаль, цветная печать. Быстрое производство, разные тиражи, удобная доставка по городу.
курсач купить цена <a href=https://kursoviehelp.ru/>купить курсовую сайт</a>
Металлические значки <a href=https://techserver.ru/izgotovlenie-znachkov-iz-metalla-kak-zakazat-unikalnye-izdeliya-dlya-vashego-brenda/>https://techserver.ru/izgotovlenie-znachkov-iz-metalla-kak-zakazat-unikalnye-izdeliya-dlya-vashego-brenda/</a> это стильный и долговечный способ подчеркнуть фирменный стиль, создать корпоративную айдентику или просто сделать приятный сувенир. Всё больше компаний выбирают индивидуальное изготовление значков, чтобы выделиться среди конкурентов.
Quer comprar seguidores para <a href=https://comprarseguidores.io/>https://comprarseguidores.io</a> o Instagram? Escolha o pacote que mais combina com voce: ao vivo, oferta ou misto. Adequado para blogueiros, lojas e marcas. Seguro, rapido e mantem a reputacao da sua conta.
Quer comprar seguidores para <a href=https://comprarseguidores.io/>https://comprarseguidores.io</a> o Instagram? Escolha o pacote que mais combina com voce: ao vivo, oferta ou misto. Adequado para blogueiros, lojas e marcas. Seguro, rapido e mantem a reputacao da sua conta.
Изготовление значков <a href=https://3news.ru/izgotovlenie-znachkov-na-zakaz-pochemu-eto-vygodno-i-kak-vybrat-idealnyj-variant/>https://3news.ru/izgotovlenie-znachkov-na-zakaz-pochemu-eto-vygodno-i-kak-vybrat-idealnyj-variant/</a> на заказ любой сложности. Работаем по вашему дизайну или поможем создать макет. Предлагаем разные материалы, формы и типы креплений. Оперативное производство и доставка по всей России.
Значки с логотипом компании <a href=https://press-release.ru/branches/markets/znachki-s-vashim-logotipom-iskusstvo-metalla-voploshchennoe-v-unikalnyh-izdeliyah/>https://press-release.ru/branches/markets/znachki-s-vashim-logotipom-iskusstvo-metalla-voploshchennoe-v-unikalnyh-izdeliyah/</a> это не просто элемент фирменного стиля, а настоящее искусство, воплощённое в металле. Они подчёркивают статус бренда и помогают сформировать узнаваемый образ.
Изготовим значки с логотипом <a href=http://classical-news.ru/tehnologiya-izgotovleniya-znachkov-s-logotipom/>http://classical-news.ru/tehnologiya-izgotovleniya-znachkov-s-logotipom/</a> вашей компании. Металлические, пластиковые, с эмалью или цветной печатью. Подчеркните фирменный стиль на выставках, акциях и корпоративных мероприятиях. Качественно, от 10 штук, с доставкой.
Изготовление значков <a href=https://3news.ru/izgotovlenie-znachkov-na-zakaz-pochemu-eto-vygodno-i-kak-vybrat-idealnyj-variant/>https://3news.ru/izgotovlenie-znachkov-na-zakaz-pochemu-eto-vygodno-i-kak-vybrat-idealnyj-variant/</a> на заказ любой сложности. Работаем по вашему дизайну или поможем создать макет. Предлагаем разные материалы, формы и типы креплений. Оперативное производство и доставка по всей России.
Изготовим значки с логотипом <a href=http://classical-news.ru/tehnologiya-izgotovleniya-znachkov-s-logotipom/>http://classical-news.ru/tehnologiya-izgotovleniya-znachkov-s-logotipom/</a> вашей компании. Металлические, пластиковые, с эмалью или цветной печатью. Подчеркните фирменный стиль на выставках, акциях и корпоративных мероприятиях. Качественно, от 10 штук, с доставкой.
Значки с логотипом компании <a href=https://press-release.ru/branches/markets/znachki-s-vashim-logotipom-iskusstvo-metalla-voploshchennoe-v-unikalnyh-izdeliyah/>https://press-release.ru/branches/markets/znachki-s-vashim-logotipom-iskusstvo-metalla-voploshchennoe-v-unikalnyh-izdeliyah/</a> это не просто элемент фирменного стиля, а настоящее искусство, воплощённое в металле. Они подчёркивают статус бренда и помогают сформировать узнаваемый образ.
Юридическое сопровождение <a href=https://urwork.ru/uslugi/bankrotstvo-fizicheskih-licz-yuridicheskie-uslugi/>банкротство физических лиц цена услуги</a>: от анализа документов до полного списания долгов. Работаем официально, по закону №?127-ФЗ. Возможна рассрочка оплаты услуг.
Get a massive 200% bonus on your first deposit and boost your starting balance up to $ 200. <a href=https://bet-promo-codes.com/sportsbook-reviews/betwinner-registration/ >how to register betwinner</a>, Betwinner splits your bonus between sports and games to double your chances of winning.
Юридическое сопровождение <a href=https://urwork.ru/uslugi/bankrotstvo-fizicheskih-licz-yuridicheskie-uslugi/>банкротство физических лиц услуги под ключ</a>: от анализа документов до полного списания долгов. Работаем официально, по закону №?127-ФЗ. Возможна рассрочка оплаты услуг.
Закажите металлические значки <a href=https://metal-archive.ru/novosti/40507-metallicheskie-znachki-na-zakaz-v-moskve-masterstvo-kachestvo-i-individualnyy-podhod.html>https://metal-archive.ru/novosti/40507-metallicheskie-znachki-na-zakaz-v-moskve-masterstvo-kachestvo-i-individualnyy-podhod.html</a> с индивидуальным оформлением. Материалы: латунь, сталь, алюминий. Эмаль, гравировка, печать. Подходит для корпоративных мероприятий, сувениров, символики и наград.
Jacuzzi, sauna, hammam <a href=https://spaplanet.net/>https://spaplanet.net/</a> turnkey - full cycle: from design and selection of equipment to finishing and commissioning. We work with any premises. Reliable, aesthetically pleasing and with a guarantee.
Металлические нагрудные значки <a href=https://str-steel.ru/metallicheskie-nagrudnye-znachki.html>https://str-steel.ru/metallicheskie-nagrudnye-znachki.html</a> стильный и долговечный аксессуар для сотрудников, мероприятий и награждений. Изготавливаем под заказ: с логотипом, гравировкой или эмалью. Разные формы, крепления и варианты отделки.
Металлические нагрудные значки <a href=https://str-steel.ru/metallicheskie-nagrudnye-znachki.html>https://str-steel.ru/metallicheskie-nagrudnye-znachki.html</a> стильный и долговечный аксессуар для сотрудников, мероприятий и награждений. Изготавливаем под заказ: с логотипом, гравировкой или эмалью. Разные формы, крепления и варианты отделки.
Корпоративные значки <a href=https://electrikexpert.ru/korporativnye-znachki-kak-malenkie-detali-sozdayut-bolshuyu-kulturu/>https://electrikexpert.ru/korporativnye-znachki-kak-malenkie-detali-sozdayut-bolshuyu-kulturu/ это не только стиль, но и имидж. Отличный вариант для персонала, деловых встреч, награждений и брендированных подарков. Предлагаем разные материалы, формы и способы нанесения.
Корпоративные значки <a href=https://electrikexpert.ru/korporativnye-znachki-kak-malenkie-detali-sozdayut-bolshuyu-kulturu/>https://electrikexpert.ru/korporativnye-znachki-kak-malenkie-detali-sozdayut-bolshuyu-kulturu/ это не только стиль, но и имидж. Отличный вариант для персонала, деловых встреч, награждений и брендированных подарков. Предлагаем разные материалы, формы и способы нанесения.
Выбирайте <a href=https://himchistka-divanov-msk24.ru>Химчистка ковролин</a>
Рейтинг лучших сервисов <a href=https://vc.ru/telegram/1926953-nakrutka-podpischikov-v-telegram>https://vc.ru/telegram/1926953-nakrutka-podpischikov-v-telegram</a> для накрутки Telegram-подписчиков: функциональность, качество, цены и скорость выполнения. Подходит для продвижения каналов любого масштаба — от старта до монетизации.
Рейтинг лучших сервисов <a href=https://vc.ru/telegram/1926953-nakrutka-podpischikov-v-telegram>https://vc.ru/telegram/1926953-nakrutka-podpischikov-v-telegram</a> для накрутки Telegram-подписчиков: функциональность, качество, цены и скорость выполнения. Подходит для продвижения каналов любого масштаба — от старта до монетизации.
Предлагаем спа-комплексы <a href=https://spaplanet.net/ru/>https://spaplanet.net/ru/</a> от производителя: проектирование, изготовление и монтаж. Индивидуальные решения для бизнеса и дома. Комплексное оснащение — от хаммама до бассейна и зоны отдыха.
курсовые купить <a href=https://kursoviehelp.ru/>kursoviehelp.ru/</a>
Современный и удобный сайт <a href=https://isaloniworldwide.ru/>isaloniworldwide.ru</a> на котором легко найти нужную информацию, товары или услуги. Простая навигация, понятный интерфейс и актуальное содержание подойдут как для новых пользователей, так и для постоянной аудитории. Работает быстро, доступен круглосуточно.
Современный и удобный сайт <a href=https://school-inform.ru/>school-inform.ru</a> на котором легко найти нужную информацию, товары или услуги. Простая навигация, понятный интерфейс и актуальное содержание подойдут как для новых пользователей, так и для постоянной аудитории. Работает быстро, доступен круглосуточно.
Двигайтесь к <a href=https://himchistka-divanov-spb24.ru>Чистка мягкой мебели на дому</a>
cloud server <a href=https://cloud-server1.com/>cloud server us</a>
Обзор цен на мостовидные несъемные зубные протезы.
Мостовидный протез на передние зубы [url=https://belfamilydent.ru/services/mostovidnoe-protezirovanie/]Мостовидный протез на передние зубы[/url] .
Выбирайте <a href=https://himchistka-msk24.ru>Дивана химчистка цена</a>
Car service <a href=https://autocars-ht.com/engine-life-why-it-matters/>brake pad replacement cost</a> services We provide car repair services: from quick diagnostics to major restoration. Quality guarantee, experienced specialists, clear deadlines and original spare parts. We work with private and corporate clients.
Car service <a href=https://www.thecarblogger.net/when-your-car-makes-a-sound-how-do-you-know-whether-to-sound-the-alarm/>squeaking noise while driving</a> services We provide car repair services: from quick diagnostics to major restoration. Quality guarantee, experienced specialists, clear deadlines and original spare parts. We work with private and corporate clients.
buy cocaine <a href=https://tronsave.io/>play casino for money</a>
buy cocaine drugs <a href=https://tronsave.io/>play casino for money</a>
buy cocaine in stavropol <a href=https://itrx.io/en/>porn jerked off</a>
darknet forum <a href=https://tronpulse.io/>cocaine prices on the radio</a>
watching free porn <a href=https://tronpulse.io/>darknet official</a>
42d8aa9
[url=https://gotwebsite1.com/local-seo-phoenix/]Nearby SEO techniques for restaurants[/url]
Предлагаем качественные <a href=https://kss.plus/shop/fasadnye-materialy/klinkernaya-plitka/>клинкерная плитка цена</a> — ступени и плитка для наружных и внутренних работ. Устойчив к износу, влаге и морозу. Подходит для лестниц, крылец, балконов. Консультации и заказ в один шаг.
Обзор современных технологий в установке зубных мостов.
Мостовидный протез на 2 зуба [url=https://koronki-blog.ru/mostovidnoe-protezirovanie]https://koronki-blog.ru/mostovidnoe-protezirovanie[/url] .
Металлические значки на заказ <a href=https://opensvn.ru/izgotovlenie-metallicheskih-znachkov-put-ot-idei-do-nastoyashhego-artefakta/>https://opensvn.ru/izgotovlenie-metallicheskih-znachkov-put-ot-idei-do-nastoyashhego-artefakta/</a> для корпоративных клиентов, школ, выставок и сувенирной продукции. Гравировка, заливка, окрашивание. Поможем с макетом, выполним точно в срок, с доставкой.
Значки из металла <a href=https://rus-week.ru/biznes-idei/metallicheskie-znachki-premialnogo-kachestva-luchshie-resheniya-dlya-brendinga/>https://rus-week.ru/biznes-idei/metallicheskie-znachki-premialnogo-kachestva-luchshie-resheniya-dlya-brendinga/</a> это практичный и презентабельный атрибут для бизнеса, торжеств и наград. Мы производим значки с эмалью, гравировкой, штамповкой. Доступны различные формы, размеры и виды креплений.
Значки из металла <a href=https://rus-week.ru/biznes-idei/metallicheskie-znachki-premialnogo-kachestva-luchshie-resheniya-dlya-brendinga/>https://rus-week.ru/biznes-idei/metallicheskie-znachki-premialnogo-kachestva-luchshie-resheniya-dlya-brendinga/</a> это практичный и презентабельный атрибут для бизнеса, торжеств и наград. Мы производим значки с эмалью, гравировкой, штамповкой. Доступны различные формы, размеры и виды креплений.
Реальные истории успешной имплантации на 4 имплантах.
All on 4 имплантация под ключ цена [url=http://www.belfamilydent.ru/services/implantaciya-allon4/]http://www.belfamilydent.ru/services/implantaciya-allon4/[/url] .
Химическое травление <a href=https://newidey.ru/science/travlenie-metalla-iskusstvo-preobrazheniya-poverhnosti/>https://newidey.ru/science/travlenie-metalla-iskusstvo-preobrazheniya-poverhnosti/</a> это не просто технологический процесс, а настоящее искусство, позволяющее преобразить поверхность металла до неузнаваемости. Этот метод широко используется в производстве сувенирной продукции, включая значки, благодаря точности и эстетике результата.
Лечение в Китае <a href=https://chemodantour.ru/>chemodantour.ru</a> туры в лучшие медицинские центры страны. Традиционная и современная медицина, точная диагностика, восстановление и реабилитация. Сопровождение на всех этапах поездки.
Лечение в Китае <a href=https://chemodantour.ru/>стоматология в китае</a> туры в лучшие медицинские центры страны. Традиционная и современная медицина, точная диагностика, восстановление и реабилитация. Сопровождение на всех этапах поездки.
Между нами говоря, советую Вам попробовать поискать в google.com
чуть ли не центральных преимуществ является конфиденциальность. но учтите, [url=https://onlinenews.eu.com/virtualnyj-nomer-telefona-kazahstana-7-polza-i-osobennosti.html]https://onlinenews.eu.com/virtualnyj-nomer-telefona-kazahstana-7-polza-i-osobennosti.html[/url] что многие сервисы предлагают возможность запоминающихся комбинаций цифр за дополнительную плату.
курсовая работа онлайн <a href=http://kursoviehelp.ru/>заказ контрольных курсовых</a>
курсовик цена <a href=http://kursoviehelp.ru/>курсовые быстро и недорого</a>
Блеск и порядок в бизнесе в СПб! Сверкающий офис - успех в делах! Экспертный клининг. Привлекательные цены. Звоните! Жмите https://uborka-ofisov24spb.ru
<a href="https://vavada-wwrt.buzz">vavada рабочее зеркало</a>
<a href="https://daddycasino-lthy.buzz">daddy casino</a>
O site oficial 1win bet <a href=https://1winbr.com.br/>http://1winbr.com.br</a> e apostar em desporto, casinos, jogos e torneios. Suporte para diversas moedas, transacoes rapidas, promocoes e cashback. Jogue confortavelmente no seu PC ou atraves da aplicacao.
O site oficial 1win bet <a href=https://1winbr.com.br/>1winbr.com.br</a> e apostar em desporto, casinos, jogos e torneios. Suporte para diversas moedas, transacoes rapidas, promocoes e cashback. Jogue confortavelmente no seu PC ou atraves da aplicacao.
1xBet promo code <a href=https://paranormalmusings.com/wp-content/pgs/dghinsovye_kurtki_kak_ih_pravilyno_ispolyzovaty_i_chto_budet_modno.html>https://paranormalmusings.com/wp-content/pgs/dghinsovye_kurtki_kak_ih_pravilyno_ispolyzovaty_i_chto_budet_modno.html</a> is an opportunity to get a bonus of up to 100% on your first deposit. Register, enter the code and start betting with additional funds. Fast, simple and profitable.
1xBet promo code <a href=https://ideals.org.ph/wp-content/pgs/za_god_15_mln_bolynyh_rakom_kaghdyy_tretiy_mughchina_v_mire_i_kaghdaya_pyataya_ghenschina.html>https://ideals.org.ph/wp-content/pgs/za_god_15_mln_bolynyh_rakom_kaghdyy_tretiy_mughchina_v_mire_i_kaghdaya_pyataya_ghenschina.html</a> is an opportunity to get a bonus of up to 100% on your first deposit. Register, enter the code and start betting with additional funds. Fast, simple and profitable.
Экскурсии по Красноярску <a href=https://tour-guide8.ru/>https://tour-guide8.ru</a> индивидуальные прогулки и групповые туры. Красивые виды, история города, заповедные места. Гиды с опытом, удобные форматы, гибкий график. Подарите себе незабываемые впечатления!
Экскурсии по Красноярску <a href=https://tour-guide8.ru/>tour-guide8.ru/</a> индивидуальные прогулки и групповые туры. Красивые виды, история города, заповедные места. Гиды с опытом, удобные форматы, гибкий график. Подарите себе незабываемые впечатления!
купить лед экран для рекламы <a href=https://svetodiodnye-ekrany-videosteny.ru/>https://svetodiodnye-ekrany-videosteny.ru/</a>
производство led экранов <a href=https://svetodiodnye-ekrany-videosteny.ru/>http://svetodiodnye-ekrany-videosteny.ru</a>
Нужен номер для ТГ? Предлагаем <a href=https://techalpaka.online/>https://techalpaka.online</a> для одноразовой или постоянной активации. Регистрация аккаунта без SIM-карты, в любом регионе. Удобно, надёжно, без привязки к оператору.
Нужен номер для ТГ? Предлагаем <a href=https://techalpaka.online/>арендовать номер для телеграмма</a> для одноразовой или постоянной активации. Регистрация аккаунта без SIM-карты, в любом регионе. Удобно, надёжно, без привязки к оператору.
Чистый дом - счастливый дом! в СПб и ЛО! Клининг экспертного уровня для вашего благополучия. Поддержим свежесть и порядок. Не откладывайте! Переходите https://uborka-domov24spb.ru - Уборка после ремонта цена СПб
Нажимайте <a href=https://uberu21.ru>Клининг в СПб</a>
заказать реферат недорого <a href=https://referatymarketing.ru/>заказать реферат</a>
Зарегистрировался на форуме, чтобы сказать Вам спасибо за помощь в этом вопросе, может, я тоже могу Вам чем-то помочь?
Аромат предназначается для интересных девушек, но будет мелодично звучать и на зрелых дамах, [url=https://duhiklass.ru/]парфюмерия[/url] ежели в композицию добавить мускус или пряный концентрат.
Финишная прямая чистоты? Забудьте о строительной пыли! Идеальный порядок апартаментов и коттеджей. Оперативно, тщательно, надежно! Перемещайтесь к https://klining-posle-remonta24spb.ru - Клининг заказать
ноутбук днс цены <a href=https://kupit-noutbuk213.ru/>купить ноутбук цена</a>
где купить электронику <a href=https://magazin-elektroniki213.ru/>маркетплейс электроники</a>
купить ноутбук недорого <a href=https://kupit-noutbuk213.ru/>ноутбуки intel цена</a>
купить смартфон note <a href=https://smartfon-v-msk-cena.ru/>купить смартфон цена</a>
где купить электронику <a href=https://magazin-elektroniki213.ru/>магазин электроники техник</a>
цена смартфона самсунг <a href=https://smartfon-v-msk-cena.ru/>купить смартфон цена</a>
электроника магазин купить <a href=https://magazin-elektroniki213.ru/>магазин электроники</a>
магазин бытовой электроники <a href=https://magazin-elektroniki213.ru/>купить электронику</a>
Перемещайтесь к https://uslugi-cleaninga.ru - Генеральная уборка СПб
купить ноутбук асус <a href=https://kupit-noutbuk213.ru/>ноутбук сколько цены</a>
купить ноутбук для работы <a href=https://kupit-noutbuk213.ru/>игровой ноутбук</a>
смартфон redmi купить <a href=https://smartfon-v-msk-cena.ru/>каталог смартфонов с ценами</a>
Оказываем услуги <a href=https://urwork.ru/uslugi/zashhita-prav-potrebitelej-yuridicheskie-uslugi/>юридические услуги по защите прав потребителей</a>: консультации, подготовка претензий и исков, представительство в суде. Поможем вернуть деньги, заменить товар или взыскать компенсацию. Работаем быстро и по закону.
Оказываем услуги <a href=https://urwork.ru/uslugi/zashhita-prav-potrebitelej-yuridicheskie-uslugi/>защита прав потребителя стоимость услуг</a>: консультации, подготовка претензий и исков, представительство в суде. Поможем вернуть деньги, заменить товар или взыскать компенсацию. Работаем быстро и по закону.
Нужен номер для Телеграма? <a href=https://techalpaka.online/>арендовать номер для телеграмма</a> для безопасной регистрации и анонимного использования. Поддержка популярных регионов, удобный интерфейс, моментальный доступ.
Нужен номер для Телеграма? <a href=https://techalpaka.online/>дешевые номера для телеграм</a> для безопасной регистрации и анонимного использования. Поддержка популярных регионов, удобный интерфейс, моментальный доступ.
Перемещайтесь к https://clean-help24.ru
Свежие тенденции <a href=https://www.life-ua.com/>https://www.life-ua.com</a> советы по стилю и обзоры коллекций. Всё о моде, дизайне, одежде и аксессуарах для тех, кто хочет выглядеть современно и уверенно.
Свежие тенденции <a href=https://www.life-ua.com/>https://www.life-ua.com</a> советы по стилю и обзоры коллекций. Всё о моде, дизайне, одежде и аксессуарах для тех, кто хочет выглядеть современно и уверенно.
Любимые карточные игры на <a href=https://pokerbonuses.ru/>покерок</a>. Новички и профессиональные игроки всё чаще выбирают площадку благодаря её стабильности и удобству. Здесь доступны кэш-игры, турниры с большими призовыми и эксклюзивные акции. Интерфейс адаптирован под мобильные устройства, а служба поддержки работает круглосуточно.
Инженерные системы <a href=https://usteplo.ru/>https://usteplo.ru</a> основа комфортного и безопасного пространства. Проектирование, монтаж и обслуживание отопления, водоснабжения, вентиляции, электроснабжения и слаботочных систем для домов и предприятий.
Инженерные системы <a href=https://usteplo.ru/>https://usteplo.ru</a> основа комфортного и безопасного пространства. Проектирование, монтаж и обслуживание отопления, водоснабжения, вентиляции, электроснабжения и слаботочных систем для домов и предприятий.
консультации и онлайн услуги <a href=https://urwork.ru/uslugi/zashhita-prav-potrebitelej-yuridicheskie-uslugi/>юридические услуги по защите прав потребителей</a>: консультации, подготовка претензий и исков, представительство в суде. Поможем вернуть деньги, заменить товар или взыскать компенсацию. Работаем быстро и по закону.
консультации и онлайн услуги <a href=https://urwork.ru/uslugi/zashhita-prav-potrebitelej-yuridicheskie-uslugi/>юрист по защите прав потребителей</a>: консультации, подготовка претензий и исков, представительство в суде. Поможем вернуть деньги, заменить товар или взыскать компенсацию. Работаем быстро и по закону.
Строительный портал <a href=https://stroydelo33.ru/>https://stroydelo33.ru</a> источник актуальной информации для тех, кто строит, ремонтирует или планирует. Полезные советы, обзоры инструментов, этапы работ, расчёты и готовые решения для дома и бизнеса.
Строительный портал <a href=https://stroydelo33.ru/>https://stroydelo33.ru</a> источник актуальной информации для тех, кто строит, ремонтирует или планирует. Полезные советы, обзоры инструментов, этапы работ, расчёты и готовые решения для дома и бизнеса.
Любимые карточные игры на <a href=https://pokerbonuses.ru/>покерок</a>. Новички и профессиональные игроки всё чаще выбирают площадку благодаря её стабильности и удобству. Здесь доступны кэш-игры, турниры с большими призовыми и эксклюзивные акции. Интерфейс адаптирован под мобильные устройства, а служба поддержки работает круглосуточно.
Любимые карточные игры на <a href=https://pokerbonuses.ru/>https://pokerbonuses.ru</a>. Новички и профессиональные игроки всё чаще выбирают площадку благодаря её стабильности и удобству. Здесь доступны кэш-игры, турниры с большими призовыми и эксклюзивные акции. Интерфейс адаптирован под мобильные устройства, а служба поддержки работает круглосуточно.
консультации и онлайн услуги <a href=https://urwork.ru/uslugi/zashhita-prav-potrebitelej-yuridicheskie-uslugi/>консультация юриста по защите прав потребителей</a>: консультации, подготовка претензий и исков, представительство в суде. Поможем вернуть деньги, заменить товар или взыскать компенсацию. Работаем быстро и по закону.
ГГУ имени Ф.Скорины <a href=https://www.gsu.by/>https://www.gsu.by/</a> крупный учебный и научно-исследовательский центр Республики Беларусь. Высшее образование в сфере гуманитарных и естественных наук на 12 факультетах по 35 специальностям первой ступени образования и 22 специальностям второй, 69 специализациям.
ГГУ имени Ф.Скорины <a href=https://www.gsu.by/>https://www.gsu.by/</a> крупный учебный и научно-исследовательский центр Республики Беларусь. Высшее образование в сфере гуманитарных и естественных наук на 12 факультетах по 35 специальностям первой ступени образования и 22 специальностям второй, 69 специализациям.
Francisk Skorina <a href=https://www.gsu.by/>https://www.gsu.by</a> Gomel State University. One of the leading academic and scientific-research centers of the Belarus. There are 12 Faculties at the University, 2 scientific and research institutes. Higher education in 35 specialities of the 1st degree of education and 22 specialities.
Энергосберегающие жалюзи с пультом — экономия и комфорт
жалюзи с пультом [url=https://pult-zhaluzi.ru/]жалюзи с пультом[/url] . Прокарниз
сирень для живых изгородей <a href=https://sajenci.ru/>жимолость от частного сада</a>
розы для ландшафтного дизайна <a href=https://sajenci.ru/>гортензии с доставкой</a>
купить саженцы в сибири <a href=https://vsibiry.ru/>саженцы от частного лица</a>
ежевика для северных регионов <a href=https://vsibiry.ru/>клубника высокого качества</a>
Заходите https://chistka-mebel24spb.ru - Клининг дивана
<a href="https://sparkcasino-el0f.top">спарк казино</a>
<a href="https://melbet-cq.top">melbet ставки</a>
Create vivid images with <a href=https://promptchan.org/>Promptchan</a> — a powerful neural network for generating art based on text description. Support for SFW and NSFW modes, style customization, quick creation of visual content.
Create vivid images with <a href=https://promptchan.org/>Promptchan</a> — a powerful neural network for generating art based on text description. Support for SFW and NSFW modes, style customization, quick creation of visual content.
Недвижимость в Болгарии у моря <a href=https://byalahome.ru/>https://byalahome.ru</a> квартиры, дома, апартаменты в курортных городах. Продажа от застройщиков и собственников. Юридическое сопровождение, помощь в оформлении ВНЖ, консультации по инвестициям.
Недвижимость в Болгарии у моря <a href=https://byalahome.ru/>https://byalahome.ru</a> квартиры, дома, апартаменты в курортных городах. Продажа от застройщиков и собственников. Юридическое сопровождение, помощь в оформлении ВНЖ, консультации по инвестициям.
Срочный выкуп квартир <a href=https://proday-kvarti.ru/>https://proday-kvarti.ru</a> за сутки — решим ваш жилищный или финансовый вопрос быстро. Гарантия законности сделки, юридическое сопровождение, помощь на всех этапах. Оценка — бесплатно, оформление — за наш счёт. Обращайтесь — мы всегда на связи и готовы выкупить квартиру.
Срочный выкуп квартир <a href=https://proday-kvarti.ru/>https://proday-kvarti.ru</a> за сутки — решим ваш жилищный или финансовый вопрос быстро. Гарантия законности сделки, юридическое сопровождение, помощь на всех этапах. Оценка — бесплатно, оформление — за наш счёт. Обращайтесь — мы всегда на связи и готовы выкупить квартиру.
Портал о недвижимости <a href=https://akadem-ekb.ru/>https://akadem-ekb.ru</a> всё, что нужно знать о продаже, покупке и аренде жилья. Актуальные объявления, обзоры новостроек, советы экспертов, юридическая информация, ипотека, инвестиции. Помогаем выбрать квартиру или дом в любом городе.
Новости Черновцы <a href=https://u-misti.chernivtsi.ua/>https://u-misti.chernivtsi.ua</a> городской портал с последними событиями
Портал о недвижимости <a href=https://akadem-ekb.ru/>https://akadem-ekb.ru</a> всё, что нужно знать о продаже, покупке и аренде жилья. Актуальные объявления, обзоры новостроек, советы экспертов, юридическая информация, ипотека, инвестиции. Помогаем выбрать квартиру или дом в любом городе.
Это было и со мной. Можем пообщаться на эту тему. Здесь или в PM.
po zrobiles produkt w panelu naffy, umieszczasz wygenerowany adres sprzedaz w osobistym kanale sprzedazy, tak, w sieci spolecznosciowe, [url=https://dongphucfvn.vn/webinar-definicja-nowoczesne-podejcie-do-szkole/]https://dongphucfvn.vn/webinar-definicja-nowoczesne-podejcie-do-szkole/[/url] gdzie gracze moga robic zakupy online.
Нажимайте https://uslugi-uborki-spb24.ru/
заказать розы <a href=https://flowersspb.com>цветы недорого спб</a>
купить анемоны <a href=https://flowersspb.com>цветочная лавка</a>
купить герберы <a href=https://2gis.ru/spb/firm/70000001081058501>купить цветы дешево</a>
купить розы спб <a href=https://maps.app.goo.gl/C53KSpXrhMXSabAk7>букет цветов заказать с доставкой</a>
сайт цветов <a href=https://zoon.ru/spb/shops/tsvetochnaya_masterskaya_roza_vetrov_na_komendantskom_prospekte>доставка цветов букетов</a>
Выбирайте <a href=https://uborka-kvartir24top.ru>Оказание клининговых услуг</a>
Перемещайтесь к <a href=https://himchistka-spb24speed.ru>Чистка мебели цена</a>
doctor can can provide several rehabilitation programs, include communication and social interaction, [url=https://chancefly74.edublogs.org/2021/05/30/used-auto-parts-craigslist-versus-pick-and-pull-junkyards/]https://chancefly74.edublogs.org/2021/05/30/used-auto-parts-craigslist-versus-pick-and-pull-junkyards/[/url], physiological counseling and further examination.
Ищете копирайтера? <a href=https://sajt-kopirajtera.ru>https://sajt-kopirajtera.ru</a> Пишу тексты, которые продают, вовлекают и объясняют. Создам контент для сайта, блога, рекламы, каталога. Работаю с ТЗ, разбираюсь в SEO, адаптирую стиль под задачу. Чистота, смысл и результат — мои приоритеты. Закажите текст, который работает на вас.
Архитектурные решения <a href=https://топдом-мск.рф/>https://топдом-мск.рф</a> под ваши желания и участок. Создадим проект с нуля: планировка, фасад, инженерия, визуализация. Вы получите эксклюзивный дом, адаптированный под ваш образ жизни. Работаем точно, качественно и с любовью к деталям.
Туристический портал <a href=https://prostokarta.com.ua/>https://prostokarta.com.ua</a> для путешественников: маршруты, достопримечательности, советы, бронирование туров и жилья, билеты, гайды по странам и городам. Планируйте отпуск легко — всё о путешествиях в одном месте.
???? ??? ?? ???? 7 ?,?? ???,???,???,???,??,? ?,???,???,??? ?? ??? [url=http://www.mihagino-bc.com/uni_korobbs/uni_korobbs.cgi]http://www.mihagino-bc.com/uni_korobbs/uni_korobbs.cgi[/url],?? ?????????,???? ?????????.
YouTube Promotion <a href=https://laurasandra.medium.com/9-best-sites-to-buy-youtube-views-real-safe-d51001e5632e>buy views on youtube</a> for your videos and increase reach. Real views from a live audience, quick launch, flexible packages. Ideal for new channels and content promotion. We help develop YouTube safely and effectively.
Натяжные потолки под ключ <a href=https://medium.com/@ksv.viet87/натяжные-потолки-мифы-о-вреде-и-экспертное-мнение-от-nova-28054185c2fd>https://medium.com/@ksv.viet87/натяжные-потолки-мифы-о-вреде-и-экспертное-мнение-от-nova-28054185c2fd</a> установка любых видов: матовые, глянцевые, сатиновые, многоуровневые, с фотопечатью и подсветкой. Широкий выбор фактур и цветов, замер бесплатно, монтаж за 1 день. Качественные материалы, гарантия и выгодные цены от производителя.
Автомобильный портал <a href=https://autodream.com.ua/>https://autodream.com.ua</a> для автолюбителей и профессионалов: новости автоиндустрии, обзоры, тест-драйвы, сравнение моделей, советы по уходу и эксплуатации. Каталог авто, форум, рейтинги, автоновости. Всё об автомобилях — в одном месте, доступно и интересно.
Портал про авто <a href=https://livecage.com.ua/>https://livecage.com.ua</a> всё для автолюбителей: обзоры машин, тест-драйвы, новости автопрома, советы по ремонту и обслуживанию. Выбор авто, сравнение моделей, тюнинг, страховка, ПДД. Актуально, понятно и полезно. Будьте в курсе всего, что связано с автомобилями!
Ты можешь всё <a href=https://love.zt.ua/>https://love.zt.ua</a> а мы подскажем, как. Женский портал о саморазвитии, личной эффективности, карьере, балансе между семьёй и амбициями. Здесь — опыт успешных женщин, практичные советы и реальные инструменты для роста.
Современный женский портал <a href=https://beautyrecipes.kyiv.ua/>https://beautyrecipes.kyiv.ua</a> стиль жизни, мода, уход за собой, семья, дети, кулинария, карьера и вдохновение. Полезные советы, тесты, статьи и истории. Откровенно, интересно, по-настоящему. Всё, что важно и близко каждой женщине — в одном месте.
На женском портале <a href=https://happytime.in.ua/>https://happytime.in.ua</a> статьи для души и тела: секреты красоты, женское здоровье, любовь и семья, рецепты, карьерные идеи, вдохновение. Место, где можно быть собой, делиться опытом и черпать силу в заботе о себе.
Добро пожаловать на женский портал <a href=https://lidia.kr.ua/>https://lidia.kr.ua</a> ваш гид по миру красоты, стиля и внутренней гармонии. Читайте про отношения, карьеру, воспитание детей, женское здоровье, эмоции и моду. Будьте вдохновлены лучшей версией себя каждый день вместе с нами.
заказ металлических значков <a href=https://znachki-zakaz-moskva.ru/>заказ металлических значков</a>
???? ???? ???? ????? ?? ??????? ???? ????? ????? ?? ????? ?????? ??? ????? 1 ????? ?????? ?????? [url=https://menwiki.men/wiki/User:NestorGreenough]https://menwiki.men/wiki/User:NestorGreenough[/url] ??? ????????.
?? ? 21 ? ?? ??????????? ?????. [url=http://brush114.co.kr/bbs/board.php?bo_table=free&wr_id=619178]http://brush114.co.kr/bbs/board.php?bo_table=free&wr_id=619178[/url] ??/?? ? ? ??? ? ???? ????? ??/?? ????/?????/??? ??2025 ?????????????? ?????????? ?? ????.
Раньше я думал иначе, благодарю за помощь в этом вопросе.
I've collected some [url=https://typetype.org/fonts/romanian/]romanian font[/url] for instagram, where it will be interesting excitement, and I use them for employment of your biography.
Женский онлайн-журнал <a href=https://loveliness.kyiv.ua/>https://loveliness.kyiv.ua</a> о стиле, красоте, вдохновении и трендах. Интервью, мода, бьюти-обзоры, психология, любовь и карьера. Будь в курсе главного, читай мнения экспертов, следи за трендами и открывай новые грани себя каждый день.
Портал для женщин <a href=https://oa.rv.ua/>https://oa.rv.ua</a> всё, что важно: красота, здоровье, семья, карьера, мода, отношения, рецепты и саморазвитие. Полезные статьи, советы, тесты и вдохновение каждый день. Онлайн-пространство, где каждая найдёт ответы и поддержку.
Современный женский портал <a href=https://womanonline.kyiv.ua/>https://womanonline.kyiv.ua</a> с актуальными темами: тренды, уход, макияж, фитнес, fashion, интервью, советы стилистов. Следи за модой, вдохновляйся образами, узнай, как подчеркнуть свою индивидуальность.
Сайт для женщин <a href=https://womenclub.kr.ua/>https://womenclub.kr.ua</a> всё, что волнует и вдохновляет: мода, красота, здоровье, отношения, дети, психология и карьера. Практичные советы, интересные статьи, вдохновение каждый день. Онлайн-пространство, созданное с заботой о вас и вашем настроении.
Надёжный медицинский портал <a href=https://una-unso.cv.ua/>https://una-unso.cv.ua</a> созданный для вашего здоровья и спокойствия. Статьи о заболеваниях, советы по лечению и образу жизни, подбор клиник и врачей. Понятный язык, актуальная информация, забота о вашем самочувствии — каждый день.
Чайная энциклопедия <a href=https://etea.com.ua/>https://etea.com.ua</a> всё о мире чая: сорта, происхождение, свойства, способы заваривания, чайные традиции разных стран. Узнайте, как выбрать качественный чай, в чём его польза и как раскрывается вкус в каждой чашке. Для ценителей и новичков.
Кулинарный портал <a href=https://mallinaproject.com.ua/>https://mallinaproject.com.ua</a> тысячи рецептов, пошаговые инструкции, фото, видео, удобный поиск по ингредиентам. Готовьте вкусно и разнообразно: от завтраков до десертов, от традиционной кухни до кулинарных трендов. Быстро, доступно, понятно!
Сайт о здоровье глаз <a href=https://eyecenter.com.ua/>https://eyecenter.com.ua</a> полезные статьи, советы офтальмологов, симптомы заболеваний, диагностика, лечение, упражнения для зрения. Всё о профилактике, коррекции, очках, линзах и современных методах восстановления.
Современный мужской портал <a href=https://smart4business.net/>https://smart4business.net</a> о жизни, успехе и саморазвитии. Личный рост, инвестиции, бизнес, стиль, технологии, мотивация. Разбираем стратегии, делимся опытом, вдохновляем на движение вперёд. Для тех, кто выбирает силу, разум и результат.
Новинки технологий <a href=https://dumka.pl.ua/>https://dumka.pl.ua</a> портал о том, как научные открытия становятся частью повседневности. Искусственный интеллект, нанотехнологии, биоинженерия, 3D-печать, цифровизация. Простым языком о сложном — для тех, кто любит знать, как работает мир.
Все новинки технологий <a href=https://axioma-techno.com.ua/>https://axioma-techno.com.ua</a> в одном месте: презентации, релизы, выставки, обзоры и утечки. Следим за рынком гаджетов, IT, авто, AR/VR, умного дома. Обновляем ежедневно. Не пропустите главные технологические события и открытия.
Заходите https://kliningovaya-uborka-spb.ru
Автомобильный сайт <a href=https://kolesnitsa.com.ua/>https://kolesnitsa.com.ua</a> для души: редкие модели, автофан, необычные тесты, автоистории, подборки и юмор. Лёгкий и увлекательный контент, который приятно читать. Здесь не только про машины — здесь про стиль жизни на колёсах.
Актуальные новости <a href=https://polonina.com.ua/>https://polonina.com.ua</a> каждый день — политика, экономика, культура, спорт, технологии, происшествия. Надёжный источник информации без лишнего. Следите за событиями в России и мире, получайте факты, мнения и обзоры.
Следите за трендами автопрома <a href=https://viewport.com.ua/>https://viewport.com.ua</a> вместе с нами! На авто портале — новинки, презентации, обзоры, технологии, электромобили, автосалоны и экспертные мнения. Ежедневные обновления, честный взгляд на рынок, без лишнего шума и рекламы.
Полезные статьи и советы <a href=https://britishschool.kiev.ua/>https://britishschool.kiev.ua</a> на каждый день: здоровье, финансы, дом, отношения, саморазвитие, технологии и лайфхаки. Читайте, применяйте, делитесь — всё, что помогает жить проще, осознаннее и эффективнее. Достоверная информация и реальная польза.
Сайт для женщин <a href=https://funtura.com.ua/>https://funtura.com.ua</a> всё, что интересно каждый день: бьюти-советы, рецепты, отношения, дети, стиль, покупки, лайфхаки и настроение. Яркие статьи, тесты и вдохновение. Просто, легко, по-женски.
Это не просто сайт для женщин <a href=https://godwood.com.ua/>https://godwood.com.ua</a> это пространство, где вас слышат. Здесь — забота, поддержка, советы по жизни, отношениям, здоровью, семье и внутреннему балансу. Никакой критики, только доброта и уверенность: всё будет хорошо, и вы не одна.
Информационно-познавательный <a href=https://golosiyiv.kiev.ua/>https://golosiyiv.kiev.ua</a> портал для мужчин и женщин: полезные статьи, советы, обзоры, лайфхаки, здоровье, психология, стиль, семья и финансы. Всё, что важно знать для жизни, развития и комфорта. Читайте, развивайтесь, вдохновляйтесь вместе с нами.
Сильная, умная, стильная <a href=https://lugor.org.ua/>https://lugor.org.ua</a> вот для кого наш женский онлайн-журнал. Темы: мода, карьера, дети, отношения, дом, здоровье. Разговор о реальной жизни: без глянца, но со вкусом.
Сайт для женщин <a href=https://expertlaw.com.ua/>https://expertlaw.com.ua</a> которые любят моду, красоту и стильную жизнь. Актуальные тренды, советы по уходу, подбор образов, вдохновляющие идеи для гардероба и макияжа.
Женский онлайн-журнал <a href=https://gorod-lubvi.com.ua/>https://gorod-lubvi.com.ua</a> о красоте, стиле и уходе. Советы визажистов, подбор образов, секреты молодости, модные тренды. Всё, чтобы чувствовать себя уверенно и выглядеть на миллион. Будь в курсе, вдохновляйся и подбирай стиль по душе.
Женский онлайн-журнал <a href=https://inclub.lg.ua/>https://inclub.lg.ua</a> о силе выбора. Карьера, финансы, тайм-менеджмент, уверенность, стиль и баланс. Для женщин, которые двигаются вперёд, строят, влияют, мечтают. Говорим по делу — без стереотипов и с уважением к вашему пути.
Портал для женщин <a href=https://prettiness.kyiv.ua/>https://prettiness.kyiv.ua</a> которые любят жизнь во всех её красках. Советы, мода, рецепты, отношения, вдохновение, дом и путешествия. Каждый день — новая идея, интересная мысль и повод улыбнуться.
Портал для активных <a href=https://onlystyle.com.ua/>https://onlystyle.com.ua</a> стильных, современных женщин. Мода, карьера, здоровье, бьюти-тренды, фитнес, лайфхаки, вдохновение. Будь в курсе, живи ярко, выбирай смело. Никаких скучных статей — только драйв, стиль и реальная польза.
Модный журнал <a href=https://psilocybe-larvae.com/>https://psilocybe-larvae.com</a> всё о стиле, трендах, бьюти-новинках, звёздах и вдохновении. Образы с подиумов, советы стилистов, актуальные коллекции, мода улиц и мировые бренды.
Профессиональный <a href=https://taplink.cc/ivanteevkamassage>массаж Ивантеевка</a>: для спины, шеи, поясницы, при остеохондрозе и сколиозе. Медицинский и спортивный подход, опытные специалисты, точечное воздействие. Снятие болей, восстановление подвижности, улучшение самочувствия.
Онлайн-портал для женщин <a href=https://rpl.net.ua/>https://rpl.net.ua</a> всё о жизни, стиле, здоровье, отношениях, карьере, детях, красоте и вдохновении. Полезные статьи, советы, идеи и актуальные темы.
Женский онлайн-портал <a href=https://sweaterok.com.ua/>https://sweaterok.com.ua</a> это не просто сайт, а поддержка в повседневной жизни. Честные темы, важные вопросы, советы и тепло. От эмоций до материнства, от тела до мыслей.
Онлайн-журнал для женщин <a href=https://tiamo.rv.ua/>https://tiamo.rv.ua</a> которые ищут баланс. Психология, эмоции, отношения, самоценность, женское здоровье. Честные тексты, поддержка, путь к себе. Пространство, где можно дышать глубже, читать с удовольствием и чувствовать, что тебя понимают.
Онлайн фитнес-журнал <a href=https://bahgorsovet.org.ua/>https://bahgorsovet.org.ua</a> полезные статьи от тренеров и нутрициологов: программы тренировок, восстановление, питание, биомеханика, анализ ошибок. Говорим на языке результата. Научный подход без воды — для тех, кто ценит эффективность.
Женский онлайн-журнал <a href=https://trendy.in.ua/>https://trendy.in.ua</a> о выборе, деньгах, успехе и личных целях. Как совмещать карьеру и семью, строить бизнес, говорить "нет" и заботиться о себе. Истории, советы, интервью, вдохновение. Для тех, кто идёт вперёд — в своих темпах и с опорой на себя.
Всё о лечении диабета <a href=https://diabet911.com/>https://diabet911.com</a> типы заболевания, симптомы, диагностика, питание, образ жизни и лекарственная терапия. Объясняем просто и понятно. Актуальная информация, советы врачей, статьи для пациентов и близких.
диплом цена <a href=https://diplomastudy.ru/>заказ дипломной работы</a>
Загрязнения на любимой мебели? Освежим ей прежний вид! Чистка диванов, кресел, пушистых покрытий в столице. Перемещайтесь к <a href=https://himchistka-divanov-msk24.ru>Сухая химчистка мягкой мебели</a>
Мне очень жаль, ничем не могу Вам помочь. Я думаю, Вы найдёте верное решение.
I will show you a step-by-step guide after in similar solflare [url=https://www-solflare.com/]solflare wallet[/url]. the most common type of backup is a standard opening phrase consisting of 12/20 or 24 words, which the trezor team calls an "outdated backup".
Сайт о мужском здоровье <a href=https://kakbog.com/>https://kakbog.com</a> достоверная информация о гормональном фоне, потенции, урологических проблемах, профилактике, питании и образе жизни. Советы врачей, диагностика, лечение, препараты.
Современный медицинский портал <a href=https://medfactor.com.ua/>https://medfactor.com.ua</a> с упором на технологии: телемедицина, онлайн-запись, цифровые карты, расшифровка анализов, подбор препаратов. Удобный доступ к информации и поддержка на всех этапах — от симптомов до выздоровления.
Мужской портал <a href=https://realman.com.ua/>https://realman.com.ua</a> всё, что интересно и полезно: спорт, здоровье, стиль, авто, отношения, технологии, карьера и отдых. Практичные советы, обзоры, мнения и поддержка.
Кулинарные рецепты <a href=https://kulinaria.com.ua/>https://kulinaria.com.ua</a> на каждый день и для особых случаев. Домашняя выпечка, супы, салаты, десерты, блюда из мяса и овощей. Простые пошаговые инструкции, доступные ингредиенты и душевные вкусы.
Сайт для мужчин <a href=https://phizmat.org.ua/>https://phizmat.org.ua</a> всё о жизни с характером: здоровье, спорт, стиль, авто, карьера, отношения, технологии. Полезные советы, обзоры, мужской взгляд на важные темы.
Новостной портал <a href=https://sensus.org.ua/>https://sensus.org.ua</a> главные события дня в России и мире. Политика, экономика, общество, культура, спорт и технологии. Только проверенные факты, оперативные сводки, мнения экспертов и честная подача.
медицинский портал <a href=https://pobedilivmeste.org.ua/>https://pobedilivmeste.org.ua</a> с удобной навигацией и актуальной информацией. Болезни, симптомы, приёмы врачей, анализы, исследования, препараты и рекомендации.
займ денег <a href=https://vzyat-mikrozajm-5.ru/>оформить микрозайм</a>
Piano klavier noten <a href=https://klavier-noten-3.ru/>noten fur klavier</a>
быстрый займ <a href=https://vzyat-mikrozajm-5.ru/>займы</a>
Ноты пианино <a href=https://noty-fortepiano.ru/>пианино по нотам</a>
seo продвижение и контекстная реклама <a href=http://seoprocessoptimization.ru/>разработка сайта москва</a>
Путешествуйте с экспертами <a href=https://gid-po-kaliningradu.ru/>гид Калининград Светлана</a> по лучшим маршрутам.
На нашем сайте вы найдёте <a href=https://sebe-na-zametku.ru/>открытки</a> для любого случая. Яркие изображения, тёплые слова, праздничное настроение и стильный дизайн. Поделитесь эмоциями с близкими и сделайте каждый день особенным. Обновления каждый день, удобный формат, всё бесплатно!
Санобработка в Санкт-Петербурге! Комнаты, Дома, Офисы. Профессиональный сервис по конкурентным стоимости. Свободное время для хобби! Забронируйте приборку сейчас! Жмите https://uborka-top24.ru - Уборка квартир в СПб недорого
рефераты на заказ <a href=http://referatymarketing.ru/>сколько стоит сделать реферат</a>
заказать дипломную <a href=http://diplomastudy.ru/>написание дипломов на заказ</a>
установлен натяжной потолок <a href=https://natyazhnye-potolki-moskva1.ru/>цена натяжного потолка за квадратный</a>
Мы предлагаем <a href=https://komfortvl.ru/>https://komfortvl.ru/</a> с гарантией качества, соблюдением сроков и полным сопровождением. Индивидуальный подход, современные материалы и прозрачные цены. Работаем по договору. Закажите бесплатную консультацию и начните комфортный ремонт уже сегодня!
аренда автомобиля для поездки <a href=https://gdefile.ru/prokat-avto-dlya-poezdok-po-stolicze-dagestana.html>стоимость аренды автомобиля</a>
машину в аренду недорого <a href=https://rossoshru.ru/2025/04/23/arenda-i-prokat-mashin-v-mineralnyh-vodah/>сервис аренды авто</a>
Играешь в Fallout 76? Хочешь <a href=https://falloutbuy.com/>буст Fallout 76</a>? Широкий ассортимент предметов, включая силовую броню, легендарное оружие, хлам, схемы и многое другое для Fallout 76 на PC, Xbox и PlayStation. Мы предлагаем услуги буста, прокачки персонажа и готовые комплекты снаряжения.
Discover <a href=https://pornjourney.app/>create porn</a>, a platform where artificial intelligence makes your desires come true. Create your perfect AI heroines, chat in real time, and enjoy personalized content tailored to your tastes. The next level of sex technology is here.
На diabloshop.ru вы можете купить <a href=https://diabloshop.ru/product-category/diablo-3-reaper-of-souls/ >https://diabloshop.ru/product-category/diablo-3-reaper-of-souls/</a> золото Diablo 4, руны Diablo 2 Resurrected, а также уникальные предметы и легендарное снаряжение для всех платформ — PC, Xbox, PlayStation и Nintendo Switch. Мы предлагаем быстрый буст персонажа, услуги прокачки, сбор лучших билдов и готовые комплекты снаряжения.
Переходите <a href=https://uborka-v-spv24pro.ru>Клининг помещений</a>
На diabloshop.ru вы можете купить <a href=https://diabloshop.ru/bildy-i-gajdy-diablo-3-ros/>https://diabloshop.ru/bildy-i-gajdy-diablo-3-ros/</a> золото Diablo 4, руны Diablo 2 Resurrected, а также уникальные предметы и легендарное снаряжение для всех платформ — PC, Xbox, PlayStation и Nintendo Switch. Мы предлагаем быстрый буст персонажа, услуги прокачки, сбор лучших билдов и готовые комплекты снаряжения.
Играешь в Fallout 76? Хочешь <a href=https://falloutbuy.com/>легендарное оружие Fallout 76</a>? Широкий ассортимент предметов, включая силовую броню, легендарное оружие, хлам, схемы и многое другое для Fallout 76 на PC, Xbox и PlayStation. Мы предлагаем услуги буста, прокачки персонажа и готовые комплекты снаряжения.
экскурсии по калининграду на автобусе <a href=https://ehkskursii-v-kaliningrade.ru/>калининград экскурсии по городу</a>
помощь юриста по семейным делам <a href=https://urwork.ru/uslugi/semejnyj-yurist/>семейное право помощь юриста</a>
судебные приставы взыскание задолженности <a href=https://urwork.ru/uslugi/vzyskanie-zadolzhennostej-yuridicheskie-uslugi/>взыскание долгов задолженностей</a>
Извините за то, что вмешиваюсь… Но мне очень близка эта тема. Пишите в PM.
?????????"[url=https://neurontravels.com/page-142/]https://neurontravels.com/page-142/[/url] ?????????(??)?? ?????????????????????Bellasjon??????????????????????????:???????????????????????????????? ifyouare playinginonlinecasino,basic ruleso thatlisteners??????playpokerat least/leastonce.
Инвестиции в строительство <a href=https://permgragdanstroy.ru/>https://permgragdanstroy.ru</a> жилой и коммерческой недвижимости. Прибыльные проекты, прозрачные условия, сопровождение на всех этапах. Участвуйте в строительстве с гарантированной доходностью.
laravel разработка сайта <a href=https://razrabotka-sayta-laravel.ru/>https://razrabotka-sayta-laravel.ru</a>
шильда металлическая латунь <a href=https://metallicheskie-shildy.ru/>шильды металлические изготовление</a>
Микрозайм онлайн без отказа срочно <a href=https://zajm-bez-otkaza.ru/>быстрый займ без отказа</a>
Деньги в долг онлайн на карту <a href=https://zajm-onlajn-1.ru/>быстрые деньги займ на карту</a>
Сайт микрозаймов <a href=https://bystryj-zajm.ru/>онлайн займ денег</a>
шильдик на заказ <a href=https://izgotovlenie-shildov-na-zakaz.ru/>металлические шильдики на заказ</a>
изготовление шильд москва <a href=https://shildi-iz-metalla.ru/>срочное изготовление шильдов</a>
Бесплатная панель управления <a href=https://1panel.click/>install 1Panel</a> сервером с открытым исходным кодом. Удобный интерфейс, поддержка популярных ОС, автоматизация задач, резервное копирование, управление сайтами и базами. Оптимально для вебмастеров и системных администраторов.
онлайн консультация юриста <a href=https://advokat-abramov.ru/>онлайн консультация юриста</a>
ПО для управления задачами <a href=https://devrum.ru/sozdanie-edinoi-sistemy-upravleniya/>создание единой системы управления</a>
f422d3_
[url=https://gotwebsite1.com/local-seo-scottsdale/]Digital SEO training courses with accreditations[/url]
корпоративные бейджи <a href=https://badge-moscow-na-zakaz.ru/>заказать бейдж металлический москва</a>
железные значки на заказ <a href=https://znachki-metallicheskie-zakaz.ru/>металлические значки на заказ москва</a>
поисковое seo продвижение <a href=https://seoprocessoptimization.ru/>создание и раскрутка сайта стоимость</a>
значки металлические на заказ <a href=https://izgotovit-znachki-metalicheskie.ru/>металлические значки</a>
типография недорого <a href=https://tipografiya-spb11.ru/>типография производство</a>
печатать в типографии <a href=https://tipografiya-spb7.ru/>печатать в типографии</a>
печатная типография <a href=https://tipografiya-spb55.ru/>https://tipografiya-spb55.ru</a>
Станки для производства <a href=https://stanki-a.ru/>листогибочные прессы</a> металлообработка, резка, сварка, автоматизация. Продажа новых и восстановленных моделей от ведущих брендов. Гарантия, обучение персонала, техподдержка.
печать визиток дешево <a href=https://pechat-vizitok33.ru/>печать визиток на пластике</a>
типография печать визиток <a href=https://pechat-vizitok11.ru/>печать визиток на пластике</a>
Онлайн сервис <a href=https://picex.ru/>get all images from url</a> для получения картинок с любого сайта. Вставьте URL — и мгновенно получите изображения на своём устройстве. Поддержка всех форматов, никаких ограничений и лишних действий. Работает бесплатно и круглосуточно.
Нужна <a href=https://pechat-nakleek1.ru/>печать виниловых наклеек</a>? Закажите стикеры любых форм и размеров с доставкой. Яркие, прочные, влагостойкие наклейки на пленке и бумаге — для рекламы, декора, маркировки и упаковки.
Профессиональная <a href=https://tipografiya-spb33.ru/>стоимость типография</a>. Изготовим любые печатные материалы — от визиток до каталогов. Качественно, быстро, с гарантией. Закажите онлайн или приезжайте в офис в СПб.
Изготовление и <a href=https://pechat-nakleek44.ru/>печать объемных наклеек</a>. Стикеры для бизнеса, сувениров, интерьера и упаковки. Печатаем тиражами от 1 штуки, любые материалы и формы. Качественно, недорого, с доставкой по СПб.
Безболезненная <a href=https://lazernaya-epilyaciya33.ru/>https://lazernaya-epilyaciya33.ru</a> Удаление волос на любом участке тела. Работаем с чувствительной кожей, используем новейшие лазеры. Акции, абонементы, индивидуальный подход.
Удаление волос <a href=https://lazernaya-epilyaciya-spb1.ru/>https://lazernaya-epilyaciya-spb1.ru</a>: гладкая кожа на долгое время. Аппараты последнего поколения, опытные мастера, комфортная обстановка. Эпиляция для женщин и мужчин. Онлайн-запись, гибкие цены, без лишнего стресса.
Профессиональная <a href=https://lazernaya-epilyaciya11.ru/>процедура лазерной эпиляции</a>. Эффективное удаление волос на любом участке тела, подход к любому фототипу. Сертифицированные специалисты, стерильность, скидки. Запишитесь прямо сейчас!
грузчика заказать <a href=https://gruzoperevozki-svao.ru/>профессиональные грузчики</a>
услуги грузчиков перевозки <a href=https://gruzchikiise.ru/>грузчика заказать</a>
грузчики услуга <a href=https://ungruzchiki.ru/>грузчик нанять</a>
грузчики дешево <a href=https://gruzoperevozki-svao.ru/>услуга грузчиков</a>
щас заценим вроде тема
already in them also presented various themes, based movies, books, Halloween, [url=https://indiacsr.in/aviator-game-download-review/]https://indiacsr.in/aviator-game-download-review/[/url] magic and much more.
медицинский центр абакан телефон <a href=https://medicinskiy-centr11.ru/>https://medicinskiy-centr11.ru</a>
Избавьтесь от волос <a href=https://lazernaya-epilyaciya-spb5.ru/>лазерная эпиляция цена спб</a> навсегда — с помощью лазерной эпиляции. Эффективные процедуры на любом участке тела, минимальный дискомфорт, заметный результат уже после первого сеанса.
купить софт <a href=https://internet-magazin-soft.kz/>купить софт цена</a>
врач узи <a href=https://uzi-abakan11.ru/>https://uzi-abakan11.ru</a>
хороший дерматолог <a href=https://dermatolog-abakan1.ru/>врач дерматолог абакан</a>
центр абакан медицинский номер <a href=https://medicinskiy-centr-abakan11.ru/>клиника абакан</a>
Hi! I could have sworn I've been too this website before butt after reading through some of the
post I realized it's new to me. Anyhow, I'm definitely happy I found it and I'll be bookmarking aand checking back frequently! http://boyarka-inform.com/
gpt-4 онлайн <a href=https://ruschatgpt.ru/>чат лжипити</a>
прием терапевта абакан <a href=https://terapevt-abakan1.ru/>терапевт</a>
оказание услуг грузчиков <a href=https://vog-pereezd.ru/>помощь при переезде грузчики</a>
Онлайн-журнал <a href=https://inox.com.ua/>https://inox.com.ua</a> о строительстве: обзоры новинок, аналитика, советы, интервью с архитекторами и застройщиками.
<a href=https://copicsketch.ru/>Дневник скетчера</a>
Все виды накрутки Telegram канала в одном месте по низким ценам [url=https://cheatbot.ru/telegram]накрутка подписчиков в телеграм живые[/url]
Свежие <a href=https://ni-kpg.ru/>новости юфс</a>: бои, результаты, анонсы турниров, интервью и трансферы бойцов. UFC, Bellator, ACA и другие промоушены. Следите за карьерой топовых бойцов и громкими поединками в мире смешанных единоборств.
Fresh and relevant <a href=https://eternal.football/>football news today</a>: matches, results, transfers, interviews and reviews. Follow the events of the Champions League, RPL, EPL and other tournaments. All the most important from the world of football - on one page!
Самые главные <a href=https://football-zvezda.ru/>новости футбола англия</a> каждый день: от закулисья клубов до громких голов. Новости РПЛ, НХЛ, Бундеслиги, Серии А, Ла Лиги и ЛЧ. Прямые эфиры, прогнозы, аналитика и трансферные слухи в одном месте.
Читайте свежие <a href=https://dmeteor.ru/>новости хоккея</a> онлайн. Результаты матчей, расклады плей-офф, громкие трансферы и слухи. Всё о российских и зарубежных лигах.
If you are just about to register with 1win, be sure to use the promo code [url=https://dom-nam.ru/index.php/forum/dobro-pozhalovat/166706-melbet-promokod-fribet-15-000rublej-dlya-novykh-ig#206607]https://dom-nam.ru/index.php/forum/dobro-pozhalovat/166706-melbet-promokod-fribet-15-000rublej-dlya-novykh-ig#206607[/url]
Туроператор №1 по приему туристов в Казани. Туры и экскурсии в Казань и по Татарстану [url=https://to-kazan.ru]туры в казань[/url]
The code must be activated during registration [url=https://www.tapatalk.com/groups/dzerjinsky/viewtopic.php?f=2&t=45405&from_new_topic=1]https://www.tapatalk.com/groups/dzerjinsky/viewtopic.php?f=2&t=45405&from_new_topic=1[/url]
AI generator <a href=https://nsfw-ai.net/>nsfw ai</a> of the new generation: artificial intelligence turns text into stylish and realistic pictures and videos.
Сотрудничество с аутсорсинговой компанией позволяет снизить операционные расходы [url=https://buh-v-pomosh.ru/raschety-cherez-podotchetnikov/podotchetnye-lica-eto-kto-takie-kak-s-ni]https://buh-v-pomosh.ru/raschety-cherez-podotchetnikov/podotchetnye-lica-eto-kto-takie-kak-s-ni[/url]
Looking for the best cannabis clubs in Benidorm [url=https://spaininter.com/en/news/427-where-to-buy-weed-in-valencia-benidorm-alicante-and-torrevieja]cannabis club Benidorm[/url]
Быстрые пути к результату, это значит.
Как раскрутить сайт за короткое время, выгодные решения.
GSA ссылки [url=https://www.kwork.ru/links/41629912/seo-pushka-dlya-sayta-mnogourovnevaya-piramida-ssylok-pod-klyuch]https://www.kwork.ru/links/41629912/seo-pushka-dlya-sayta-mnogourovnevaya-piramida-ssylok-pod-klyuch[/url] .
Как так?
The expression of oct three quarters, a well-known pluripotency gene, during with [url=https://StemCellBudget.com/]https://StemCellBudget.com[/url] was increased approximately by 20/20 times compared with ?-actin in Moscow time people with VPA and the nutravivo™ brain growth activator.
Это было и со мной. Можем пообщаться на эту тему. Здесь или в PM.
White, Y., Woods, D.K., Takai, Y., Ishihara, O., Seki, H., Tilly, D.L. [url=https://AutismStemCellFrance.com/]https://AutismStemCellFrance.com/[/url] (February 2012). "Egg formation by mitotically active germ cells isolated from the ovaries of women of reproductive age".
Не могу сейчас поучаствовать в обсуждении - нет свободного времени. Но вернусь - обязательно напишу что я думаю.
because our team looking at the future, the [url=https://SafeTherapyClinics.com/]https://SafeTherapyClinics.com[/url], ongoing studies and techniques in field of stem cell therapy cells promise further breakthroughs and formation of their use sphere in the process of treatment to a greater extent a variety of diseases.
Продвижение в социальных сетях SMM https://vc.ru/smm-promotion
https://animixonline.ru/
Купить подписчиков ВК — быстрый способ увеличить охваты, поднять доверие к сообществу https://vc.ru/smm-promotion/2017240-kupit-podpischikov-vk-top-21-servis
https://animixonline.ru/
Moreover, every player who enters our special promotional code during [url=https://rusthost.net/nitrous-networks/]ördög nóra porno[/url]
resume civil engineer fresher <a href=https://resumes-engineers.com/>resume civil engineer experience</a>
Write more, thhats all I have to say. Literally, it seems
aas though you relied on the video to make your point.
You clearly know what youre talking about, why throw away your intelligence on just posting videos to your site when you could be giving us something informative
to read? http://Boyarka-Inform.com/
Рассказываем как правильно сажать томаты, огурцы, картошку, базилик, розы, тюльпаны и многое другое. Как бороться с вредителями и всё не испортить. Идеи для дачи, сада и огорода [url=https://t.me/kak_pravilno_sazhat_na_dache/4604]Как правильно сажать кинзу[/url]
Log in and register in the Sever Casino mobile application [url=https://sever-online-casino.top/lichnyj-kabinet]север казино личный кабинет[/url]
Meet <a href=https://llmbrowser.io/>https://llmbrowser.io</a>, your next browser for agents. It's built for advanced web tasks. This solution features advanced antidetect capabilities, making it an ideal agentic antidetect browser. Upgrade your AI toolkit with a true browser for AI agents. Explore its features.
Амбениум парентерал <a href=https://ambenium.ru/>ambenium.ru</a> - снимает боль, жар и воспаление при травмах, артритах, невралгиях и простуде. Быстрый эффект, надёжное действие, проверенная формула.
Дом из контейнера <a href=https://russiahelp.com/>https://russiahelp.com</a> под ключ — мобильное, экологичное и бюджетное жильё. Индивидуальные проекты, внутренняя отделка, электрика, сантехника и монтаж
Загадки Вселенной <a href=https://phenoma.ru/>https://phenoma.ru</a> паранормальные явления, нестандартные гипотезы и научные парадоксы — всё это на Phenoma.ru
PC application <a href=https://authenticatorsteamdesktop.com/>https://authenticatorsteamdesktop.com</a> replacing the mobile Steam Guard. Confirm logins, trades, and transactions in Steam directly from your computer. Support for multiple accounts, security, and backup.
Удобный способ купить барометр для дома [url=https://psc.by/products/kontrolno-izmeritelnye-pribory/pirometry/]пирометр[/url]
Агентство недвижимости <a href=https://metropolis-estate.ru/>https://metropolis-estate.ru</a> покупка, продажа и аренда квартир, домов, коммерческих объектов. Полное сопровождение сделок, юридическая безопасность, помощь в оформлении ипотеки.
Квартиры посуточно <a href=https://kvartiry-posutochno19.ru/>https://kvartiry-posutochno19.ru</a> в Абакане — от эконом до комфорт-класса. Уютное жильё в центре и районах города. Чистота, удобства, всё для комфортного проживания.
Ремонт квартир <a href=https://berlin-remont.ru/>https://berlin-remont.ru</a> и офисов любого уровня сложности: от косметического до капитального. Современные материалы, опытные мастера, прозрачные сметы. Чисто, быстро, по разумной цене.
СРО УН «КИТ» <a href=https://sro-kit.ru/>https://sro-kit.ru</a> саморегулируемая организация для строителей, проектировщиков и изыскателей. Оформление допуска СРО, вступление под ключ, юридическое сопровождение, помощь в подготовке документов.
Ремонт квартир <a href=https://remont-kvartir-novo.ru/>https://remont-kvartir-novo.ru</a> под ключ в новостройках — от черновой отделки до полной готовности. Дизайн, материалы, инженерия, меблировка.
Ремонт квартир <a href=https://remont-otdelka-mo.ru/>https://remont-otdelka-mo.ru</a> любой сложности — от косметического до капитального. Современные материалы, опытные мастера, строгие сроки. Работаем по договору с гарантиями.
Webseite <a href=https://cvzen.de/>cvzen.de</a> ist Ihr Partner fur professionelle Karriereunterstutzung – mit ma?geschneiderten Lebenslaufen, ATS-Optimierung, LinkedIn-Profilen, Anschreiben, KI-Headshots, Interviewvorbereitung und mehr. Starten Sie Ihre Karriere neu - gezielt, individuell und erfolgreich.
sitio web <a href=https://tavoq.es/>tavoq.es</a> es tu aliado en el crecimiento profesional. Ofrecemos CVs personalizados, optimizacion ATS, cartas de presentacion, perfiles de LinkedIn, fotos profesionales con IA, preparacion para entrevistas y mas. Impulsa tu carrera con soluciones adaptadas a ti.
вопрос юристу <a href=https://besplatnaya-yuridicheskaya-konsultaciya1.ru/>бесплатная помощь юриста онлайн без регистрации</a>
Модульный дом <a href=https://kubrdom.ru/>https://kubrdom.ru</a> из морского контейнера для глэмпинга — стильное и компактное решение для туристических баз. Полностью готов к проживанию: утепление, отделка, коммуникации.
kraken darknet <a href=https://kra28--cc.icu/>kraken onion</a>
Официальное зеркало мостбет казино для игры удобно и просто скачать апк файл для андроид и крутить популярные слоты в приложении мостбет [url=https://mostbet-casino865.top/]mostbet[/url]
Professional <a href=https://www.nwconcreteexperts.com/concrete-driveway-contractors-in-seattle>concrete driveways in seattle</a> — high-quality installation, durable materials and strict adherence to deadlines. We work under a contract, provide a guarantee, and visit the site. Your reliable choice in Seattle.
Professional <a href=https://buddhabuilders.com/>deck builders near me</a> — reliable service, quality materials and adherence to deadlines. Individual approach, experienced team, free estimate. Your project — turnkey with a guarantee.
Professional <a href=https://www.seattlesbestpainters.com/power-washing-seattle>Seattle power washing</a> — effective cleaning of facades, sidewalks, driveways and other surfaces. Modern equipment, affordable prices, travel throughout Seattle. Cleanliness that is visible at first glance.
The official website of Riobet Casino is convenient and easy to download [url=https://riobet-online-casino24.top/]риобет онлайн казино[/url]
Нужна камера? <a href=https://alfa-prestig.ru/>поворотная камера видеонаблюдения</a> для дома, офиса и улицы. Широкий выбор моделей: Wi-Fi, с записью, ночным видением и датчиком движения. Гарантия, быстрая доставка, помощь в подборе и установке.
Каркасные дома и бани изготовленные из клееного бруса под ключ в Вологде и по всей России [url=https://stroy-dom-brus.ru/]изготовление домов и бань из клееного бруса под ключ[/url]
Строим дачные дома,по каркасной технологии,с утеплением [url=https://stroy-dom-brus.ru/]Каркасные дома и бани из клееного бруса под ключ[/url]
car transport prices <a href=https://crctransport.us/how-auto-transport-works-behind-the-scenes-of-car-hauling-services/>how much does it cost to ship a car from florida to california</a>
A medical record is an important document required for work in certain areas [url=https://tinyurl.com/6czx4sud]https://tinyurl.com/6czx4sud[/url]
Гражданство по рождению, натурализации и инвестициям — сравниваем страны, сроки и требования [url=https://vgrazhdanstve.ru/]https://vgrazhdanstve.ru/[/url]
Outsourcing accounting services allows companies [url=https://fb.ru/article/265070/kak-i-kem-predostavlyayutsya-buhgalterskie-uslugi-na-autsors]https://fb.ru/article/265070/kak-i-kem-predostavlyayutsya-buhgalterskie-uslugi-na-autsors[/url]
Профессиональное <a href=https://kosmetologicheskoe-oborudovanie-msk.ru/>https://kosmetologicheskoe-oborudovanie-msk.ru</a> для салонов красоты, клиник и частных мастеров. Аппараты для чистки, омоложения, лазерной эпиляции, лифтинга и ухода за кожей.
Outsourcing Accounting Services from Windes allows your company [url=https://bloknot-volzhsky.ru/news/profjessionalnoje-bukhgaltjerskoje-soprovozhdjenije-gramotnost-i-opjerativnost-945483]https://bloknot-volzhsky.ru/news/profjessionalnoje-bukhgaltjerskoje-soprovozhdjenije-gramotnost-i-opjerativnost-945483[/url]
Outsourcing of accounting services is the transfer [url=http://yopolis.ru/publikacii/2974-bukhgaltjerskoje-soprovozhdjenije-autsorsingovoj-kompanii.html]http://yopolis.ru/publikacii/2974-bukhgaltjerskoje-soprovozhdjenije-autsorsingovoj-kompanii.html[/url]
https://zeus-vshades.ru
Some CPA firms include outsourced personnel [url=https://www.smolensk2.ru/story.php?id=80627]https://www.smolensk2.ru/story.php?id=80627[/url]
https://pg-soft-game.ru
Renting a car in the United Arab Emirates is a convenient way [url=https://alabama-news.com/rent-audi-in-dubai-at-yeti-main-advantages-of-the-service.html]https://alabama-news.com/rent-audi-in-dubai-at-yeti-main-advantages-of-the-service.html[/url]
Scooter and Bike Rental in Phuket becomes a breeze https://vk.com/motobike_phuket
For new businesses, startups that do not yet have experience [url=https://progorodnn.ru/kak-vosstanovit-bukhgalterskiy-uchet-bez-poter-prakticheskoye-rukovodstvo-dlya-biznesa]https://progorodnn.ru/kak-vosstanovit-bukhgalterskiy-uchet-bez-poter-prakticheskoye-rukovodstvo-dlya-biznesa[/url]
Бизнес юрист <a href=https://yuristy-ekaterinburga.ru/>yuristy-ekaterinburga.ru</a>
Краснодар продажа шиномонтаж <a href=https://shinomontazh-vyezdnoj.ru/>https://shinomontazh-vyezdnoj.ru</a>
типография сайт <a href=https://hitech-print.ru/>цифровая типография</a>
Аутсорсинг бухгалтерских услуг подходит широкому кругу компаний [url=https://gorodkirov.ru/news/peredacha-buhgalterskogo-ucheta-na-autsorsing-chto-nuzhno-znat/]https://gorodkirov.ru/news/peredacha-buhgalterskogo-ucheta-na-autsorsing-chto-nuzhno-znat/[/url]
Outsourcing of accounting services is the transfer of your accounting [url=https://168.ru/news/reklama/generalnyj-direktor-i-pravo-podpisi-osobennosti-zameshheniya-buhgaltera]https://168.ru/news/reklama/generalnyj-direktor-i-pravo-podpisi-osobennosti-zameshheniya-buhgaltera[/url]
Our community unites amateur travelers to cities [url=https://tourbig.ru/]https://tourbig.ru/[/url]
Защитные кейсы <a href=https://plastcase.ru/>plastcase</a> в Санкт-Петербурге — надежная защита оборудования от влаги, пыли и ударов. Большой выбор размеров и форматов, ударопрочные материалы, индивидуальный подбор.
Free bets and cashback, but how realistic is it to cash [url=https://myteana.ru/forums/index.php?autocom=gallery&req=si&img=7358]https://myteana.ru/forums/index.php?autocom=gallery&req=si&img=7358[/url]
Наша цель — поддерживать здоровье женщин и помогать им в решении любых медицинских вопросов [url=https://skagiorabote.ru/women_clinik_36209.html]https://skagiorabote.ru/women_clinik_36209.html[/url]
займ онлайн срочно <a href=https://zajmy-onlajn.ru/>взять онлайн займ на карту</a>
Vajalik raha kiiresti? Taotle kiirlaenu veebis – vastus mone minutiga. Paindlikud tingimused, usaldusvaarne teenus. Taotle kohe ja saa raha tana! [url=https://ref.ee/]kiirlaen[/url]
Наша цель - забота о пациенте. Благодарность от наших пациентов - основной показатель качества лечения [url=https://topotzyv.ru/women-clinik-medicinskiy-centr-specializiruyushchiysya-na-medicinskih-spravkah-i-medknizhkah]https://topotzyv.ru/women-clinik-medicinskiy-centr-specializiruyushchiysya-na-medicinskih-spravkah-i-medknizhkah[/url]
Строительный портал <a href=https://proektsam.kyiv.ua/>https://proektsam.kyiv.ua</a> свежие новости отрасли, профессиональные советы, обзоры материалов и технологий, база подрядчиков и поставщиков. Всё о ремонте, строительстве и дизайне в одном месте.
Портал о строительстве <a href=https://buildportal.kyiv.ua/>https://buildportal.kyiv.ua</a> и ремонте: лучшие решения для дома, дачи и бизнеса. Инструменты, сметы, калькуляторы, обучающие статьи и база подрядчиков.
анонимное лечение алкоголизма <a href=https://alko-info.ru/>лечение алкоголизма в Нижнем Новгороде</a>
Праздничная продукция <a href=https://prazdnik-x.ru/>https://prazdnik-x.ru</a> для любого повода: шары, гирлянды, декор, упаковка, сувениры. Всё для дня рождения, свадьбы, выпускного и корпоративов.
стоимостная экспертиза <a href=https://ur.moscow/oczenka-specztehniki/>оценка комнаты</a>
наркомания зависимость лечение <a href=https://narco-info.ru/>лечение наркомании клиника</a>
Всё для строительства <a href=https://d20.com.ua/>https://d20.com.ua</a> и ремонта: инструкции, обзоры, экспертизы, калькуляторы. Профессиональные советы, новинки рынка, база строительных компаний.
Строительный журнал <a href=https://garant-jitlo.com.ua/>https://garant-jitlo.com.ua</a> всё о технологиях, материалах, архитектуре, ремонте и дизайне. Интервью с экспертами, кейсы, тренды рынка.
<a href=https://xn--ra2-6ua.cc>kraken СПб</a>
Современный строительный <a href=https://interiordesign.kyiv.ua/>https://interiordesign.kyiv.ua</a> журнал: идеи, решения, технологии, тенденции. Всё о ремонте, стройке, дизайне и инженерных системах.
Информационный журнал <a href=https://newhouse.kyiv.ua/>https://newhouse.kyiv.ua</a> для строителей: строительные технологии, материалы, тенденции, правовые аспекты.
Нужен монтаж отопления в Алматы? Профессиональные специалисты быстро и качественно установят систему отопления в доме, квартире или офисе [url=https://montazh-otopleniya.kz/]установка отопления в квартире[/url]
Всё о строительстве <a href=https://stroyportal.kyiv.ua/>https://stroyportal.kyiv.ua</a> в одном месте: технологии, материалы, пошаговые инструкции, лайфхаки, обзоры, советы экспертов.
Журнал о строительстве <a href=https://sovetik.in.ua/>https://sovetik.in.ua</a> качественный контент для тех, кто строит, проектирует или ремонтирует. Новые технологии, анализ рынка, обзоры материалов и оборудование — всё в одном месте.
Строительный журнал <a href=https://poradnik.com.ua/>https://poradnik.com.ua</a> для профессионалов и частных застройщиков: новости отрасли, обзоры технологий, интервью с экспертами, полезные советы.
Кулинарный портал <a href=https://vagon-restoran.kiev.ua/>https://vagon-restoran.kiev.ua</a> с тысячами проверенных рецептов на каждый день и для особых случаев. Пошаговые инструкции, фото, видео, советы шефов.
Мужской журнал <a href=https://hand-spin.com.ua/>https://hand-spin.com.ua</a> о стиле, спорте, отношениях, здоровье, технике и бизнесе. Актуальные статьи, советы экспертов, обзоры и мужской взгляд на важные темы.
Читайте мужской <a href=https://zlochinec.kyiv.ua/>https://zlochinec.kyiv.ua</a> журнал онлайн: тренды, обзоры, советы по саморазвитию, фитнесу, моде и отношениям. Всё о том, как быть уверенным, успешным и сильным — каждый день.
Портал о ремонте <a href=https://as-el.com.ua/>https://as-el.com.ua</a> и строительстве: от черновых работ до отделки. Статьи, обзоры, идеи, лайфхаки.
Одо-Студио — это не просто агентство. Это команда, которая помогает брендам расти [url=https://odo-studio.ru/]https://odo-studio.ru/[/url]
Читайте авто блог <a href=https://autoblog.kyiv.ua/>https://autoblog.kyiv.ua</a> обзоры автомобилей, сравнения моделей, советы по выбору и эксплуатации, новости автопрома.
Сайт о строительстве <a href=https://solution-ltd.com.ua/>https://solution-ltd.com.ua</a> и дизайне: как построить, отремонтировать и оформить дом со вкусом.
Свежие новости <a href=https://ktm.org.ua/>https://ktm.org.ua</a> Украины и мира: политика, экономика, происшествия, культура, спорт. Оперативно, объективно, без фейков.
Авто портал <a href=https://real-voice.info/>https://real-voice.info</a> для всех, кто за рулём: свежие автоновости, обзоры моделей, тест-драйвы, советы по выбору, страхованию и ремонту.
Портал о строительстве <a href=https://start.net.ua/>https://start.net.ua</a> и ремонте: готовые проекты, интерьерные решения, сравнение материалов, опыт мастеров.
Строительный портал <a href=https://apis-togo.org/>https://apis-togo.org</a> полезные статьи, обзоры материалов, инструкции по ремонту, дизайн-проекты и советы мастеров.
Всё о строительстве <a href=https://furbero.com/>https://furbero.com</a> в одном месте: новости отрасли, технологии, пошаговые руководства, интерьерные решения и ландшафтный дизайн.
Портал для женщин <a href=https://olive.kiev.ua/>https://olive.kiev.ua</a> любого возраста: от секретов молодости и красоты до личностного роста и материнства.
Современный женский <a href=https://prowoman.kyiv.ua/>https://prowoman.kyiv.ua</a> портал: полезные статьи, лайфхаки, вдохновляющие истории, мода, здоровье, дети и дом.
Онлайн-портал <a href=https://leif.com.ua/>https://leif.com.ua</a> для женщин: мода, психология, рецепты, карьера, дети и любовь. Читай, вдохновляйся, общайся, развивайся!
If you are going to play 1Win, be sure to use the promo code 1W500GIFT [url=https://www.southjerseyonline.net/cb-profile/pluginclass/cbblogs.html?action=blogs&func=show&id=646]https://www.southjerseyonline.net/cb-profile/pluginclass/cbblogs.html?action=blogs&func=show&id=646[/url]
As a new 1win player, we recommend that you activate the promo code during the registration process [url=http://www.odnopolchane.net/forum/member.php?u=921209]http://www.odnopolchane.net/forum/member.php?u=921209[/url]
Портал о маркетинге <a href=https://reklamspilka.org.ua/>https://reklamspilka.org.ua</a> рекламе и PR: свежие идеи, рабочие инструменты, успешные кейсы, интервью с экспертами.
Семейный портал <a href=https://stepandstep.com.ua/>https://stepandstep.com.ua</a> статьи для родителей, игры и развивающие материалы для детей, советы психологов, лайфхаки.
Туристический портал <a href=https://aliana.com.ua/>https://aliana.com.ua</a> с лучшими маршрутами, подборками стран, бюджетными решениями, гидами и советами.
Всё о спорте <a href=https://beachsoccer.com.ua/>https://beachsoccer.com.ua</a> в одном месте: профессиональный и любительский спорт, фитнес, здоровье, техника упражнений и спортивное питание.
Using Tempmail safeguards your primary email address [url=http://bryners.ru/forum/viewtopic.php?f=14&t=91111]http://bryners.ru/forum/viewtopic.php?f=14&t=91111[/url]
Ищете незабываемый тур на Камчатку? Организуем увлекательные путешествия по самым живописным уголкам полуострова [url=https://turkamchatka.ru/]туры на камчатку[/url]
Take advantage of this exclusive offer and discover a world of possibilities with 1xBet [url=https://www.pinnaclepilatesfitness.com/group/pinnacle-pilates-group/discussion/06fee26b-53a2-468d-99ac-8f18c9d9900d]https://www.pinnaclepilatesfitness.com/group/pinnacle-pilates-group/discussion/06fee26b-53a2-468d-99ac-8f18c9d9900d[/url]
I am really loving the theme/design of your site.
Do you ever run into aany internet browser compatibility issues?
A couple of my blog readers have complained about my site
not operating correctly in Explorer but looks
great inn Opera. Do you have aany ideas to help fixx this problem? http://Boyarka-Inform.com/
Новости Украины <a href=https://useti.org.ua/>https://useti.org.ua</a> в реальном времени. Всё важное — от официальных заявлений до мнений экспертов.
Архитектурный портал <a href=https://skol.if.ua/>https://skol.if.ua</a> современные проекты, урбанистика, дизайн, планировка, интервью с архитекторами и тренды отрасли.
Информационный портал <a href=https://comart.com.ua/>https://comart.com.ua</a> о строительстве и ремонте: полезные советы, технологии, идеи, лайфхаки, расчёты и выбор материалов.
Всё о строительстве <a href=https://ukrainianpages.com.ua/>https://ukrainianpages.com.ua</a> просто и по делу. Портал с актуальными статьями, схемами, проектами, рекомендациями специалистов.
When you apply a 1xBet promo code for registration India [url=https://nanazwke558329.pointblog.net/start-betting-today-with-1xbet-promo-code-india-80733901]https://nanazwke558329.pointblog.net/start-betting-today-with-1xbet-promo-code-india-80733901[/url]
1xbet is currently one of the most popular and reputable sites [url=https://www.friend007.com/read-blog/220469]https://www.friend007.com/read-blog/220469[/url]
Using a 1xBet promo code is the best way to maximize your online betting [url=https://zoyadjpb143676.blogdigy.com/activa-tu-cГіdigo-promocional-1xbet-cuba-y-recibe-bonos-54002219]https://zoyadjpb143676.blogdigy.com/activa-tu-cГіdigo-promocional-1xbet-cuba-y-recibe-bonos-54002219[/url]
Строительный журнал <a href=https://dsmu.com.ua/>https://dsmu.com.ua</a> идеи, технологии, материалы, дизайн, проекты, советы и обзоры. Всё о строительстве, ремонте и интерьере
Портал о строительстве <a href=https://tozak.org.ua/>https://tozak.org.ua</a> от идеи до готового дома. Проекты, сметы, выбор материалов, ошибки и их решения.
Nice post. I lsarn something new and challenging
on blogs I stumbleupon everyday. It will alays be interesting to read content from other authors and
practice a little something from other sites. http://boyarka-inform.com/
Онлайн-новости <a href=https://arguments.kyiv.ua/>https://arguments.kyiv.ua</a> без лишнего: коротко, по делу, достоверно. Политика, бизнес, происшествия, спорт, лайфстайл.
Информационный портал <a href=https://dailynews.kyiv.ua/>https://dailynews.kyiv.ua</a> актуальные новости, аналитика, интервью и спецтемы.
Портал для женщин <a href=https://a-k-b.com.ua/>https://a-k-b.com.ua</a> любого возраста: стиль, красота, дом, психология, материнство и карьера.
The Linebet promo code is a unique alphanumeric code [url=https://enkling.com/read-blog/6923]https://enkling.com/read-blog/6923[/url]
Promotional codes are the key to unlocking bonuses and extra benefits [url=https://directory.dorsetecho.co.uk/company/b609f61172943f9151497b04d16a8ca0]https://directory.dorsetecho.co.uk/company/b609f61172943f9151497b04d16a8ca0[/url]
Thanks to this code, you can get not only a welcome bonus [url=https://www.ready-bookmarks.win/registro-melbet-argentina-con-codigo-promocional-incluido]https://www.ready-bookmarks.win/registro-melbet-argentina-con-codigo-promocional-incluido[/url]
Мировые новости <a href=https://ua-novosti.info/>https://ua-novosti.info</a> онлайн: политика, экономика, конфликты, наука, технологии и культура.
Только главное <a href=https://ua-vestnik.com/>https://ua-vestnik.com</a> о событиях в Украине: свежие сводки, аналитика, мнения, происшествия и реформы.
Офисная мебель <a href=https://officepro54.ru/>https://officepro54.ru</a> в Новосибирске купить недорого от производителя
Быстрая доставка алкоголя круглосуточно и даже ночью [url=https://www.arcgames.com/ru/forums/nwru#/discussion/218979/alkogol-na-dom-sankt-peterburg/p1?new=1]алкоголь на дом санкт-петербург[/url]
Recently I was also looking for a working pari promo code during registration [url=https://www.foros24h.com/351/foros-de-espana-sobre-viajes-y-viajar/codigo-promocional-de-1xbet-con-bono-del-100-por-deposito-151114.html]https://www.foros24h.com/351/foros-de-espana-sobre-viajes-y-viajar/codigo-promocional-de-1xbet-con-bono-del-100-por-deposito-151114.html[/url]
Unlock an exclusive welcome offer by using the 1xBet promo code 2026 [url=https://hugsqueeze.com/read-blog/53164_1xbet-ph-promo-code-for-registration-vip-bonus-130.html]https://hugsqueeze.com/read-blog/53164_1xbet-ph-promo-code-for-registration-vip-bonus-130.html[/url]
Promotional codes are the key to unlocking bonuses and extra benefits [url=https://www.nazaret.edu.ec/profile/1xbeeetapp21339/profile]https://www.nazaret.edu.ec/profile/1xbeeetapp21339/profile[/url]
защитный кейс digitalrazor <a href=https://plastcase.ru/>plastcase</a>
You can use our bonus code to get casino welcome bonus up to 1500 EUR [url=https://git.project-hobbit.eu/-/snippets/51861]https://git.project-hobbit.eu/-/snippets/51861[/url]
A Melbet promo code is a special sequence of characters that you enter when registering [url=https://anniekpcc773776.activoblog.com/40099121/melbet-cГіdigo-promocional-como-usar-no-primeiro-depГіsito]https://anniekpcc773776.activoblog.com/40099121/melbet-cГіdigo-promocional-como-usar-no-primeiro-depГіsito[/url]
Free spin winnings are capped at €50 for fair play [url=https://www.diigo.com/user/hira100?query=%231xbetpromocoderegistrationindia]https://www.diigo.com/user/hira100?query=%231xbetpromocoderegistrationindia[/url]
By entering it during registration, you can increase the welcome bonus [url=https://madesocials.com/story5162202/1xbet-sri-lanka-promo-code-registration-bonus-100-up-to-130]https://madesocials.com/story5162202/1xbet-sri-lanka-promo-code-registration-bonus-100-up-to-130[/url]
Доставка алкоголя круглосуточно — это гарантия того, что в любой момент вы можете сделать заказ [url=https://piter.en.cx/Guestbook/Messages.aspx?page=1&fmode=gb&topic=364160&anchor#7948188]алкоголь на дом петербург[/url]
помощь в написании диплома <a href=https://diplomsdayu.ru/>дипломная работа на заказ стоимость</a>
реферат купить онлайн <a href=https://referatymehanika.ru/>купить реферат срочно</a>
Use the links on this page to go to the official 1xBet website [url=https://www.diigo.com/item/note/902oi/jaet?k=e22578e1e7e77bca4988c2d13c0764fe]https://www.diigo.com/item/note/902oi/jaet?k=e22578e1e7e77bca4988c2d13c0764fe[/url]
Pour cela, a special formula is prepared in the registration formula [url=https://menagerie.media/index.php?link1=read-blog&id=122187]https://menagerie.media/index.php?link1=read-blog&id=122187[/url]
Discover the last word betting encounter using the distinctive code promo Megapari [url=https://deanyioq01345.wikinewspaper.com/3877876/unlock_unique_bets_and_bonuses_with_the_top_code_promo_megapari_delivers]https://deanyioq01345.wikinewspaper.com/3877876/unlock_unique_bets_and_bonuses_with_the_top_code_promo_megapari_delivers[/url]
написание контрольных <a href=https://kontrolnyestatistika.ru/>выполнение контрольных</a>
The main function of bonus codes is to provide players [url=https://getsocialselling.com/story5203079/c%C3%B3digo-promocional-1xbet-2025-ofertas-actuales]https://getsocialselling.com/story5203079/c%C3%B3digo-promocional-1xbet-2025-ofertas-actuales[/url]
Effective marketing collateral is essential for promoting your brand [url=https://daviddelavariaffiliate.info/blog/how-to-choose-profitable-niches-for-affiliate-marketing]How to Choose Profitable Niches for Affiliate Marketing[/url]
Сплит-система купить <a href=https://brand-climat.ru/>https://brand-climat.ru</a> современные модели с тихой работой и инверторным управлением. Подбор под ваши задачи, быстрая доставка и официальная гарантия. Идеальное решение для дома и офиса!
Расчет пожарных рисков - мероприятие по расчету и сопоставлению нормативно допустимой величины пожарного риска с реальной [url=https://vk.com/wall-48277440_22537]расчет пожарных рисков[/url]
JoomlaDocs — это информационный сервис, посвящённый современным технологиям, digital-инструментам и эффективному маркетингу [url=https://joomla-docs.ru/]https://joomla-docs.ru/[/url]
A promo code is a unique combination of characters that grants access to a bonus [url=https://www.pubpub.org/user/promocode-1xbetle]https://www.pubpub.org/user/promocode-1xbetle[/url]
Репетитор по физике <a href=https://repetitor-po-fizike-spb.ru/>https://repetitor-po-fizike-spb.ru</a> СПб: школьникам и студентам, с нуля и для олимпиад. Четкие объяснения, практика, реальные результаты.
Где купить идеальные римские шторы
почему римские шторы в салоне лучше чем покупать готовые [url=https://rimskie-salon-vs-gotovye.ru/]почему римские шторы в салоне лучше чем покупать готовые[/url] .
Cross Stitch Pattern in PDF format <a href=https://cross-stitch-patterns-free-download.store/>https://cross-stitch-patterns-free-download.store/</a> a perfect choice for embroidery lovers! Unique designer chart available for instant download right after purchase.
Consider the Dubai Free Zones as your opportunity for seamless immigration [url=http://longlive.com/node/7787]http://longlive.com/node/7787[/url]
Вы можете рассчитывать на эффективные услуги по диагностике, ремонту и заправке кондиционеров [url=https://holod.by/284/uslugi/zamena-podshipnika-avtokondicionera.html]Замена подшипника автокондиционера[/url]
Центр профессионального ухода за пожилыми "Радость жизни" [url=https://angelladydety.getbb.ru/viewtopic.php?f=65&t=37786&view=unread]https://angelladydety.getbb.ru/viewtopic.php?f=65&t=37786&view=unread[/url]
Residents of the Philippines, take note: the 20Bet promo code MAX300 [url=https://www.imdb.com/list/ls599761618/]https://www.imdb.com/list/ls599761618/[/url]
Надёжная фурнитура <a href=https://furnitura-dla-okon.ru/>https://furnitura-dla-okon.ru</a> для пластиковых окон: всё для ремонта и комплектации. От ручек до многозапорных механизмов.
https://xnudes.app/
TGDIGITAL – комплексное продвижение Telegram-каналов и чатов под ключ для любого законного бизнеса и тематики [url=https://tgdigital.ru/]как сделать инвайтинг в Телеграм[/url]
Мы создадим оптимальную стратегию для продвижения вашего бизнеса в Telegram [url=https://tgdigital.ru/]tgdigital.ru продвижение каналов[/url]
This means that they are available 24 hours a day and you can contact them for help [url=http://jakarta.pks.id/mobil-pks-kultwit-penjelasan-mahfudzsiddiq/#comment-204941]http://jakarta.pks.id/mobil-pks-kultwit-penjelasan-mahfudzsiddiq/#comment-204941[/url]
Заказать авторские букеты цветов с круглосуточной и бесплатной доставкой [url=https://buketi-zakaz.ru/]цветы рядом доставка москва[/url]
Think the fun stops at the welcome bonus? Think again [url=https://www.imdb.com/list/ls599725416/]https://www.imdb.com/list/ls599725416/[/url]
<a href=https://spin-better.net/>porno xxx hot</a>
Entfernen von Tapeten, Putz oder Fliesen an Wanden; Demontage der Medienversorgungen, wie Luftungs- und Rohrleitungen und Kabel; Beraumung und Entsorgung [url=https://demontagen-entkernungen.de/demontage/]demontage arbeiten Bayern[/url]
We've curated a list of the best low-cost small business ideas and essential tips [url=https://justpaste.me/business-setup-consultants-in-Dubai]business setup in dubai[/url]
трансфер прага <a href=https://inotur.com/strany-sng/5896-kak-dobratsya-iz-aeroporta-pragi-v-otel-udobnye-resheniya-ot-letisteexpress.html>русское такси прага</a>
займу онлайн на карту <a href=https://mfo-online-zaymi.ru/>кредит 365</a>
хотите сделать утепление <a href=http://www.stroyip.ru/article/1525/11708.html>http://www.stroyip.ru/article/1525/11708.html</a>
https://pokerdom.today/
В нашем магазине вы найдете лучшие Undetected читы для Escape From Tarkov [url=https://pkzsk.info/pochemu-wh-satano-luchshie-chity-dlya-escape-from-tarkov/]https://pkzsk.info/pochemu-wh-satano-luchshie-chity-dlya-escape-from-tarkov/[/url]
Срочный микрозайм <a href=https://truckers-money.ru/>https://truckers-money.ru</a> круглосуточно: оформите онлайн и получите деньги на карту за считаные минуты. Без звонков, без залога, без лишних вопросов.
Срочные микрозаймы <a href=https://stuff-money.ru/>https://stuff-money.ru</a> с моментальным одобрением. Заполните заявку онлайн и получите деньги на карту уже сегодня. Надёжно, быстро, без лишней бюрократии.
Discover <a href=https://www.savin-kuk.me/>Savin Kuk savin kuk</a>, a picturesque corner of Montenegro. Skiing, hiking, panoramic views and the cleanest air. A great choice for a relaxing and active holiday.
https://xn----7sbfkbe0dyb.xn--p1ai
An extremely hardcore game, Escape from Tarkov aims to provide players [url=https://pkzsk.info/pochemu-wh-satano-luchshie-chity-dlya-escape-from-tarkov/]https://pkzsk.info/pochemu-wh-satano-luchshie-chity-dlya-escape-from-tarkov/[/url]
<a href="https://sovtehnika.ru/casino/pinco.html">Казино Pinco слот Alexander the Great World Conqueror</a>
Онлайн займы срочно <a href=https://moon-money.ru/>https://moon-money.ru</a> деньги за 5 минут на карту. Без справок, без звонков, без отказов. Простая заявка, моментальное решение и круглосуточная выдача.
Unlock exclusive rewards with the latest Melbet promo code for 2026 [url=https://www.craigslistdir.org/melbet-promo-code_393015.html]https://www.craigslistdir.org/melbet-promo-code_393015.html[/url]
Это игра стрелялка основанная на максимальной реалистичности игрового геймплея [url=https://rusdigi.org/news/chity-dlya-rainbow-six-siege-deadlock-i-scum-preimushestvo-v-igre.html]https://rusdigi.org/news/chity-dlya-rainbow-six-siege-deadlock-i-scum-preimushestvo-v-igre.html[/url]
ремонт стиральной машины вирпул <a href=https://remontstiralki-na-domu.ru/>ремонт стиральных машин канди</a>
ремонт стиральных машин miele <a href=https://remont-stiralka-help.ru/>номер телефона ремонт стиральных машин</a>
Hindi News <a href=https://tfipost.in/>https://tfipost.in</a> latest news from India and the world. Politics, business, events, technology and entertainment - just the highlights of the day.
Mountain Topper <a href=https://www.lnrprecision.com/>https://www.lnrprecision.com</a> transceivers from the official supplier. Compatibility with leading brands, stable supplies, original modules, fast service.
New AI generator <a href=https://nsfw-ai.net/>ai nsfw generator</a> of the new generation: artificial intelligence turns text into stylish and realistic image and videos.
Melbet stands out with its vast sports betting markets [url=https://www.avnupparwahi.edu.in/profile/melbetpromo73552/profile]https://www.avnupparwahi.edu.in/profile/melbetpromo73552/profile[/url]
Animal Feed <a href=https://pvslabs.com/>https://pvslabs.com</a> Supplements in India: Vitamins, Amino Acids, Probiotics and Premixes for Cattle, Poultry, Pigs and Pets. Increased Productivity and Health.
Производим уходовую SPA-косметику, используя эфирные масла и натуральные ингредиенты, большинство из которых - эндемики Байкала [url=https://terrua.ru/tpost/8smau7yv51-kak-zapustit-kosmeticheskii-brend-vistra]открытие косметического производства[/url]
ремонт стиральных машин сименс <a href=https://remontstiralok-online.ru/>ремонт стиральных машин бош</a>
Пройти обследование на медкнижку можно с ПН по ПТ с 9:00 до 18:00 во всех центрах [url=https://dentaleclinic.ru/]медицинская книжка в день обращения[/url]
Как оформить карту <a href=https://vc.ru/money/2028014-kak-oformit-inostrannuyu-bankovskuyu-kartu-onlajn-iz-rossii-v-2025-godu>карта банка из Киргизии</a> для россиян в 2025 году. Зарубежную банковскую карту можно открыть и получить удаленно онлайн с доставкой в Россию и другие страны. Карты подходят для оплаты за границей.
Dolacz do Vavada PL i zagraj w topowe gry kasynowe online [url=https://psycholog-rudnik.pl/100fs-bez-depozytu/]100 darmowych spinów bez depozytu[/url]
В современном мире онлайн-казино стали очень популярными, и каждый день появляются новые платформы, предлагающие разнообразные игры и привлекательные бонусы [url=https://streamers-play.info/]Какое казино стримит evelone[/url]
Если вы ищете казино, где можно начать играть с минимальным депозитом в 100 рублей, то мы подготовили для вас обзор лучших онлайн-казино, которые предлагают такие возможности [url=https://100rub-casinos.info/]https://100rub-casinos.info/[/url]
Entdecken Sie die Deutsche Online Casinos fur ein faires Spielerlebnis [url=https://de-onlinecasinos.com/casino/vulkan-spiele-casino/]vulkan spiele casino[/url]
•очешь продать авто? <a href=https://t.me/s/magicalauto>telegram канал продажа и выкуп авто</a>
The Inter Milan striker has cemented his position as one of Europe's most lethal goalscorers [url=https://plinko2game.com]https://plinko2game.com[/url]
Медицинский центр <a href=https://s-klinika.ru/>https://s-klinika.ru</a> с современным оборудованием и опытными врачами. Диагностика, лечение, профилактика — взрослым и детям.
Производство и монтаж <a href=https://verspk.ru/>https://verspk.ru</a> инженерных и технологических систем для промышленных объектов.
When the symbol selection is activated in the bonus game [url=https://starburst2slots.com]https://starburst2slots.com[/url]
LEBO Coffee <a href=https://lebo.ru/>https://lebo.ru</a> натуральный кофе премиум-качества. Зерновой, молотый, в капсулах. Богатый вкус, аромат и свежая обжарка. Для дома, офиса и кофеен.
Gymnastics Hall of Fame <a href=https://usghof.org/>https://usghof.org</a> Biographies of Great Athletes Who Influenced the Sport. A detailed look at gymnastics equipment, from bars to mats.
создать сайт через нейросеть <a href=https://sozday-sayt-s-ai.ru/>https://sozday-sayt-s-ai.ru</a>
Быстрый рост канала – залог успеха в Telegram, но органическое продвижение часто требует слишком много времени [url=https://vc.ru/services/1876178-nakrutka-podpischikov-telegram-top-10-servisov-kupit-zhivyh-ili-botov]бесплатная накрутка подписчиков тг[/url]
Spend a few days on the Vaud Riviera and benefit [url=]https://rennerusa.com[/url]
The selection includes slots from Thunderkick, Pragmatic Play, Yggdrasil Gaming and other [url=https://lecapsole.com/]https://lecapsole.com/[/url]
Финансовый кризис — это не только экономическая проблема, но и серьезное испытание для семейных отношений [url=https://zanmsk.ru/obrazovanie-v-sfere-bankrotstva-vostrebovannost-i-perspektivy-karery/]https://zanmsk.ru/obrazovanie-v-sfere-bankrotstva-vostrebovannost-i-perspektivy-karery/[/url]
клиника здоровье <a href=https://www.klinika-chernogoriya.me/>клиника</a>
orthopedic clinic near me <a href=https://www.hospital-montenegro.me/>Tivat hospital</a>
A franchise consisting of several action films released since 1996 [url=https://mastergradperm.ru/]миссия невыполнима онлайн[/url]
Lately I have been seeing more and more 1xBet ads [url=https://rekforum.ru/viewtopic.php?t=43102]https://rekforum.ru/viewtopic.php?t=43102[/url]
Виртуальные номера для Telegram <a href=https://basolinovoip.com/>https://basolinovoip.com</a> создавайте аккаунты без SIM-карты. Регистрация за минуту, широкий выбор стран, удобная оплата. Идеально для анонимности, работы и продвижения.
Odjeca i aksesoari za hotele <a href=https://www.hotelska-posteljina-damast.me/>hotelski program</a> po sistemu kljuc u ruke: uniforme za sobarice, recepcionere, SPA ogrtaci, papuce, peskiri. Isporuke direktno od proizvodaca, stampa logotipa, jedinstveni stil.
Watch online movie Mission: Impossible All Parts [url=https://irkutskhostel.ru/]миссия невыполнима 3 онлайн[/url]
Онлайн-платформа для автоматизации рабочих процессов и взаимодействия между отделами и сотрудниками компании [url=https://blog.themarfa.name/obzor-siervisa-sbis-dlia-upravlieniia-biznies-protsiessami/]внутренний электронный документооборот[/url]
доставка суши барнаул <a href=https://www.hospital-montenegro.me/>суши барнаул каталог</a>
Сеть цветочных магазинов в Крыму КУПИ БУКЕТ занимается быстрой доставкой цветов по всему Крыму, самый большой ассортимент цветов и самая быстрая доставка [url=https://xn----btbmjjd5a3ace.xn--p1acf/]Купить букет цветов в Севастополе[/url]
Лицензированное казино предлагает огромный выбор игр, включая популярные слоты [url=https://androsovo.ru/]миссия невыполнима 2 онлайн[/url]
Магазин брендовых кроссовок <a href=https://kicksvibe.ru/>https://kicksvibe.ru</a> Nike, Adidas, New Balance, Puma и другие. 100% оригинал, новые коллекции, быстрая доставка, удобная оплата. Стильно, комфортно, доступно!
заказать суши в барнауле <a href=https://sushi-barnaul.ru/>заказать суши в барнауле</a>
лучшие сайты казино <a href=https://t.me/toplistcasinos>русские казино онлайн</a>
Миссия невыполнима - это зрелищная серия боевиков, в которой Этан Хант, высококвалифицированный агент IMF [url=https://lotoclubkz-online.com/]миссия невыполнима онлайн[/url]
Watch Movie Mission Impossible team embark on their most [url=http://russian-heritage.ru/]миссия невыполнима онлайн[/url]
[u][b]We are rushing to your relief[/b][/u]—a unit among professionals who will rapidly repair some consequences of an plumbing urgency within your apartment!
[u][b]Their fast reaction[/b][/u] - this answer towards decreasing our fees of certain future significant repairs!
[url=https://5.gp/b31q6i3y][b]Feel our speed alongside quality among service right now![/b][/url]
Усыпление и кремация кошек и собак в Санкт-Петербурге [url=https://veterinarnayaclinica.ru/]Ветклиника в санкт-петербурге[/url]
Modern operations <a href=https://www.surgery-montenegro.me/>https://www.surgery-montenegro.me</a> innovative technologies, precision and safety. Minimal risk, short recovery period. Plastic surgery, ophthalmology, dermatology, vascular procedures.
Профессиональное <a href=https://prp-expert.ru/>https://prp-expert.ru</a>: PRP, Plasmolifting, протоколы и нюансы проведения процедур. Онлайн курс обучения плазмотерапии.
Онлайн-курсы <a href=https://obuchenie-plasmoterapii.ru/>prp терапия обучение</a>: теория, видеоуроки, разбор техник. Обучение с нуля и для практикующих. Доступ к материалам 24/7, сертификат после прохождения, поддержка преподавателя.
Watch online video Mission Impossible 4 Ghost Protocol 2011 on the channel [url=https://mbdou234.ru/]миссия невыполнима 4 онлайн[/url]
Seit vielen Jahren stehen Elfa Pods fur zuverlassige Qualitat [url=https://sites.google.com/view/elfa-pods-kompatiebl/home]Elfa pods[/url]
the best and interesting <a href=https://www.jec.qa/>https://www.jec.qa</a>
interesting and new <a href=https://www.panamericano.us/>https://www.panamericano.us</a>
best site online <a href=https://playplayfun.com/>https://playplayfun.com</a>
visit the site online <a href=https://www.amakmeble.pl/>https://www.amakmeble.pl</a>
Dolacz do GG Bet Polska i swiat legalnych gier hazardowych online [url=https://hejmo.pl/recenzje-ggbet/]kasynie online[/url]
сли вам нужно купить шатры в Минске, наш каталог предлагает лучшие решения для бизнеса [url=https://planeta-r.by/palatki_torgovyie_i_sadovyie_.html~183]палатка торговая купить[/url]
visit the site <a href=https://underatexassky.com/>https://underatexassky.com</a>
go to the site <a href=https://petitedanse.com.br/>https://petitedanse.com.br</a>
Профессиональная <a href=https://narkologicheskaya-klinika43.ru/>наркологическая клиника казань</a>. Лечение зависимостей, капельницы, вывод из запоя, реабилитация. Анонимно, круглосуточно, с поддержкой врачей и психологов.
Рефрижераторные перевозки <a href=https://msk-news.net/other/2025/03/29/637040.html>https://msk-news.net/other/2025/03/29/637040.html</a> по России и СНГ. Контроль температуры от -25°C до +25°C, современные машины, отслеживание груза.
Выбирайте казино <a href=https://casinopiastrix.ru/>пиастрикс казино</a> с оплатой через Piastrix — это удобно, безопасно и быстро! Топ-игры, лицензия, круглосуточная поддержка.
Ищете казино <a href=https://sbpcasino.ru/>казино с СБП</a>? У нас — мгновенные переводы, слоты от топ-провайдеров, живые дилеры и быстрые выплаты. Безопасность, анонимность и мобильный доступ!
Компания Chipik.BY специализируется на изготовлении ключей в Минске [url=https://vesiskitim.ru/2021/01/29/185338-proizvodstvo-i-izgotovlenie-klyuchej]https://vesiskitim.ru/2021/01/29/185338-proizvodstvo-i-izgotovlenie-klyuchej[/url]
Хирurgija u Crnoj Gori <a href=https://www.hirurgija-crna-gora.me/>https://www.hirurgija-crna-gora.me</a> savremena klinika, iskusni ljekari, evropski standardi. Planirane i hitne operacije, estetska i opsta hirurgija, udobnost i bezbjednost.
Fifty Shades of Grey (2015 ) is based on the best-selling novel of the same name by Erica Leonard James [url=https://www.vdsv.ru/]50 оттенков серого смотреть онлайн[/url]
Start playing for real money and win big sums in top slot machines [url=https://jackpot666vodka.ru/]водка казино[/url]
The film reveals the confrontation between Blade and the vampire Deacon Frost [url=https://mytsrcn.ru/]блейд смотреть онлайн[/url]
Смотреть фильмы <a href=https://kinobadi.mom/>kinobadi.mom</a> и сериалы бесплатно, самый большой выбор фильмов и сериалов , многофункциональное сортировка, также у нас есть скачивание в mp4 формате
Выбор застройщика <a href=https://spartak-realty.ru/>https://spartak-realty.ru</a> важный шаг при покупке квартиры. Расскажем, как проверить репутацию, сроки сдачи, проектную документацию и избежать проблем с новостройкой.
Недвижимость в Балашихе <a href=https://balashihabest.ru/>https://balashihabest.ru</a> комфорт рядом с Москвой. Современные жилые комплексы, школы, парки, транспорт. Объекты в наличии, консультации, юридическое сопровождение сделки.
Поставка нерудных материалов <a href=https://sr-sb.ru/>https://sr-sb.ru</a> песок, щебень, гравий, отсев. Прямые поставки на стройплощадки, карьерный материал, доставка самосвалами.
Лайфхаки для ремонта <a href=https://stroibud.ru/>https://stroibud.ru</a> квартиры и дома: нестандартные решения, экономия бюджета, удобные инструменты.
Женский журнал <a href=https://e-times.com.ua/>https://e-times.com.ua</a> о красоте, моде, отношениях, здоровье и саморазвитии. Советы, тренды, рецепты, вдохновение на каждый день. Будь в курсе самого интересного!
Туристический портал <a href=https://atrium.if.ua/>https://atrium.if.ua</a> всё для путешественников: путеводители, маршруты, советы, отели, билеты и отзывы. Откройте для себя новые направления с полезной информацией и лайфхаками.
Женский онлайн-журнал <a href=https://socvirus.com.ua/>https://socvirus.com.ua</a> мода, макияж, карьера, семья, тренды. Полезные статьи, интервью, обзоры и вдохновляющий контент для настоящих женщин.
Портал про ремонт <a href=https://prezent-house.com.ua/>https://prezent-house.com.ua</a> полезные советы, инструкции, дизайн-идеи и лайфхаки. От черновой отделки до декора. Всё о ремонте квартир, домов и офисов — просто, понятно и по делу.
Всё о ремонте <a href=https://sevgr.org.ua/>https://sevgr.org.ua</a> на одном портале: полезные статьи, видеоуроки, проекты, ошибки и решения. Интерьерные идеи, советы мастеров, выбор стройматериалов.
Портал про ремонт <a href=https://techproduct.com.ua/>https://techproduct.com.ua</a> для тех, кто строит, переделывает и обустраивает. Рекомендации, калькуляторы, фото до и после, инструкции по всем этапам ремонта.
Бюро дизайна <a href=https://sinega.com.ua/>https://sinega.com.ua</a> интерьеров: функциональность, стиль и комфорт в каждой детали. Предлагаем современные решения, индивидуальный подход и поддержку на всех этапах проекта.
Портал о строительстве <a href=https://bms-soft.com.ua/>https://bms-soft.com.ua</a> от фундамента до кровли. Технологии, лайфхаки, выбор инструментов и материалов. Честные обзоры, проекты, сметы, помощь в выборе подрядчиков.
Ремонт и строительство <a href=https://mtbo.org.ua/>https://mtbo.org.ua</a> всё в одном месте. Сайт с советами, схемами, расчетами, обзорами и фотоидееями. Дом, дача, квартира — строй легко, качественно и с умом.
The color palette and patterns of the packaging are the first thing that catches the eye [url=https://telegra.ph/Korporativnye-podarki-s-logotipom-kak-usilit-brend-cherez-sladosti-07-11]https://telegra.ph/Korporativnye-podarki-s-logotipom-kak-usilit-brend-cherez-sladosti-07-11[/url]
Сайт о ремонте <a href=https://sota-servis.com.ua/>https://sota-servis.com.ua</a> и строительстве: от черновых работ до декора. Технологии, материалы, пошаговые инструкции и проекты.
Онлайн-журнал <a href=https://elektrod.com.ua/>https://elektrod.com.ua</a> о строительстве: технологии, законодательство, цены, инструменты, идеи. Для строителей, архитекторов, дизайнеров и владельцев недвижимости.
Женские новости <a href=https://biglib.com.ua/>https://biglib.com.ua</a> каждый день: мода, красота, здоровье, отношения, семья, карьера. Актуальные темы, советы экспертов и вдохновение для современной женщины.
Все главные женские <a href=https://pic.lg.ua/>https://pic.lg.ua</a> новости в одном месте! Мировые и российские тренды, стиль жизни, психологические советы, звёзды, рецепты и лайфхаки.
Женский онлайн-журнал <a href=https://bestwoman.kyiv.ua/>https://bestwoman.kyiv.ua</a> для тех, кто ценит себя. Мода, уход, питание, мотивация и женская энергия в каждой статье.
Портал о строительстве <a href=https://ateku.org.ua/>https://ateku.org.ua</a> и ремонте: от фундамента до крыши. Пошаговые инструкции, лайфхаки, подбор материалов, идеи для интерьера.
Строительный портал <a href=https://avian.org.ua/>https://avian.org.ua</a> для профессионалов и новичков: проекты домов, выбор материалов, технологии, нормы и инструкции.
Строительный сайт <a href=https://diasoft.kiev.ua/>https://diasoft.kiev.ua</a> всё о строительстве и ремонте: пошаговые инструкции, выбор материалов, технологии, дизайн и обустройство.
Журнал о строительстве <a href=https://kennan.kiev.ua/>https://kennan.kiev.ua</a> новости отрасли, технологии, советы, идеи и решения для дома, дачи и бизнеса. Фото-проекты, сметы, лайфхаки, рекомендации специалистов.
На строительном сайте <a href=https://eeu-a.kiev.ua/>https://eeu-a.kiev.ua</a> вы найдёте всё: от выбора кирпича до дизайна спальни. Актуальная информация, фото-примеры, обзоры инструментов, консультации специалистов.
Сайт о строительстве <a href=https://domtut.com.ua/>https://domtut.com.ua</a> и ремонте: практичные советы, инструкции, материалы, идеи для дома и дачи.
Sewage pumping stations (SPS) are engineering hydraulic structures designed [url=https://kns-kupit.ru/]канализационные насосные станции производство[/url]
Сайт о ремонте <a href=https://mia.km.ua/>https://mia.km.ua</a> и строительстве — полезные советы, инструкции, идеи, выбор материалов, технологии и дизайн интерьеров.
Сайт о ремонте <a href=https://rusproekt.org/>https://rusproekt.org</a> и строительстве: пошаговые инструкции, советы экспертов, обзор инструментов, интерьерные решения.
Всё для ремонта <a href=https://zip.org.ua/>https://zip.org.ua</a> и строительства — в одном месте! Сайт с понятными инструкциями, подборками товаров, лайфхаками и планировками.
Автомобильный портал <a href=https://just-forum.com/>https://just-forum.com</a> всё об авто: новости, тест-драйвы, обзоры, советы по ремонту, покупка и продажа машин, сравнение моделей.
резка металла лазером цена <a href=https://lazernaya-rezka-msk.ru/>лазерный раскрой листового металла</a>
Полезный сайт для ремонта <a href=https://rvps.kiev.ua/>https://rvps.kiev.ua</a> и строительства: от черновых работ до отделки и декора. Всё о планировке, инженерных системах, выборе подрядчика и обустройстве жилья.
Онлайн-портал <a href=https://spkokna.com.ua/>https://spkokna.com.ua</a> для современных родителей: беременность, роды, уход за малышами, школьные вопросы, советы педагогов и врачей.
Современный женский журнал <a href=https://superwoman.kyiv.ua/>https://superwoman.kyiv.ua</a> стиль, успех, любовь, уют. Новости, идеи, лайфхаки и мотивация для тех, кто ценит себя и своё время.
Сайт для женщин <a href=https://womanfashion.com.ua/>https://womanfashion.com.ua</a> которые ценят себя и своё время. Мода, косметика, вдохновение, мотивация, здоровье и гармония.
Женский онлайн-журнал <a href=https://abuki.info/>https://abuki.info</a> мода, красота, здоровье, психология, отношения и вдохновение. Полезные статьи, советы экспертов и темы, которые волнуют современных женщин.
Современный авто портал <a href=https://simpsonsua.com.ua/>https://simpsonsua.com.ua</a> автомобили всех марок, тест-драйвы, лайфхаки, ТО, советы по покупке и продаже. Для тех, кто водит, ремонтирует и просто любит машины.
Онлайн авто портал <a href=https://sedan.kyiv.ua/>https://sedan.kyiv.ua</a> для автолюбителей и профессионалов. Новинки автоиндустрии, цены, характеристики, рейтинги, покупка и продажа автомобилей, автофорум.
Актуальные новости <a href=https://uapress.kyiv.ua/>https://uapress.kyiv.ua</a> на одном портале: события России и мира, интервью, обзоры, репортажи. Объективно, оперативно, профессионально. Будьте в курсе главного!
JoyCasino — популярное онлайн-казино с широким выбором слотов [url=https://facetoshi.live/blogs/12102/Ртикет-РІ-наземных-казино-правила-поведения]https://facetoshi.live/blogs/12102/Ртикет-РІ-наземных-казино-правила-поведения[/url]
Нужна помощь в устранении небольших недочетов или проведении мелкого ремонта [url=https://krasnodar.rukizolotye.ru/]мастер на час Краснодар[/url]
Современный мужской портал <a href=https://kompanion.com.ua/>https://kompanion.com.ua</a> полезный контент на каждый день. Новости, обзоры, мужской стиль, здоровье, авто, деньги, отношения и лайфхаки без воды.
Новости Украины <a href=https://pto-kyiv.com.ua/>https://pto-kyiv.com.ua</a> и мира сегодня: ключевые события, мнения экспертов, обзоры, происшествия, экономика, политика.
Сайт для женщин <a href=https://storinka.com.ua/>https://storinka.com.ua</a> всё о моде, красоте, здоровье, психологии, семье и саморазвитии. Полезные советы, вдохновляющие статьи и тренды для гармоничной жизни.
Следите за событиями <a href=https://kiev-pravda.kiev.ua/>https://kiev-pravda.kiev.ua</a> дня на новостном портале: лента новостей, обзоры, прогнозы, мнения. Всё, что важно знать сегодня — быстро, чётко, объективно.
Новостной портал <a href=https://thingshistory.com/>https://thingshistory.com</a> для тех, кто хочет знать больше. Свежие публикации, горячие темы, авторские колонки, рейтинги и хроники. Удобный формат, только факты.
кулинарный мастер-класс <a href=https://svoi-culinary-club.ru/>фуршет Воронеж</a>
мирена спираль форум <a href=https://spiral-mirena1.ru/>спираль мирена</a>
https://uztm-ural.ru/catalog/tugoplavkie-metally/
ремонт бака стиральной машины <a href=https://remont-stiralka-help.ru/>ремонт стиральных машин цены</a>
ремонт стиральных машин адреса <a href=https://remontstiralki-na-domu.ru/>ремонт стиральных машин lg</a>
Call a home repairman - how much does it cost on [url=https://krasnodar.rukizolotye.ru/]мастер на час[/url]
Вы когда-нибудь задумывались, как быстро и легко найти точное значение слова [url=https://dontsova-books.ru/tolkovye-slovari/]https://dontsova-books.ru/tolkovye-slovari/[/url]
Spending hours choosing what to watch [url=https://www.vdsv.ru/]блейд смотреть онлайн[/url]
Safe <a href=https://monicablaire.com>pinco apk</a> download!
<a href=https://brainhire.ru/>искусственный интеллект в управлении персоналом</a>
<a href=https://cazinonarubli.ru/>Игровые аппараты на деньги</a>
A Russian special-purpose missile submarine disappears without a trace during a secret mission [url=https://lkraa35.cc]кракен переходник ссылка[/url]
Hello men
Hello. A 18 very cool site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://appsandapplications.com/power-guzzlers-avoid-these-mistakes-to-save-your-smartphone-battery/>https://thinkcomputers.org/what-makes-your-computer-fast-or-slow/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello men
Hello. A 18 very cool site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://appsandapplications.com/power-guzzlers-avoid-these-mistakes-to-save-your-smartphone-battery/>https://thinkcomputers.org/what-makes-your-computer-fast-or-slow/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A 18 perfect site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://www.sportsgossip.com/travel-sickness-these-tips-and-home-remedies-really-help/>https://www.arcyart.com/blog/2023/08/07/glasgow-a-magnificent-scottish-city-you-need-to-visit/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A 18 perfect site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://www.sportsgossip.com/travel-sickness-these-tips-and-home-remedies-really-help/>https://www.arcyart.com/blog/2023/08/07/glasgow-a-magnificent-scottish-city-you-need-to-visit/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A 18 perfect site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://www.sportsgossip.com/travel-sickness-these-tips-and-home-remedies-really-help/>https://www.arcyart.com/blog/2023/08/07/glasgow-a-magnificent-scottish-city-you-need-to-visit/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello !
Hi. A 18 perfect site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://www.sportsgossip.com/travel-sickness-these-tips-and-home-remedies-really-help/>https://www.arcyart.com/blog/2023/08/07/glasgow-a-magnificent-scottish-city-you-need-to-visit/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello colleagues
Hello. A 18 cool site 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://newyorkspaces.com/the-storied-history-of-the-louvre-pariss-crown-jewel/>https://www.newscase.com/interesting-water-parks-from-all-over-the-world/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello .
Hello. A 18 fine site 1 that I found on the Internet.
Check out this website. There's a great article there. <a href=https://www.visitfashions.com/womens-clothing-fashion-for-summer/>http://www.iplayapps.de/so-schuetzt-man-kinder-beim-spielen-auf-apple-geraeten-tipps-37580/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
<a href=https://htmlprof.ru/>раскрутка сайта цены</a>
Hello men
Hi. A 18 fine website 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://factnewsph.com/2023/08/smart-home-gadgets-the-future-of-modern-living.html>https://tvboxbee.com/harnessing-the-power-of-visuals-a-guide-to-effective-communication/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
[url=https://dtcc.edu.vn/]kraken актуальные ссылки[/url]
[url=https://dtcc.edu.vn/]kraken онион тор[/url]
https://sngmedia.vip/
<a href=https://ishq.de/>кракен даркнет</a>
הגב, הידיים היו עוברות לצוואר, מחזיקות אותה ומרימות אותה למעלה כדי לנשוך את אוזנה, לנשק את שפתיה, שהסטירה. - אה! - היא צעקה, אבל מיד גנחה כשהוא הכניס את הזין מאחור. עכשיו הוא זיין אותה ללא <a href=https://milfxxx4k.com/>סקס דיסקרטי</a>
В следующем месяце экзамены,
а вы всё ещё сомневаетесь, с чего
начать?
Онлайн-курсы по ЕГЭ по литературе — уже стартовали!
Вас обучают репетиторы с высоким рейтингом.
Что входит в курс:
- Практика по всем темам
- Домашние задания с проверкой
- Обратная связь 24/7
- Тренировка на реальных заданиях
Занятия: на собственной платформе — можно смотреть в записи.
Не упустите шанс!
Запись тут: литература100
<a href=https://pena-montazhnaya.ru/>https://pena-montazhnaya.ru/</a>
<a href=https://www.colabinc.com/>blacksprut onion</a>
<a href=https://spinbetter.link/>porno</a>
<a href=https://www.glicol.ru/>https://www.glicol.ru/</a>
Современные канализационные насосные станции – надёжное решение для вашего объекта! Предлагаем КНС любой мощности с автоматикой и защитой от засоров. Автоматическое управление, высокая производительность, долговечность материалов. Решаем задачи от частных домов до промышленных объектов. Гарантия качества и быстрая доставка, подробнее тут: <a href=https://kns-kupit.ru/>https://kns-kupit.ru/</a>
<a href=https://b2b-tech.ru/>https://b2b-tech.ru/</a>
<a href=https://www.object-store.de/>Mega darknet</a>
בחיוך מרוצה. גם הוא שמע. כן, עיסוי ארוטי כזה קשה לא לשמוע. כנראה שהטעינה שלהם התקרבה לגמר, כך גרם לתומאס לעשות זאת. היא שאלה אותו מדוע הוא עשה זאת ותומאס סיפר לה על אהבתו. ואז אליזבת ריחמה <a href=https://sextubehd.net/>like this</a>
Простой способ быть на связи — рабочий адрес , <a href=https://y2kra.cc>кракен меф</a> который открывается всегда. Проверено лично.
<a href=https://y2kra.cc>кракен ссылка официальная</a> 2025 доступ есть, работает без проблем. Если нужно прямо сейчас — преходи по ссылке, не тупи.
Актуальные тренды сегодня <a href=https://jb5.ru/>подробнее</a>: фото, видео и медиа. Всё о том, что популярно сегодня — в России и в мире. Мода, визуальные стили, digital-направления и соцсети. Следите за трендами и оставайтесь в курсе главных новинок каждого дня.
לא היה אכפת לי. הוא הצמיד אותי לקיר והתחלנו להתנשק. שפתיו נוקשות, לשונו חצופה, הוא נשך בי ישר, מתנקז כשאני יוצא ואני רואה אותו זורם במורד ירכה, מתערבב עם הלחות שלה. אני נופל ליד, מתנשף, והיא <a href=https://lazytubeporn.com/>the full report</a>
Нужен буст в игре? <a href=https://duneshop.ru/>купить оружие dune awakening</a> легендарная броня, костюмы, скины и уникальные предметы. Всё для выживания на Арракисе!
<a href=https://www.object-store.de/>Мега сайт</a>
Among the films , you can find experimental films shot outside all canons [url=https://smr02.ru/]бесславные ублюдки смотреть онлайн[/url]
Официальный сайт <a href=https://y2kra.cc>маркет кракен</a> . Удобно и надёжно. Иногда это всё, что нужно. Рабочая ссылка уже тут.
Зашёл на <a href=https://y2kra.cc>кра36</a> официальное зеркало, проверил — всё на месте, работает. Подключайся, пока адрес сайта активен.
Хватит терять время на поиски <a href=https://y2kra.cc>кракен сайт вход</a>. Всё, что нужно, уже перед тобой. Адрес работает, соединение стабильное, вход без лишнего шума.
חפציו, ואיחל לשלום בהצלחה, עזב. אתה בסדר? שאל ד ' את אשתו כשיצאה מהמקלחת. - אני לא יודע-היא מה את עושה ... למה ... אני לא יכולה ... אני נשואה ... מרינה גונחת, מבינה שבעלה מעולם לא עשה כל כך <a href=https://xxxultrahd.net/>זונות רוסיות</a>
Discover rafting <a href=https://www.tara-montenegro-rafting.me/>https://www.tara-montenegro-rafting.me</a> – the perfect holiday for nature lovers and extreme sports enthusiasts. The UNESCO-listed Tara Canyon will amaze you with its beauty and energy.
Продвижение социальных сетей https://vc.ru/smm-promotion
Зашёл на <a href=https://y2kra.cc>kra35</a> официальное зеркало, проверил — всё на месте, работает. Подключайся, пока адрес сайта активен.
<a href=https://www.reumatologia.org.br/>kraken darknet ссылка</a>
Если ищеш <a href=https://y2kra.cc>кракен тор зеркало</a> или зеркало, которая просто работает — поздравляю, ты нашел. Подключайся и пользуйся.
Гидроизоляция зданий <a href=https://gidrokva.ru/>https://gidrokva.ru</a> и сооружений любой сложности. Фундаменты, подвалы, крыши, стены, инженерные конструкции.
<a href=https://darica.bel.tr>kraken сайт</a>
Заказать дипломную работу <a href=https://diplomikon.ru>diplomikon.ru</a> недорого и без стресса. Выполняем работы по ГОСТ, учитываем методички и рекомендации преподавателя.
Официальный сайт <a href=https://y2kra.cc>сайт кракен онион ссылка</a> . Удобно и надёжно. Иногда это всё, что нужно. Рабочая ссылка уже тут.
Надоело натыкаться на нерабочие или фишинговые ссылки? <a href=https://y2kra.cc>kraken зеркало</a> попробуй этот вариант — он проверен и не подводит. Всё работает, как надо.
Come in – don’t miss the latest: <a href=https://www.manaolahawaii.com/>https://www.manaolahawaii.com</a>
Простой способ быть на связи — рабочий адрес , <a href=https://y2kra.cc>кракен как зайти</a> который открывается всегда. Проверено лично.
<a href=https://darica.bel.tr>kraken актуальные ссылки</a>
<a href=https://exponentphilanthropy.org/>Mega darknet</a>
This map provides a foundational view of the land where Jesus walked [url=https://www.wonderpartyrental.com/off-site-events]party stylist[/url]
<a href=https://exponentphilanthropy.org/>Mega darknet</a>
Editorial take: engagement holds up best when teams <a href=https://buffalonews.com/exclusive/article_3a7e34b2-e365-5562-87fc-933727e1cd2b.html>buy real twitter followers</a> and avoid big surges.
Устал от фейков и скама? Здесь всё иначе. <a href=https://y2kra.cc>сайт кракен онион ссылка</a> 2025. Один адрес — и ты на связи.
<a href=https://exponentphilanthropy.org/>Мега ссылка</a>
Для тех, кто ценит время: <a href=https://y2kra.cc>кракен маркет</a> работает стабильно, без лишнего шума и ошибок.
The Pari catalog contains 20+ sports for beginners and pros [url=https://www.imdb.com/list/ls4105500655/]https://www.imdb.com/list/ls4105500655/[/url]
Если ищеш <a href=https://y2kra.cc>кракен ссылка телеграм</a> или зеркало, которая просто работает — поздравляю, ты нашел. Подключайся и пользуйся.
How many years do you need to work [url=https://xseria.mobi/user/wufiySpoff/]https://xseria.mobi/user/wufiySpoff/[/url]
Иногда хочется просто открыть сайт <a href=https://y2kra.cc>кракен ссылка вход</a> и не думать о том, сработает он или нет. Здесь именно так. KRAKEN 2025
2. зайти в [url=https://yjspic.top/home.php?mod=space&uid=83896&do=profile&from=space]https://yjspic.top/home.php?mod=space&uid=83896&do=profile&from=space[/url] Кассу. 3. определиться с способ пополнения. они напоминают комнаты live игрового заведения, но за итогами тиража отвечает ГСЧ, но не реальный человек.
Иногда хочется просто открыть сайт <a href=https://y2kra.cc>кракен ссылка вход</a> и не думать о том, сработает он или нет. Здесь именно так. KRAKEN 2025
Иногда хочется просто открыть сайт <a href=https://y2kra.cc>маркет кракен</a> и не думать о том, сработает он или нет. Здесь именно так. KRAKEN 2025
Диплом под ключ <a href=https://diplomnazakaz-online.ru/>https://diplomnazakaz-online.ru</a> от выбора темы до презентации. Профессиональные авторы, оформление по ГОСТ, высокая уникальность.
Ты на шаг ближе к стабильному входу на <a href=https://y2kra.cc>кракен тор</a>. Адрес проверен, соединение защищено, всё просто. Актуальная информация всегда доступна.
Сайт предоставляет подробные инструкции по ремонту, демонтажу и установке бамперов для различных марок автомобилей [url=https://carsfunix.fandom.com/ru/wiki/%D0%91%D0%B0%D0%BC%D0%BF%D0%B5%D1%80]бампер[/url]
Cabinet IQ McKinney
3180 Eldorado Pkwy STE 100, McKinney,
TX 75072, Unites Ѕtates
(469) 202-6005
Laminate
<a href=https://spinbetterkh.com/>porno</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://redesip.org>blacksprut зеркала</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut <a href=https://alchemycreations.co.uk>blacksprut ссылка</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://colabinc.com>блэкспрут дакрнет</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://kimberlywylie.com>блэкспрут онион</a>
Лучшие и актуальные <a href=https://droptopsite2.ru/>промокоды на бесплатные ставки в слотах</a> в популярных букмекерских конторах. Бонусы за регистрацию, фрибеты, удвоение депозита. Обновления каждый день.
Ваш безопасный портал <a href=https://bitcoin7.ru/>bitcoin7.ru</a> в мир криптовалют! Последние новости о криптовалютах Bitcoin, Ethereum, USDT, Ton, Solana. Актуальные курсы крипты и важные статьи о криптовалютах. Начните зарабатывать на цифровых активах вместе с нами
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://poison-games.com>black sprout</a>
Всё о металлообработке <a href=https://j-metall.ru/>https://j-metall.ru</a> и металлах: технологии резки, сварки, литья, фрезеровки. Свойства металлов, советы для производства и хобби.
Этот британский документальный фильм показывает неприятные стороны новой эры [url=https://kinokrad.inc/110-konstantin-2-2025.html]Константин 2 смотреть онлайн[/url]
Only we have the newest materials: <a href=https://cere-india.org/>https://cere-india.org</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://poison-games.com>блэкспрут вход</a>
buy esim for india <a href=https://esim-buy1.com/>buy esim for iphone</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut <a href=https://alchemycreations.co.uk>блэк спрут</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://redesip.org>как зайти на blacksprut</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut <a href=https://alchemycreations.co.uk>блэкспрут вход</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://kimberlywylie.com>black sprout</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://kimberlywylie.com>blacksprut сайт</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://kimberlywylie.com>blacksprut com зеркало</a>
The main reason is often a lack of information about [url=https://radiocert.ru/incs/pgs/melbet_promokod___bonus_pri_registracii.html]https://radiocert.ru/incs/pgs/melbet_promokod___bonus_pri_registracii.html[/url]
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://kimberlywylie.com>blacksprut darknet</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut <a href=https://alchemycreations.co.uk>black sprout</a>
<a href=https://spinbetterkh.com/>porno teens double</a>
There are several ways to get the current Melbet promo code [url=https://promo-bonus.com/avis-bookmaker-1-win-et-code-promo/]https://promo-bonus.com/avis-bookmaker-1-win-et-code-promo/[/url]
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://poison-games.com>блэкспрут дакрнет</a>
porn video free <a href=https://catfee.io/>porn vk</a>
Нужен дом? <a href=https://stroitelstvo-domov-kazan1.ru/>строительство домов под ключ</a> — от проекта до отделки. Каркасные, кирпичные, брусовые, из газобетона. Гарантия качества, соблюдение сроков, индивидуальный подход.
Интересная статья: <a href=https://alwayswoman.com/ru/zdorove/pechen-sos-glavnye-priznaki-problem-kotorye-nelzya-ignorirovat/>Печень SOS: главные признаки проблем, которые нельзя игнорировать</a>
Читать полностью: <a href=https://autogrok.com/ru/avtovladeltsam/zhizn-v-dome-na-kolesah-5-let-svobody-i-priklyuchenij-na-dorogah-opyt-avtovladeltsa/>Жизнь в доме на колесах: 5+ лет свободы и приключений на дорогах (опыт автовладельца)</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://kimberlywylie.com>блэкспрут онион</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut
<a href=https://redesip.org>блэкспрут ссылка</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut <a href=https://alchemycreations.co.uk>блэкспрут не работает</a>
While the official list of participants for TI14 has [url=https://theinternational2025.com/the-international-2025-teams-to-watch-and-qualification-dynamics/]open qualifier ti 2025[/url]
<a href=https://object-store.de>Мега онион</a>
blacksprut
блэкспрут
black sprut
блэк спрут
blacksprut вход
блэкспрут ссылка
blacksprut ссылка
blacksprut onion
блэкспрут сайт
блэкспрут вход
блэкспрут онион
блэкспрут дакрнет
blacksprut darknet
blacksprut сайт
блэкспрут зеркало
blacksprut зеркало
black sprout
blacksprut com зеркало
блэкспрут не работает
blacksprut зеркала
как зайти на blacksprut <a href=https://alchemycreations.co.uk>blacksprut сайт</a>
An exciting and innovative online casino that attracts players [url=https://smr02.ru/]купить сиалис индийского производства[/url]
<a href=https://dtcc.edu.vn/>kraken актуальные ссылки</a>
<a href=https://spinbetter24.net/>black wife porno</a>
https://xnudes.ai/
Круглосуточное обновление: мировые и российские новости, факты, аналитика. “Сегодня в эфире”: чётко и по делу [url=https://www.newsefir.net/all-news]https://www.newsefir.net/all-news[/url]
Our micro-SaaS launch doc has a mid-page note—“after onboarding 30 users, <a href=https://intercom.help/graming/en/articles/11793747-9-best-sites-to-buy-twitter-x-followers-in-2025-real-fast-safe>buy 100 x followers</a> to strengthen social proof.”
We held off paid ads until after a controlled test to <a href=https://buffalonews.com/exclusive/article_76d1e70c-c87f-5d3b-aa96-e4f9812134a5.html>buy tiktok likes and views</a>; the baseline mattered.
After a few failed attempts with sketchy apps, I finally checked Reddit. It listed the <a href=https://www.reddit.com/r/GamingInsider/comments/1m1nt3p/best_gambling_site_need_online_casino/>best online slot sites</a> and I haven’t looked back since.
<a href=https://dtcc.edu.vn/>кракен ссылка onion</a>
Полезная статья: <a href=https://rstnews.com/yablochnyj-pirog-s-kremom-retsept-italyanskoj-klassiki-dlya-vashej-kuhni/>Яблочный пирог с кремом: рецепт итальянской классики для вашей кухни</a>
Читать подробнее: <a href=https://car-off.com/ru/avtovladeltsam/rejting-avtomobilej-samye-dovolnye-vladeltsy-vybirayut-eti-modeli/>Рейтинг автомобилей: самые довольные владельцы выбирают эти модели</a>
Go to the 1xBet platform or download the mobile application [url=][/url]
Читать статью: <a href=https://thewomansway.com/ru/zdorove/zdorove-zhenshhiny-gid-po-krasote-samochuvstviyu-i-dolgoletiyu/>Здоровье женщины: гид по красоте, самочувствию и долголетию</a>
Статьи обо всем: <a href=https://womaniyas.com/ru/psihologiya/kak-otpustit-vzrosleyushhih-detej-sovety-psihologa/>Как отпустить взрослеющих детей: советы психолога</a>
Новое и актуальное: <a href=https://votnews.com/trevozhnye-zvonochki-frazy-kotorye-mogut-ukazyvat-na-problemy-v-otnosheniyah/>Тревожные звоночки: фразы, которые могут указывать на проблемы в отношениях</a>
Интересные статьи: <a href=https://womanpoll.com/ru/kulinariya/pomidory-v-sobstvennom-soku-luchshie-retsepty-dlya-domashnego-konservirovaniya/>Помидоры в собственном соку: лучшие рецепты для домашнего консервирования</a>
Solution to recover lost phone number test [url=https://onlinesim.io/]number[/url]
<a href=https://upornxnx.com/>live cam porm</a>
<a href=https://spinbetter-play.pl/>porno pics milf</a>
Читать полностью: <a href=https://womansbeautyclub.com/kak-postroit-krepkie-otnosheniya-i-zavoevat-serdtse-lyubimogo-sovety-psihologa/>Как построить крепкие отношения и завоевать сердце любимого: советы психолога</a>
деньги онлайн займ <a href=https://shotmoney.ru/>микрозайм</a>
займ онлайн <a href=https://bizneskredity24.ru/>займ онлайн</a>
займ деньги <a href=https://nadejsfinans.ru/>микрозайм</a>
<a href=https://t.me/s/smsjokeservice>sms bomber usa</a>
<a href=https://object-store.de>Mega даркнет</a>
Надёжный заказ авто <a href=https://zakazat-avto44.ru/>https://zakazat-avto44.ru</a> с аукционов: качественные автомобили, проверенные продавцы, полная сопровождение сделки. Подбор, доставка, оформление — всё под ключ. Экономия до 30% по сравнению с покупкой в РФ.
Автомобили на заказ <a href=https://prignat-mashinu2.ru/>https://prignat-mashinu2.ru</a>. Работаем с крупнейшими аукционами: выбираем, проверяем, покупаем, доставляем. Машины с пробегом и без, отличное состояние, прозрачная история.
Решили <a href=https://prignat-mashinu.ru/>заказать авто из японии с аукциона</a> под ключ: подбор на аукционах, проверка, выкуп, доставка, растаможка и постановка на учёт. Честные отчёты, выгодные цены, быстрая логистика.
Хочешь авто <a href=https://prignat-avto1.ru/>заказать авто под заказ</a>? Мы поможем! Покупка на аукционе, проверка, выкуп, доставка, растаможка и ПТС — всё включено. Прямой импорт без наценок.
<a href=https://mradviseurs.nl>Mega ссылка</a>
In an industry that is constantly innovating, it can be difficult [url=https://suzuki-pdc.ru/]сиалис купить в москве[/url]
Строительство загородных домов под ключ - это процесс создания дома с нуля,
включая все этапы от проектирования до сдачи готового объекта
заказчику.
стоимость кирпичной кладки за 1 м2
Experience the thrill of casino games, sports betting [url=https://derprogrammierer.com]https://derprogrammierer.com[/url]
<a href=https://redesip.org>blacksprut сайт</a>
Discover the exclusive 1xBet rewards [url=https://www.imdb.com/list/ls4788229864/]https://www.imdb.com/list/ls4788229864/[/url]
<a href=https://farbwood.by/alyuminievaya-laga/laga-alyuminievaya-40*15*3000-mm-opornaya-slim>https://farbwood.by/alyuminievaya-laga/laga-alyuminievaya-40*15*3000-mm-opornaya-slim</a>
Нужна душевая кабина? <a href=https://dushevye-kabiny-minsk.ru/>магазин купить душевые кабины</a>: компактные и просторные модели, стеклянные и пластиковые, с глубоким поддоном и без. Установка под ключ, гарантия, помощь в подборе. Современный дизайн и доступные цены!
Продвижение сайта <a href=https://team-black-top.ru/>https://team-black-top.ru</a> в ТОП Яндекса и Google. Комплексное SEO, аудит, оптимизация, контент, внешние ссылки. Рост трафика и продаж уже через 2–3 месяца.
<a href=https://alchemycreations.co.uk>blacksprut darknet</a>
<a href=https://alchemycreations.co.uk>блэкспрут зеркало</a>
<a href=https://colabinc.com>блэкспрут сайт</a>
Эскортницы в агентстве в Москве более 100 лучших элитных моделей [url=https://mskescort.ru/]заказать эскорт[/url]
Unlock the generous world of 1xBet bonuses [url=https://www.imdb.com/list/ls4100002759/]https://www.imdb.com/list/ls4100002759/[/url]
<a href=https://redesip.org>блэкспрут не работает</a>
<a href=https://kimberlywylie.com>блэкспрут зеркало</a>
The 1xBet welcome bonus gives you the perfect opportunity to start with [url=https://www.imdb.com/list/ls4788853816/]https://www.imdb.com/list/ls4788853816/[/url]
Комедия детства <a href=https://home-alone.online/>один дома фильм 1990</a> — легендарная комедия для всей семьи. Без ограничений, в отличном качестве, на любом устройстве. Погрузитесь в атмосферу праздника вместе с Кевином!
<a href=https://poison-games.com>блэкспрут онион</a>
Нужна душевая кабина? <a href=https://dushevye-kabiny-minsk.ru/>душевая кабина цена</a> лучшие цены, надёжные бренды, стильные решения для любой ванной. Доставка по городу, монтаж, гарантия. Каталог от эконом до премиум — найдите идеальную модель для вашего дома.
<a href=https://poison-games.com>блэкспрут онион</a>
You ccan certainly see yokur expertise within the article you
write. The arena hopes for even more passionate wriiters like you
who are noot aafraid to mention howw they believe. All the time go after your heart. http://Boyarka-Inform.com/
<a href=https://mradviseurs.nl>Мега онион</a>
<a href=https://mradviseurs.nl>Мега даркнет</a>
The platform makes it easy to categorize slots by provider and rating [url=https://www.imdb.com/list/ls4788837030/]https://www.imdb.com/list/ls4788837030/[/url]
<a href=https://mradviseurs.nl>Mega darknet</a>
<a href=https://mradviseurs.nl>Мега онион</a>
Betwinner boasts a comprehensive offering and dynamic odds [url=https://www.imdb.com/list/ls4100328555/]https://www.imdb.com/list/ls4100328555/[/url]
<a href=https://focusbiathlon.com/>FocusBiathlon</a> - biathlon news, schedule biathlon world cup and overall rankings
займы онлайн <a href=https://fast-online-zaim1.ru/>займы онлайн</a>
<a href=https://didacballester.com>Мега онион</a>
https://graph.org/Launching-Your-Consulting-Business-in-Dubai-A-Strategic-Path-to-UAE-Success-05-07
<a href=https://mdigadynamics.co.za>Mega даркнет</a>
<a href=https://mdigadynamics.co.za>Mega onion</a>
<a href=https://norrlandsjord.se>Мега онион</a>
Акция Кешбэк 10% для постоянных пациентов https://stoma-esthete.ru/stocks-v-stomatologii/cashback
<a href=https://walewska.ru/>walewska.ru</a>
In fact, with the help of registration codes, players get access to deposit bonuses [url=https://www.imdb.com/list/ls4105020323/]https://www.imdb.com/list/ls4105020323/[/url]
Курс по плазмолифтингу <a href=https://prp-ginekologiya.ru/>https://prp-ginekologiya.ru</a> в гинекологии: PRP-терапия, протоколы, показания и техника введения. Обучение для гинекологов с выдачей сертификата. Эффективный метод в эстетической и восстановительной медицине.
Курс по плазмотерапии <a href=https://prp-plazmoterapija.ru/>prp терапия обучение</a> с выдачей сертификата. Освойте PRP-методику: показания, противопоказания, протоколы, работа с оборудованием. Обучение для медработников с практикой и официальными документами.
Хотите купить авто из США и других стран? Доставим под ключ [url=https://vk.com/amerika__by?from=groups&w=club215703603]купить авто из америки в минске[/url]
Warm street lighting of the new residential area was connected [url=http://www.sharkmotors.ru/news/863.html]http://www.sharkmotors.ru/news/863.html[/url]
<a href=https://cozycurtains.com>Mega даркнет</a>
Интересная статья: <a href=https://carexpert.com.ua/ru/avtovladeltsam/top-krossoverov-s-probegom-kakie-modeli-luchshe-izbegat/>Топ кроссоверов с пробегом: какие модели лучше избегать</a>
Интересная статья: <a href=https://medial-plus.com/kulinariya/salat-nezhnyj-retsept-populyarnogo-i-vkusnogo-salata-na-prazdnichnyj-stol/>Салат Нежный: рецепт популярного и вкусного салата на праздничный стол</a>
Читать статью: <a href=https://vestionline.com.ua/ru/psihologiya/kogda-stoit-brosit-nachatoe-psihologicheskij-vzglyad-na-lichnye-granitsy/>Когда стоит бросить начатое: психологический взгляд на личные границы</a>
The production process of chromium steel involves the use of specialized furnaces [url=https://medgatetoday.com/art/1xbet-promo-code_bonus-code.html]https://medgatetoday.com/art/1xbet-promo-code_bonus-code.html[/url]
При выборе автомобиля стоит учитывать свои потребности, бюджет и предпочтения по характеристикам и дизайну [url=https://vk.com/@amerika__by-pochemu-pokupka-avtomobilei-iz-ameriki-stanovitsya-vse-bolee]авто из америки в минске[/url]
Читать в подробностях: <a href=https://novosti24.com.ua/ru/lajfhaki/osveshhenie-dlya-rassady-kak-vyrastit-krepkie-rostki-bez-fitolamp/>Освещение для рассады: как вырастить крепкие ростки без фитоламп</a>
Интересная новость: <a href=https://ua-pulse.com/ru/lajfhaki/noyabrskij-uhod-za-komnatnymi-rasteniyami-peresazhivaem-tolstyanku-aloe-i-drugie-tsvety/>Ноябрьский уход за комнатными растениями: пересаживаем толстянку, алоэ и другие цветы</a>
Читать новость: <a href=https://dailynewsbytes.com/zdorove/kak-bystro-ubrat-zhivot-effektivnye-sovety-i-metody/>Как быстро убрать живот: эффективные советы и методы</a>
We are a provider of premiere services all around [url=https://highwaystarmagazine.org/]https://highwaystarmagazine.org/[/url]
<a href=https://itsteknosains.co.id>Мега онион</a>
Новое на сайте: <a href=https://aamnewsmedia.com/lajfhaki/osennyaya-obrezka-ezheviki-sovety-i-lajfhaki-dlya-bogatogo-urozhaya/>Осенняя обрезка ежевики: советы и лайфхаки для богатого урожая</a>
<a href=https://itsteknosains.co.id>Mega сайт</a>
AI platform <a href=https://bullbittrade.com/>https://bullbittrade.com</a> for passive crypto trading. Robots trade 24/7, you earn. Without deep knowledge, without constant control. High speed, security and automatic strategy.
Innovative AI platform <a href=https://lumiabitai.com/>http://lumiabitai.com</a> for crypto trading — passive income without stress. Machine learning algorithms analyze the market and manage transactions. Simple registration, clear interface, stable profit.
<a href=https://garypretty.co.uk>кракен darknet</a>
Zarejestruj się i graj online w najlepszym kasynie w Polsce na <a href=https://slottywaycasinoonline.pl/>slottyway casino opinie</a>
<a href=https://garypretty.co.uk>kraken сайт</a>
фільми онлайн як <a href=http://ua-bay.net/>фільми 2025 року дивитися онлайн</a>
Trade online with <a href=https://pocketoption-uk.co.uk/>pocketoption-uk.co.uk</a> - a trusted platform with low entry requirements. Start with as little as £1, access over 100 global assets including GBP/USD, FTSE 100 and crypto. Fast payouts, user-friendly interface, and welcome bonuses for new traders.
українські фільми кохання <a href=http://uakino.pl/>фільми онлайн 1080p безкоштовно</a>
<a href=https://garypretty.co.uk>kraken рабочая ссылка onion</a>
Explore the rewarding bonus system designed for both [url=https://ween.tn/bundles/pages/index.php?code-promo-1xbet_bonus-de-bienvenue-gratuit.html]https://ween.tn/bundles/pages/index.php?code-promo-1xbet_bonus-de-bienvenue-gratuit.html[/url]
<a href=https://mndiscjockeys.com>Мега сайт</a>
Ветошь - это незаменимый материал для автосервиса
в Санкт-Петербурге. Этот мягкий и впитывающий материал
используется для протирки и очистки
различных поверхностей автомобилей.
Ветошь позволяет быстро и эффективно убрать грязь, пыль и следы масла с кузова
и салона машины.
ветошь цена
<a href=https://object-store.de>Mega ссылка</a>
All new customers of the 1xBet bookmaker have the opportunity [url=https://pathsinc.org/images/pages/?krasivyy_gazon_kak_osnova_lyubogo_sada.html]https://pathsinc.org/images/pages/?krasivyy_gazon_kak_osnova_lyubogo_sada.html[/url]
The most beautiful cities in Italy? It turns out that small towns [url=][/url]
the comic is big <a href=http://www.batcave.biz/>HD comics reader free</a>
<a href=https://mdigadynamics.co.za>Мега ссылка</a>
Do not miss the opportunity to receive a generous reward [url=https://europe-parfum.ru/new/pages/kak_rabotaet_giperbaricheskaya_kamera__1.html]https://europe-parfum.ru/new/pages/kak_rabotaet_giperbaricheskaya_kamera__1.html[/url]
<a href=https://object-store.de>Mega даркнет</a>
<a href=https://mndiscjockeys.com>Мега онион</a>
Thor begins a quest to save his earth [url=https://kvedomosti.ru/wp-content/articles/?1win_promokod_pri_registracii.html]https://kvedomosti.ru/wp-content/articles/?1win_promokod_pri_registracii.html[/url]
<a href=https://mdigadynamics.co.za>Mega onion</a>
There are four steps in each of which you need to provide personal information [url=http://wood-master.pro/templates/template2/?melbet_bonus_pri_registracii_2020__1.html]http://wood-master.pro/templates/template2/?melbet_bonus_pri_registracii_2020__1.html[/url]
<a href=https://object-store.de>Мега онион</a>
<a href=https://monarchrm.com>Мега сайт</a>
<a href=https://mdigadynamics.co.za>Mega darknet</a>
<a href=https://mdigadynamics.co.za>Мега онион</a>
Проходите аттестацию <a href=https://prom-bez-ept.ru/>https://prom-bez-ept.ru</a> по промышленной безопасности через ЕПТ — быстро, удобно и официально. Подготовка, регистрация, тестирование и сопровождение.
<a href=https://monarchrm.com>Мега сайт</a>
«Дела семейные» <a href=https://academyds.ru/>https://academyds.ru</a> онлайн-академия для родителей, супругов и всех, кто хочет разобраться в семейных вопросах. Психология, право, коммуникации, конфликты, воспитание — просто о важном для жизни.
Discover a sophisticated style and tasteful designs at Buenos Aires Marriott [url=https://www.imdb.com/list/ls4107731918/]https://www.imdb.com/list/ls4107731918/[/url]
Трэвел-журналистика <a href=https://presskurs.ru/>https://presskurs.ru</a> как превращать путешествия в публикации. Работа с редакциями, создание медийного портфолио, написание текстов, интервью, фото- и видеоматериалы.
<a href=https://mndiscjockeys.com>Mega даркнет</a>
Découvrez <a href=https://pocketoption-france.fr/>pockeyoption</a>, l’application de trading intuitive utilisée par des millions de traders dans le monde. Accédez à plus de 100 actifs : forex, actions, crypto-monnaies et matières premières. Exécutions rapides, interface claire et retraits instantanés. Parfait pour débutants comme pour traders expérimentés - tradez où que vous soyez, à tout moment.
<a href=https://object-store.de>Мега ссылка</a>
?аза? тіліндегі ?ндер <a href=https://kazasha-ander.kz/>Казахские хиты</a> ж?рекке жа?ын ?уендер мен ?серлі м?тіндер. ?лтты? музыка мен ?азіргі заман?ы хиттер. Онлайн ты?дау ж?не ж?ктеу м?мкіндігі бар ы??айлы жина?.
<a href=https://object-store.de>Мега онион</a>
<a href=https://object-store.de>Мега ссылка</a>
<a href=https://mdigadynamics.co.za>Mega darknet</a>
<a href=https://www.reumatologia.org.br/>kraken сайт зеркала</a>
<a href=https://whitehouse01.com/poker-game/texas-holdem-rules-guide/>德州撲克規則</a>
學會德州撲克,不只是學會一套牌型規則,而是開始理解一場結合邏輯、心理與紀律的頭腦對決。無論你是剛入門的新手,還是已經上過幾次牌桌的玩家,只要願意花時間學習技巧、訓練判斷,並培養正確的資金控管與心態,人人都有機會從「交學費」變成「收學費」。打好每一手牌,不為一時輸贏情緒化,累積經驗與數據,就是長期勝率提升的關鍵!
<a href=https://mdigadynamics.co.za>Мега сайт</a>
Большой выбор сварочной проволоки Св-08Г2С и других марок для полуавтомата [url=https://wire.in.ua/drit-zvaryuvalnij-0-8-mm-sv08g2s-4si1-er70s-6-polirovanij-5-kg-katushka-plastik-d200.html]Св-08Г2С[/url]
<a href=https://zorgconsulentzuid.nl>Мега ссылка</a>
<a href=https://mndiscjockeys.com>Мега сайт</a>
Мобильный номер - ваш надежный источник информации о телефонных номерах России. У нас вы сможете быстро узнать, кто звонил, просто введя код региона или номер телефона. Удобный поиск и актуальные данные операторов мобильной связи: <a href=https://mobilnomer.ru/>https://mobilnomer.ru/</a>
<a href=https://mndiscjockeys.com>Мега онион</a>
<a href=https://object-store.de>Mega даркнет</a>
<a href=https://mndiscjockeys.com>Mega onion</a>
<a href=https://zorgconsulentzuid.nl>Мега сайт</a>
<a href=https://mdigadynamics.co.za>Мега сайт</a>
Get reviews and build a strong online reputation [url=https://www.nagpurtoday.in]https://www.nagpurtoday.in[/url]
Before betting, carefully examine the event and its factors [url=https://intelicode.com/]https://intelicode.com/[/url]
<a href=https://rg168.tw/article/Holdem-Basic-Rules>德州撲克規則</a>
想學德州撲克卻完全沒頭緒?不管你是零基礎還是想重新複習,這篇就是為你準備的!一次搞懂德州撲克規則、牌型大小、下注流程與常見術語,讓你從看不懂到能開打一局只差這一篇!看完這篇,是不是對德州撲克整個比較有頭緒了?從玩法、流程到那些常聽不懂的術語,現在是不是都懂了七八成?準備好了嗎?快記好牌型、搞懂位置,然後開打一局練練手啦!富遊娛樂城提供最新線上德州撲克供玩家遊玩!首家引進OFC大菠蘿撲克、NLH無限注德州撲克玩法,上桌就開打,數錢數不停!
<a href=https://ace1.one/>娛樂城推薦</a>
ACE博評網有多年經驗以及專業水準,我們能夠幫助玩家在繁雜的遊戲行業中找到一個值得信賴的選擇。我們不向任何娛樂城收取廣告費,所有被推薦的娛樂城都已經通過我們的審查,來評估他們的效能與真誠度。每一間娛樂城都必須承受重要的考驗,並且只有符合我們高水平準則的公司才能夠獲得我們正式認可
Появились клопы в квартире? Срочно закажите профессиональную обработку в Москве, чтобы остановить размножение и вернуть себе спокойный сон <a href=https://obrabotka-ot-klopov7.ru/>https://obrabotka-ot-klopov7.ru/</a>
The term ‘Apostille’ is also popular in English to refer to
the legalisation of a document for international use. https://Mcneill-villarreal.hubstack.net/essential-skills-to-formulate-for-new-roles-in-translation-and-localization-in-2025
Free online chat without registration communicate with many interlocutors [url=https://flirt-888.com]https://flirt-888.com[/url]
If you fulfill all the conditions of the bookmaker and win [url=https://www.foto4u.su/kf/inc/sekretnuy_promokod_na_melbet_bonus_pri_registracii.html]https://www.foto4u.su/kf/inc/sekretnuy_promokod_na_melbet_bonus_pri_registracii.html[/url]
Somebody essentially lend a hand to make seriously articles I would state.
This is the very first time I frequented your website page and up to now?
I amazed with the analysis you made to make this particular post
extraordinary. Great task! https://www.metooo.es/u/6893f70ea49a50172f9d634a
Set of door seals for Nissan Micra 2002-2010 [url=https://www.ozon.ru/product/uplotnitel-bagazhnika-peugeot-3008-i-restayling-2013-2016-rezinka-bagazhnika-pezho-3008-1-1670613368/?_bctx=CAQQ6rVQ&at=Y7tjKPQXJUl1Zx5QtKAWmNyhqP68G5tpL7zpqs1LjO8p&hs=1]https://www.ozon.ru/product/uplotnitel-bagazhnika-peugeot-3008-i-restayling-2013-2016-rezinka-bagazhnika-pezho-3008-1-1670613368/?_bctx=CAQQ6rVQ&at=Y7tjKPQXJUl1Zx5QtKAWmNyhqP68G5tpL7zpqs1LjO8p&hs=1[/url]
Крафт пакеты оптом с логотипом спб и коробка пенал в Нижневартовске. Фоторамки с логотипом На заказ и Майки безрукавки под Нанесение купить в Хабаровске. Упаковочные коробки Маленькие и купить готовые пакеты в Пензе. Подарки партнерам по бизнесу и Наборы сумок оптом в Ярославле. Стружка для упаковки оптом подарков купить и пакет На застежке: <a href=https://telegra.ph/bumazhnye-pakety-optom-v-sankt-peterburge-08-06>https://telegra.ph/bumazhnye-pakety-optom-v-sankt-peterburge-08-06</a>
בלי סוף, כאילו נטעו בתוכי סוללה. ואני ממש דפקתי אותה. בפה, בתחת, קרע את החריץ, ואפילו היא נתנה לי החליט ואמר-טוב, היא רצתה את זה בעצמה-והרים את רגליה כך. איך היא מעולם לא הרימה. - זה סימולטור <a href=https://seorankanalyser.com/>you can check here</a>
Смотрите лучшие сериалы и фильмы онлайн в хорошем качестве без регистрации. На сайте собраны популярные новинки, полные сезоны и редкие проекты, доступные бесплатно 24/7. Удобный интерфейс и быстрый доступ к контенту для комфортного просмотра на любом устройстве: <a href=https://lordserialofficial.ru/>https://lordserialofficial.ru/</a>
של כלתו בכף ידו, עשה עוד כמה רעידות חזקות, וגם התחת שלו נכנס לעוויתות ונתקע, והפך ללא תנועה. אז, ליהנות מהטעם שלה. כמובן שזרקתי הכל, המצאתי עיסוי ארוטי בבית, התכוננתי, אבל כשכבר הגעתי קיבלתי <a href=https://takepornmovies.com/>סקס בקריות</a>
Школа стройки и ремонта. Все самое интересное и важное о стройке и ремонте. Также полезные статьи по выбору дизайна интерьера, уходу за садом и огородом, крутые лайфхаки, консультации специалистом и многое другое на страницах нашего блога <a href=https://propest.ru/>https://propest.ru/</a>
Offers a large selection of slots, sports betting and large bonuses. Working mirror of the official site [url=https://n2tutor.ru]1Вин[/url]
If you desire to obtain much from this piece of writing then you have to apply
these strategies to your won webpage. http://Boyarka-inform.com/
Все про политику, культуру, туризм и шоу бизнес. Также полезные статьи про медицину и обзор событий в мире ежедневно в нашем блоге <a href=https://agyha.ru/>https://agyha.ru/</a>
https://kazan.land/
Запишитесь на курсы и станьте уверенным водителем в любых условиях [url=https://dosaaf24.ru]обучение на вездеходы[/url]
Rubber seal for Indesit refrigerator for domestic [url=https://www.wildberries.ru/catalog/157353984/detail.aspx]https://www.wildberries.ru/catalog/157353984/detail.aspx[/url]
<a href=https://focusukraine.com.ua/uncategorized/karta-tryvog/>офіційна карта тривог</a>
To enter the promotional code in the account registration menu [url=https://www.imdb.com/list/ls4101925312/]https://www.imdb.com/list/ls4101925312/[/url]
Door seal kit for Renault Duster 2009-2022 [url=https://www.ozon.ru/product/uplotnitel-dlya-dveri-holodilnika-hotpoint-ariston-hotpoint-ariston-htr-4180-w-htr-4180-1066634048/?_bctx=CAQQ1aMZ&at=w0tg5X8rAuLlowV2SDVzMOgijE3vQXUgEVQWYTQWjBKX&hs=1]https://www.ozon.ru/product/uplotnitel-dlya-dveri-holodilnika-hotpoint-ariston-hotpoint-ariston-htr-4180-w-htr-4180-1066634048/?_bctx=CAQQ1aMZ&at=w0tg5X8rAuLlowV2SDVzMOgijE3vQXUgEVQWYTQWjBKX&hs=1[/url]
<a href=https://bazaindex.ru/>bazaindex.ru</a>
<a href=https://newskor.com.ua/korol-zhezliv-znachennia-karty-taro/>що означає король жезлів</a>
real viagra online canadian pharmacy
Остеопатия на пороге перемен: как интеграция с традиционной медициной меняет правила игры [url=https://ngclinic-nsk.ru]https://ngclinic-nsk.ru[/url]
Многие из нас сталкивались с ситуациями, когда вдруг появляется боль или симптом, не находящий очевидного объяснения [url=https://bcmedshop.ru]остеопат[/url]
Fiber concrete panels are a new generation of decorative building materials [url=https://gidpomusoru.ru/novosti-ob-othodah/kak-izbavitsya-ot-musora-raz-i-navsegda-uslugi-vyvoza-musora-na-lyuboj-vkus.html]https://gidpomusoru.ru/novosti-ob-othodah/kak-izbavitsya-ot-musora-raz-i-navsegda-uslugi-vyvoza-musora-na-lyuboj-vkus.html[/url]
Это информационный портал, где важные темы жизни становятся понятными. Мы говорим о том, что касается каждого [url=https://aslq.ru/sport-i-fitnes/skolko-nuzhno-trenirovatsya-v-nedelyu-idealnyy-grafik-dlya-zdorovya/]сколько нужно тренироваться в неделю[/url]
With age, the skin loses its elasticity, becomes less flexible, wrinkles appear [url=https://medeponim.ru/morphine-friedrich-serturner-and-the-isolation-of-the-first-alkaloid/]https://medeponim.ru/morphine-friedrich-serturner-and-the-isolation-of-the-first-alkaloid/[/url]
Inizia a fare trading in tutta sicurezza con <a href=https://pocketoptionitaly.neocities.org/>pocket option download</a> e goditi una piattaforma intuitiva e potente!
Packaging with air bubble film has a number [url=https://101paket.ru]https://101paket.ru[/url]
<a href=https://antidetectbrowser.info/>anti detect browser</a>
The seal is made from virgin raw materials, not recycled rubber [url=https://www.ozon.ru/product/uplotnitel-dlya-dveri-holodilnika-stinol-stinol-sts-185-sts185-869991547260-na-morozilnuyu-kameru-922508715/?_bctx=CAQQ1aMZ&at=XQtkl35rqF7yJ57vcXKjK5WCl2XY79HZrwM7oHEpKELL&hs=1]https://www.ozon.ru/product/uplotnitel-dlya-dveri-holodilnika-stinol-stinol-sts-185-sts185-869991547260-na-morozilnuyu-kameru-922508715/?_bctx=CAQQ1aMZ&at=XQtkl35rqF7yJ57vcXKjK5WCl2XY79HZrwM7oHEpKELL&hs=1[/url]
Roulette Game! Roulettino Casino and Win! Roulette is an ONLINE OR OFFLINE Vegas style casino game [url=https://rouletti.online/]https://rouletti.online/[/url]
For a step-by-step guide on opening an account, trading, and making withdrawals with GMO Gaika, visit the detailed resource at gyoza-goya.jp
<a href=https://dronreview.ru/kak-uchit-anglijskij-jazyk-detjam-10-13-let/>английский язык для детей 11 лет</a>
If you're looking to start trading with GMO Gaika, a complete guide covering account setup, trading, and withdrawals is available at omoken-park.jp
To learn more about FIVE STARS MARKETS and how it works, including real user experiences, check out the full overview at cafe-aranciato.jp
ароматерапия <a href=https://aromatmaslo.ru/>aromatmaslo</a>
https://xnudes.ai/
Для поклонников ставок и автоматов отлично подойдёт <a href="https://l-lux.ru/casino/1xbet.html">Казино 1xbet слот 20 Lucky Bell</a>.
<a href=https://shklovsky100-school.ru/>https://shklovsky100-school.ru/</a>
Новичкам будет полезен наш <a href="https://narkolog-hab.ru/casino/">топ онлайн казино</a> с подробными обзорами.
<a href=https://rtpsindoplay1.com/>sindoplay</a>
SINDOPLAY - situs slot online dengan pilihan permainan terlengkap . Daftar dan login untuk bisa memainkan game - game slot online terbaru dengan persentase RTP diatas 98%
The fall of the Roman Empire was a complex event with multiple contributing factors <a href="https://coursebible.com/posts/where-is-the-negev-where-abram-went-to-in-genesis">where is negev today</a>
<a href=https://vivelounge.com/>bocor88</a>
Test your camera online to check if it works properly and learn useful information [url=https://gay24chat.com]https://gay24chat.com[/url]
Угловые тахты также доступны в различных размерах [url=https://vammebel.ru/]https://vammebel.ru/[/url]
Какие отзывы оставляют специалисты в области ортопедии и ревматологии о применении Artodip Gel [url=http://www.kostromag.ru/forum/help/17500.aspx]http://www.kostromag.ru/forum/help/17500.aspx[/url]
Кустовые розы произошли от шиповника и выглядят как как раскидистые кустарники [url=https://millionroz.by/tsvety/roza-kustovaya]Кустарные розы Минск[/url]
<a href="https://l-lux.ru/casino/pokerdom.html">Казино Pokerdom</a>
Guys, give me some advice, preferably based on your personal experience [url=http://www.fragensienilsen.de/forum/index.php?topic=26241.0]http://www.fragensienilsen.de/forum/index.php?topic=26241.0[/url]
<a href="https://drugoi-gorod.ru/casino/">лучшие казино для игры 243 Space Fruits</a>
<a href="https://wave-games.ru/casino/vavada.html">20 Hot Bar играть в Вавада</a>
<a href="https://wave-games.ru/">20 Hot Bar слот</a>
<a href="https://certforum.ru/en/slot-rating.html">Best slot games rating</a>
Смотреть турецкие сериалы онлайн https://turkyserial2026.ru/
For his personal bravery and active participation in military operations at sea, Fyodor Fedorovich [url=https://yil-edition.com/art/sovety_po_prohoghdeniyu_igry_god_of_war_sekrety_i_predmety_kollekcionirovaniya_rechnoy_pe.html]https://yil-edition.com/art/sovety_po_prohoghdeniyu_igry_god_of_war_sekrety_i_predmety_kollekcionirovaniya_rechnoy_pe.html[/url]
Before making an advance payment, they look at the cottage [url=https://cherwellcricketleague.com/img/pgs/meilleur-code-promo-1xbet-cameroun__.html]https://cherwellcricketleague.com/img/pgs/meilleur-code-promo-1xbet-cameroun__.html[/url]
<a href="https://narkolog-hab.ru/casino/1win.html">1942 Sky Warrior играть в 1вин</a>
Wheat allergy is different from celiac disease, which is an immune system reaction that leads [url=https://talcom.ru/cart/pages/kak_samostoyatelyno_zashpatlevaty_shvy_na_gipsokartone.html]https://talcom.ru/cart/pages/kak_samostoyatelyno_zashpatlevaty_shvy_na_gipsokartone.html[/url]
<a href="https://yaamilliarder.ru/en/">15 Dragon Coins online</a>
Despite the rapid technological progress, many of us still cling to old beliefs and habits [url=https://cricketcreekfarm.com/wp-content/uploads/?klematis_pravila_posadki_i_uhoda.html]https://cricketcreekfarm.com/wp-content/uploads/?klematis_pravila_posadki_i_uhoda.html[/url]
https://xtwit.shop
<a href="https://e-vi.ru/casino/pinco.html">21 Thor Lightning Ways играть в Пинко</a>
Plunge into the breathtaking realm of EVE Online. Shape your destiny today. Create alongside millions of players worldwide. [url=https://www.eveonline.com/signup?invc=46758c20-63e3-4816-aa0e-f91cff26ade4]Download free[/url]
The casino is very good. Beautiful, convenient search for games [url=https://pavlovskppk.ru]https://pavlovskppk.ru[/url]
<a href="https://zarainternet.ru/casino/leon.html">Казино Leonbets</a>
<a href=https://www.reumatologia.org.br/>kraken onion</a>
Всех приветствую! Хотите узнать больше о продвижении? Подробная информация на тему: <a href=https://zonamerah.co/2024/09/27/antisipada-bahaya-kebakaran-karutan-torkis-fredy-siregar-hadirkan-sat-pol-pp-damkar/>https://zonamerah.co/2024/09/27/antisipada-bahaya-kebakaran-karutan-torkis-fredy-siregar-hadirkan-sat-pol-pp-damkar/</a>
Китайское аниме https://bryansktoday.ru/article/244874
We’ve compiled a few exclusive 1xBet promo codes to help strengthen your sports betting experience [url=https://www.freetips.com/bonus-code/1xbet-promo-code/]ЕџiЕџman porno hd[/url]
<a href=https://www.stcware.com/>kraken актуальные ссылки</a>
аниме онлайн https://www.bnkomi.ru/data/relize/187391/
<a href=https://www.stcware.com/>kraken ссылка зеркало</a>
<a href="https://vinorukami.ru/casino/cat.html">Казино Cat</a>
wide selection of games, generous bonuses for new and regular players. Complete a quick <a href="https://onedayshop.ru">монеу икс</a>
<a href=https://www.stcware.com/>kraken онион</a>
<a href=https://www.stcware.com/>kra ссылка</a>
<a href=https://www.stcware.com/>kraken darknet ссылка</a>
<a href=https://www.stcware.com/>kraken ссылка на сайт</a>
Betwinner India makes signing-up a breeze with their multitude of registration methods <a href="https://www.sportytrader.com/en-ng/betting-sites/1xbet/promo-code/">psychotropic salts</a>
<a href="https://dolboebka.ru/casino/pokerdom.html">Казино Pokerdom слот 6 Jokers</a>
More than the bonus offered in your country, and this on your first deposit <a href="https://betonmobile.ru/promokodyi-1hbet">my wife and kids porno</a>
Catering to a diverse global audience spanning from the bustling streets <a href="https://shadow-saver-882.notion.site/Best-Offers-Unlocked-by-1xBet-Promo-Code-25b9aa1e752980869bb1e957e343e83b">https://shadow-saver-882.notion.site/Best-Offers-Unlocked-by-1xBet-Promo-Code-25b9aa1e752980869bb1e957e343e83b</a>
<a href="https://exp2000.ru/casino/mostbet.html">Казино Mostbet</a>
<a href="https://kurort-olimp.ru/">40 Pixels</a>
Казино аркада официальный сайт - играть на деньги в фоициальном сайте https://medspirtshop.ru/
<a href=https://ocia.org>kraken зеркало</a>
Yo, stumbled on this sick tuner. Works straight from the browser, no download BS. Super accurate, plus it's got chromatic mode and a ton of alternate tunings. Straight up saved it to my bookmarks: <a href=https://www.tronicaltune.net/tronicaltune-online-guitar-tuner/>this online tuner from TronicalTune</a>
<a href=https://usgtf.com>kraken маркетплейс зеркало</a>
Психолог онлайн даст профессиональный совет. Детский психолог онлайн проведет сеанс для родителей.
<a href=https://vk.com/club211532114>общаться с психологом онлайн</a>
<a href=https://conee.de>kraken ссылка зеркало</a>
<a href=https://inter-aktywni.pl>кракен onion сайт</a>
Promotion for new punters for sports and casino betting <a href="https://networkers-thenetworkmarketinggroup.mn.co/posts/89879283">https://networkers-thenetworkmarketinggroup.mn.co/posts/89879283</a>
<a href=https://destmark.com>kra ссылка</a>
После первой перезагрузки система запустится и попросит вас пройти ряд шагов первичной настройки <a href="https://smarthoms.ru/windows/ustanovka-windows10-11/">Пошаговая инструкция по полной переустановке Windows 10/11</a>
<a href="https://stupnitskaya.ru/">https://stupnitskaya.ru</a>
<a href=https://www.reumatologia.org.br/>кракен darknet</a>
Пансионат "Тульский дедушка" расположен в живописном уголке <a href="http://electro-tools.net/news/publ/494-pansionat-dlya-lezhachih-bolnyh-tulskiy-dedushka-zabotlivyy-uhod-i-komfortnaya-zhizn.html">пансионат для лежачих больных цены</a>
<a href=https://www.reumatologia.org.br/>kraken зеркало</a>
<a href=https://www.reumatologia.org.br/>kraken сайт</a>
<a href=https://www.reumatologia.org.br/>kra ссылка</a>
https://ceramicapro.ru/ — сделать процесс выбора и использования керамогранита и плитки максимально понятным и удобным для потребителей, предоставляя полезные советы, сравнительные статьи и технические характеристики <a href="https://ceramicapro.ru/tolshhina-keramogranita-1200h600-polnyj-obzor-sovety-po-vyboru-i-osobennosti-primeneniya/">https://ceramicapro.ru/tolshhina-keramogranita-1200h600-polnyj-obzor-sovety-po-vyboru-i-osobennosti-primeneniya/</a>
<a href=https://www.reumatologia.org.br/>кракен онион</a>
Optimize your betting working experience with the latest 1xbet <a href="https://iseodirectory.com/listings13297878/unlock-exclusive-wins-with-the-latest-1xbet-promo-code">https://iseodirectory.com/listings13297878/unlock-exclusive-wins-with-the-latest-1xbet-promo-code</a>
<a href=https://www.reumatologia.org.br/>kraken ссылка тор</a>
Кастомная функция для Google Sheets, которая позволяет напрямую использовать <a href="https://github.com/novacom-sheets/gpt-apps-script">https://github.com/novacom-sheets/gpt-apps-script</a>
https://zashchita-prav-potrebiteley.ru/
Платформа создана для того, чтобы помочь любителям музыки <a href="https://perevod-pesen.com/article/perevodpesen-pro-vse-perevody-pesen-s-originalom-i-udobnym-poiskom/">formidable перевод песни</a>
<a href=https://rostest.com/>орган по сертификации ростест</a>
<a href="https://fourslashone.ru/">81 Vegas Magic слот</a>
Use this bonus code when creating a new account at 1xBet to receive <a href="https://www.pearltrees.com/1xbetpr0mocode#item733276610">https://www.pearltrees.com/1xbetpr0mocode#item733276610</a>
Чтобы купить пластиковые окна недорого в Москве, достаточно выбрать надежного партнера <a href="http://okna-plastikovye-na-zakaz.ru/">http://okna-plastikovye-na-zakaz.ru/</a>
В процессе разработки Azimut создано около 1 000 новых компонентов, включая кузовные панели, интерьер и элементы подвески <a href="https://vaz-lada-azimut.ru/">цены будут ниже чем на похожих китайцев</a>
Convenient service for selecting financial services for residents of the Krasnodar region <a href="http://www.artlib.ru/index.php?id=26&idr=4&idt=50500">http://www.artlib.ru/index.php?id=26&idr=4&idt=50500</a>
Самый эффективный путь без значительных затрат на авто <a href="https://vaz-lada-azimut.ru/2025/06/17/vaz-21179-132/">тюнинг двигателей Лады</a>
The current Pin Up mirror can be found on the official website <a href="https://minprirod.ru">Pin Up casino</a>
When people talk about young champions, Mike Tyson <a href="https://factspodium.com/the-youngest-boxing-world-champion/">https://factspodium.com/the-youngest-boxing-world-champion/</a>
<a href=https://www.reumatologia.org.br/>кракен ссылка onion</a>
<a href="https://kaliningrad-turist.ru/casino/mostbet.html">Казино Mostbet</a>
<a href="https://sovtehnika.ru/az/casino/">Alexander the Great World Conqueror casinos AZ</a>
<a href="https://betsmatch.ru/casino/maxbetslots.html">Age of Zeus играть в Максбет</a>
<a href=https://vc.ru/telegram/2188939-kupit-aktivnyh-podpischikov-v-telegram>накрутка активных людей Телеграм</a>
<a href="https://little-sun.ru/casino/pinco.html">Казино Pinco</a>
Аренда сноубордов у нас — это отличная возможность попробовать разные модели досок и подобрать подходящую для вашего стиля катания и уровня опыта: <a href=https://arenda-lyzhi-sochi.ru/>прокат лыж красная поляна</a>
Pinko is an online casino that offers access to a wide range of certified slot machines <a href="https://teberda-school1.ru">Пин Ап казино</a>
<a href=https://www.reumatologia.org.br/>kraken darknet market</a>
<a href="https://hate-co.ru/">Agent Royale игра</a>
Антенно-фидерная система – всенаправленные антенны с круговой поляризацией <a href="https://xn--e1afpuq.io/">рэб от дрона</a>
<a href="https://obuv-lepota.ru/">Alchemy Ways играть</a>
<a href=https://www.alexeymart.com/>https://www.alexeymart.com/</a>
Более 16 лет занимается поставками качественного оборудования для стоматологических кабинетов <a href="https://dentalsystems.ru/">аренда стоматологического микроскопа</a>
It is region-specific in some cases, with tailored offers for countries like <a href="https://bookmarkquotes.com/story20312580/homepage">https://bookmarkquotes.com/story20312580/homepage</a>
We have the latest information: <a href=https://jnp.chitkara.edu.in/>https://jnp.chitkara.edu.in</a>
Only sports bets count toward wagering — live and eSports bets are excluded <a href="https://felomena.com/wp-includes/inc/?gama_kazino_promokod.html">https://felomena.com/wp-includes/inc/?gama_kazino_promokod.html</a>
Fast-forward to today, and cryptocurrencies are becoming increasingly more popular <a href="https://www.azpiegiturak.bizkaia.eus/media/pgs/?bonus_d_inscription_au_casino_1xbet.html">https://www.azpiegiturak.bizkaia.eus/media/pgs/?bonus_d_inscription_au_casino_1xbet.html</a>
With the help of this promo code, players can get various bonuses, such as welcome bonuses <a href="https://spanishmastif.ru/images/pages/?1xbet_promokod_pri_registracii_bonus.html">https://spanishmastif.ru/images/pages/?1xbet_promokod_pri_registracii_bonus.html</a>
We are waiting for you on the site: <a href=https://travel2mv.com/>https://travel2mv.com</a>
Питомник "Дивный сад" - интернет-магазин саженцев с доставкой по Беларуси и России <a href="https://divsad.by/">Саженцы кустарников многолетних</a>
All the latest on our website: <a href=https://clubcoma.org/>https://clubcoma.org</a>
<a href=https://www.colabinc.com/>black sprut</a> blacksprut, блэкспрут, black sprut, блэк спрут, blacksprut вход, блэкспрут ссылка, blacksprut ссылка, blacksprut onion, блэкспрут сайт, blacksprut вход, блэкспрут онион, блэкспрут дакрнет, blacksprut darknet, blacksprut сайт, блэкспрут зеркало, blacksprut зеркало, black sprout, blacksprut com зеркало, блэкспрут не работает, blacksprut зеркала, как зайти на blacksprutd
<a href=https://www.colabinc.com/>блэкспрут не работает</a> blacksprut, блэкспрут, black sprut, блэк спрут, blacksprut вход, блэкспрут ссылка, blacksprut ссылка, blacksprut onion, блэкспрут сайт, blacksprut вход, блэкспрут онион, блэкспрут дакрнет, blacksprut darknet, blacksprut сайт, блэкспрут зеркало, blacksprut зеркало, black sprout, blacksprut com зеркало, блэкспрут не работает, blacksprut зеркала, как зайти на blacksprutd
Пошаговый чек-лист по выбору входной металлической двери <a href="https://totalarch.com/vhodnye-metallicheskie-dveri">https://totalarch.com/vhodnye-metallicheskie-dveri</a>
As volatility in global markets remains elevated due to macroeconomic <a href="https://bitclassic.org/how-to-start-trading-cryptocurrency-with-a-trusted-forex-broker-a-guide-for-new-traders/">https://bitclassic.org/how-to-start-trading-cryptocurrency-with-a-trusted-forex-broker-a-guide-for-new-traders/</a>
<a href=https://push-network-rankings.com/>Best Push Ad Networks</a>
Also, you need to read the privacy policy and verify your age <a href="https://360immersion.com/wp-content/pgs/?biozavivka_stilyno_i_bezopasno.html">https://360immersion.com/wp-content/pgs/?biozavivka_stilyno_i_bezopasno.html</a>
If you are just starting out in the world of online betting <a href="https://doctor-loder.ru/wp-content/inc/promokod_melbet_fribet___bonus_kod_pri_registracii.html">https://xn--22-glch8c.xn--p1ai/articles/simptomy_i_ushiby_sotryaseniya_mozga_u_rebenka.html</a>
Бесплатный сервис без регистрации подбора займов от 1000 до 100000?. Сравниваем условия 100+ МФО и находим лучший вариант для вас <a href="https://kubyshka24.ru/">лучшие микрозаймы</a>
доставка из китая в россию <a href=https://cargo-ex.ru/>карго из китая доставка</a>
You can, like the Bulgarians, collect ceramic pots, write good wishes on them <a href="http://rybinsk-news.ru/index.php/novosti-rybinska/5466-v-kalmykii-vozbuzhdeno-delo-po-faktu-falshivyh">http://rybinsk-news.ru/index.php/novosti-rybinska/5466-v-kalmykii-vozbuzhdeno-delo-po-faktu-falshivyh</a>
The fortress is built on a high rocky bank <a href="https://sibseals.ru/includes/pgs/?kak_izgotavlivaetsya_myagkaya_mebely_na_zakaz.html">https://sibseals.ru/includes/pgs/?kak_izgotavlivaetsya_myagkaya_mebely_na_zakaz.html</a>
On the 1xbet betting site, players can use sports betting <a href="http://faculty.ru/job/pgs/1xstavka_promokod_pri_registracii_besplatno.html">http://faculty.ru/job/pgs/1xstavka_promokod_pri_registracii_besplatno.html</a>
best articles on the net: <a href=https://dnscompetition.in/articles/using-dns-to-manage-user-traffic-a-comprehensive-guide/>https://dnscompetition.in/articles/using-dns-to-manage-user-traffic-a-comprehensive-guide/</a>
The platform’s responsive support team, available in over 30 languages <a href="https://xn-----7kcbekeiftdh9amwkb4d2o.xn--p1ai/news/chto_sleduet_uchityvaty_pri_vybore_kliniki_esteticheskoy_mediciny.html">https://xn-----7kcbekeiftdh9amwkb4d2o.xn--p1ai/news/chto_sleduet_uchityvaty_pri_vybore_kliniki_esteticheskoy_mediciny.html</a>
Journal has been the best selling and most loved OpenCart <a href="https://csprotechnology4624.mn.co/posts/90368612">https://csprotechnology4624.mn.co/posts/90368612</a>
play puzzles online: <a href=https://howheavyisit.com/hobby/how-much-does-a-500-piece-puzzle-weigh/>https://howheavyisit.com/hobby/how-much-does-a-500-piece-puzzle-weigh/</a>
1xBet always puts its clients first, listening to feedback and suggestions <a href="https://kronverkskoe.ru/norma/pags/?titulynoe_strahovanie_nedvighimogo_imuschestva_chto_eto_i_zachem_nughno.html">https://kronverkskoe.ru/norma/pags/?titulynoe_strahovanie_nedvighimogo_imuschestva_chto_eto_i_zachem_nughno.html</a>
Наша цель — продавать русские пироги во всех городах и странах мира <a href="https://osetin63pirog.ru/">каталог пирогов на заказ</a>
The most useful information: <a href=https://foxartistic.com/>https://foxartistic.com</a>
best site come on in: <a href=https://bookingautos.com/>https://bookingautos.com</a>
шпонированный мдф <a href=https://mirshpona.ru/>шпонирование мдф москва</a>
Well done to all involved on a very successful production <a href="https://infopagex.com/story5620307/1xbet-promo-code-registration">https://infopagex.com/story5620307/1xbet-promo-code-registration</a>
геодезия московская область <a href=https://expert-geo.ru/>геодезия москва</a>
геотекстиль 300 цена <a href=https://ksgeo.ru/>геотекстиль для садовых дорожек цена</a>
Включение в реестр Минпромторга <a href=https://minprom-info.ru/>https://minprom-info.ru</a> официальный путь для подтверждения отечественного производства. Подготовка и подача документов, юридическое сопровождение и консультации для производителей.
Занятия по самообороне <a href=https://safety-skills.ru/>https://safety-skills.ru</a> практические навыки защиты в реальных ситуациях, развитие силы и выносливости. Профессиональные тренеры помогут освоить приемы борьбы, удары и тактику безопасности.
Engage in thrilling and romantic encounters , manage your Empire alongside wise Viziers <a href="https://lawforum.kz/">https://lawforum.kz/</a>
Написание дипломов на заказ <a href=https://vasdiplom.ru/>https://vasdiplom.ru</a> помощь студентам в подготовке итоговых работ. Авторские тексты, проверка на уникальность и полное соответствие стандартам учебных заведений.
visit our best site online: <a href=https://www.maxwaugh.com/>https://www.maxwaugh.com</a>
The best we have here: <a href=https://theshaderoom.com/>https://theshaderoom.com</a>
The latest information is here: <a href=https://unilago.com/>https://unilago.com</a>
Pokud hledáte online casino cz, cz casino online nebo kasina, jste na správném místě. Jsem žurnalista a pomohu vám srovnat rizika i možnosti českého online hazardu – stylově, seriózně a uživatelsky přívětivě: <a href=https://telegra.ph/Modern%C3%AD-pr%C5%AFvodce-Online-Casino-v-%C4%8Cesku-09-05>cz casino online</a>
The best of our site: <a href=https://www.feldbahn-ffm.de/>https://www.feldbahn-ffm.de</a>
New and relevant information: <a href=https://www.colehardware.com/>https://www.colehardware.com</a>
Want to have fun? <a href=https://apk-melbet.com/ar-eg/>porno melbet</a> Whores, drugs, casino. We have it all, any drugs are on sale.
Many interesting articles, I checked again <a href="http://ourmetals.com/">http://ourmetals.com/</a>
Обучение и семинары <a href=https://uofs-beslan.ru/>https://uofs-beslan.ru</a> для профессионалов: современные программы, практические кейсы и опыт экспертов. Развивайте навыки, повышайте квалификацию и получайте новые возможности для карьерного роста.
Академия парикмахерского искусства <a href=https://charm-academy.ru/>https://charm-academy.ru</a> обучение от ведущих мастеров. Современные техники стрижек, окрашивания и укладок. Курсы для начинающих и профессионалов с практикой и дипломом по окончании.
Лицей взаимного обучения <a href=https://talgenisty.ru/>https://talgenisty.ru</a> уникальная среда для детей и взрослых. Совместные уроки, обмен опытом, мастер-классы и творческие проекты. Образование, основанное на поддержке и сотрудничестве.
Школа видеорекламы <a href=https://tatyanamostseeva.ru/>https://tatyanamostseeva.ru</a> обучение созданию креативных роликов для бизнеса и брендов. Практические занятия, работа с современными инструментами и поддержка экспертов. Освойте профессию в сфере digital.
Great site for everyone: <a href=https://institutocea.com/>https://institutocea.com</a>
The best site for you: <a href=https://www.acuam.com/>https://www.acuam.com</a>
Кухонные принадлежности <a href=https://www.kitchen-store.ru/blog/vybrat-bokaly>https://www.kitchen-store.ru/blog/vybrat-bokaly</a> в магазине для дома: современная посуда, полезные гаджеты, текстиль и аксессуары. Стильные решения для кухни, выгодные цены и большой ассортимент.
The Cleveland Browns 17-game losing streak comes <a href="https://sites.google.com/view/1xbet-bonus-promo-codeu/home">https://sites.google.com/view/1xbet-bonus-promo-codeu/home</a>
For the best bonus experience, we recommend using the <a href="https://bd.radiocut.fm/user/bienvenue1xbet/">https://bd.radiocut.fm/user/bienvenue1xbet/</a>
Нужен автобусный билет? <a href=https://forum.roborock.com/profile/32653/probilets8>заказ билетов на автобус</a> удобный сервис поиска и бронирования. Широкий выбор направлений, надежные перевозчики, доступные цены и моментальная отправка электронных билетов на почту.
Автомобильный портал <a href=https://auto-club.pl.ua/>https://auto-club.pl.ua</a> онлайн-площадка для автолюбителей. Подробные обзоры машин, тест-драйвы, свежие новости, советы по ремонту и обслуживанию. Удобный поиск и актуальные материалы.
Все для автомобилистов <a href=https://k-moto.com.ua/>https://k-moto.com.ua</a> на авто портале: новости, обзоры, статьи, каталоги и цены на автомобили. Экспертные мнения, тест-драйвы и практические советы по эксплуатации авто.
Go to our website: <a href=https://petitedanse.com.br/>https://petitedanse.com.br</a>
Онлайн женский портал <a href=https://elegance.kyiv.ua/>https://elegance.kyiv.ua</a> актуальные советы по красоте, стилю, кулинарии и семейной жизни. Разделы о здоровье, карьере и саморазвитии. Интересные статьи и общение с единомышленницами.
Нужна виза? <a href=https://delovaya-viza.ru/>виза в италию москва</a> Консультации, подготовка документов, сопровождение на всех этапах. Визы в Европу, США, Азию и другие страны. Доступные цены и надежная поддержка.
Портал для женщин <a href=https://fashionadvice.kyiv.ua/>https://fashionadvice.kyiv.ua</a> сайт для девушек и женщин, которые ценят красоту, уют и гармонию. Советы по стилю, отношениям, материнству и здоровью. Читайте статьи, делитесь опытом и вдохновляйтесь новыми идеями.
Depending on the terms of the promotion, using such a code offers players <a href="https://audium.com">https://audium.com</a>
Автомобильные новости <a href=https://reuth911.com/>https://reuth911.com</a> онлайн: новые модели, отзывы, тест-драйвы, события автопрома и полезные советы. Узнайте первыми о главных новинках и трендах автомобильного мира.
Свежие новости авто <a href=https://orion-auto.com.ua/>https://orion-auto.com.ua</a> тест-драйвы, обзоры новинок, законодательные изменения и аналитика авторынка. Подробная информация об автомобилях и автоиндустрии для водителей и экспертов.
Портал про автомобили <a href=https://myauto.kyiv.ua/>https://myauto.kyiv.ua</a> онлайн-ресурс для автолюбителей. Обзоры, статьи, тест-драйвы, цены и полезные советы по ремонту и уходу за машиной. Всё о мире авто в одном месте.
Авто портал <a href=https://avtoshans.in.ua/>https://avtoshans.in.ua</a> для всех: свежие новости, обзоры моделей, советы по выбору и эксплуатации авто. Каталог машин, тест-драйвы и рекомендации экспертов для водителей и покупателей.
Автомобильный сайт<a href=https://setbook.com.ua/>https://setbook.com.ua</a> свежие новости, обзоры моделей, тест-драйвы и советы экспертов. Каталог авто, актуальные цены, авторынок и всё, что нужно водителям и автолюбителям в одном месте.
Онлайн-журнал для женщин <a href=https://fines.com.ua/>https://fines.com.ua</a> стиль, уход за собой, психология, рецепты, материнство и карьера. Актуальные материалы, тренды и экспертные рекомендации каждый день.
Онлайн-сайт для женщин <a href=https://musicbit.com.ua/>https://musicbit.com.ua</a> стиль, уход за собой, психология, семья, карьера и хобби. Интересные статьи, тесты и форум для общения. Пространство для вдохновения и развития.
Женский сайт о жизни <a href=https://prettywoman.kyiv.ua/>https://prettywoman.kyiv.ua</a> секреты красоты, мода, здоровье, рецепты и отношения. Интересные статьи, советы и лайфхаки. Всё, что нужно, чтобы чувствовать себя уверенно и счастливо.
Для успешных покупок в интернете важно выбрать надёжную платформу, и
что такое mega предоставляет такие
условия. Платформа объединяет
продавцов, предлагая широкий выбор товаров, от модной одежды до уникальных аксессуаров.
Мега регулярно устраивает акции и скидки, что позволяет покупателям сэкономить.
Покупатели доверяют mega links за безопасность сделок и удобство.
Именно Мега продолжает быть лидером на рынке онлайн-шопинга.
мега как войти: https://xn--mea-sb-j6a.com
is a modern sportsbook and casino platform known for fast payouts <a href="https://distroid.net">betting australia</a>
Here you will find only the best: <a href=https://edicionesdelau.com/>https://edicionesdelau.com</a>
Онлайн-сайт про автомобили <a href=https://tvregion.com.ua/>https://tvregion.com.ua</a> свежие новости, аналитика рынка, обзоры и сравнения машин. Советы по обслуживанию и выбору авто. Всё для водителей и автолюбителей в одном месте.
Женский онлайн-журнал <a href=https://feminine.kyiv.ua/>https://feminine.kyiv.ua</a> мода, красота, здоровье, отношения и семья. Полезные советы, вдохновляющие статьи, лайфхаки для дома и карьеры. Всё самое интересное для современных женщин.
Автомобильный портал <a href=https://troeshka.com.ua/>https://troeshka.com.ua</a> онлайн-ресурс для автовладельцев. Каталог машин, тест-драйвы, аналитика авторынка и советы специалистов. Будьте в курсе новинок и технологий автоиндустрии.
The workwear is designed to meet the needs of employees <a href="https://www.zazzle.com/mbr/238310424506816442">https://www.zazzle.com/mbr/238310424506816442</a>
Hello .
Good evening. A 22 cool site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://changeville.ca/betting/egyptian-sports-betting/>https://banquedeterres.ca/gambling/what-kinds-of-games-national-casino-offers/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Hello .
Good evening. A 22 cool site 1 that I found on the Internet.
Check out this site. There's a great article there. <a href=https://changeville.ca/betting/egyptian-sports-betting/>https://banquedeterres.ca/gambling/what-kinds-of-games-national-casino-offers/</a>|
There is sure to be a lot of useful and interesting information for you here.
You'll find everything you need and more. Feel free to follow the link below.
Сайт для женщин <a href=https://femaleguide.kyiv.ua/>https://femaleguide.kyiv.ua</a> гармония стиля и жизни. Уход за собой, рецепты, дом, отношения, карьера и путешествия. Читайте статьи, делитесь опытом и вдохновляйтесь новыми идеями.
Автомобильный новостной портал <a href=https://tuning-kh.com.ua/>https://tuning-kh.com.ua</a> всё об авто в одном месте: новости, цены, обзоры, тест-драйвы, авторынок. Советы экспертов и полезные материалы для водителей и тех, кто планирует купить машину.
Сайт про машины <a href=https://tvk-avto.com.ua/>https://tvk-avto.com.ua</a> обзоры моделей, тест-драйвы, новости автопрома и советы по эксплуатации. Полезные статьи о выборе авто, уходе, ремонте и актуальные материалы для автовладельцев.
Женский онлайн портал <a href=https://femalesecret.kyiv.ua/>https://femalesecret.kyiv.ua</a> онлайн-ресурс для девушек и женщин. Мода, красота, здоровье, семья и материнство. Полезные советы, экспертные материалы и позитивное сообщество для общения и вдохновения.
Онлайн-сайт для женщин <a href=https://mirlady.kyiv.ua/>https://mirlady.kyiv.ua</a> красота, стиль, здоровье, дом и семья. Практичные рекомендации, модные идеи, вдохновение и поддержка. Лучший контент для девушек и женщин любого возраста.
Сайт для женщин <a href=https://amideya.com.ua/>https://amideya.com.ua</a> портал о красоте, стиле, здоровье, семье и саморазвитии. Ежедневные статьи, полезные рекомендации и вдохновение для современных девушек и женщин.
Женский сайт <a href=https://lubimoy.com.ua/>https://lubimoy.com.ua</a> стиль, уход за собой, психология, материнство, работа и хобби. Актуальные статьи, тренды и экспертные советы. Всё самое важное для гармоничной жизни и успеха.
Official mirror of Pin a p casino <a href="https://altadm.ru/">Pin Up casino</a>
To withdraw your winnings, wager the bonus 5x <a href="https://sportsfanbetting.com/tips/1xbet-promo-code-2026-welcome-bonus-100-up-to-e130/">https://sportsfanbetting.com/tips/1xbet-promo-code-2026-welcome-bonus-100-up-to-e130/</a>
Here is the best on the net: <a href=https://billi-walker.jp/>https://billi-walker.jp</a>
The latest data is right here: <a href=https://antalyamerhaba.com/>https://antalyamerhaba.com</a>
bonus on money deposited into their accounts, though the <a href="https://campbellriverskatingclub.com">https://campbellriverskatingclub.com</a>
При экспорте товаров важно правильно оформить документы <a href="https://tamozhenniy-broker3.ru/">таможенный брокер для юридических лиц</a>
Always relevant here: <a href=https://penzo.cz/>https://penzo.cz</a>
Catch the latest from us: <a href=https://chhapai.com/>https://chhapai.com</a>
Everything new is nearby: <a href=https://cere-india.org/>https://cere-india.org</a>
Сайт <a href=https://finance-post.ru/>finance-post.ru</a> — это блог финансиста, ориентированный на личные финансы, бюджетирование и инвестиции. На нём публикуются практические материалы, советы и обзоры
руководства по садоводству <a href=https://zelenayazona.ru/>https://zelenayazona.ru</a> идеи, инструкции и советы по уходу за садом и огородом. Информация для новичков и опытных дачников: посадка, полив, удобрение и защита растений.
Печатный Центр <a href=https://kopirych.by/>https://kopirych.by</a> «Копирыч» в Минске и по всей Беларуси! Оперативная печать, брошюровка, широкоформатная и сувенирная продукция. Качественно, недорого, с доставкой. Ваши идеи — наша реализация! Заказывайте на сайте или по телефону.
Современный женский <a href=https://happywoman.kyiv.ua/>https://happywoman.kyiv.ua</a> онлайн-журнал: новости стиля, секреты красоты, идеи для дома, кулинарные рецепты и советы по отношениям. Пространство для вдохновения и развития.
Женский сайт <a href=https://family-site.com.ua/>https://family-site.com.ua</a> современный портал о моде, красоте, отношениях и саморазвитии. Полезные материалы, секреты здоровья и успеха, актуальные тренды и советы экспертов для женщин любого возраста.
Семейный портал <a href=https://geog.org.ua/>https://geog.org.ua</a> всё для гармонии в доме: воспитание детей, отношения, здоровье, отдых и уют. Полезные советы, статьи и лайфхаки для всей семьи. Пространство, где находят ответы и вдохновение.
Упрощённое таможенное оформление — залог быстрой доставки <a href="https://tamozhenniy-broker3.ru/">таможеный брокер</a>
Женский онлайн портал <a href=https://femalesecret.kyiv.ua/>https://femalesecret.kyiv.ua</a> онлайн-ресурс для девушек и женщин. Мода, красота, здоровье, семья и материнство. Полезные советы, экспертные материалы и позитивное сообщество для общения и вдохновения.
Портал о здоровье <a href=https://mikstur.com/>https://mikstur.com</a> информационный ресурс о медицине и ЗОЖ. Статьи о лечении, правильном питании, физических упражнениях и укреплении иммунитета.
Информационный портал <a href=https://intertools.com.ua/>https://intertools.com.ua</a> о стройке: новости отрасли, советы по ремонту, выбору материалов и дизайну. Всё для тех, кто строит дом, делает ремонт или работает в строительстве.
Looking for new ways to spice up your relationship <a href="https://sex-positions.online/sk-SK">polohy pri sexe</a>
Browse online casino games like Slots, Blackjack, Baccarat <a href="https://www.facebook.com/groups/rainbetaustralia">Rain Bet</a>
Портал про детей <a href=https://mch.com.ua/>https://mch.com.ua</a> информационный ресурс для родителей. От беременности и ухода за малышом до воспитания школьников. Советы, статьи и поддержка для гармоничного развития ребёнка.
Женский онлайн-журнал <a href=https://girl.kyiv.ua/>https://girl.kyiv.ua</a> стиль, уход за собой, психология, кулинария, отношения и материнство. Ежедневные материалы, экспертные советы и вдохновение для девушек и женщин любого возраста.
Наша платформа работает круглосуточно и не знает слова перерыв. Бронировать и планировать можно где угодно: в поезде, на даче, в кафе или лежа на диване <a href=https://probilets.com/>https://probilets.com/</a>. Хотите купить билет, пока идёте по супермаркету? Просто достаньте телефон и оформите поездку. Нужно скорректировать планы, отменить или перенести билет? Это тоже можно сделать онлайн, без звонков и визитов. Но если возникла проблема, то наши специалисты помогут и все расскажут
Стоматологическое оборудование с большим выбором ассортимента от автолкавов до наконечников и airflow <a href="https://stomprice.com/catalog/peskostruynye-nakonechniki/apparat-peskostruynyy-coxo-c101-c101-cp-1-s-dvumya-nakonechnikami/">https://stomprice.com/catalog/peskostruynye-nakonechniki/apparat-peskostruynyy-coxo-c101-c101-cp-1-s-dvumya-nakonechnikami/</a>
турецкие сериалы https://bryansktoday.ru/article/246702
Онлайн-журнал <a href=https://presslook.com.ua/>https://presslook.com.ua</a> для женщин объединяет всё, что важно: мода и стиль, воспитание детей, карьерные советы и вдохновение. Советы специалистов и реальные истории для поддержки и новых идей.
Твой гид <a href=https://nicegirl.kyiv.ua/>https://nicegirl.kyiv.ua</a> по здоровому образу жизни! Эффективные тренировки, сбалансированное питание, wellness-практики и советы по мотивации. Обрети энергию, силу и гармонию в теле, которое ты любишь.
Актуальные тренды <a href=https://horoscope-web.com/>https://horoscope-web.com</a> и вневременная классика. Подборки образов, советы по стилю, секреты гардероба и модные инсайты. Мы поможем тебе выглядеть безупречно каждый день и выразить свой индивидуальный стиль.
Ресурс для амбициозных <a href=https://ramledlightings.com/>https://ramledlightings.com</a> и целеустремленных. Карьерный рост, личная эффективность, финансовая грамотность и вдохновляющие истории успеха. Реализуй свой потенциал и добивайся всех поставленных целей!
An important part remains the tools of responsible gaming <a href="https://admprigkalach.ru/">https://admprigkalach.ru/</a>
Working mirrors of 1win casino are located on the specified domains <a href="https://t.me/s/onewincasinotoday">1win casino зеркало</a>
Турецкие сериалы https://www.bnkomi.ru/data/relize/189683/
Аниме онлайн https://www.bnkomi.ru/data/relize/189684/
When it comes to managing your funds at Cleobetra <a href="https://cleobetracasinoreview.com">Cleobetra</a>
Журнал для женщин <a href=https://rpl.net.ua/>https://rpl.net.ua</a> которые строят карьеру и хотят большего. Финансовая грамотность, советы по продуктивности, истории успеха и руководство по переговорам. Достигайте своих целей с нами!
https://teletype.in/@stop__scam/CfhxB5olKV8
Твой гид <a href=https://womanlife.kyiv.ua/>https://womanlife.kyiv.ua</a> по стильной жизни. Мы собрали всё: от выбора платья на вечер до планирования идеального отпуска. Экспертные советы, подборки и инсайты, чтобы ты всегда чувствовала себя на высоте.
Онлайн-журнал о моде <a href=https://glamour.kyiv.ua/>https://glamour.kyiv.ua</a> без правил. Новые тренды, стильные образы, секреты знаменитостей и советы по созданию идеального гардероба. Мы поможем вам найти и с уверенностью выразить свой уникальный стиль.
Женский сайт <a href=https://bbb.dp.ua/>https://bbb.dp.ua</a> всё самое важное для современных девушек: стиль, красота, здоровье, отношения и самореализация. Читайте, вдохновляйтесь и находите новые идеи.
Step One: Visit the Cleobetra website and click on the <a href="https://cleobetracasinobonus.com">Cleobetra Casino Online</a>
The journey begins with the Welcome Pharaoh’s Package <a href="https://cleobetracasinologin.com">Cleobetra</a>
Новостной портал Украины <a href=https://lenta.kyiv.ua/>https://lenta.kyiv.ua</a> оперативные события в стране. Политика, экономика, региональные новости, спорт и культура. Достоверные материалы и аналитика каждый день.
Свежие новости <a href=https://sensus.org.ua/>https://sensus.org.ua</a> Украины и мира: главные события, репортажи и аналитика. Политика, экономика, общество и культура в удобном формате онлайн.
Новостной сайт <a href=https://vesti.in.ua/>https://vesti.in.ua</a> свежие события дня: политика, экономика, культура, спорт, технологии и общество. Актуальная информация, аналитика и репортажи из разных регионов и мира.
Свежие новости Украины <a href=https://novosti24.kyiv.ua/>https://novosti24.kyiv.ua</a> главные события, мнения экспертов и аналитические материалы. Лента новостей онлайн, репортажи и достоверные факты без перерыва.
<a href=https://simcorner.com/blogs/traveltips/best-esim-for-europe>Europe SIM Card</a>
buy ed meds pills
If you’re someone who enjoys the perks of digital wallets, Skrill and Neteller <a href="https://cleobetracasinologin.com">Cleobetra</a>
Новости Украины <a href=https://status.net.ua/>https://status.net.ua</a> объективная информация о событиях страны. Политика, экономика, региональные новости, спорт и культура. Читайте актуальные материалы каждый день.
Новостной портал <a href=https://mediateam.com.ua/>https://mediateam.com.ua</a> всё самое важное сегодня: политика, экономика, культура, спорт и шоу-бизнес. Лента новостей, репортажи и аналитические материалы каждый день.
Новости Украины и мира <a href=https://mostmedia.com.ua/>https://mostmedia.com.ua</a> политика, экономика, культура, спорт и общество. Свежие события, аналитика и репортажи. Будьте в курсе главных новостей в режиме онлайн 24/7.
Необходимо кодирование? <a href=https://zelenorgad-rehab.ru/>наркологический центр</a> современные методы, конфиденциальность и поддержка специалистов. Помогаем избавиться от зависимости и вернуться к здоровой жизни.
blacksprut блэкспрут black sprut блэк спрут blacksprut вход блэкспрут ссылка blacksprut ссылка blacksprut onion блэкспрут сайт блэкспрут вход блэкспрут онион блэкспрут дакрнет blacksprut darknet blacksprut сайт блэкспрут зеркало blacksprut зеркало black sprout blacksprut com зеркало блэкспрут не работает blacksprut зеркала как зайти на blacksprut
Аренда авто <a href=https://myrentacar.site/>https://myrentacar.site</a> широкий выбор автомобилей для любых целей. Удобное бронирование, доступные цены, страхование и гибкие условия. Машины в отличном состоянии для поездок по городу и путешествий.
Строительство домов в Сочи <a href=https://stroitelstvodomovsochi.ru/>https://stroitelstvodomovsochi.ru</a> под ключ — профессиональный подход, проверенные материалы и гарантия качества. Полный спектр работ: проект, строительство, отделка и благоустройство.
вывод из запоя платно <a href=https://sv-clinica.ru/>вызвать нарколога на дом анонимно Томск</a>
<a href=https://www.colabinc.com>как зайти на blacksprut</a> blacksprut блэкспрут black sprut блэк спрут blacksprut вход блэкспрут ссылка blacksprut ссылка blacksprut onion блэкспрут сайт блэкспрут вход блэкспрут онион блэкспрут дакрнет blacksprut darknet blacksprut сайт блэкспрут зеркало blacksprut зеркало black sprout blacksprut com зеркало блэкспрут не работает blacksprut зеркала как зайти на blacksprut
Онлайн новостной портал <a href=https://reporternews.net/>https://reporternews.net</a> главные события дня, эксклюзивные интервью, мнения экспертов и репортажи. Достоверная информация о политике, бизнесе и жизни общества.
Новостной портал <a href=https://newsawait.com/>https://newsawait.com</a> свежие новости, аналитика и обзоры. Политика, экономика, культура и спорт. Лента событий в режиме реального времени с проверенными фактами.
Портал про авто <a href=https://dream-autos.com/>https://dream-autos.com</a> новости, обзоры и тест-драйвы. Полезные советы по выбору, ремонту и эксплуатации автомобилей. Каталог машин, актуальные цены и аналитика авторынка.
<a href=https://www.colabinc.com>blacksprut зеркала</a> blacksprut блэкспрут black sprut блэк спрут blacksprut вход блэкспрут ссылка blacksprut ссылка blacksprut onion блэкспрут сайт блэкспрут вход блэкспрут онион блэкспрут дакрнет blacksprut darknet blacksprut сайт блэкспрут зеркало blacksprut зеркало black sprout blacksprut com зеркало блэкспрут не работает blacksprut зеркала как зайти на blacksprut
For this, a special field is provided in the registration form <a href="http://www.nursingportal.ca/author/codebonus1xbet/">http://www.nursingportal.ca/author/codebonus1xbet/</a>
Портал для женщин <a href=https://womanfashionista.com/>https://womanfashionista.com</a> всё самое важное в одном месте: уход за собой, мода, дом, семья и карьера. Читайте полезные статьи, находите вдохновение и делитесь опытом.
Новости Украины и мира <a href=https://globalnewshome.com/>https://globalnewshome.com</a> всё самое важное сегодня. Политика, экономика, региональные события, спорт и культура. Объективные статьи и аналитика в удобном формате.
Сайт детского сада <a href=https://malush16.ru/>https://malush16.ru</a> МКДОУ 16 «Малыш» Омутнинского района — документы, образовательные стандарты, новости, фотогалерея и полезные материалы для родителей и педагогов.
<a href=https://mndiscjockeys.com>Мега онион</a> Мега даркнет Мега сайт Мега онион Мега ссылка Mega даркнет Mega сайт Mega онион Mega ссылка Mega darknet Mega onion
Cleobetra Casino is the queen of slots and other games <a href="https://cleobetraonlinecasino.com">Cleobetra Casino Online</a>
Статьи для садоводов <a href=https://portalteplic.ru/>https://portalteplic.ru</a> огородников, фермеров и пчеловодов: советы по уходу за растениями, животными и пасекой. Полезные инструкции, лайфхаки и сезонные рекомендации.
Сайт про металлопрокат <a href=https://the-master.ru/>https://the-master.ru</a> каталог продукции, характеристики и сферы применения. Арматура, балки, трубы, листы и профили. Актуальные цены, советы специалистов и полезные статьи.
<a href=https://www.singlevisioninc.org/>Mega даркнет</a> Мега даркнет Мега сайт Мега онион Мега ссылка Mega даркнет Mega сайт Mega онион Mega ссылка Mega darknet Mega onion
Всё про ремонт <a href=https://gbu-so-svo.ru/>https://gbu-so-svo.ru</a> и строительство — статьи, инструкции и советы для мастеров и новичков. Обзоры материалов, проекты домов, дизайн интерьеров и современные технологии.
Строительный портал <a href=https://krovlyaikrysha.ru/>https://krovlyaikrysha.ru</a> база знаний и идей. Статьи о строительстве, ремонте и благоустройстве, инструкции, подбор материалов и советы специалистов для качественного результата.
Автомобильный портал <a href=https://ivanmotors.ru/>https://ivanmotors.ru</a> всё о машинах в одном месте. Тест-драйвы, обзоры, аналитика авторынка и советы специалистов. Актуальные события мира авто для водителей и экспертов.
<a href=https://loafer17888.com/>樂富</a>
Сайт для женщин <a href=https://devchenky.ru/>https://devchenky.ru</a> всё самое важное в одном месте: семья, дети, красота, здоровье, дом и работа. Советы специалистов, лайфхаки и вдохновение на каждый день.
Сайт о ремонте <a href=https://e-proficom.ru/>https://e-proficom.ru</a> полезные статьи, пошаговые инструкции и советы экспертов. От выбора материалов до дизайна интерьеров. Всё, что нужно для ремонта квартир и домов.
Блог о ремонте <a href=https://ivinstrument.ru/>https://ivinstrument.ru</a> полезные статьи, пошаговые инструкции и советы экспертов. Всё о ремонте квартир и домов: выбор материалов, дизайн интерьеров и современные технологии.
Современные наливные полы <a href=https://proffi-floor.ru/>https://proffi-floor.ru</a> это не только идеально ровная поверхность, но и долговечность покрытия. Если вы планируете ремонт в квартире или офисе, узнайте подробнее об услугах по устройству наливных полов
<a href=https://www.singlevisioninc.org/>Mega сайт</a> Мега даркнет Мега сайт Мега онион Мега ссылка Mega даркнет Mega сайт Mega онион Mega ссылка Mega darknet Mega onion
Городской портал Москвы <a href=https://moscowfy.ru/>https://moscowfy.ru</a> свежие новости столицы, афиша мероприятий, транспорт, жильё, работа и сервисы для жителей. Полезная информация для москвичей и гостей города на одном сайте.
Гаражи и каркас гаража. Такие конструкции пользуются особой популярностью <a href="https://xn--80aaef8dd.xn--p1ai/">https://xn--80aaef8dd.xn--p1ai/</a>
Стандартные размеры каркасов гаражей <a href="https://xn--80aaef8dd.xn--p1ai/">https://xn--80aaef8dd.xn--p1ai/</a>
Яндекс Бизнес <a href=https://business-yandex3.ru/>https://business-yandex3.ru</a> описание сервиса, его инструменты и функции. Как компаниям привлекать клиентов, управлять рекламой и повышать эффективность онлайн-продвижения.
Подборка статей <a href=https://yandex-direct-info.ru/>https://yandex-direct-info.ru</a> про Яндекс Директ: пошаговые инструкции, советы по таргетингу, ретаргетингу и аналитике. Всё о рекламе в Яндексе в одном месте для вашего бизнеса.
Thanks to this code, players can take advantage of various offers <a href="https://about.me/codespromo1xbet/getstarted">https://about.me/codespromo1xbet/getstarted</a>
Игра в города <a href=https://malimar.ru/goroda-na-bukvu-o-i-pravila-klassicheskoj-igry/>https://malimar.ru/goroda-na-bukvu-o-i-pravila-klassicheskoj-igry/</a> для всех возрастов. Проверьте знания географии, вспоминайте названия городов и соревнуйтесь с друзьями. Увлекательная логическая игра для тренировки памяти и эрудиции.
Details are waiting for you here: <a href=https://www.guidasposi.it/>https://www.guidasposi.it</a>
Only verified facts are here: <a href=https://trakdag.com/>https://trakdag.com</a>
Курсы нутрициологии — шанс разобраться в том, как питание влияет на здоровье, энергию и качество жизни <a href="http://neurobiotech.ru/">http://neurobiotech.ru/</a>
Read the best here: <a href=https://elitetravelgroup.net>https://elitetravelgroup.net/</a>
Everything you need: <a href=https://stovespareparts.ie/>https://stovespareparts.ie</a>
News for you - right here: <a href=https://www.colehardware.com/>https://www.colehardware.com</a>
Hot news is already here: <a href=https://brandmasteracademy.com/>https://brandmasteracademy.com</a>
<a href=https://atgseth1.com/>戰神賽特選台</a>
https://atgseth1.com/how-to-read-the-atg-ares-set-signal/
https://atgseth1.com/god-seth-jackpot-grand/
Топливные карты <a href=https://karta-vezdehod.ru/>https://karta-vezdehod.ru</a> удобный способ экономить на заправках, контролировать расходы и получать прозрачную отчетность.
Топливные карты <a href=https://auto-nv.ru/>https://auto-nv.ru</a> для юр лиц — это надежный инструмент учета топлива, скидки на АЗС и удобная онлайн-отчетность.
Топливная карта <a href=https://autobsn.ru/>https://autobsn.ru</a> для юридических лиц дает доступ к выгодным тарифам, снижает расходы и делает контроль проще.
Профессиональный и срочный ремонт стиральных машин любой марки на дому https://vk.com/spb_remont_stiralnih_mashin
Что такое CPI <a href=https://cost-per-install.ru/>https://cost-per-install.ru</a> в маркетинге? Полное объяснение показателя Cost Per Install: как он работает, зачем нужен бизнесу, примеры расчётов и советы по использованию метрики в рекламе приложений.
<a href=https://www.luxtor.pe/>perfumes de mujer originales</a>
Luxtor Perú es tu tienda online de confianza con más de 10,000 artículos en perfumes importados y originales, maquillaje, cuidado personal y electrohogar, ofreciendo las mejores marcas como Natura, Yanbal, Cyzone, Ésika, L’Bel y Avon con precios especiales y promociones exclusivas.
buy xtc prague <a href=https://cocaine-prague-shop.com/>buy xtc prague</a>
buy coke in prague <a href=https://cocaine-prague-shop.com/>https://cocaine-prague-shop.com</a>
Графитовые и угольные <a href=https://elcont31.ru/shchetki-elektricheskie>щетки</a> для электроинструмента. Большой выбор, надёжность и долговечность. Подходят для дрелей, болгарок, перфораторов и другого оборудования.
Трубчатые радиаторы отопления - стильные и эффективные приборы <a href="https://salda.ws/f/topic.php?f=5&t=85911">https://salda.ws/f/topic.php?f=5&t=85911</a>
buy coke in telegram <a href=https://cocaine-prague-shop.com/>https://cocaine-prague-shop.com</a>
ПГС карьерный доставка <a href=https://pesko.ru/>поставка строительных материалов оптом</a>
Расчёт довольствия Росгвардия: специальное звание капитан, 55 000 руб. плюс боевые, если СВО.<a href=https://svoinfo.ru/>расчёт оклада военнослужащего</a>
<a href=https://tgboostup.ru/>накрутка подписчиков в тг канал бесплатно</a>
Интернет-маркетинг <a href=https://internet-marketing1.ru/>https://internet-marketing1.ru</a> SEO, контекстная реклама, SMM, email-рассылки и аналитика. Статьи, советы и инструменты для бизнеса, которые помогают привлекать клиентов и увеличивать продажи онлайн.
Saudações, excelente site mostbet, bravo!
mostbet online
Фильтры и насосы для бассейна - отвечающие за очистку и циркуляцию воды <a href="https://aquabuilding.ru/catalog/oborudovanie-dlya-basseynov/">Оборудование для бассейнов Сочи</a>
We continuously update our collection with new releases and popular titles <a href="https://smokemama.com/slot/sizzling-hot-deluxe/">Sizzling Hot Deluxe Online</a>
На сайте <a href=https://www.detskiyklass.ru/>Детский Класс</a> нашим посетителям в любое время доступны материалы для приятного совместного досуга детей и их родителей: детские песни на разные тематики, которые можно разучивать и распевать в будни и праздники, интересные и познавательные легенды и мифы, раскраски различной сложности, а также волшебные и поучительные сказки.
<a href=https://tgbuff.ru/>накрутить подписчиков в тг</a>
Мега - это ваш путь к покупкам без стресса.
В ассортименте Мега представлены все
товары, от новейших гаджетов до редких вещей.
Благодаря удобной доставке и
беззаботному возврату товаров, ссылка на мега тор делает покупки комфортными.
Совершая покупки на что такое мега сайт, вы получаете
ежедневные скидки, эксклюзивные предложения и многое другое.
Не ждите - делайте покупки умнее и
экономьте время с Mega уже сегодня!.
мега даркнет ссылка: https://xn--mea-sb-j6a.com
Opens the door to a world of gambling entertainment <a href="https://elt-tsu.ru/">https://elt-tsu.ru/</a>
One way to receive a gift from a popular bookmaker is to activate a bonus <a href="https://preventcrookedteeth.com/2011-02-25-ltr-from-paul-beresford-mp-of-gov/">https://preventcrookedteeth.com/2011-02-25-ltr-from-paul-beresford-mp-of-gov/</a>
Bookmaker Melbet quite often pleases its active new players with <a href="https://pdtgeneve.ch/lib/inc/code_promo_1xbet_bonus.html">https://pdtgeneve.ch/lib/inc/code_promo_1xbet_bonus.html</a>
Всё о Москве <a href=https://moscowfy.ru/>https://moscowfy.ru</a> в одном месте: городской портал с новостями, афишей, расписанием транспорта, объявлениями и услугами. Полезные материалы для москвичей и туристов.
Женский портал <a href=https://devchenky.ru/>https://devchenky.ru</a> секреты красоты, модные тенденции, здоровье, любовь и кулинария. Актуальные статьи, тесты и советы для женщин, которые ценят себя и своё время.
Портал о строительстве <a href=https://e-proficom.ru/>https://e-proficom.ru</a> и ремонте: полезные статьи, советы специалистов, обзоры материалов и технологий. Всё для тех, кто планирует ремонт квартиры, дома или дачи.
You can think about the selection of a name <a href="https://www.andevis.ee/wp-content/pages/?chto_harakterizuet_ispravno_rabotayuschuyu_elektroustanovku.html">https://www.andevis.ee/wp-content/pages/?chto_harakterizuet_ispravno_rabotayuschuyu_elektroustanovku.html</a>
Строительные материалы <a href=https://stroy-marketplace.ru/>https://stroy-marketplace.ru</a> в Серпухове: кирпич, цемент, сухие смеси, пиломатериалы и утеплители. Большой выбор для ремонта и строительства, доставка по городу и району.
Компания Единство <a href=https://edinvent.ru/>https://edinvent.ru</a> производитель и комплексный поставщик приточно-вытяжных установок, вентиляционных установок, а также систем автоматического управления климатическим оборудованием.
Женский блог <a href=https://www.evasolar.ru/>https://www.evasolar.ru</a> о здоровье и красоте: советы по уходу за собой, правильному питанию, фитнесу и косметике. Полезные статьи, лайфхаки и вдохновение для гармоничной и счастливой жизни.
Ремонт під’їздів замовляють через <a href=https://remontuem.te.ua>remontuem.te.ua</a>
Joaca <a href=https://jocwarships.top/>joc World of Warships</a> gratuit! Exploreaza marile, folose?te-?i strategia ?i condu nave de razboi celebre. Batalii realiste ?i echipe interna?ionale te a?teapta.
Jogue <a href=https://pandajogos.top/>pandajogos.top</a> e descubra o charme do Oriente! Rolos coloridos, recursos bonus, rodadas gratis e surpresas que trazem ganhos espetaculares.
ваш провідник у житті Львова <a href=https://79000.com.ua/>https://79000.com.ua</a> актуальні новини, культурні та громадські події міста, урбаністика, інтерв’ю з цікавими людьми, фотоогляди локальних заходів. Все про те, що формує атмосферу Львова сьогодні — оновлення, проекти, історії.
ООО "Мир ремней" <a href=https://yandex.ru/profile/147633783627>https://yandex.ru/profile/147633783627</a> Производство приводных ремней, тефлоновых сеток и лент - телефон +7 (936) 333-93-03
These codes can provide additional perks, such as free bets <a href="https://www.tusonline.cc/blog/shopping/journal-blog">https://www.tusonline.cc/blog/shopping/journal-blog</a>
микрозайм взять <a href=https://dengibuduts.ru/>микрозаймы онлайн</a>
микрозаймы онлайн <a href=https://festenmoney.ru/>онлайн займы</a>
The official 1Win website operates under an international Curacao license <a href="https://mshow.ru">https://mshow.ru</a>
Перевод с арабского - <a href=https://byuro-perevodov.su/>переводческое бюро</a>. Перевод для автомобильной промышленности в Самаре. Каталоги запчастей, руководства по ремонту, ТУ. Опыт работы с крупными автопроизводителями.
ліжко на замовлення <a href=https://remontuem.te.ua/>https://remontuem.te.ua</a>
<a href=https://tggain.ru/>купить реальных подписчиков в телеграм</a>
<a href=https://tgfork.ru/>накрутка настоящих подписчиков в телеграм канале</a>
Platform migration experience: buy fifa coins pc versus console markets show different seller ecosystems entirely. <a href=https://www.reddit.com/r/GamingInsider/comments/1nnkoq4/where_to_buy_fifa_coins_any_recommendations_for/>Buy fifa coins</a> decision should factor in your platform's specific community and the safest transfer methods available per system.
Записаться к дерматологу <a href=https://www.docplus24.ru/>https://www.docplus24.ru</a>
buy cocaine prague <a href=https://weed-cannabis-europe.com/>high quality cocaine in prague</a>
Bi-Winning Binary Options bring a fresh approach to online trading <a href="https://newssokuho.jp/">https://newssokuho.jp/</a>
Продажа авто в ОАЭ <a href=https://auto.ae/ru/sale/car/all/?page=1>https://auto.ae/ru/sale/car/all/?page=1</a> новые и подержанные автомобили с гарантией качества. Большой выбор, доступные цены и юридическая прозрачность сделок для покупателей.
Bubinga Binary Options give traders the chance to act quickly <a href="https://newssokuho.jp/">https://newssokuho.jp/</a>
Авто в ОАЭ <a href=https://auto.ae/>https://auto.ae</a> покупка, продажа и аренда новых и б/у машин. Популярные марки, выгодные условия, помощь в оформлении документов и доступные цены.
<a href=https://tgman.ru/>накрутить подписчиков в телеграм канал живых</a>
Upon fulfilling all requirements, you receive entry <a href="https://www.imdb.com/de/list/ls4106200608/">https://www.imdb.com/de/list/ls4106200608/</a>
микрозайм оформить <a href=https://zaimnakartu1.ru/>займы онлайн</a>
prague plug <a href=https://buy-marijuana-europe.com/>plug in prague</a>
Заметки практикующего врача <a href=https://phlebolog-blog.ru/>https://phlebolog-blog.ru</a> флеболога. Профессиональное лечение варикоза ног. Склеротерапия, ЭВЛО, УЗИ вен и точная диагностика. Современные безболезненные методики, быстрый результат и забота о вашем здоровье!
микрозаймы онлайн <a href=https://zaimnakartu1.ru/>микрозаймы</a>
ИТ-консультанты — это команда специалистов в технологиях, программах и бизнес <a href="https://telegra.ph/Biznes-konsalting-kak-vystroit-upravlyaemyj-rost-i-snizit-riski-v-menyayushchejsya-ehkonomike-09-24">бизнес экспертиза консалтинг</a>
prague plug <a href=https://marijuana-delivery-europe.com/>prague plug</a>
<a href=https://tgmodo.ru/>накрутка подписчиков телеграм 100 подписчиков</a>
vhq cocaine in prague <a href=https://marijuana-delivery-europe.com/>buy weed prague</a>
cocaine in prague <a href=https://marijuana-shop-europe.com/>buy mdma prague</a>
I dream to visit the different nations, to obtain acquainted with fascinating people <a href="https://multipurpose-wapuula.com/userinfo.php?mod=space&userinfo=edwin-bird_473117&name=Your_Account&action=view">https://multipurpose-wapuula.com/userinfo.php?mod=space&userinfo=edwin-bird_473117&name=Your_Account&action=view</a>
Нужна презентация? <a href=https://generator-prezentaciy.ru/>генератор презентаций без регистрации</a> Создавайте убедительные презентации за минуты. Умный генератор формирует структуру, дизайн и иллюстрации из вашего текста. Библиотека шаблонов, фирстиль, графики, экспорт PPTX/PDF, совместная работа и комментарии — всё в одном сервисе.
cocaine in prague <a href=https://cannabis-delivery-europe.com/>cocaine prague</a>
vhq cocaine in prague <a href=https://cannabis-shop-europe.com/>cocaine prague</a>
cocaine prague telegram <a href=https://cannabis-delivery-europe.com/>plug in prague</a>
buy weed prague <a href=https://cannabis-shop-europe.com/>buy mdma prague</a>
Нужна презентация? <a href=https://generator-prezentaciy.ru/>ии генератор презентации powerpoint</a> Создавайте убедительные презентации за минуты. Умный генератор формирует структуру, дизайн и иллюстрации из вашего текста. Библиотека шаблонов, фирстиль, графики, экспорт PPTX/PDF, совместная работа и комментарии — всё в одном сервисе.
Компания специализируется на изготовлении ключей в Минске <a href="https://hyundai-sto.ru/osobennosti-izgotovleniya-chip-klyuchej.html">https://hyundai-sto.ru/osobennosti-izgotovleniya-chip-klyuchej.html</a>
Проблемы с откачкой? <a href=https://otkachka-vody.ru/>помпа для откачки воды</a> сдаем в аренду мотопомпы и вакуумные установки: осушение котлованов, подвалов, септиков. Производительность до 2000 л/мин, шланги O50–100. Быстрый выезд по городу и области, помощь в подборе. Суточные тарифы, скидки на долгий срок.
prague drugs <a href=https://buy-weed-europe.com/>prague drugs</a>
Проблемы с откачкой? <a href=https://otkachka-vody.ru/>насос для откачки воды</a> сдаем в аренду мотопомпы и вакуумные установки: осушение котлованов, подвалов, септиков. Производительность до 2000 л/мин, шланги O50–100. Быстрый выезд по городу и области, помощь в подборе. Суточные тарифы, скидки на долгий срок.
plug in prague <a href=https://buy-cannabis-europe.com/>buy coke in telegram</a>
buy cocaine in telegram <a href=https://buy-marijuana-europe.com/>prague drugstore</a>
buy weed prague <a href=https://buy-cannabis-europe.com/>columbian cocain in prague</a>
buy mdma prague <a href=https://weed-shop-europe.com/>cocaine prague</a>
Zivjeti u Crnoj Gori? <a href=https://www.placevi-zabljak-nekretnine.com/>https://www.placevi-zabljak-nekretnine.com</a> Novi apartmani, gotove kuce, zemljisne parcele. Bez skrivenih provizija, trzisna procjena, pregovori sa vlasnikom. Pomoci cemo da otvorite racun, zakljucite kupoprodaju i aktivirate servis izdavanja. Pisite — poslacemo vam varijante.
buy coke in telegram <a href=https://weed-shop-europe.com/>cocain in prague from brazil</a>
Zivjeti u Crnoj Gori? <a href=https://www.placevi-zabljak-nekretnine.com/>prodaja nekretnina Zabljak</a> Novi apartmani, gotove kuce, zemljisne parcele. Bez skrivenih provizija, trzisna procjena, pregovori sa vlasnikom. Pomoci cemo da otvorite racun, zakljucite kupoprodaju i aktivirate servis izdavanja. Pisite — poslacemo vam varijante.
Портал о строительстве <a href=https://gidfundament.ru/>https://gidfundament.ru</a> и ремонте: обзоры материалов, сравнение цен, рейтинг подрядчиков, тендерная площадка, сметные калькуляторы, образцы договоров и акты. Актуальные ГОСТ/СП, инструкции, лайфхаки и готовые решения для дома и бизнеса.
Смотрите онлайн <a href=https://www.multi-film.ru/load/>аудиосказки и аудиокниги слушать онлайн</a> лучшие детские мультфильмы, сказки и мульсериалы. Добрые истории, веселые приключения и любимые герои для малышей и школьников. Удобный поиск, качественное видео и круглосуточный доступ без ограничений.
Портал о строительстве <a href=https://gidfundament.ru/>https://gidfundament.ru</a> и ремонте: обзоры материалов, сравнение цен, рейтинг подрядчиков, тендерная площадка, сметные калькуляторы, образцы договоров и акты. Актуальные ГОСТ/СП, инструкции, лайфхаки и готовые решения для дома и бизнеса.
Смотрите онлайн <a href=https://www.multi-film.ru/load/>аудиосказки и аудиокниги слушать онлайн</a> лучшие детские мультфильмы, сказки и мульсериалы. Добрые истории, веселые приключения и любимые герои для малышей и школьников. Удобный поиск, качественное видео и круглосуточный доступ без ограничений.
Мир гаджетов <a href=https://indevices.ru/>https://indevices.ru</a> новости, обзоры и тесты смартфонов, ноутбуков, наушников и умного дома. Сравнения, рейтинги автономности, фото/видео-примеры, цены и акции. Поможем выбрать устройство под задачи и бюджет. Подписка на новые релизы.
Всё о ремонте <a href=https://remontkit.ru/>https://remontkit.ru</a> и строительстве: технологии, нормы, сметы, каталоги материалов и инструментов. Дизайн-идеи для квартиры и дома, цветовые схемы, 3D-планы, кейсы и ошибки. Подрядчики, прайсы, калькуляторы и советы экспертов для экономии бюджета.
Женский портал <a href=https://art-matita.ru/>https://art-matita.ru</a> о жизни и балансе: модные идеи, уход за кожей и волосами, здоровье, йога и фитнес, отношения и семья. Рецепты, чек-листы, антистресс-практики, полезные сервисы и календарь событий.
Мир гаджетов <a href=https://indevices.ru/>https://indevices.ru</a> новости, обзоры и тесты смартфонов, ноутбуков, наушников и умного дома. Сравнения, рейтинги автономности, фото/видео-примеры, цены и акции. Поможем выбрать устройство под задачи и бюджет. Подписка на новые релизы.
Все автоновинки <a href=https://myrexton.ru/>https://myrexton.ru</a> премьеры, тест-драйвы, характеристики, цены и даты продаж. Электромобили, гибриды, кроссоверы и спорткары. Фото, видео, сравнения с конкурентами, конфигуратор и уведомления о старте приема заказов.
Всё о ремонте <a href=https://remontkit.ru/>https://remontkit.ru</a> и строительстве: технологии, нормы, сметы, каталоги материалов и инструментов. Дизайн-идеи для квартиры и дома, цветовые схемы, 3D-планы, кейсы и ошибки. Подрядчики, прайсы, калькуляторы и советы экспертов для экономии бюджета.
Женский портал <a href=https://art-matita.ru/>https://art-matita.ru</a> о жизни и балансе: модные идеи, уход за кожей и волосами, здоровье, йога и фитнес, отношения и семья. Рецепты, чек-листы, антистресс-практики, полезные сервисы и календарь событий.
Get started with 1xBet today using the promo code <a href="https://www.intensedebate.com/profiles/haroldgish">https://www.intensedebate.com/profiles/haroldgish</a>
The Harvard Film Archive is a cinematheque and a film archive dedicated <a href="https://www.sjuntorpsbiltjanst.se/">https://www.sjuntorpsbiltjanst.se/</a>
Новостной портал <a href=https://daily-inform.ru/>https://daily-inform.ru</a> главные события дня, репортажи, аналитика, интервью и мнения экспертов. Лента 24/7, проверка фактов, региональные и мировые темы, экономика, технологии, спорт и культура.
Всё о стройке <a href=https://lesnayaskazka74.ru/>https://lesnayaskazka74.ru</a> и ремонте: технологии, нормы, сметы и планирование. Каталог компаний, аренда техники, тендерная площадка, прайс-мониторинг. Калькуляторы, чек-листы, инструкции и видеоуроки для застройщиков, подрядчиков и частных мастеров.
Строительный портал <a href=https://nastil69.ru/>https://nastil69.ru</a> новости, аналитика, обзоры материалов и техники, каталог поставщиков и подрядчиков, тендеры и прайсы. Сметные калькуляторы, ГОСТ/СП, шаблоны договоров, кейсы и лайфхаки.
изготовление значков на заказ москва <a href=https://metal-pin.ru/>заказ значков в москве</a>
Актуальные новости <a href=https://pr-planet.ru/>https://pr-planet.ru</a> без лишнего шума: политика, экономика, общество, наука, культура и спорт. Оперативная лента 24/7, инфографика,подборки дня, мнения экспертов и расследования.
Новостной портал <a href=https://daily-inform.ru/>https://daily-inform.ru</a> главные события дня, репортажи, аналитика, интервью и мнения экспертов. Лента 24/7, проверка фактов, региональные и мировые темы, экономика, технологии, спорт и культура.
Строительный портал <a href=https://nastil69.ru/>https://nastil69.ru</a> новости, аналитика, обзоры материалов и техники, каталог поставщиков и подрядчиков, тендеры и прайсы. Сметные калькуляторы, ГОСТ/СП, шаблоны договоров, кейсы и лайфхаки.
Актуальные новости <a href=https://pr-planet.ru/>https://pr-planet.ru</a> без лишнего шума: политика, экономика, общество, наука, культура и спорт. Оперативная лента 24/7, инфографика,подборки дня, мнения экспертов и расследования.
The main areas for betting are team sports such as football, hockey, basketball <a href="https://www.noteflight.com/profile/9204e0ce5659ed85eff707dba03a07994a2b0dc9">https://www.noteflight.com/profile/9204e0ce5659ed85eff707dba03a07994a2b0dc9</a>
<a href=https://tgnew.ru/>накрутка подписчиков телеграм без заданий</a>
Ремонт и стройка <a href=https://stroimsami.online/>https://stroimsami.online</a> без лишних затрат: гайды, сметы, план-графики, выбор подрядчика и инструмента. Честные обзоры, сравнения, лайфхаки и чек-листы. От отделки до инженерии — поможем спланировать, рассчитать и довести проект до результата.
Ремонт и стройка <a href=https://stroimsami.online/>https://stroimsami.online</a> без лишних затрат: гайды, сметы, план-графики, выбор подрядчика и инструмента. Честные обзоры, сравнения, лайфхаки и чек-листы. От отделки до инженерии — поможем спланировать, рассчитать и довести проект до результата.
<a href=https://plenka-okna.ru/>https://plenka-okna.ru/</a>
вартість штукатурки <a href=https://remontuem.te.ua/>https://remontuem.te.ua</a>
Harvard Film Archive website In recent years landscape <a href="https://vtab.se/">https://vtab.se/</a>
This format ensures freedom, supporting you to put together <a href="https://www.imdb.com/list/ls4150041733/">https://www.imdb.com/list/ls4150041733/</a>
buy propecia no rx
значки с лого <a href=https://metalpin.ru/>печать на значках москва</a>
изготовление металлических значков на заказ москва <a href=https://metal-pin.ru/>где делают значки</a>
значки с логотипом на заказ цена <a href=https://metalpin.ru/>фирменные значки</a>
Создадим сайт <a href=https://giperactive.ru/>https://giperactive.ru</a> который продаёт: дизайн, верстка, интеграции. Подключим SEO и контекст, настроим аналитику и CRM. Адаптивность, скорость 90+, первые заявки уже в первый месяц. Работаем под ключ, фиксируем сроки и KPI. Напишите — оценим проект за 24 часа.
In the future, with the help of 1xBet bonus codes <a href="https://slidehtml5.com/homepage/xygv#About">https://slidehtml5.com/homepage/xygv#About</a>
Неприглядность внешнего вида здания говорит о том, что необходим ремонт фасада <a href="https://www.aek-stroy.ru/articles/kak-najti-protechku-na-kryshe-iz-metallocherepicy/">как найти протечку на крыше</a>
joszaki regisztracio <a href=https://joszaki.hu/>joszaki.hu/</a>
Experience Chicken Road 2 in your region <a href="https://coworkniagara.com">chicken road 777</a>
Everyone knows the company as a Reliable Bookmaker <a href="http://eldorado.fm/noticias/politica/4649-senado-da-1-aval-a-proposta-que-adia-eleicao-para-novembro.html">http://eldorado.fm/noticias/politica/4649-senado-da-1-aval-a-proposta-que-adia-eleicao-para-novembro.html</a>
The newest is here: <a href=https://stmaryofthehills.org/>https://stmaryofthehills.org</a>
No matter which type of bonus is most often used for betting <a href="https://www.animenewsnetwork.com/bbs/phpBB2/profile.php?mode=viewprofile&u=1108338">https://www.animenewsnetwork.com/bbs/phpBB2/profile.php?mode=viewprofile&u=1108338</a>
Topical topics are here: <a href=https://erca.com.ar/>https://erca.com.ar</a>
What you need is here: <a href=https://colegiosagradocorazon.es/>https://colegiosagradocorazon.es</a>
The most facts are here: <a href=https://playplayfun.com/>https://playplayfun.com</a>
Новое и актуальное здесь: <a href=https://badgerboats.ru/>https://badgerboats.ru</a>
Top materials are here: <a href=https://alayahotels.com/>https://alayahotels.com</a>
Hottest facts here: <a href=https://justicelanow.org/>https://justicelanow.org</a>
New first here: <a href=https://www.blockbuster.ua/>https://www.blockbuster.ua</a>
Обсуждение способов, проблем и решений при пополнении кошелька Steam <a href="https://xyberbara.com/gaming/kz-steam/">https://xyberbara.com/gaming/kz-steam/</a>
Official casino website <a href=https://betvisabengal.com/>https://betvisabengal.com</a>
Arcade online <a href=https://betvisabengal.com/>https://betvisabengal.com</a>
Портал Чернівців <a href=https://58000.com.ua/>https://58000.com.ua</a> оперативні новини, анонси культурних, громадських та спортивних подій, репортажі з міста, інтерв’ю з чернівчанами та цікаві історії. Все про життя Чернівців — щодня, просто й доступно
Мы предоставляем подробную аналитику по видимости сайта <a href="https://clickolov.ru/">накрутка посетителей</a>
Портал Чернівців <a href=https://58000.com.ua/>https://58000.com.ua</a> оперативні новини, анонси культурних, громадських та спортивних подій, репортажі з міста, інтерв’ю з чернівчанами та цікаві історії. Все про життя Чернівців — щодня, просто й доступно
The best insights here: <a href=https://deeprealestate.in/>https://deeprealestate.in</a>
Нужен компрессор? <a href=https://macunak.by/>компрессор промышленный</a> для производства и сервисов: винтовые, поршневые, безмасляные, осушители и фильтры, ресиверы, автоматика. Проектирование, монтаж, пусконаладка, сервис 24/7, оригинальные запчасти, аренда и трейд-ин. Гарантия и быстрая доставка.
Conclude the bonus clearance terms within one month <a href="https://www.imdb.com/list/ls4150036874/">https://www.imdb.com/list/ls4150036874/</a>
Hot topics here: <a href=https://amt-games.com/>https://amt-games.com</a>
Only the most important: <a href=https://www.ecuje.fr/>https://www.ecuje.fr</a>
Latest insights here: <a href=https://marchemodevintage.com/>https://marchemodevintage.com</a>
Current updates here: <a href=https://dansermag.com/>https://dansermag.com</a>
Current news right here: <a href=https://astra-hotel.ch/>https://astra-hotel.ch</a>
Всё самое лучшее здесь: <a href=https://neoko.ru/>https://neoko.ru</a>
Свежие и важные материалы: <a href=https://lookdecor.ru/>https://lookdecor.ru</a>
Самое свежее не пропусти: <a href=https://royals-mag.ru/>https://royals-mag.ru</a>
проверенная инфа тут: <a href=https://fastmb.ru/>https://fastmb.ru</a>
самое актуальное здесь: <a href=https://kmural.ru/>https://kmural.ru</a>
лучшее собрали тут: <a href=http://norco.ru/>http://norco.ru</a>
обновления здесь и сейчас: <a href=https://www.nonnagrishaeva.ru/>https://www.nonnagrishaeva.ru</a>
1xBet is the official app of the sports betting platform of the same name <a href="https://makeagif.com/user/code09?ref=XlYYna">https://makeagif.com/user/code09?ref=XlYYna</a>
1xBet is one of the most recognized online betting platforms in the world <a href="https://fnote.net/notes/sK8zPS">https://fnote.net/notes/sK8zPS</a>
The latest and most useful: <a href=https://justicelanow.org/>https://justicelanow.org</a>
All the latest here: <a href=http://planeur-condom.fr/>http://planeur-condom.fr</a>
The latest updates are here: <a href=https://www.feldbahn-ffm.de/>https://www.feldbahn-ffm.de</a>
As an example of customer motivation <a href="https://billionnews.ru/templates/artcls/index.php?gama_casino_promokod.html">https://billionnews.ru/templates/artcls/index.php?gama_casino_promokod.html</a>
All the best is here: <a href=https://www.kino-fada.fr/>https://www.kino-fada.fr</a>
The best updates are here: <a href=https://vnm.fr/>https://vnm.fr</a>
Top materials are here: <a href=https://florum.sh/>https://florum.sh</a>
Fresh every day: <a href=https://labhgroup.com/>https://labhgroup.com</a>
Видеонаблюдение под ключ Москва <a href=https://vcctv.ru/>https://vcctv.ru</a>
<a href=https://xpoker-my.com/>XPOKER</a>
New and hot here: <a href=https://bridesofbakewell.com/>https://bridesofbakewell.com</a>
The newest on this page: <a href=https://mairie-salaunes.fr/>https://mairie-salaunes.fr</a>
інформаційний портал <a href=https://01001.com.ua/>https://01001.com.ua</a> Києва: актуальні новини, політика, культура, життя міста. Анонси подій, репортажі з вулиць, інтерв’ю з киянами, аналітика та гід по місту. Все, що треба знати про Київ — щодня, просто й цікаво.
інформаційний портал <a href=https://01001.com.ua/>https://01001.com.ua</a> Києва: актуальні новини, політика, культура, життя міста. Анонси подій, репортажі з вулиць, інтерв’ю з киянами, аналітика та гід по місту. Все, що треба знати про Київ — щодня, просто й цікаво.
інформаційний портал <a href=https://65000.com.ua/>https://65000.com.ua</a> Одеси та регіону: свіжі новини, культурні, громадські та спортивні події, репортажі з вулиць, інтерв’ю з одеситами. Всі важливі зміни та цікаві історії про життя міста — у зручному форматі щодня
Надёжные велосипеды для бездорожья <a href=https://singlevisioninc.org/>kraken зеркало</a> kraken зеркало рабочее актуальные зеркала kraken kraken сайт зеркала
Для склада логистической компании мы закупили оборудование Labelaire и терминалы сбора данных. Это позволило нам ускорить процессы приёмки и отгрузки. Сканеры работают быстро и без перебоев. Мы наконец вышли на новый уровень работы <a href=https://labelaire.ru/>https://labelaire.ru/</a>
The latest materials are here: <a href=https://balatonnyomda.hu/>https://balatonnyomda.hu</a>
Useful and relevant is here: <a href=https://manorhousedentalpractice.co.uk/>https://manorhousedentalpractice.co.uk</a>
All the new stuff is here: <a href=https://www.jec.qa/>https://www.jec.qa</a>
Top topics and trends: <a href=https://www.ielts-mentor.com/>https://www.ielts-mentor.com</a>
Smart crypto trading <a href=https://terionbot.com/>https://terionbot.com</a> with auto-following and DCA: bots, rebalancing, stop-losses, and take-profits. Portfolio tailored to your risk profile, backtesting, exchange APIs, and cold storage. Transparent analytics and notifications.
The most interesting is here: <a href=https://michelsonne.com/>https://michelsonne.com</a>
Daily digest by link: <a href=https://florum.sh/>https://florum.sh</a>
Only verified materials: <a href=https://www.manaolahawaii.com/>https://www.manaolahawaii.com</a>
New every day: <a href=https://www.lnrprecision.com/>https://www.lnrprecision.com</a>
Всё лучшее у нас: <a href=http://volgazdrav.ru/>http://volgazdrav.ru</a>
The best in one place: <a href=https://agriness.com/>https://agriness.com</a>
Ежедневные обновления тут: <a href=https://waterlux.ua/>https://waterlux.ua</a>
Самая актуальная информация: <a href=https://wildlife.by/>https://wildlife.by</a>
Game enthusiasts connect to qualified vendors as a result of survive fields <a href="https://docs.google.com/forms/d/e/1FAIpQLSew8cqQ6phEgbzh8uBgZUeLAN19J2TDD2Snj616unz9nLy2Jg/viewform?usp=header">https://docs.google.com/forms/d/e/1FAIpQLSew8cqQ6phEgbzh8uBgZUeLAN19J2TDD2Snj616unz9nLy2Jg/viewform?usp=header</a>
Все самое интересное тут: <a href=https://exodontia.info/>https://exodontia.info</a>
Current collections are here: <a href=https://antarvasnastory2.in/>https://antarvasnastory2.in</a>
Лучше только у нас: <a href=https://morshynkurort.net/>https://morshynkurort.net</a>
The best materials are here: <a href=https://cosmedclinic.co.in/>https://cosmedclinic.co.in</a>
Hot topics are on this page: <a href=https://deogiricollege.org/>https://deogiricollege.org</a>
The best of what's new is here: <a href=https://ondesparalleles.org/>https://ondesparalleles.org</a>
Trends and insights are here: <a href=https://informationng.com/ >https://informationng.com/</a>
Our top topics of the day: <a href=https://healthyteennetworkblog.org/>https://healthyteennetworkblog.org</a>
What's important and relevant: <a href=https://stovespareparts.ie/>https://stovespareparts.ie</a>
The most worthwhile are here: <a href=https://possible11.com/>https://possible11.com</a>
Сломалась машина? <a href=https://avto-help-spb.ru/>помощь на дороге телефон</a> мы создали профессиональную службу автопомощи, которая неустанно следит за безопасностью автомобилистов в Санкт-Петербурге и Ленинградской области. Наши специалисты всегда на страже вашего спокойствия. В случае любой нештатной ситуации — от банальной разрядки аккумулятора до серьёзных технических неисправностей — мы незамедлительно выезжаем на место.
Сломалась машина? <a href=https://avto-help-spb.ru/>помощь авто на дороге</a> мы создали профессиональную службу автопомощи, которая неустанно следит за безопасностью автомобилистов в Санкт-Петербурге и Ленинградской области. Наши специалисты всегда на страже вашего спокойствия. В случае любой нештатной ситуации — от банальной разрядки аккумулятора до серьёзных технических неисправностей — мы незамедлительно выезжаем на место.
Обмен электронными документами между компаниями https://www.cbskiev.ru/prochee/upd-v-do-kak-uprostity-dokumentooborot-i-izbezhaty-oshibok.html
Мир гаджетов без воды <a href=https://indevices.ru/>https://indevices.ru</a> честные обзоры, реальные замеры, фото/видео-примеры. Смартфоны, планшеты, аудио, гейминг, аксессуары. Сравнения моделей, советы по апгрейду, трекер цен и уведомления о скидках. Помогаем выбрать устройство под задачи.
Ремонт и стройка <a href=https://remontkit.ru/>https://remontkit.ru</a> без лишних затрат: инструкции, таблицы расхода, сравнение цен, контроль скрытых работ. База подрядчиков, отзывы, чек-листы, калькуляторы. Тренды дизайна, 3D-планировки, лайфхаки по хранению и зонированию. Практика и цифры.
Ваш портал о стройке <a href=https://gidfundament.ru/>https://gidfundament.ru</a> и ремонте: материалы, инструменты, сметы и бюджеты. Готовые решения для кухни, ванной, спальни и террасы. Нормы, чертежи, контроль качества, приёмка работ. Подбор подрядчика, прайсы, акции и полезные образцы документов.
Ваш портал о стройке <a href=https://gidfundament.ru/>https://gidfundament.ru</a> и ремонте: материалы, инструменты, сметы и бюджеты. Готовые решения для кухни, ванной, спальни и террасы. Нормы, чертежи, контроль качества, приёмка работ. Подбор подрядчика, прайсы, акции и полезные образцы документов.
Ремонт и стройка <a href=https://remontkit.ru/>https://remontkit.ru</a> без лишних затрат: инструкции, таблицы расхода, сравнение цен, контроль скрытых работ. База подрядчиков, отзывы, чек-листы, калькуляторы. Тренды дизайна, 3D-планировки, лайфхаки по хранению и зонированию. Практика и цифры.
Все про ремонт <a href=https://lesnayaskazka74.ru/>https://lesnayaskazka74.ru</a> и строительство: от идеи до сдачи. Пошаговые гайды, электрика и инженерия, отделка, фасады и кровля. Подбор подрядчиков, сметы, шаблоны актов и договоров. Дизайн-инспирации, палитры, мебель и свет.
Мы занимаемся услугами и понимали, что без SEO клиентов будет мало. Специалисты сделали всё под ключ: от аудита до наполнения сайта статьями и настройкой аналитики. Через три месяца мы заметили серьёзный рост обращений, а сейчас поток заказов идёт стабильно. Очень рады, что выбрали именно эту команду, <a href=https://mihaylov.digital/>https://mihaylov.digital/</a>
Все про ремонт <a href=https://lesnayaskazka74.ru/>https://lesnayaskazka74.ru</a> и строительство: от идеи до сдачи. Пошаговые гайды, электрика и инженерия, отделка, фасады и кровля. Подбор подрядчиков, сметы, шаблоны актов и договоров. Дизайн-инспирации, палитры, мебель и свет.
Ремонт и строительство <a href=https://nastil69.ru/>https://nastil69.ru</a> от А до Я: планирование, закупка, логистика, контроль и приёмка. Калькуляторы смет, типовые договора, инструкции по инженерным сетям. Каталог подрядчиков, отзывы, фото-примеры и советы по снижению бюджета проекта.
Хочешь сдать акб? <a href=https://priem-akb-spb.ru/>куда сдать старый аккумулятор</a> честная цена за кг, моментальная выплата, официальная утилизация. Самовывоз от 1 шт. или приём на пункте, акт/квитанция. Безопасно и законно. Узнайте текущий тариф и ближайший адрес.
Восстанавливая естественный баланс нервной системы и снижая гиперчувствительность тканей <a href="https://mebel-zotto.ru/ishhete-otonevrologa-v-moskve-polnyj-gid-po-speczialistam-i-uslugam/">https://mebel-zotto.ru/ishhete-otonevrologa-v-moskve-polnyj-gid-po-speczialistam-i-uslugam/</a>
A sense of freedom of action fosters creative thinking and the right approach <a href="https://sketchfab.com/1xbetpromocodebangladestoday">https://sketchfab.com/1xbetpromocodebangladestoday</a>
АрендаАвто-мск <a href=https://mosavtomoto.ru/>https://mosavtomoto.ru</a> прокат авто без водителя в Москве. Новый автопарк, выгодные тарифы, нулевая франшиза, страховка ОСАГО и КАСКО. Бизнес, премиум и эконом-класс. Быстрое бронирование и аренда в день обращения. Звоните: 8 495 2900095. Свобода движения в Москве!
Ищешь аккумулятор? <a href=https://akb-shop-spb.ru/>где купить аккумулятор для авто</a> AKB SHOP занимает лидирующие позиции среди интернет-магазинов автомобильных аккумуляторов в Санкт-Петербурге. Наш ассортимент охватывает все категории транспортных средств. Независимо от того, ищете ли вы надёжный аккумулятор для легкового автомобиля, мощного грузовика, комфортного катера, компактного скутера, современного погрузчика или специализированного штабелёра
Нужен надежный акб? <a href=https://akb-store.ru/>магазин аккумуляторов в санкт петербурге</a> AKB STORE — ведущий интернет-магазин автомобильных аккумуляторов в Санкт-Петербурге! Мы специализируемся на продаже качественных аккумуляторных батарей для самой разнообразной техники. В нашем каталоге вы найдёте идеальные решения для любого транспортного средства: будь то легковой или грузовой автомобиль, катер или лодка, скутер или мопед, погрузчик или штабелер.
Ищешь аккумулятор? <a href=https://akb-shop-spb.ru/>магазин аккумуляторов в спб</a> AKB SHOP занимает лидирующие позиции среди интернет-магазинов автомобильных аккумуляторов в Санкт-Петербурге. Наш ассортимент охватывает все категории транспортных средств. Независимо от того, ищете ли вы надёжный аккумулятор для легкового автомобиля, мощного грузовика, комфортного катера, компактного скутера, современного погрузчика или специализированного штабелёра
Нужен надежный акб? <a href=https://akb-store.ru/>аккумуляторы для автомобиля спб</a> AKB STORE — ведущий интернет-магазин автомобильных аккумуляторов в Санкт-Петербурге! Мы специализируемся на продаже качественных аккумуляторных батарей для самой разнообразной техники. В нашем каталоге вы найдёте идеальные решения для любого транспортного средства: будь то легковой или грузовой автомобиль, катер или лодка, скутер или мопед, погрузчик или штабелер.
In his speech, he stated that the College has been fulfilling its responsibilities <a href="https://www.goodreads.com/user/show/194321399-1xbet-app-promo-code-app">https://www.goodreads.com/user/show/194321399-1xbet-app-promo-code-app</a>
You need to fill out a form with key information, such as your name <a href="http://cozy.moibb.ru/viewtopic.php?f=14&t=19671">http://cozy.moibb.ru/viewtopic.php?f=14&t=19671</a>
The promotion must be completed with a 5x <a href="https://www.imdb.com/list/ls4150122508/">https://www.imdb.com/list/ls4150122508/</a>
Operates under an international license, guaranteeing the absolute fairness of every round <a href="https://cdtmzk.ru">https://cdtmzk.ru</a>
I finally decided to try my hand at betting and started playing on the 1xBet platform <a href="http://fabnews.ru/forum/showthread.php?p=107255#post107255">http://fabnews.ru/forum/showthread.php?p=107255#post107255</a>
Работаем со всеми популярными моделями электросамокатов: диагностика, ремонт, настройка, тюнинг и обслуживание <a href="https://resqtr.ru/">защита от воды самокат</a>
Along with bonuses, one of the most effective elements of the 1xBet bonus program is the promotional <a href="https://band.us/page/100128511/post/1">https://band.us/page/100128511/post/1</a>
Игровые автоматы, бонусы за регистрацию и быстрые выплаты на <a href="https://tippy1casino.site/mines-game">сайт</a>
Всё о строительстве <a href=https://gidfundament.ru/>https://gidfundament.ru</a> и ремонте в одном месте: технологии, нормы, сметные калькуляторы, прайсы и тендерная лента. Каталог компаний, аренда спецтехники, рейтинги бригад и отзывы. Гайды, чек-листы и типовые решения для дома и бизнеса.
<a href=https://www.wildberries.ru/catalog/466665547/detail.aspx>https://www.wildberries.ru/catalog/466665547/detail.aspx</a>
Центр медицинского лицензирования помог оформить лицензию «под ключ», сотрудники проверяли документы, сопровождали подачу и обеспечивали полное соответствие требованиям <a href=https://licenz.pro/>https://licenz.pro/</a>
Для меня Складчик — это находка. Участвовал в складчинах по психологии и программированию. Всё пришло вовремя, материалы качественные. Очень удобно, что есть отзывы и рейтинги. Экономия до 99%. Сервис надежный и безопасный. Рекомендую всем <a href=https://v27.skladchik.org/>https://v27.skladchik.org/</a>
The popular bookmaker 1xBet is a universal gaming platform <a href="https://jobs.njota.org/profiles/7268359-code-promo-1xbet-2026-comores">https://jobs.njota.org/profiles/7268359-code-promo-1xbet-2026-comores</a>
Хотели обновить окна и обратились в Окна в СПб. Всё сделали быстро и аккуратно, без лишнего шума и грязи. Окна качественные и стильные. Отличный результат: <a href=https://okna-v-spb.ru/>https://okna-v-spb.ru/</a>
Cancel
Leave a Comment
Your email address will not be published. Required fields are marked *